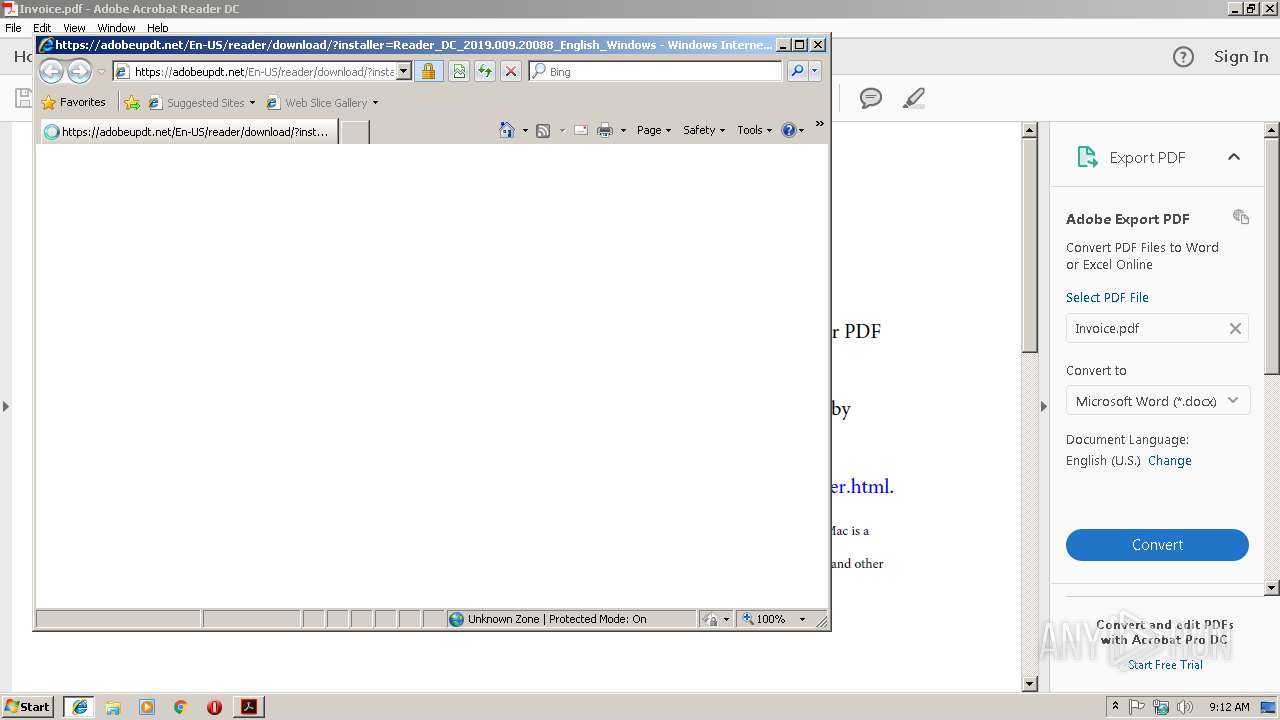
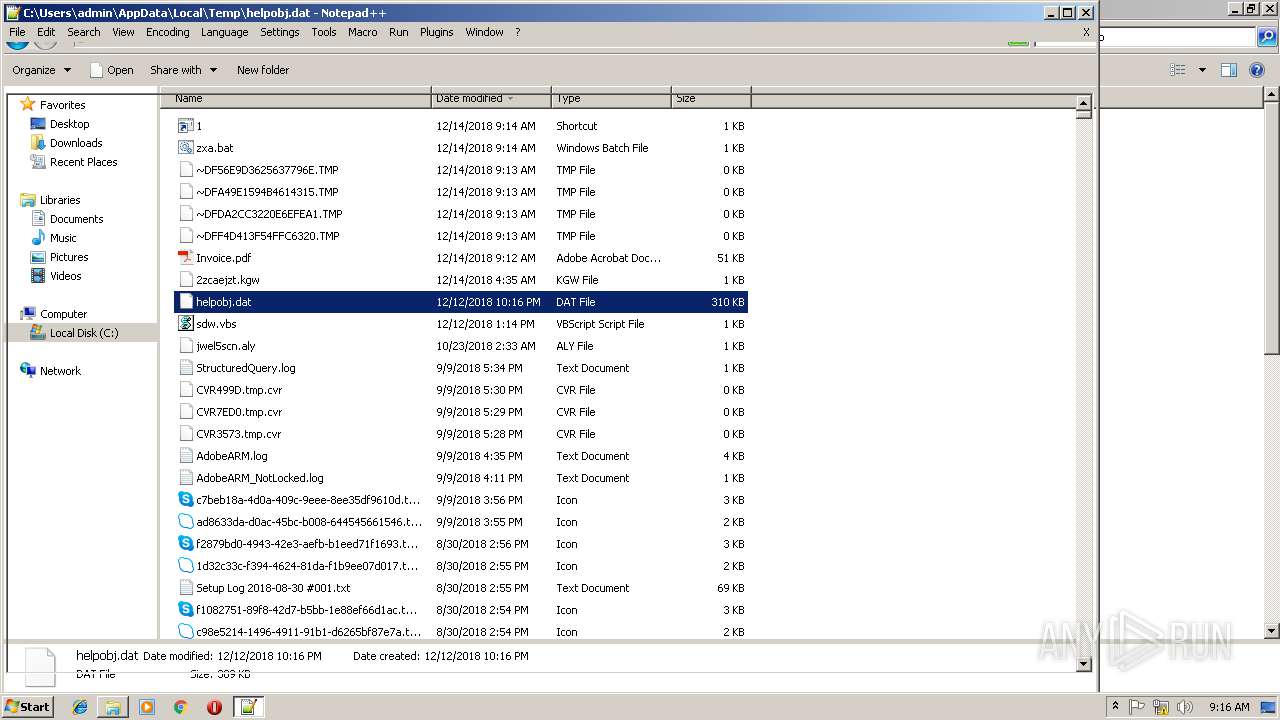
| File name: | Invoice.pdf |
| Full analysis: | https://app.any.run/tasks/83914fb9-2c9e-4ff1-81ee-edd935d1b61f |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 09:12:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.6 |
| MD5: | BF4EA62BB7117B1D5F31873C84A95F5A |
| SHA1: | 3FC7D7F1D47B2AC971D778F580CF64A112127AA9 |
| SHA256: | F4B9219F329803DD45AFD5646351DE456E608DD946830C961EC66C6C25E52CAC |
| SSDEEP: | 768:mnvprrOfgeilCWjlod6NrqH6Q0kKjlod7XXbUZsXo/jlodUNrqH6Q0k9Nfz:kBOCYnENrg6xkzpXbpKNrg6xk9Jz |
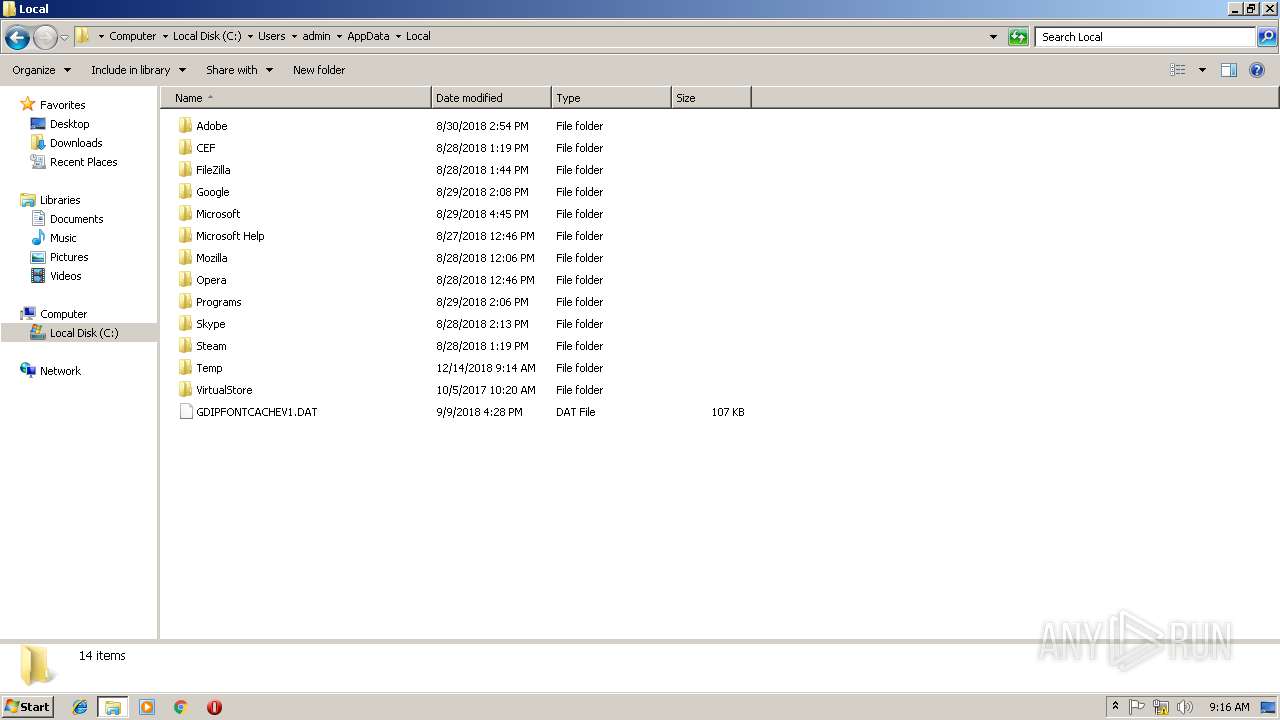
MALICIOUS
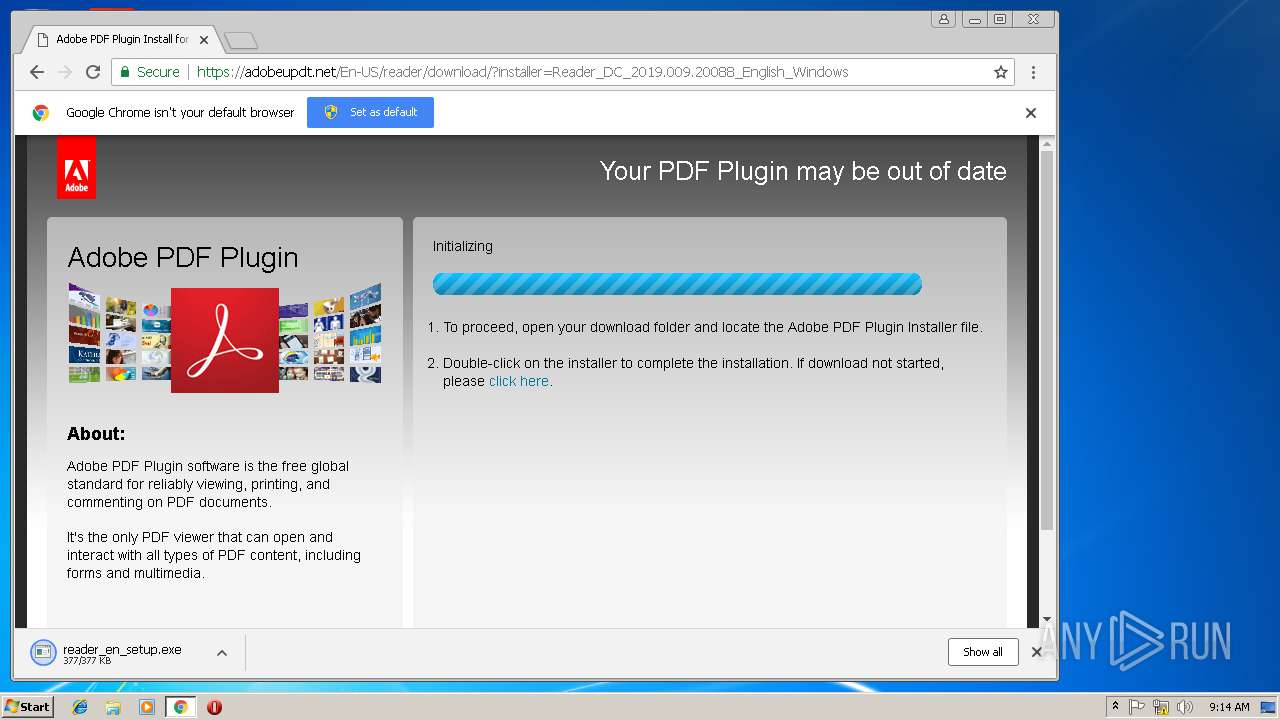
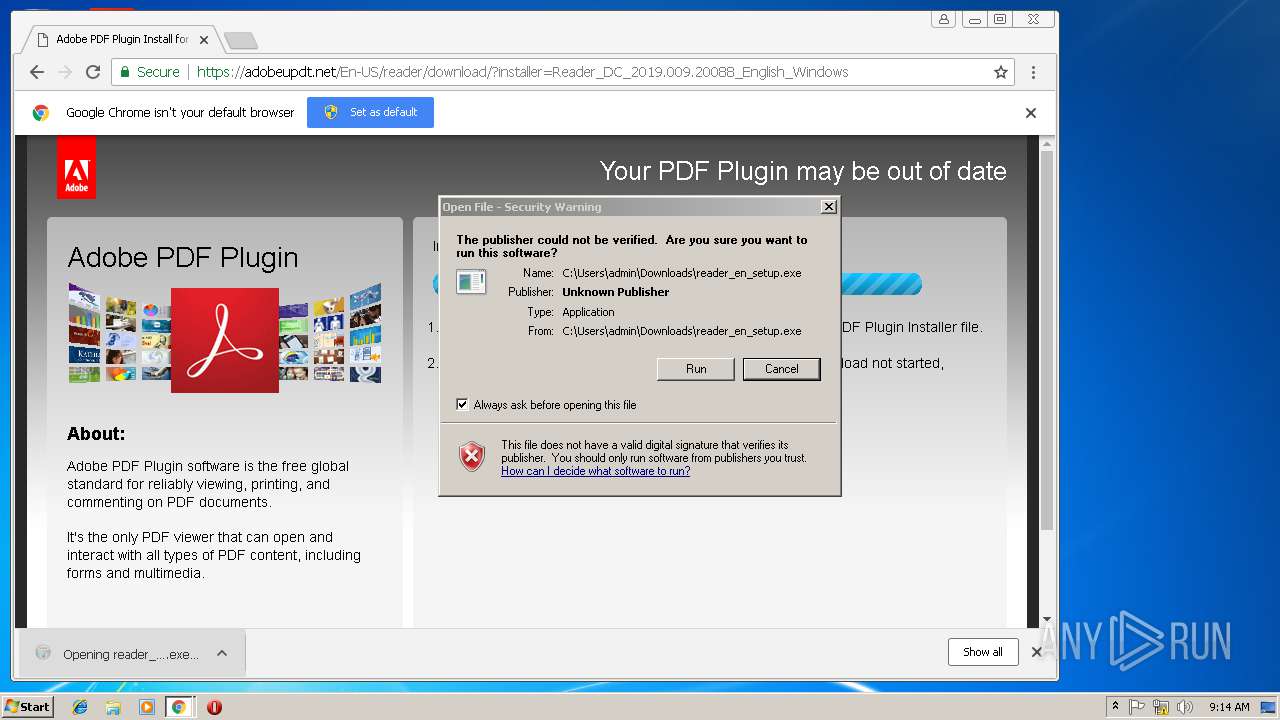
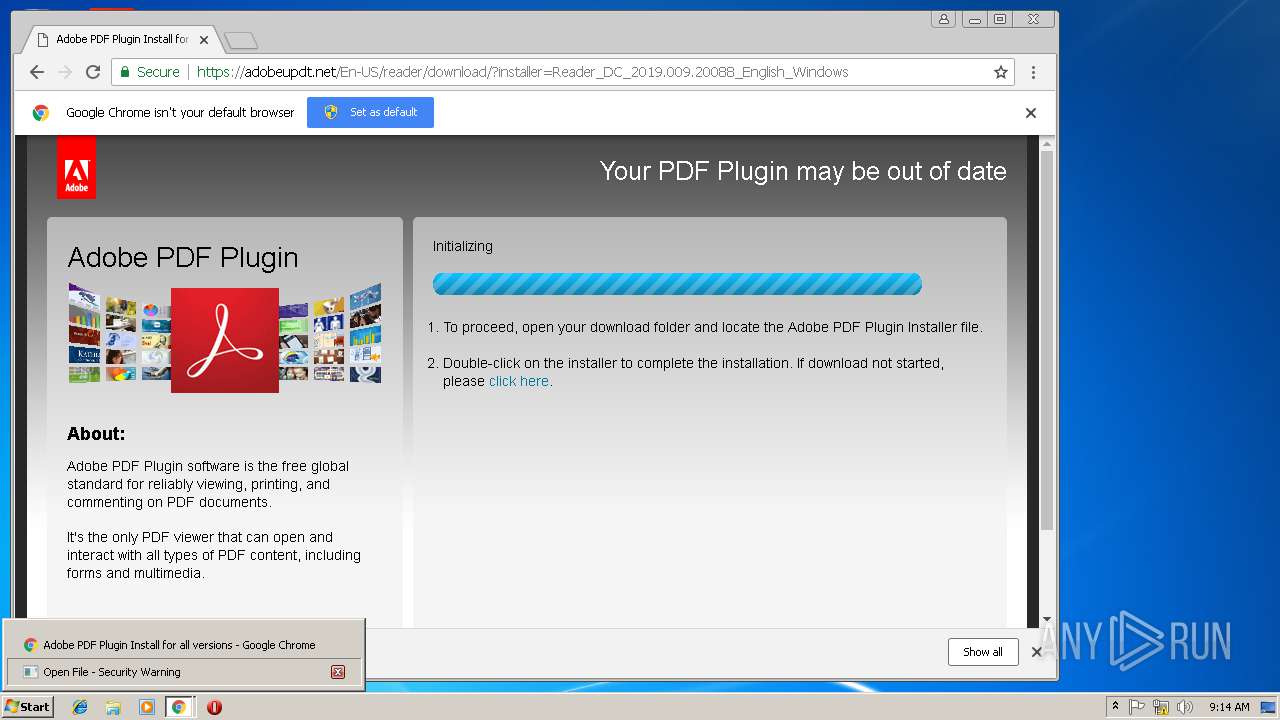
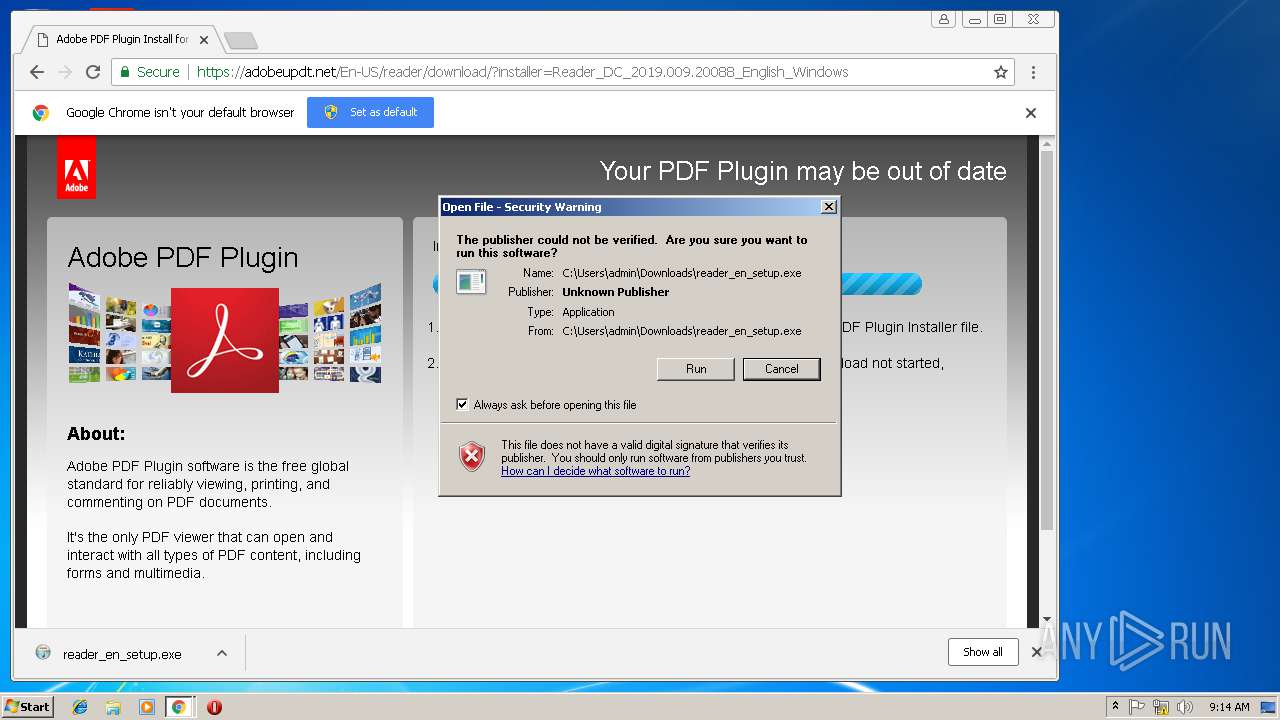
Application was dropped or rewritten from another process
- reader_en_setup.exe (PID: 2436)
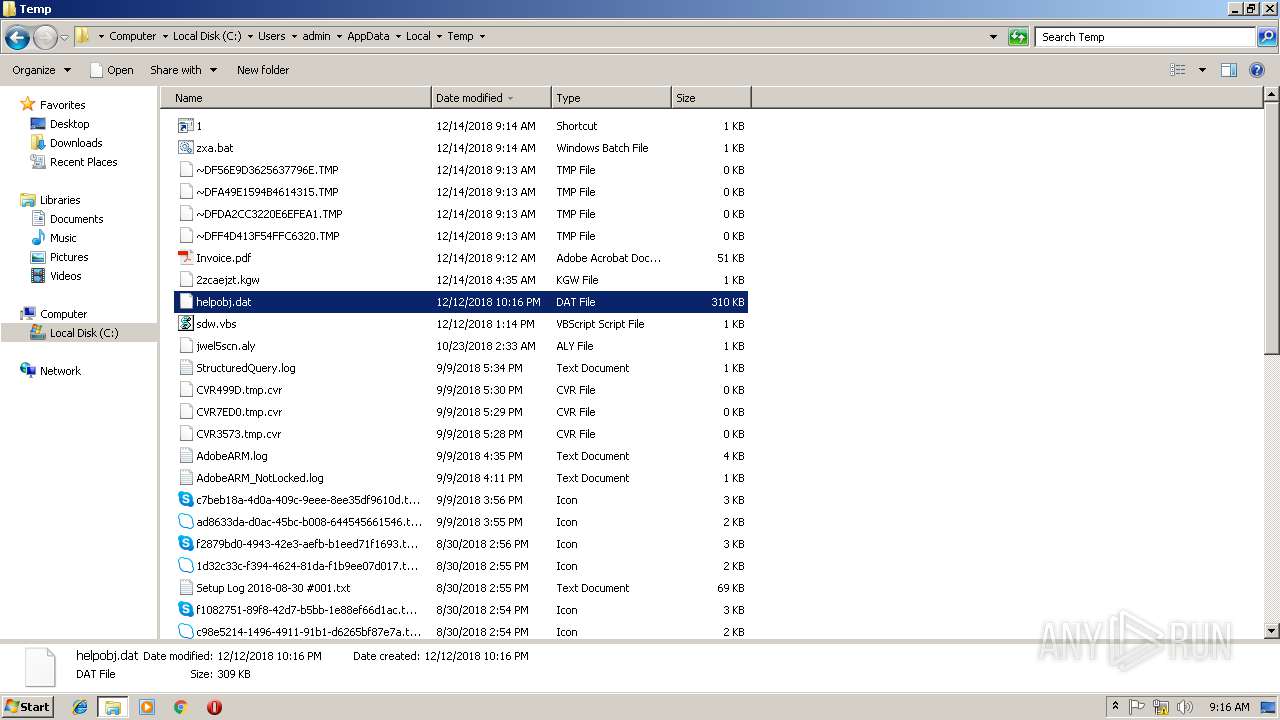
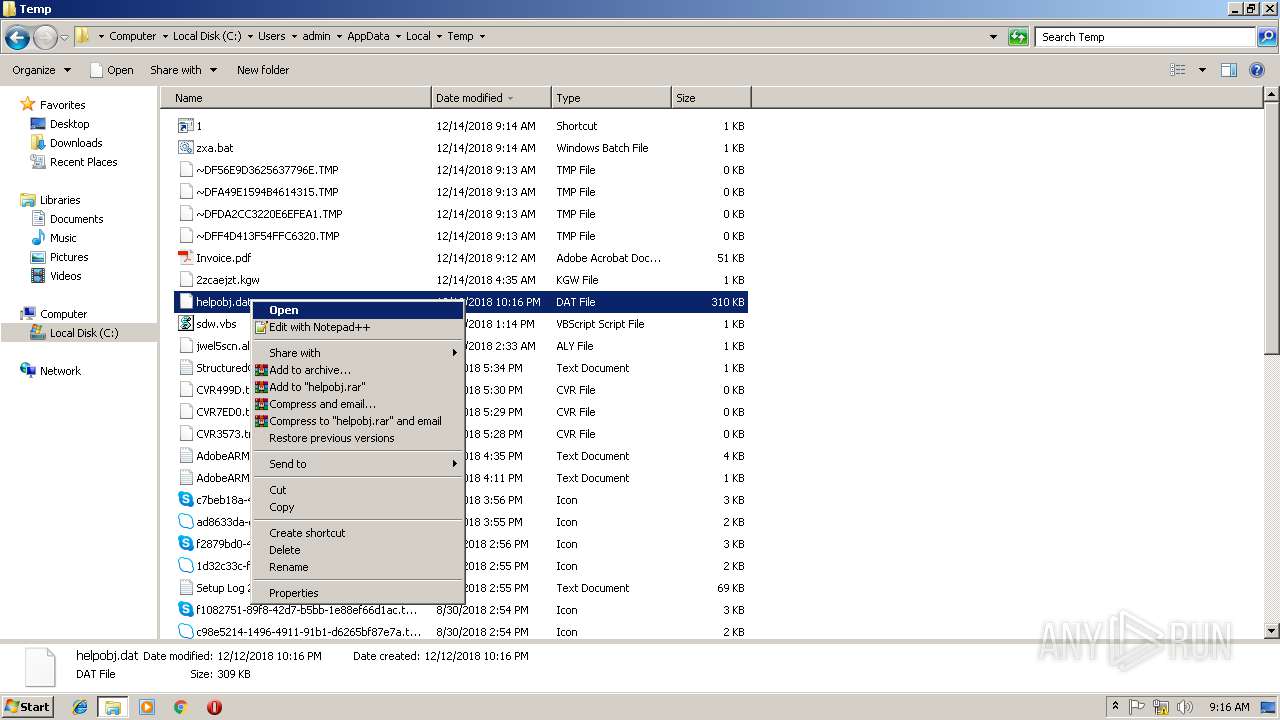
Loads dropped or rewritten executable
- rundll32.exe (PID: 2572)
- rundll32.exe (PID: 3936)
