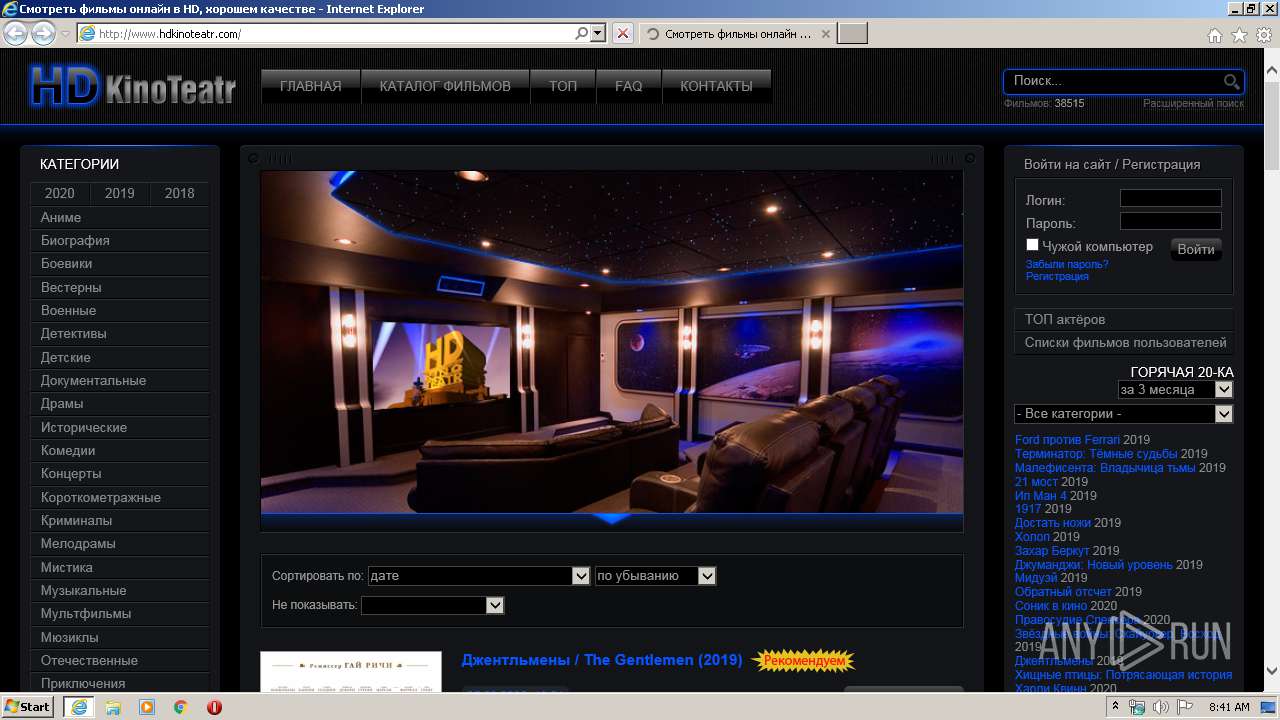
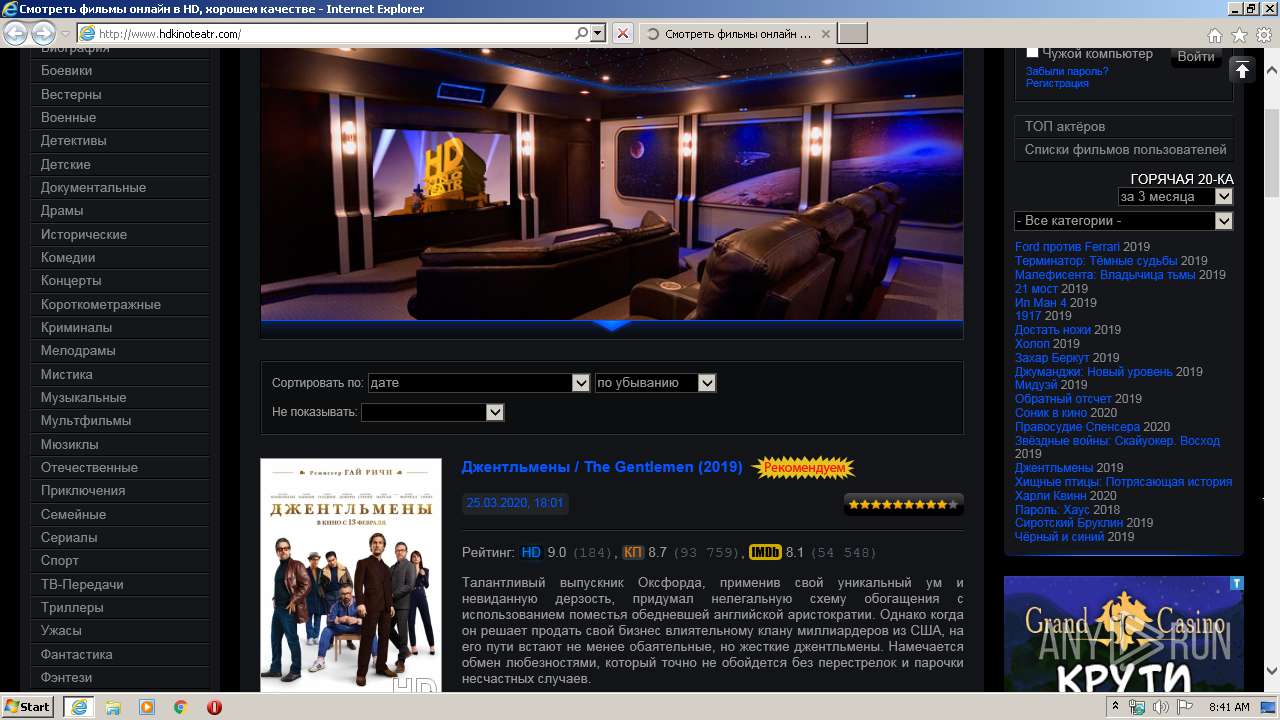
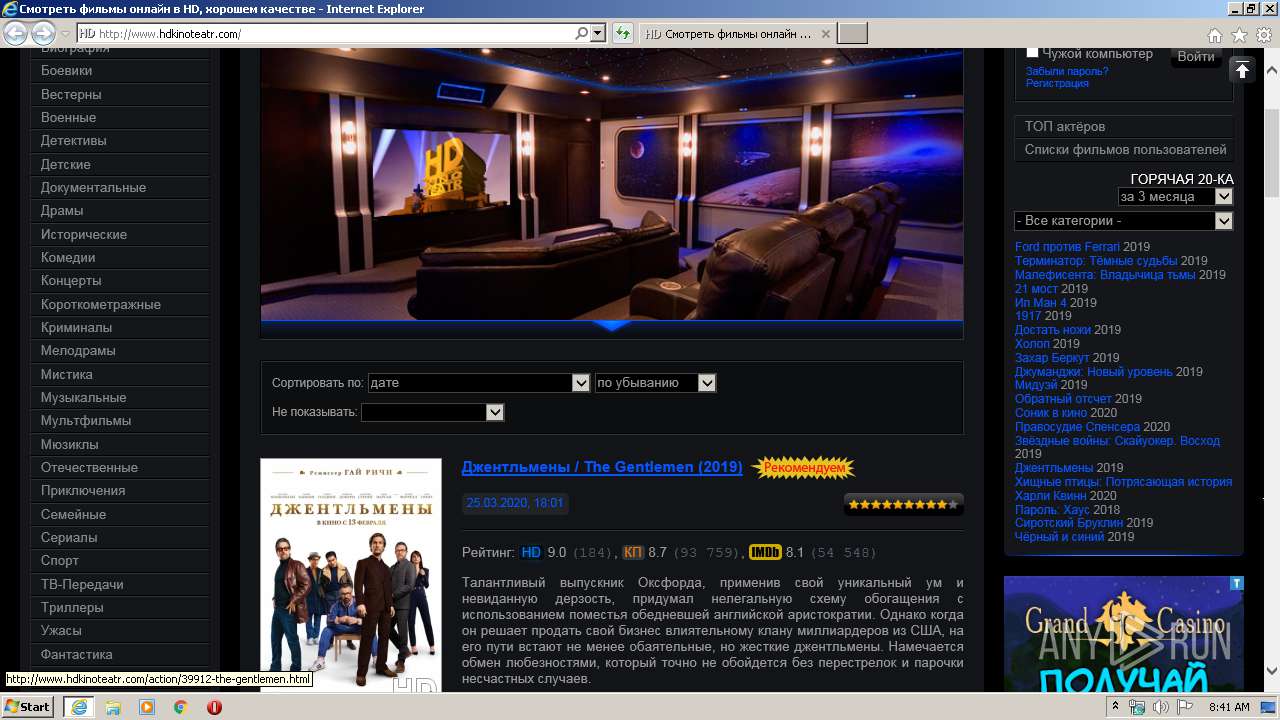
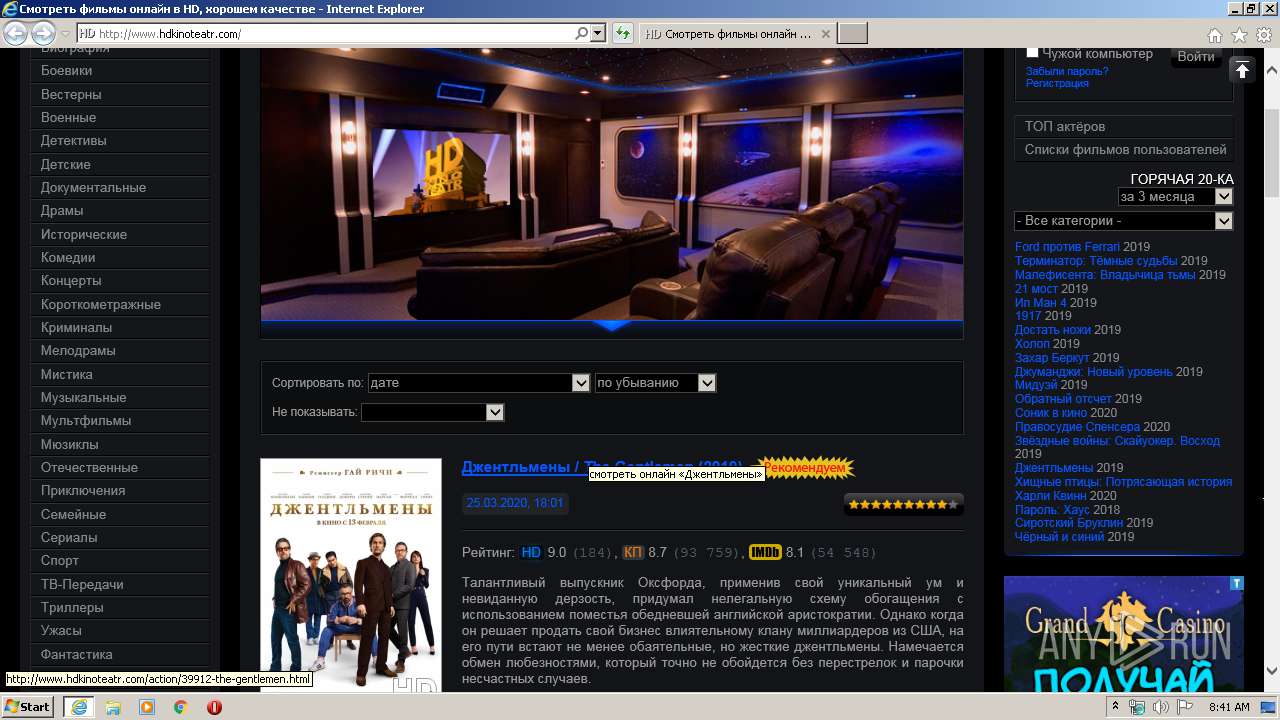
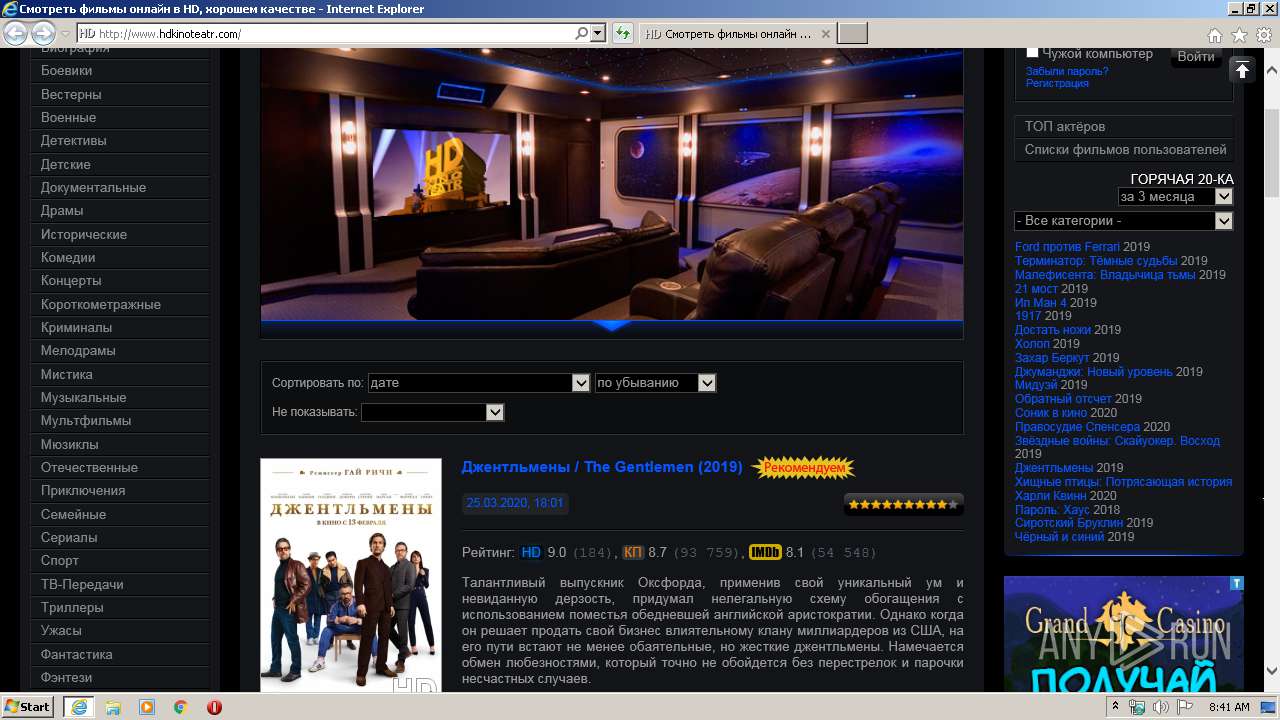
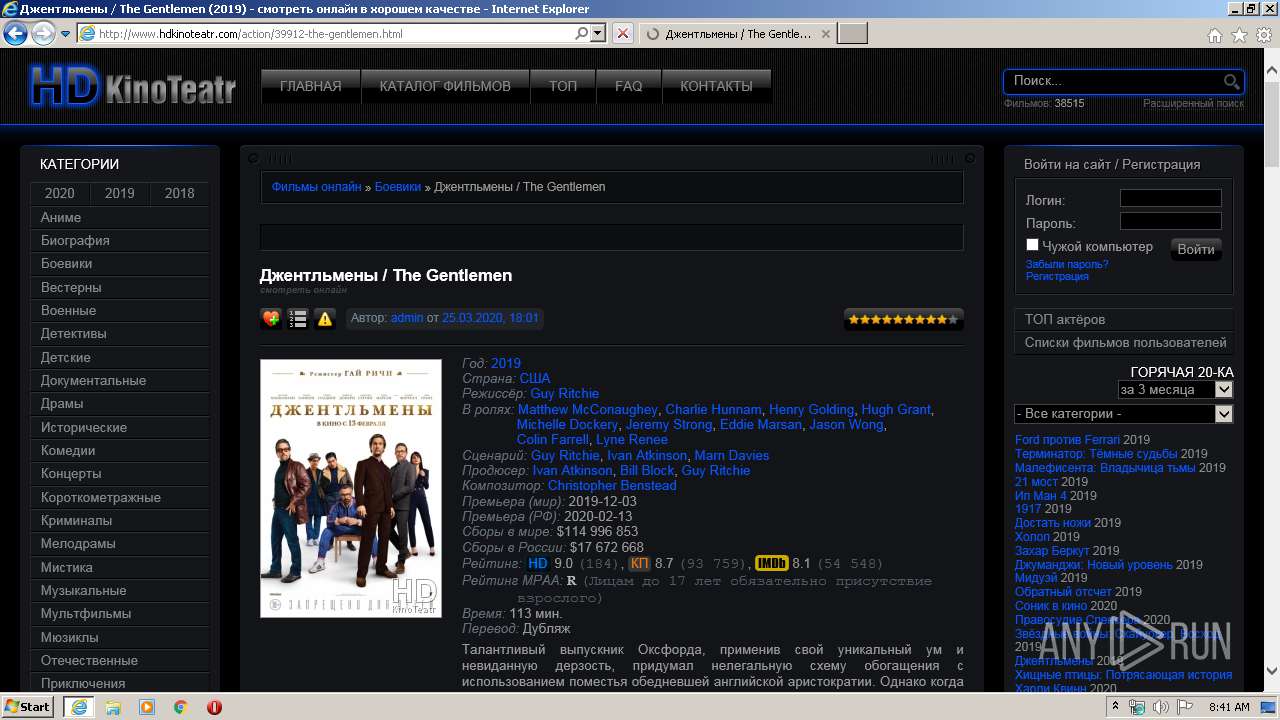
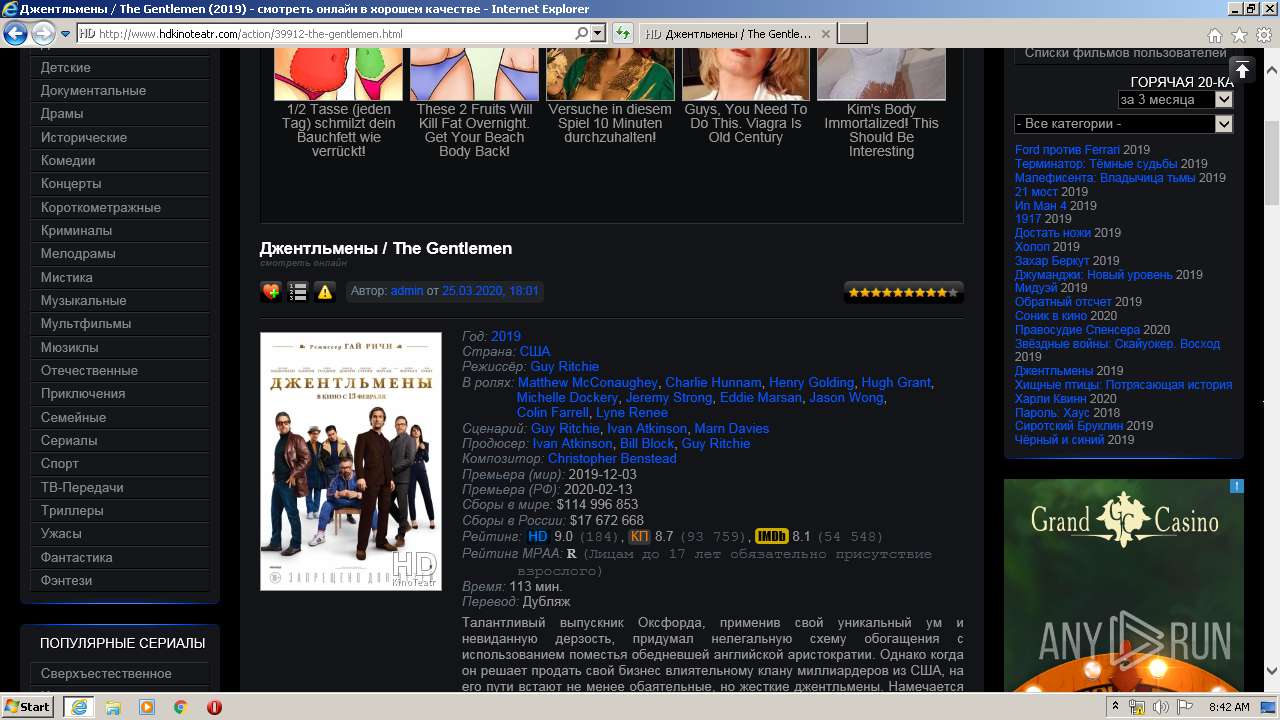
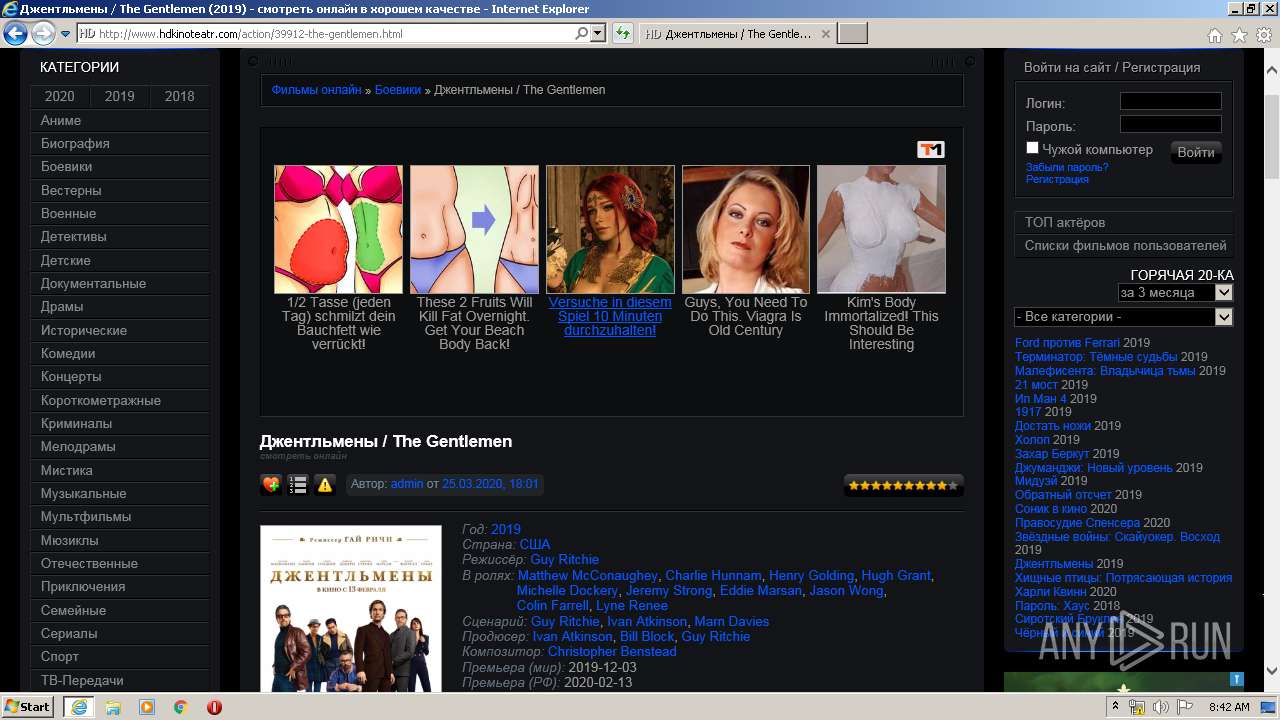
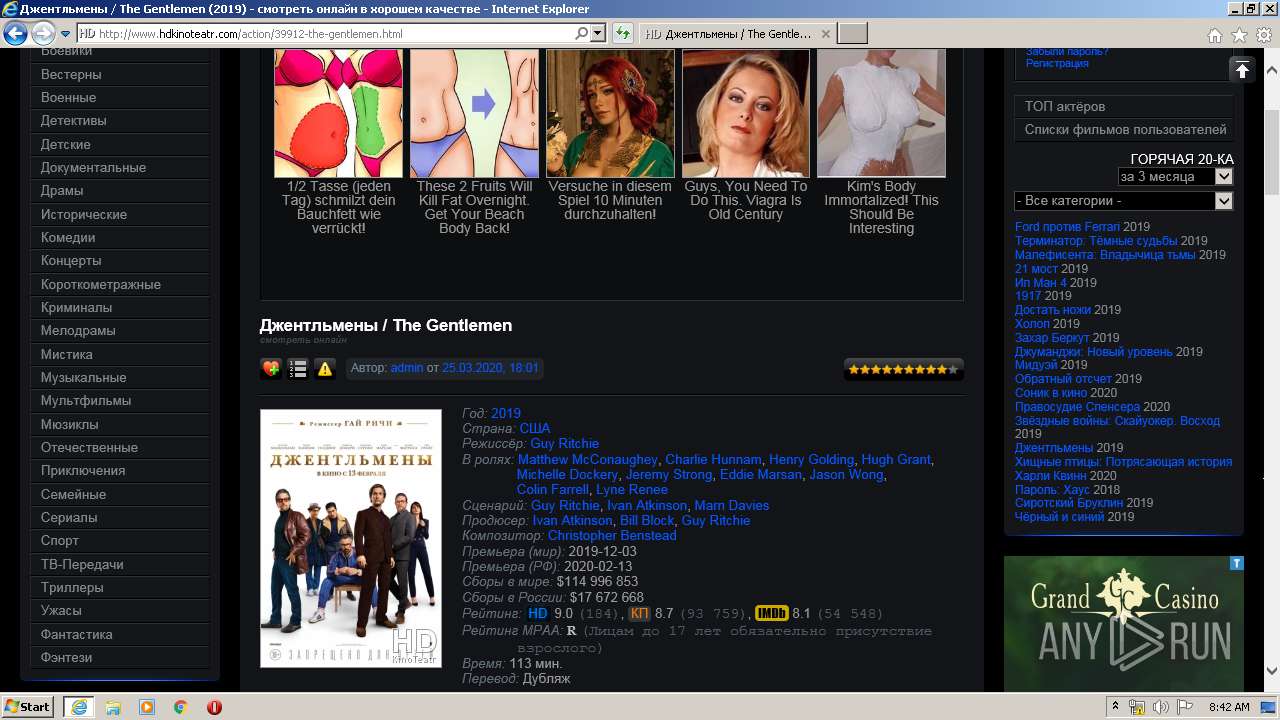
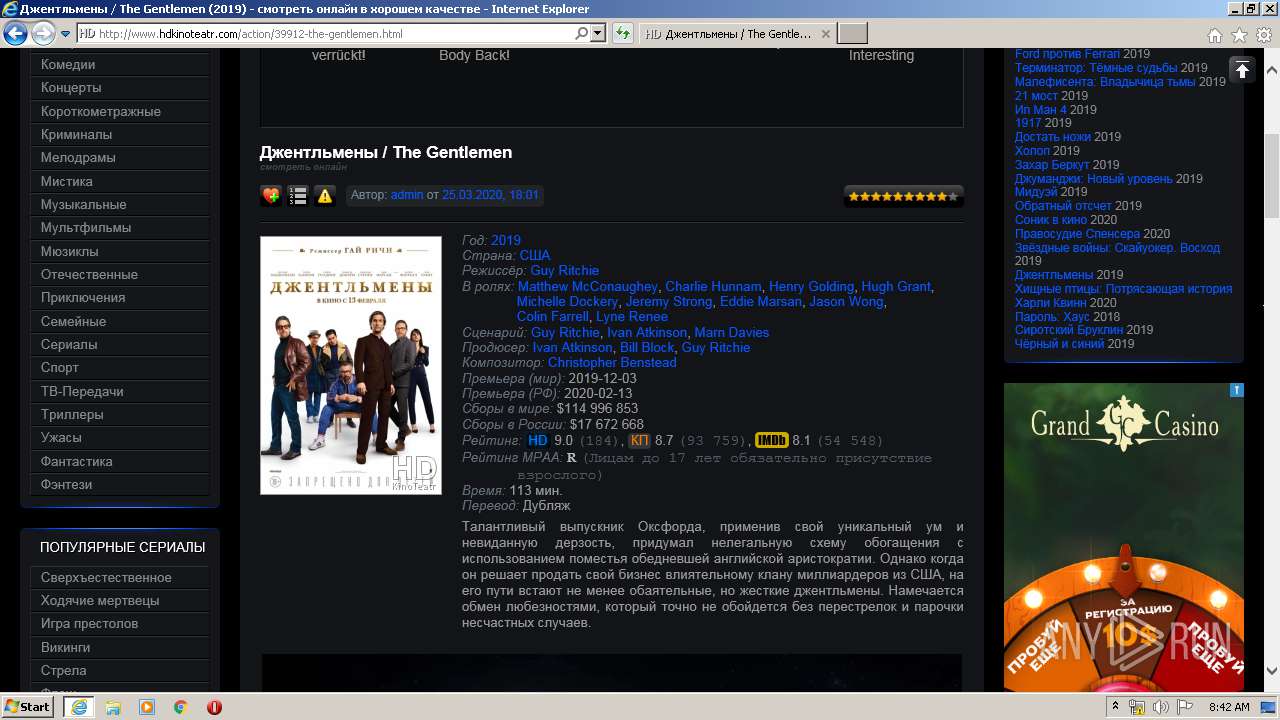
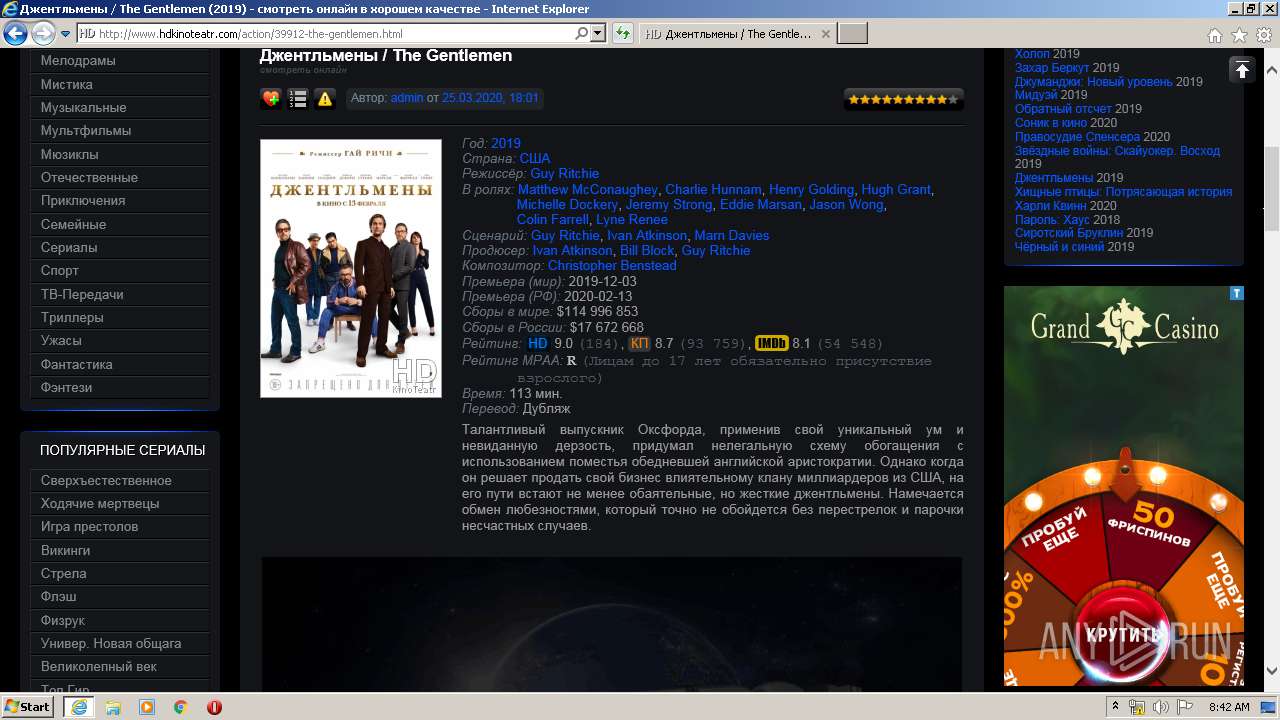
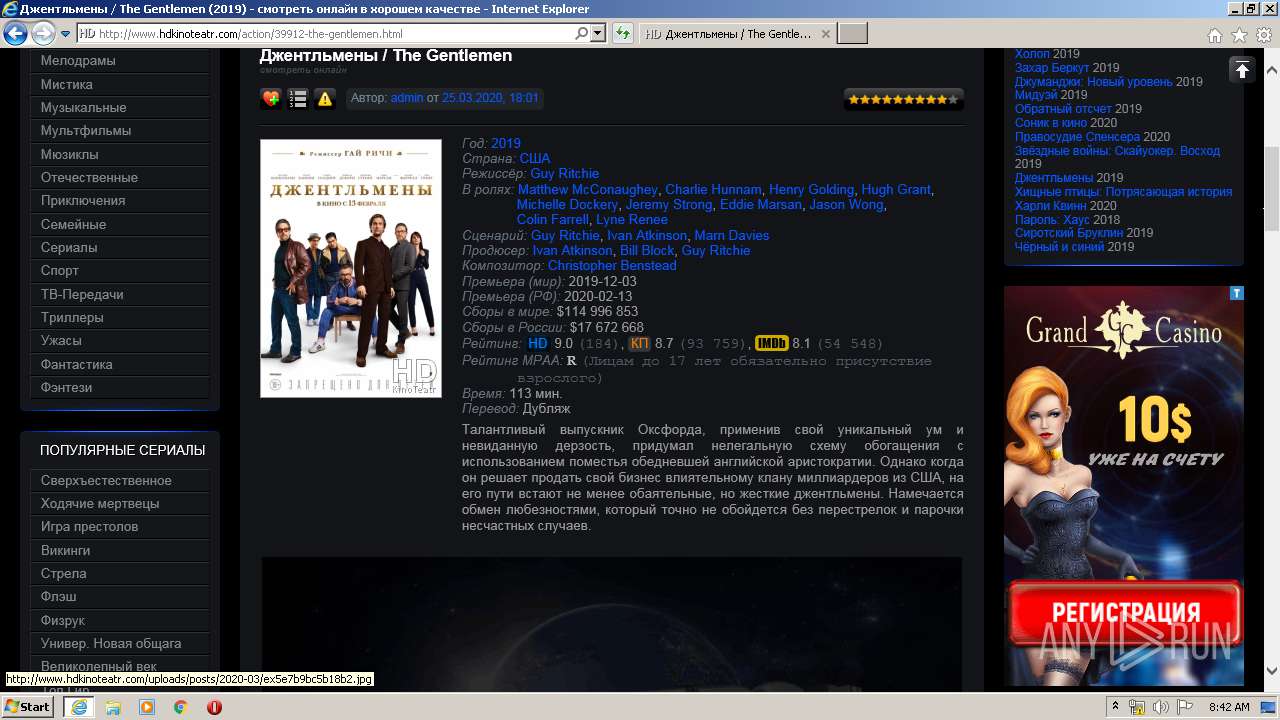
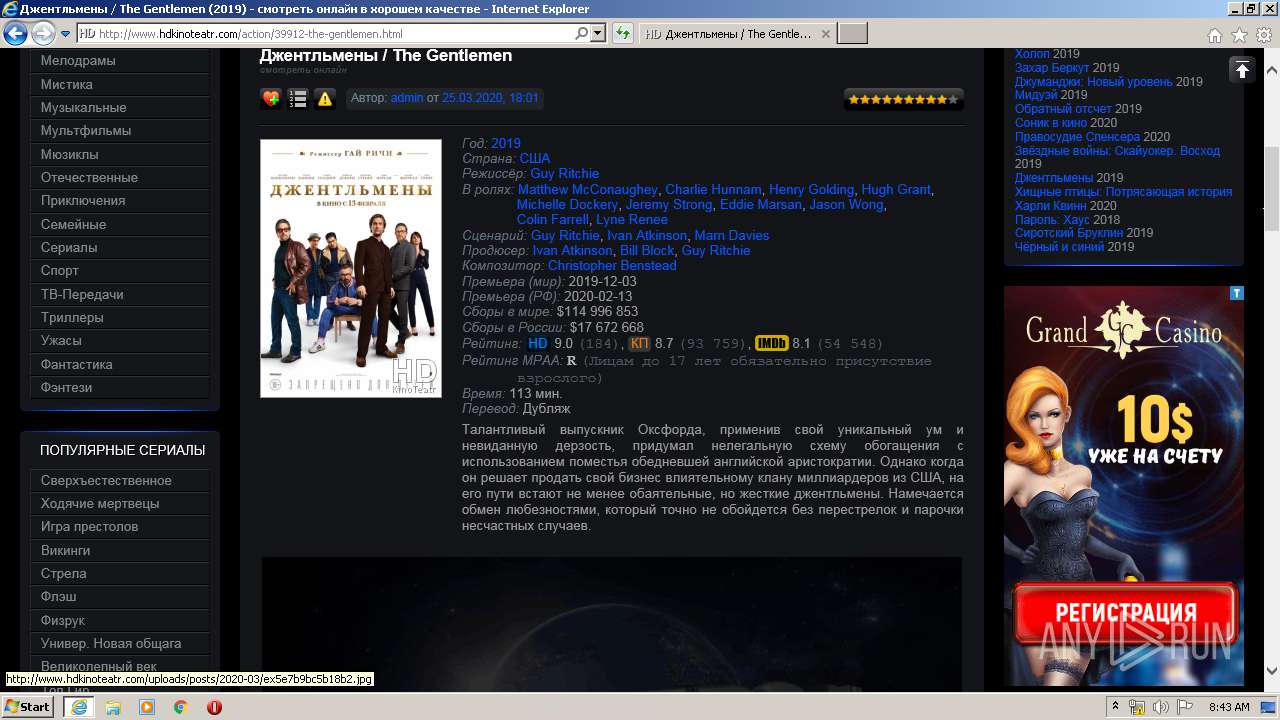
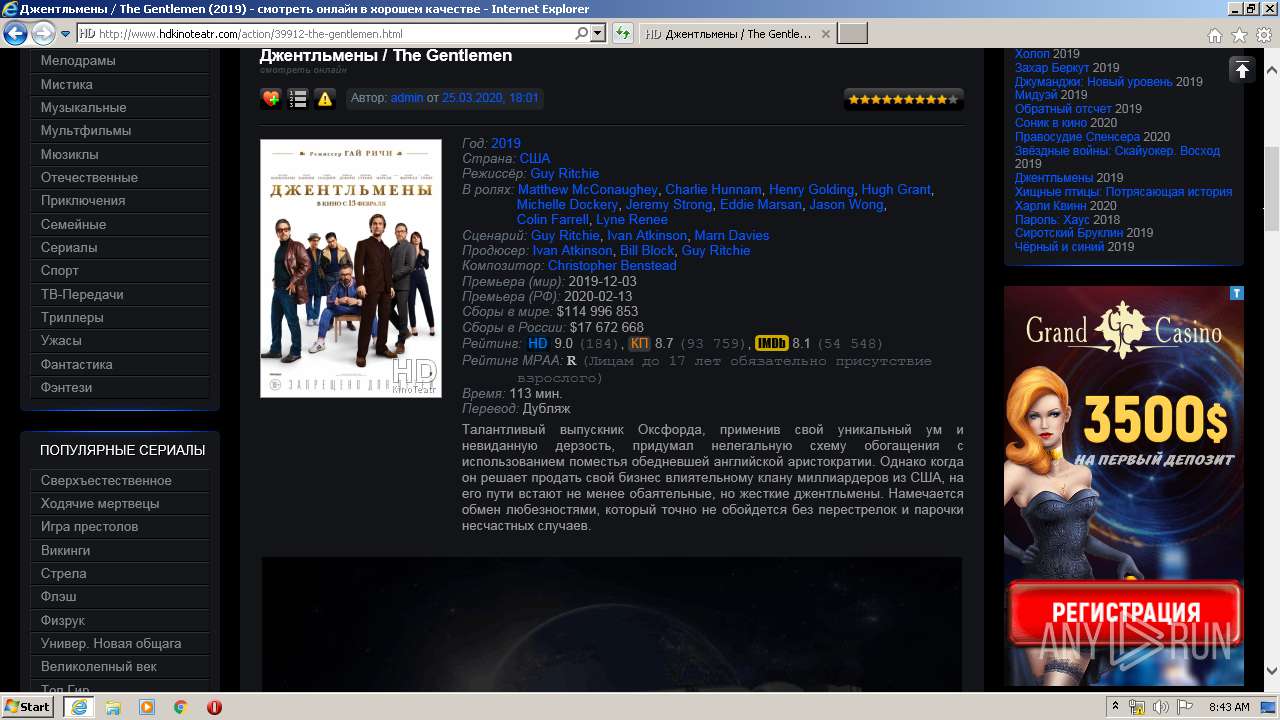
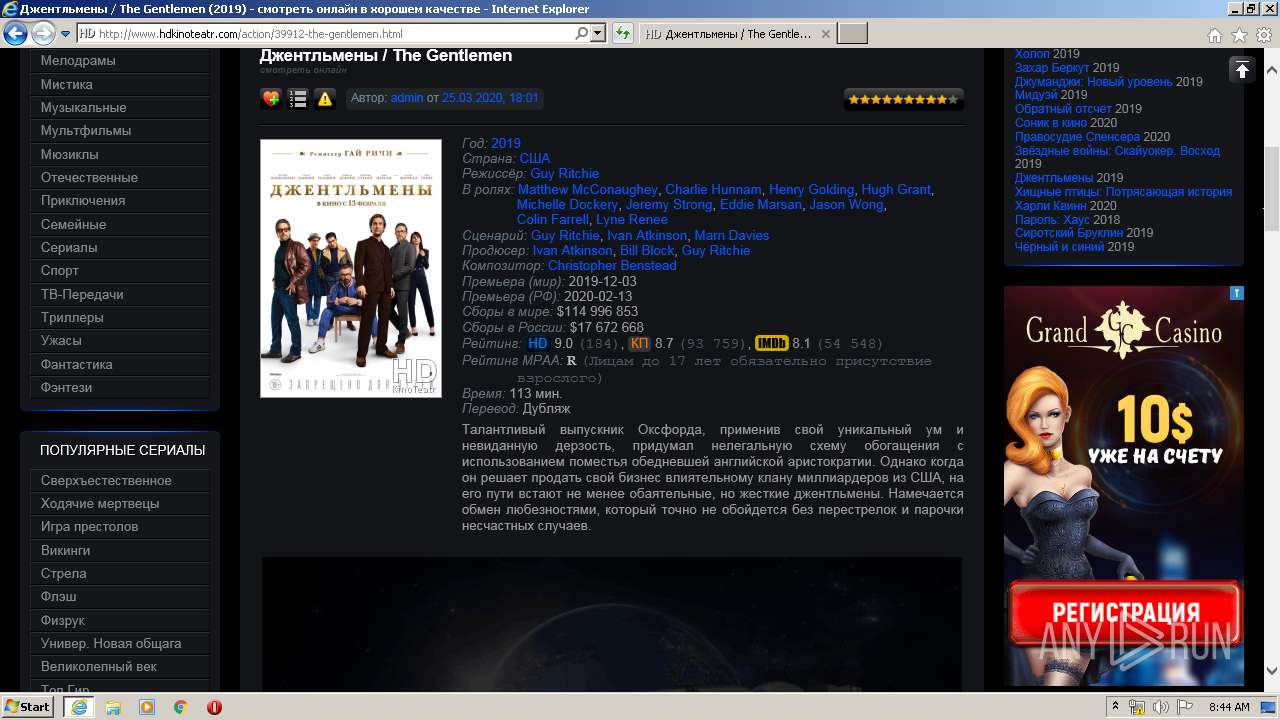
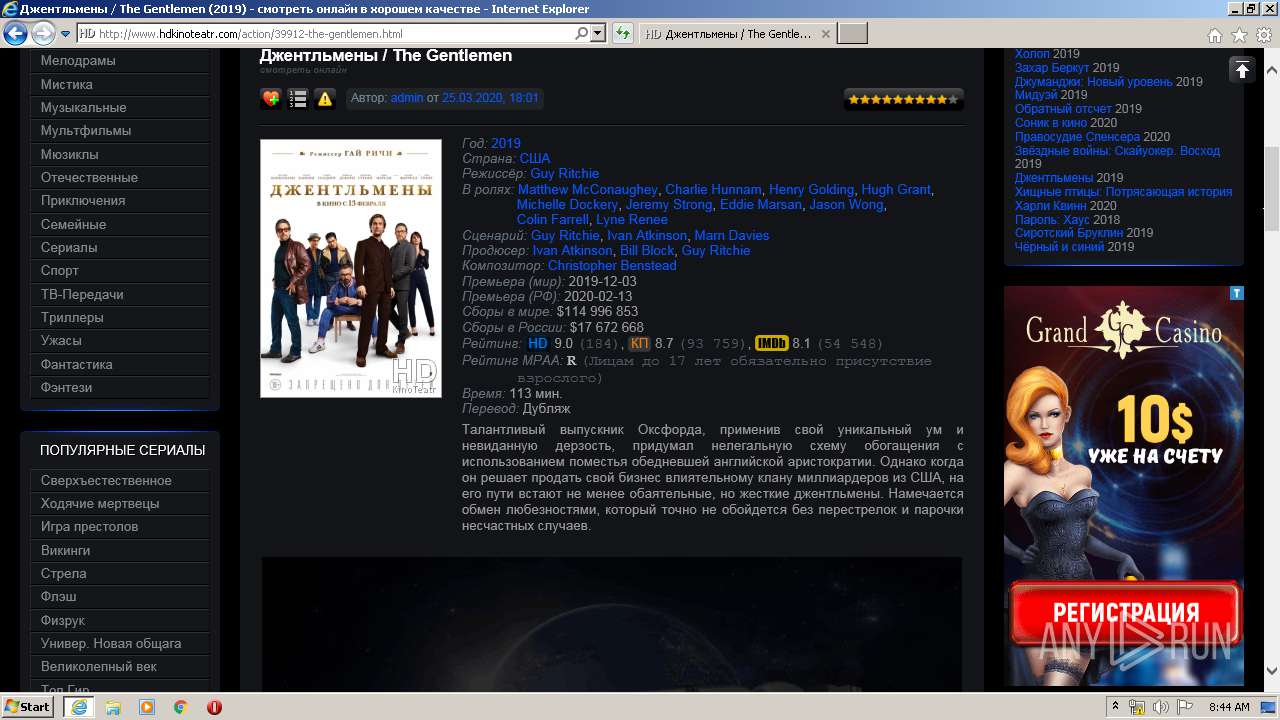
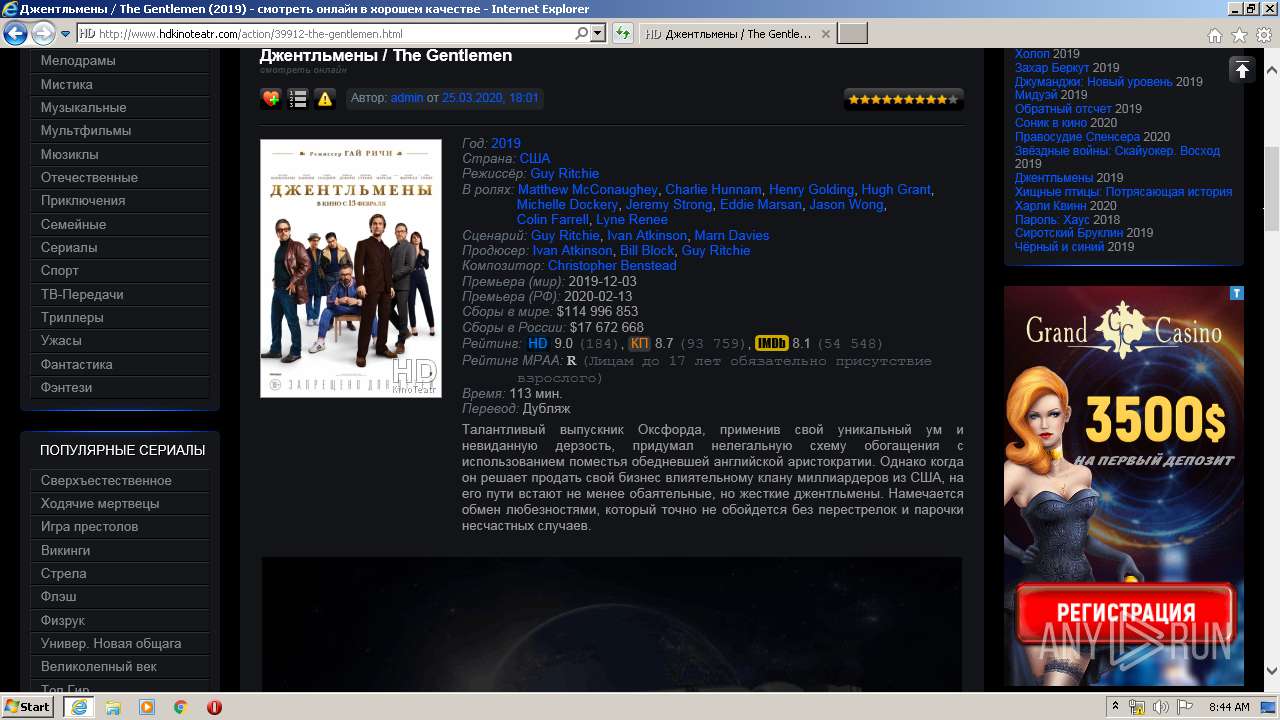
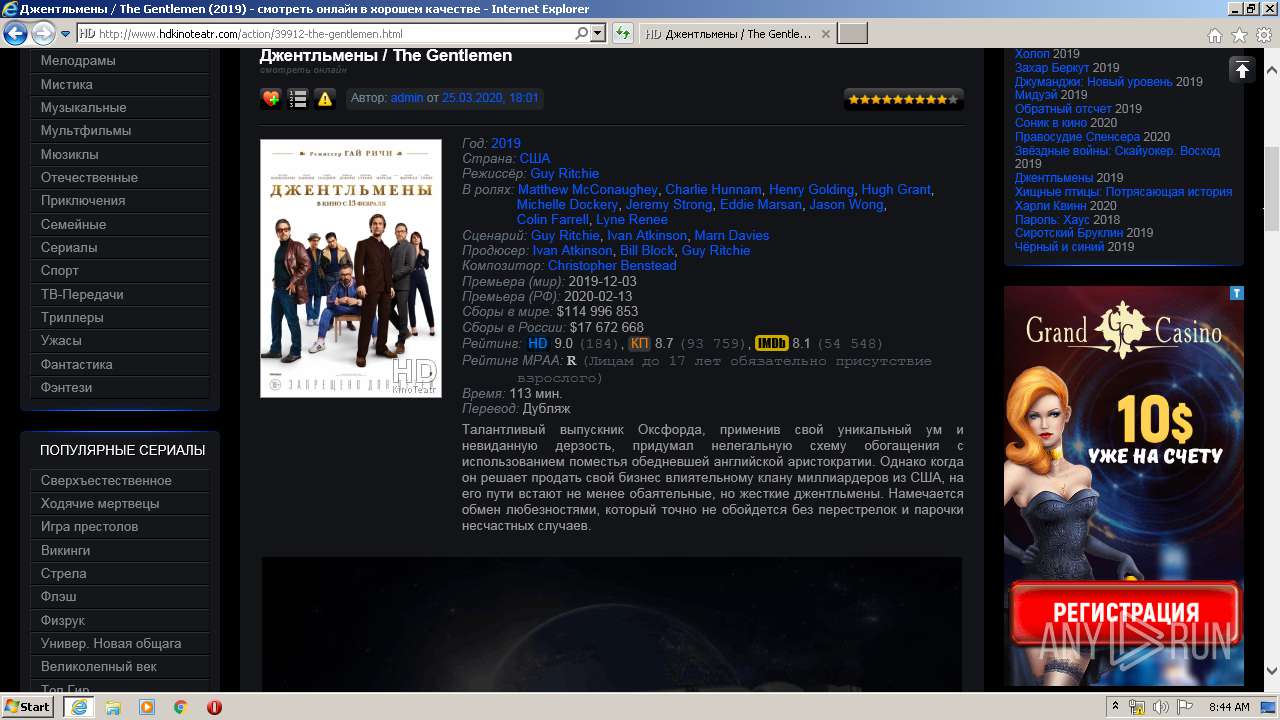
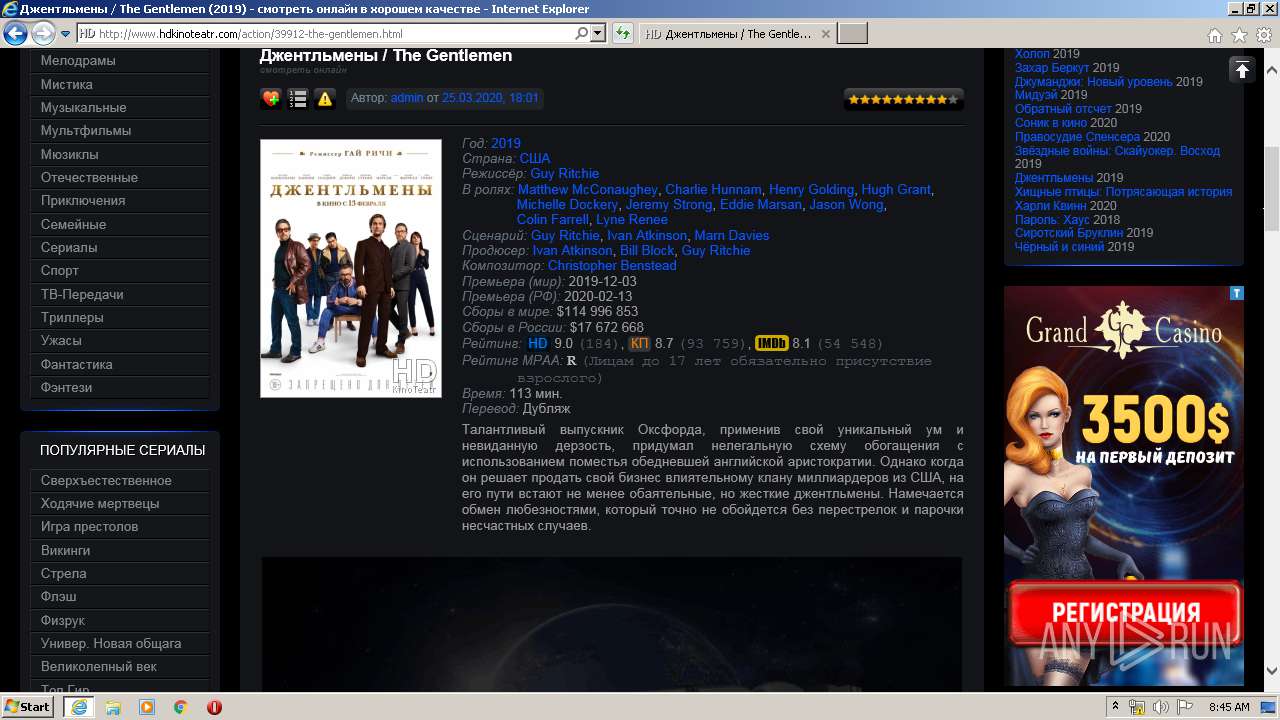
| URL: | http://www.hdkinoteatr.com/ |
