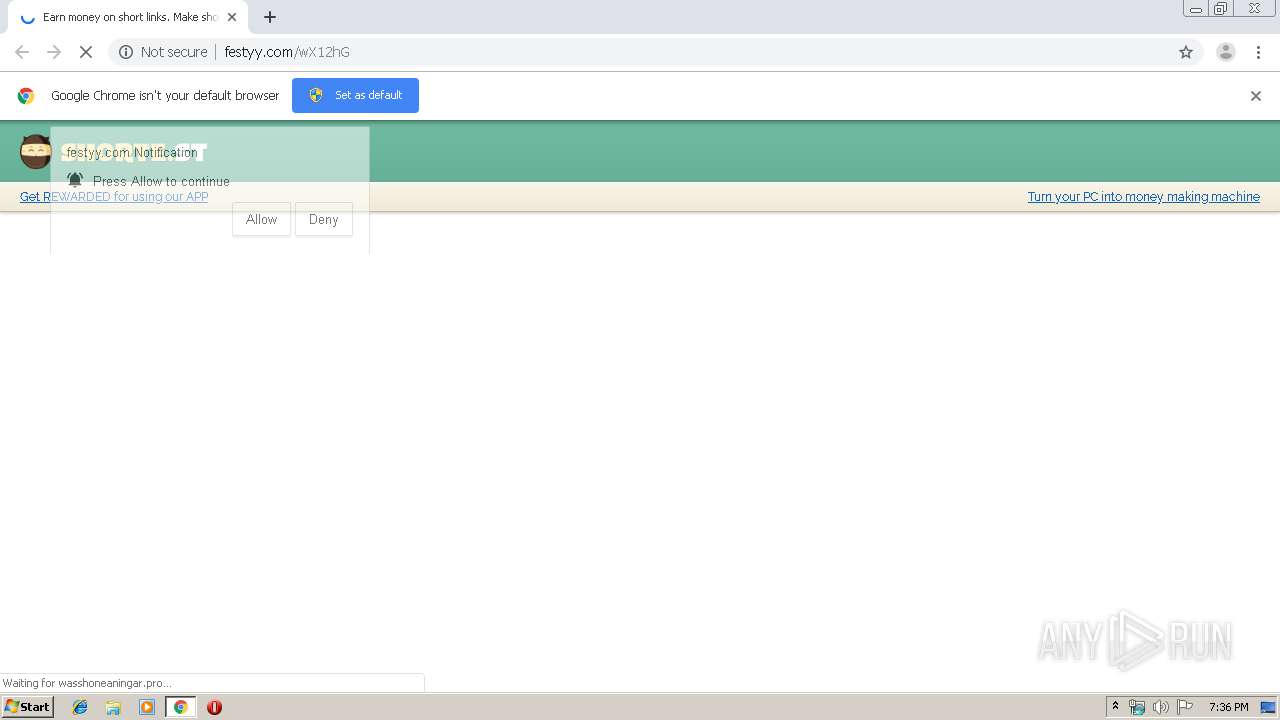
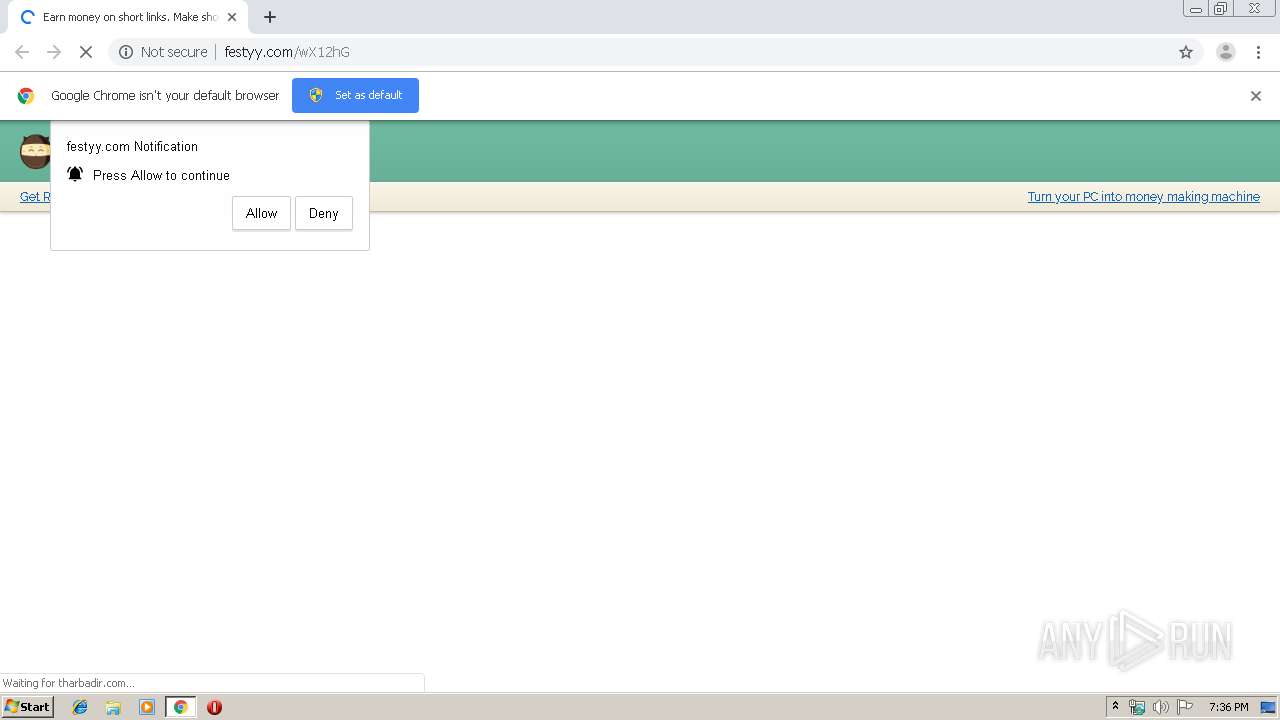
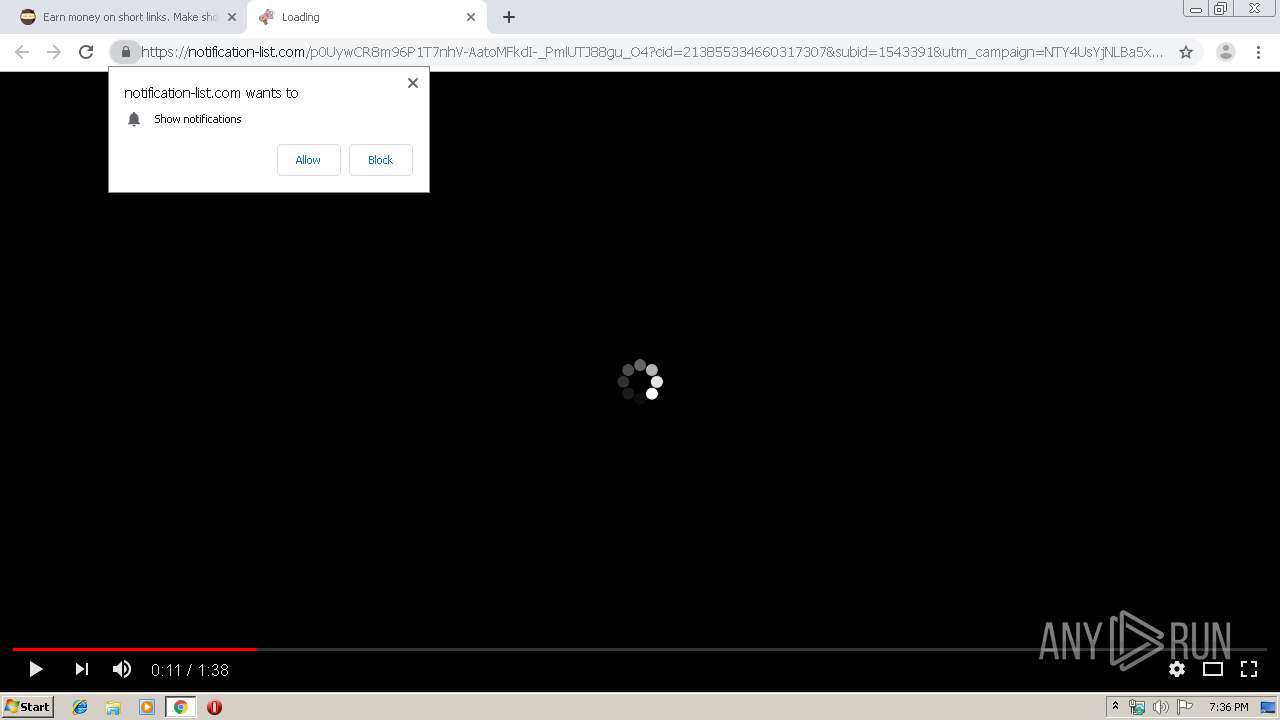
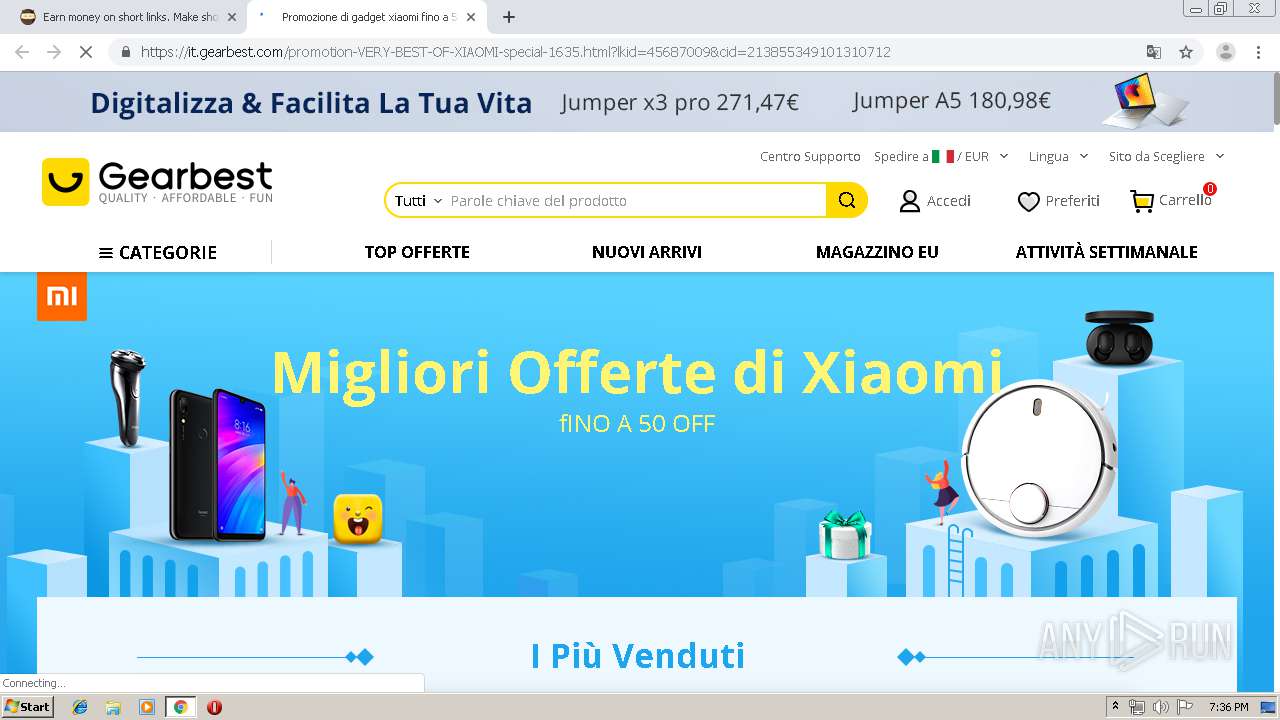
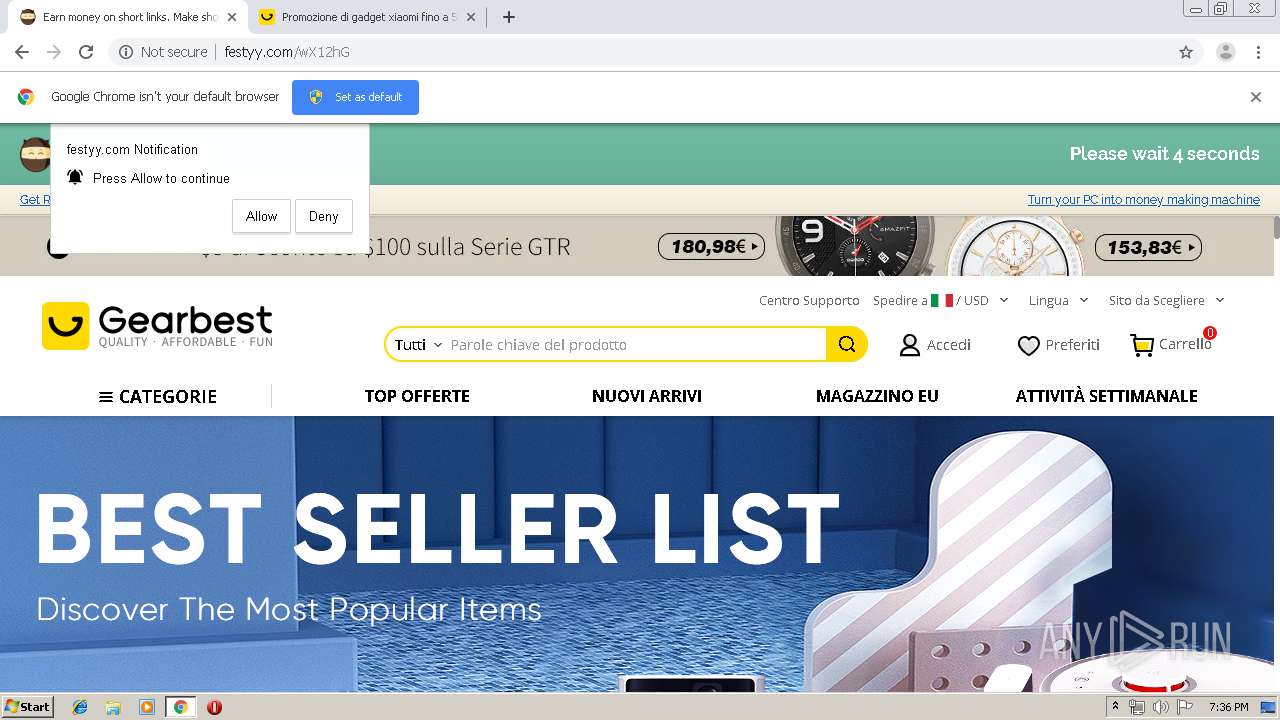
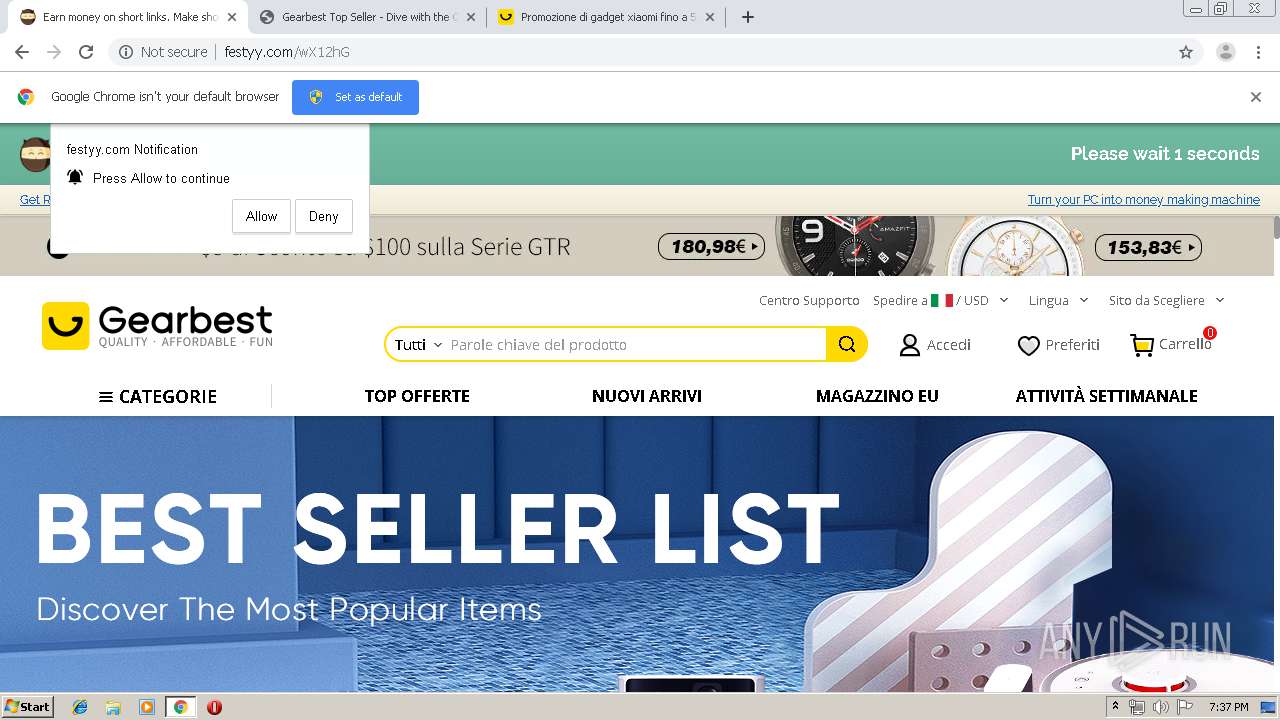
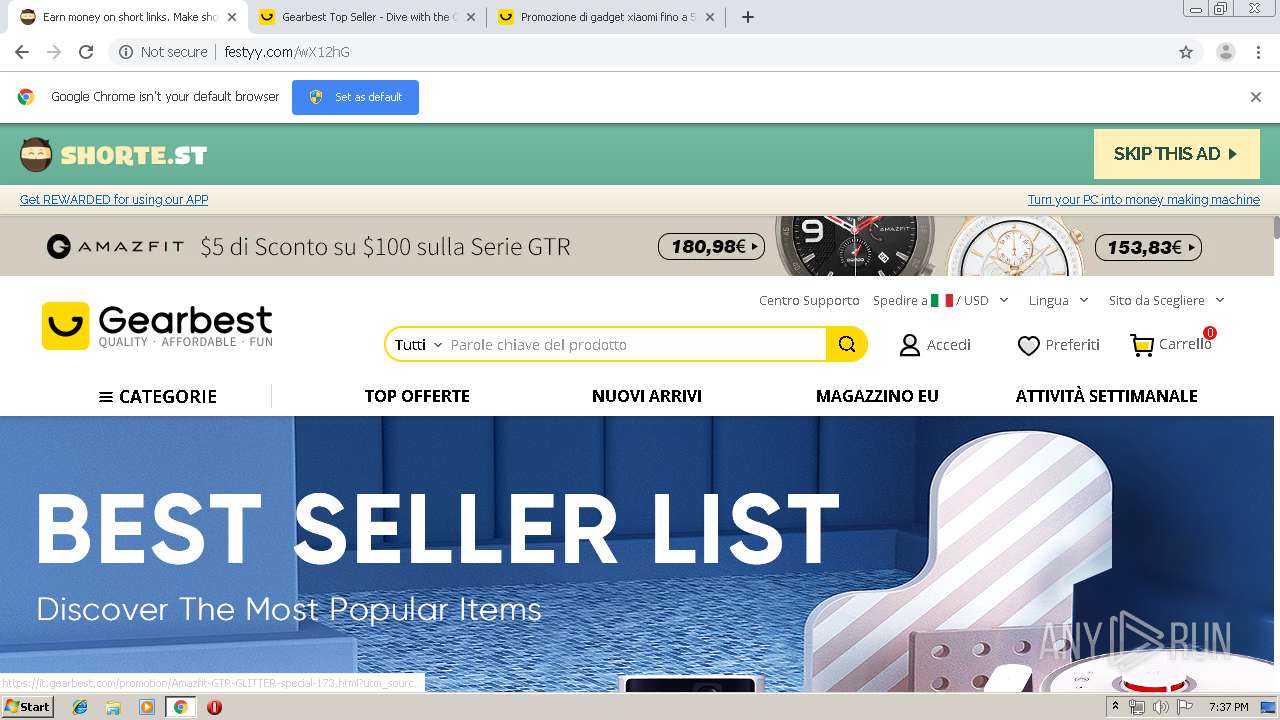
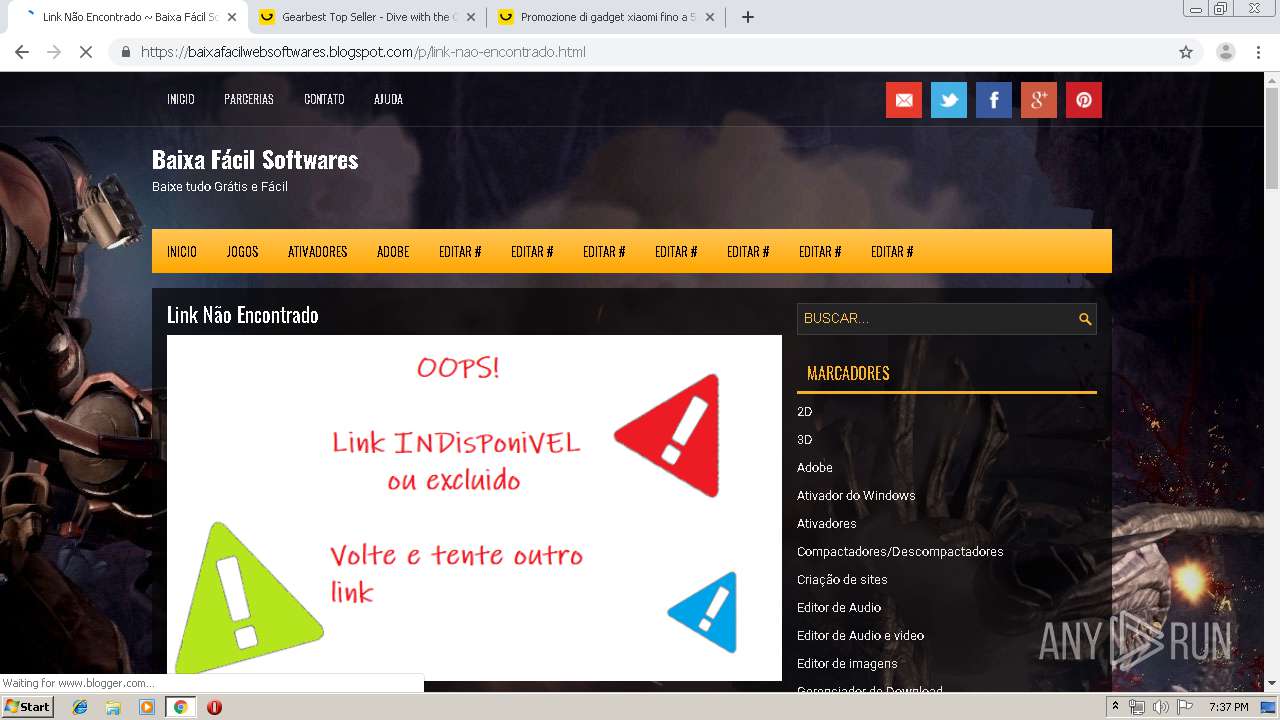
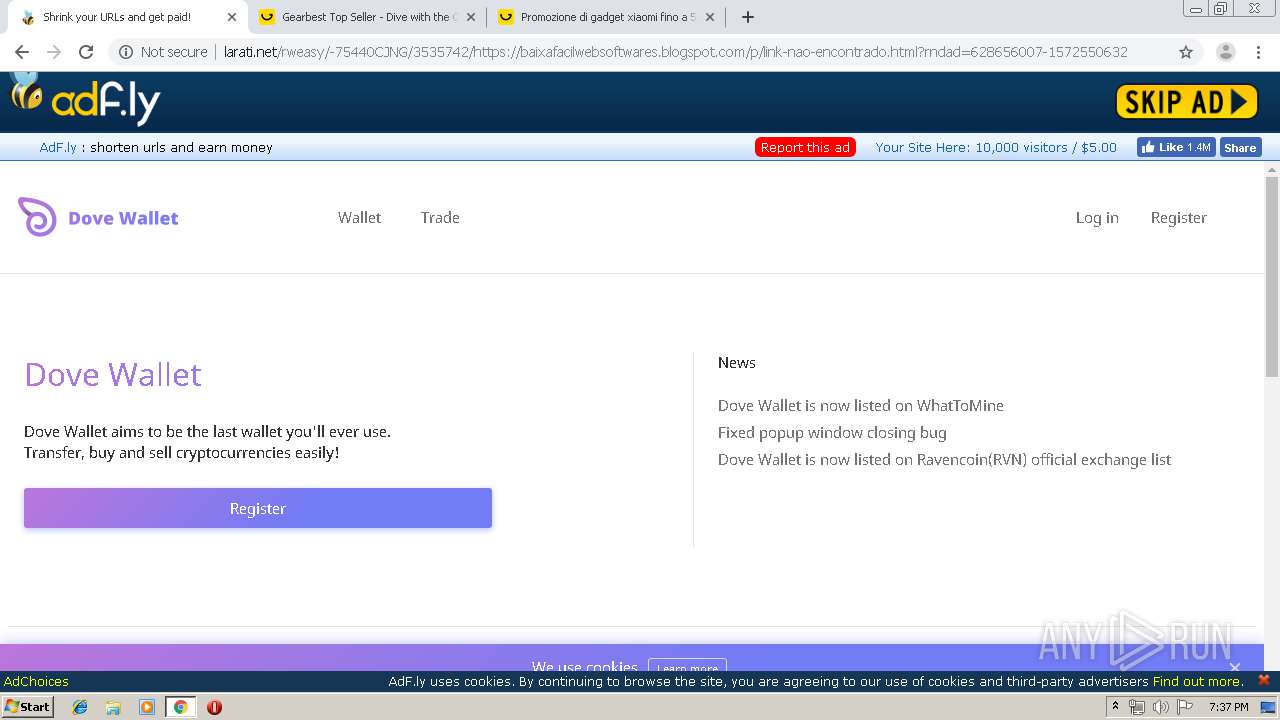
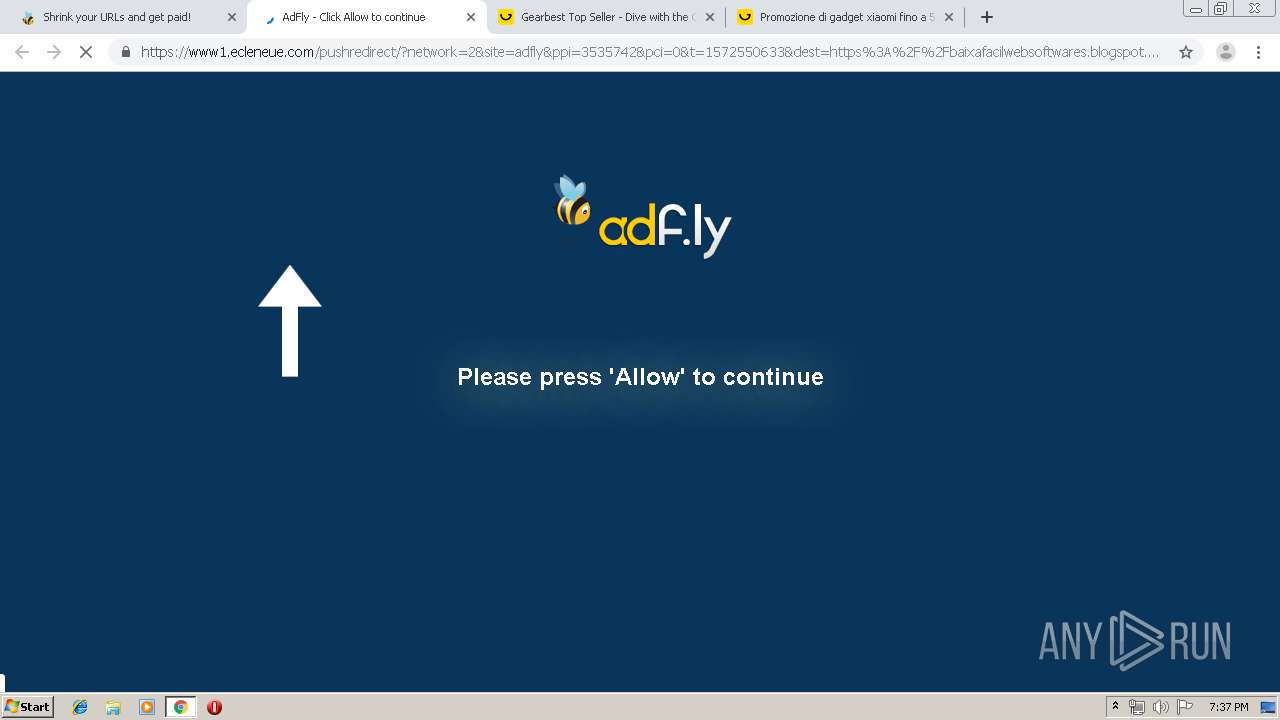
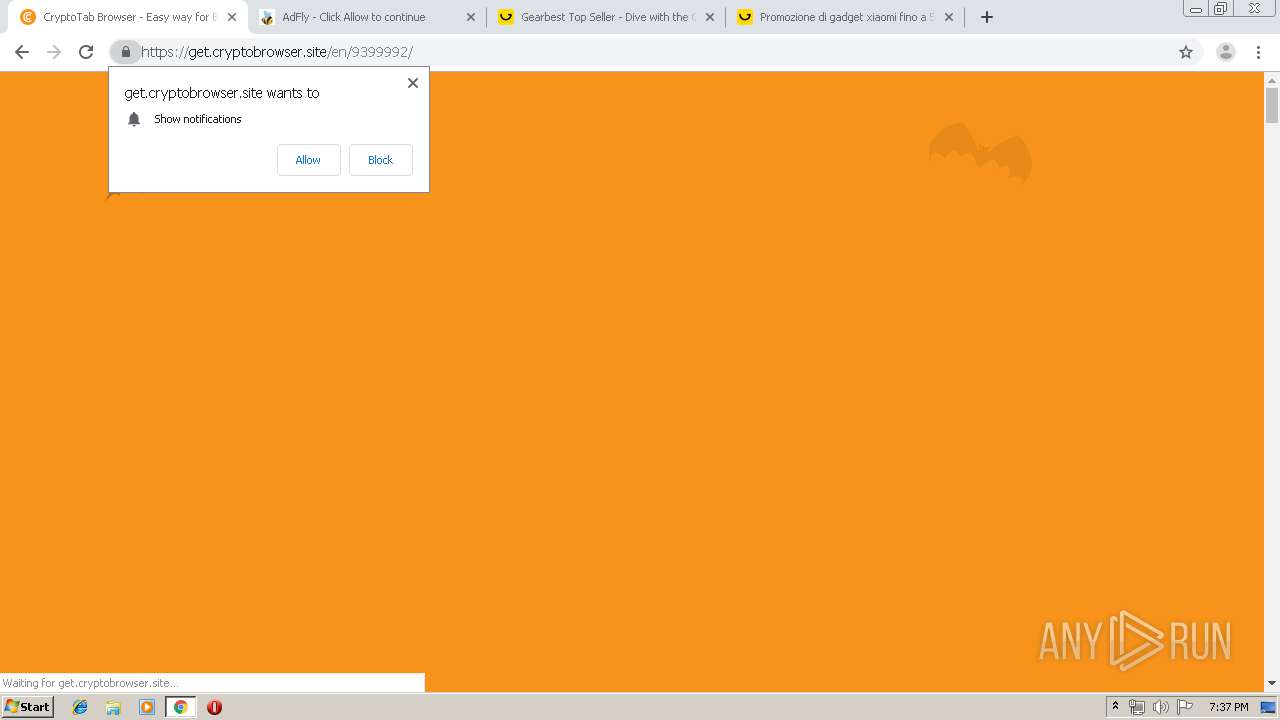
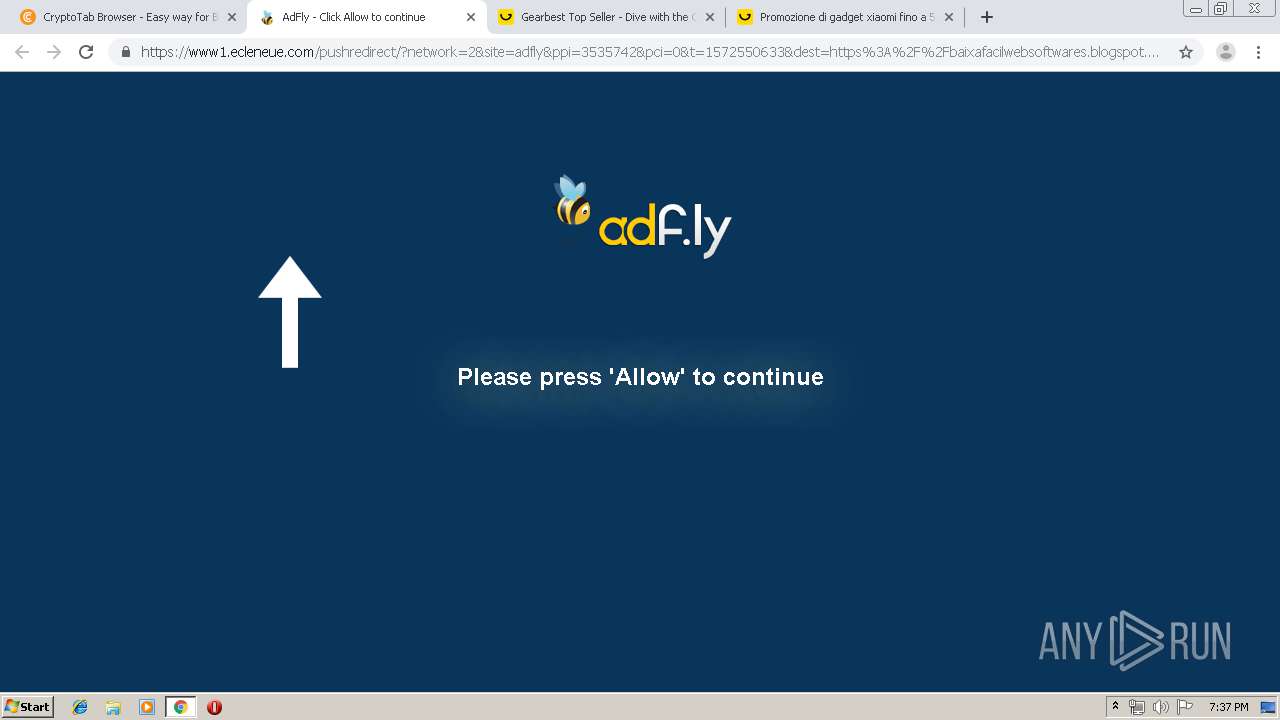
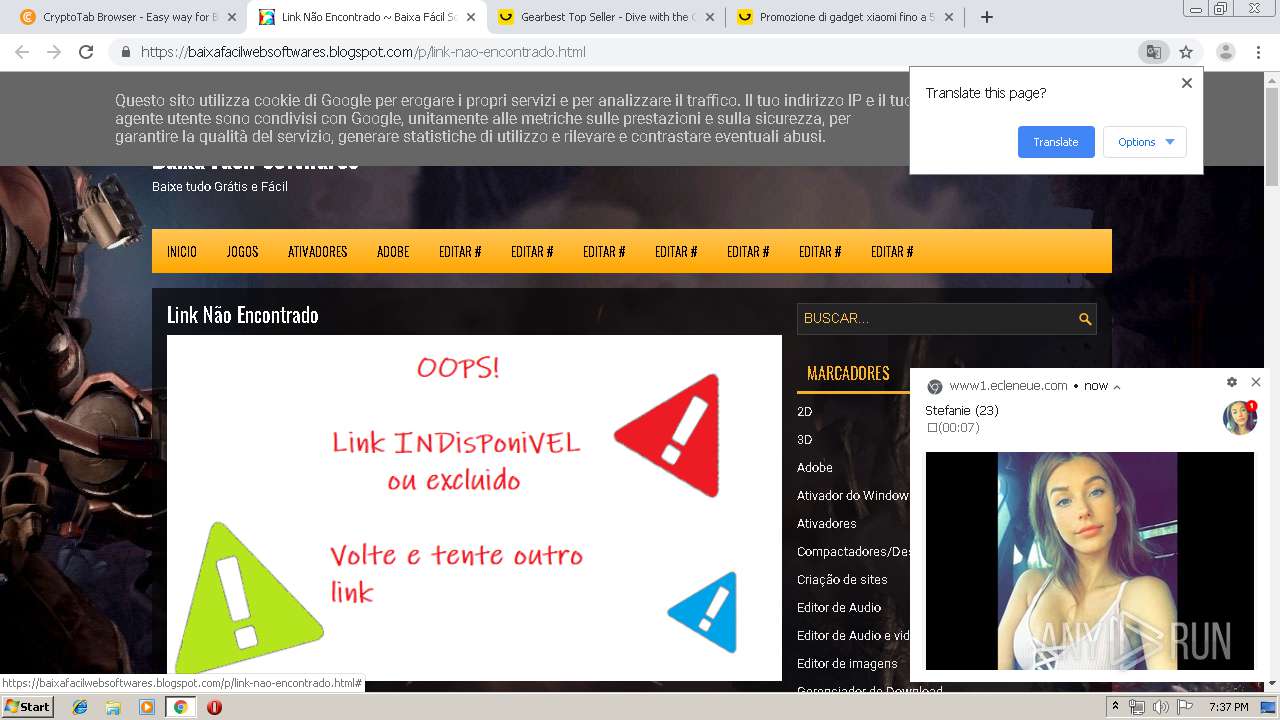
| URL: | http://festyy.com/wX12hG |
| Full analysis: | https://app.any.run/tasks/2f6ffd7a-7e45-486e-a880-d4ddca4ebcdf |
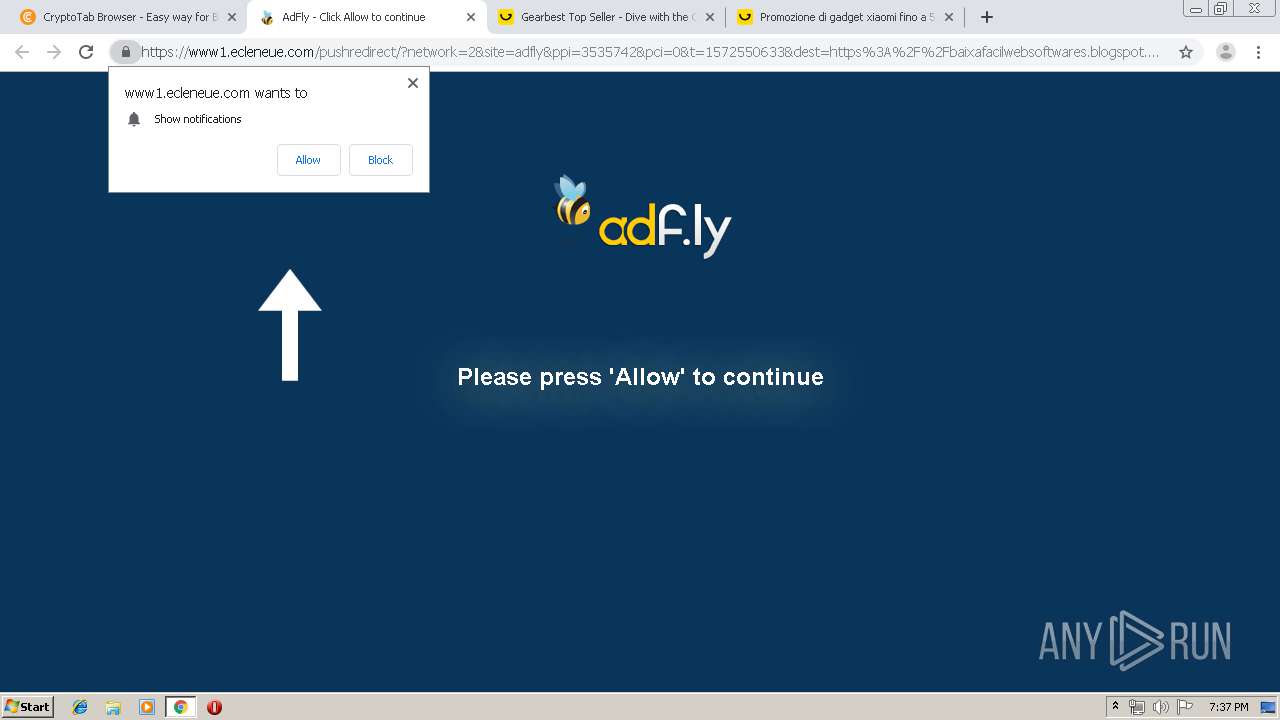
| Verdict: | No threats detected |
| Analysis date: | October 31, 2019, 19:36:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FE8094267EF0550FDA582314B01CF5EB |
| SHA1: | 6B65C033AF236C7777975514361962BB084E1ED5 |
| SHA256: | F4C2C53B0910A13D879ADE4AB9760DD2519D38196A1E5E7B3484D5233477A5DF |
| SSDEEP: | 3:N1KYhTw:CYFw |
MALICIOUS
No malicious indicators.SUSPICIOUS
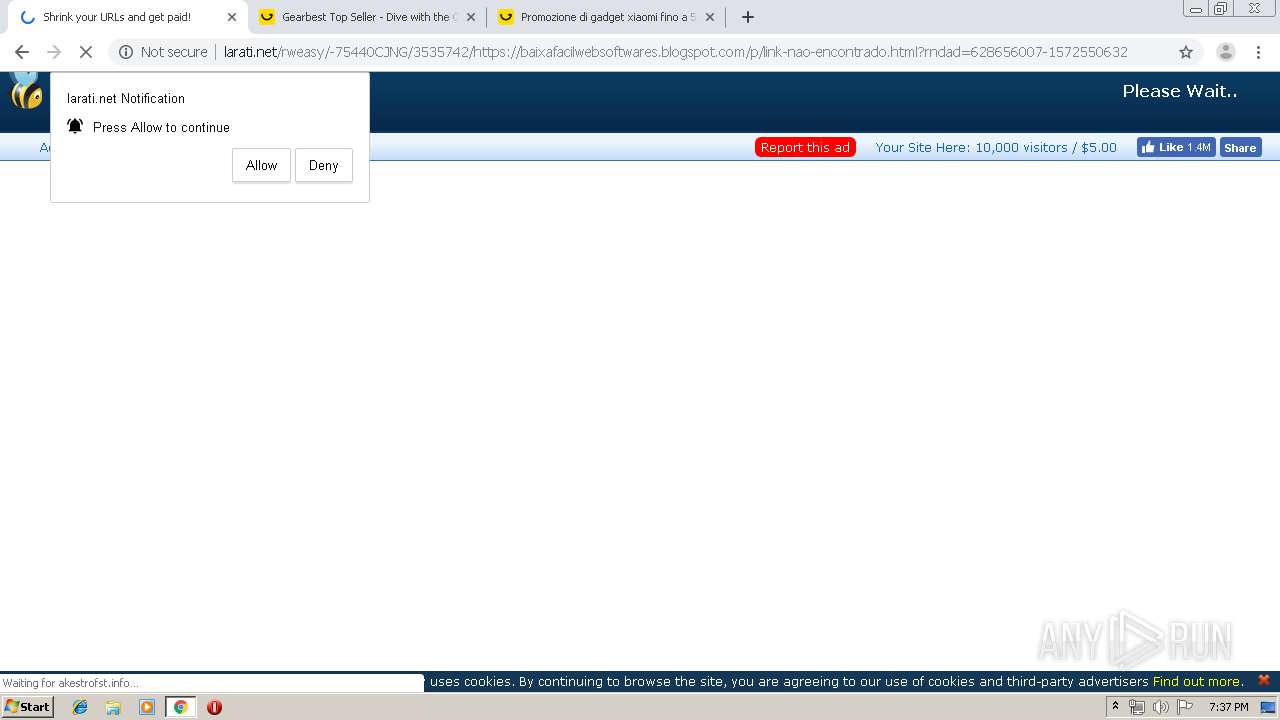
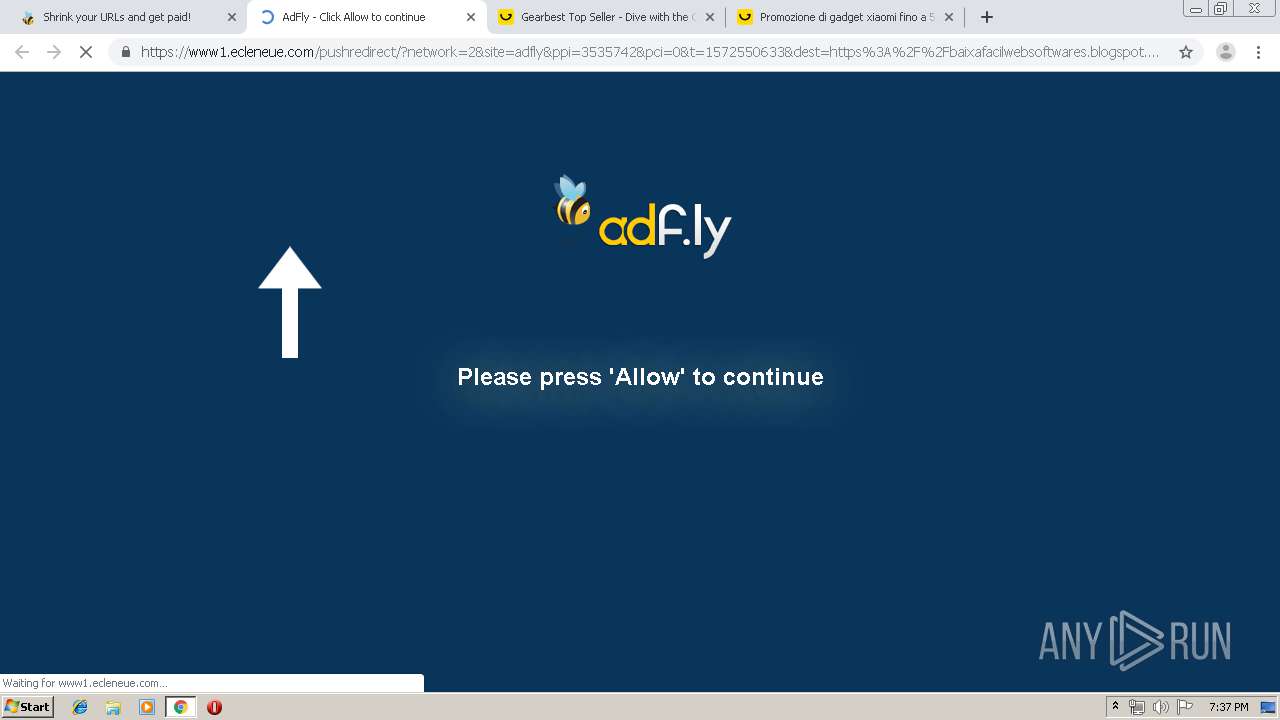
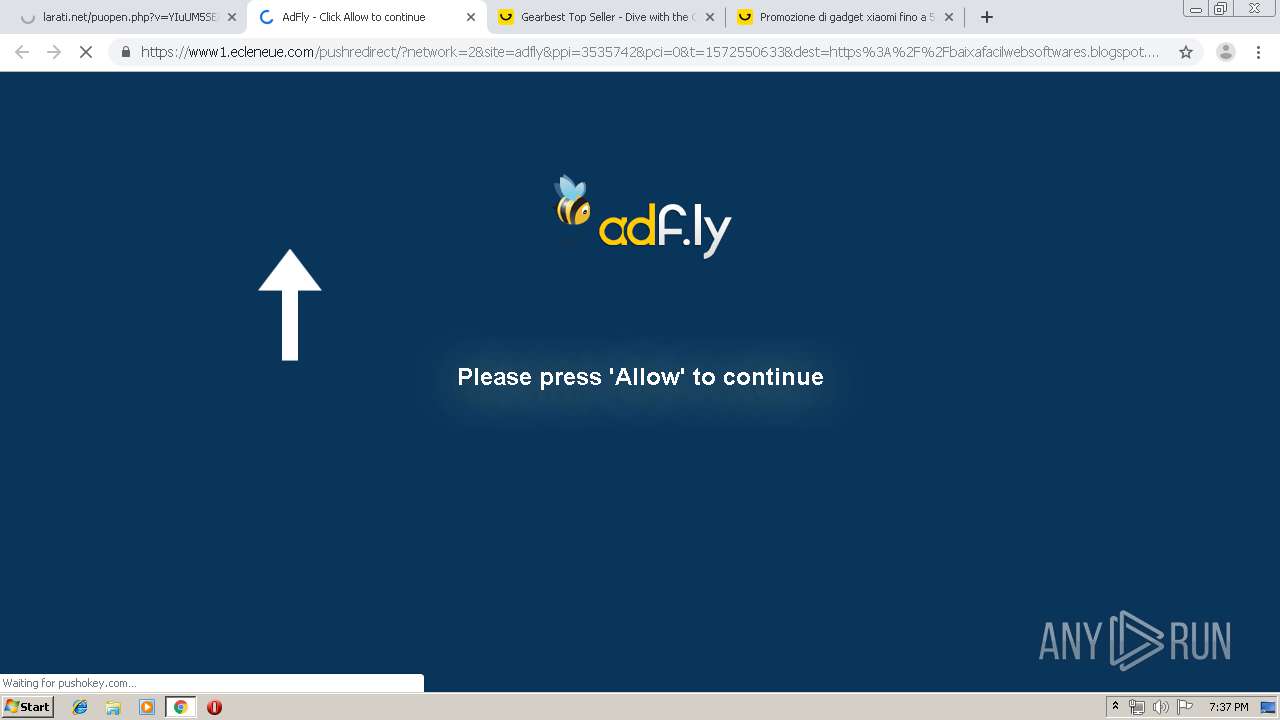
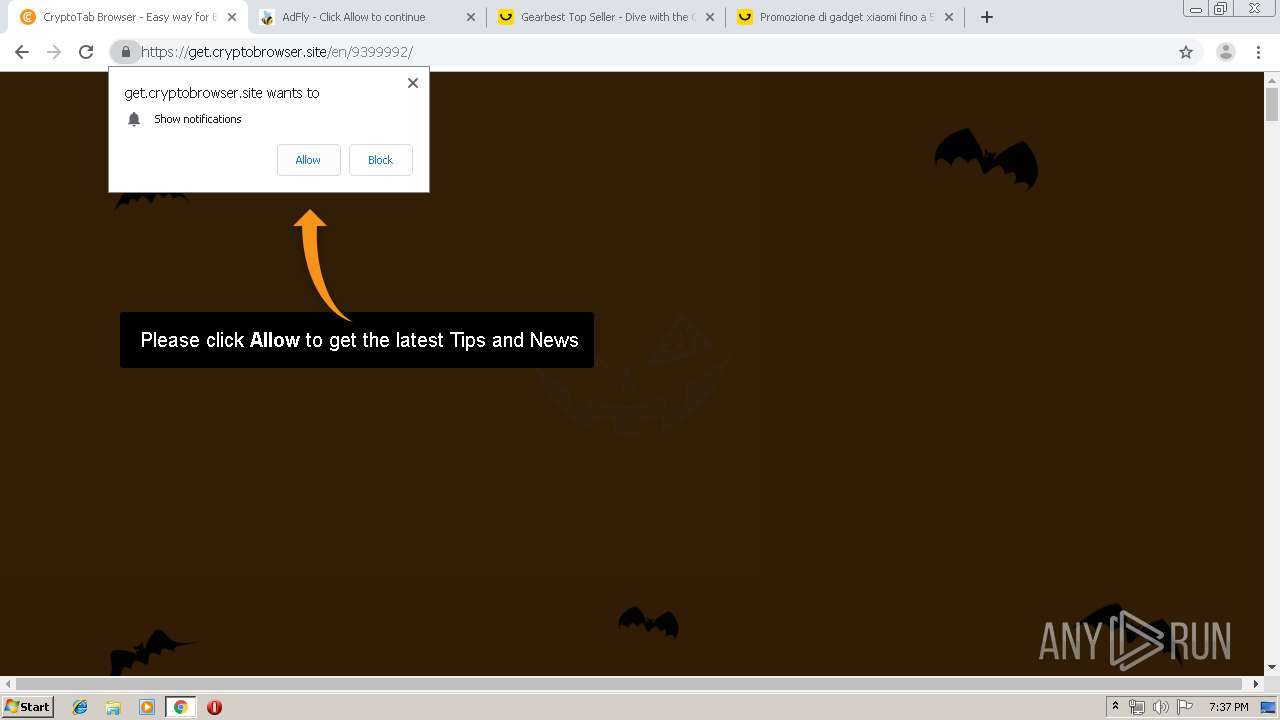
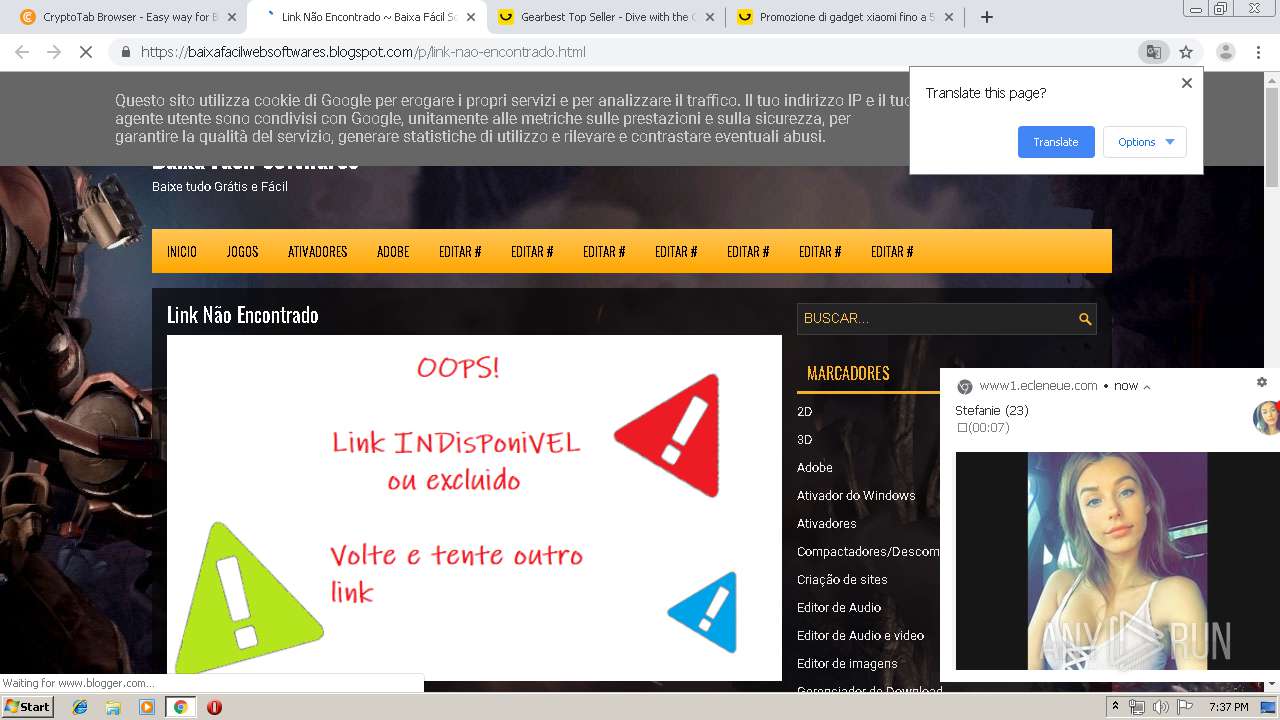
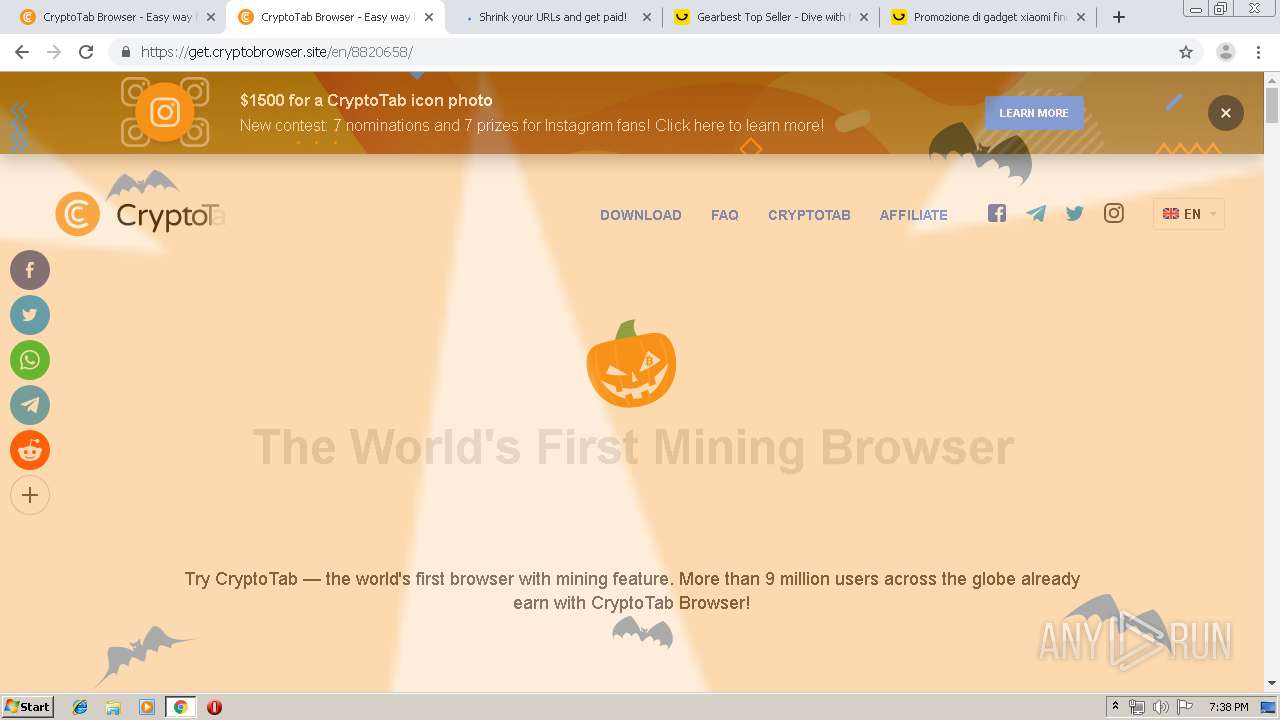
Modifies files in Chrome extension folder
- chrome.exe (PID: 1948)
INFO
Reads the hosts file
- chrome.exe (PID: 1948)
- chrome.exe (PID: 2084)
Reads settings of System Certificates
- chrome.exe (PID: 2084)
Changes settings of System certificates
- chrome.exe (PID: 2084)
Dropped object may contain TOR URL's
- chrome.exe (PID: 1948)
Application launched itself
- chrome.exe (PID: 1948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
99
Monitored processes
64
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1721904495698389149 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=37865223856037476 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3520547479564340040 --mojo-platform-channel-handle=4808 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2712 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2367892284189645763 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10183886395388750537 --renderer-client-id=57 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1700 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8481044991929084092 --renderer-client-id=40 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6577600266536606573 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7983812472372308610 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3620 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13327520542302318643,14185662005431868472,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=142558938143883115 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
694
Read events
558
Write events
131
Delete events
5
Modification events
| (PID) Process: | (1948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1948-13217024193686875 |
Value: 259 | |||
| (PID) Process: | (1948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1948) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
410
Text files
347
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3a46189c-65bd-45f3-b433-522e98d1bf7f.tmp | — | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a8cd.TMP | text | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a8dd.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
116
TCP/UDP connections
227
DNS requests
138
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
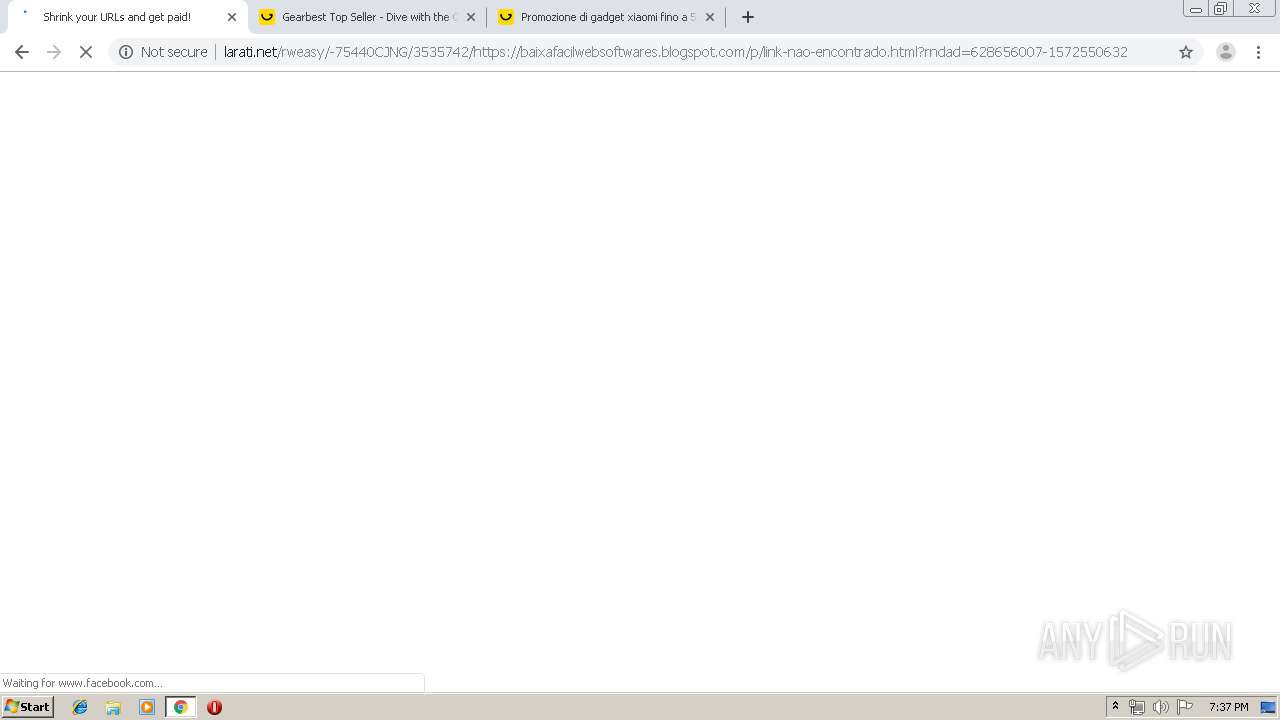
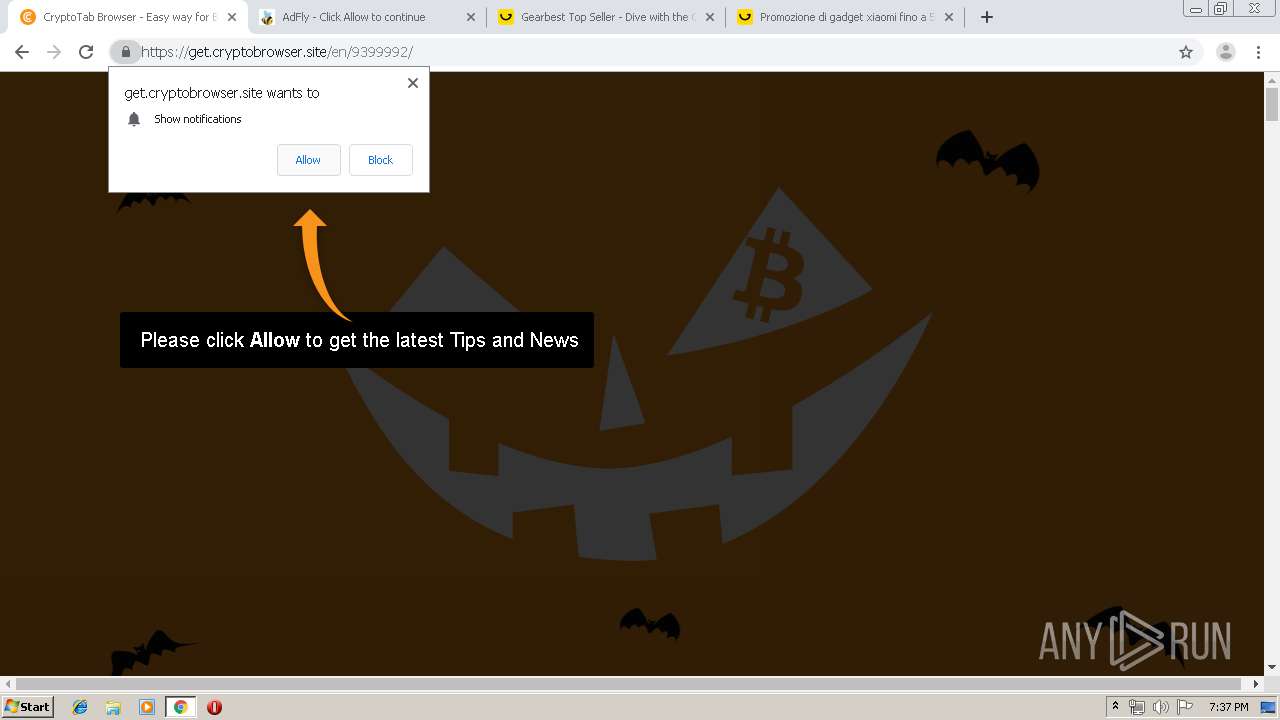
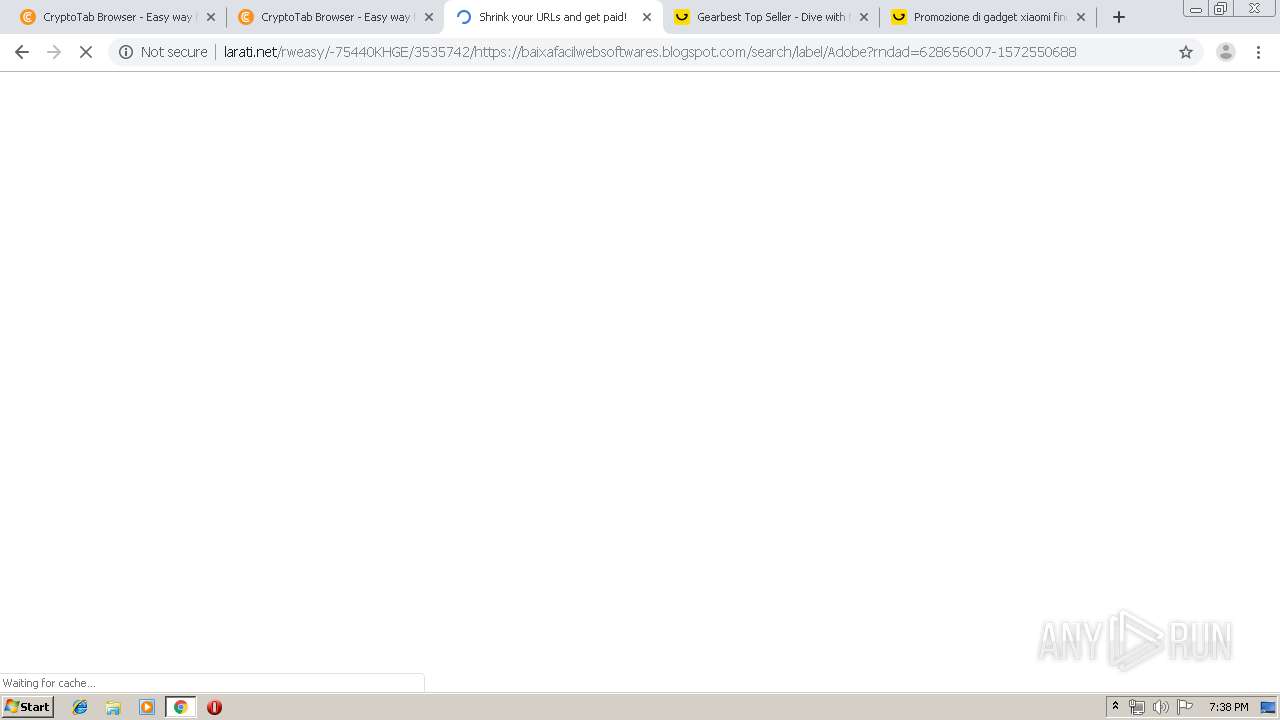
2084 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://festyy.com/grey_wizard_rewrite_js/?b=kevepuL7uDtv48a2kBNOaKX%2B6aTAC0auqFn4g7g0pt4%3D | PL | text | 2.06 Kb | suspicious |
2084 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://festyy.com/grey_wizard_rewrite/shst_en/error/smeweb_error.css | PL | text | 375 Kb | suspicious |
2084 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://festyy.com/bundles/advertisement/img/tracking.gif?test=408bd887fee77063b94c9b013a7c60a56e536229 | PL | compressed | 28.5 Kb | suspicious |
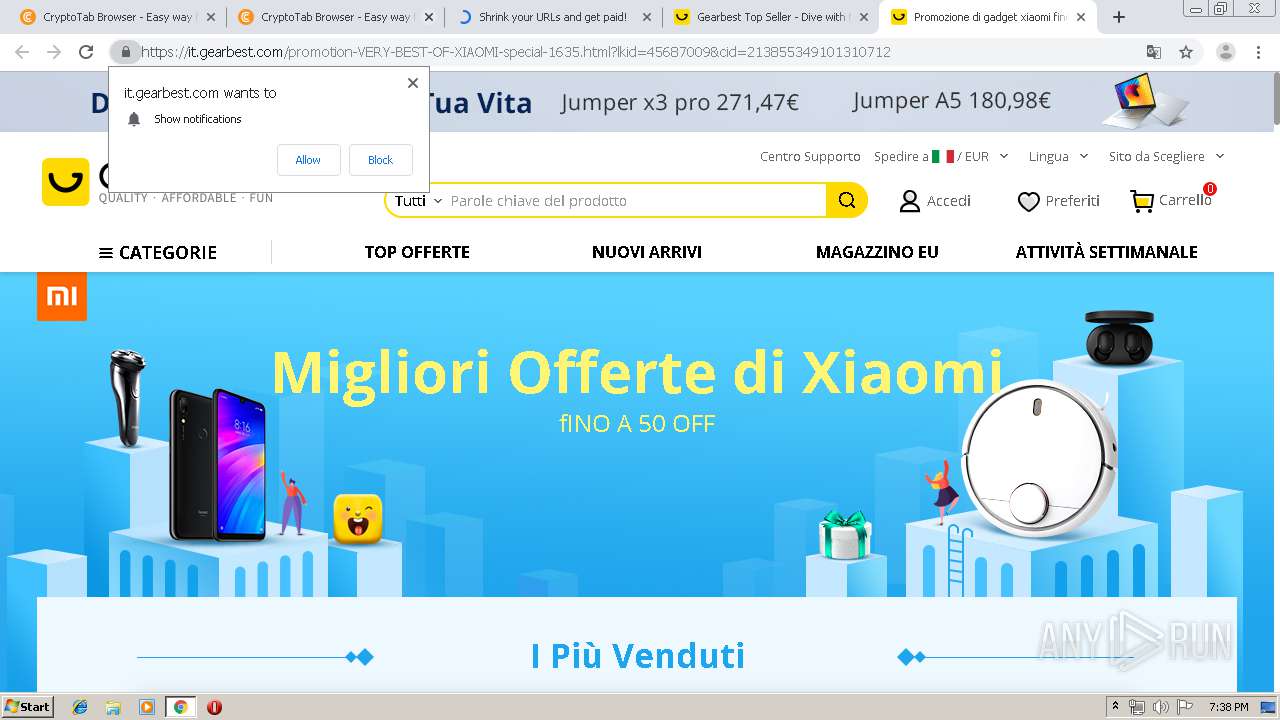
2084 | chrome.exe | GET | 403 | 185.66.120.52:80 | http://festyy.com/wX12hG | PL | html | 1.94 Kb | suspicious |
2084 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://festyy.com/wX12hG | PL | html | 28.5 Kb | suspicious |
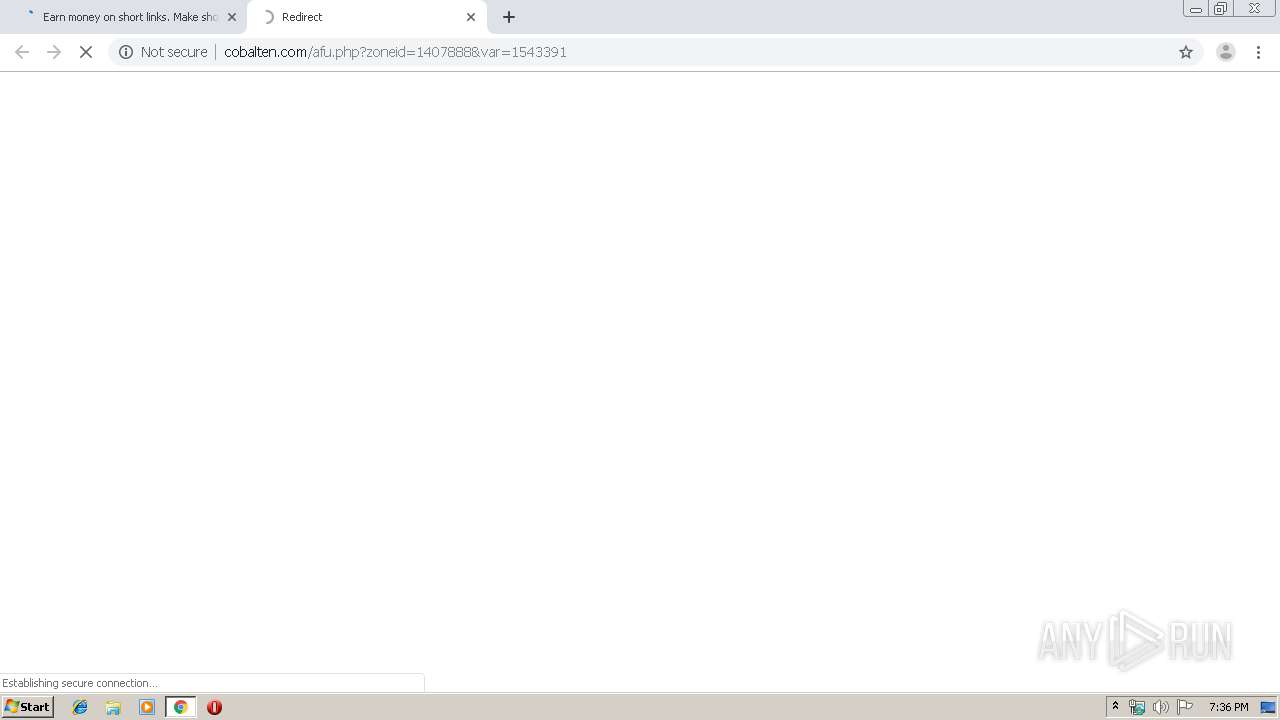
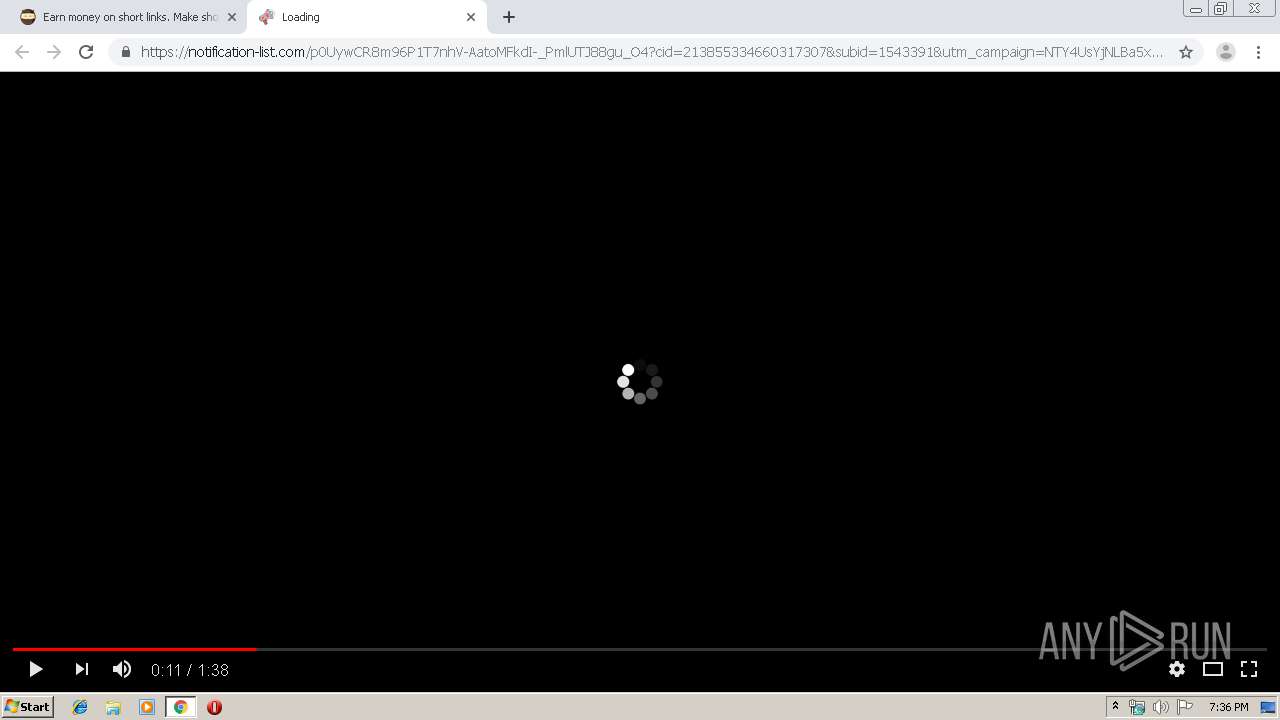
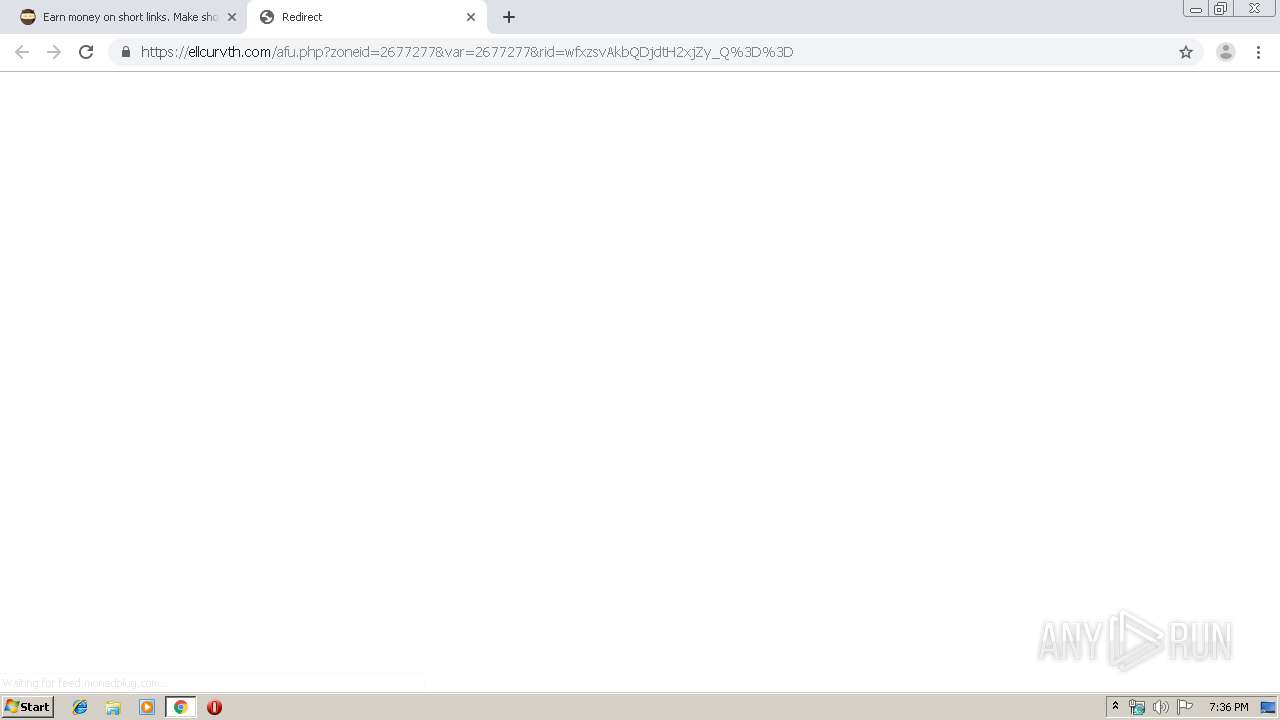
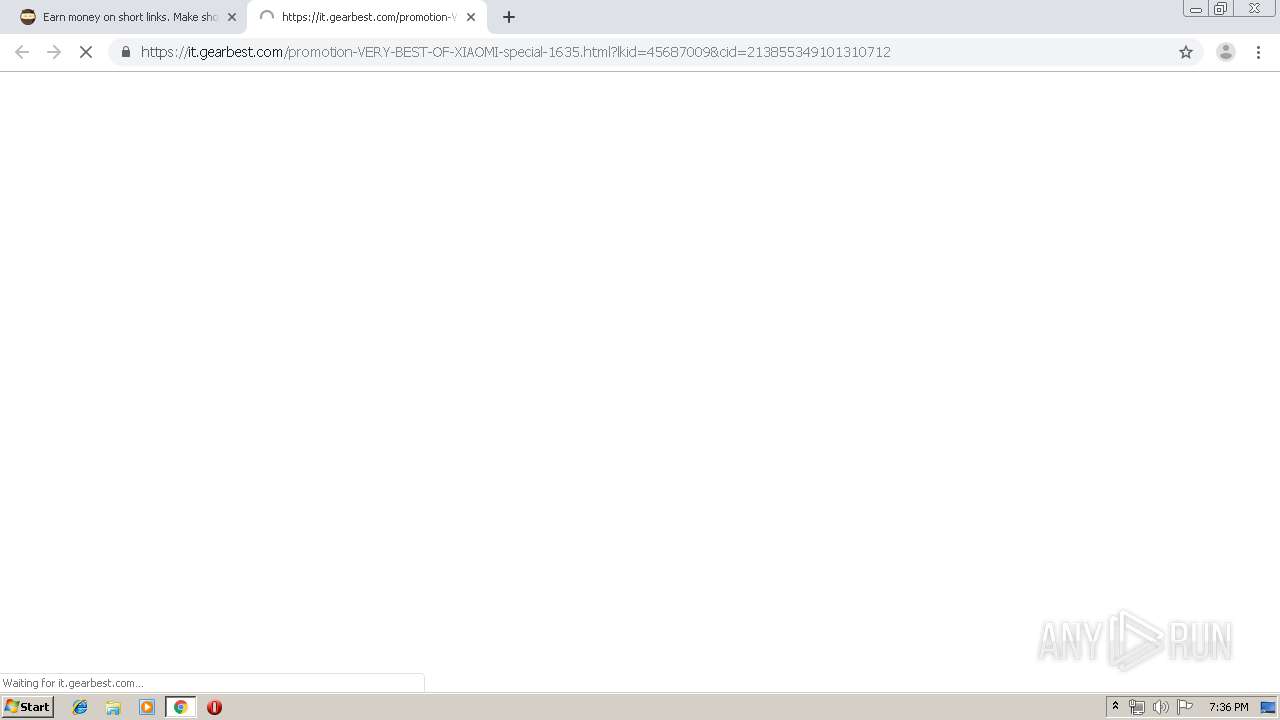
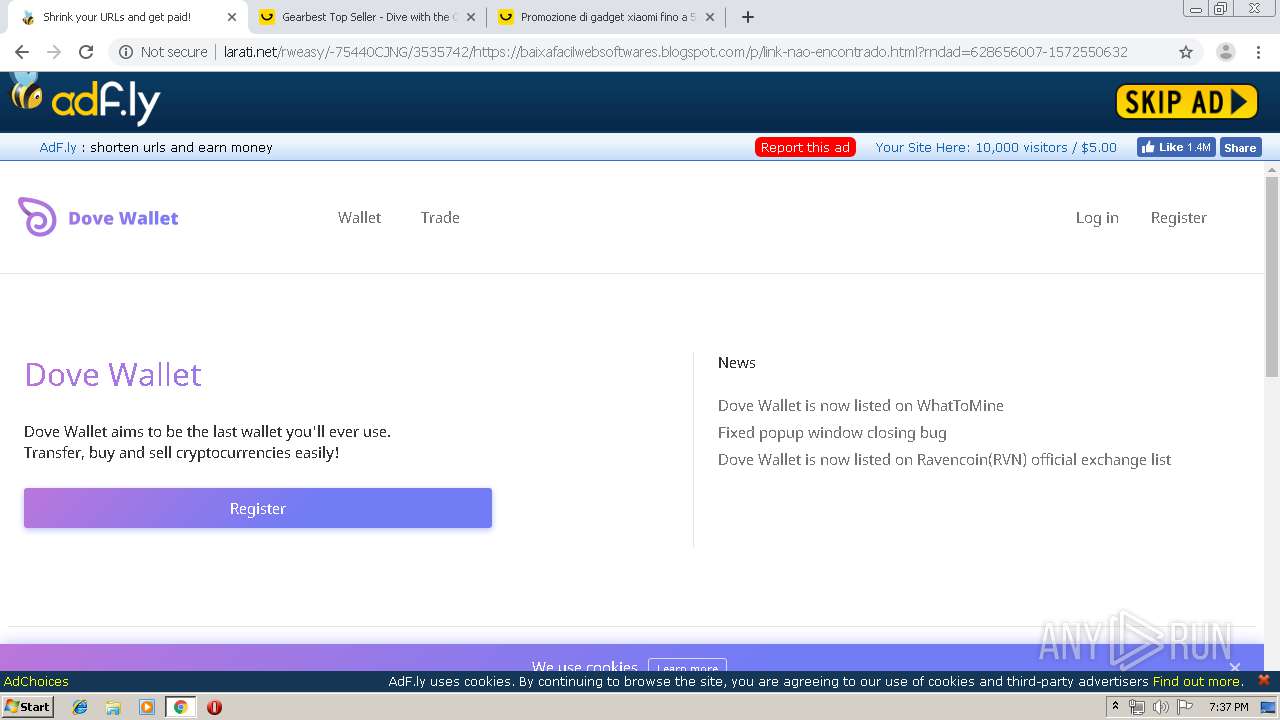
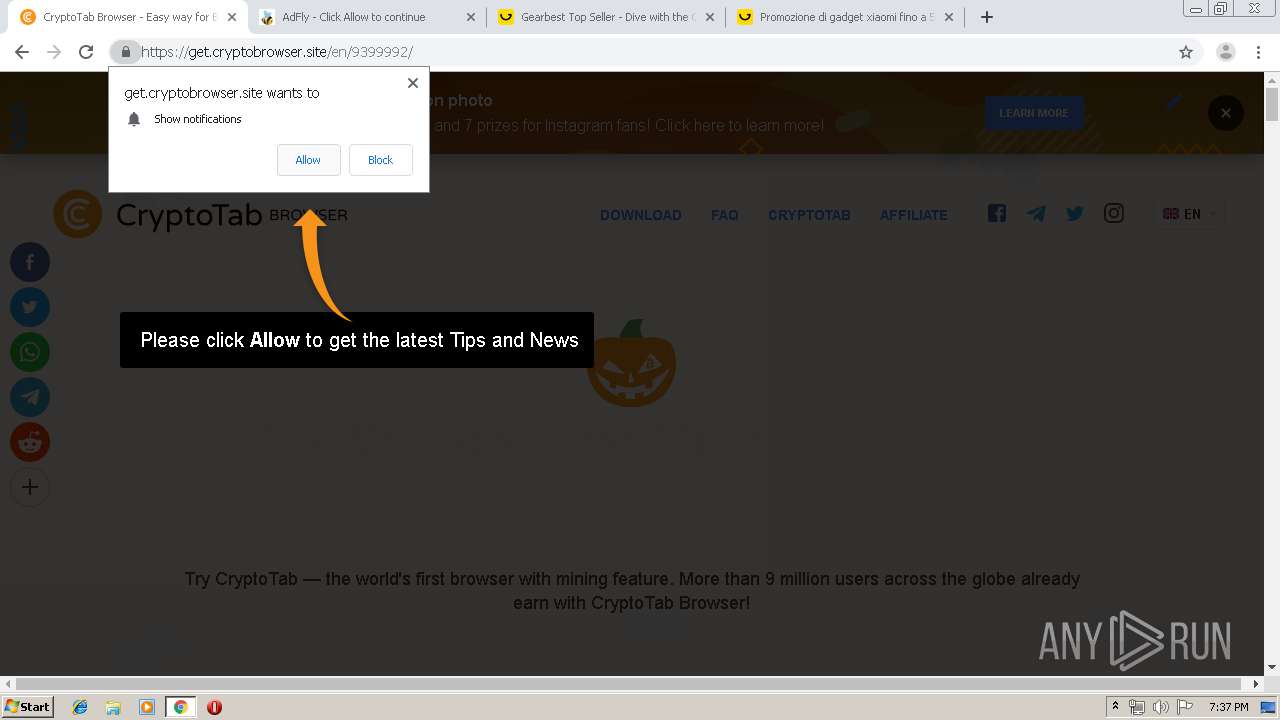
2084 | chrome.exe | GET | 200 | 13.32.222.153:80 | http://d3ud741uvs727m.cloudfront.net/?vudud=716233 | US | compressed | 33.3 Kb | whitelisted |
2084 | chrome.exe | GET | 200 | 185.66.120.52:80 | http://festyy.com/bundles/smeweb/js/xvideos.js | PL | text | 6.13 Kb | suspicious |
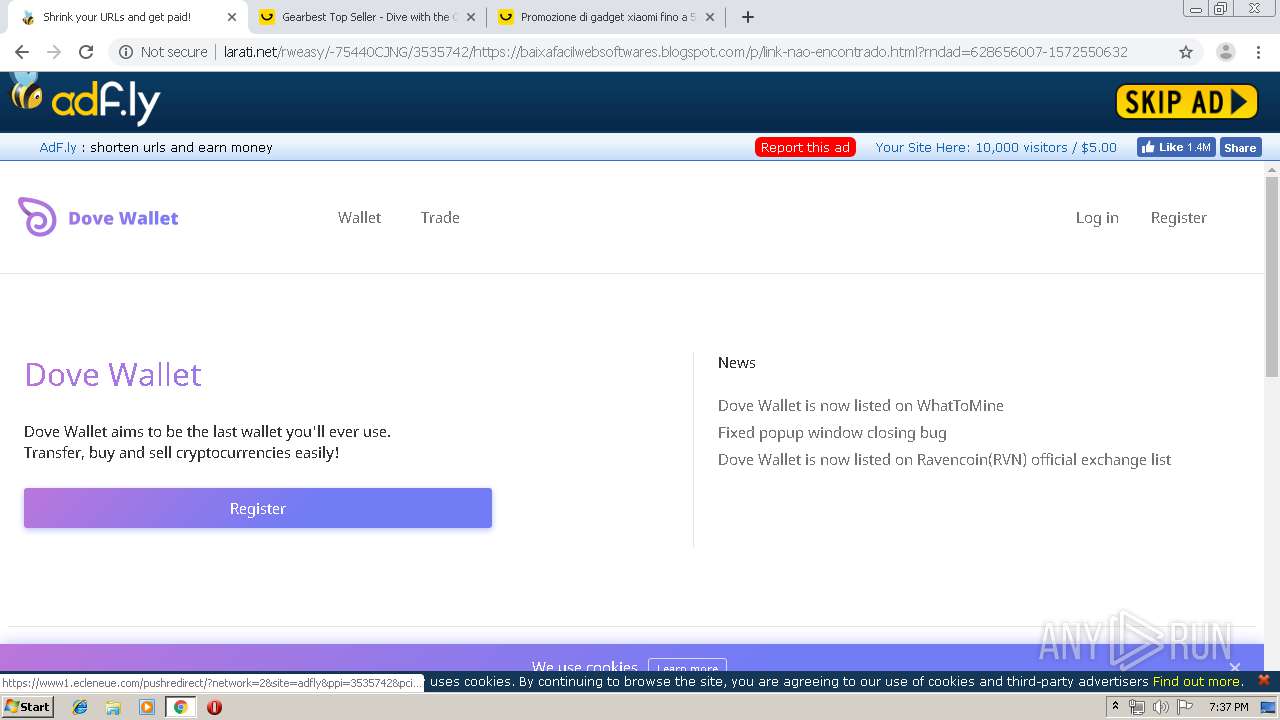
2084 | chrome.exe | GET | 200 | 78.140.188.190:80 | http://static.sh.st/js/packed/interstitial-page.js?2019-04-23.0 | NL | text | 24.6 Kb | unknown |
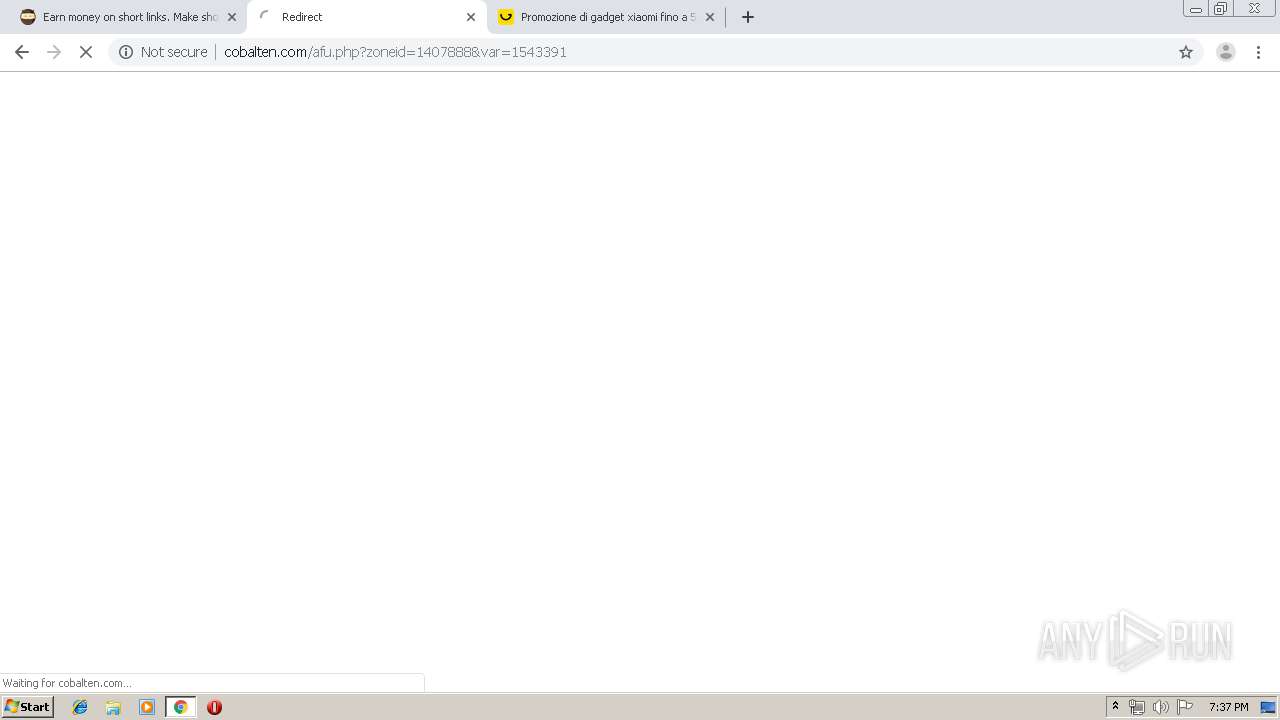
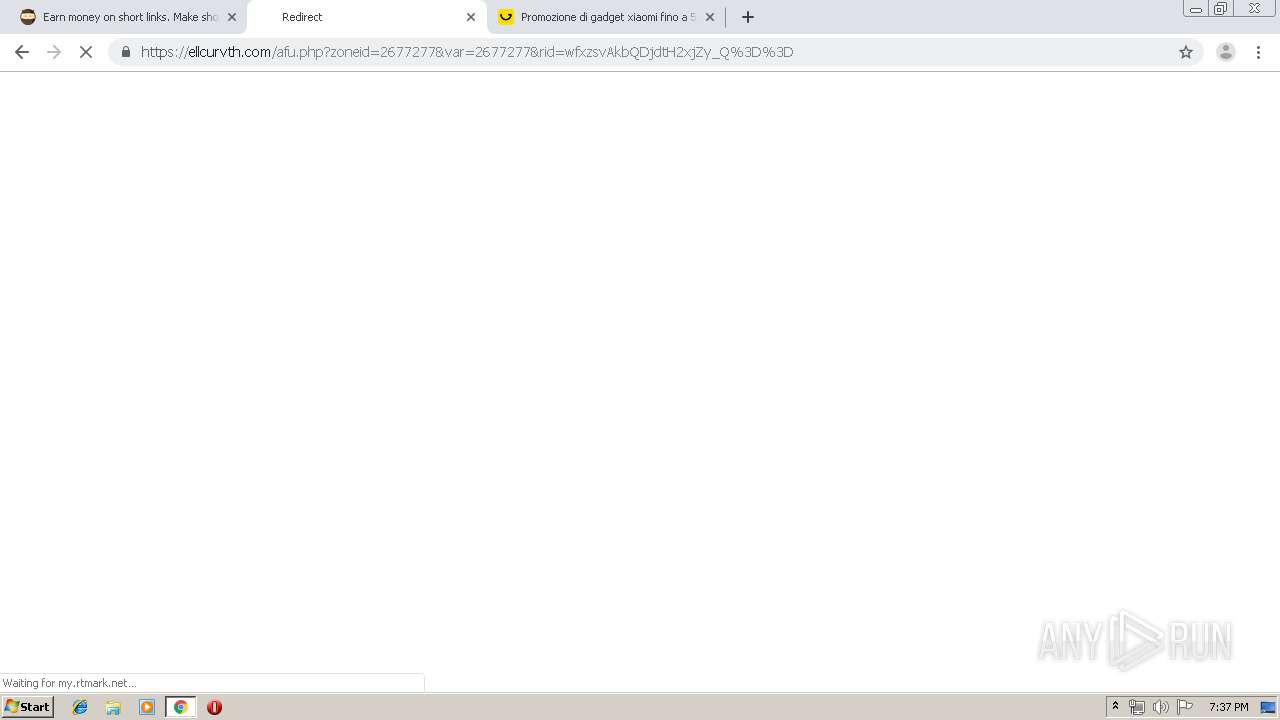
2084 | chrome.exe | GET | 200 | 206.54.165.217:80 | http://cobalten.com/apu.php?zoneid=1543391 | NL | text | 26.5 Kb | malicious |
2084 | chrome.exe | GET | 200 | 172.217.23.97:80 | http://themes.googleusercontent.com/static/fonts/raleway/v6/PKCRbVvRfd5n7BTjtGiFZBsxEYwM7FgeyaSgU71cLG0.woff | US | woff | 41.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2084 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 185.66.120.52:80 | festyy.com | Grey Wizard Sp. z o.o. | PL | malicious |
2084 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 172.217.21.238:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 172.217.23.97:80 | themes.googleusercontent.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 78.140.191.213:80 | go.onclasrv.com | Webzilla B.V. | NL | unknown |
2084 | chrome.exe | 172.217.22.104:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2084 | chrome.exe | 35.227.234.224:80 | analytics.shorte.st | — | US | unknown |
2084 | chrome.exe | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
festyy.com |
| suspicious |
accounts.google.com |
| shared |
www.google-analytics.com |
| whitelisted |
themes.googleusercontent.com |
| whitelisted |
shorte.st |
| unknown |
static.shorte.st |
| unknown |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
static.sh.st |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
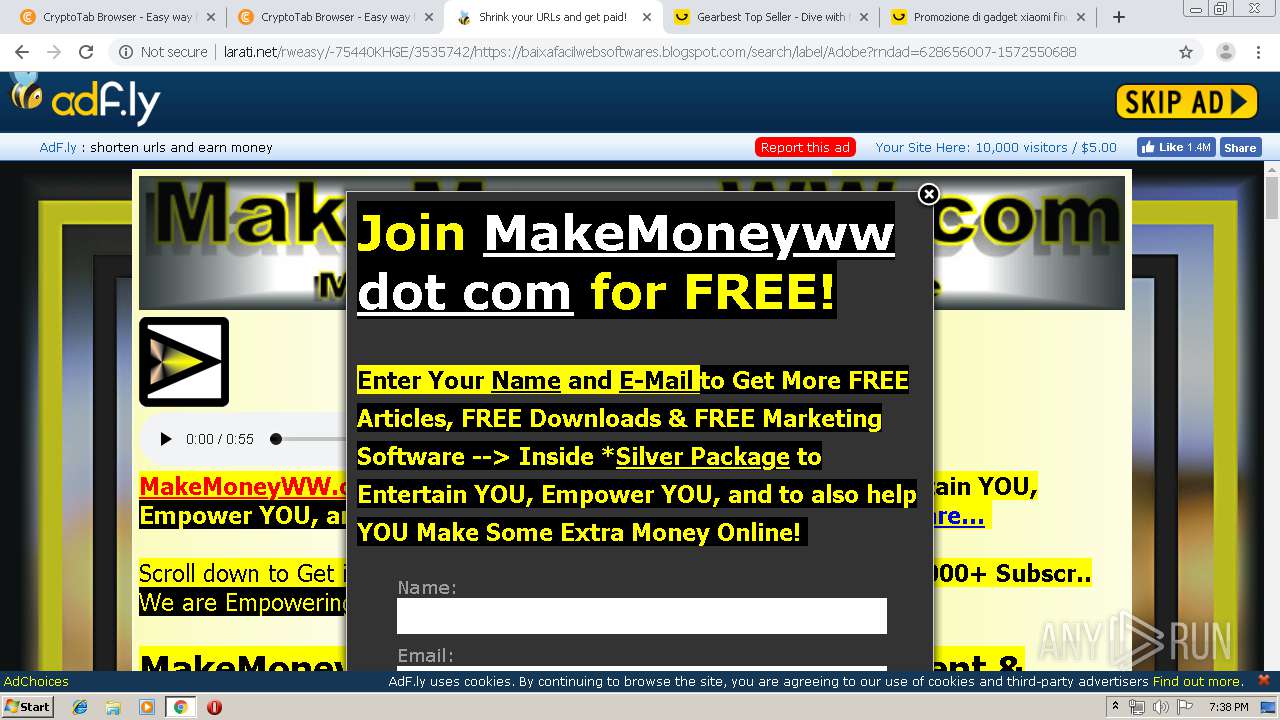
2084 | chrome.exe | Attempted User Privilege Gain | AV POLICY Observed Suspicious JScript serving Adware Inbound |
2084 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |