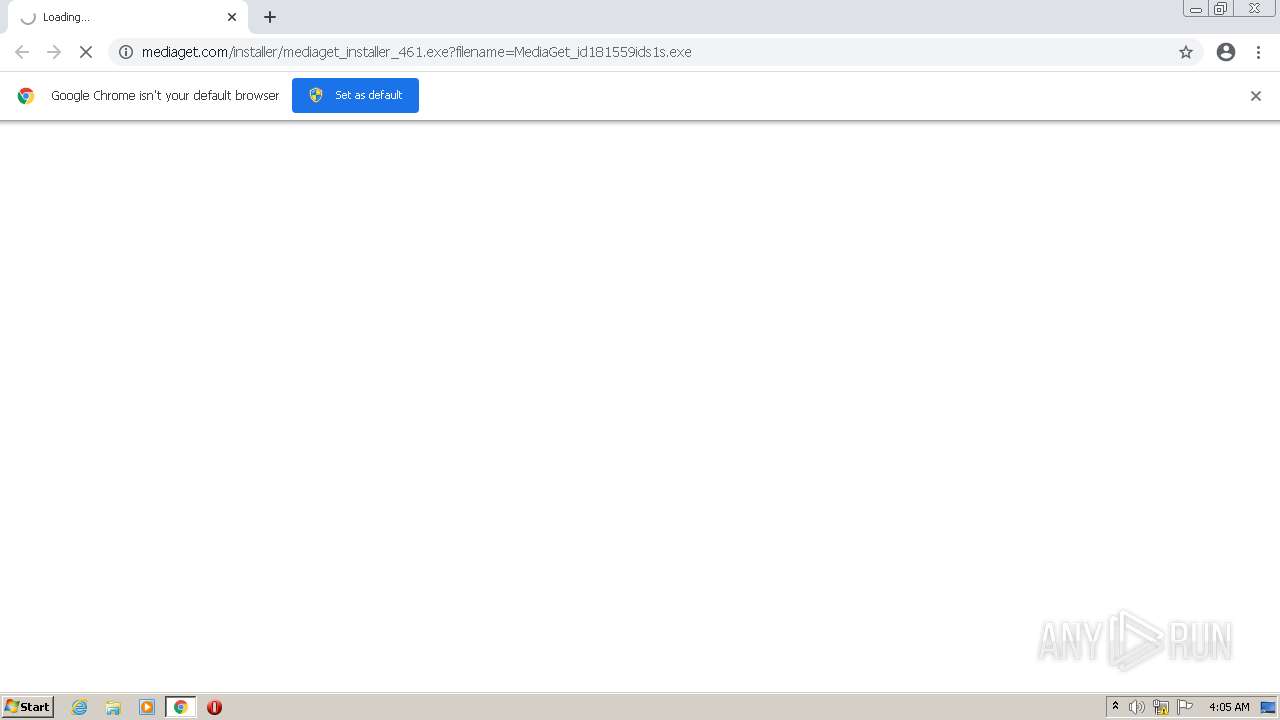
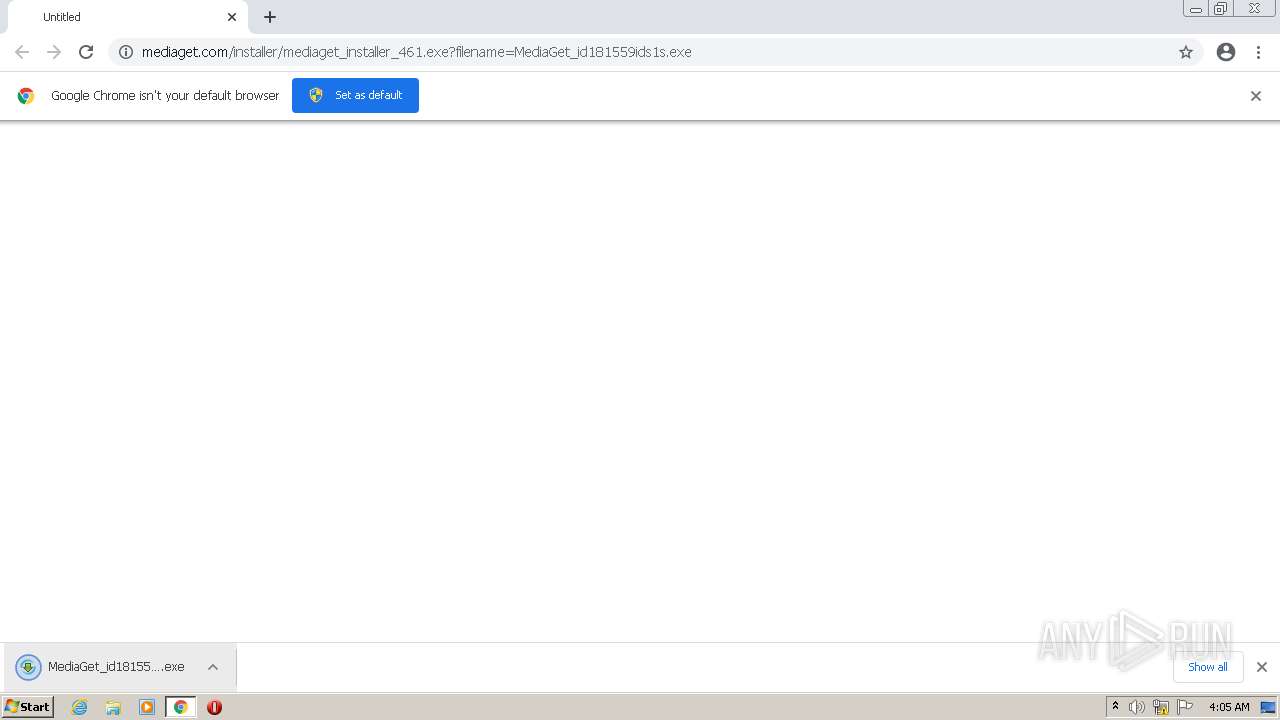
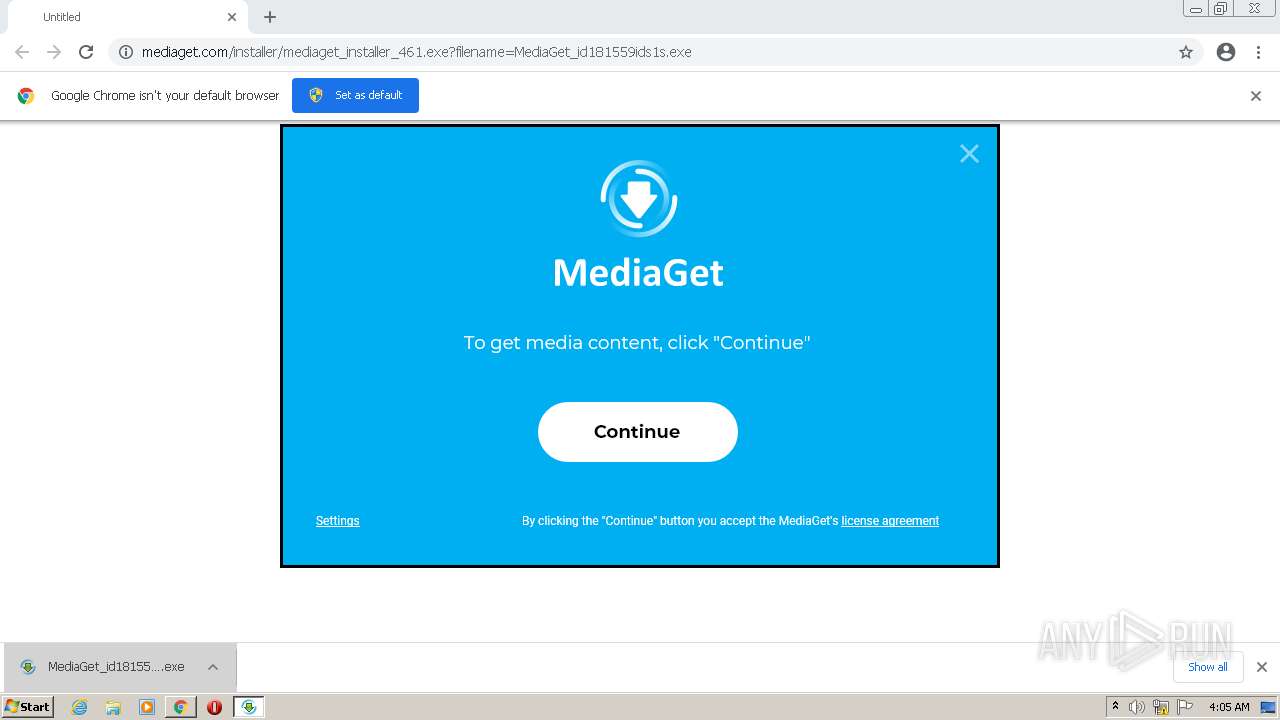
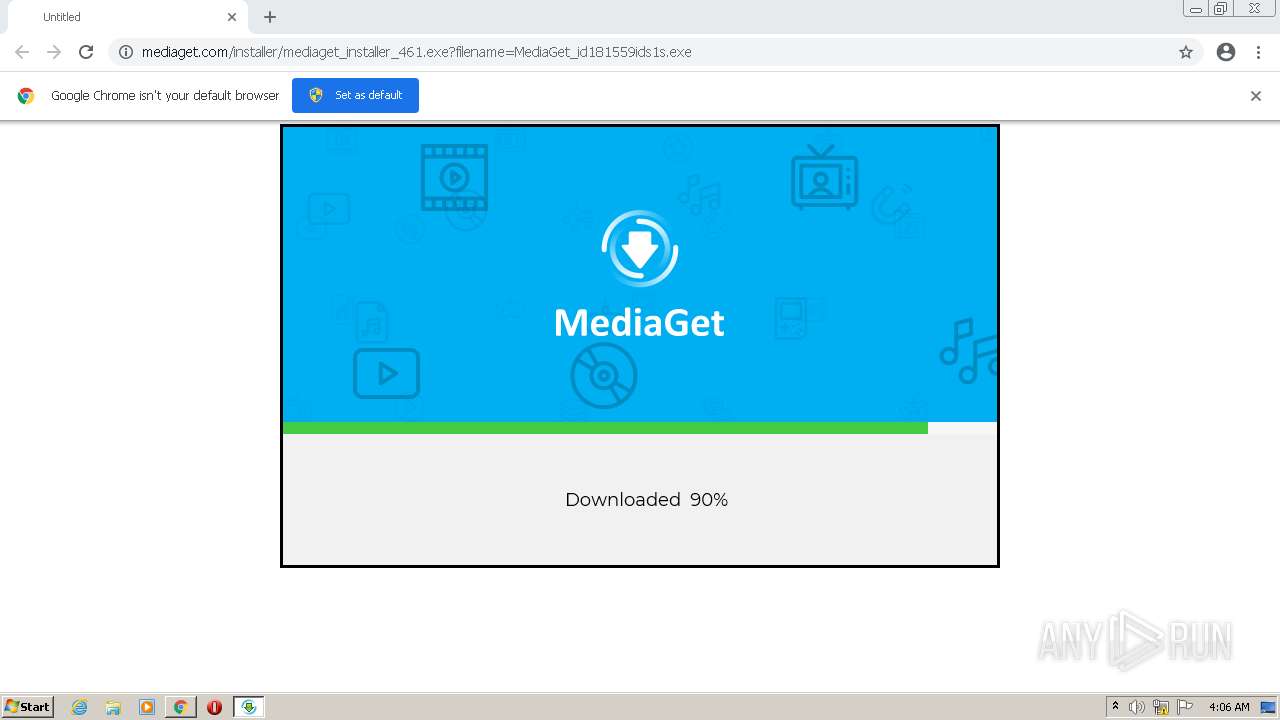
| URL: | https://mediaget.com/installer/mediaget_installer_461.exe?filename=MediaGet_id181559ids1s.exe |
| Full analysis: | https://app.any.run/tasks/8aa10d05-3eb4-451f-9780-819b57887a5d |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2022, 04:05:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4BE53697875E9FF35ED7C6D11C8A8021 |
| SHA1: | F6A666F581E15A366AD0BF3FD94B78260EA3268E |
| SHA256: | F4D59110F22D6848BC2B0F8114E9EC0AED6C31B387F889DC62DF0B3A3A3BFE5A |
| SSDEEP: | 3:N8KryKCgOXKI9DMLWgOXhOiF+jR6MiSBakA:2KrNCgOXT9DkOXhJJxSBakA |
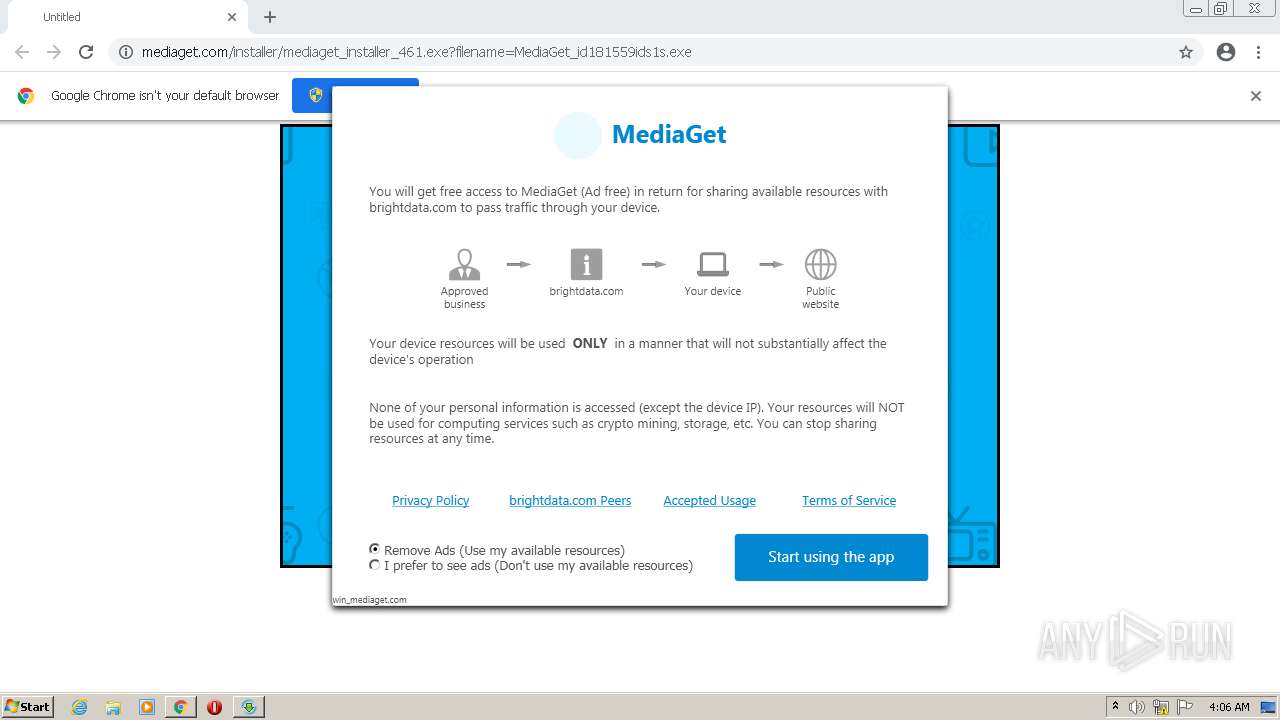
MALICIOUS
Actions looks like stealing of personal data
- MediaGet_id181559ids1s.exe (PID: 3828)
Application was dropped or rewritten from another process
- MediaGet_id181559ids1s.exe (PID: 3828)
- MediaGet_id181559ids1s.exe (PID: 3812)
- lum_inst.exe (PID: 2364)
- net_updater32.exe (PID: 3352)
- test_wpf.exe (PID: 2716)
- net_updater32.exe (PID: 884)
- mediaget.exe (PID: 3588)
- mediaget_crashpad_handler.exe (PID: 3452)
- net_updater32.exe (PID: 2868)
- QtWebEngineProcess.exe (PID: 3332)
- QtWebEngineProcess.exe (PID: 4080)
- luminati-m-controller.exe (PID: 3160)
- QtWebEngineProcess.exe (PID: 3352)
- test_wpf.exe (PID: 2672)
- test_wpf.exe (PID: 3944)
- QtWebEngineProcess.exe (PID: 2484)
- idle_report.exe (PID: 2176)
- net_svc.exe (PID: 3844)
- net_svc.exe (PID: 1864)
- net_svc.exe (PID: 3244)
- idle_report.exe (PID: 3772)
- idle_report.exe (PID: 3184)
- net_svc.exe (PID: 3660)
- net_svc.exe (PID: 3568)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3832)
- net_updater32.exe (PID: 3352)
- mediaget.exe (PID: 3588)
- mediaget_crashpad_handler.exe (PID: 3452)
- QtWebEngineProcess.exe (PID: 3332)
- QtWebEngineProcess.exe (PID: 3352)
- QtWebEngineProcess.exe (PID: 4080)
- luminati-m-controller.exe (PID: 3160)
- net_updater32.exe (PID: 2868)
- QtWebEngineProcess.exe (PID: 2484)
Drops executable file immediately after starts
- lum_inst.exe (PID: 2364)
- lum_inst.tmp (PID: 3228)
- luminati-m-controller.exe (PID: 3160)
Changes settings of System certificates
- net_updater32.exe (PID: 3352)
- QtWebEngineProcess.exe (PID: 3332)
Changes the autorun value in the registry
- mediaget.exe (PID: 3588)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3776)
- lum_inst.exe (PID: 2364)
- lum_inst.tmp (PID: 3228)
- net_updater32.exe (PID: 3352)
- MediaGet_id181559ids1s.exe (PID: 3828)
- luminati-m-controller.exe (PID: 3160)
- net_updater32.exe (PID: 2868)
- mediaget.exe (PID: 3588)
Reads internet explorer settings
- MediaGet_id181559ids1s.exe (PID: 3828)
Reads the computer name
- MediaGet_id181559ids1s.exe (PID: 3828)
- lum_inst.tmp (PID: 3228)
- net_updater32.exe (PID: 3352)
- test_wpf.exe (PID: 2716)
- net_updater32.exe (PID: 884)
- mediaget.exe (PID: 3588)
- net_updater32.exe (PID: 2868)
- QtWebEngineProcess.exe (PID: 3332)
- test_wpf.exe (PID: 2672)
- luminati-m-controller.exe (PID: 3160)
- test_wpf.exe (PID: 3944)
- idle_report.exe (PID: 2176)
- idle_report.exe (PID: 3772)
- net_svc.exe (PID: 3844)
- idle_report.exe (PID: 3184)
Reads Microsoft Outlook installation path
- MediaGet_id181559ids1s.exe (PID: 3828)
Checks supported languages
- MediaGet_id181559ids1s.exe (PID: 3828)
- lum_inst.exe (PID: 2364)
- lum_inst.tmp (PID: 3228)
- net_updater32.exe (PID: 3352)
- test_wpf.exe (PID: 2716)
- net_updater32.exe (PID: 884)
- mediaget.exe (PID: 3588)
- net_updater32.exe (PID: 2868)
- mediaget_crashpad_handler.exe (PID: 3452)
- QtWebEngineProcess.exe (PID: 3332)
- QtWebEngineProcess.exe (PID: 3352)
- QtWebEngineProcess.exe (PID: 4080)
- luminati-m-controller.exe (PID: 3160)
- test_wpf.exe (PID: 2672)
- test_wpf.exe (PID: 3944)
- idle_report.exe (PID: 2176)
- QtWebEngineProcess.exe (PID: 2484)
- net_svc.exe (PID: 3244)
- net_svc.exe (PID: 3844)
- net_svc.exe (PID: 1864)
- idle_report.exe (PID: 3772)
- net_svc.exe (PID: 3568)
- idle_report.exe (PID: 3184)
- net_svc.exe (PID: 3660)
Creates a software uninstall entry
- MediaGet_id181559ids1s.exe (PID: 3828)
Reads Windows owner or organization settings
- lum_inst.tmp (PID: 3228)
Drops a file with too old compile date
- MediaGet_id181559ids1s.exe (PID: 3828)
- mediaget.exe (PID: 3588)
Creates files in the user directory
- MediaGet_id181559ids1s.exe (PID: 3828)
Reads the Windows organization settings
- lum_inst.tmp (PID: 3228)
Drops a file that was compiled in debug mode
- lum_inst.tmp (PID: 3228)
- net_updater32.exe (PID: 3352)
- MediaGet_id181559ids1s.exe (PID: 3828)
- luminati-m-controller.exe (PID: 3160)
- net_updater32.exe (PID: 2868)
- mediaget.exe (PID: 3588)
Adds / modifies Windows certificates
- net_updater32.exe (PID: 3352)
- QtWebEngineProcess.exe (PID: 3332)
Reads Environment values
- net_updater32.exe (PID: 3352)
- mediaget.exe (PID: 3588)
- luminati-m-controller.exe (PID: 3160)
- net_updater32.exe (PID: 2868)
Creates files in the program directory
- net_updater32.exe (PID: 3352)
Application launched itself
- net_updater32.exe (PID: 3352)
- net_svc.exe (PID: 3844)
Changes default file association
- MediaGet_id181559ids1s.exe (PID: 3828)
- mediaget.exe (PID: 3588)
Executed as Windows Service
- net_updater32.exe (PID: 2868)
Creates files in the Windows directory
- net_updater32.exe (PID: 2868)
Removes files from Windows directory
- net_updater32.exe (PID: 2868)
Drops a file with a compile date too recent
- mediaget.exe (PID: 3588)
INFO
Checks supported languages
- chrome.exe (PID: 3776)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 3152)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 344)
- chrome.exe (PID: 2580)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 2620)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 2236)
- WISPTIS.EXE (PID: 3420)
- chrome.exe (PID: 448)
Reads the computer name
- chrome.exe (PID: 3944)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 2580)
- chrome.exe (PID: 1264)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2620)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 2512)
- WISPTIS.EXE (PID: 3420)
Reads the hosts file
- chrome.exe (PID: 1264)
- chrome.exe (PID: 3776)
- mediaget.exe (PID: 3588)
- QtWebEngineProcess.exe (PID: 3332)
Application launched itself
- chrome.exe (PID: 3776)
Reads settings of System Certificates
- chrome.exe (PID: 1264)
- chrome.exe (PID: 3776)
- net_updater32.exe (PID: 3352)
- net_updater32.exe (PID: 884)
- net_updater32.exe (PID: 2868)
- mediaget.exe (PID: 3588)
- QtWebEngineProcess.exe (PID: 3332)
Checks Windows Trust Settings
- chrome.exe (PID: 3776)
- net_updater32.exe (PID: 3352)
- net_updater32.exe (PID: 2868)
Dropped object may contain Bitcoin addresses
- MediaGet_id181559ids1s.exe (PID: 3828)
- mediaget.exe (PID: 3588)
Reads the date of Windows installation
- chrome.exe (PID: 2400)
Application was dropped or rewritten from another process
- lum_inst.tmp (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
47
Malicious processes
14
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=976 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 884 | "C:\Users\admin\MediaGet2\Luminati-m\net_updater32.exe" --install win_mediaget.com --no-cleanup | C:\Users\admin\MediaGet2\Luminati-m\net_updater32.exe | net_updater32.exe | ||||||||||||
User: admin Company: Luminati Networks Ltd. Integrity Level: HIGH Description: Luminati SDK Updater Exit code: 0 Version: 1.240.55 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1044,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1232 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\MediaGet2\Luminati-m\luminati\net_svc.exe" --report-idle | C:\Users\admin\MediaGet2\Luminati-m\luminati\net_svc.exe | — | net_svc.exe | |||||||||||
User: admin Company: Luminati Networks Ltd. Integrity Level: MEDIUM Description: Luminati SDK Engine Exit code: 0 Version: 1.245.997 Modules
| |||||||||||||||
| 2176 | C:\Users\admin\MediaGet2\Luminati-m\luminati\idle_report.exe 63642 | C:\Users\admin\MediaGet2\Luminati-m\luminati\idle_report.exe | — | net_updater32.exe | |||||||||||
User: admin Company: Luminati Networks Ltd. Integrity Level: MEDIUM Description: idle_report Exit code: 0 Version: 1.240.55 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3160 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\AppData\Local\Temp\luminati\lum_inst.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\luminati\lum_inst.exe | MediaGet_id181559ids1s.exe | ||||||||||||
User: admin Company: luminati Integrity Level: HIGH Description: luminati Setup Exit code: 101 Version: Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1484 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2484 | "C:\Users\admin\MediaGet2\QtWebEngineProcess.exe" --type=renderer --disable-speech-api --enable-threaded-compositing --enable-features=AllowContentInitiatedDataUrlNavigations,TracingServiceInProcess --disable-features=BackgroundFetch,ConsolidatedMovementXY,DnsOverHttpsUpgrade,FormControlsRefresh,MojoVideoCapture,PictureInPicture,SmsReceiver,UseSkiaRenderer,WebPayments,WebUSB --disable-gpu-compositing --lang=en-US --webengine-schemes=qrc:sLV --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3180 /prefetch:1 | C:\Users\admin\MediaGet2\QtWebEngineProcess.exe | — | mediaget.exe | |||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: LOW Description: C++ Application Development Framework Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
Total events
61 316
Read events
60 411
Write events
832
Delete events
73
Modification events
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3776) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
502
Suspicious files
152
Text files
446
Unknown types
103
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-621460F0-EC0.pma | — | |
MD5:— | SHA256:— | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f6569a6e-4a28-42b3-a4ef-54a44ce7ff58.tmp | text | |
MD5:— | SHA256:— | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12c953.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF12c972.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3776 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
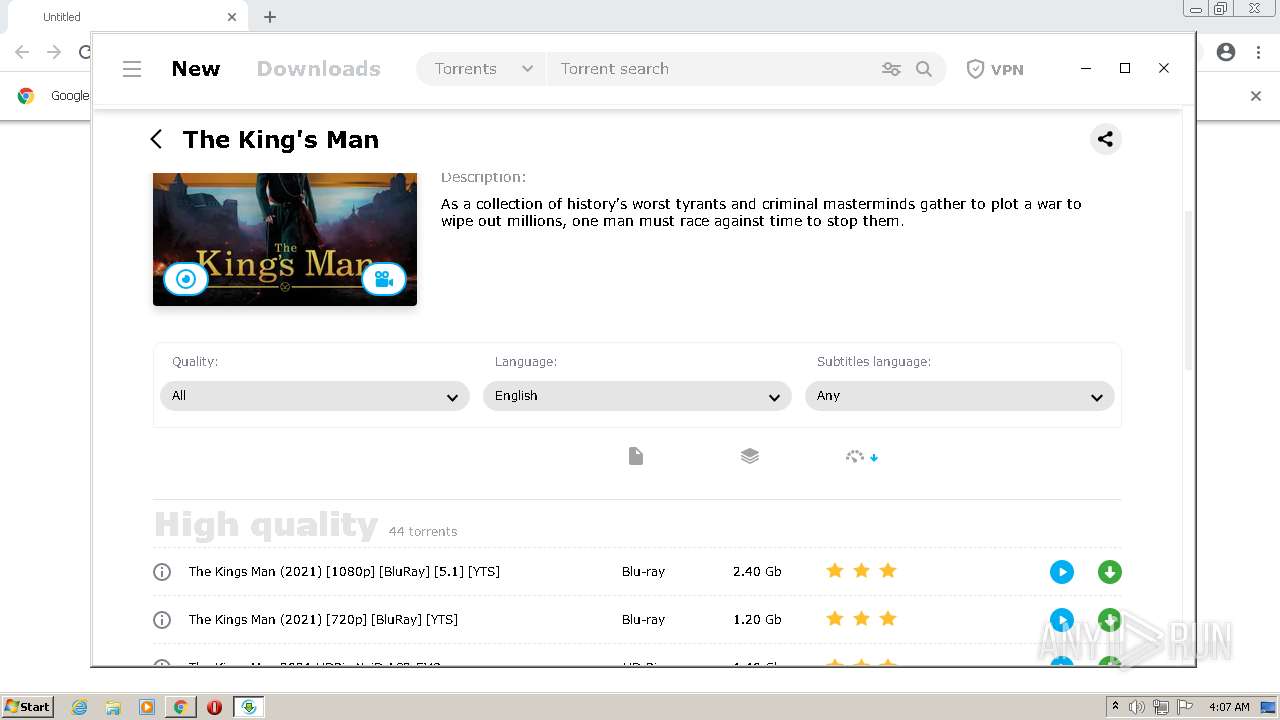
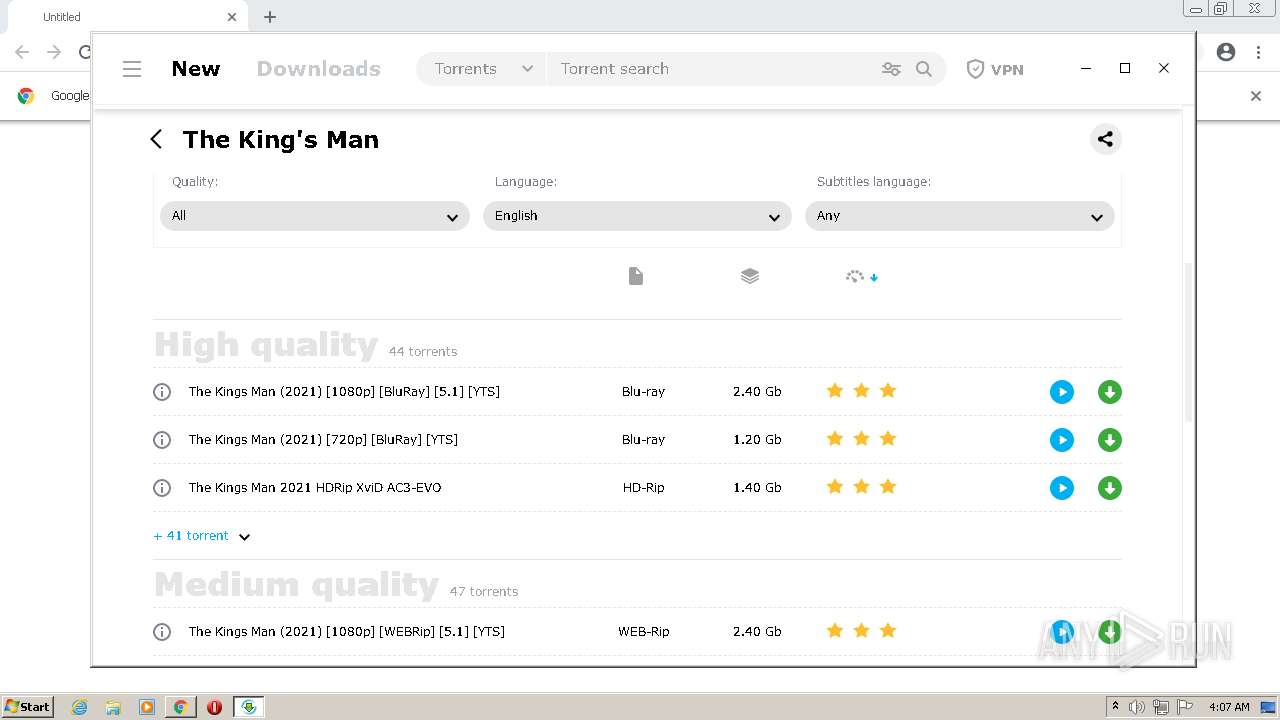
HTTP(S) requests
45
TCP/UDP connections
131
DNS requests
73
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGMyQUFYUjhaZkNqaEUyZDFCRWM2S3dUZw/1.0.0.11_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
872 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOGMyQUFYUjhaZkNqaEUyZDFCRWM2S3dUZw/1.0.0.11_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | crx | 2.80 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.70 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 718 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 178 Kb | whitelisted |
— | — | GET | 200 | 61.216.109.95:6969 | http://tracker.dler.org:6969/announce?info_hash=X%8e%97hT!%c9%27%92_%ee-X%82%c7%99%90%9e%07%0d&peer_id=MG-3.01.4157_Q4Lh-MH&port=10522&uploaded=0&downloaded=0&left=21563415&corrupt=0&key=FD4F1070&event=started&numwant=200&compact=1&no_peer_id=1&supportcrypto=1&redundant=0 | TW | binary | 1.27 Kb | suspicious |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 7.36 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 20.9 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 413 Kb | whitelisted |
1264 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?8c3dd89e03910b17 | US | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
872 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
1264 | chrome.exe | 142.250.185.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1264 | chrome.exe | 142.250.185.163:443 | — | Google Inc. | US | whitelisted |
— | — | 51.15.85.51:443 | mediaget.com | Online S.a.s. | FR | unknown |
3828 | MediaGet_id181559ids1s.exe | 51.15.85.51:443 | mediaget.com | Online S.a.s. | FR | unknown |
3828 | MediaGet_id181559ids1s.exe | 51.15.98.239:443 | mediaget.com | Online S.a.s. | FR | suspicious |
3352 | net_updater32.exe | 162.125.66.15:443 | uc395e9f1e920d95fe18e03abfdf.dl.dropboxusercontent.com | Dropbox, Inc. | DE | malicious |
3352 | net_updater32.exe | 162.125.66.18:443 | www.dropbox.com | Dropbox, Inc. | DE | suspicious |
3352 | net_updater32.exe | 192.81.214.145:443 | perr.l-err.biz | Digital Ocean, Inc. | US | suspicious |
3352 | net_updater32.exe | 167.172.28.221:443 | perr.l-err.biz | — | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
mediaget.com |
| suspicious |
accounts.google.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
www.dropbox.com |
| shared |
uc395e9f1e920d95fe18e03abfdf.dl.dropboxusercontent.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3352 | net_updater32.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
— | — | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent Announce |
— | — | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent Announce |
— | — | Potential Corporate Privacy Violation | GPL P2P BitTorrent announce request |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent Announce |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
mediaget.exe | AUTOSELECT OGL
|
mediaget.exe | > __thiscall Application::Application(int &,char *[])
|
mediaget.exe | os version: "6.1.7601v" __ os name: "Windows 7 Version 6.1 (Build 7601: SP 1)"
|
mediaget.exe | > int __thiscall Application::exec(void)
|
mediaget.exe | > __thiscall MediagetServerSettings::MediagetServerSettings(void)
|
mediaget.exe | INSTALL ID: "" _ OLD ID: ""
|
mediaget.exe | reseller - "" installId ""
|
mediaget.exe | > void __thiscall MediagetServerSettings::flushSettings(void)
|
mediaget.exe | main libvlc debug: VLC media player - 3.0.16 Vetinari
|
mediaget.exe | main libvlc debug: Copyright � 1996-2021 the VideoLAN team
|