| Full analysis: | https://app.any.run/tasks/145110ae-28d7-4a31-9368-10f5d23c1d6e |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2020, 08:41:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DAD57F742A1591A0D8D3AEA39679530F |
| SHA1: | 478F6C9C47888F8CDAD96C51B6E534D6D7B5FFB8 |
| SHA256: | F4D46076167DA7D18A7C464743893FB2742A6E0244EAEE059C675B87E74F1690 |
| SSDEEP: | 3:N1KJS4CMLUbd3:Cc4PLUbd3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 404)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3968)
- iexplore.exe (PID: 1524)
Changes internet zones settings
- iexplore.exe (PID: 1524)
Reads internet explorer settings
- iexplore.exe (PID: 3968)
Creates files in the user directory
- iexplore.exe (PID: 1524)
- iexplore.exe (PID: 3968)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 404)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 3968)
Reads settings of System Certificates
- iexplore.exe (PID: 1524)
- iexplore.exe (PID: 3968)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1524)
Changes settings of System certificates
- iexplore.exe (PID: 1524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
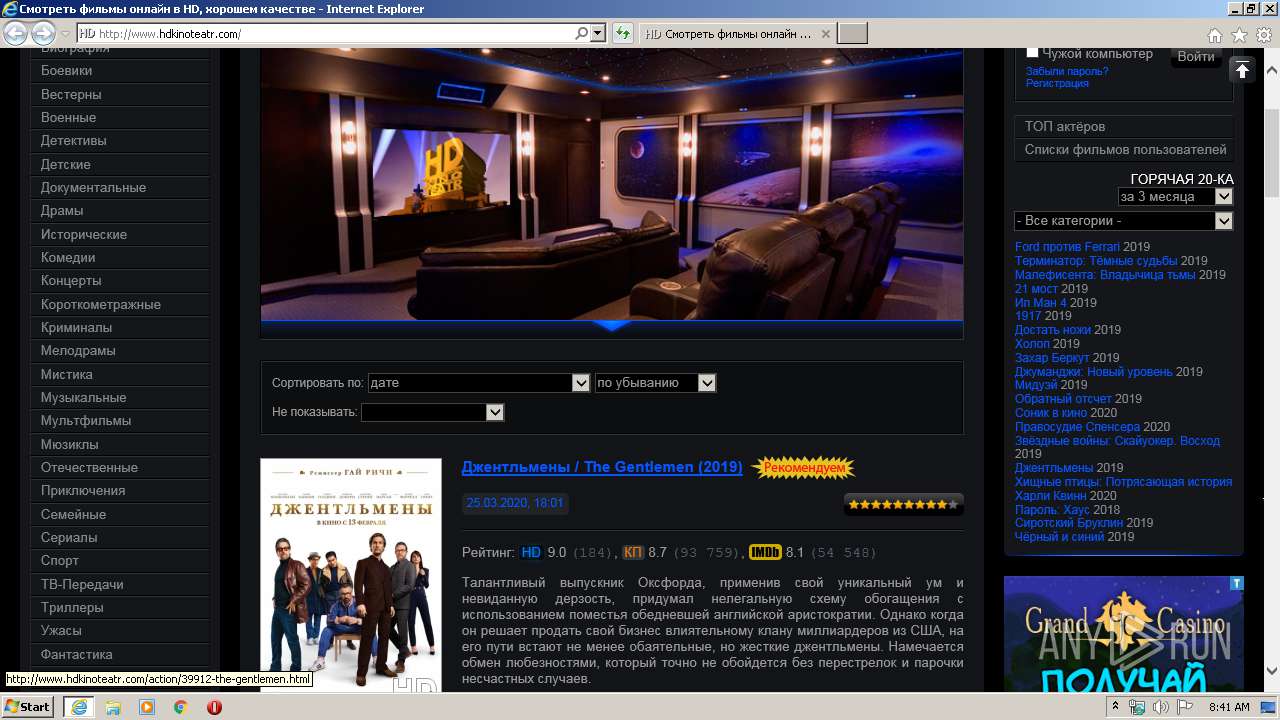
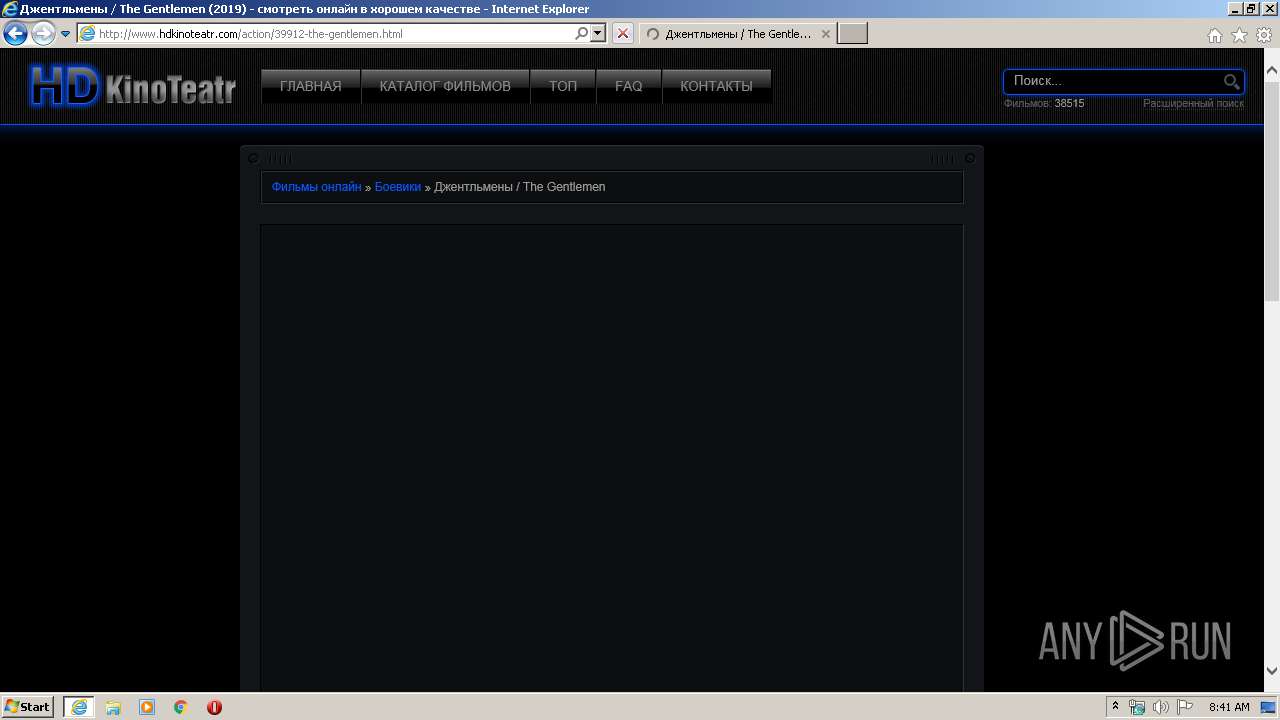
| 1524 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.hdkinoteatr.com/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1524 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
9 218
Read events
2 259
Write events
4 715
Delete events
2 244
Modification events
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2369058202 | |||
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30802963 | |||
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
125
Text files
370
Unknown types
78
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8QU1CQCK.txt | — | |
MD5:— | SHA256:— | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1UAOJV3W.txt | — | |
MD5:— | SHA256:— | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\453HF2UZ.txt | — | |
MD5:— | SHA256:— | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\dle.min[1].js | html | |
MD5:440F6824B1C2520ED2924A0E6971F110 | SHA256:69F29E1C43A85155278E636EF865F8F3414EE146E35C48C80C064230F776FD98 | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jqueryui[1].js | text | |
MD5:75DE4E40946169B4276BE999D5E1C15E | SHA256:0496AF1756CC35C3C7BC0B5B6FD4FD53E5BDFBE4E2A40E551553AB680BC5A3F8 | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\lists[1].js | text | |
MD5:D7C2BFE0D215E29DC4DE1443A87E55E6 | SHA256:138C51738B4828BACFA9E17B5E246368FDD8063009F3EE5E0BE4479E049EB9D2 | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\uppod_flash[1].js | text | |
MD5:08B758676243F0F9EAE29BD166850AAF | SHA256:0DF50CA48B9339F712F16E66C544B1392E0574E543289A553825CB3059ACE020 | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\funcs[1].js | text | |
MD5:45679BE7C8EFFCEF6DB97FBF97EF8D77 | SHA256:6A0D0F4660DDA12C78D9B14B98B96DF3FA5A4FD0A4C8711EEB94AA871FFFCBB9 | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\engine[1].css | text | |
MD5:D5B228760C9DCCE4F9FEDC4D599657FA | SHA256:CC8D8E2F564A8F78BAB72A363347BAACC3062850793E2E671BF630D4DEE1C2FE | |||
| 3968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jquery.moreless[1].js | html | |
MD5:3339E924CBB3C492DAA239CC8A4D70CA | SHA256:17248033AF8B875A232A75A9BFFC5E5775BC63106AEEFFCE0BB80C621ABA61DB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
253
TCP/UDP connections
206
DNS requests
73
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/engine/classes/js/jqueryui.js | US | text | 50.3 Kb | whitelisted |
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/ | US | html | 18.4 Kb | whitelisted |
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/templates/HD-kino-dark/style/style.min.css?v=55 | US | text | 7.97 Kb | whitelisted |
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/engine/classes/js/jquery.js | US | html | 32.4 Kb | whitelisted |
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/engine/classes/js/dle.min.js?v=52 | US | html | 11.6 Kb | whitelisted |
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/engine/classes/js/jquery.moreless.js | US | html | 398 b | whitelisted |
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/templates/HD-kino-dark/style/engine.css | US | text | 3.28 Kb | whitelisted |
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/engine/classes/js/lists.js?v=2 | US | text | 686 b | whitelisted |
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/engine/classes/js/swfobject.js | US | text | 3.78 Kb | whitelisted |
3968 | iexplore.exe | GET | 200 | 104.27.134.153:80 | http://www.hdkinoteatr.com/engine/skins/token-input.js | US | text | 4.32 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | iexplore.exe | 87.250.250.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
3968 | iexplore.exe | 104.27.134.153:80 | — | Cloudflare Inc | US | unknown |
3968 | iexplore.exe | 92.223.124.254:443 | jsc.traffic-media.co.uk | G-Core Labs S.A. | DE | suspicious |
3968 | iexplore.exe | 185.199.108.153:443 | weblion777.github.io | GitHub, Inc. | NL | shared |
3968 | iexplore.exe | 185.199.109.153:443 | weblion777.github.io | GitHub, Inc. | NL | shared |
3968 | iexplore.exe | 193.200.64.134:80 | pbcde.com | HZ Hosting Ltd | NL | unknown |
3968 | iexplore.exe | 172.217.22.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3968 | iexplore.exe | 185.60.216.19:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3968 | iexplore.exe | 193.200.64.134:443 | pbcde.com | HZ Hosting Ltd | NL | unknown |
3968 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hdkinoteatr.com |
| whitelisted |
jsc.traffic-media.co.uk |
| suspicious |
weblion777.github.io |
| malicious |
partnercoll.github.io |
| malicious |
pbcde.com |
| unknown |
www.google-analytics.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
mrelko.com |
| suspicious |
counter.yadro.ru |
| whitelisted |
mc.yandex.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3968 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
3968 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
3968 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
3968 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
3968 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |