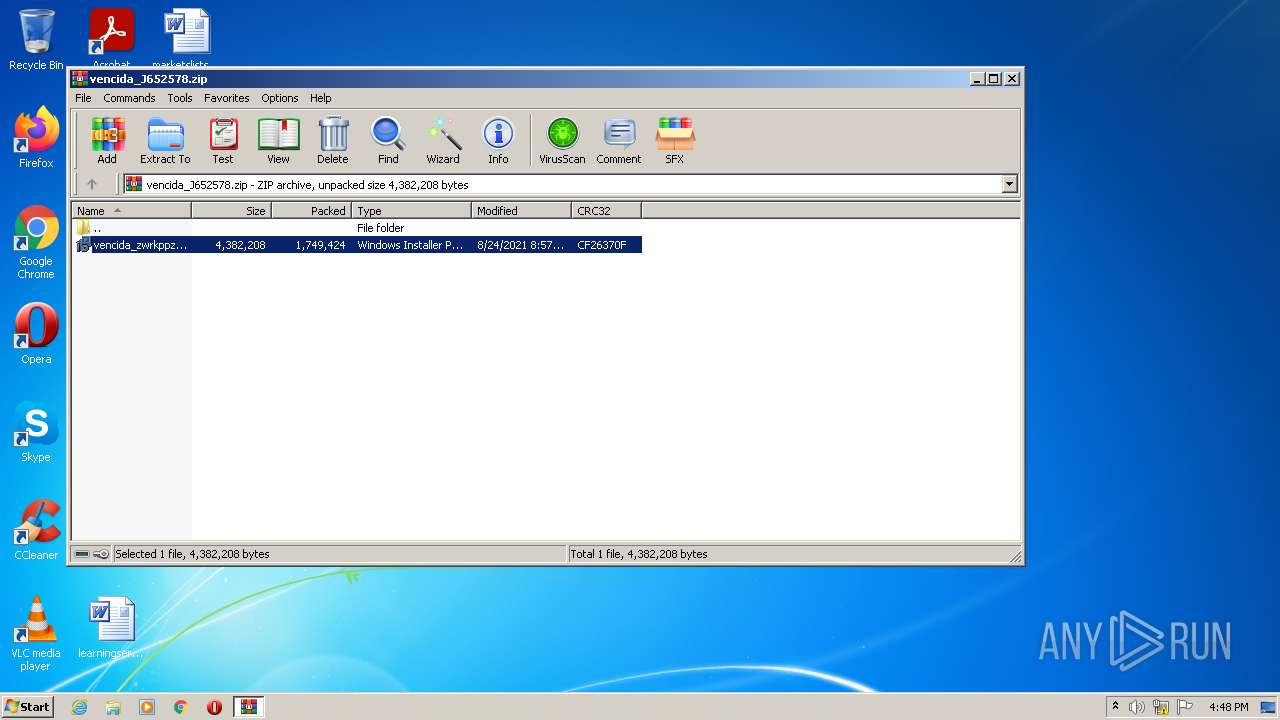
| File name: | vencida_J652578.zip |
| Full analysis: | https://app.any.run/tasks/ca273dd3-0c55-40d3-b57a-94cc7b2830d1 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 16:48:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D7930677973A81830433F17BD56BA842 |
| SHA1: | E1A6DCBB292CD7A64071BACF5A8C00A07981EA25 |
| SHA256: | F5061906FFE0725067ADA699207270F653CEEB28BB55068CFAFA9CAFCFDF6001 |
| SSDEEP: | 24576:cuCuJmFxlGtvJQ2sNLb9rVKMURxtffdLYmHNRUqzfEm8RmzduiZ3PozJEQ1O1n7D:8uJeQi24b90lnBFtS08RvltEsW7jU2 |
MALICIOUS
Drops executable file immediately after starts
- msiexec.exe (PID: 3956)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2228)
- MsiExec.exe (PID: 3408)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3912)
Checks supported languages
- WinRAR.exe (PID: 3912)
Starts Microsoft Installer
- WinRAR.exe (PID: 3912)
Executed as Windows Service
- msiexec.exe (PID: 3956)
Reads Windows owner or organization settings
- msiexec.exe (PID: 1440)
- msiexec.exe (PID: 3956)
- msiexec.exe (PID: 3720)
Reads the Windows organization settings
- msiexec.exe (PID: 1440)
- msiexec.exe (PID: 3956)
- msiexec.exe (PID: 3720)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3956)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 3956)
Application launched itself
- msiexec.exe (PID: 3956)
INFO
Checks supported languages
- msiexec.exe (PID: 3956)
- msiexec.exe (PID: 1440)
- MsiExec.exe (PID: 2228)
- msiexec.exe (PID: 3720)
- MsiExec.exe (PID: 3408)
Reads the computer name
- msiexec.exe (PID: 1440)
- msiexec.exe (PID: 3956)
- MsiExec.exe (PID: 2228)
- MsiExec.exe (PID: 3408)
- msiexec.exe (PID: 3720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | vencida_zwrkppzaxqa.msi |
|---|---|
| ZipUncompressedSize: | 4382208 |
| ZipCompressedSize: | 1749424 |
| ZipCRC: | 0xcf26370f |
| ZipModifyDate: | 2021:08:24 19:57:14 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
39
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1440 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Rar$EXa3912.6382\vencida_zwrkppzaxqa.msi" | C:\Windows\System32\msiexec.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2228 | C:\Windows\system32\MsiExec.exe -Embedding 0ECF5CB1F359711551DB633C4229FC91 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3408 | C:\Windows\system32\MsiExec.exe -Embedding D9DCC003DFA71B12513676F3A4A3C05F | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3720 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Rar$EXa3912.7228\vencida_zwrkppzaxqa.msi" | C:\Windows\System32\msiexec.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3912 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\vencida_J652578.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3956 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 154
Read events
5 080
Write events
51
Delete events
23
Modification events
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\vencida_J652578.zip | |||
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3912) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
6
Suspicious files
8
Text files
0
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3912 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3912.6382\vencida_zwrkppzaxqa.msi | — | |
MD5:— | SHA256:— | |||
| 3956 | msiexec.exe | C:\Windows\Installer\19450e.msi | — | |
MD5:— | SHA256:— | |||
| 3912 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3912.7228\vencida_zwrkppzaxqa.msi | — | |
MD5:— | SHA256:— | |||
| 3956 | msiexec.exe | C:\Windows\Installer\194512.msi | — | |
MD5:— | SHA256:— | |||
| 3956 | msiexec.exe | C:\Windows\Installer\194510.ipi | binary | |
MD5:— | SHA256:— | |||
| 3956 | msiexec.exe | C:\Windows\Installer\SourceHash{B9336F0D-359B-45BE-BF2A-8661F790585D} | binary | |
MD5:— | SHA256:— | |||
| 3956 | msiexec.exe | C:\Config.Msi\194511.rbs | binary | |
MD5:— | SHA256:— | |||
| 3956 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF4C24555C42BD8883.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3956 | msiexec.exe | C:\Windows\Installer\MSI46A6.tmp | binary | |
MD5:— | SHA256:— | |||
| 3956 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFE19BA4E24D103457.TMP | gmc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report