| File name: | RtkBtManServ.exe |
| Full analysis: | https://app.any.run/tasks/e236de88-26e8-46cf-9764-37ac8e660fbf |
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2024, 08:50:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 88AB0BB59B0B20816A833BA91C1606D3 |
| SHA1: | 72C09B7789A4BAC8FEE41227D101DAED8437EDEB |
| SHA256: | F4FB42C8312A6002A8783E2A1AB4571EB89E92CD192B1A21E8C4582205C37312 |
| SSDEEP: | 49152:AsmhnqAs9pJc0dnKh+Q0N1rs+vIUSg+6+8ohnRh1Na1OKM6nYAKhFQpSH3Oh5gxz:6qXpy05Q0N1rsYSZ6BoXh1kkypSH3Ohu |
MALICIOUS
Drops the executable file immediately after the start
- RtkBtManServ.exe (PID: 3628)
- RtkBtManServ.exe (PID: 4320)
- RtkBtManServ.exe (PID: 2892)
- RtkBtManServ.exe (PID: 5220)
- RtkBtManServ.exe (PID: 2968)
- RtkBtManServ.exe (PID: 4264)
- RtkBtManServ.exe (PID: 2404)
- RtkBtManServ.exe (PID: 4800)
- RtkBtManServ.exe (PID: 3156)
- RtkBtManServ.exe (PID: 2992)
- RtkBtManServ.exe (PID: 4052)
- RtkBtManServ.exe (PID: 3392)
- RtkBtManServ.exe (PID: 3560)
- RtkBtManServ.exe (PID: 2392)
- RtkBtManServ.exe (PID: 3720)
- RtkBtManServ.exe (PID: 2860)
- RtkBtManServ.exe (PID: 1908)
- RtkBtManServ.exe (PID: 1784)
- RtkBtManServ.exe (PID: 3124)
SUSPICIOUS
Executable content was dropped or overwritten
- RtkBtManServ.exe (PID: 3628)
- RtkBtManServ.exe (PID: 4320)
- RtkBtManServ.exe (PID: 2892)
- RtkBtManServ.exe (PID: 5220)
- RtkBtManServ.exe (PID: 2968)
- RtkBtManServ.exe (PID: 4264)
- RtkBtManServ.exe (PID: 2404)
- RtkBtManServ.exe (PID: 4800)
- RtkBtManServ.exe (PID: 3156)
- RtkBtManServ.exe (PID: 2992)
- RtkBtManServ.exe (PID: 3392)
- RtkBtManServ.exe (PID: 4052)
- RtkBtManServ.exe (PID: 3560)
- RtkBtManServ.exe (PID: 3720)
- RtkBtManServ.exe (PID: 2392)
- RtkBtManServ.exe (PID: 2860)
- RtkBtManServ.exe (PID: 1908)
- RtkBtManServ.exe (PID: 1784)
- RtkBtManServ.exe (PID: 3124)
Executes application which crashes
- RtkBtManServ.exe (PID: 3628)
- RtkBtManServ.exe (PID: 4320)
- RtkBtManServ.exe (PID: 2892)
- RtkBtManServ.exe (PID: 5220)
- RtkBtManServ.exe (PID: 2968)
- RtkBtManServ.exe (PID: 2404)
- RtkBtManServ.exe (PID: 4264)
- RtkBtManServ.exe (PID: 4800)
- RtkBtManServ.exe (PID: 3156)
- RtkBtManServ.exe (PID: 4052)
- RtkBtManServ.exe (PID: 1784)
- RtkBtManServ.exe (PID: 1908)
- RtkBtManServ.exe (PID: 2392)
INFO
Checks supported languages
- RtkBtManServ.exe (PID: 3628)
- RtkBtManServ.exe (PID: 4320)
- RtkBtManServ.exe (PID: 2892)
- RtkBtManServ.exe (PID: 5220)
- RtkBtManServ.exe (PID: 2968)
- RtkBtManServ.exe (PID: 2404)
- RtkBtManServ.exe (PID: 4264)
- RtkBtManServ.exe (PID: 3156)
- RtkBtManServ.exe (PID: 2992)
- RtkBtManServ.exe (PID: 4800)
- RtkBtManServ.exe (PID: 3392)
- RtkBtManServ.exe (PID: 4052)
- RtkBtManServ.exe (PID: 3560)
- RtkBtManServ.exe (PID: 2392)
- RtkBtManServ.exe (PID: 3720)
- RtkBtManServ.exe (PID: 1908)
- RtkBtManServ.exe (PID: 2860)
- RtkBtManServ.exe (PID: 3124)
- RtkBtManServ.exe (PID: 1784)
Reads the machine GUID from the registry
- RtkBtManServ.exe (PID: 3628)
- RtkBtManServ.exe (PID: 4320)
- RtkBtManServ.exe (PID: 2892)
- RtkBtManServ.exe (PID: 2968)
- RtkBtManServ.exe (PID: 2404)
- RtkBtManServ.exe (PID: 5220)
- RtkBtManServ.exe (PID: 4264)
- RtkBtManServ.exe (PID: 3156)
- RtkBtManServ.exe (PID: 2992)
- RtkBtManServ.exe (PID: 4800)
- RtkBtManServ.exe (PID: 3392)
- RtkBtManServ.exe (PID: 3560)
- RtkBtManServ.exe (PID: 4052)
- RtkBtManServ.exe (PID: 3720)
- RtkBtManServ.exe (PID: 2392)
- RtkBtManServ.exe (PID: 2860)
- RtkBtManServ.exe (PID: 1908)
- RtkBtManServ.exe (PID: 1784)
- RtkBtManServ.exe (PID: 3124)
Reads the computer name
- RtkBtManServ.exe (PID: 3628)
- RtkBtManServ.exe (PID: 4320)
- RtkBtManServ.exe (PID: 2892)
- RtkBtManServ.exe (PID: 5220)
- RtkBtManServ.exe (PID: 2968)
- RtkBtManServ.exe (PID: 2404)
- RtkBtManServ.exe (PID: 4264)
- RtkBtManServ.exe (PID: 4800)
- RtkBtManServ.exe (PID: 3156)
- RtkBtManServ.exe (PID: 2992)
- RtkBtManServ.exe (PID: 3392)
- RtkBtManServ.exe (PID: 4052)
- RtkBtManServ.exe (PID: 3560)
- RtkBtManServ.exe (PID: 2392)
- RtkBtManServ.exe (PID: 3720)
- RtkBtManServ.exe (PID: 2860)
- RtkBtManServ.exe (PID: 1908)
- RtkBtManServ.exe (PID: 3124)
- RtkBtManServ.exe (PID: 1784)
Checks proxy server information
- WerFault.exe (PID: 2892)
- WerFault.exe (PID: 1580)
- WerFault.exe (PID: 4180)
- WerFault.exe (PID: 5524)
- WerFault.exe (PID: 1736)
- WerFault.exe (PID: 4524)
- WerFault.exe (PID: 3780)
- WerFault.exe (PID: 1616)
- WerFault.exe (PID: 2276)
- WerFault.exe (PID: 4808)
- WerFault.exe (PID: 740)
- WerFault.exe (PID: 6100)
- WerFault.exe (PID: 4084)
Reads the software policy settings
- WerFault.exe (PID: 2892)
- WerFault.exe (PID: 1580)
- WerFault.exe (PID: 4180)
- WerFault.exe (PID: 5524)
- WerFault.exe (PID: 1736)
- WerFault.exe (PID: 4524)
- WerFault.exe (PID: 3780)
- WerFault.exe (PID: 1616)
- WerFault.exe (PID: 2276)
- WerFault.exe (PID: 6100)
- WerFault.exe (PID: 4084)
- WerFault.exe (PID: 4808)
- WerFault.exe (PID: 740)
Create files in a temporary directory
- RtkBtManServ.exe (PID: 3628)
- RtkBtManServ.exe (PID: 4320)
- RtkBtManServ.exe (PID: 2892)
- RtkBtManServ.exe (PID: 2968)
- RtkBtManServ.exe (PID: 2404)
- RtkBtManServ.exe (PID: 5220)
- RtkBtManServ.exe (PID: 4264)
- RtkBtManServ.exe (PID: 4800)
- RtkBtManServ.exe (PID: 3156)
- RtkBtManServ.exe (PID: 2992)
- RtkBtManServ.exe (PID: 3392)
- RtkBtManServ.exe (PID: 3560)
- RtkBtManServ.exe (PID: 4052)
- RtkBtManServ.exe (PID: 3720)
- RtkBtManServ.exe (PID: 2392)
- RtkBtManServ.exe (PID: 2860)
- RtkBtManServ.exe (PID: 1784)
- RtkBtManServ.exe (PID: 1908)
- RtkBtManServ.exe (PID: 3124)
Creates files or folders in the user directory
- WerFault.exe (PID: 2892)
- WerFault.exe (PID: 1580)
- WerFault.exe (PID: 4180)
- WerFault.exe (PID: 5524)
- WerFault.exe (PID: 1736)
- WerFault.exe (PID: 3780)
- WerFault.exe (PID: 4524)
- WerFault.exe (PID: 1616)
- WerFault.exe (PID: 2276)
- WerFault.exe (PID: 4084)
- WerFault.exe (PID: 6100)
- WerFault.exe (PID: 4808)
- WerFault.exe (PID: 740)
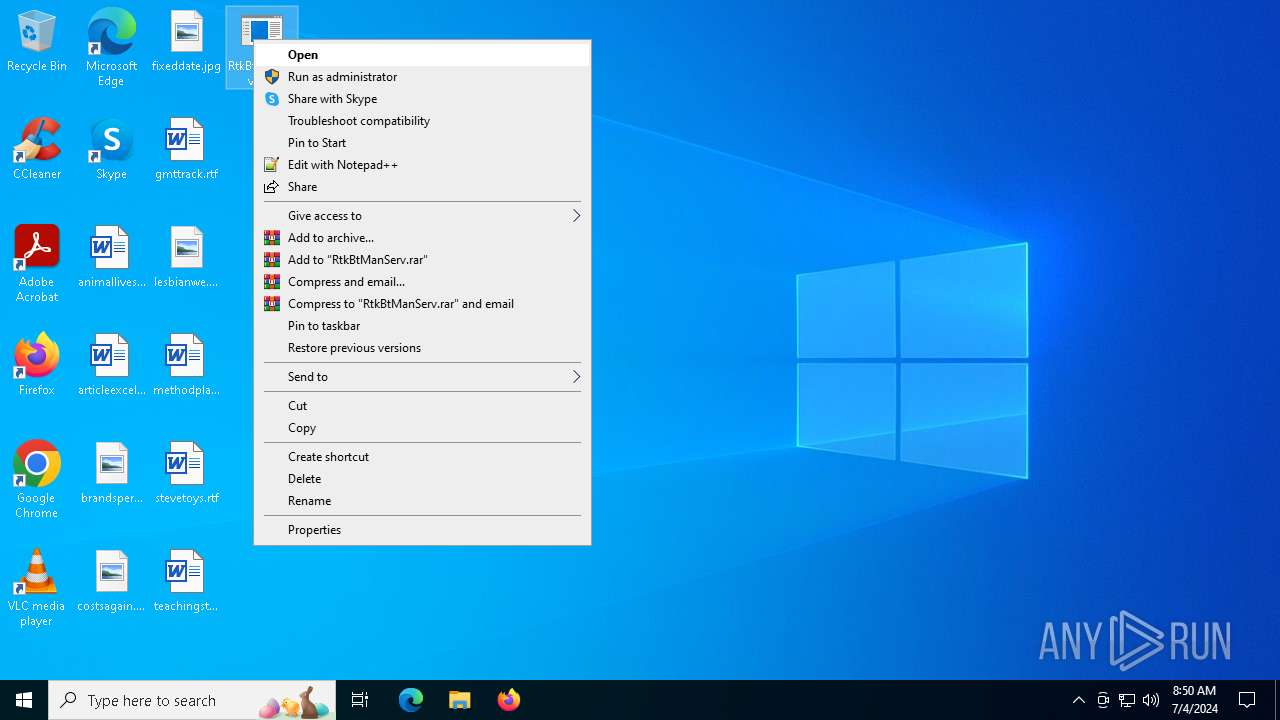
Manual execution by a user
- RtkBtManServ.exe (PID: 4320)
- RtkBtManServ.exe (PID: 2968)
- RtkBtManServ.exe (PID: 2892)
- RtkBtManServ.exe (PID: 5220)
- RtkBtManServ.exe (PID: 2404)
- RtkBtManServ.exe (PID: 4264)
- RtkBtManServ.exe (PID: 3156)
- RtkBtManServ.exe (PID: 4800)
- RtkBtManServ.exe (PID: 2992)
- RtkBtManServ.exe (PID: 3392)
- RtkBtManServ.exe (PID: 4052)
- RtkBtManServ.exe (PID: 3560)
- RtkBtManServ.exe (PID: 2860)
- RtkBtManServ.exe (PID: 2392)
- RtkBtManServ.exe (PID: 3720)
- RtkBtManServ.exe (PID: 1908)
- RtkBtManServ.exe (PID: 3124)
- RtkBtManServ.exe (PID: 1784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:04:17 11:56:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 2957824 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2d413e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | RtkBtManServ |
| FileVersion: | 1.0.0.0 |
| InternalName: | RtkBtManServ.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | RtkBtManServ.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
173
Monitored processes
32
Malicious processes
19
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 740 | C:\WINDOWS\system32\WerFault.exe -u -p 1784 -s 1016 | C:\Windows\System32\WerFault.exe | RtkBtManServ.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | C:\WINDOWS\system32\WerFault.exe -u -p 4320 -s 1032 | C:\Windows\System32\WerFault.exe | RtkBtManServ.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | C:\WINDOWS\system32\WerFault.exe -u -p 4800 -s 1016 | C:\Windows\System32\WerFault.exe | RtkBtManServ.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1736 | C:\WINDOWS\system32\WerFault.exe -u -p 2968 -s 988 | C:\Windows\System32\WerFault.exe | RtkBtManServ.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1784 | "C:\Users\admin\Desktop\RtkBtManServ.exe" | C:\Users\admin\Desktop\RtkBtManServ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RtkBtManServ Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1908 | "C:\Users\admin\Desktop\RtkBtManServ.exe" | C:\Users\admin\Desktop\RtkBtManServ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RtkBtManServ Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\WerFault.exe -u -p 3156 -s 1020 | C:\Windows\System32\WerFault.exe | RtkBtManServ.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\Desktop\RtkBtManServ.exe" | C:\Users\admin\Desktop\RtkBtManServ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RtkBtManServ Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2404 | "C:\Users\admin\Desktop\RtkBtManServ.exe" | C:\Users\admin\Desktop\RtkBtManServ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RtkBtManServ Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2860 | "C:\Users\admin\Desktop\RtkBtManServ.exe" | C:\Users\admin\Desktop\RtkBtManServ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RtkBtManServ Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
95 339
Read events
95 330
Write events
3
Delete events
6
Modification events
| (PID) Process: | (1580) WerFault.exe | Key: | \REGISTRY\A\{cef23de6-2269-dd7f-b394-4df0d530c736}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (1580) WerFault.exe | Key: | \REGISTRY\A\{cef23de6-2269-dd7f-b394-4df0d530c736}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1580) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsSelfHost\FIDs |
| Operation: | delete value | Name: | AllFlights |
Value: | |||
Executable files
110
Suspicious files
320
Text files
79
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\xwizard.cfg | text | |
MD5:AE8EED5A6B1470AEC0E7FECE8B0669EF | SHA256:3F6CA2BC068C8436044DAAB867F8FF8F75060048B29882CB2AC9FDEF1800DF9E | |||
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\winhlp32.exe | executable | |
MD5:A776E68F497C996788B406A3DC5089EB | SHA256:071E26DDF5323DD9ED6671BCDE89DF73D78BAC2336070E6CB9E3E4B93BDE78D1 | |||
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\hh.exe | executable | |
MD5:4D4C98ECA32B14AEB074DB34CD0881E4 | SHA256:4182172A01BDFC08C5CF7E8652F7D9D81858345A770E2B6B507840E4C1C7764F | |||
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\bfsvc.exe | executable | |
MD5:899D3ED011EB58459B8A4FC2B81F0924 | SHA256:5E3F311AE67F046B56435067BCDD39FBF836FA0421FBC8C8B0E43E8E47524954 | |||
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\splwow64.exe | executable | |
MD5:0D8360781E488E250587A17FBEFA646C | SHA256:EBFF7D07EFDA7245192CE6ECD7767578152B515B510C887CA2880A2566071F64 | |||