- rundll32.exe (PID: 2312)
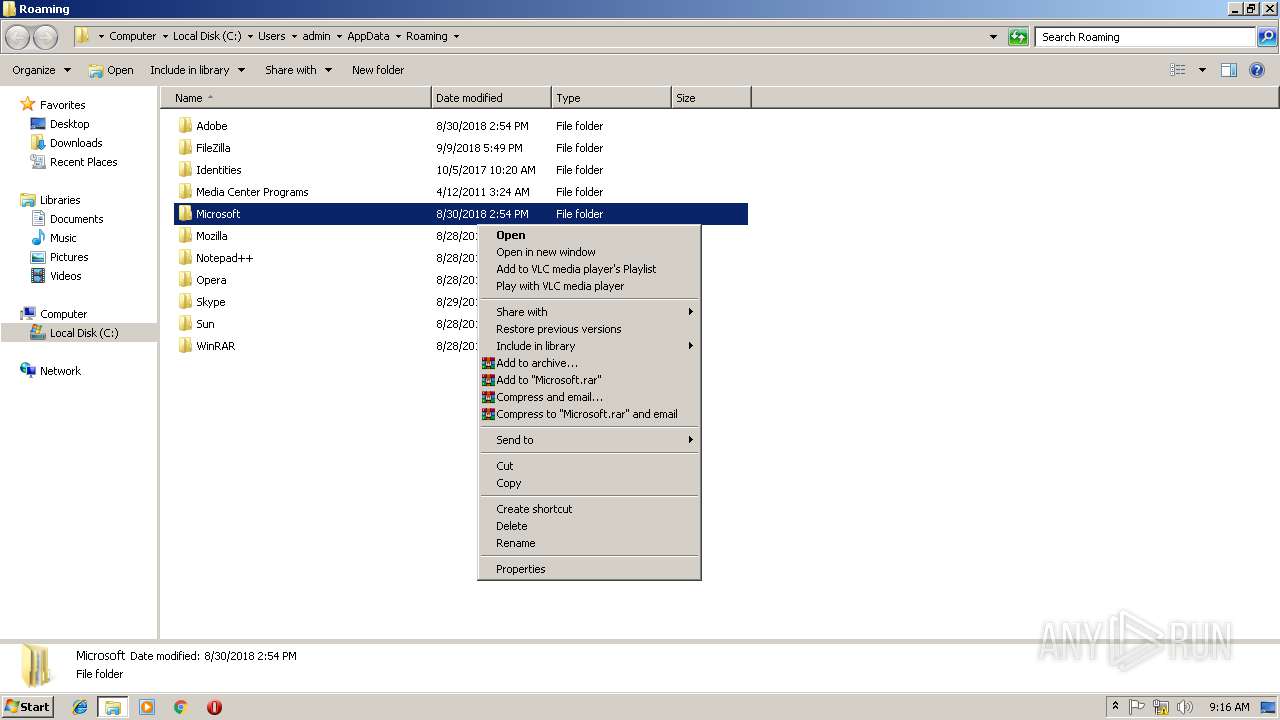
Changes settings of System certificates
- rundll32.exe (PID: 2572)
Starts NET.EXE to view/change users group
- cmd.exe (PID: 3708)
SUSPICIOUS
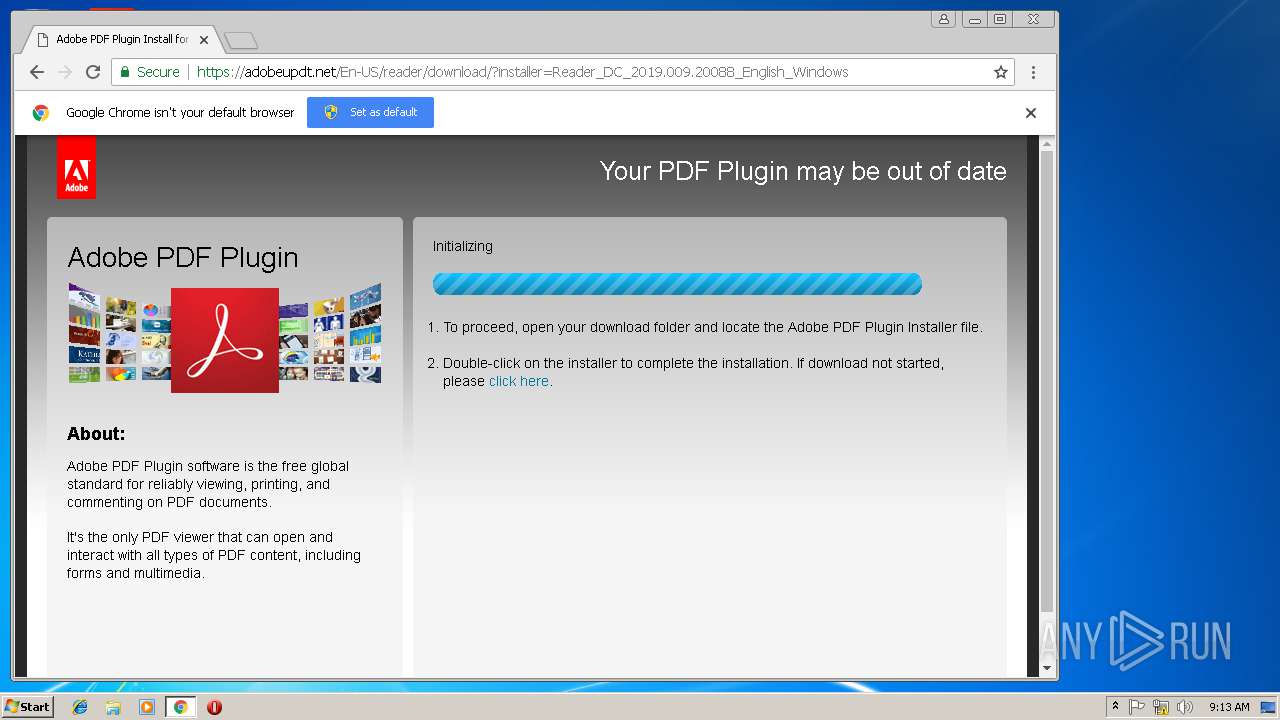
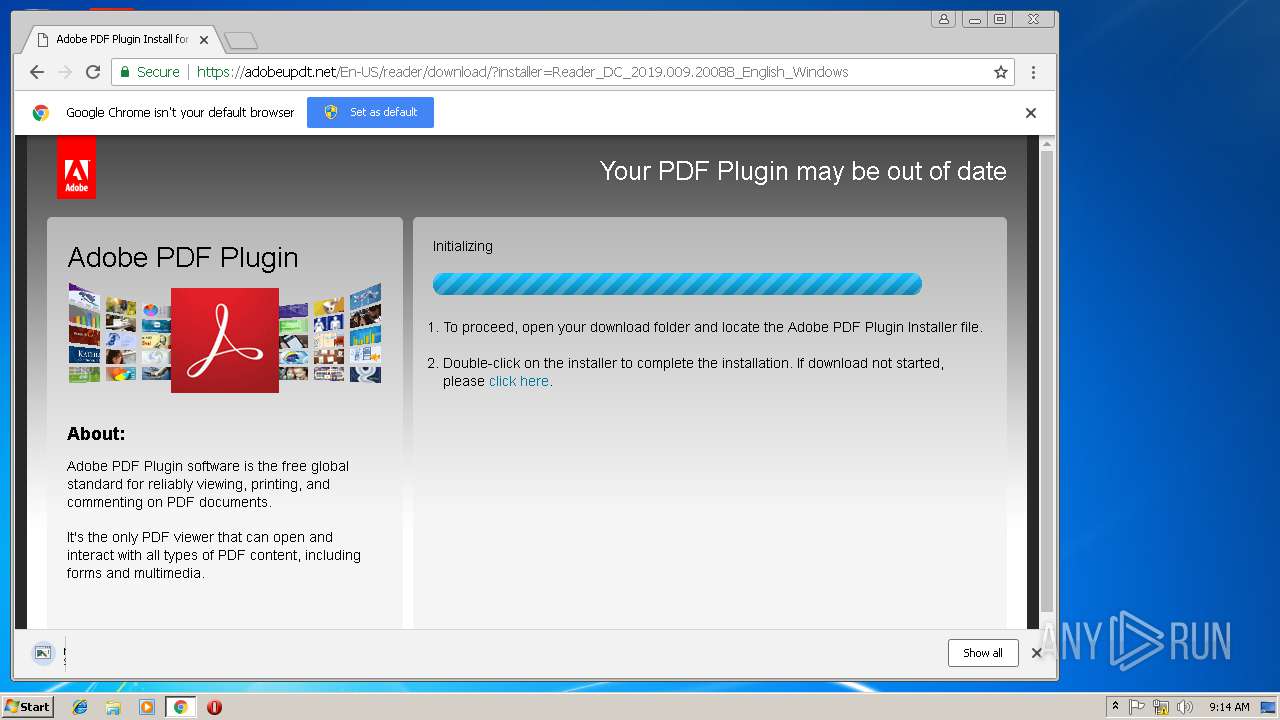
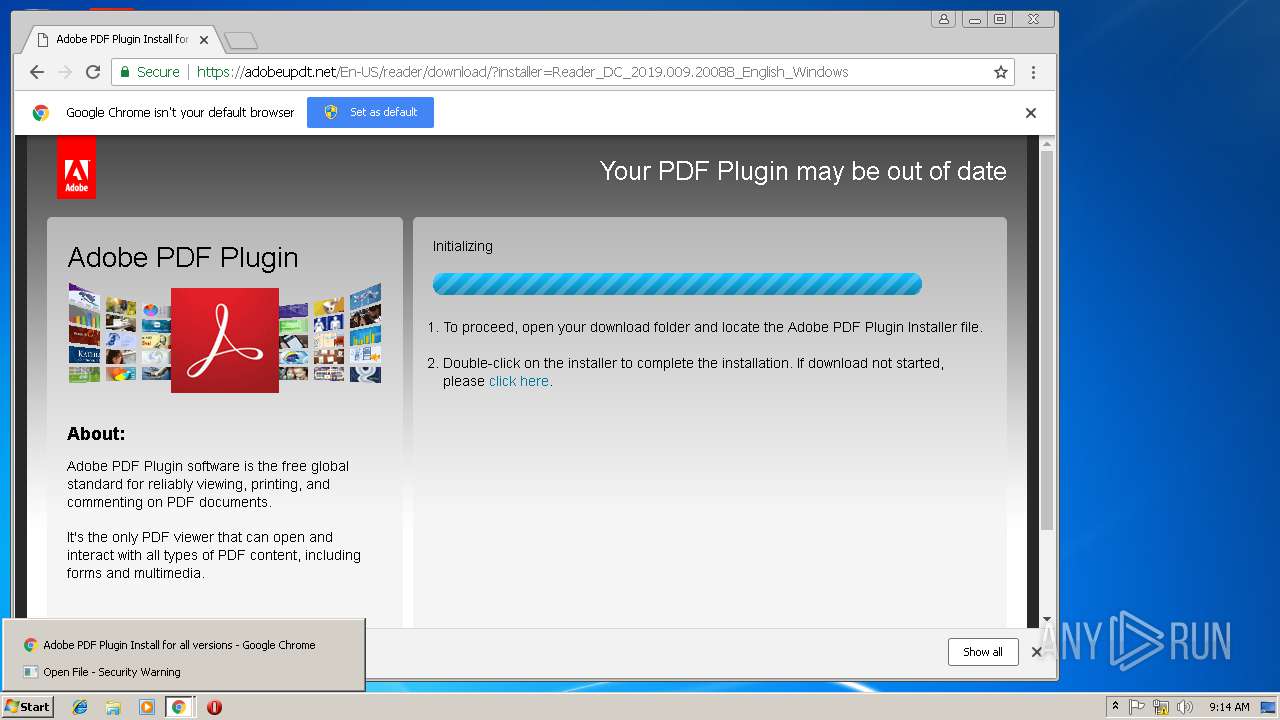
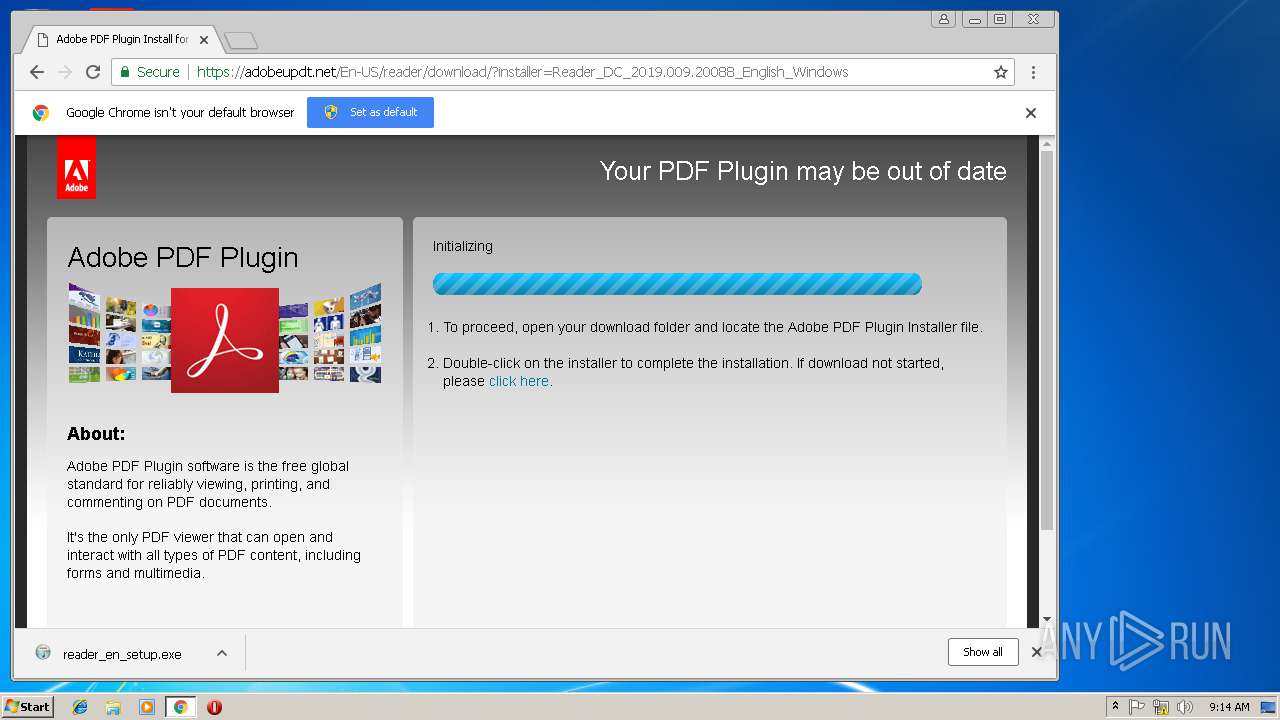
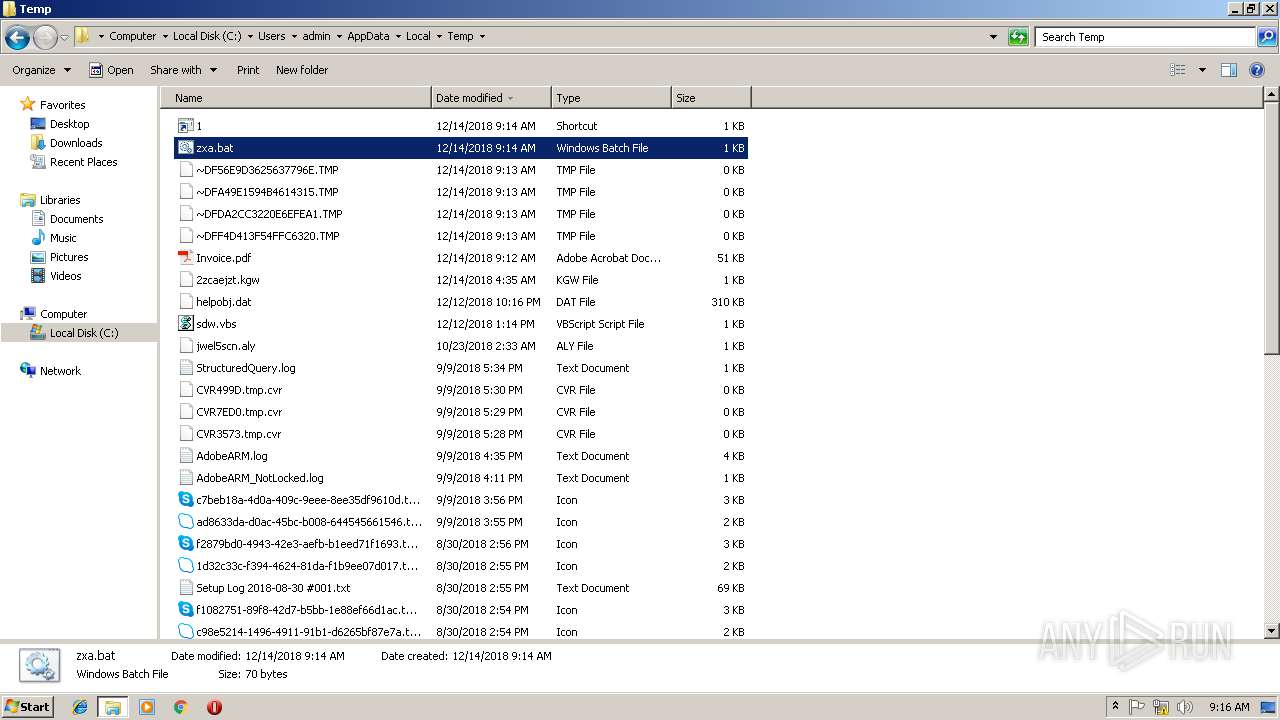
Executable content was dropped or overwritten
- chrome.exe (PID: 3504)
- reader_en_setup.exe (PID: 2436)
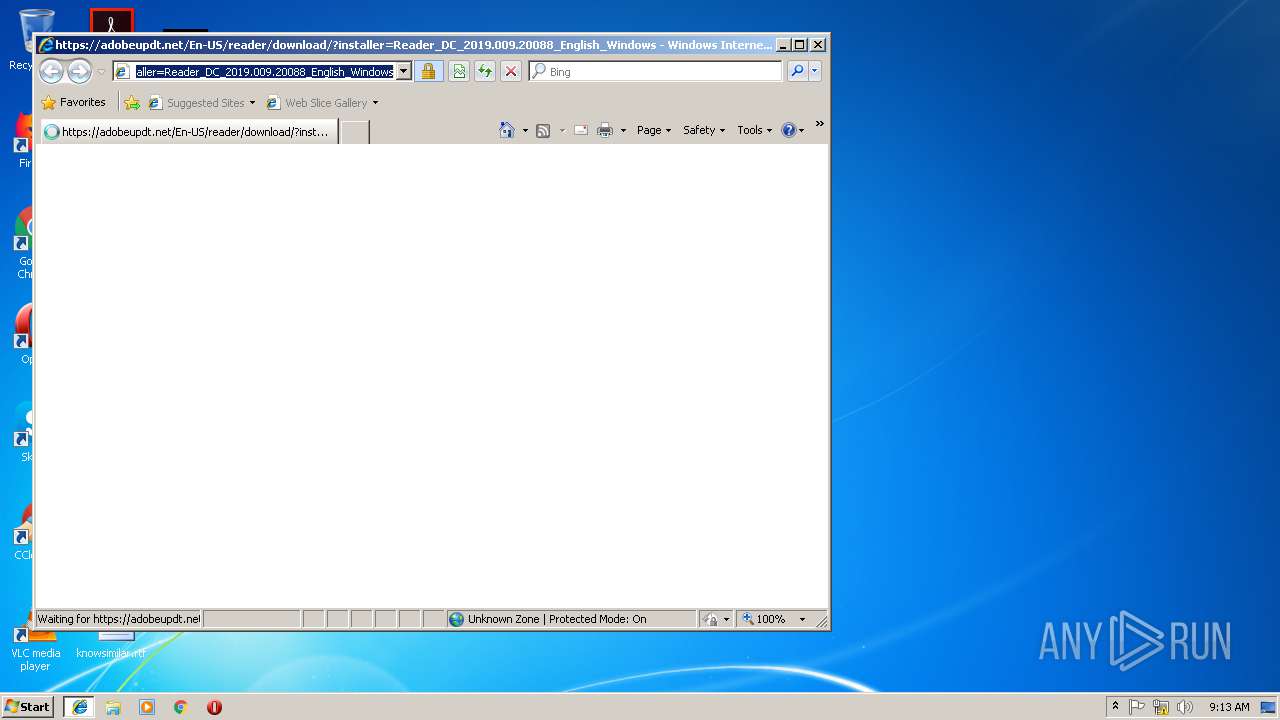
Starts Internet Explorer
- AcroRd32.exe (PID: 3488)
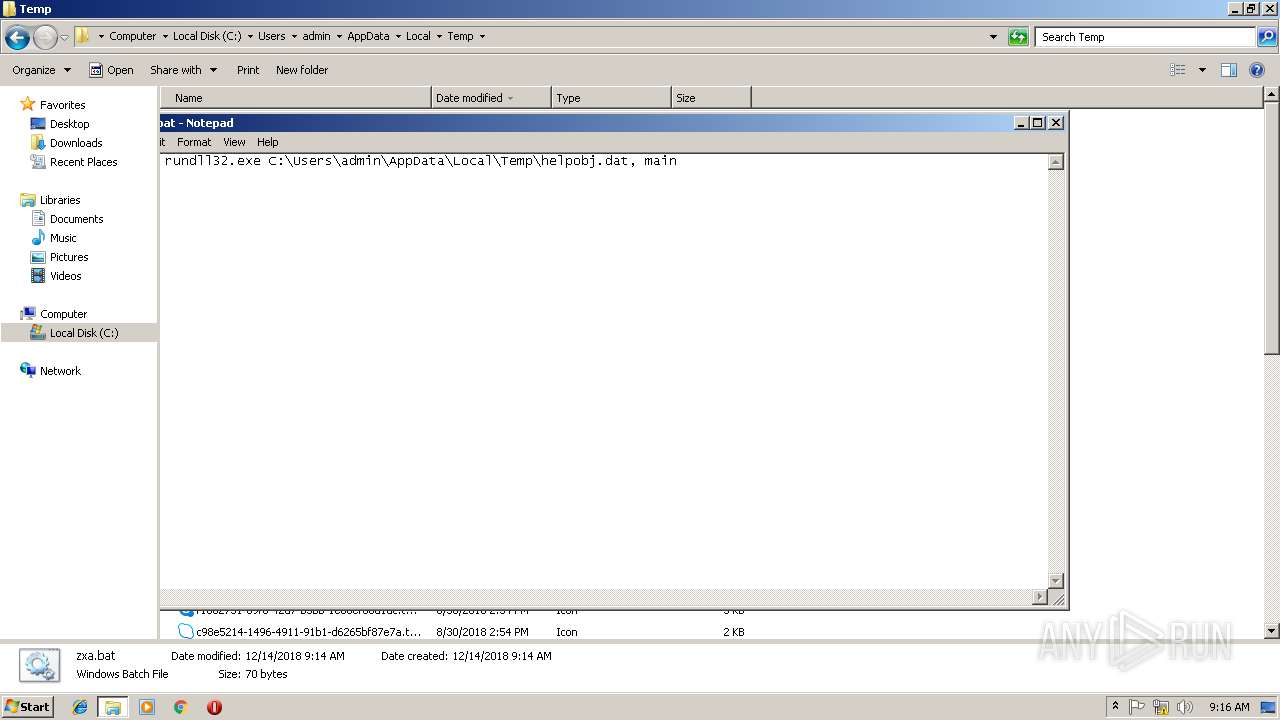
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3688)
- cmd.exe (PID: 1176)
- cmd.exe (PID: 1088)
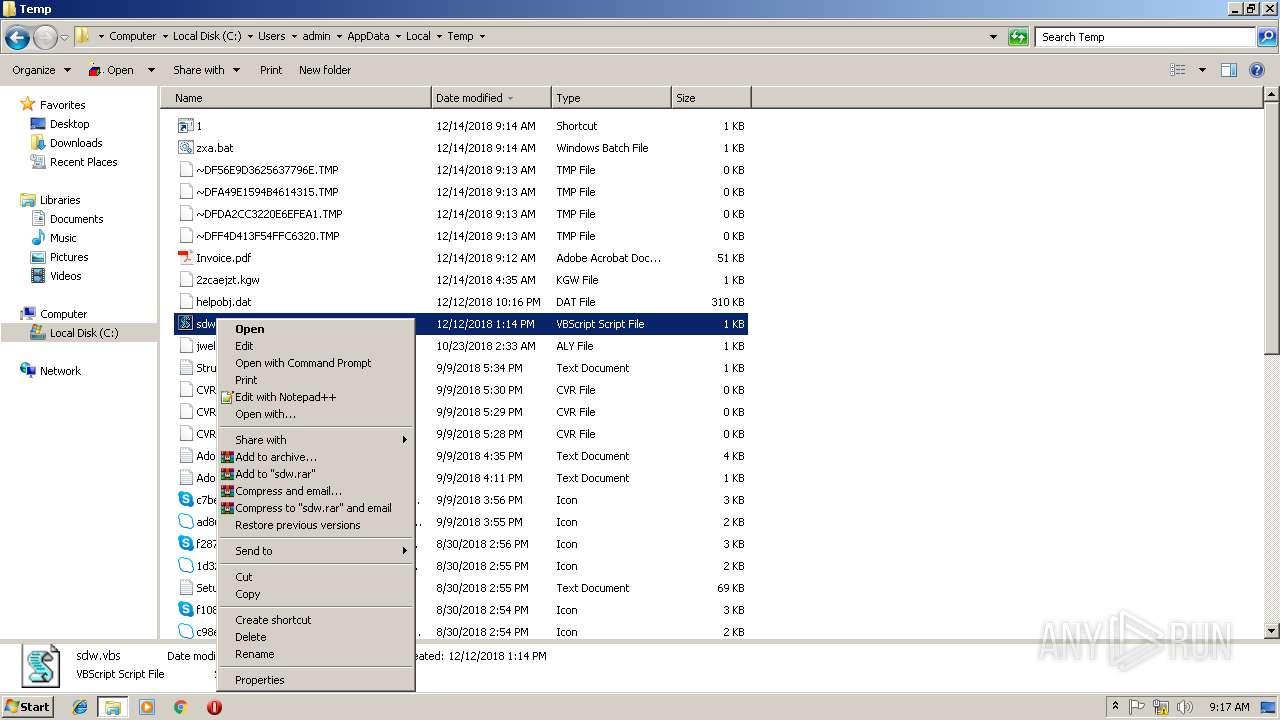
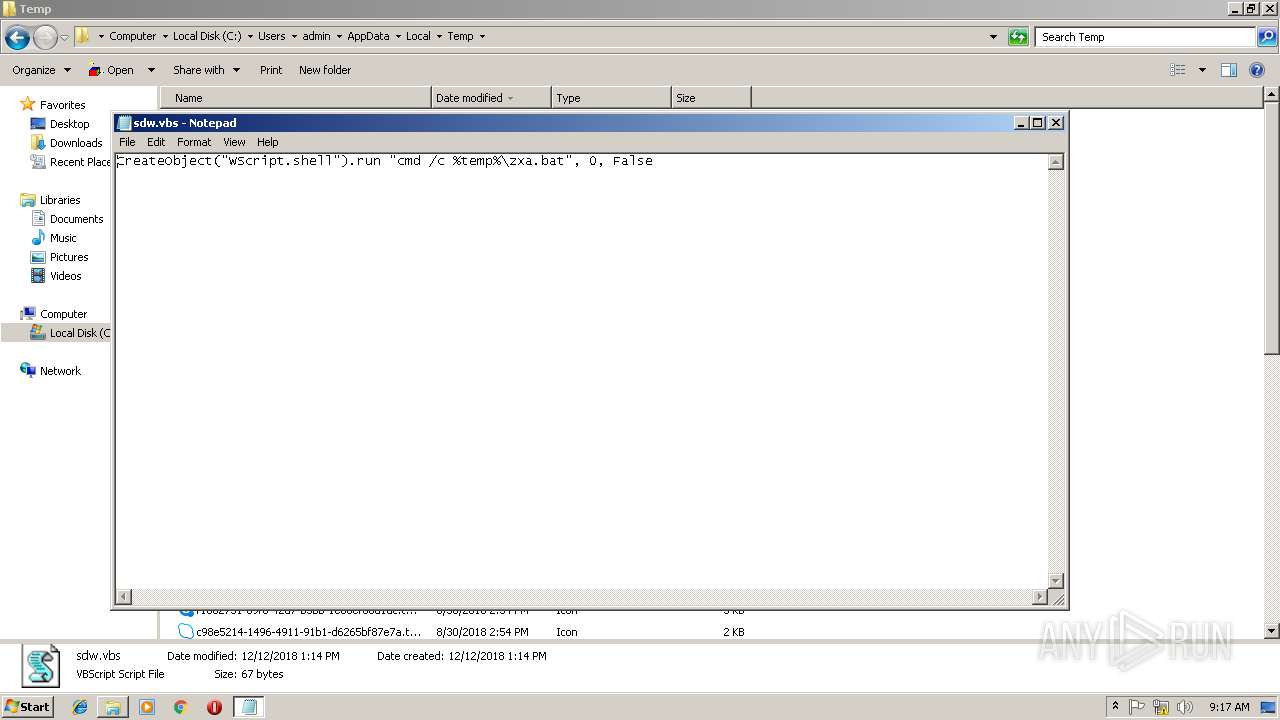
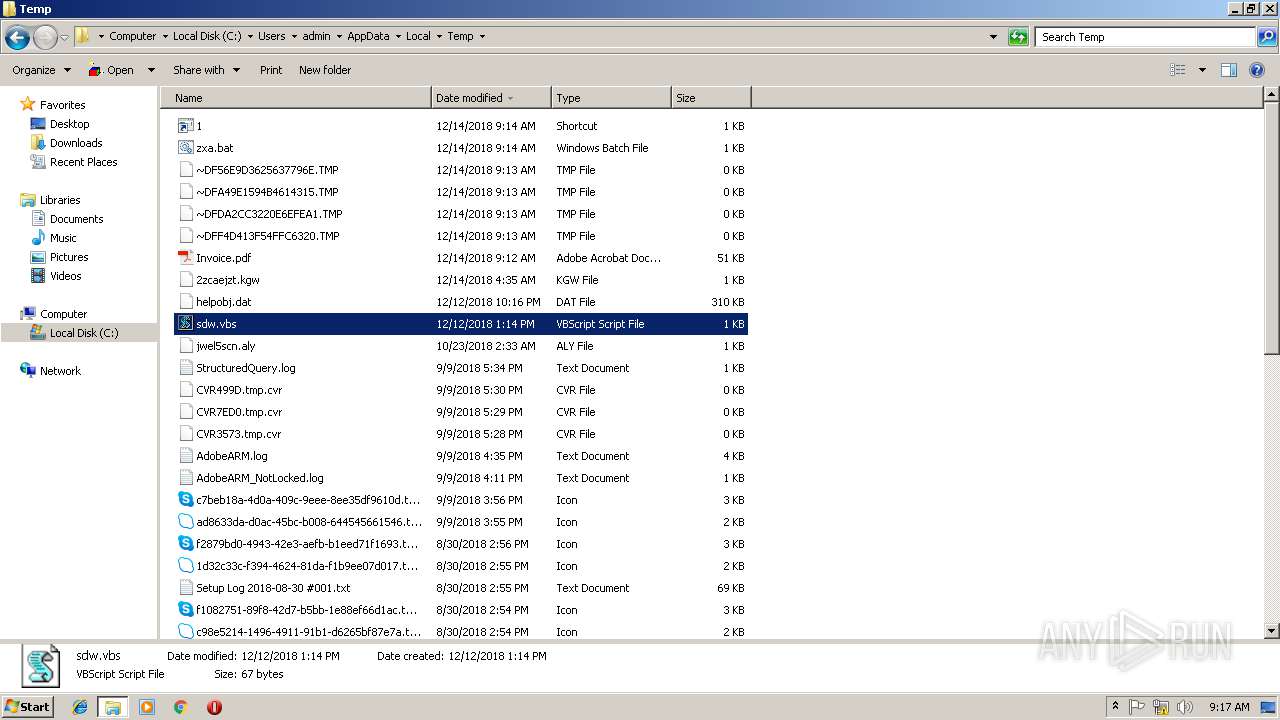
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3868)
- rundll32.exe (PID: 2572)
- WScript.exe (PID: 1148)
- WScript.exe (PID: 2600)
Executes scripts
- reader_en_setup.exe (PID: 2436)
Adds / modifies Windows certificates
- rundll32.exe (PID: 2572)
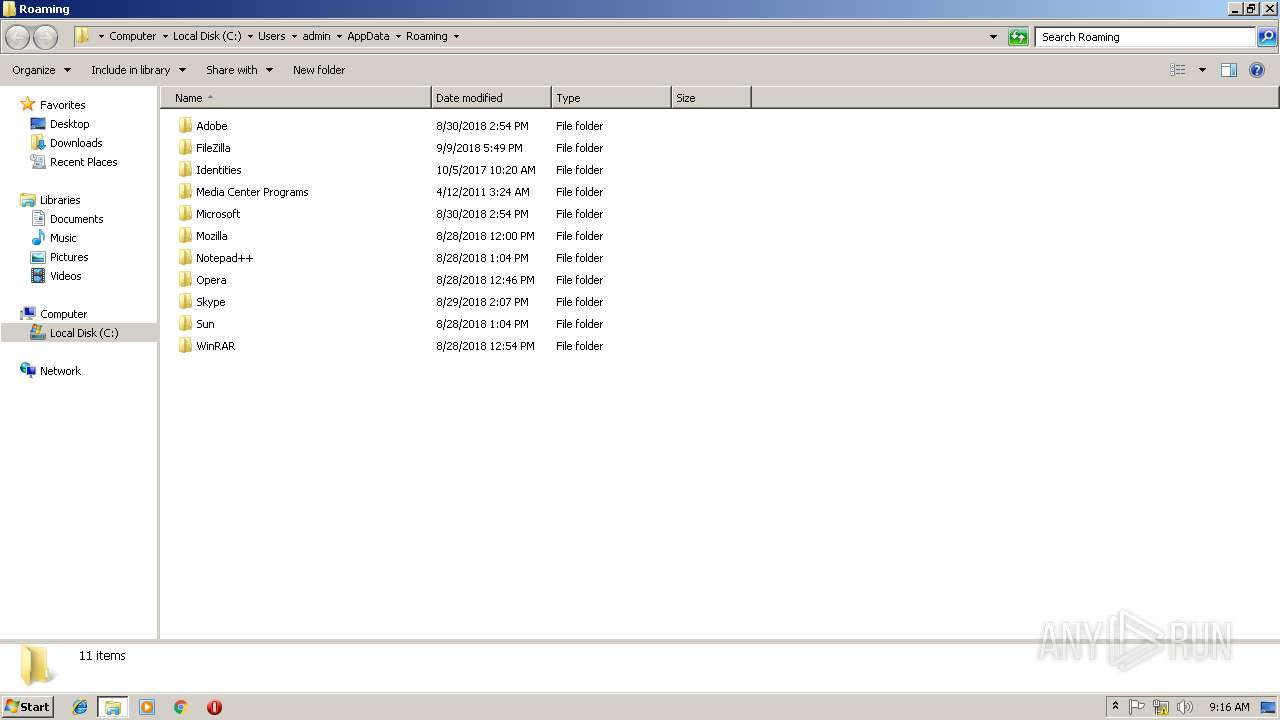
Creates files in the user directory
- notepad++.exe (PID: 2660)
INFO
Creates files in the user directory
- AcroRd32.exe (PID: 3488)
Reads Internet Cache Settings
- iexplore.exe (PID: 2296)
- chrome.exe (PID: 3504)
Reads internet explorer settings
- iexplore.exe (PID: 2296)
Reads settings of System Certificates
- chrome.exe (PID: 3504)
Application launched itself
- RdrCEF.exe (PID: 2992)
- AcroRd32.exe (PID: 3488)
- chrome.exe (PID: 3504)
Changes internet zones settings
- iexplore.exe (PID: 3680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.6 |
|---|---|
| Linearized: | No |
| CreateDate: | 2018:12:04 14:28:02+03:00 |
| Creator: | Adobe Acrobat 11.0 |
| ModifyDate: | 2018:12:13 14:56:04+03:00 |
| Producer: | Модуль Acrobat Web Capture 11.0 |
| Title: | Upgrade to all-new Adobe Reader, free PDF viewer |
| HasXFA: | No |
| PageCount: | 1 |
XMP
| XMPToolkit: | Adobe XMP Core 5.4-c005 78.147326, 2012/08/23-13:03:03 |
|---|---|
| ModifyDate: | 2018:12:13 14:56:04+03:00 |
| CreateDate: | 2018:12:04 14:28:02+03:00 |
| MetadataDate: | 2018:12:13 14:56:04+03:00 |
| CreatorTool: | Adobe Acrobat 11.0 |
| Format: | application/pdf |
| Title: | Upgrade to all-new Adobe Reader, free PDF viewer |
| DocumentID: | uuid:85bcf508-c8f1-4cc2-8b3b-bb8796397931 |
| InstanceID: | uuid:b005d623-74a1-4789-9306-60fdbc4f0a56 |
| Producer: | Модуль Acrobat Web Capture 11.0 |
Total processes
74
Monitored processes
34
Malicious processes
3
Suspicious processes
3
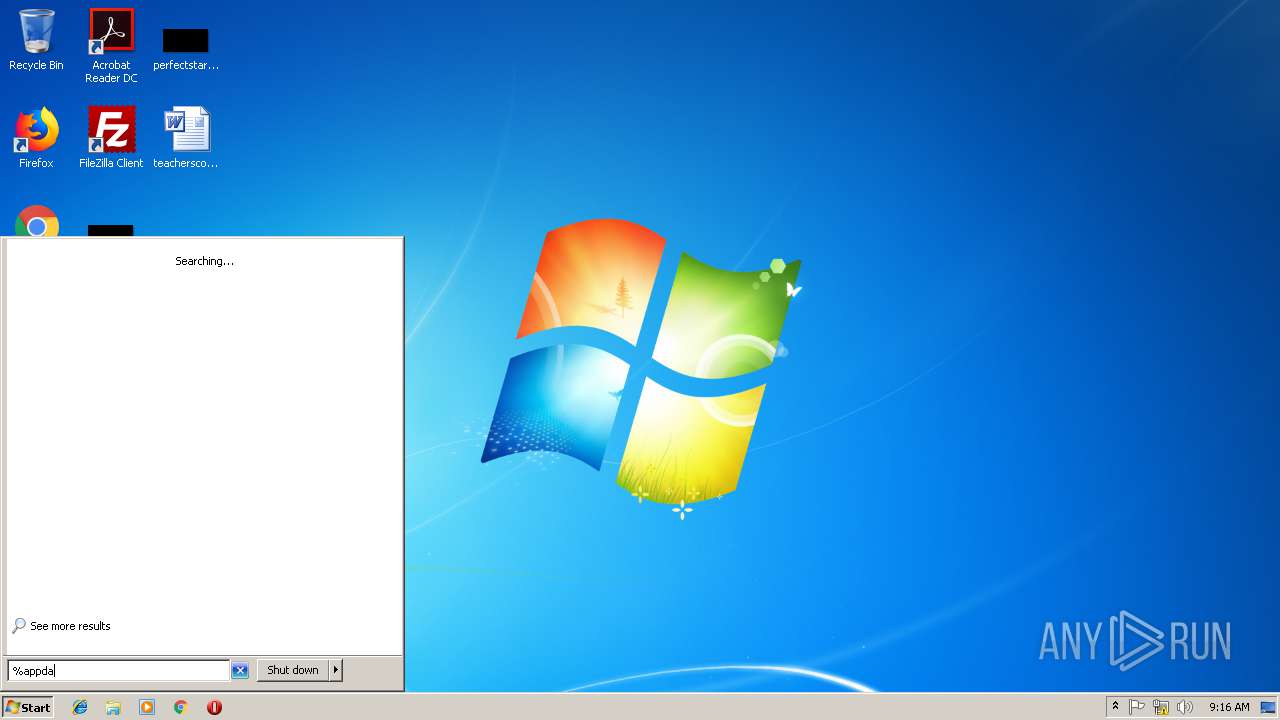
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,18102336394523641768,10761462838020187869,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3D6D1FF904C69E28BB17315512AB4108 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3D6D1FF904C69E28BB17315512AB4108 --renderer-client-id=7 --mojo-platform-channel-handle=3804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
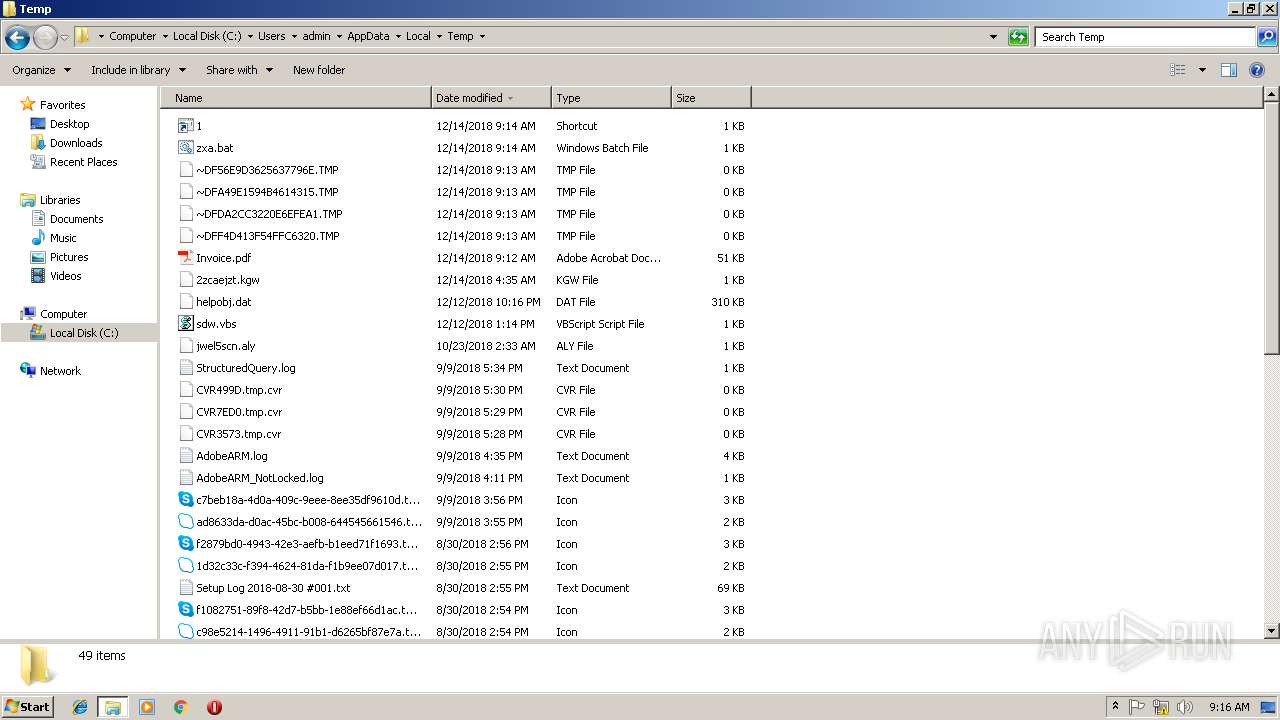
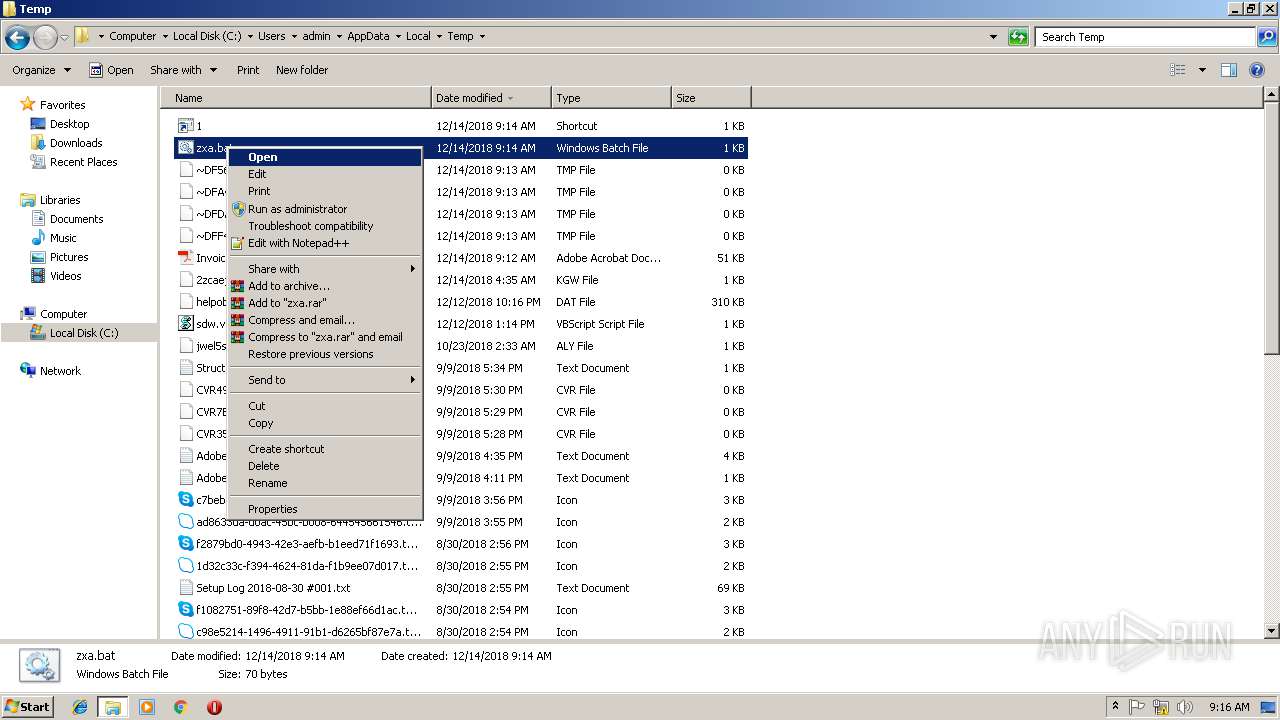
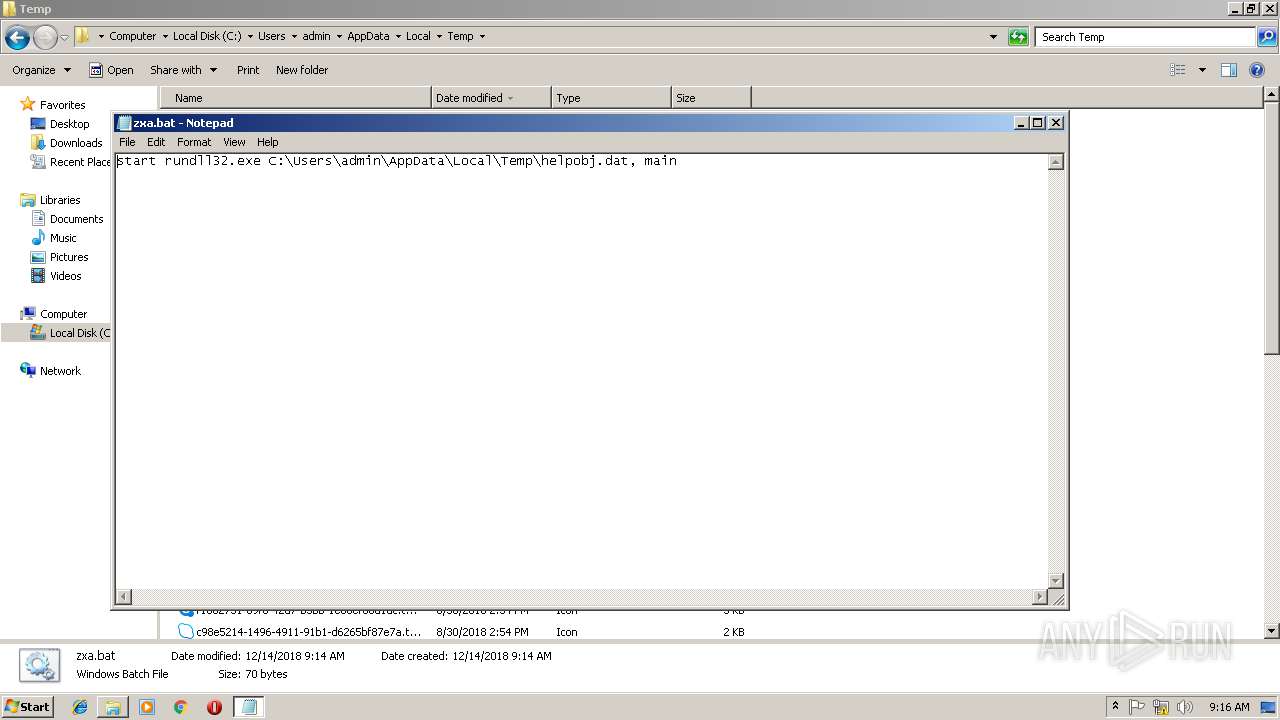
| 1088 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\zxa.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1148 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\sdw.vbs" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1176 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\zxa.bat | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=884,18102336394523641768,10761462838020187869,131072 --enable-features=PasswordImport --service-pipe-token=38663A13B517C4D27104F653180A6256 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=38663A13B517C4D27104F653180A6256 --renderer-client-id=5 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2492 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2284 | net group /domain | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3680 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
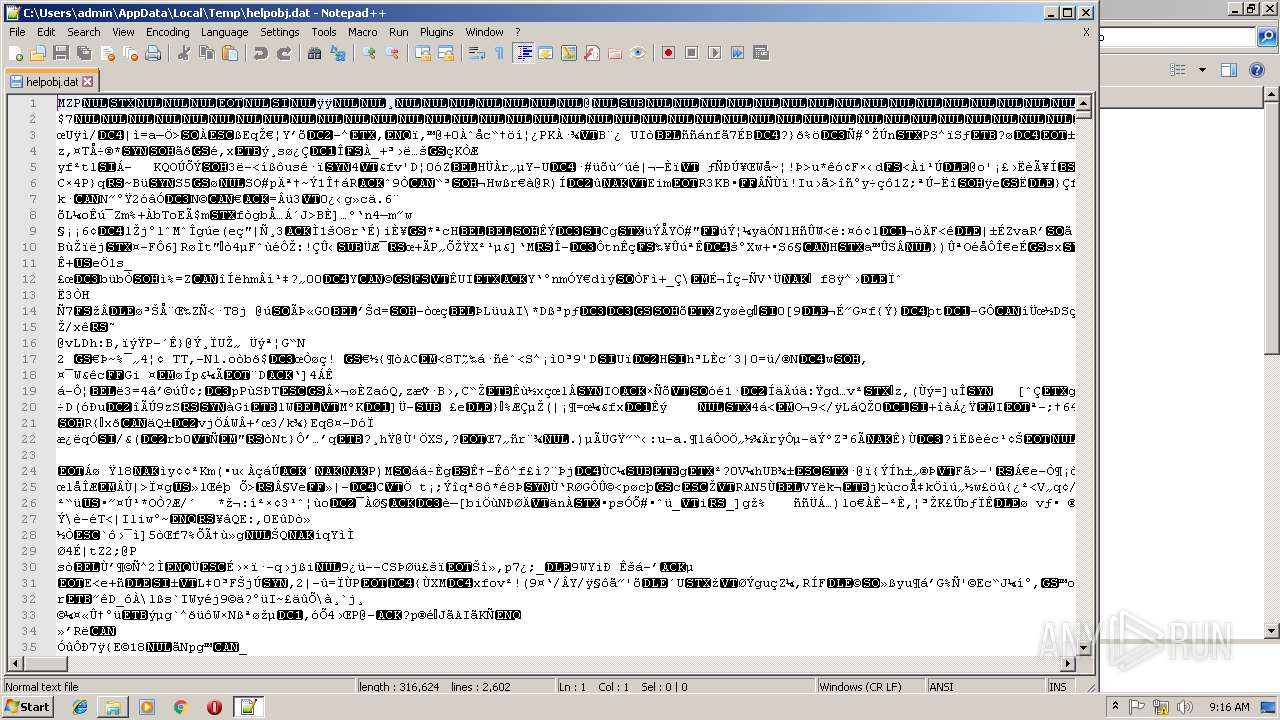
| 2312 | rundll32.exe C:\Users\admin\AppData\Local\Temp\helpobj.dat, main | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2992.0.1742824632\64729188" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
Total events
2 052
Read events
1 852
Write events
195
Delete events
5
Modification events
| (PID) Process: | (2828) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2828) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bForms_AdhocWorkflowBackup |
Value: 0 | |||
| (PID) Process: | (2828) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (2828) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (3680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3680) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
77
Text files
92
Unknown types
21
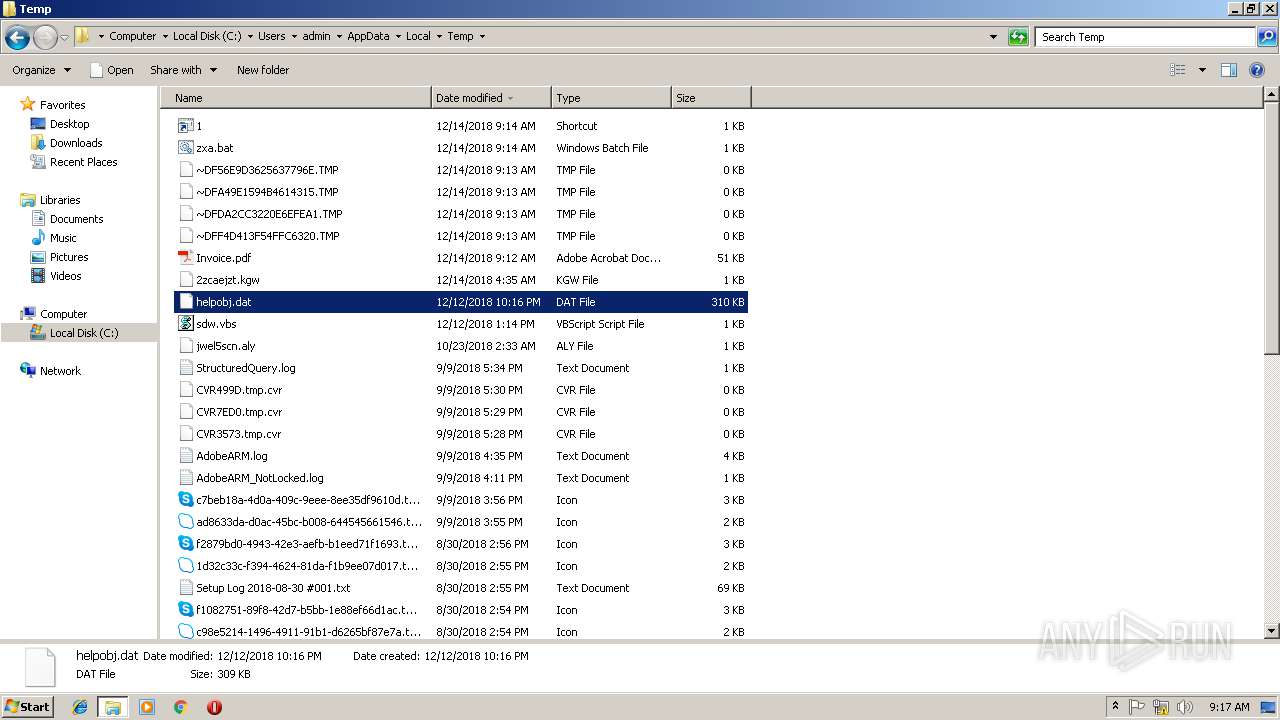
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2828 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2296 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\download[1].txt | — | |
MD5:— | SHA256:— | |||
| 2828 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R108fmye_frqop7_26k.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rjvs0cg_frqop6_26k.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1b1vcri_frqop9_26k.tmp | — | |
MD5:— | SHA256:— | |||
| 2828 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rxo65q9_frqop8_26k.tmp | — | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF4D413F54FFC6320.TMP | — | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDA2CC3220E6EFEA1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
133
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3488 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
3488 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
— | — | GET | 200 | 195.138.255.24:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | DE | der | 471 b | whitelisted |
3488 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
— | — | GET | 200 | 195.138.255.24:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | DE | der | 727 b | whitelisted |
3680 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3488 | AcroRd32.exe | GET | 304 | 2.16.186.32:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
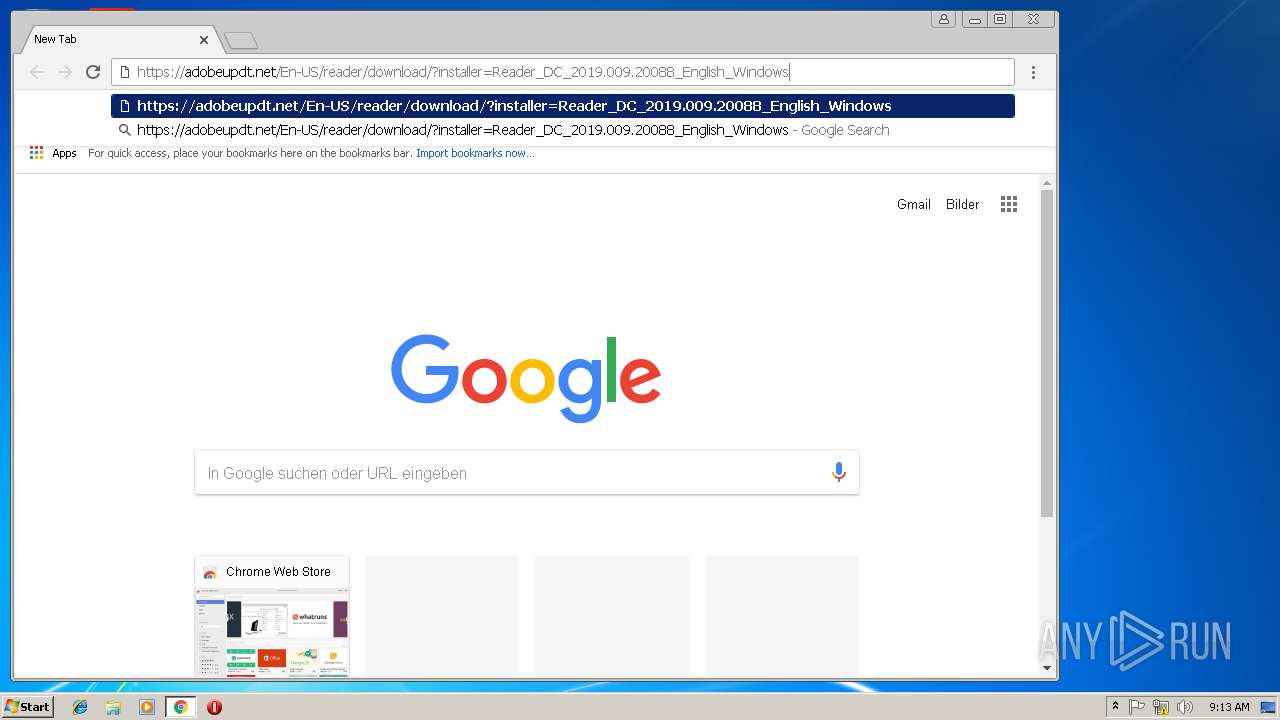
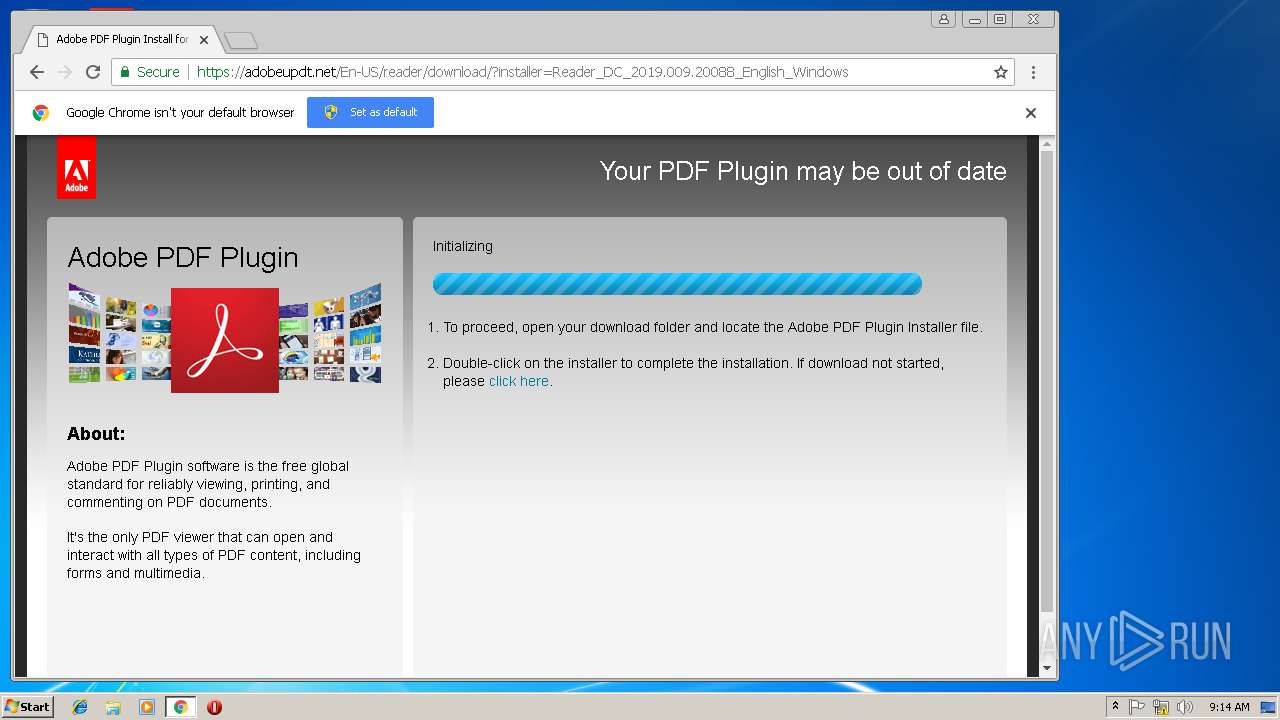
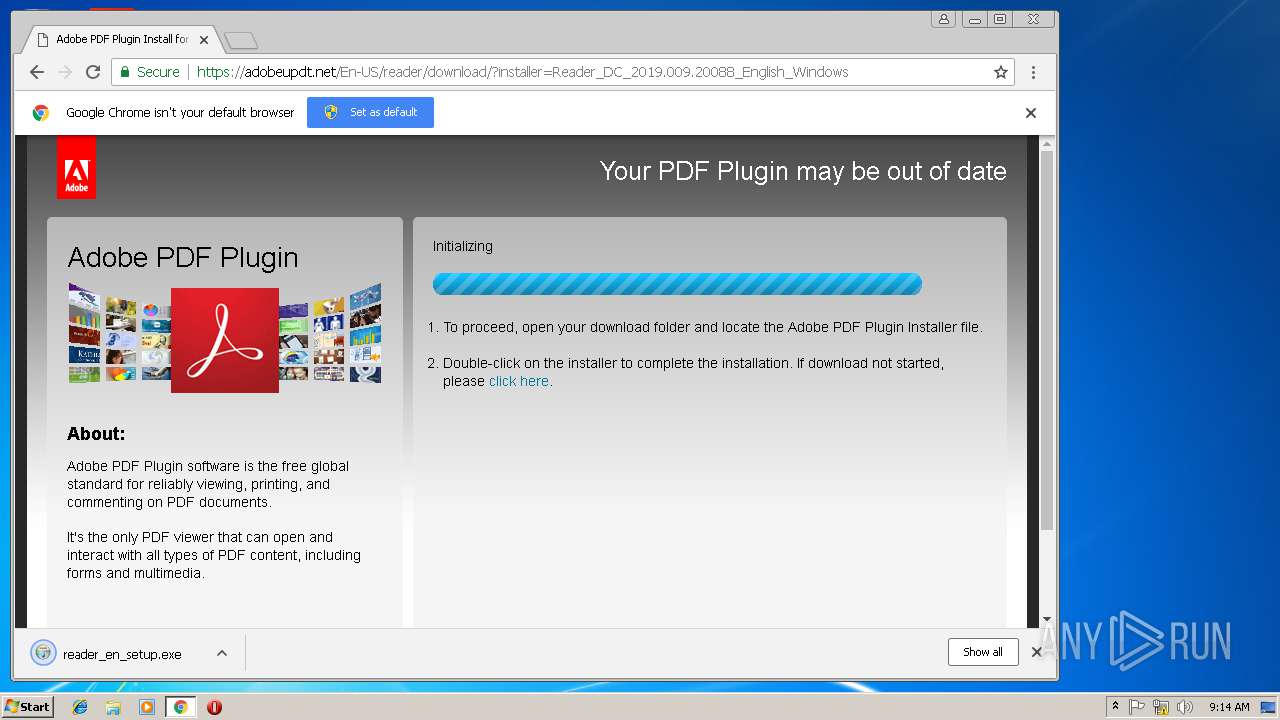
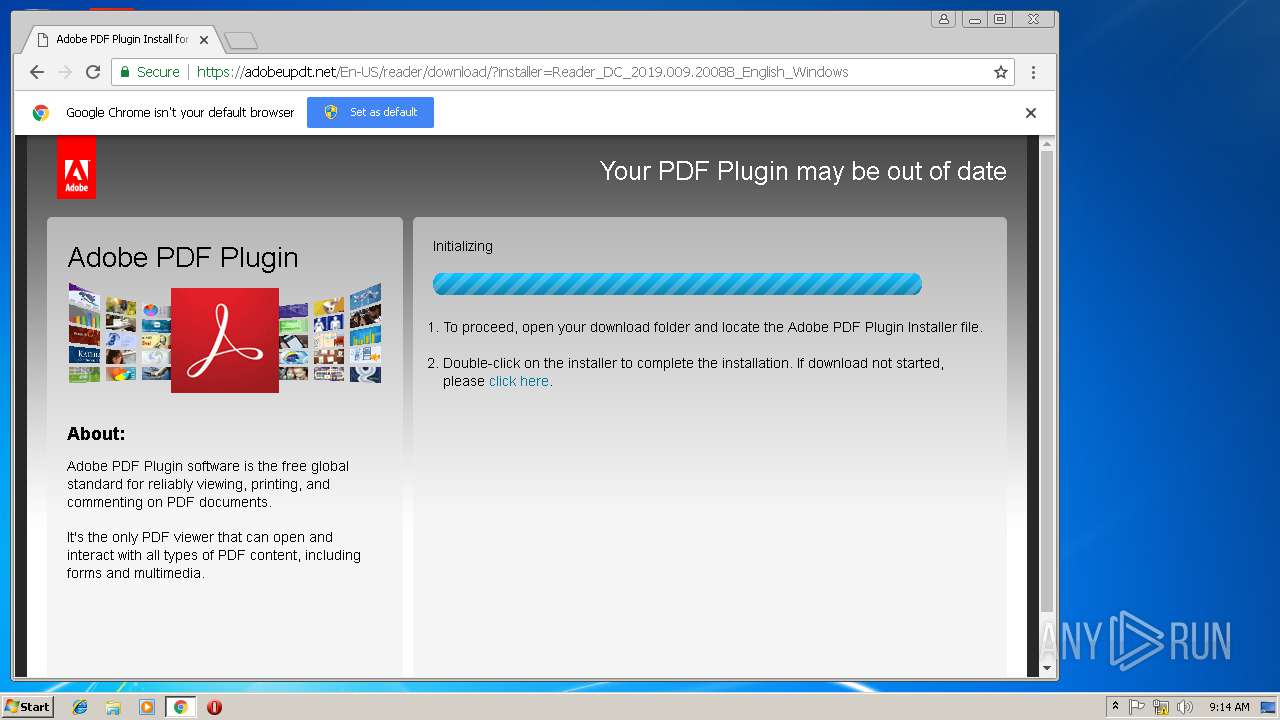
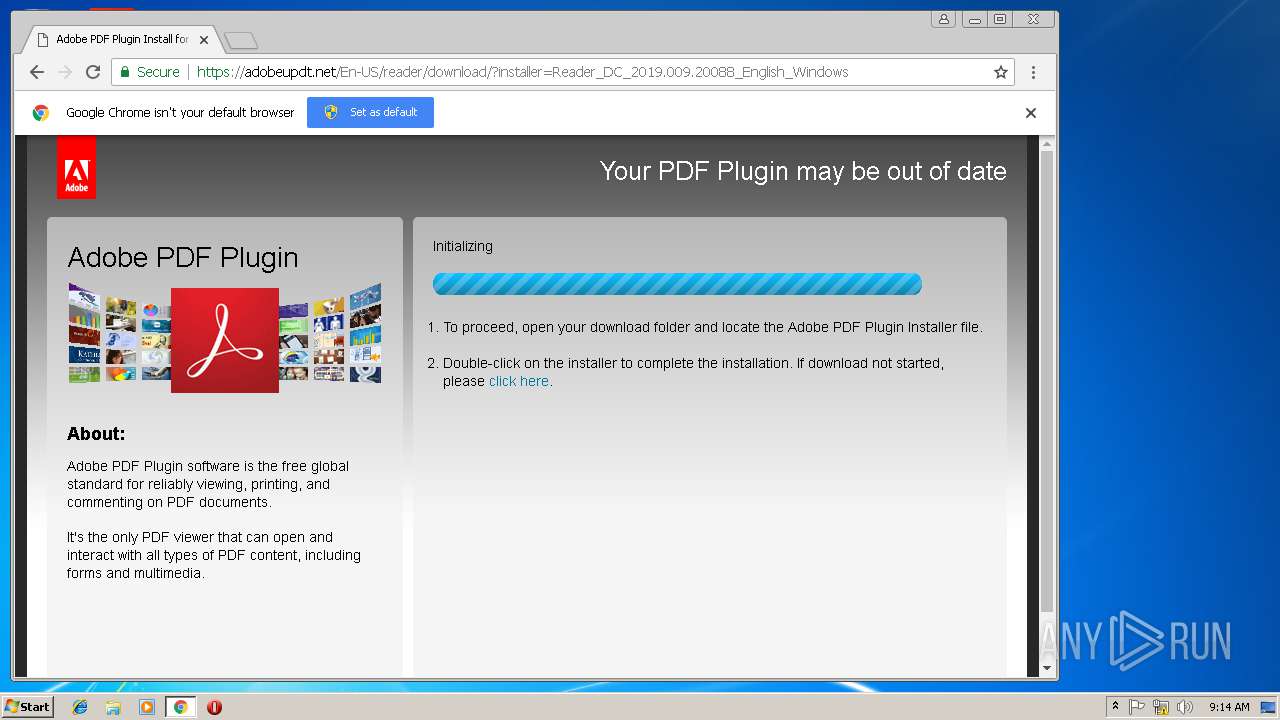
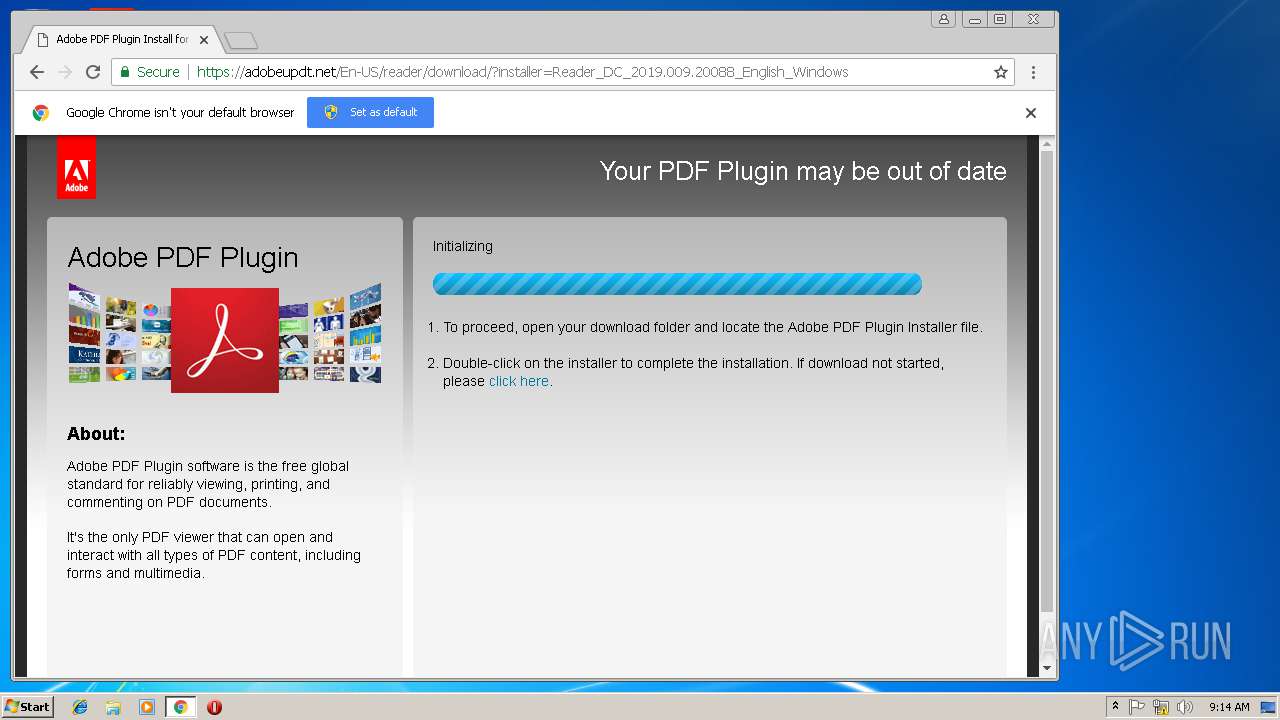
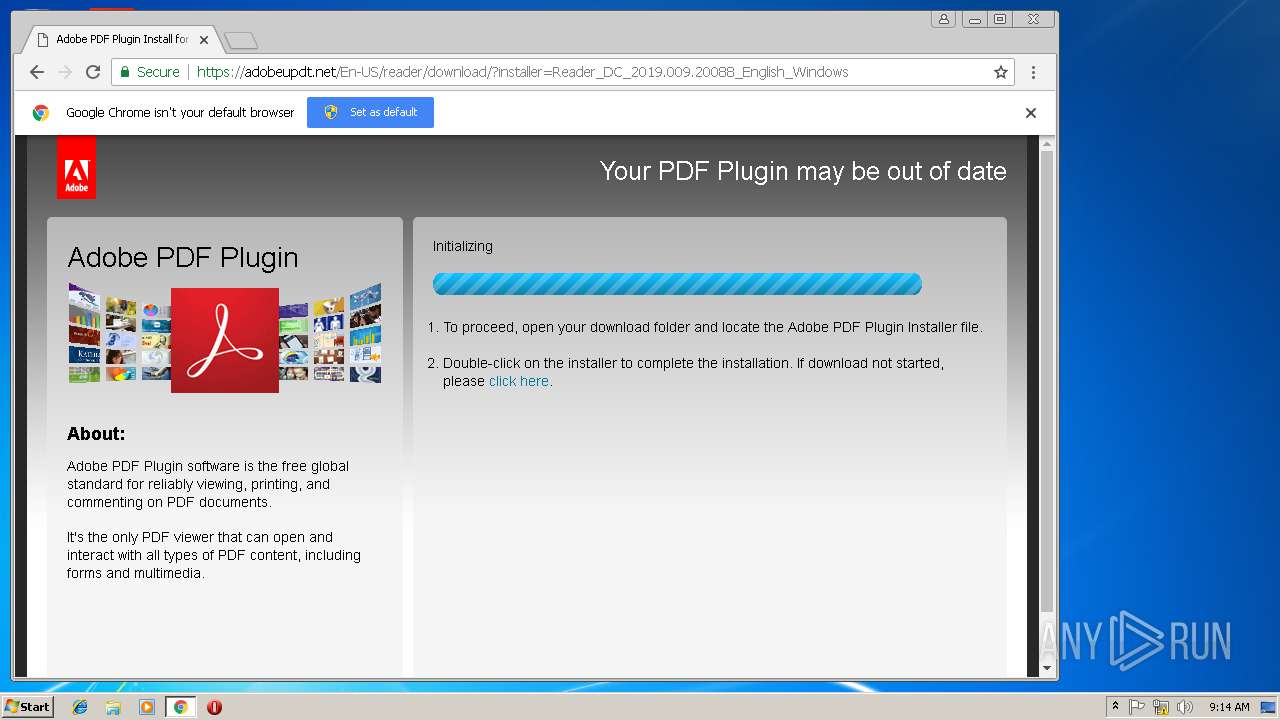
2296 | iexplore.exe | 195.123.212.248:443 | adobeupdt.net | ITL Company | LV | unknown |
3488 | AcroRd32.exe | 2.16.186.32:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
3488 | AcroRd32.exe | 23.210.248.251:443 | armmf.adobe.com | Akamai International B.V. | NL | whitelisted |
3504 | chrome.exe | 216.58.211.100:443 | www.google.com | Google Inc. | US | whitelisted |
3504 | chrome.exe | 195.123.212.248:443 | adobeupdt.net | ITL Company | LV | unknown |
3504 | chrome.exe | 172.217.168.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2572 | rundll32.exe | 37.252.9.68:443 | afgdhjkrm.pw | — | DE | malicious |
2988 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
3504 | chrome.exe | 172.217.168.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
adobeupdt.net |
| unknown |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
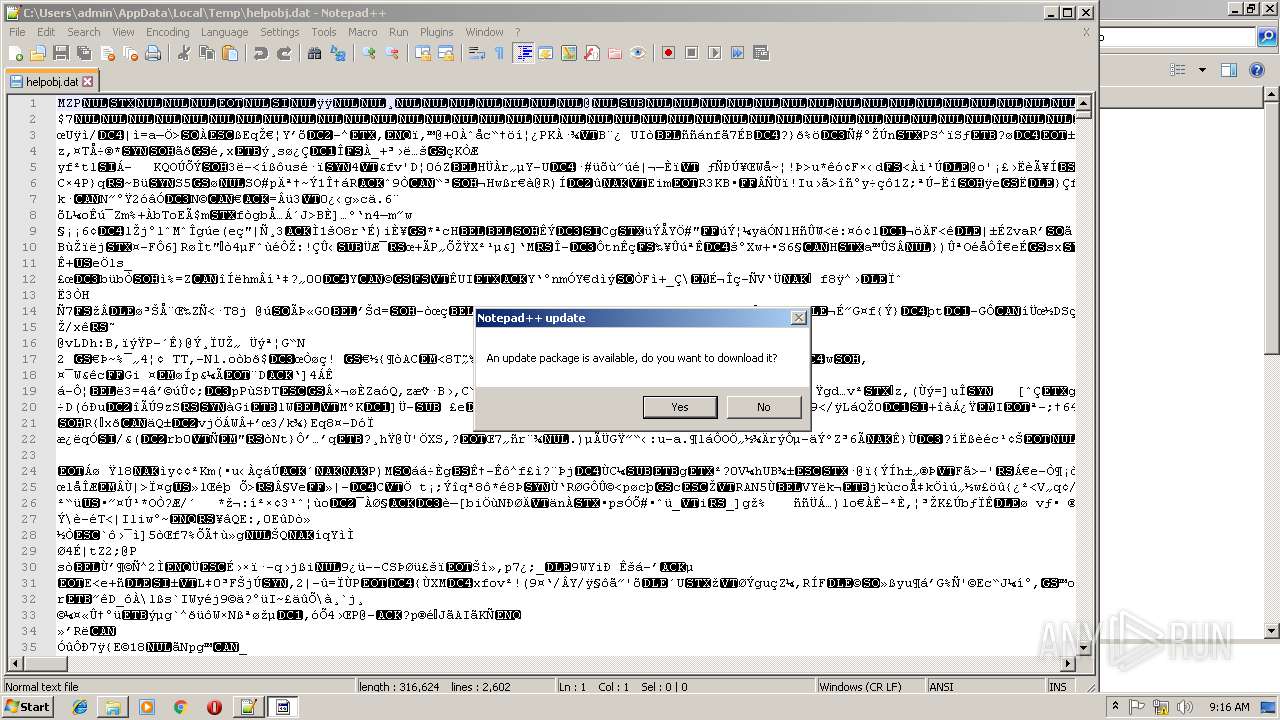
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|