| download: | usbac_setup_smof.exe |
| Full analysis: | https://app.any.run/tasks/4cc3e242-2c01-461a-a920-2c81a035c390 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 15:37:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 41D240FD2E9EA9CAF4251EE68ED235EA |
| SHA1: | 1EF051CD93A3414B5454A727C608C4A630D05646 |
| SHA256: | F52E77E843152162E6E94C58928F34F5B8DA8E40EEA2EBBE2A29EB625EB9939F |
| SSDEEP: | 49152:mnvVpDi/6+R70pvRJoaAi8PYQRSdCuBJnUs+tf0G98bSy2U+d6i:Ipen50x9X8wfBJnUsbnbD2Pd9 |
MALICIOUS
Loads dropped or rewritten executable
- VIS32X.EXE (PID: 2344)
- usbac_setup_smof.exe (PID: 1948)
Application was dropped or rewritten from another process
- SETUP.EXE (PID: 588)
- VIS32X.EXE (PID: 2344)
- USBsupervisor.exe (PID: 2444)
Registers / Runs the DLL via REGSVR32.EXE
- VIS32X.EXE (PID: 2344)
Changes the autorun value in the registry
- VIS32X.EXE (PID: 2344)
SUSPICIOUS
Executable content was dropped or overwritten
- usbac_setup_smof.exe (PID: 1948)
- SETUP.EXE (PID: 588)
- VIS32X.EXE (PID: 2344)
Creates files in the Windows directory
- SETUP.EXE (PID: 588)
- VIS32X.EXE (PID: 2344)
Creates COM task schedule object
- REGSVR32.EXE (PID: 828)
Creates files in the program directory
- VIS32X.EXE (PID: 2344)
Creates a software uninstall entry
- VIS32X.EXE (PID: 2344)
Creates files in the user directory
- VIS32X.EXE (PID: 2344)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2000:02:05 17:07:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.55 |
| CodeSize: | 35328 |
| InitializedDataSize: | 18432 |
| UninitializedDataSize: | 38400 |
| EntryPoint: | 0x5d6a |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.0.1 |
| ProductVersionNumber: | 9.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Self-extracting Setup (created with Visual Installer) |
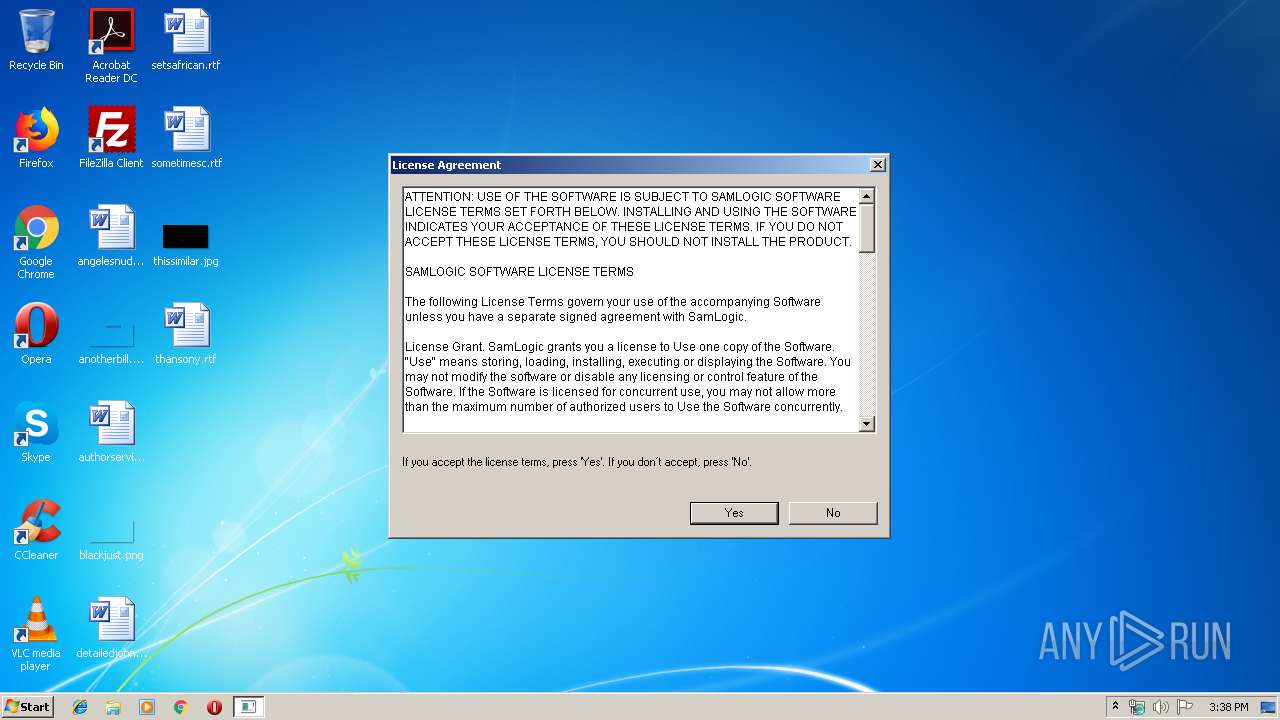
| CompanyName: | SamLogic |
| FileDescription: | Self-extracting Setup (created with Visual Installer) |
| FileVersion: | 9.00.01 |
| InternalName: | selfxfe |
| LegalCopyright: | Copyright © SamLogic |
| OriginalFileName: | selfxfe.exe |
| ProductName: | Visual Installer |
| ProductVersion: | 9.00.01 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Feb-2000 16:07:32 |
| Detected languages: |
|
| Comments: | Self-extracting Setup (created with Visual Installer) |
| CompanyName: | SamLogic |
| FileDescription: | Self-extracting Setup (created with Visual Installer) |
| FileVersion: | 9.00.01 |
| InternalName: | selfxfe |
| LegalCopyright: | Copyright © SamLogic |
| OriginalFilename: | selfxfe.exe |
| ProductName: | Visual Installer |
| ProductVersion: | 9.00.01 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 05-Feb-2000 16:07:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000089BF | 0x00008A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49581 |
.bss | 0x0000A000 | 0x00009480 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00014000 | 0x00000040 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.03148 |
.data | 0x00015000 | 0x000016D8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.49324 |
.idata | 0x00017000 | 0x00000954 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.99947 |
.edata | 0x00018000 | 0x00000234 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.31275 |
.rsrc | 0x00019000 | 0x00000EEC | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.55881 |
.reloc | 0x0001A000 | 0x00000F1A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.04047 |
actdlvry | 0x0001B000 | 0x00294000 | 0x00293A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.9986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 1.5 | 4 | Latin 1 / Western European | English - United States | UNKNOWN |
104 | 2.91463 | 218 | Latin 1 / Western European | English - United States | RT_DIALOG |
105 | 2.16096 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
MainWndProc | 2 | 0x00001000 |
StatusDlgProc | 3 | 0x000011A4 |
DZStartSelfEx | 4 | 0x0000188B |
DZEndSelfEx | 5 | 0x00001967 |
DZSelfEx | 6 | 0x000028FD |
99 | 0x00000000 | |
RemoveDoubleQuotes | 100 | 0x00004154 |
Total processes
41
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | "C:\Users\admin\AppData\Local\Temp\VIEXPAND\SETUP.EXE" | C:\Users\admin\AppData\Local\Temp\VIEXPAND\SETUP.EXE | usbac_setup_smof.exe | ||||||||||||
User: admin Company: SamLogic Integrity Level: HIGH Description: Setup Program Exit code: 0 Version: 9, 0, 0, 10 Modules
| |||||||||||||||
| 828 | C:\Windows\system32\REGSVR32.EXE "c:\windows\system32\MSVBVM60.dll" -s | C:\Windows\system32\REGSVR32.EXE | — | VIS32X.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | C:\Windows\system32\REGSVR32.EXE "c:\windows\system32\Comdlg32.ocx" -s | C:\Windows\system32\REGSVR32.EXE | — | VIS32X.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | "C:\Users\admin\AppData\Local\Temp\usbac_setup_smof.exe" | C:\Users\admin\AppData\Local\Temp\usbac_setup_smof.exe | explorer.exe | ||||||||||||
User: admin Company: SamLogic Integrity Level: HIGH Description: Self-extracting Setup (created with Visual Installer) Exit code: 0 Version: 9.00.01 Modules
| |||||||||||||||
| 2344 | C:\Users\admin\AppData\Local\Temp\VISETUP\VIS32X.EXE C:\Users\admin\AppData\Local\Temp\VIEXPAND | C:\Users\admin\AppData\Local\Temp\VISETUP\VIS32X.EXE | SETUP.EXE | ||||||||||||
User: admin Company: SamLogic Integrity Level: HIGH Description: Visual Installer Main Installer Exit code: 0 Version: 9, 0, 0, 28 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\SamLogic\USB Supervisor\USBsupervisor.exe" | C:\Program Files\SamLogic\USB Supervisor\USBsupervisor.exe | — | VIS32X.EXE | |||||||||||
User: admin Company: SamLogic Software Integrity Level: HIGH Description: USB Supervisor Exit code: 0 Version: 1.1.0.1 Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\AppData\Local\Temp\usbac_setup_smof.exe" | C:\Users\admin\AppData\Local\Temp\usbac_setup_smof.exe | — | explorer.exe | |||||||||||
User: admin Company: SamLogic Integrity Level: MEDIUM Description: Self-extracting Setup (created with Visual Installer) Exit code: 3221226540 Version: 9.00.01 Modules
| |||||||||||||||
| 3004 | C:\Windows\system32\REGSVR32.EXE "c:\windows\system32\SLXButn.ocx" -s | C:\Windows\system32\REGSVR32.EXE | — | VIS32X.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3900 | C:\Windows\system32\REGSVR32.EXE "c:\windows\system32\Comdlg32.ocx" -s | C:\Windows\system32\REGSVR32.EXE | — | VIS32X.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
782
Read events
646
Write events
120
Delete events
16
Modification events
| (PID) Process: | (1948) usbac_setup_smof.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1948) usbac_setup_smof.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3900) REGSVR32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F9043C85-F6F2-101A-A3C9-08002B2F49FB} |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3900) REGSVR32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F9043C85-F6F2-101A-A3C9-08002B2F49FB} |
| Operation: | write | Name: | |
Value: Microsoft Common Dialog Control, version 6.0 (SP6) | |||
| (PID) Process: | (3900) REGSVR32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F9043C85-F6F2-101A-A3C9-08002B2F49FB}\InprocServer32 |
| Operation: | write | Name: | |
Value: c:\windows\system32\Comdlg32.ocx | |||
| (PID) Process: | (3900) REGSVR32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F9043C85-F6F2-101A-A3C9-08002B2F49FB}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (3900) REGSVR32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComDlg.CommonDialog |
| Operation: | write | Name: | |
Value: Microsoft Common Dialog Control, version 6.0 (SP6) | |||
| (PID) Process: | (3900) REGSVR32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComDlg.CommonDialog\CLSID |
| Operation: | write | Name: | |
Value: {F9043C85-F6F2-101A-A3C9-08002B2F49FB} | |||
| (PID) Process: | (3900) REGSVR32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComDlg.CommonDialog\CurVer |
| Operation: | write | Name: | |
Value: MSComDlg.CommonDialog.1 | |||
| (PID) Process: | (3900) REGSVR32.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComDlg.CommonDialog.1 |
| Operation: | write | Name: | |
Value: Microsoft Common Dialog Control, version 6.0 (SP6) | |||
Executable files
21
Suspicious files
4
Text files
108
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1948 | usbac_setup_smof.exe | C:\Users\admin\AppData\Local\Temp\H1a02792\_ad48.adx | ini | |
MD5:— | SHA256:— | |||
| 1948 | usbac_setup_smof.exe | C:\Users\admin\AppData\Local\Temp\VIEXPAND\FILEDATA.DAT | compressed | |
MD5:— | SHA256:— | |||
| 588 | SETUP.EXE | C:\Users\admin\AppData\Local\Temp\VISETUP\temp.000 | — | |
MD5:— | SHA256:— | |||
| 1948 | usbac_setup_smof.exe | C:\Users\admin\AppData\Local\Temp\VIEXPAND\FILELIST.INF | text | |
MD5:— | SHA256:— | |||
| 1948 | usbac_setup_smof.exe | C:\Users\admin\AppData\Local\Temp\_ad48.dll | executable | |
MD5:350B8FA87BA295530FC18A393F13DD39 | SHA256:DCBBBCA362638E938F26E81CD7E0B4ABE152B14ADC4EB95EF89D7DC7566CB015 | |||
| 1948 | usbac_setup_smof.exe | C:\Users\admin\AppData\Local\Temp\VIEXPAND\DESOBJ.DAT | compressed | |
MD5:9A9F32BFFFD888A803F35361A9EFD2E8 | SHA256:018DAF1813EF85D7295A5395400BB801422FC10F79E9FF4A3FE6A96DEE3519EE | |||
| 588 | SETUP.EXE | C:\Windows\temp.000 | — | |
MD5:— | SHA256:— | |||
| 1948 | usbac_setup_smof.exe | C:\Users\admin\AppData\Local\Temp\VIEXPAND\ENGLISH-INTERNET-USBAC.LNG | text | |
MD5:535E249FC5BA67B1D4F727BF6C440C3D | SHA256:1740C4BA0D370F59ACD114652861AAB387AD0007BDFE912F18474447A8E65634 | |||
| 1948 | usbac_setup_smof.exe | C:\Users\admin\AppData\Local\Temp\VIEXPAND\SETUP.EXE | executable | |
MD5:62AC659F6364E50BA9770CD61182AC02 | SHA256:569F056983D5E24F5867B880678B0B0031BCD04229D4923B4498106A78EE36C7 | |||
| 1948 | usbac_setup_smof.exe | C:\Users\admin\AppData\Local\Temp\VIEXPAND\W5U.man | xml | |
MD5:5186D0F494ED0CDE18AD27E0A7394502 | SHA256:752ADEDF7763BB6969D4B9777A6291A12ED17732AFF1EC8BB242E99247309A14 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report