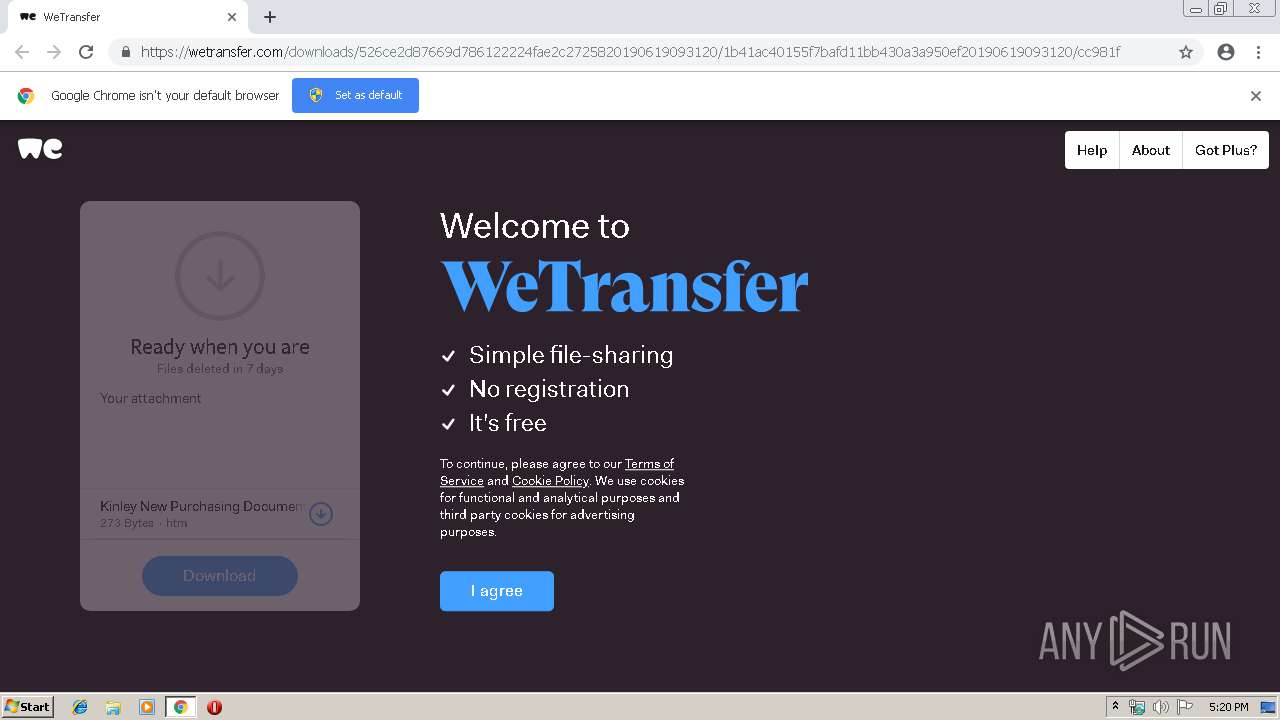
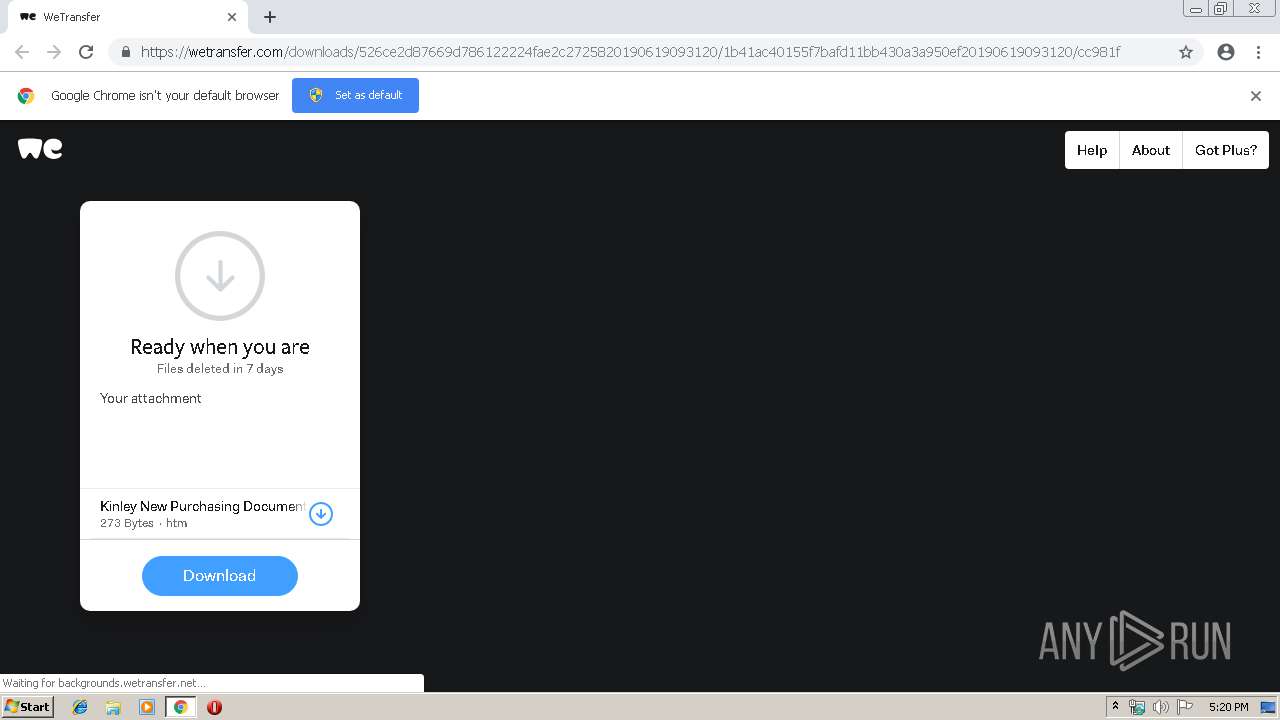
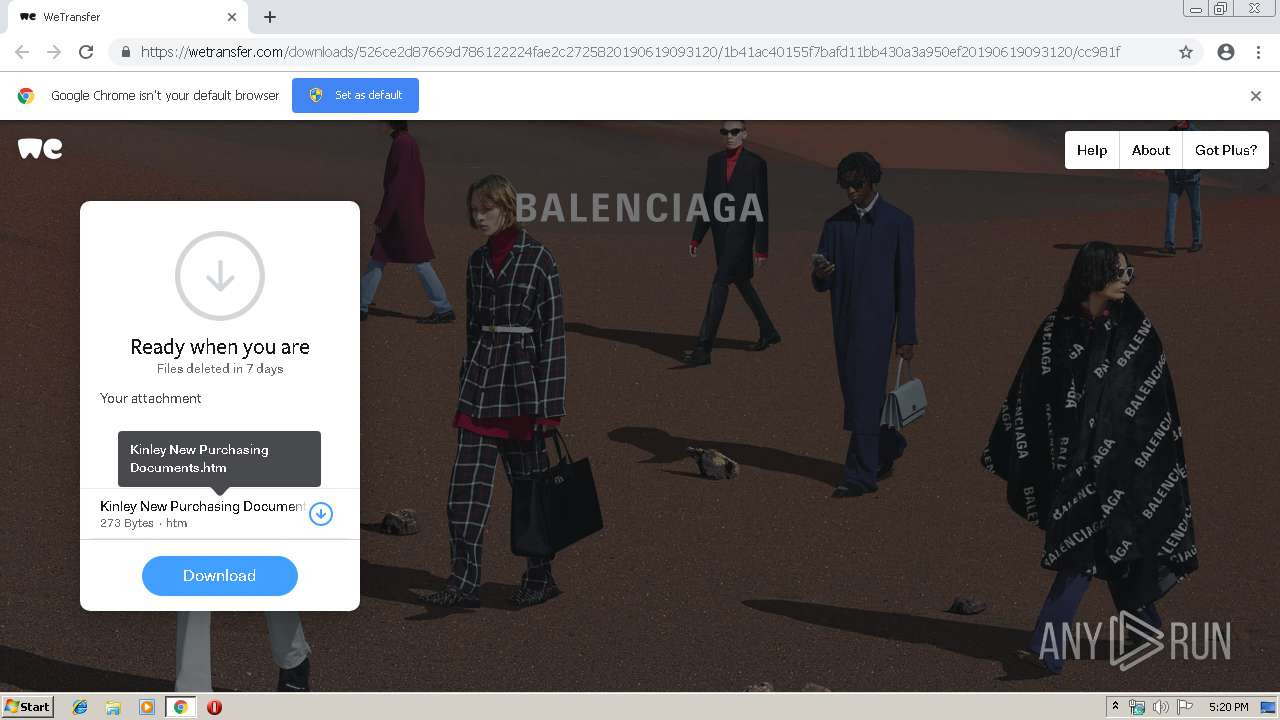
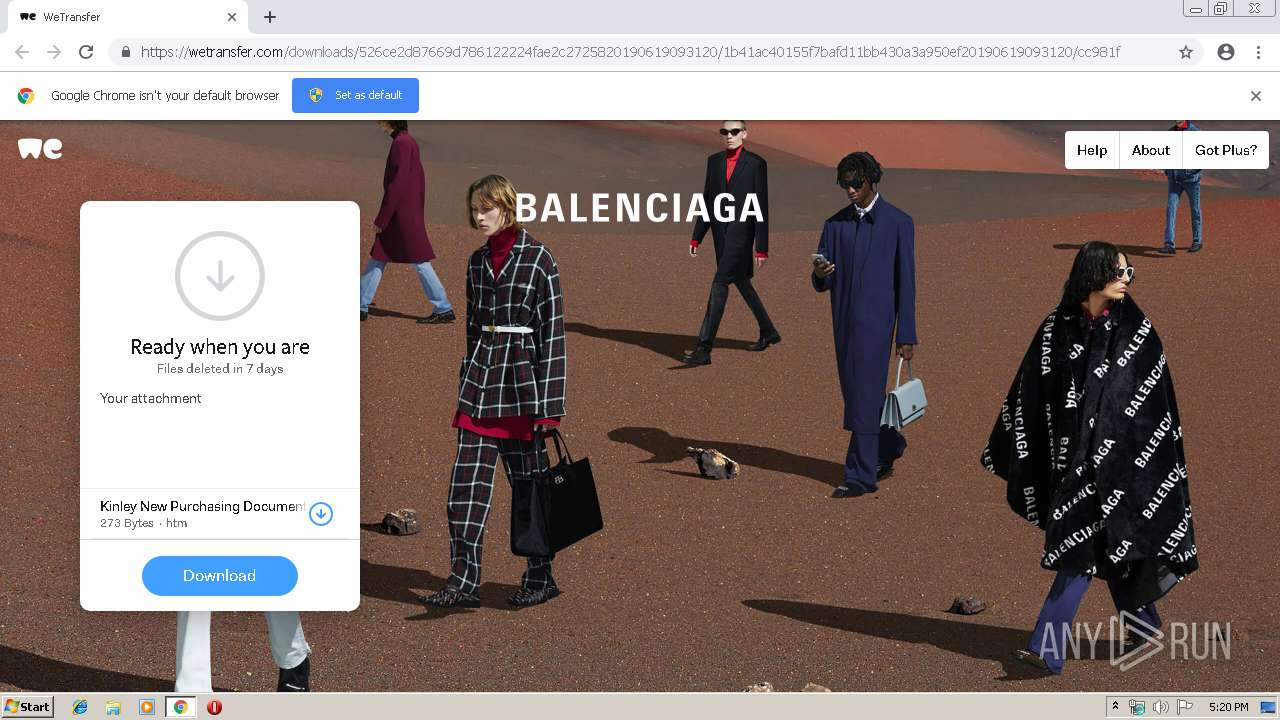
| URL: | https://wetransfer.com/downloads/526ce2d87669d786122224fae2c2725820190619093120/1b41ac40155f7bafd11bb430a3a950ef20190619093120/cc981f |
| Full analysis: | https://app.any.run/tasks/c2045573-1729-4c72-850f-a26f78cedb4f |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 16:19:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5755D1DA228F5D305E56928DF3198D5F |
| SHA1: | FDCC2866E2AB23A73A4248E78F57EF577CEFD1CA |
| SHA256: | F4EFADAA1977E44DB7AD21B6A3B6D5ABB91285BAF045BEC25F651607B4624EBA |
| SSDEEP: | 3:N8RCYKMXKQXITcBuYX3RlGCeFKtgUHRdG+9dNw6h4XpYtgRJn:2EYNaQXNlXhl4EgUxdz4XpqgRJn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2988)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2988)
Reads Microsoft Office registry keys
- chrome.exe (PID: 2988)
Reads settings of System Certificates
- chrome.exe (PID: 2988)
Application launched itself
- chrome.exe (PID: 2988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=125579007123944257 --mojo-platform-channel-handle=464 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1591518395332927680 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1591518395332927680 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13469813023389807981 --mojo-platform-channel-handle=4284 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1778165847153774349 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1778165847153774349 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15096332155784628139 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15096332155784628139 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15724906485675538755 --mojo-platform-channel-handle=4928 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10383316255243427263 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10383316255243427263 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --service-pipe-token=9224297308187589924 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9224297308187589924 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12775575083650748914 --mojo-platform-channel-handle=4252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7571182727255606888 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7571182727255606888 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
636
Read events
524
Write events
107
Delete events
5
Modification events
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2988-13205434810312875 |
Value: 259 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
87
Text files
212
Unknown types
12
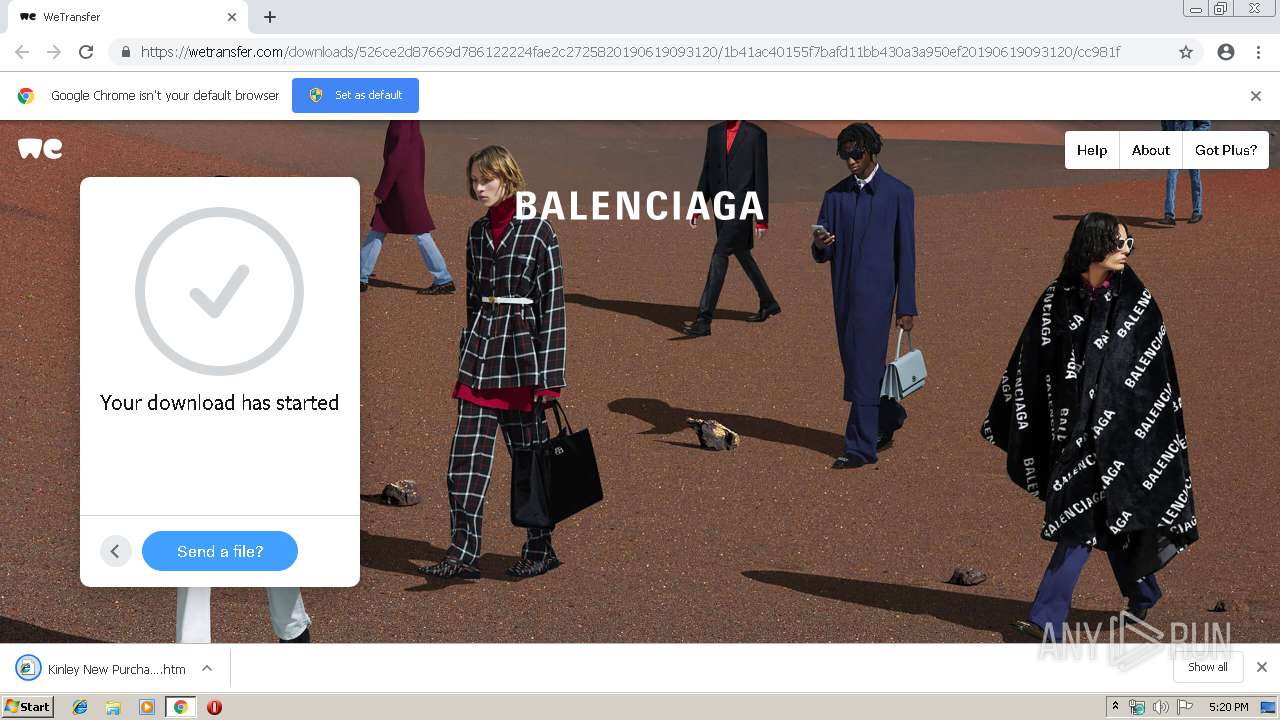
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bba3b1ae-e562-4241-8ad6-5251d14aeb71.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
96
DNS requests
54
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
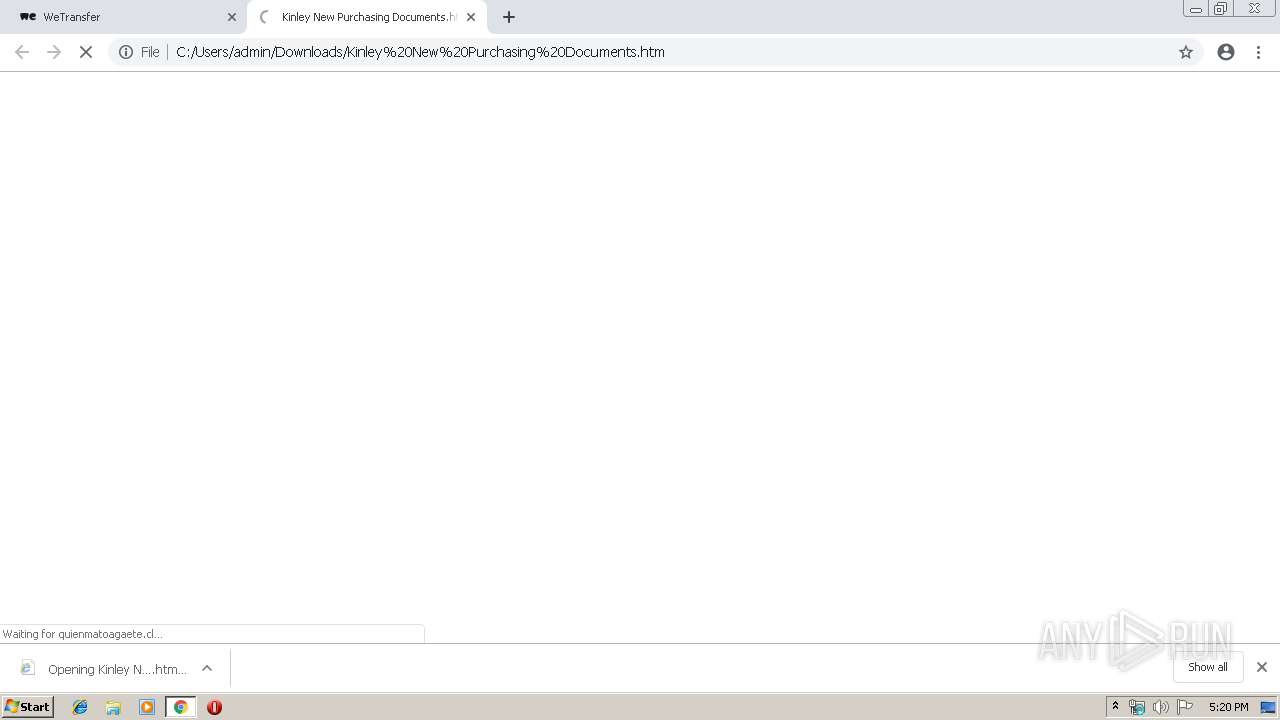
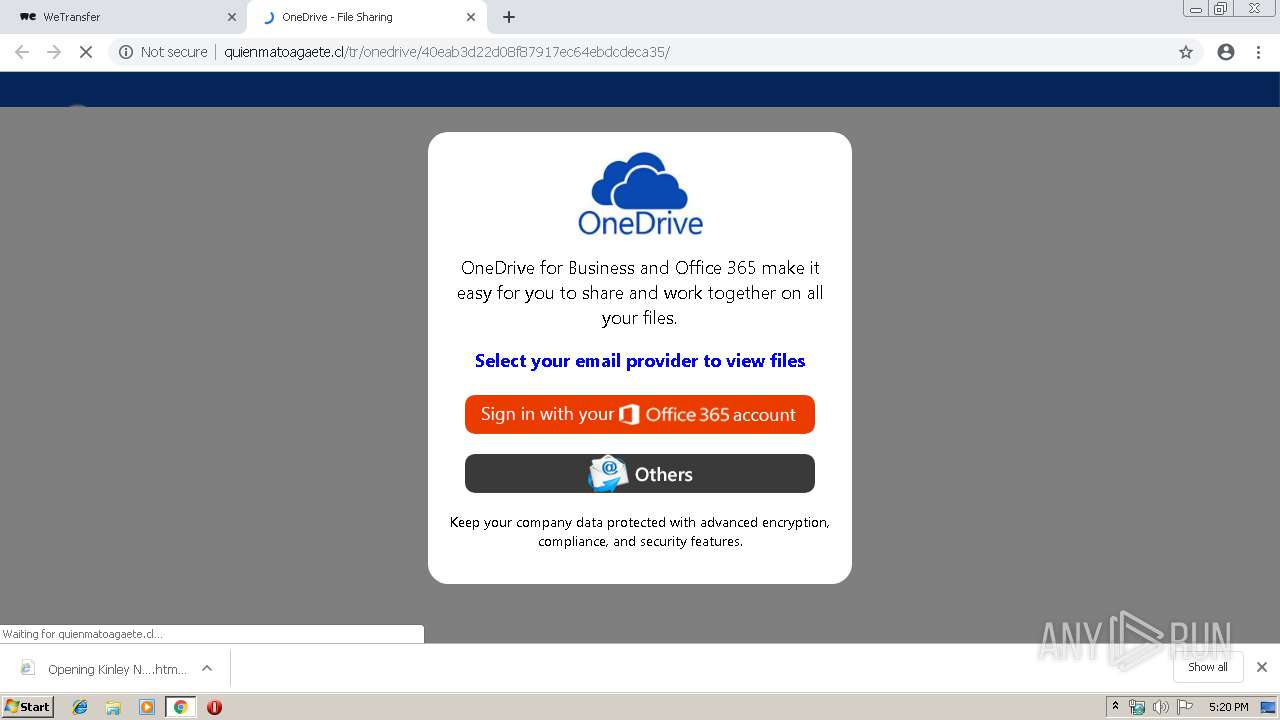
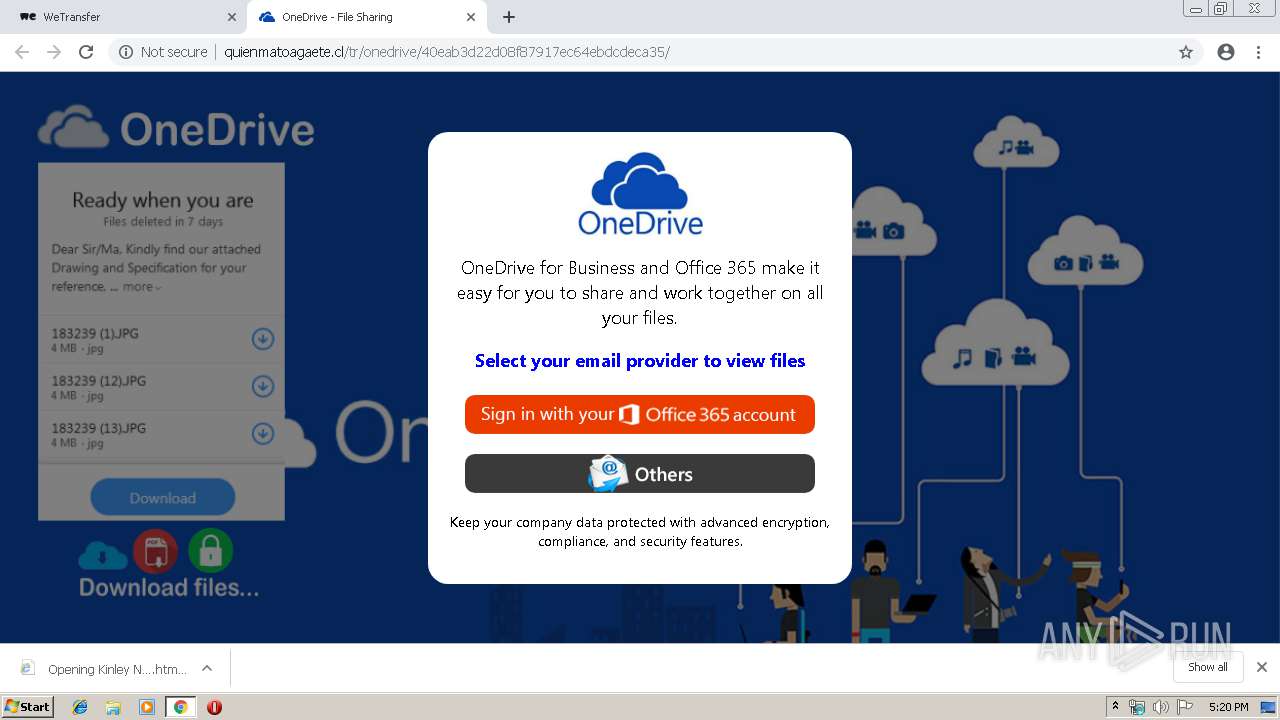
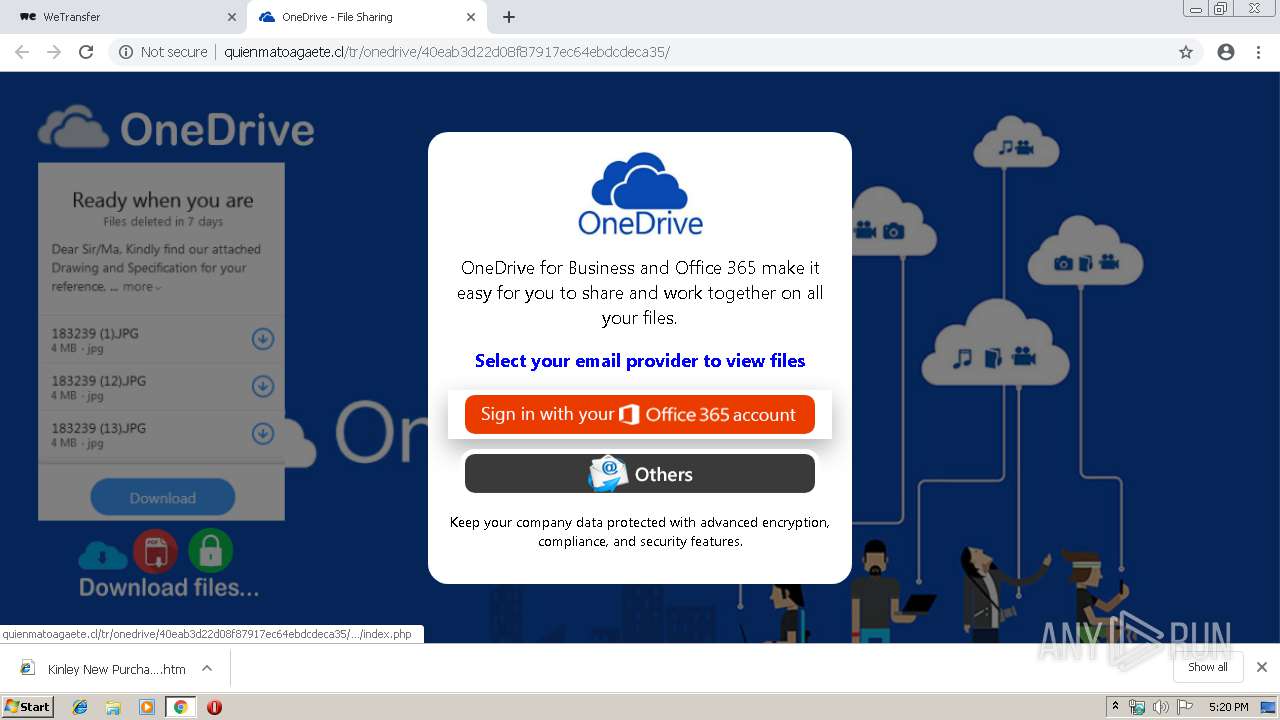
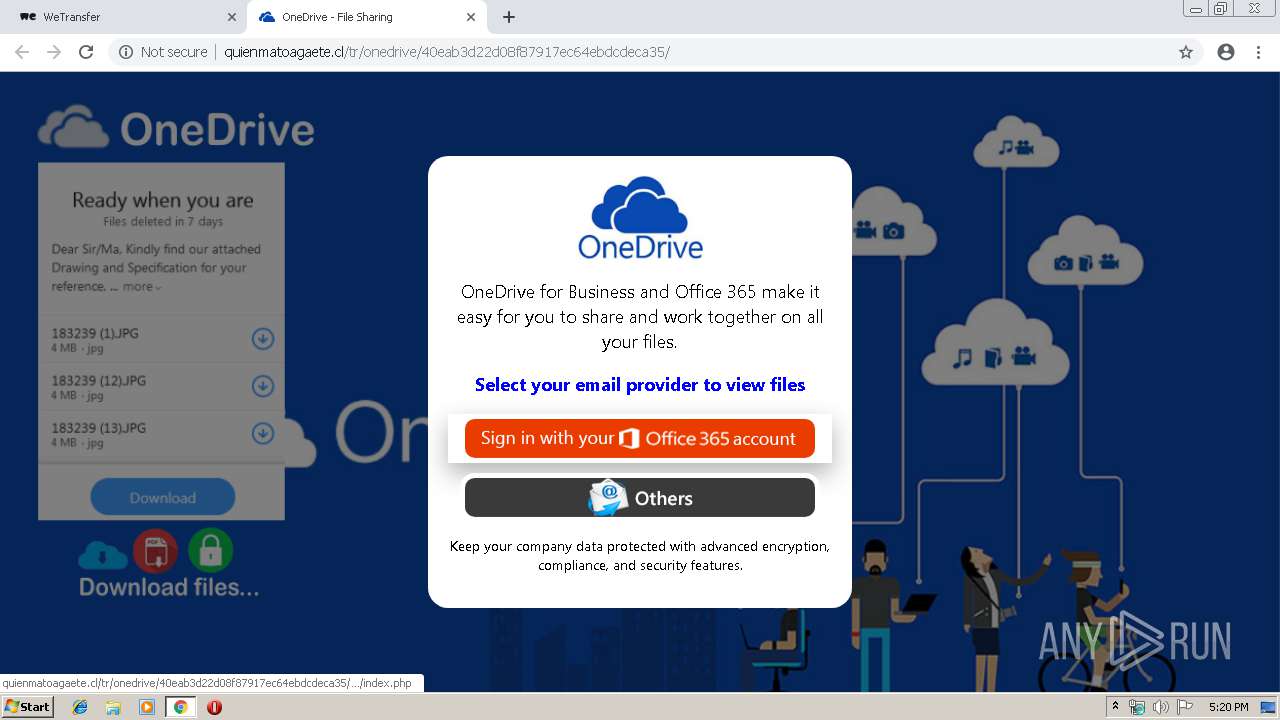
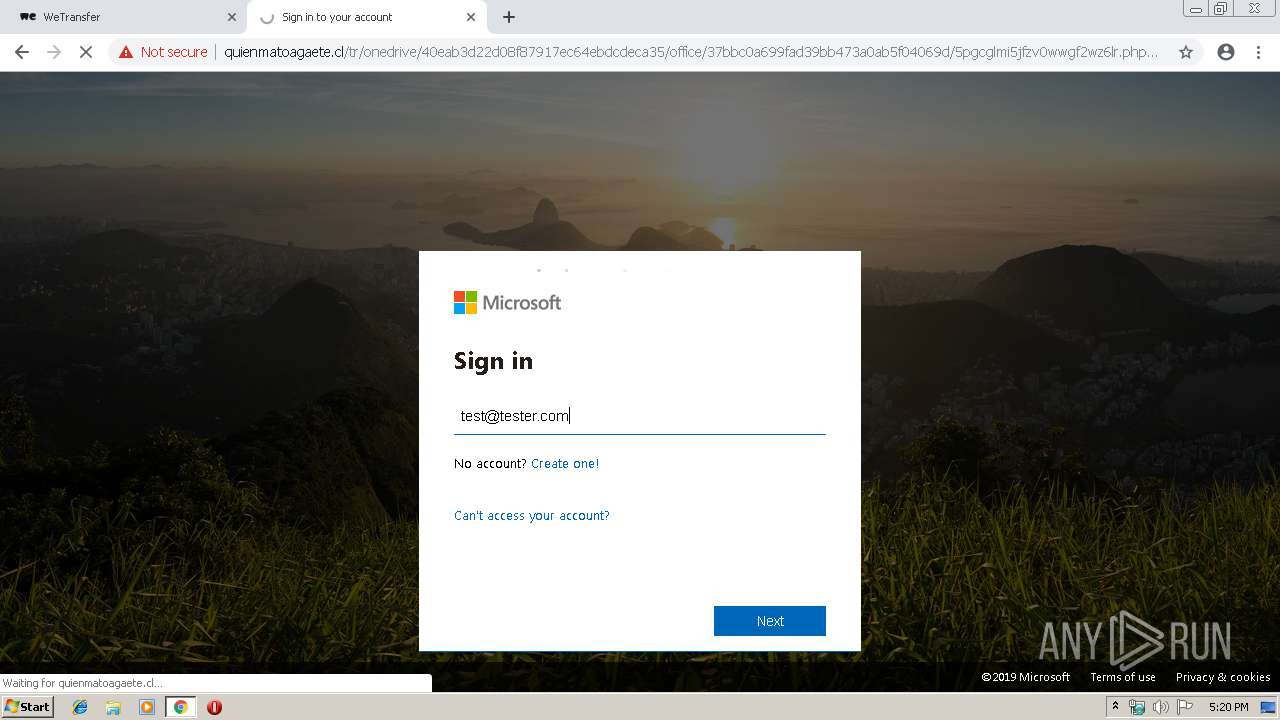
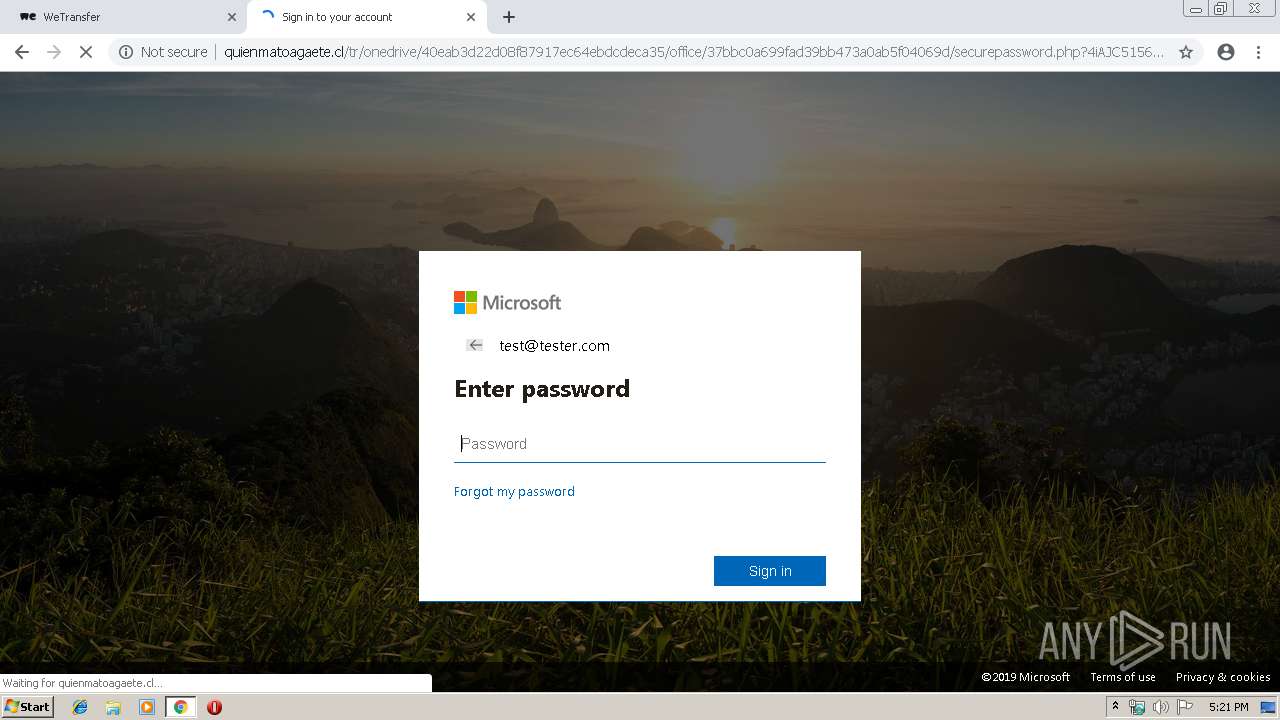
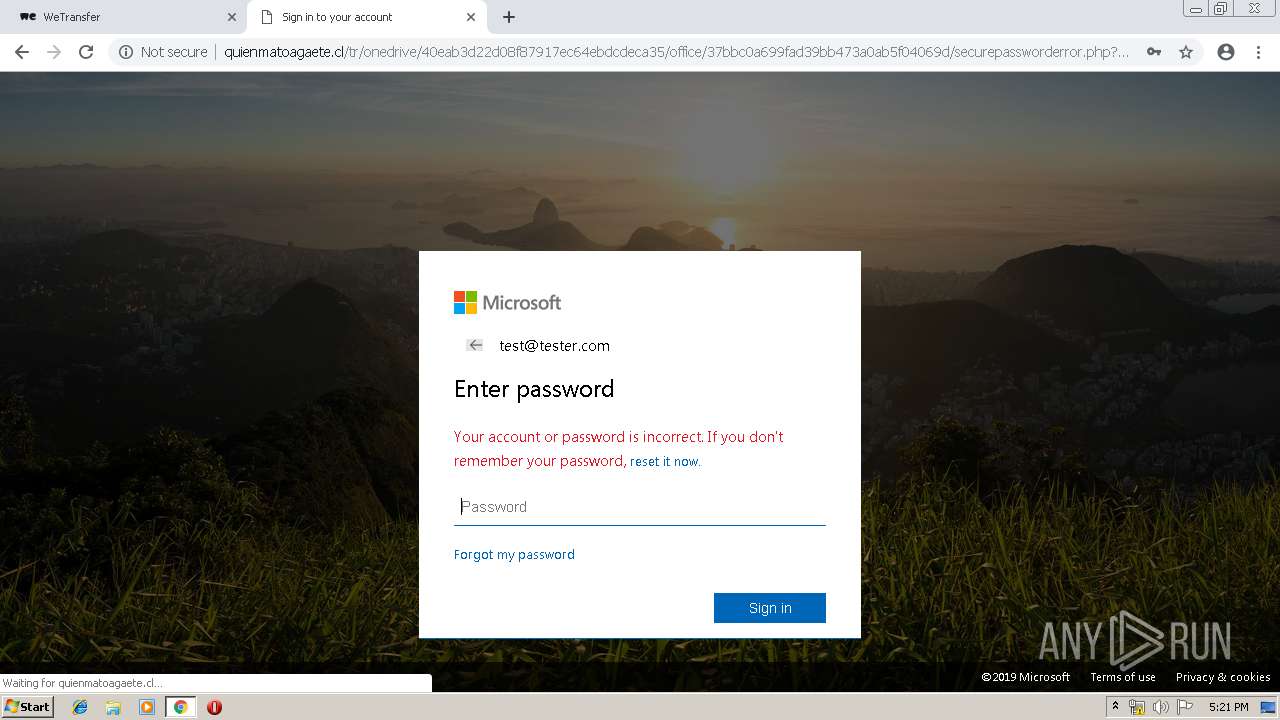
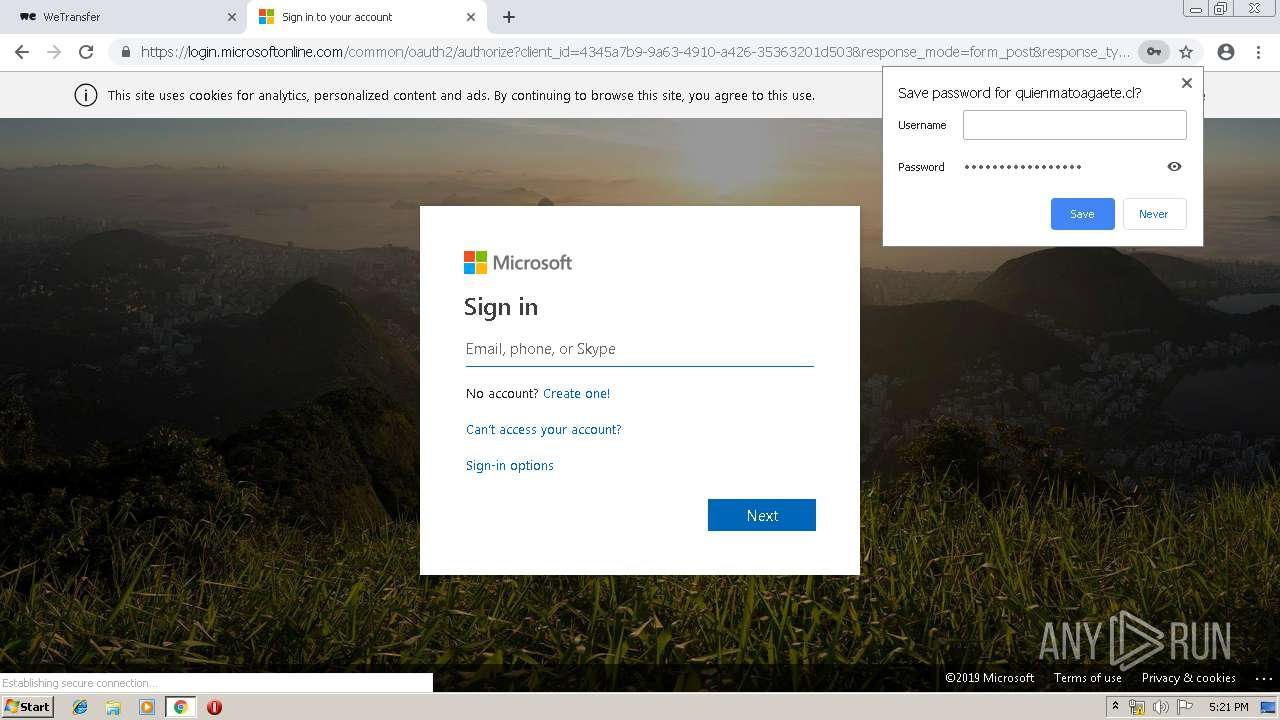
2988 | chrome.exe | GET | 302 | 192.185.117.26:80 | http://quienmatoagaete.cl/tr/onedrive/40eab3d22d08f87917ec64ebdcdeca35/office/index.php | US | — | — | malicious |
2988 | chrome.exe | GET | 301 | 192.185.117.26:80 | http://quienmatoagaete.cl/tr/onedrive/40eab3d22d08f87917ec64ebdcdeca35 | US | html | 347 b | malicious |
2988 | chrome.exe | GET | 200 | 192.185.117.26:80 | http://quienmatoagaete.cl/tr/onedrive/40eab3d22d08f87917ec64ebdcdeca35/office_signin.png | US | image | 5.78 Kb | malicious |
2988 | chrome.exe | GET | 200 | 192.185.117.26:80 | http://quienmatoagaete.cl/tr/onedrive/40eab3d22d08f87917ec64ebdcdeca35/driveback.png | US | image | 297 Kb | malicious |
2988 | chrome.exe | GET | 200 | 173.194.183.201:80 | http://r4---sn-aigl6nl7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=217.147.89.18&mm=28&mn=sn-aigl6nl7&ms=nvh&mt=1560960757&mv=u&pl=22&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2988 | chrome.exe | GET | 200 | 192.185.117.26:80 | http://quienmatoagaete.cl/tr/onedrive/40eab3d22d08f87917ec64ebdcdeca35/email_signin.png | US | image | 7.52 Kb | malicious |
2988 | chrome.exe | GET | 302 | 192.185.117.26:80 | http://quienmatoagaete.cl/tr/onedrive/ | US | html | 314 b | malicious |
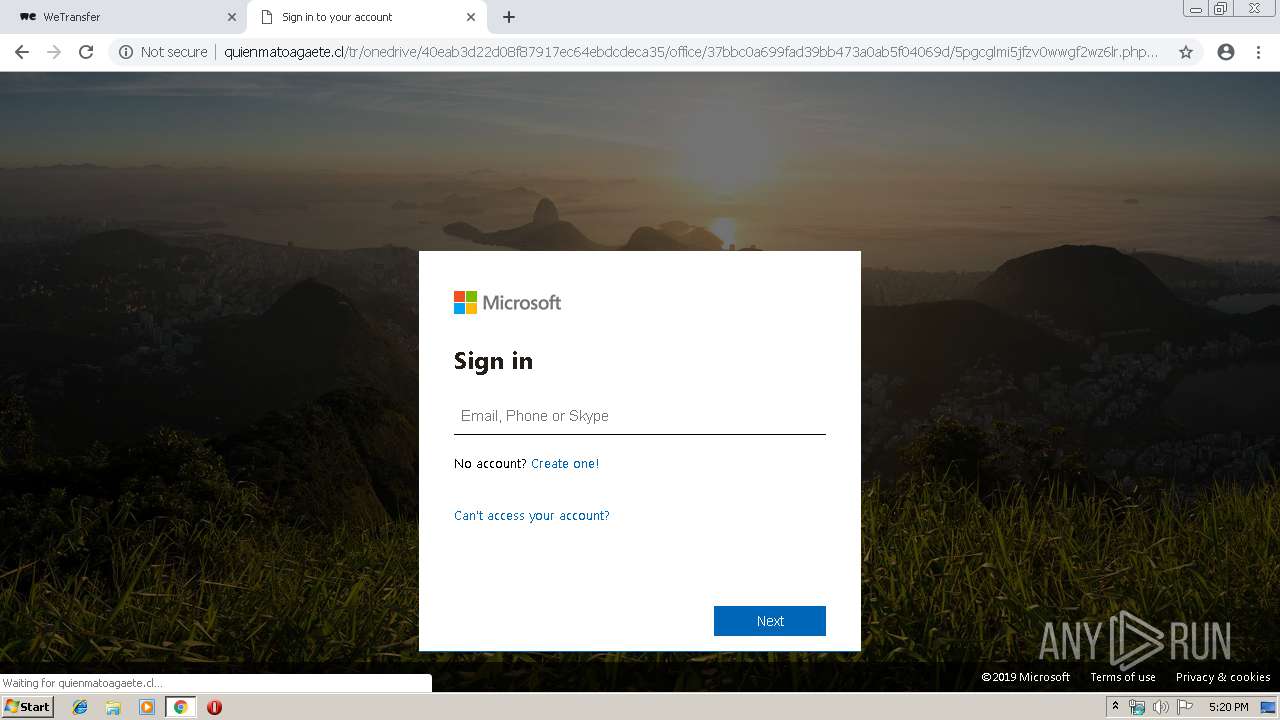
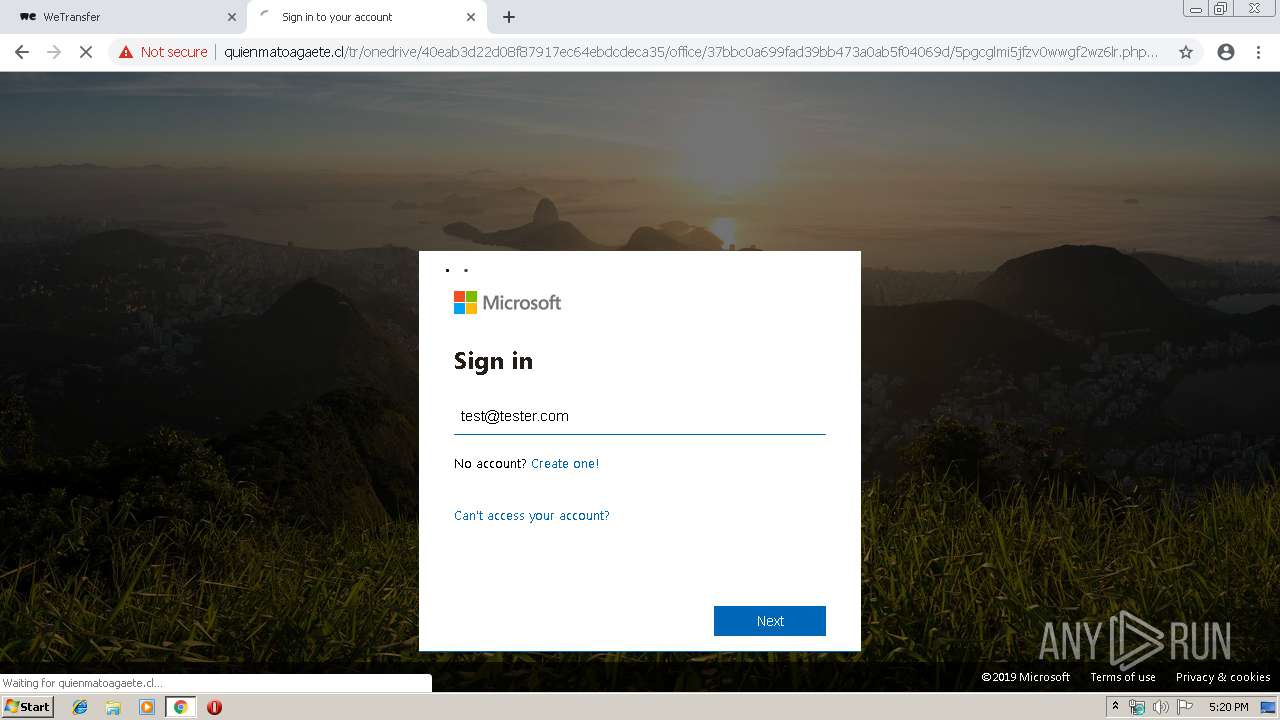
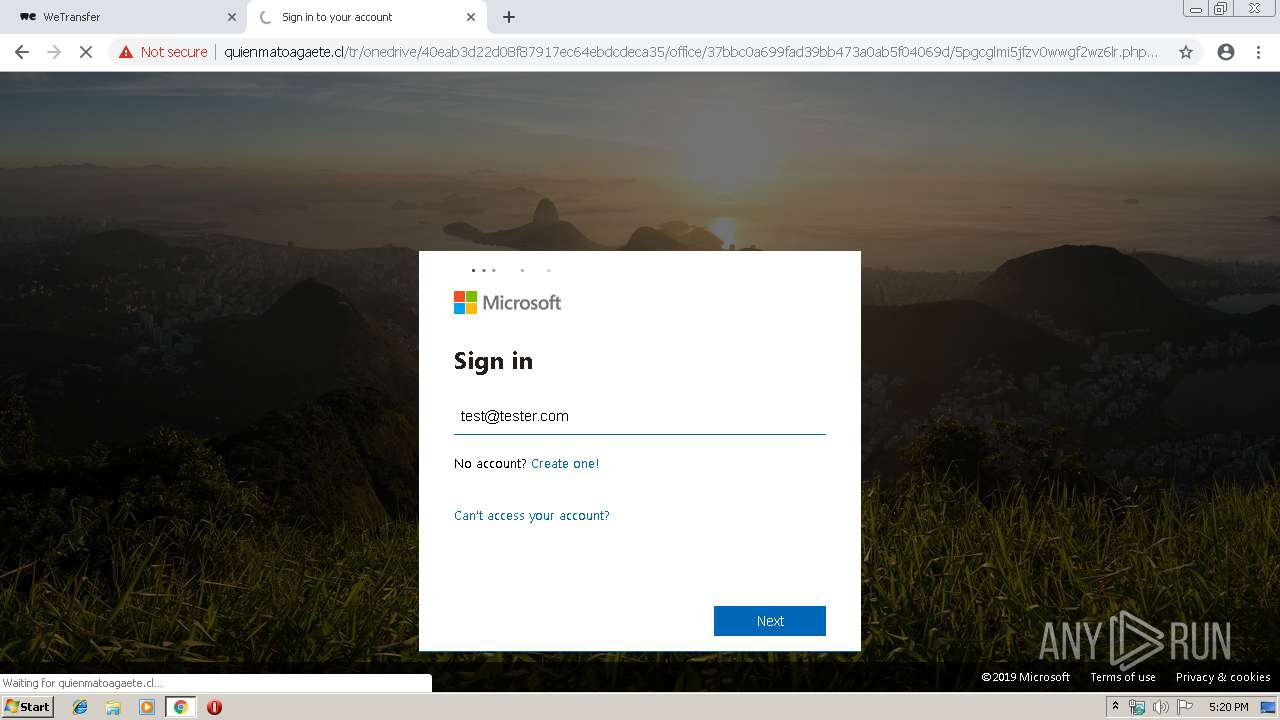
2988 | chrome.exe | GET | 302 | 192.185.117.26:80 | http://quienmatoagaete.cl/tr/onedrive/40eab3d22d08f87917ec64ebdcdeca35/office/37bbc0a699fad39bb473a0ab5f04069d/ | US | html | 387 b | malicious |
2988 | chrome.exe | GET | 301 | 192.185.117.26:80 | http://quienmatoagaete.cl/tr/onedrive/40eab3d22d08f87917ec64ebdcdeca35/office/37bbc0a699fad39bb473a0ab5f04069d | US | html | 387 b | malicious |
2988 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 52.211.136.15:443 | wetransfer.com | Amazon.com, Inc. | IE | unknown |
2988 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
2988 | chrome.exe | 52.222.168.85:80 | x.ss2.us | Amazon.com, Inc. | US | suspicious |
2988 | chrome.exe | 34.240.55.77:443 | wtplus.wetransfer.com | Amazon.com, Inc. | IE | unknown |
2988 | chrome.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2988 | chrome.exe | 52.222.167.233:443 | prod-cdn.wetransfer.net | Amazon.com, Inc. | US | suspicious |
2988 | chrome.exe | 31.13.92.14:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2988 | chrome.exe | 52.218.24.82:443 | wetransferbackgrounds-eu.s3.amazonaws.com | Amazon.com, Inc. | IE | unknown |
2988 | chrome.exe | 151.101.1.140:443 | www.redditstatic.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
wetransfer.com |
| shared |
accounts.google.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
prod-cdn.wetransfer.net |
| whitelisted |
wtplus.wetransfer.com |
| shared |
backgrounds.wetransfer.net |
| whitelisted |
e-10220.adzerk.net |
| whitelisted |
assets.wetransfer.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2988 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Phishing Redirect Feb 09 2016 |
2988 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |
2988 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Phishing Redirect Feb 09 2016 |
2988 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Generic Phish Jan 14 2016 |
6 ETPRO signatures available at the full report