| File name: | cpuz.exe |
| Full analysis: | https://app.any.run/tasks/c2b9ac17-6ebf-423d-ad80-690fc88b3680 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 18:15:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 0E129FCB849E52A5289847376C650B64 |
| SHA1: | 092444DC0B7E01756E1D99FF80123AB611E5E535 |
| SHA256: | F4EEB2E879D497DA9F112ED8AB9D9111D173695A4D1C597B76C8DEAAF4428C25 |
| SSDEEP: | 98304:828gK6u49Mhl+kBucMvGLiT2mZ4gJlVT904xgFx0ZZWbWEvq:28DB904g0Z |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- cpuz.exe (PID: 6356)
Drops a system driver (possible attempt to evade defenses)
- cpuz.exe (PID: 6356)
There is functionality for VM detection VirtualBox (YARA)
- cpuz.exe (PID: 6356)
INFO
Checks supported languages
- cpuz.exe (PID: 6356)
The sample compiled with english language support
- cpuz.exe (PID: 6356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:11:05 17:35:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 1561600 |
| InitializedDataSize: | 2719744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11da7e |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.2.0 |
| ProductVersionNumber: | 2.1.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | CPUID |
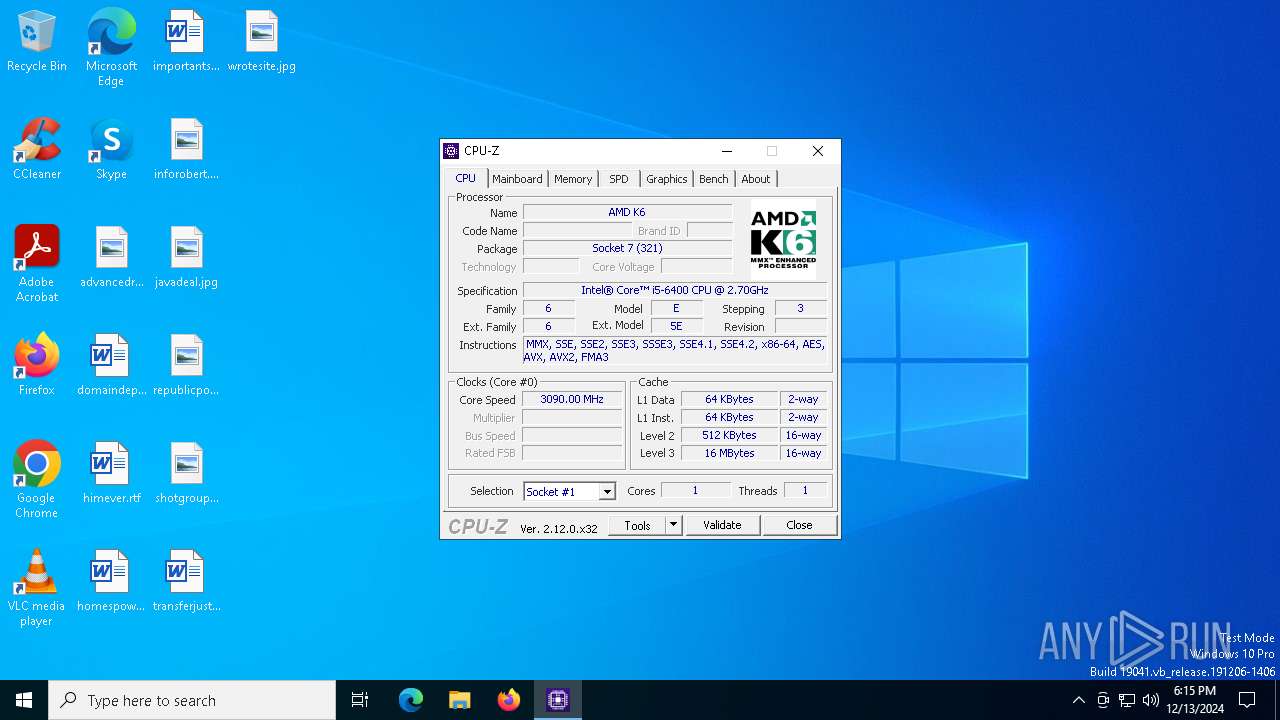
| FileDescription: | CPU-Z Application |
| FileVersion: | 2, 1, 2, 0 |
| InternalName: | cpuz.exe |
| LegalCopyright: | Copyright (C) 2004-2024 |
| OriginalFileName: | cpuz.exe |
| ProductName: | CPU-Z Application |
| ProductVersion: | 2, 1, 2, 0 |
Total processes
127
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Users\admin\AppData\Local\Temp\cpuz.exe" | C:\Users\admin\AppData\Local\Temp\cpuz.exe | — | explorer.exe | |||||||||||
User: admin Company: CPUID Integrity Level: MEDIUM Description: CPU-Z Application Exit code: 3221226540 Version: 2, 1, 2, 0 Modules
| |||||||||||||||
| 6356 | "C:\Users\admin\AppData\Local\Temp\cpuz.exe" | C:\Users\admin\AppData\Local\Temp\cpuz.exe | explorer.exe | ||||||||||||
User: admin Company: CPUID Integrity Level: HIGH Description: CPU-Z Application Exit code: 0 Version: 2, 1, 2, 0 Modules
| |||||||||||||||
Total events
647
Read events
644
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6356) cpuz.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6356) cpuz.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6356) cpuz.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6356 | cpuz.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\cpuid[1].ver | text | |
MD5:03227385FB57A2325464E3259C1D0BD1 | SHA256:1B1D07CB419EDA8BAED1C9309B849025DCBD3696880D93B74F85AEDB75A26855 | |||
| 6356 | cpuz.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3B1450E238DC7F7F2439D6ACCB941B30 | binary | |
MD5:87890DE3832DE03746BB1B351E63DED1 | SHA256:6EFAB48EE7974F714DD2AD4D9DE9A2ABC9F3432694D6102559D15D3D4815A044 | |||
| 6356 | cpuz.exe | C:\Windows\Temp\cpuz159\cpuz159_x64.sys | executable | |
MD5:0BA6064A087746D2F490C06FD913ABD0 | SHA256:11911910A4E8F2C575C47DB7A61BA857C056D13A84498C87AC5FE15AC8C5DD98 | |||
| 6356 | cpuz.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:3DFCA46E00FFA4795C72A41375F159D3 | SHA256:DCBA1A505396539BAC40A7253C9F5DCCF06CBB79957E21D56305E1FC3AF5F40E | |||
| 6356 | cpuz.exe | C:\Windows\Temp\cpuz_driver_6356.log | text | |
MD5:F984605BE6B69FF678CAAE40B1FE0E0A | SHA256:55F8D9530CB14690868D406B3078DE8625E22FF8F225CEFBD237B080B35AAB31 | |||
| 6356 | cpuz.exe | C:\Users\admin\AppData\Local\Temp\cpuz.ini | text | |
MD5:603C418617B5C748AB4BD820F87087E9 | SHA256:CAB84711040DF3A6C540AFB262E3796955DB5013C9E888BCECA1CEB8B54C74C2 | |||
| 6356 | cpuz.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\3B1450E238DC7F7F2439D6ACCB941B30 | der | |
MD5:05D90007B5D32E651E786DA6EC1E8397 | SHA256:7685AEE65E7D07777068D7F54183D6FF15CC89A056F16A9B313A7325B723402B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
36
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6356 | cpuz.exe | GET | 200 | 95.101.54.106:80 | http://r11.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQaUrm0WeTDM5ghfoZtS72KO9ZnzgQUCLkRO6XQhRi06g%2BgrZ%2BGHo78OCcCEgN6UE9zcfGrUQ6lXKQJFs5Dlg%3D%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7000 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6168 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7000 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5864 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.168.100.95:49682 | — | — | — | unknown |
6356 | cpuz.exe | 195.154.81.43:443 | download.cpuid.com | Online S.a.s. | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
download.cpuid.com |
| whitelisted |
r11.o.lencr.org |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |