| File name: | Yeni alış sifariş siyahısı.exe |
| Full analysis: | https://app.any.run/tasks/86c7e55c-75bc-4f8d-bbee-779ff1936389 |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 11:42:40 |
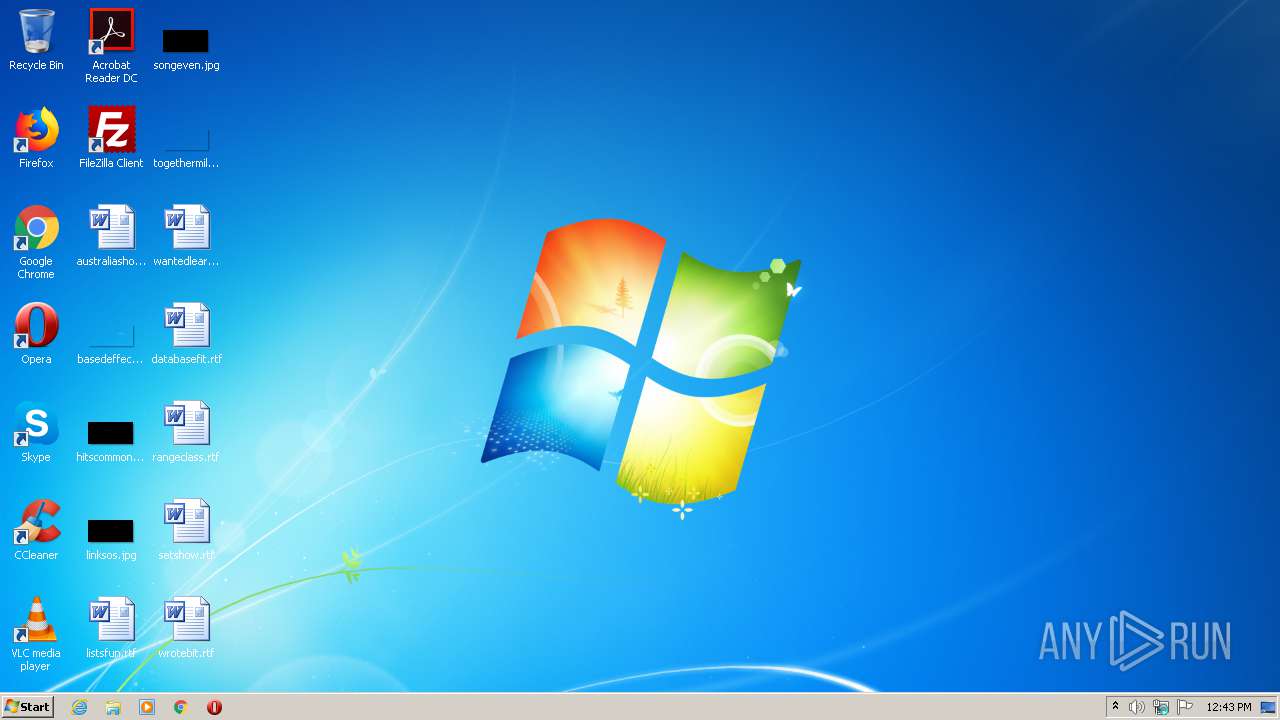
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 46BCE4CDBC93E61340B1FE04693B7536 |
| SHA1: | 85F661D10D5EF5B2F8D34122CA0B7581FDC39470 |
| SHA256: | F4CBB077C89F62BB6542489C882B324E8E2880DC3970E2540E61D1D25FFF157A |
| SSDEEP: | 49152:EkuyzVj7Lxj9WjwZVhlZfyiSCyiSV/CznFw9:ErgywZVLpi |
MALICIOUS
Changes settings of System certificates
- Yeni alış sifariş siyahısı.exe (PID: 2720)
SUSPICIOUS
Reads Internet Cache Settings
- Yeni alış sifariş siyahısı.exe (PID: 2720)
Starts CMD.EXE for commands execution
- help.exe (PID: 2368)
Adds / modifies Windows certificates
- Yeni alış sifariş siyahısı.exe (PID: 2720)
Creates files in the user directory
- Yeni alış sifariş siyahısı.exe (PID: 2720)
INFO
Manual execution by user
- help.exe (PID: 2368)
Reads the hosts file
- help.exe (PID: 2368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (58.7) |
|---|---|---|
| .scr | | | Windows screen saver (17.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.9) |
| .exe | | | Win32 Executable (generic) (6.1) |
| .exe | | | Win16/32 Executable Delphi generic (2.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 393728 |
| InitializedDataSize: | 235520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x616e0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.21.0.0 |
| ProductVersionNumber: | 16.21.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Sysinternals Process Explorer |
| FileVersion: | 16.21 |
| InternalName: | Process Explorer |
| LegalCopyright: | Copyright © 1998-2017 Mark Russinovich |
| LegalTrademarks: | Copyright (C) 1998-2017 Mark Russinovich |
| OriginalFileName: | Procexp.exe |
| ProductName: | Process Explorer |
| ProductVersion: | 16.21 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Sysinternals Process Explorer |
| FileVersion: | 16.21 |
| InternalName: | Process Explorer |
| LegalCopyright: | Copyright © 1998-2017 Mark Russinovich |
| LegalTrademarks: | Copyright (C) 1998-2017 Mark Russinovich |
| OriginalFilename: | Procexp.exe |
| ProductName: | Process Explorer |
| ProductVersion: | 16.21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0005F960 | 0x0005FA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55782 |
.itext | 0x00061000 | 0x00000730 | 0x00000800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.86404 |
.data | 0x00062000 | 0x00025A60 | 0x00025C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.64516 |
.bss | 0x00088000 | 0x000035C0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0008C000 | 0x0000259C | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.18388 |
.tls | 0x0008F000 | 0x00000034 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00090000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.195869 |
.reloc | 0x00091000 | 0x00006A84 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65225 |
.rsrc | 0x00098000 | 0x0000A650 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15536 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.03149 | 1916 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 5.79224 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.50191 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.26991 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.6949 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4084 | 3.1081 | 440 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4085 | 3.40093 | 504 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4086 | 3.45672 | 204 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
url.dll |
user32.dll |
version.dll |
Total processes
44
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2148 | C:\Windows\System32\TapiUnattend.exe | C:\Windows\System32\TapiUnattend.exe | — | Yeni alış sifariş siyahısı.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Windows(TM) Telephony Unattend Action Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Windows\System32\help.exe" | C:\Windows\System32\help.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Help Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
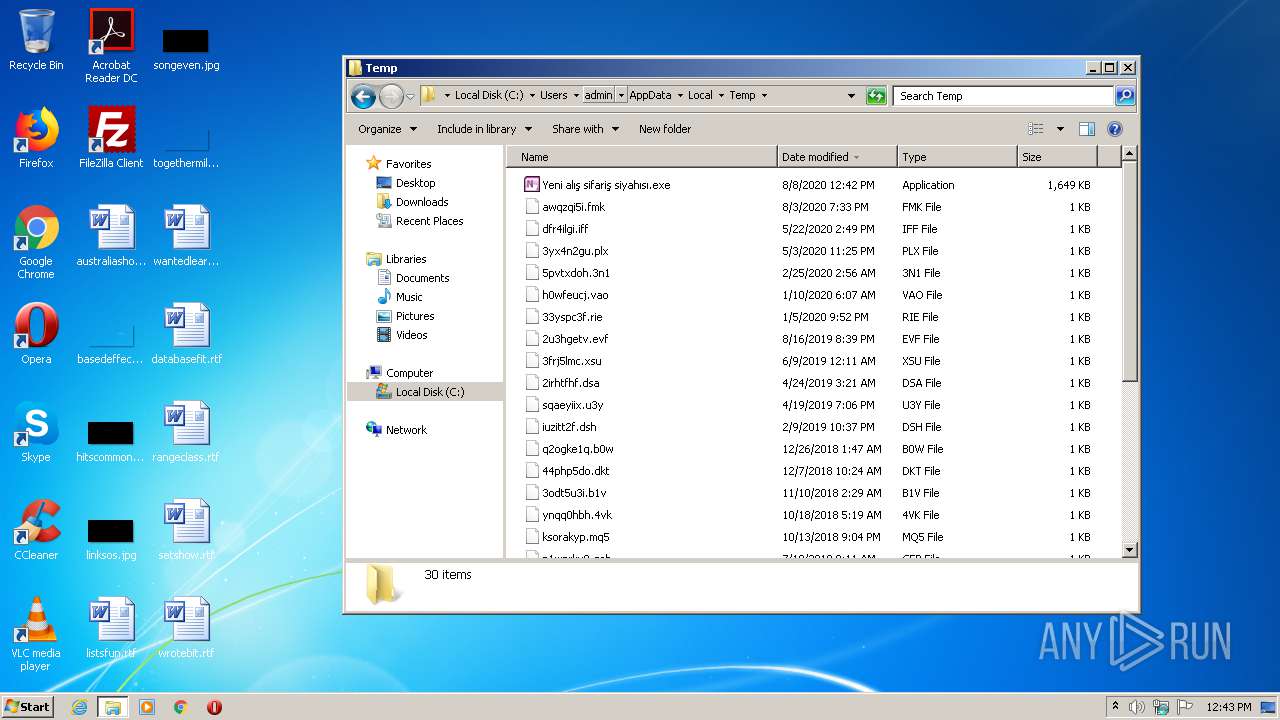
| 2720 | "C:\Users\admin\AppData\Local\Temp\Yeni alış sifariş siyahısı.exe" | C:\Users\admin\AppData\Local\Temp\Yeni alış sifariş siyahısı.exe | explorer.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals Process Explorer Exit code: 0 Version: 16.21 Modules
| |||||||||||||||
| 4084 | /c del "C:\Windows\System32\TapiUnattend.exe" | C:\Windows\System32\cmd.exe | — | help.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
66
Read events
36
Write events
28
Delete events
2
Modification events
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2720) Yeni alış sifariş siyahısı.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
Executable files
0
Suspicious files
6
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\Local\Temp\Cab6482.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\Local\Temp\Tar6483.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_979AB563CEB98F2581C14ED89B8957D4 | binary | |
MD5:— | SHA256:— | |||
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_979AB563CEB98F2581C14ED89B8957D4 | der | |
MD5:— | SHA256:— | |||
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6AF4EE75E3A4ABA658C0087EB9A0BB5B_F80805103A05D4F74523519C6EAD8FC0 | der | |
MD5:— | SHA256:— | |||
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | der | |
MD5:— | SHA256:— | |||
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\64DCC9872C5635B1B7891B30665E0558_5552C20A2631357820903FD38A8C0F9F | binary | |
MD5:— | SHA256:— | |||
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Osudddd[1] | text | |
MD5:— | SHA256:— | |||
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6AF4EE75E3A4ABA658C0087EB9A0BB5B_F80805103A05D4F74523519C6EAD8FC0 | binary | |
MD5:— | SHA256:— | |||
| 2720 | Yeni alış sifariş siyahısı.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\26JCZQGB.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2720 | Yeni alış sifariş siyahısı.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 314 b | whitelisted |
2720 | Yeni alış sifariş siyahısı.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
2720 | Yeni alış sifariş siyahısı.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEDJAnJQUGG0bwuno3m2vDJ8%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.18.233.62:443 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
2720 | Yeni alış sifariş siyahısı.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
2720 | Yeni alış sifariş siyahısı.exe | 162.159.134.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
cdn.discordapp.com |
| shared |
ocsp.comodoca.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |