| File name: | JDownloader.jar |
| Full analysis: | https://app.any.run/tasks/94781859-5107-4868-a269-aa85c2f87772 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2020, 04:31:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | 995E43D989E30CFD5289DA17F41275FA |
| SHA1: | 6006E0915D2A485EF6DE684BDC78357EC80EB07B |
| SHA256: | F52342201874896EDA372063F7B704B7A3758D0FE1CA9F5F9B485CCBCFE3AC97 |
| SSDEEP: | 49152:1bra1QxXQN2LMZQ94EUUO8CcAzvPYFlu+KJLDM9CHz+hE2yMwe3HUy367YVKMdpN:wi6eMu40AzUlu/JLDM4HCLKmpzAOyi |
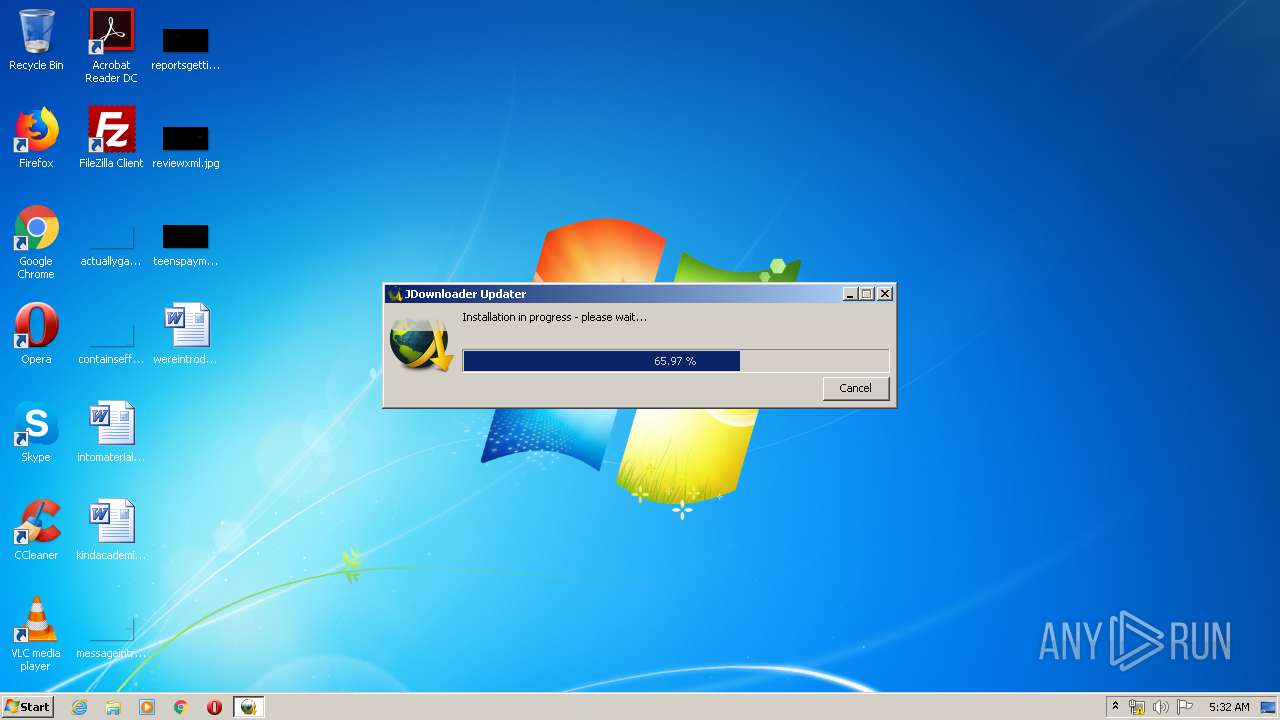
MALICIOUS
Loads dropped or rewritten executable
- javaw.exe (PID: 3552)
- javaw.exe (PID: 1332)
- javaw.exe (PID: 2084)
SUSPICIOUS
Executable content was dropped or overwritten
- javaw.exe (PID: 3552)
- javaw.exe (PID: 2084)
- javaw.exe (PID: 1332)
Application launched itself
- javaw.exe (PID: 3552)
- javaw.exe (PID: 1332)
Executes JAVA applets
- javaw.exe (PID: 1332)
- javaw.exe (PID: 3552)
Uses REG.EXE to modify Windows registry
- javaw.exe (PID: 3552)
- javaw.exe (PID: 2084)
Creates files in the user directory
- javaw.exe (PID: 3552)
INFO
Drops Coronavirus (possible) decoy
- javaw.exe (PID: 2084)
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 3552)
- javaw.exe (PID: 2084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:11:30 11:42:05 |
| ZipCRC: | 0x390f57d5 |
| ZipCompressedSize: | 119 |
| ZipUncompressedSize: | 138 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
42
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1140 | reg query "HKEY_CURRENT_USER\Control Panel\Desktop" /v "ForegroundLockTimeout" | C:\Windows\system32\reg.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar C:\Users\admin\AppData\Local\Temp\tmp\update\self\JDU\JDownloader.jar -selftest tmp/selftest_1586925114401 C:\Users\admin\AppData\Local\Temp | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1832 | reg query "HKEY_CURRENT_USER\Control Panel\Desktop" /v "ForegroundLockTimeout" | C:\Windows\system32\reg.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar JDownloader.jar -afterupdate | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\JDownloader.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
61
Read events
61
Write events
0
Delete events
0
Modification events
Executable files
39
Suspicious files
16
Text files
1 294
Unknown types
2 258
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\cfg\ProxySelector.proxies.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\cfg\org.jdownloader.settings.InternetConnectionSettings.customproxylist.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\update\versioninfo\JD\org.appwork.updatesys.client.tracker.TrackConfig.tracklog.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\update\versioninfo\JDU\org.appwork.updatesys.client.tracker.TrackConfig.tracklog.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\tmp\update\JD\updatePackage.id.bac | — | |
MD5:— | SHA256:— | |||
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\tmp\update\JDU\updatePackage.id.bac | — | |
MD5:— | SHA256:— | |||
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\tmp\update\JD\updatePackage | — | |
MD5:— | SHA256:— | |||
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\cfg\org.jdownloader.updatev2.UpdateSettings.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\cfg\org.jdownloader.settings.InternetConnectionSettings.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3552 | javaw.exe | C:\Users\admin\AppData\Local\Temp\update\versioninfo\JDU\org.appwork.updatesys.client.tracker.TrackConfig.json.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
10
DNS requests
5
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3552 | javaw.exe | GET | 200 | 176.9.34.43:80 | http://update.appwork.org/jcgi/track?rt=SO&jn=JDownloader.jar&pv=5&cv=2100000001&ping=&uid=1586925083229_-4692590382423189063_jd&pkh=12f1848a883e733ed40fffff0dae2f35&app=JD&os=WINDOWS&arch=X86&os64=0&jvm64=0&urev=2147483647&srev=-1&surev=-1&ct=Normal&data=%7B%22json%22%3A%22%7B%5C%22timeStamp%5C%22%3A1586925083943%2C%5C%22data%5C%22%3A%5C%22%7B%5C%5C%5C%22resume%5C%5C%5C%22%3Afalse%2C%5C%5C%5C%22expectedBytes%5C%5C%5C%22%3A33752192%2C%5C%5C%5C%22clientRepo%5C%5C%5C%22%3A%5C%5C%5C%22JDownloader%2F201707061810%5C%5C%5C%22%2C%5C%5C%5C%22cdnSignature%5C%5C%5C%22%3A%5C%5C%5C%22VALID%5C%5C%5C%22%2C%5C%5C%5C%22serverTag%5C%5C%5C%22%3A%5C%5C%5C%22nginx%2F1.17.8%5C%5C%5C%22%2C%5C%5C%5C%22url%5C%5C%5C%22%3A%5C%5C%5C%22http%3A%2F%2Fcdn12.appwork.org%2FJD%2F13803%2F1586875845539309653e099d963cc93917827320f2f49_00a440fadb9b4087a832b74567a1b52dee858477f-0%5C%5C%5C%22%2C%5C%5C%5C%22responseCode%5C%5C%5C%22%3A200%2C%5C%5C%5C%22timeStamp%5C%5C%5C%22%3A1586925083943%2C%5C%5C%5C%22duration%5C%5C%5C%22%3A20750%2C%5C%5C%5C%22responseBytes%5C%5C%5C%22%3A33752192%2C%5C%5C%5C%22resumeFrom%5C%5C%5C%22%3A0%2C%5C%5C%5C%22bytes%5C%5C%5C%22%3A33752192%2C%5C%5C%5C%22host%5C%5C%5C%22%3A%5C%5C%5C%22cdn12.appwork.org%5C%5C%5C%22%2C%5C%5C%5C%22logVersion%5C%5C%5C%22%3A1%2C%5C%5C%5C%22contentType%5C%5C%5C%22%3A%5C%5C%5C%22application%2Foctet-stream%5C%5C%5C%22%2C%5C%5C%5C%22status%5C%5C%5C%22%3A%5C%5C%5C%22OK%5C%5C%5C%22%7D%5C%22%2C%5C%22id%5C%22%3A1586925083948%2C%5C%22type%5C%22%3A%5C%22TRAFFIC_LOG%5C%22%7D%22%2C%22type%22%3A%22TRAFFIC_LOG%22%7D&1586925104693 | DE | — | 2 b | suspicious |
1332 | javaw.exe | GET | 302 | 176.9.34.43:80 | http://update.appwork.org/jcgi/lastchance?app=JD&pkh=12f1848a883e733ed40fffff0dae2f35&jh=0ee18a29e8fffada88ea15e6410d5e07&rev=-1&srev=-1&urev=-1&surev=-1&rt=ST&st=1 | DE | — | — | suspicious |
3552 | javaw.exe | GET | 200 | 176.9.34.43:80 | http://update.appwork.org/jcgi/pkg?rt=SO&jn=JDownloader.jar&pv=5&cv=2100000001&ping=&uid=1586925083635_-3333409489452660248_jds&pkh=12f1848a883e733ed40fffff0dae2f35&app=JDU&os=WINDOWS&arch=X86&os64=0&jvm64=0&ct=Normal&rev=-1&dedup=INTRA&awfcxz=1&dst=-1&lng=en_US&chlg=0&jdiff=1&1586925083635 | DE | text | 3.30 Kb | suspicious |
3552 | javaw.exe | GET | 200 | 176.9.34.43:80 | http://update.appwork.org/jcgi/pkg?rt=SO&jn=JDownloader.jar&pv=5&cv=2100000001&ping=&uid=1586925083229_-4692590382423189063_jd&pkh=12f1848a883e733ed40fffff0dae2f35&app=JD&os=WINDOWS&arch=X86&os64=0&jvm64=0&urev=2147483647&srev=-1&surev=-1&ct=Normal&rev=-1&dedup=INTRA&awfcxz=1&dst=-1&lng=en_US&chlg=0&jdiff=1&1586925083744 | DE | text | 3.30 Kb | suspicious |
3552 | javaw.exe | GET | 200 | 176.9.43.113:80 | http://cdn6.appwork.org/JDU/13835/1586875678715463369d7354619fb6b2e89c5b33aa9a3_04c24bc6ac9131116824ff5b8b4c3a3997f668bb3-0 | DE | binary | 3.19 Mb | suspicious |
3552 | javaw.exe | GET | 200 | 136.243.166.109:80 | http://cdn12.appwork.org/JD/13803/1586875845539309653e099d963cc93917827320f2f49_00a440fadb9b4087a832b74567a1b52dee858477f-0 | DE | binary | 32.1 Mb | suspicious |
3552 | javaw.exe | GET | 200 | 176.9.34.43:80 | http://update.appwork.org/jcgi/pkg?rt=SO&jn=JDownloader.jar&pv=5&cv=2100000001&ping=&uid=1586925083229_-4692590382423189063_jd&pkh=12f1848a883e733ed40fffff0dae2f35&app=JD&os=WINDOWS&arch=X86&os64=0&jvm64=0&urev=-1&srev=-1&surev=-1&ct=Normal&rev=-1&dedup=INTRA&awfcxz=1&dst=-1&lng=en_US&chlg=0&jdiff=1&1586925083244 | DE | text | 10 b | suspicious |
1332 | javaw.exe | GET | 200 | 176.9.34.43:80 | http://cdn4.appwork.org/JD/JD_lastChanceRescueMe.jar.enc | DE | binary | 1.66 Kb | suspicious |
2084 | javaw.exe | GET | 200 | 176.9.34.43:80 | http://update.appwork.org/jcgi/pkg?st=0&rt=SO&jn=JDownloader.jar&pv=9&cv=20190425001&pkh=12f1848a883e733ed40fffff0dae2f35&app=JD&os=WINDOWS&osr=WINDOWS_7&arch=X86&os64=0&jvm64=0&java=18092014&uid=dnt_&urev=13835&srev=-1&surev=13835&ct=Normal&rev=13803&dedup=INTRA&awfcxz=1&dst=-1&lng=en_US&chlg=0&jdiff=1&1586925121494 | DE | text | 163 b | suspicious |
3552 | javaw.exe | GET | 200 | 176.9.34.43:80 | http://update.appwork.org/jcgi/track?rt=SO&jn=JDownloader.jar&pv=5&cv=2100000001&ping=&uid=1586925083635_-3333409489452660248_jds&pkh=12f1848a883e733ed40fffff0dae2f35&app=JDU&os=WINDOWS&arch=X86&os64=0&jvm64=0&ct=Normal&data=%7B%22json%22%3A%22%7B%5C%22timeStamp%5C%22%3A1586925083950%2C%5C%22data%5C%22%3A%5C%22%7B%5C%5C%5C%22resume%5C%5C%5C%22%3Afalse%2C%5C%5C%5C%22expectedBytes%5C%5C%5C%22%3A3342384%2C%5C%5C%5C%22clientRepo%5C%5C%5C%22%3A%5C%5C%5C%22JDownloader%2F201707061810%5C%5C%5C%22%2C%5C%5C%5C%22cdnSignature%5C%5C%5C%22%3A%5C%5C%5C%22VALID%5C%5C%5C%22%2C%5C%5C%5C%22serverTag%5C%5C%5C%22%3A%5C%5C%5C%22nginx%2F1.17.8%5C%5C%5C%22%2C%5C%5C%5C%22url%5C%5C%5C%22%3A%5C%5C%5C%22http%3A%2F%2Fcdn6.appwork.org%2FJDU%2F13835%2F1586875678715463369d7354619fb6b2e89c5b33aa9a3_04c24bc6ac9131116824ff5b8b4c3a3997f668bb3-0%5C%5C%5C%22%2C%5C%5C%5C%22responseCode%5C%5C%5C%22%3A200%2C%5C%5C%5C%22timeStamp%5C%5C%5C%22%3A1586925083950%2C%5C%5C%5C%22duration%5C%5C%5C%22%3A3781%2C%5C%5C%5C%22responseBytes%5C%5C%5C%22%3A3342384%2C%5C%5C%5C%22resumeFrom%5C%5C%5C%22%3A0%2C%5C%5C%5C%22bytes%5C%5C%5C%22%3A3342384%2C%5C%5C%5C%22host%5C%5C%5C%22%3A%5C%5C%5C%22cdn6.appwork.org%5C%5C%5C%22%2C%5C%5C%5C%22logVersion%5C%5C%5C%22%3A1%2C%5C%5C%5C%22contentType%5C%5C%5C%22%3A%5C%5C%5C%22application%2Foctet-stream%5C%5C%5C%22%2C%5C%5C%5C%22status%5C%5C%5C%22%3A%5C%5C%5C%22OK%5C%5C%5C%22%7D%5C%22%2C%5C%22id%5C%22%3A1586925083947%2C%5C%22type%5C%22%3A%5C%22TRAFFIC_LOG%5C%22%7D%22%2C%22type%22%3A%22TRAFFIC_LOG%22%7D&1586925087732 | DE | — | 2 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3552 | javaw.exe | 176.9.34.43:80 | update.appwork.org | Hetzner Online GmbH | DE | suspicious |
3552 | javaw.exe | 176.9.43.113:80 | cdn6.appwork.org | Hetzner Online GmbH | DE | suspicious |
3552 | javaw.exe | 136.243.166.109:80 | cdn12.appwork.org | Hetzner Online GmbH | DE | suspicious |
1332 | javaw.exe | 176.9.34.43:80 | update.appwork.org | Hetzner Online GmbH | DE | suspicious |
2084 | javaw.exe | 176.9.34.43:80 | update.appwork.org | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.appwork.org |
| suspicious |
cdn6.appwork.org |
| suspicious |
cdn12.appwork.org |
| suspicious |
cdn4.appwork.org |
| suspicious |
Threats
10 ETPRO signatures available at the full report