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\snuvcdsm.exe | executable | |
MD5:053778713819BEAB3DF309DF472787CD | SHA256:F999357A17E672E87FBED66D14BA2BEBD6FB04E058A1AAE0F0FDC49A797F58FE | |||
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\xwizard.exe | executable | |
MD5:DF991217F1CFADD9ACFA56F878DA5EE7 | SHA256:DEB1246347CE88E8CDD63A233A64BC2090B839F2D933A3097A2FD8FD913C4112 | |||
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\costura.costura.dll.compressed | binary | |
MD5:9AB99399CB17964E3E30B7DDEB6BB8B9 | SHA256:BDFED3E39A17DBC95D43FC5141904414A62E8B459F338F65A2F1C3D1FACDDD2F | |||
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\costura.dotnetzip.dll.compressed | binary | |
MD5:D8DDF1B53026B9CD42CB65CBA187F726 | SHA256:1C180A0267230CB43C84ED8CD3B2BD1A660C54AED994001ECFE94CF71D951FF6 | |||
| 3628 | RtkBtManServ.exe | C:\Users\admin\AppData\Local\Temp\bfsvc.cfg | text | |
MD5:5242530A2B65089696F3CF8E5EE02FF7 | SHA256:239A1D9844DDBD0E650F8E5DE69A2A40067106A79878FA4948A8039F1573B781 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
35
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4752 | MoUsoCoreWorker.exe | GET | 200 | 88.221.110.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
4976 | RUXIMICS.exe | GET | 200 | 88.221.110.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
1832 | svchost.exe | GET | 200 | 88.221.110.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | unknown |
4752 | MoUsoCoreWorker.exe | GET | 200 | 23.211.9.92:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | unknown |
1832 | svchost.exe | GET | 200 | 23.211.9.92:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | unknown |
4976 | RUXIMICS.exe | GET | 200 | 23.211.9.92:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | unknown |
— | — | POST | 200 | 20.189.173.9:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1832 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4976 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4752 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4752 | MoUsoCoreWorker.exe | 88.221.110.122:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4976 | RUXIMICS.exe | 88.221.110.122:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1832 | svchost.exe | 88.221.110.122:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4752 | MoUsoCoreWorker.exe | 23.211.9.92:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4976 | RUXIMICS.exe | 23.211.9.92:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1832 | svchost.exe | 23.211.9.92:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |