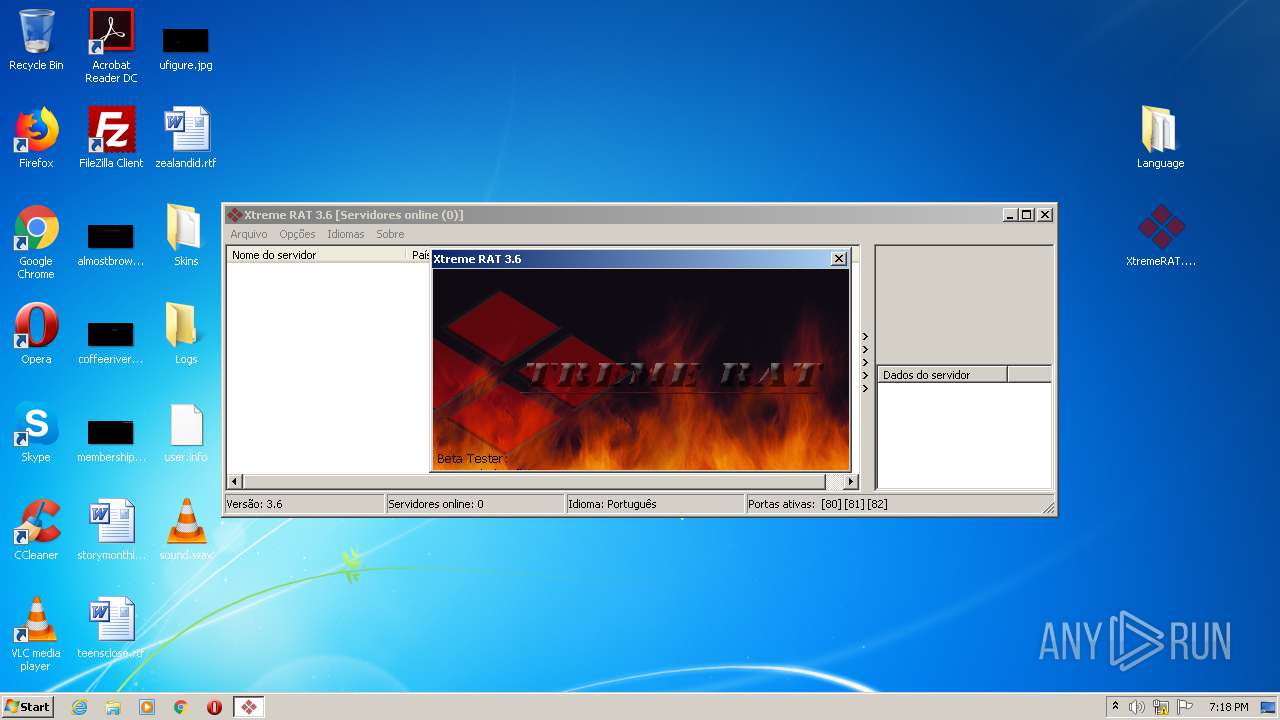
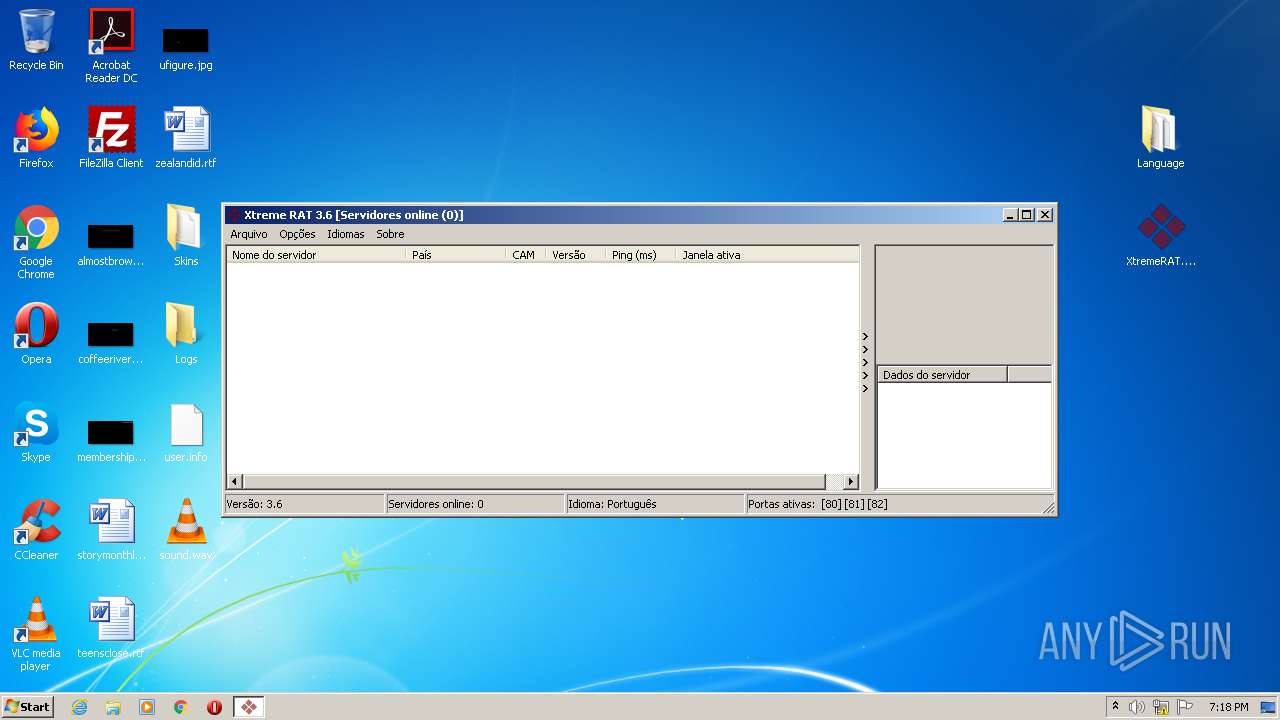
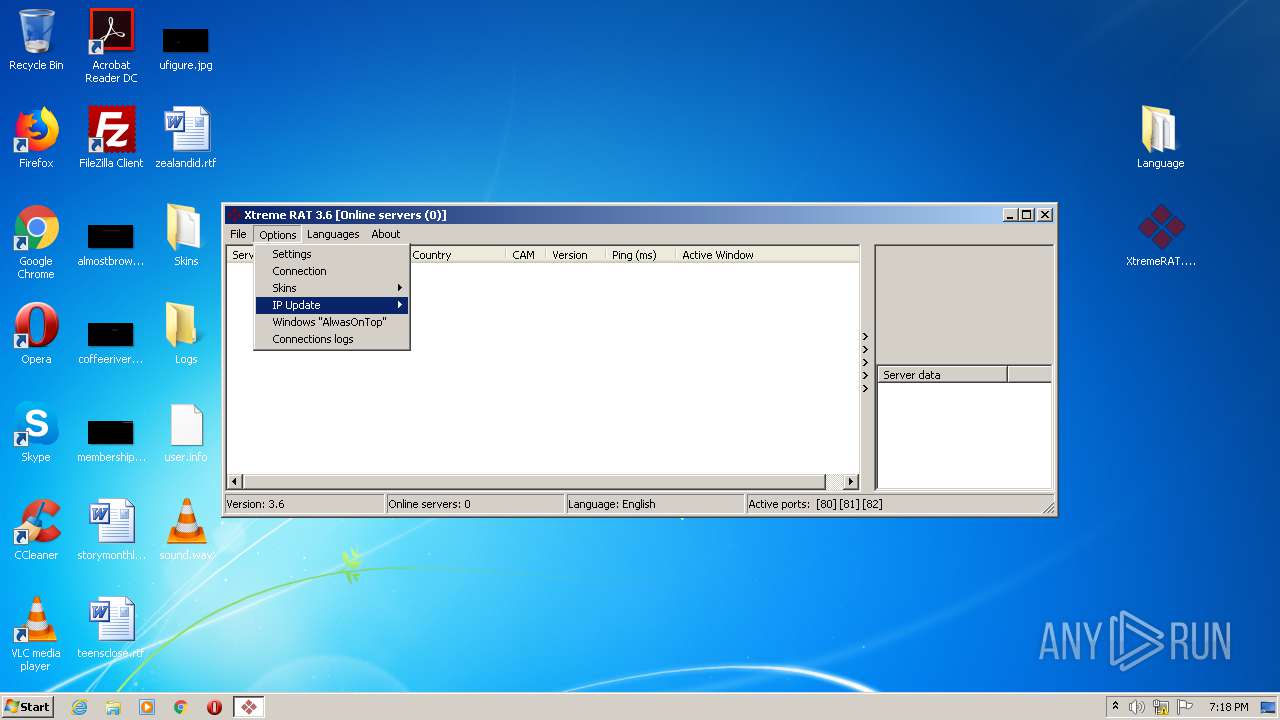
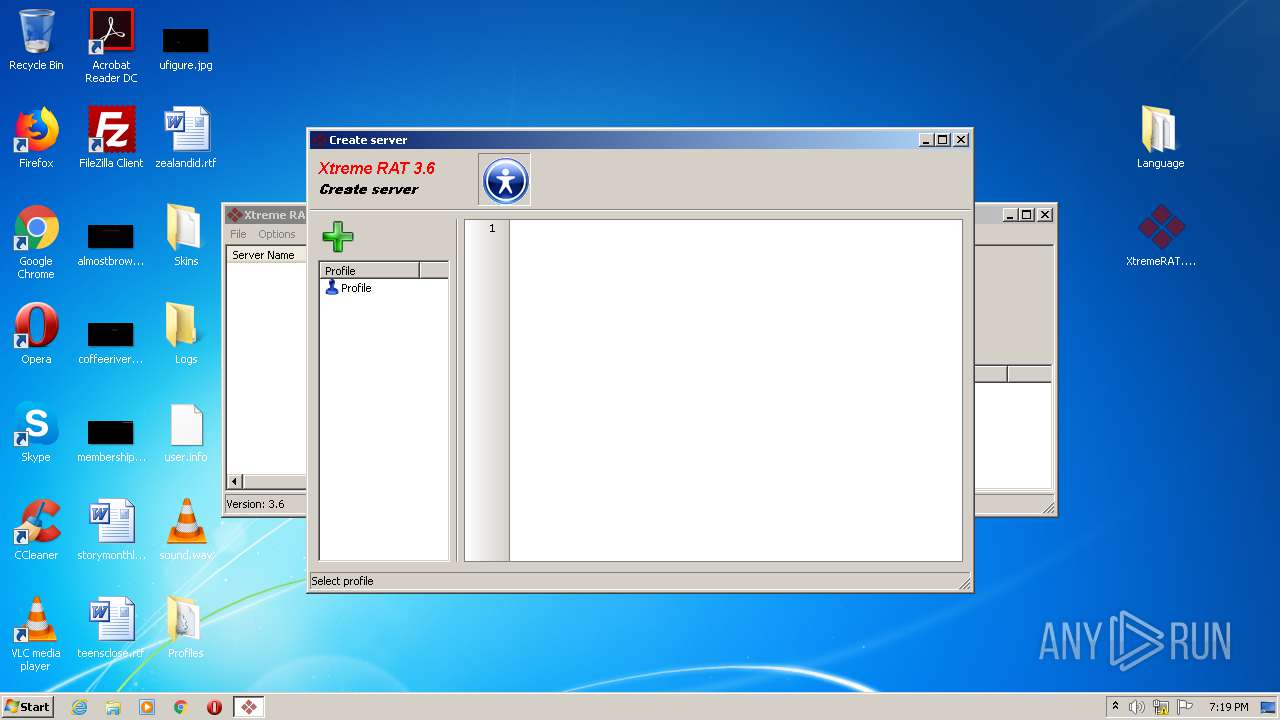
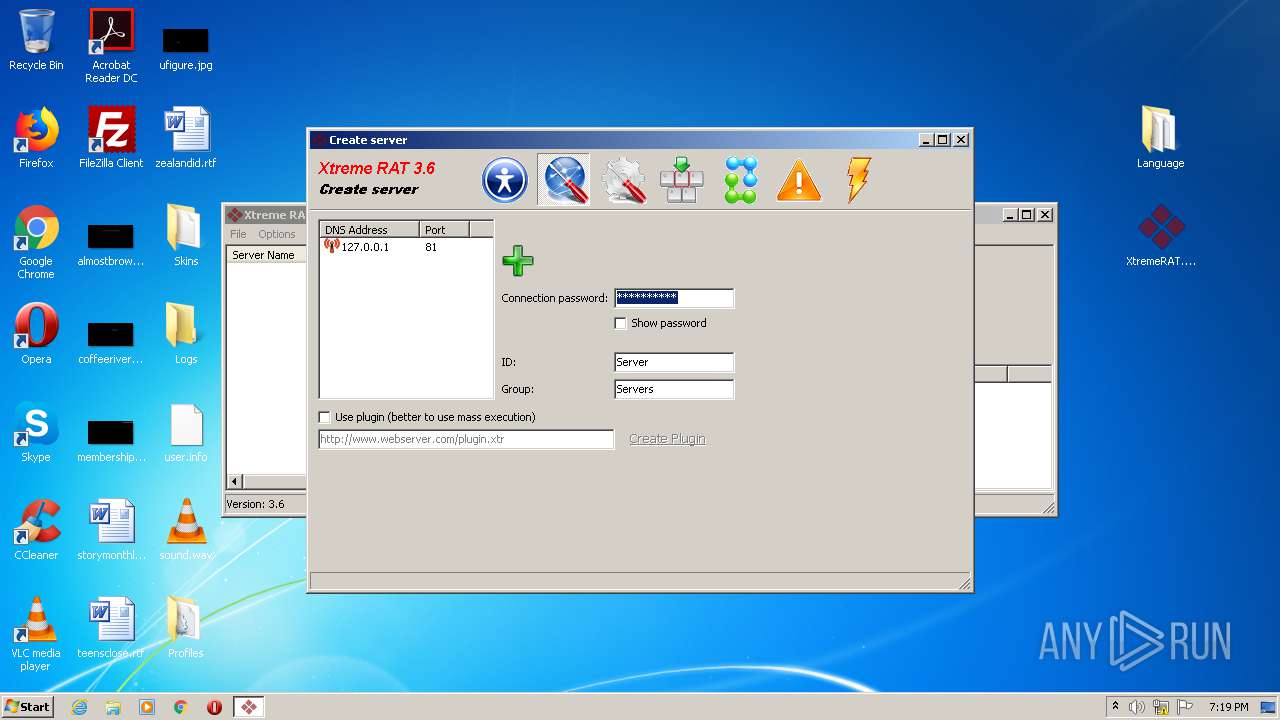
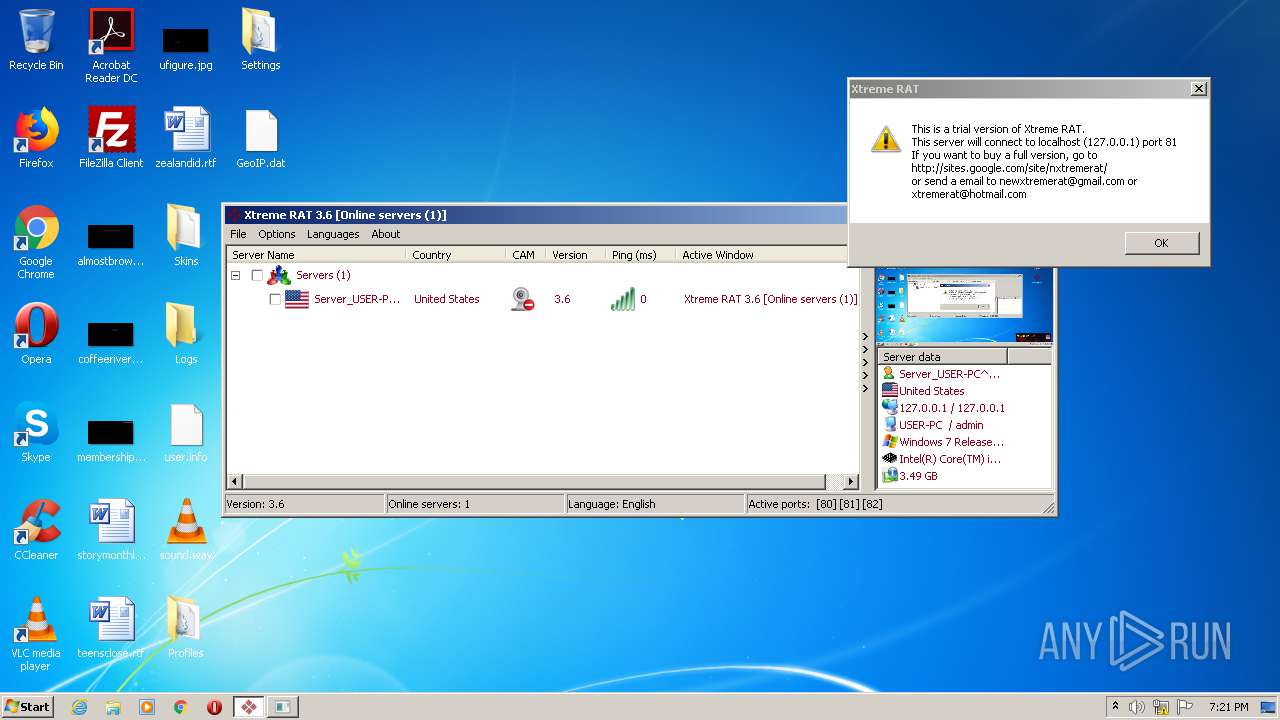
| File name: | XtremeRAT.zip |
| Full analysis: | https://app.any.run/tasks/39b4cb8b-a2ec-404b-a4f4-f1c6f8e38694 |
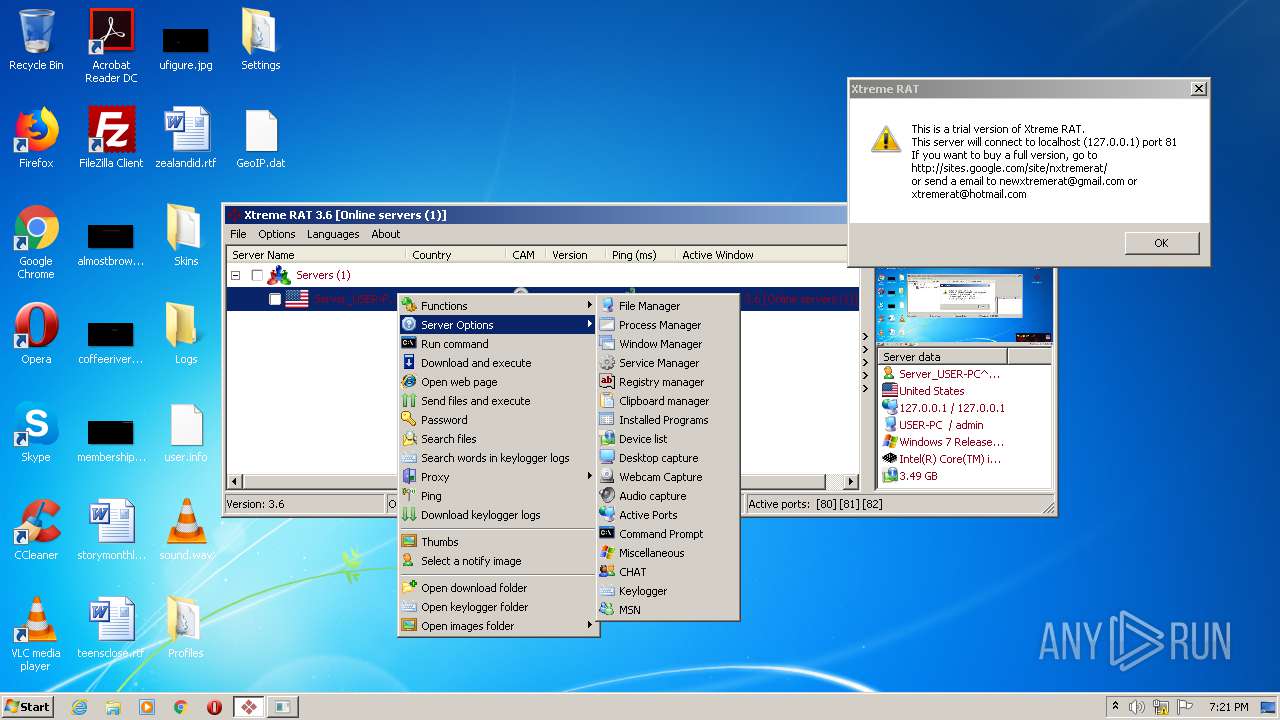
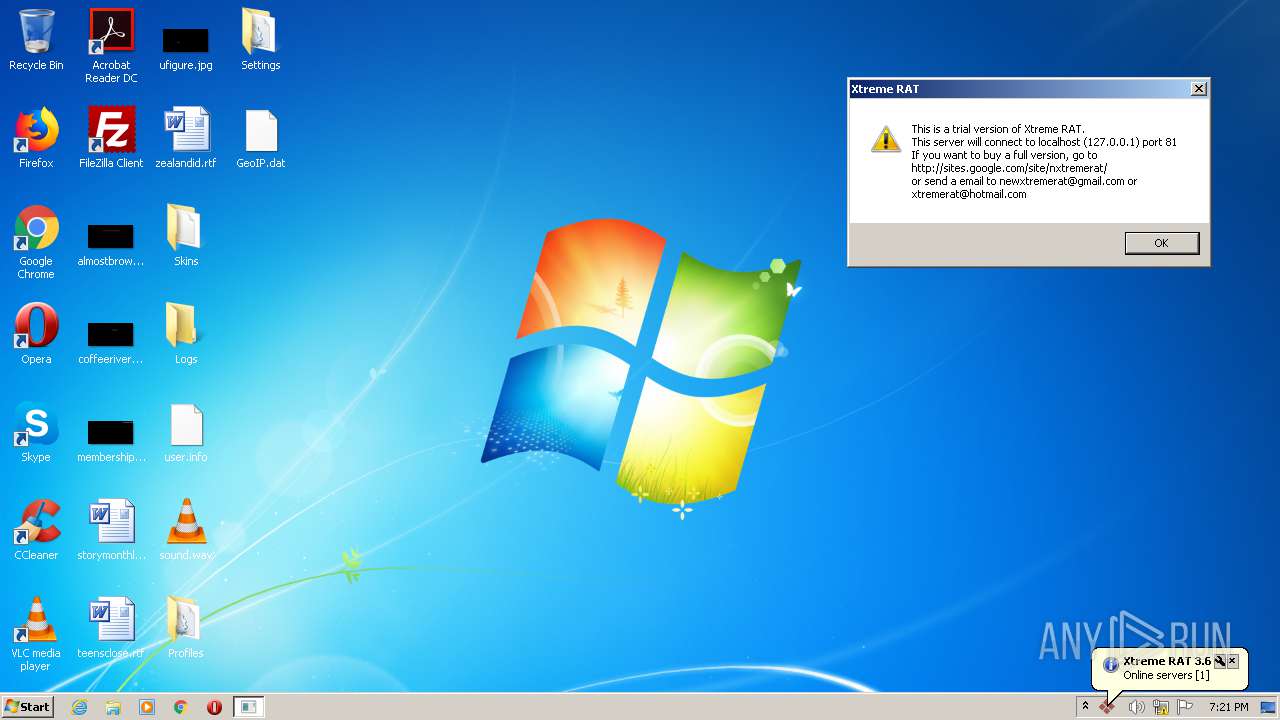
| Verdict: | Malicious activity |
| Analysis date: | August 29, 2020, 18:16:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6908D1BEFD41783DA6EBA7F1FCC8FD3A |
| SHA1: | C040740ADB367715F74CAC004C6634DF6EED8427 |
| SHA256: | F4AD6CC762F0998A5BE6D080D780D76846DD5C75C5C02AA96CB15F4D1FF67790 |
| SSDEEP: | 98304:SPghTJ2UIFmXsHug4SznAtEx3jBnzUxV8VSPzz0+iYUk7ozDQDx7dhT:S0TJ2UIFJz4S0Sx3VzUxV8VSv0NFuxPT |
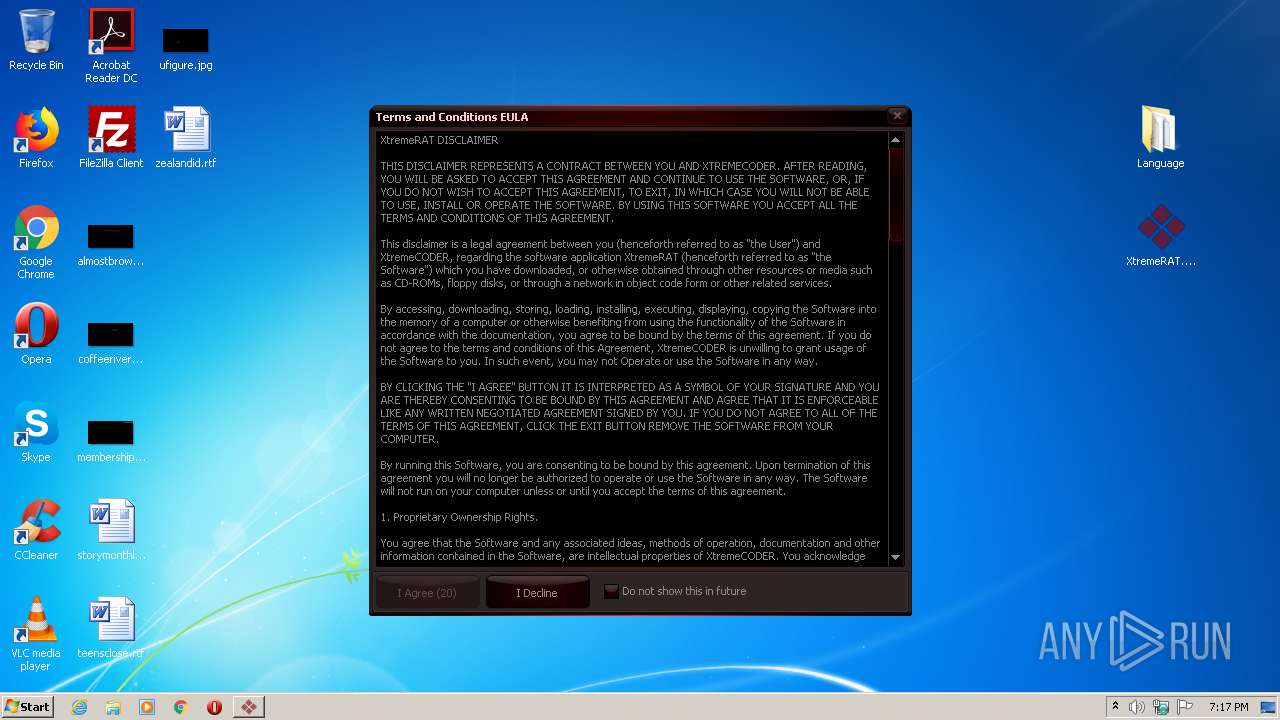
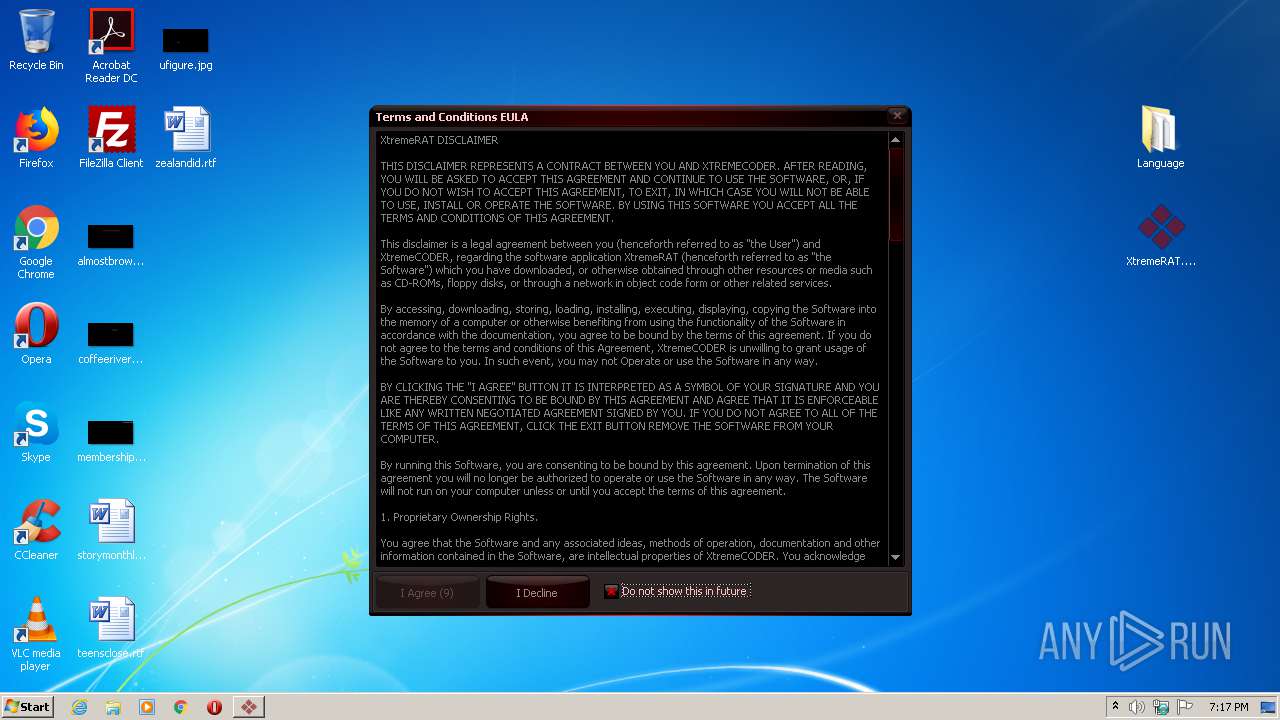
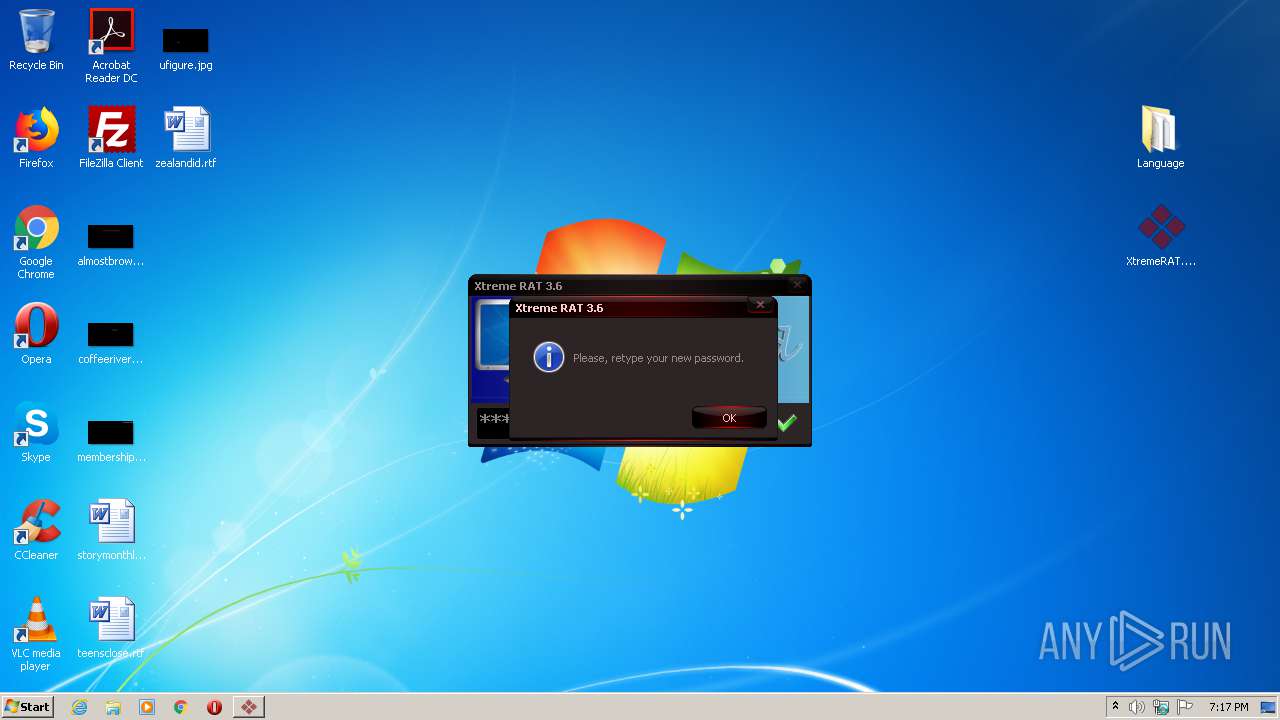
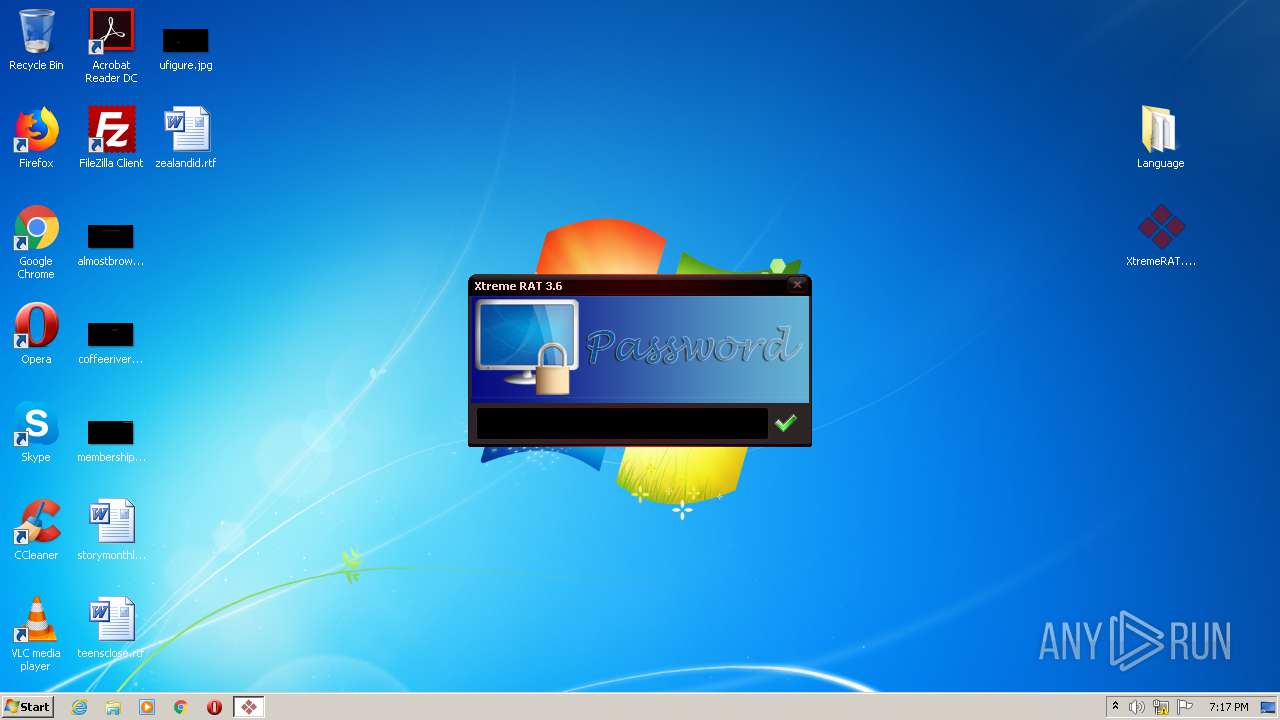
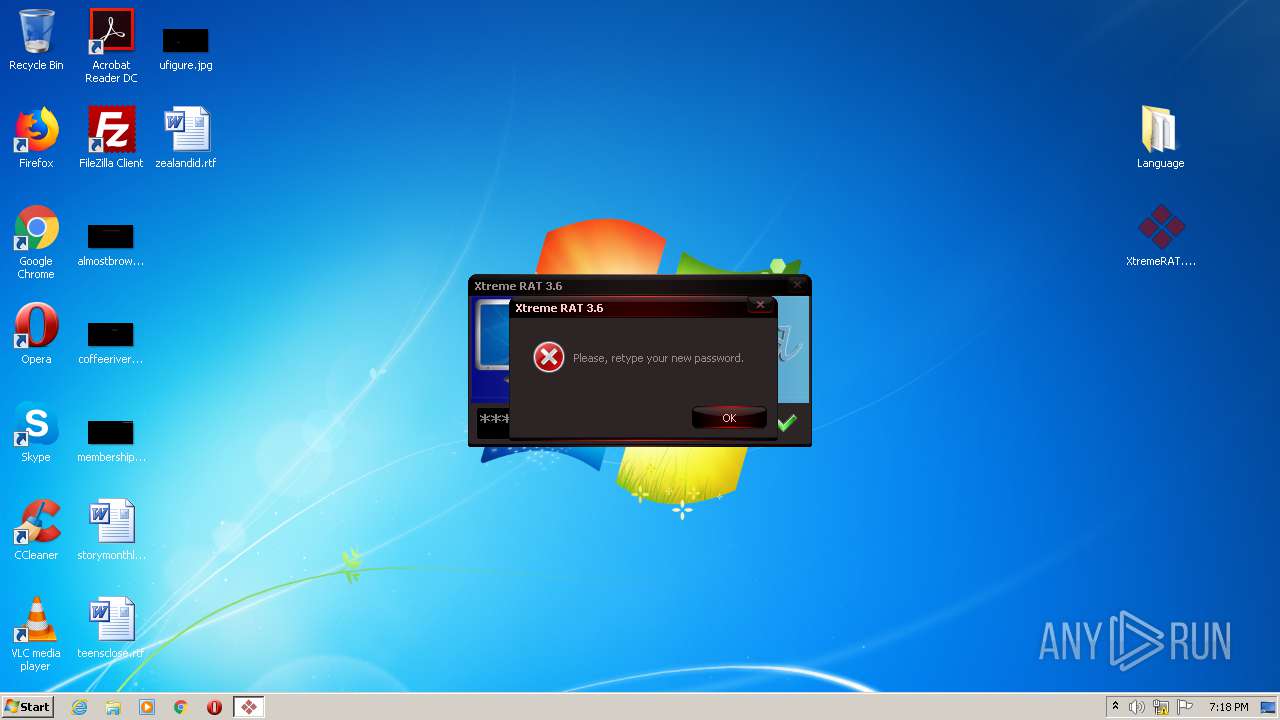
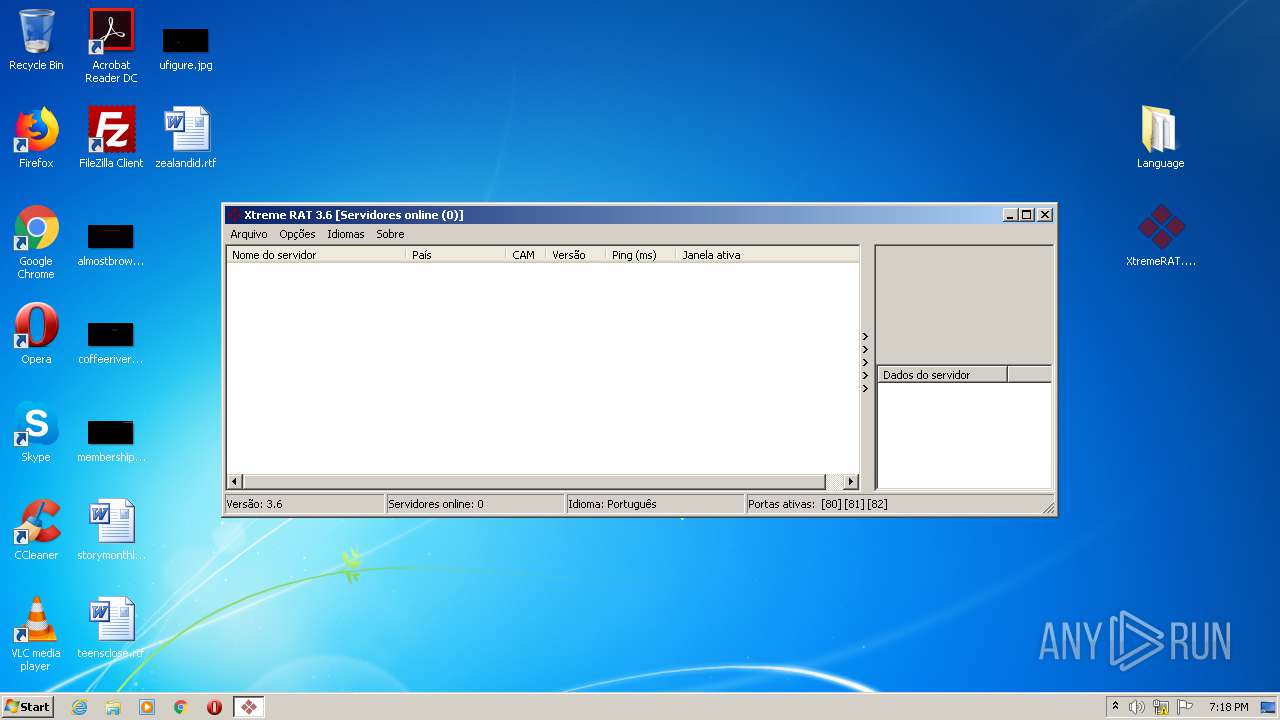
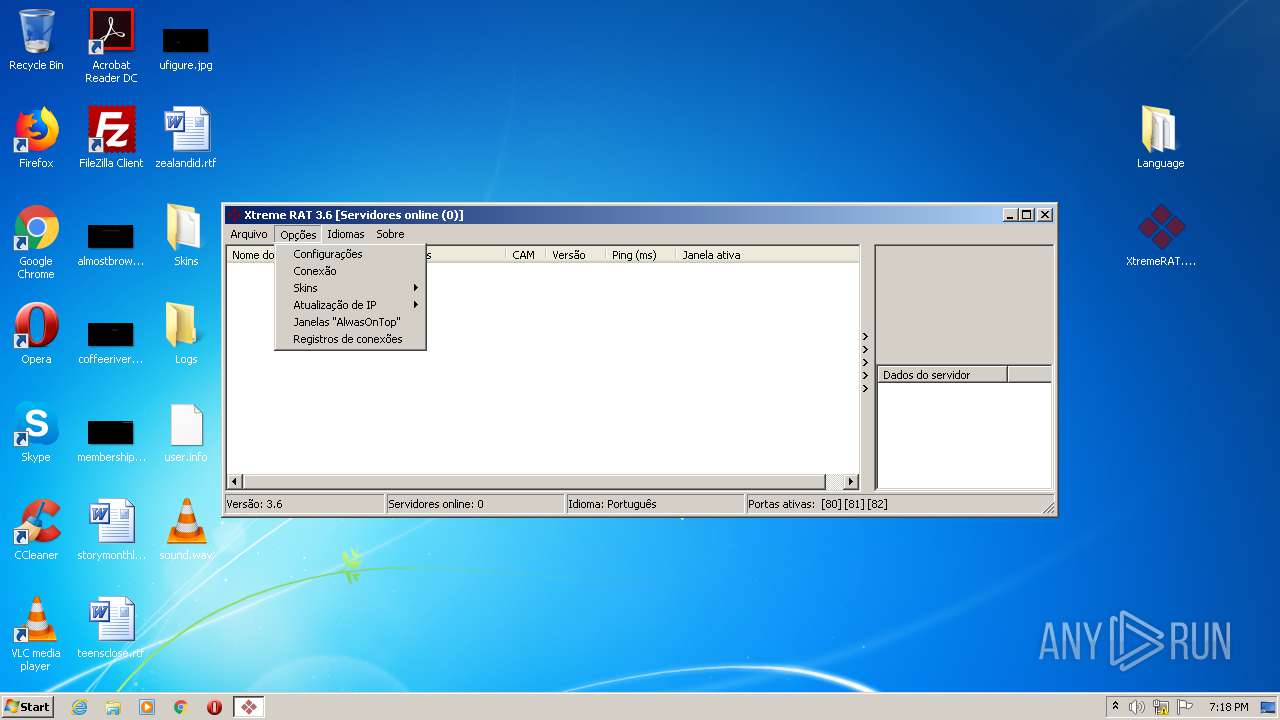
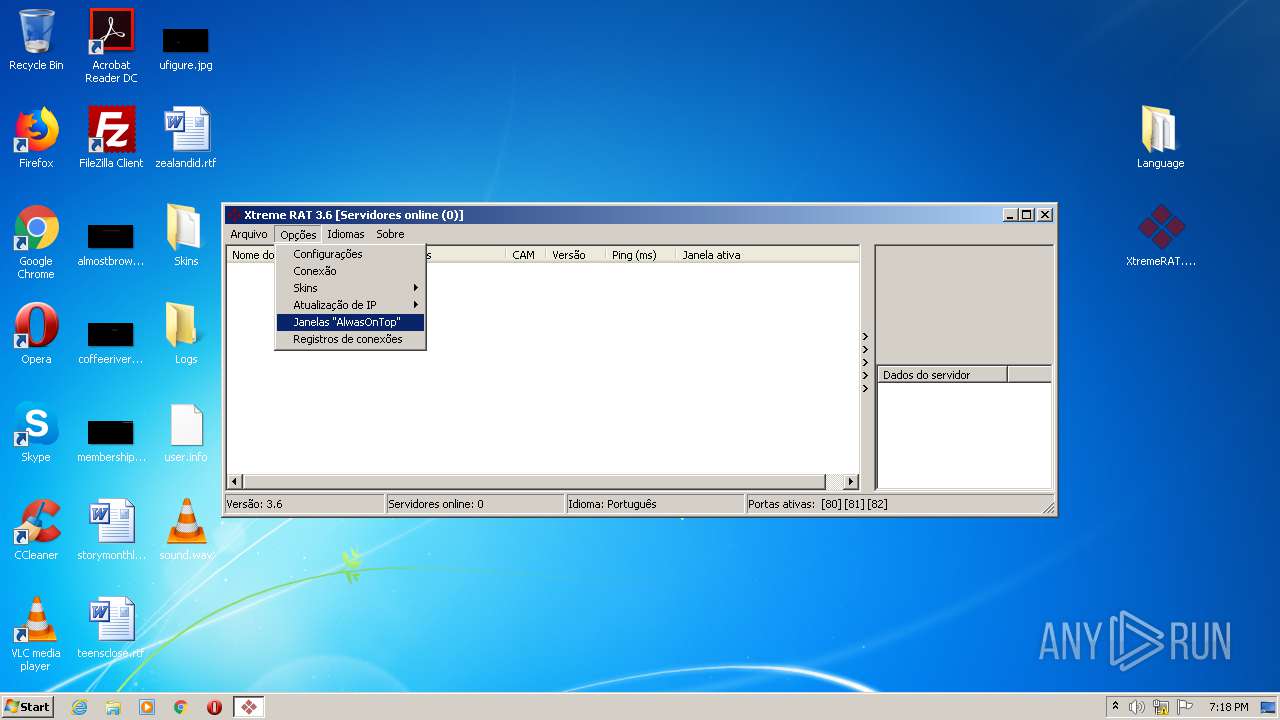
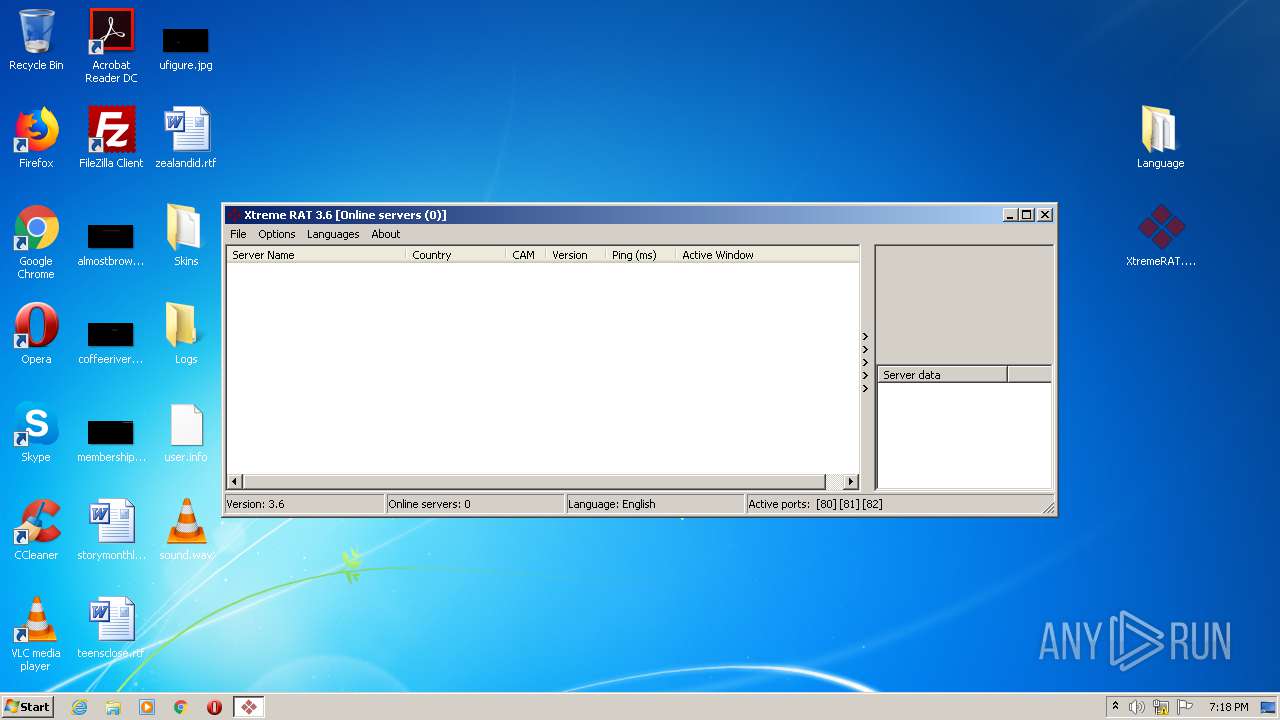
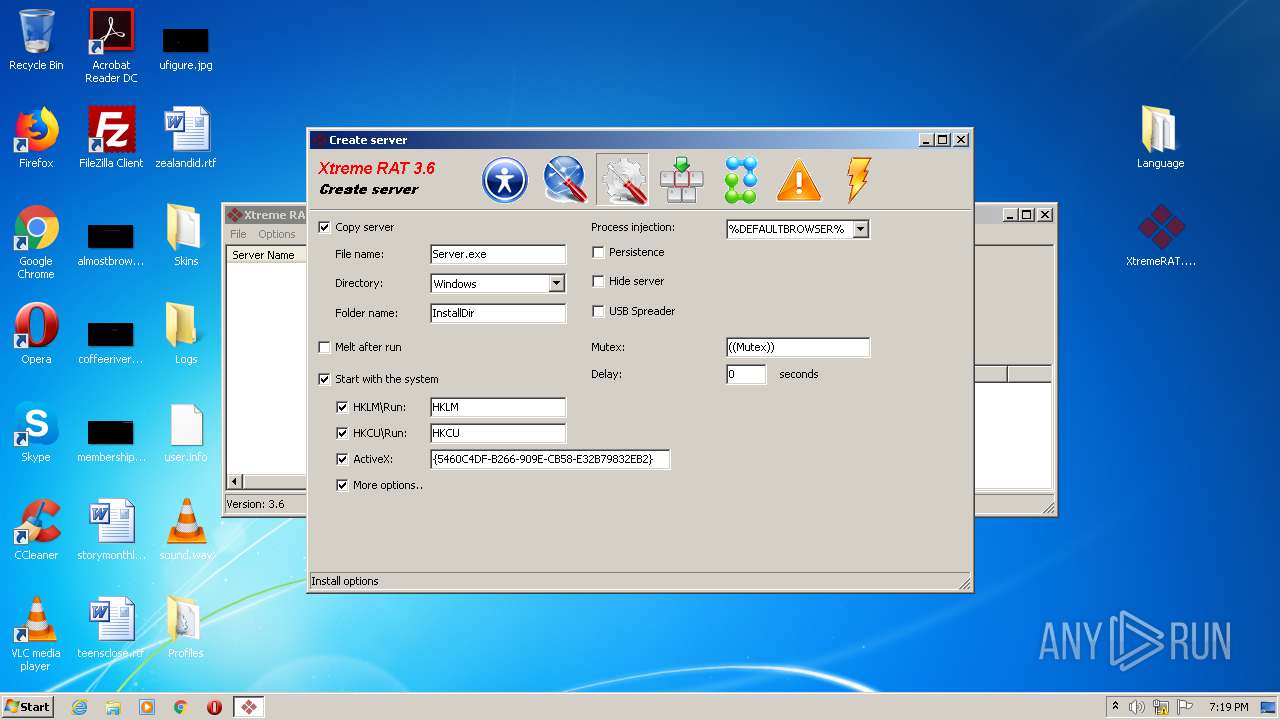
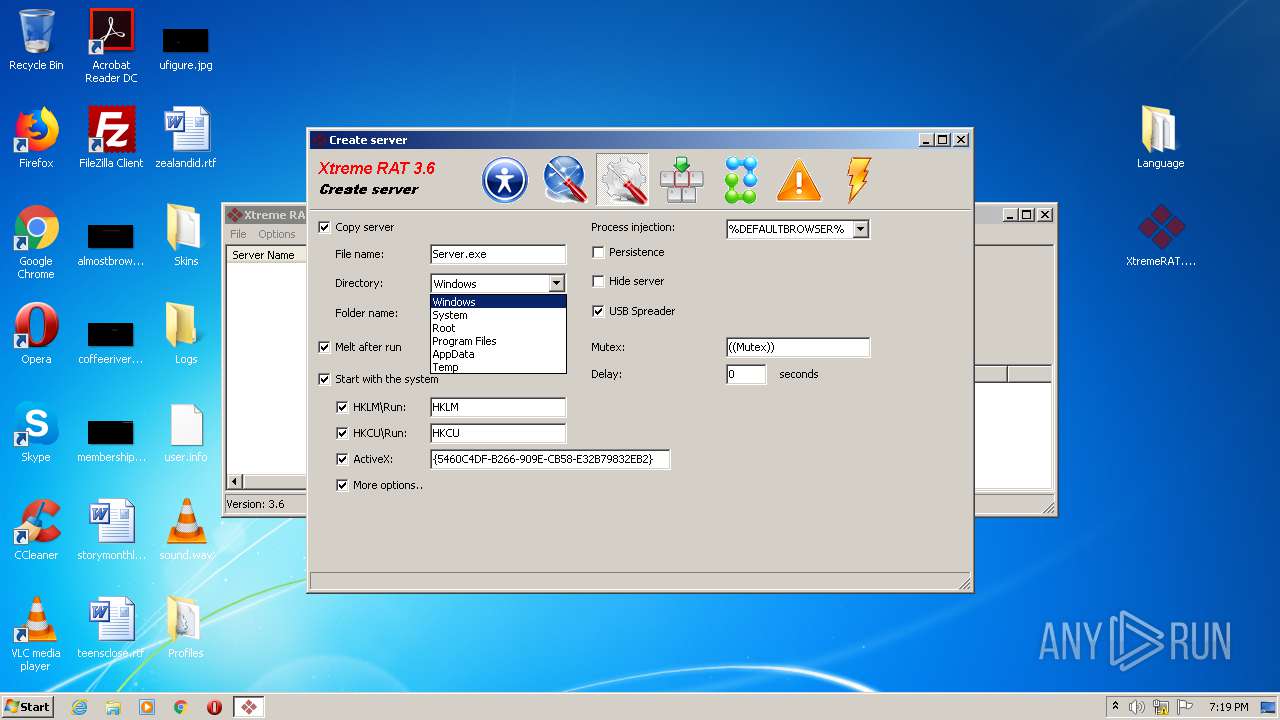
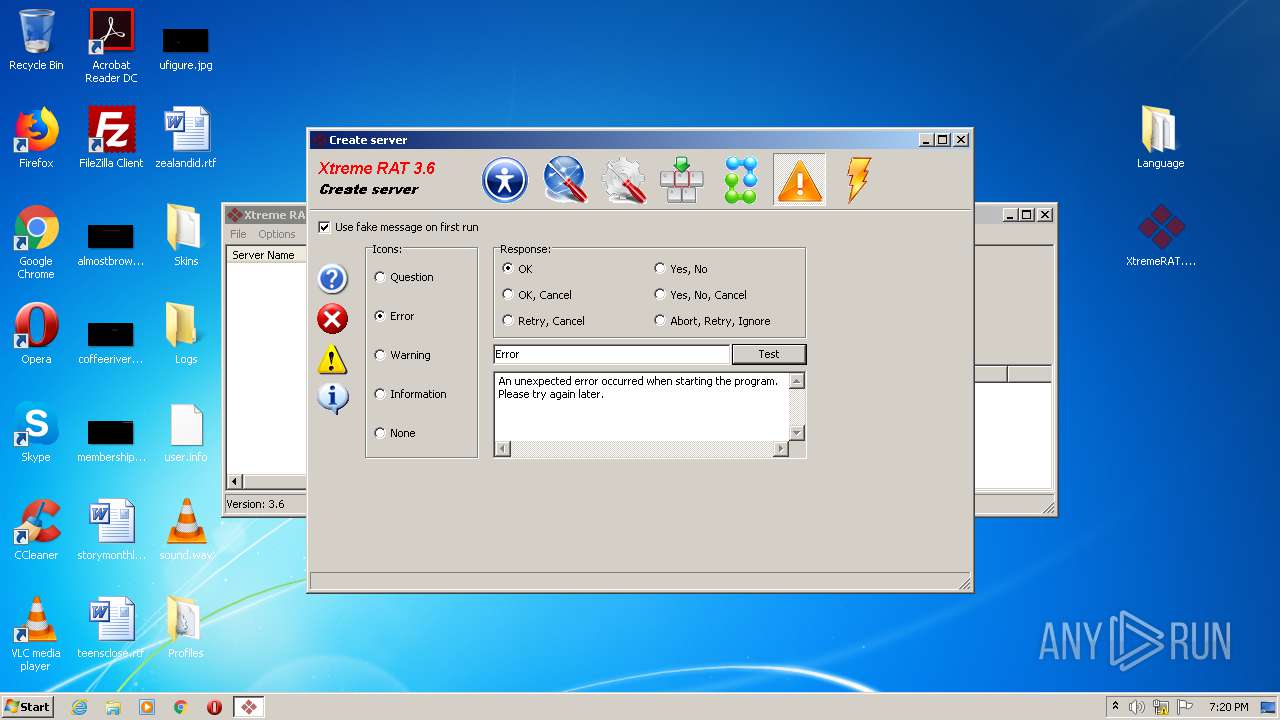
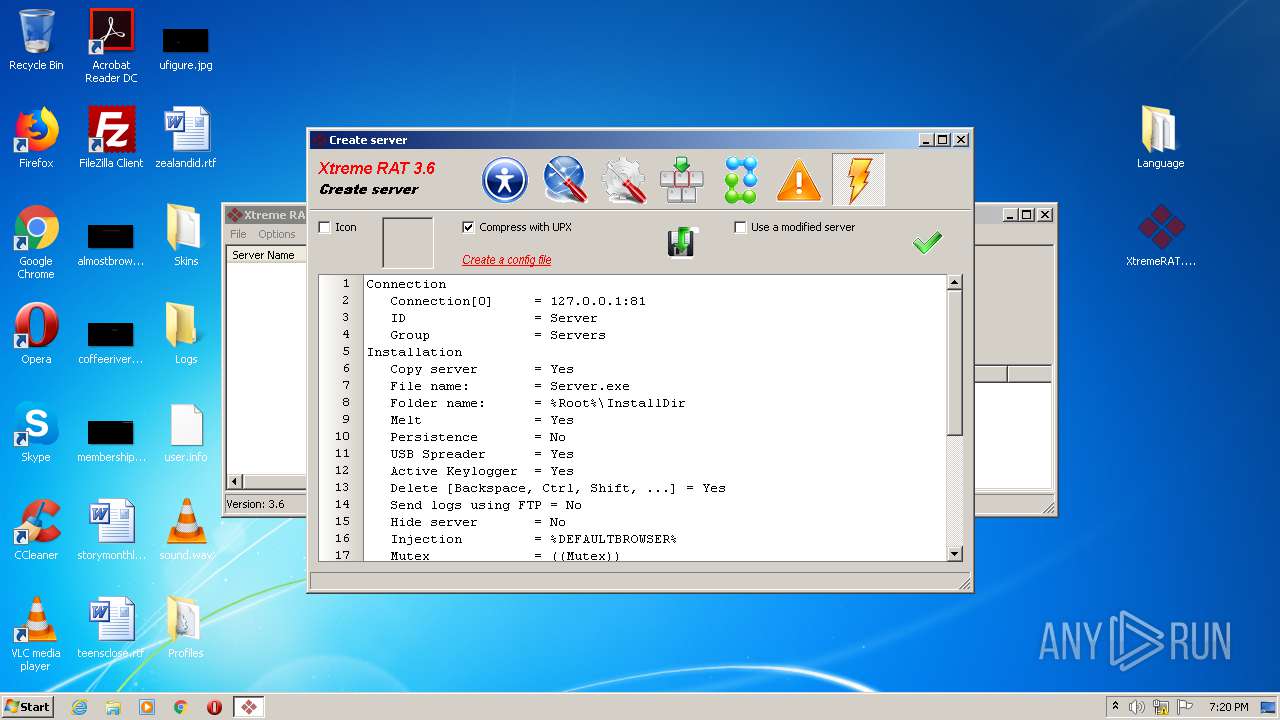
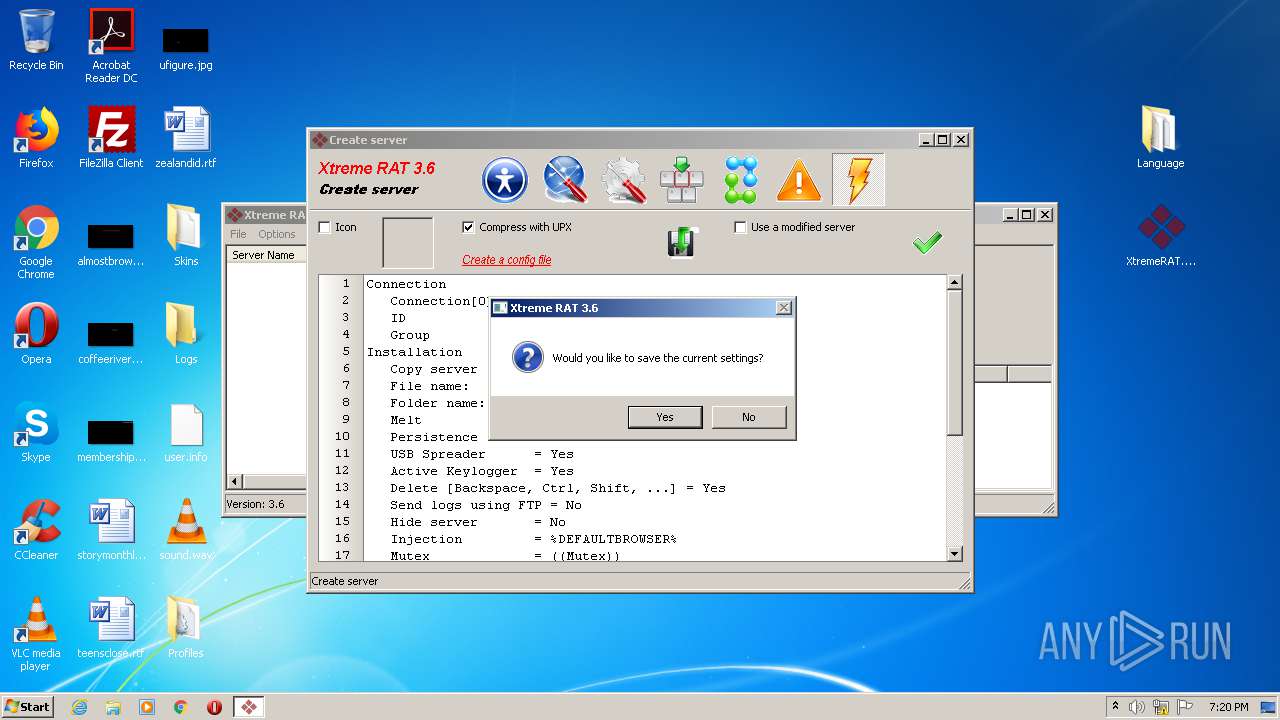
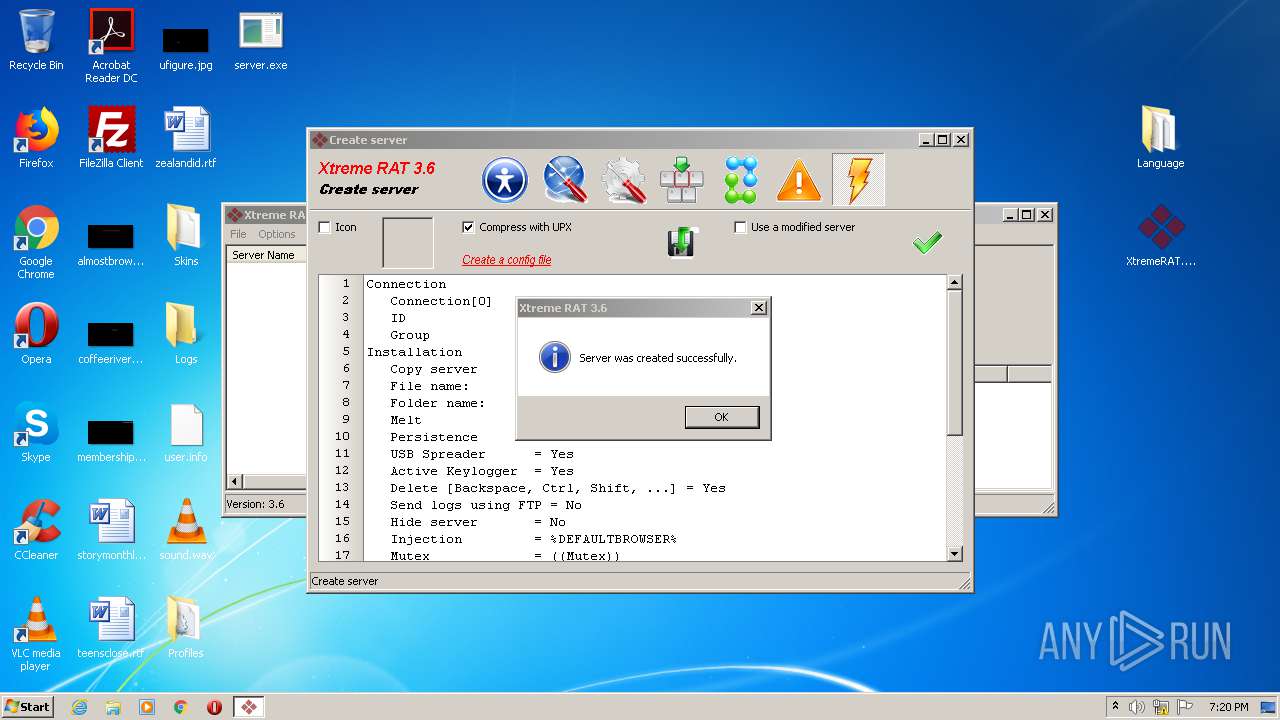
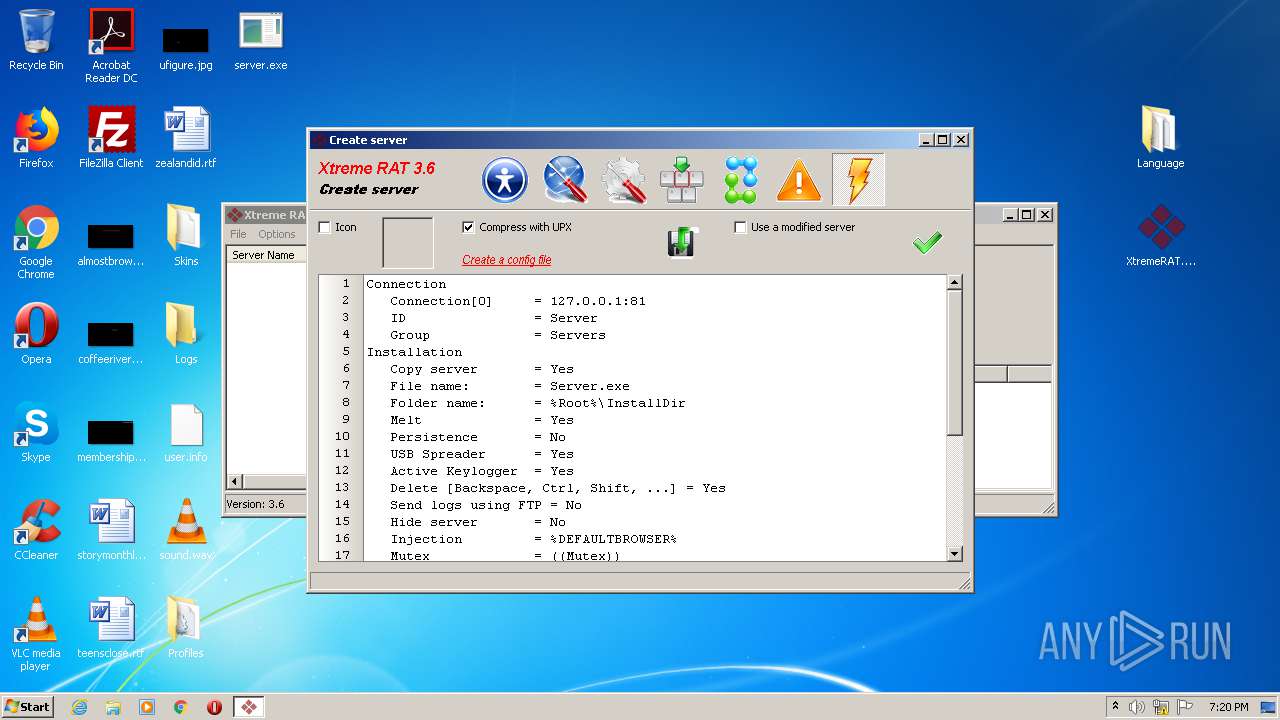
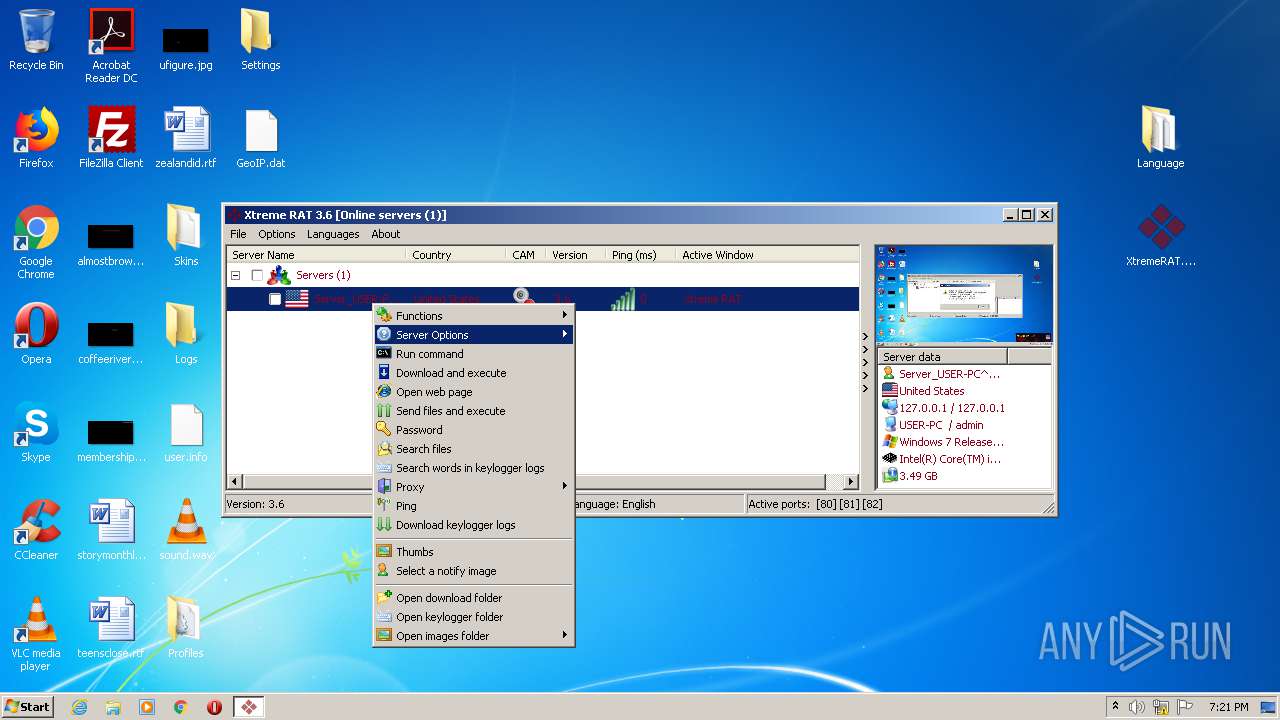
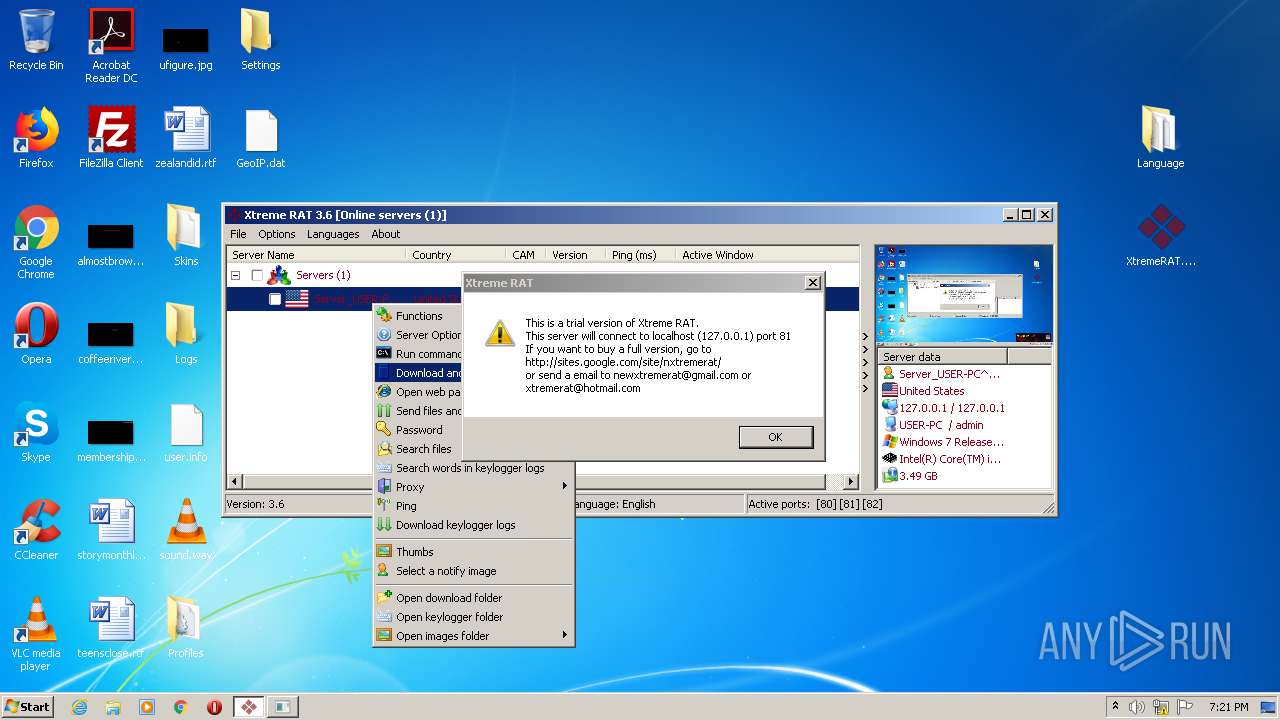
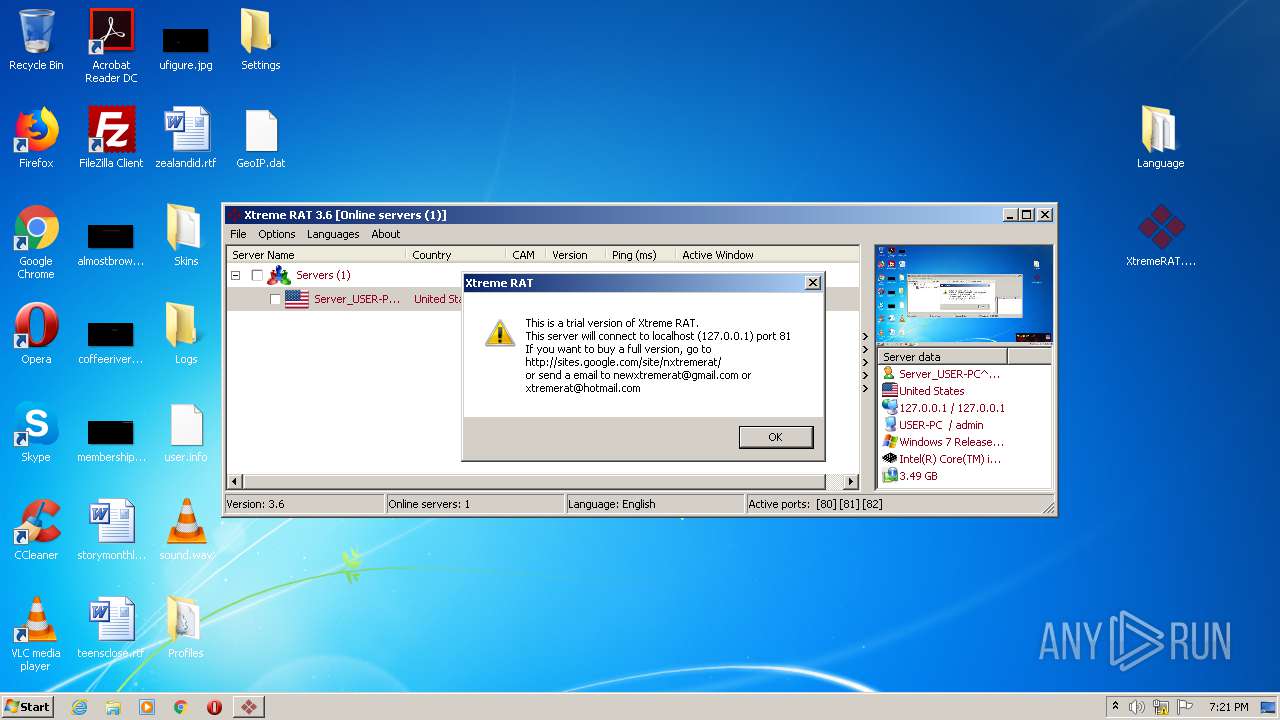
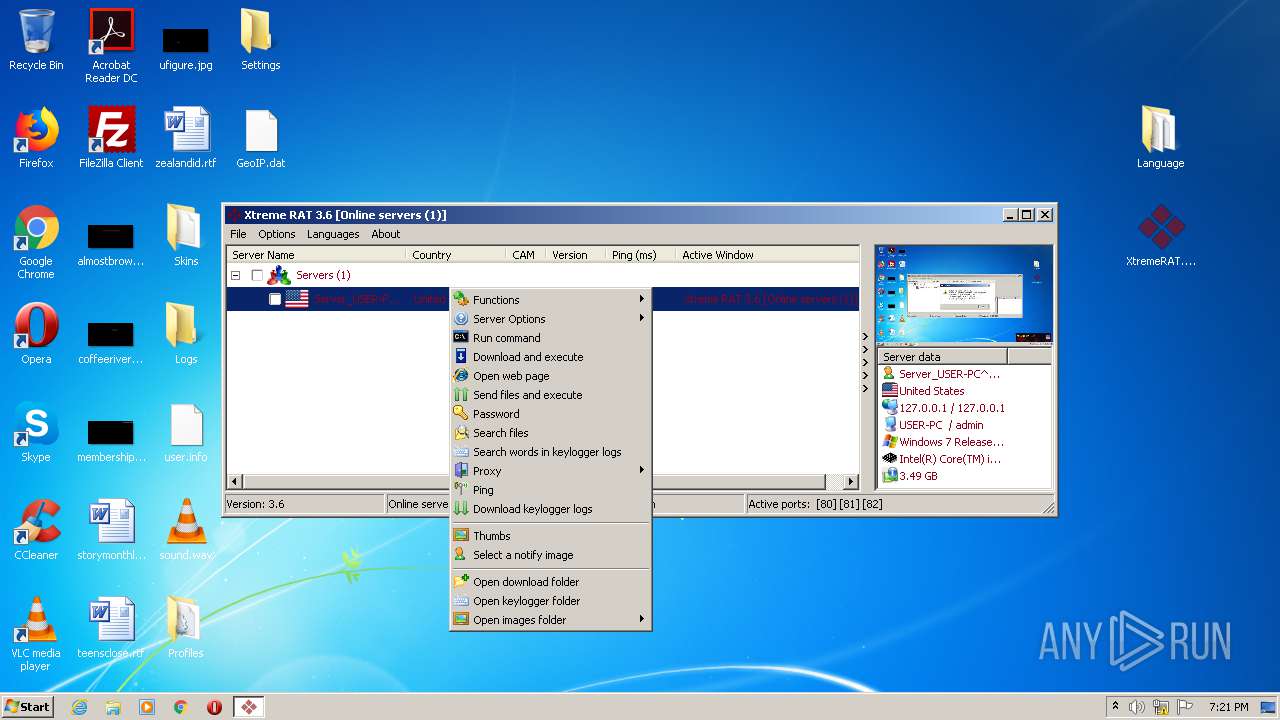
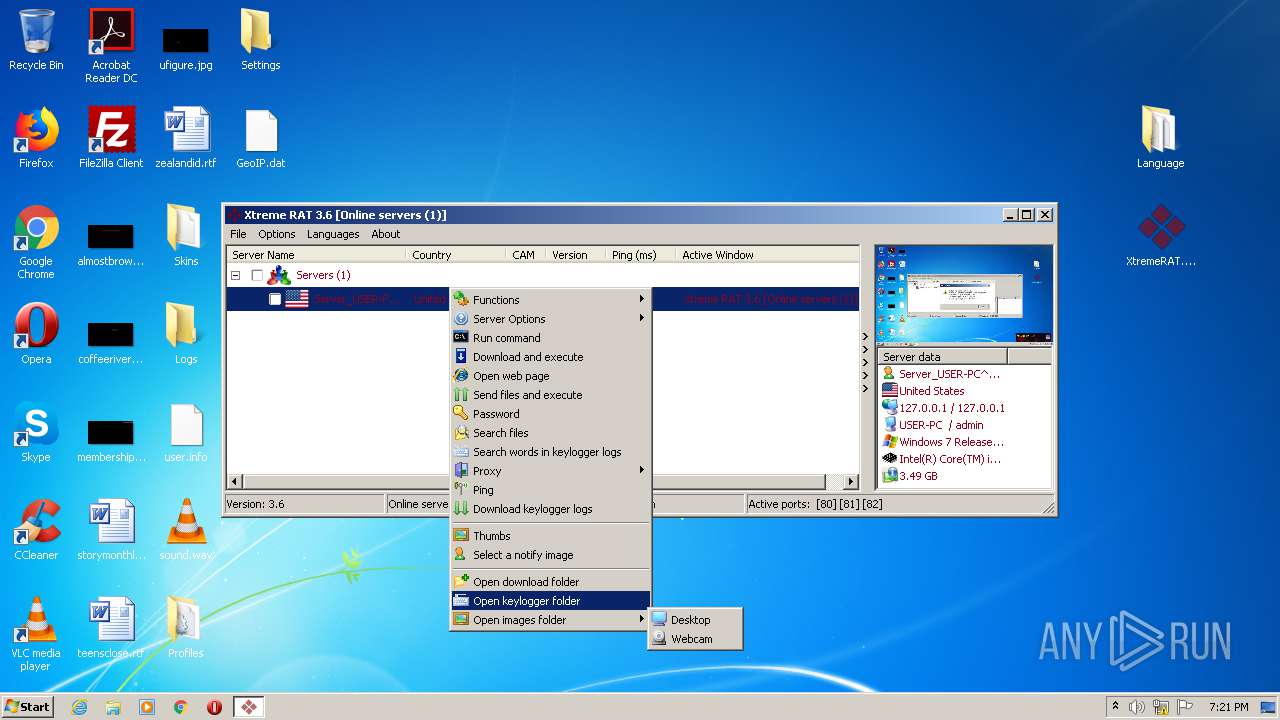
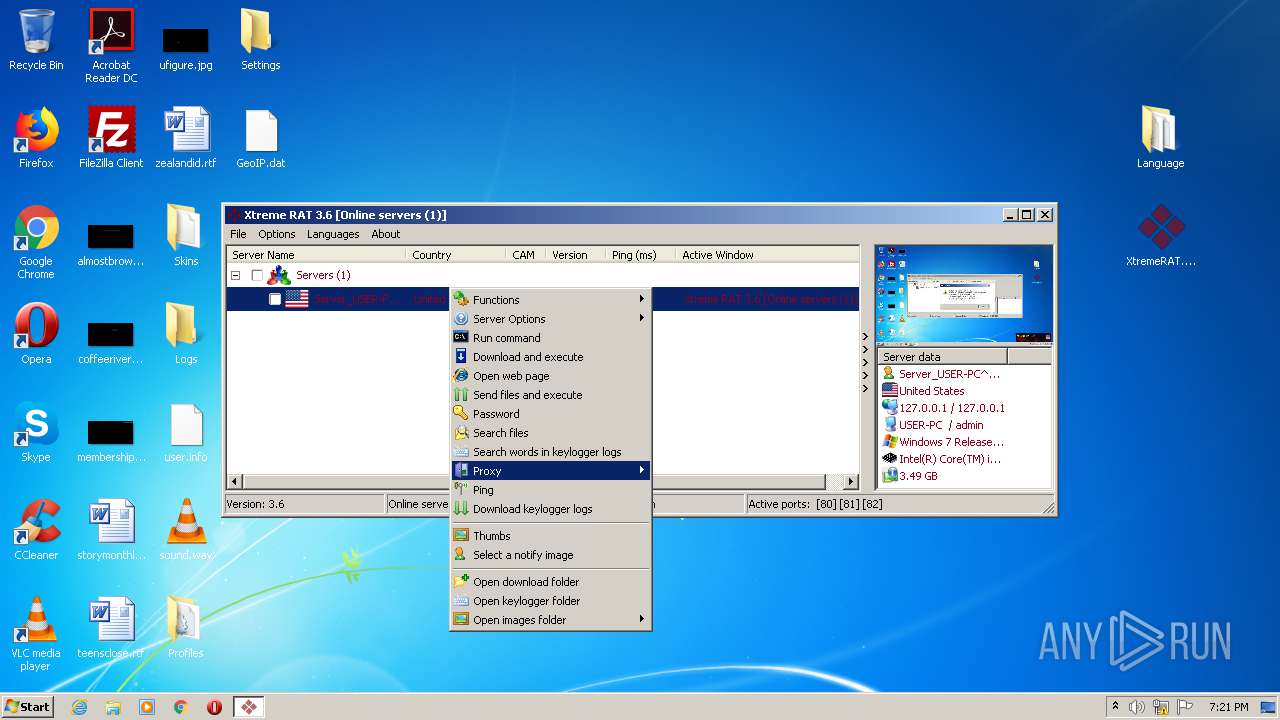
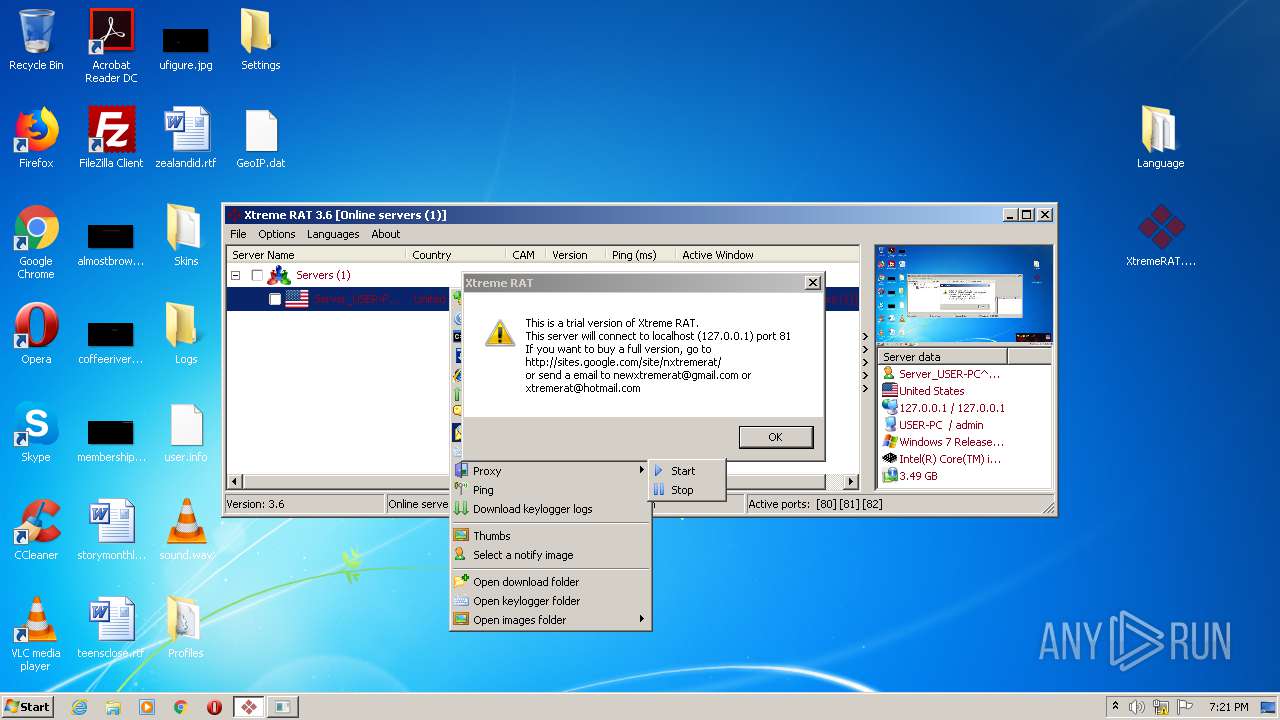
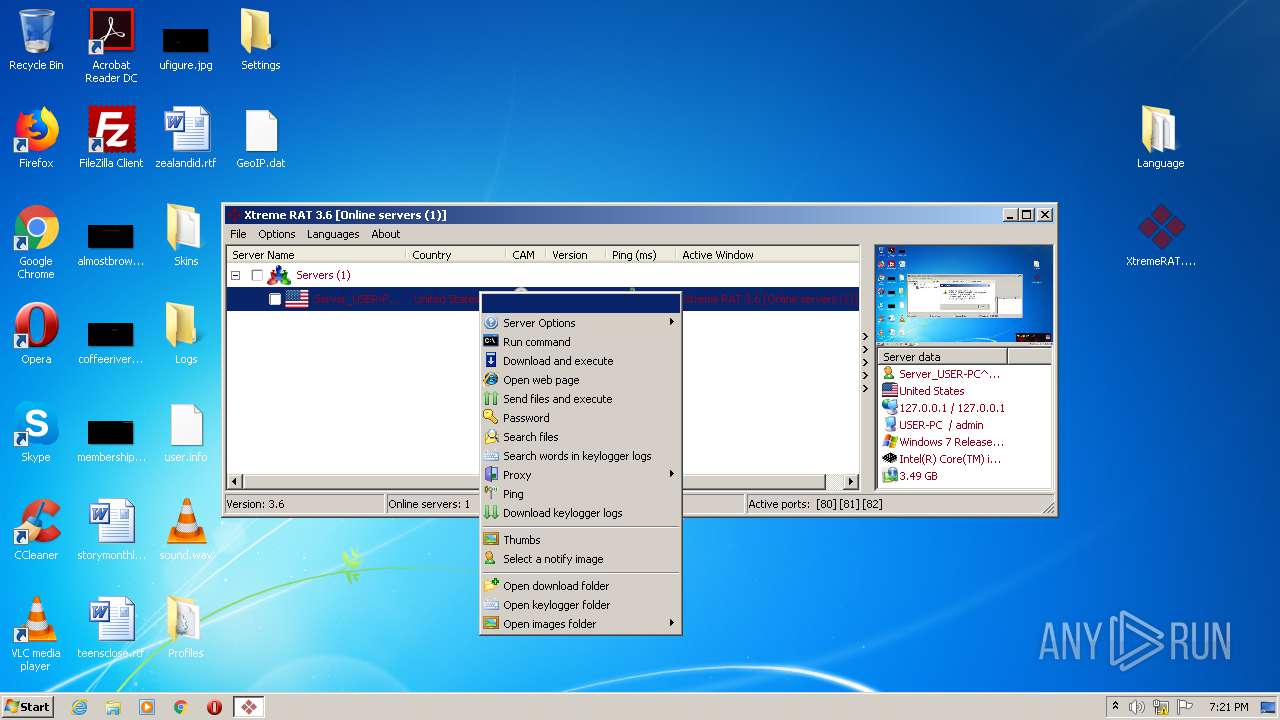
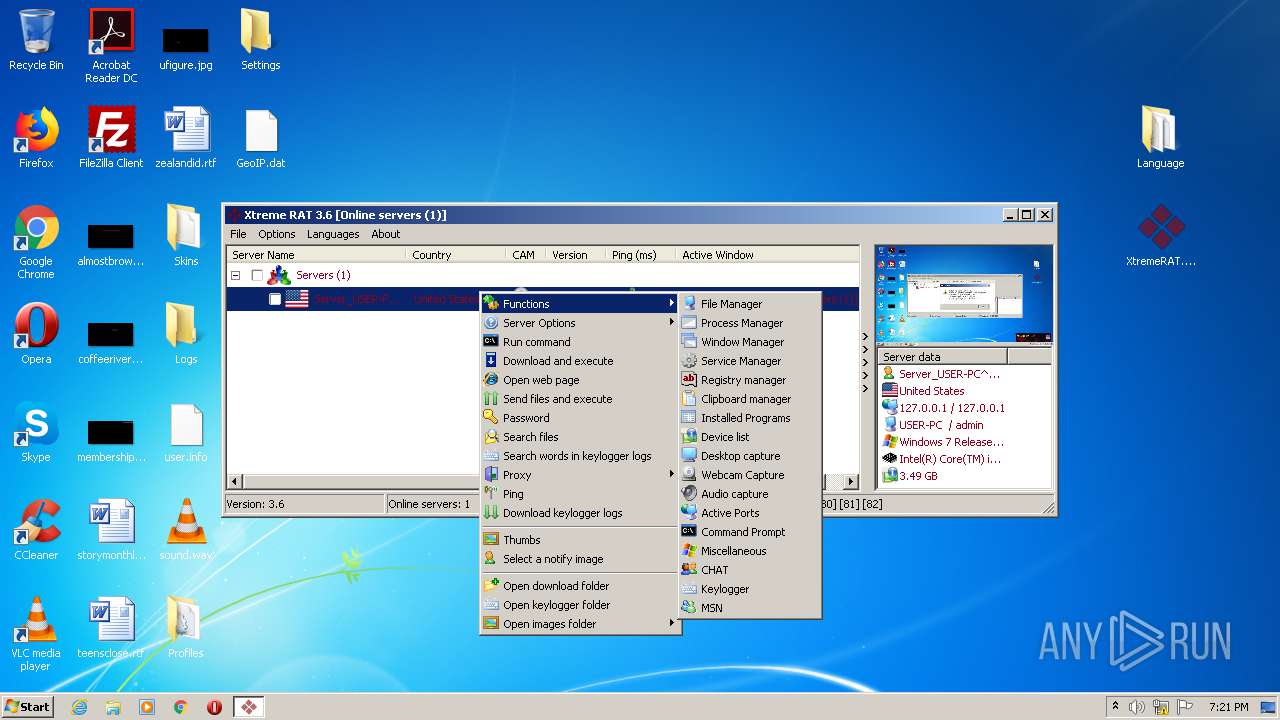
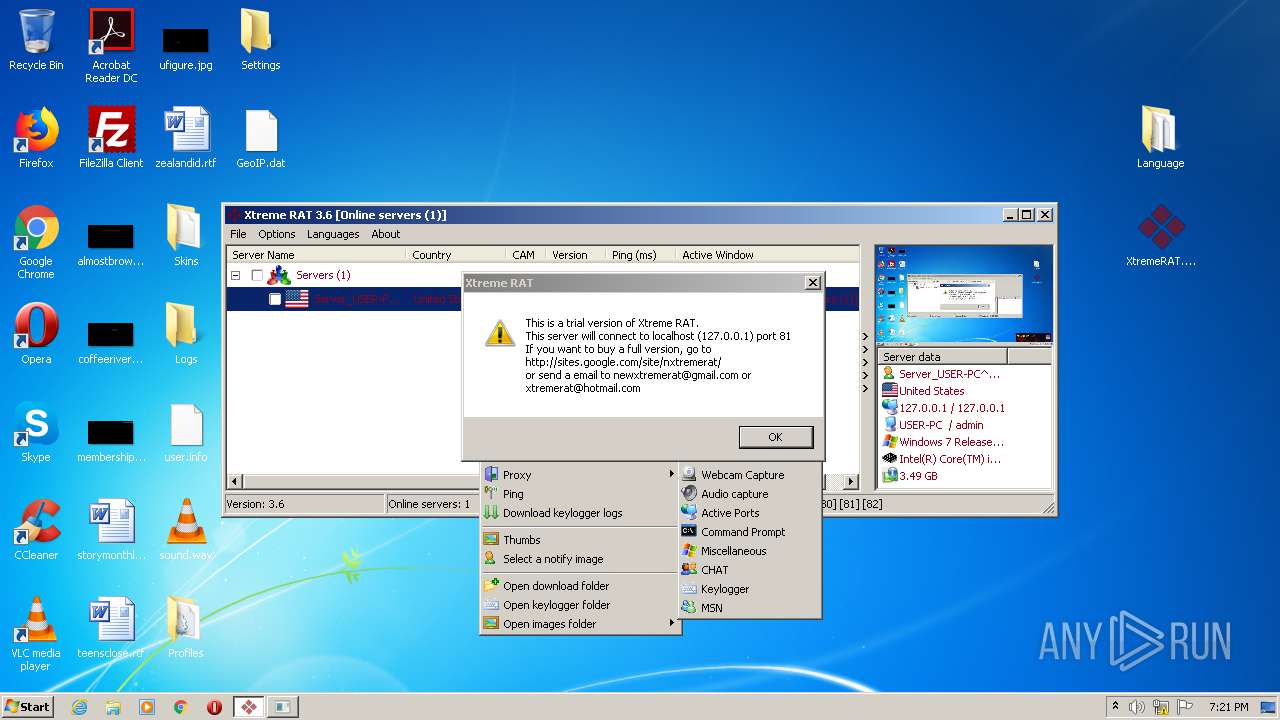
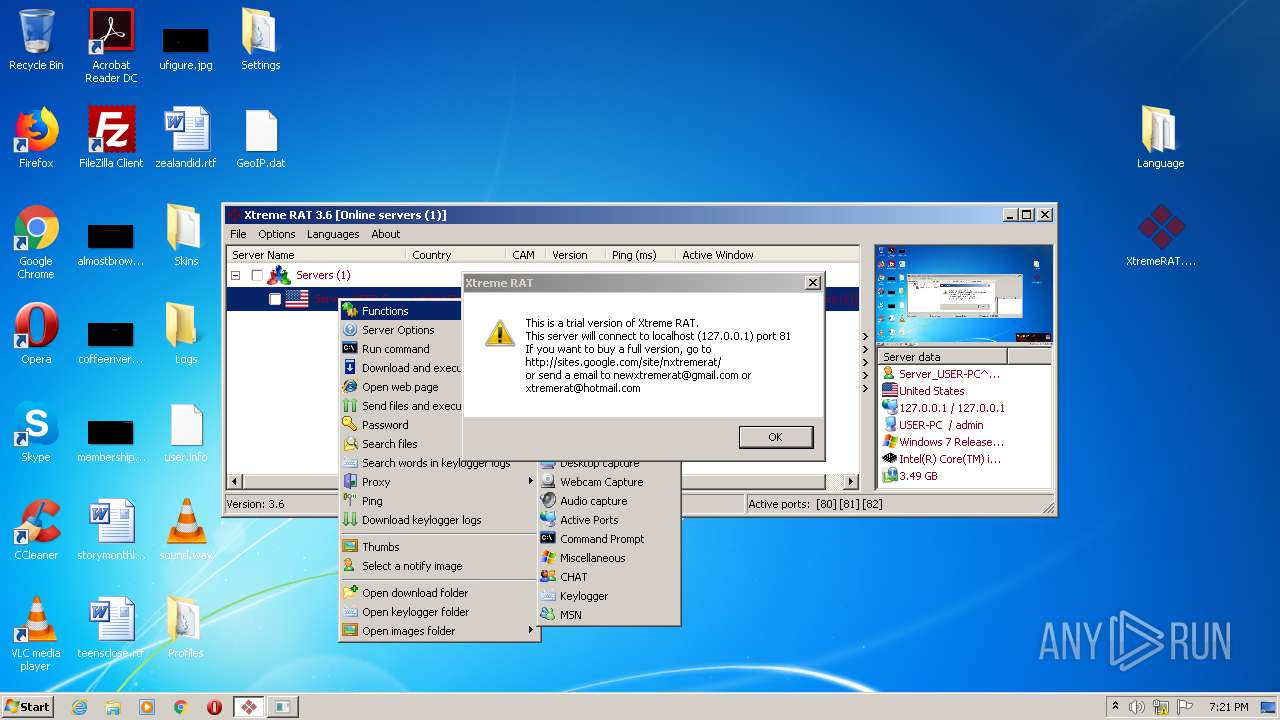
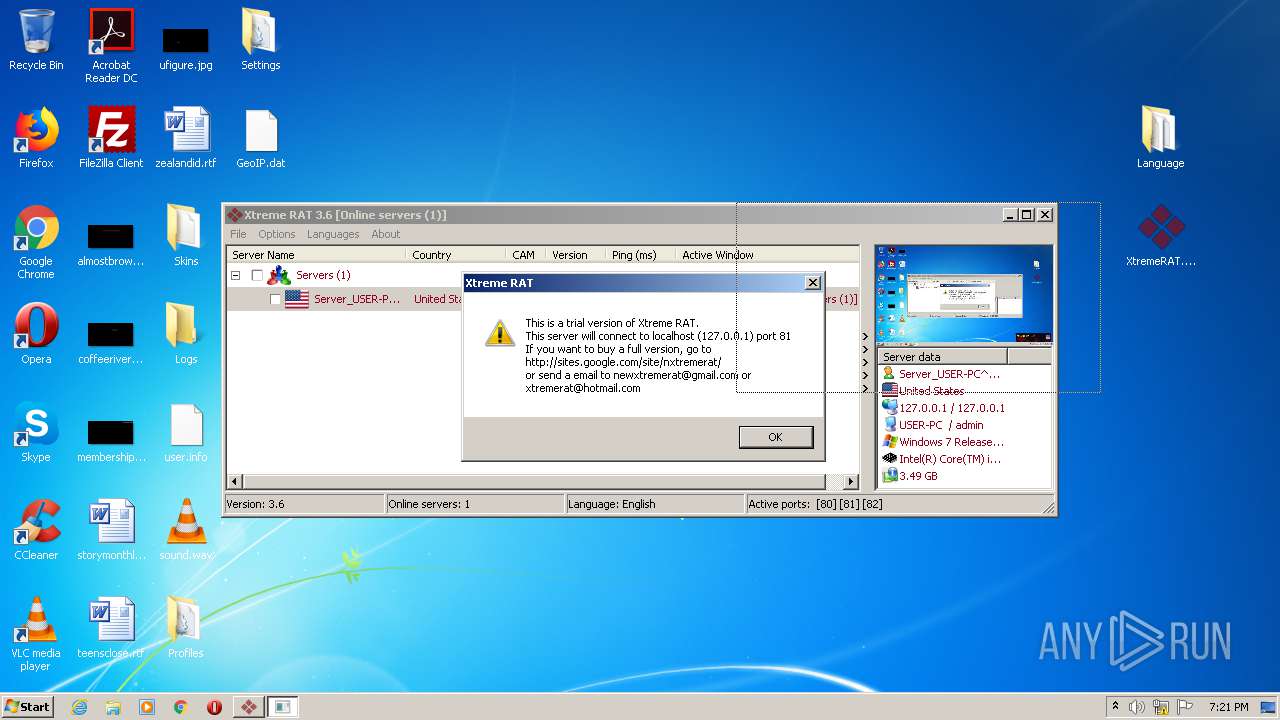
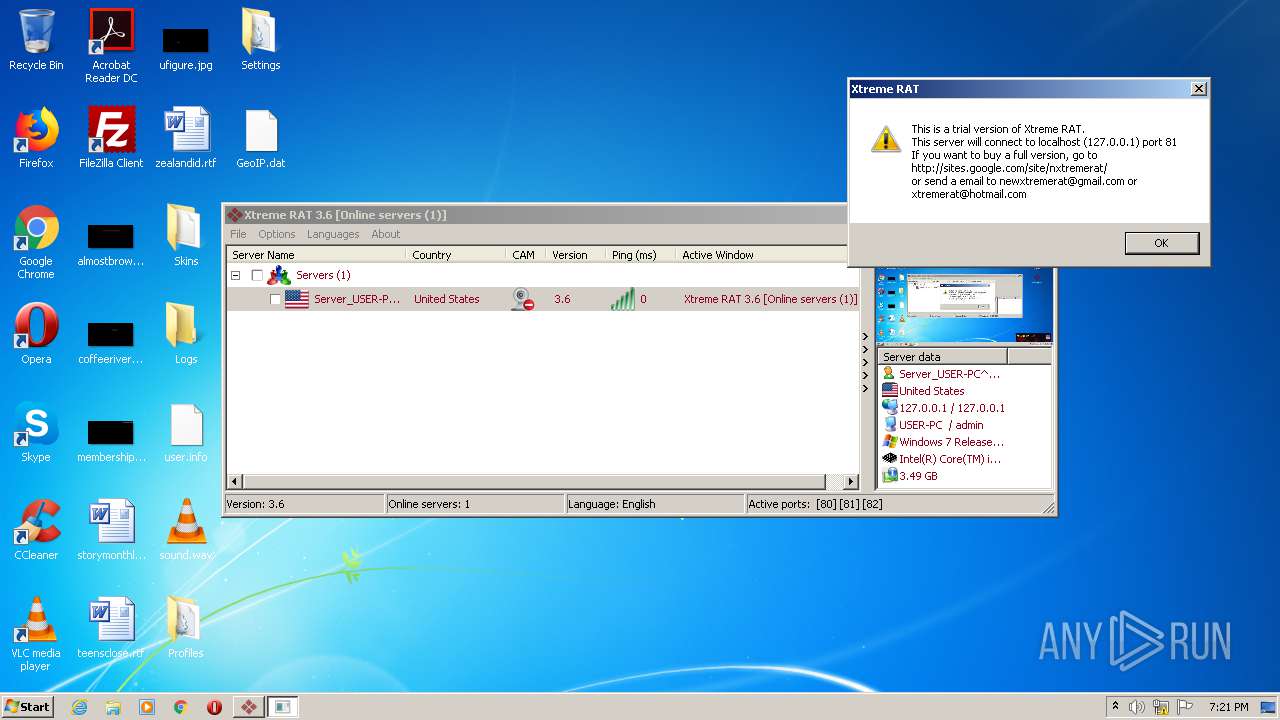
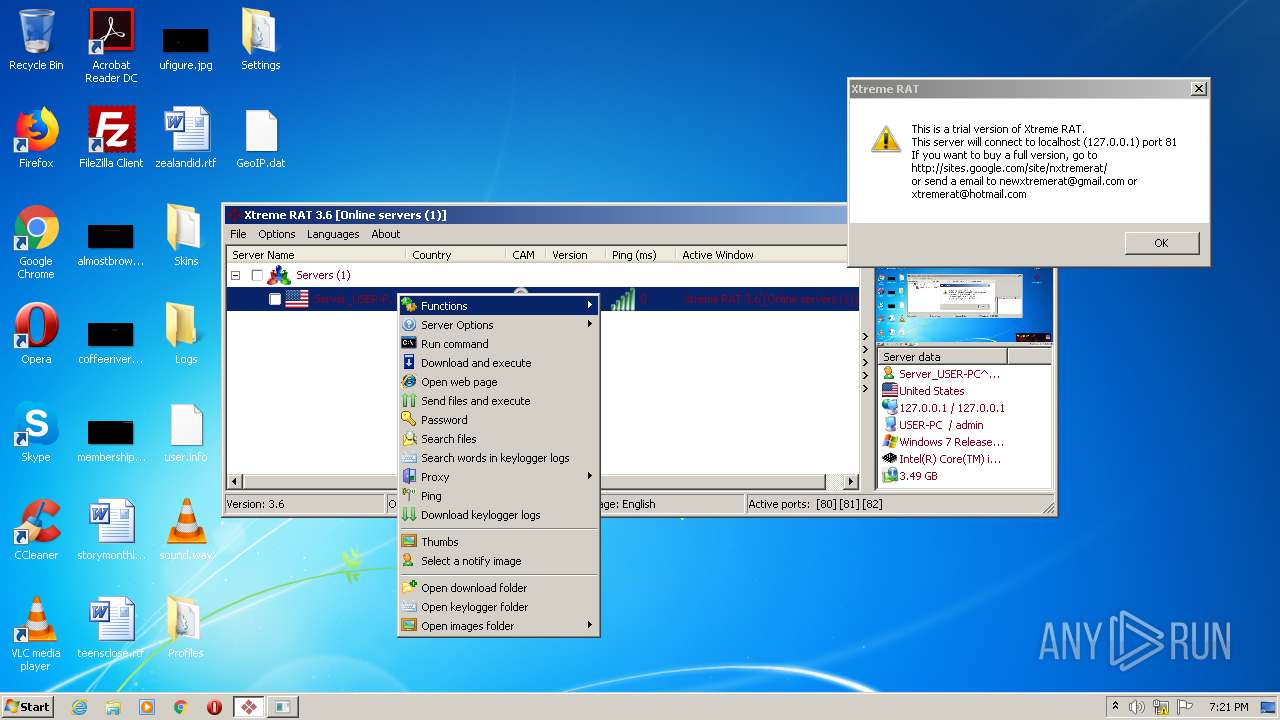
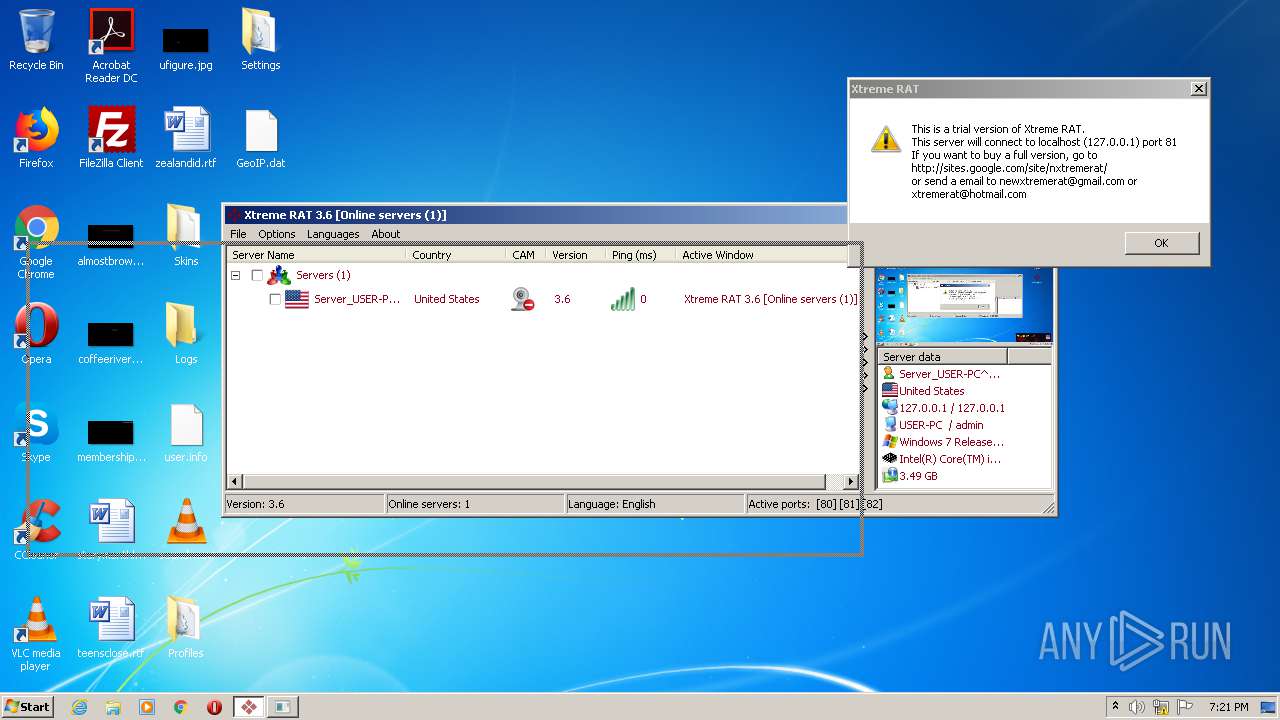
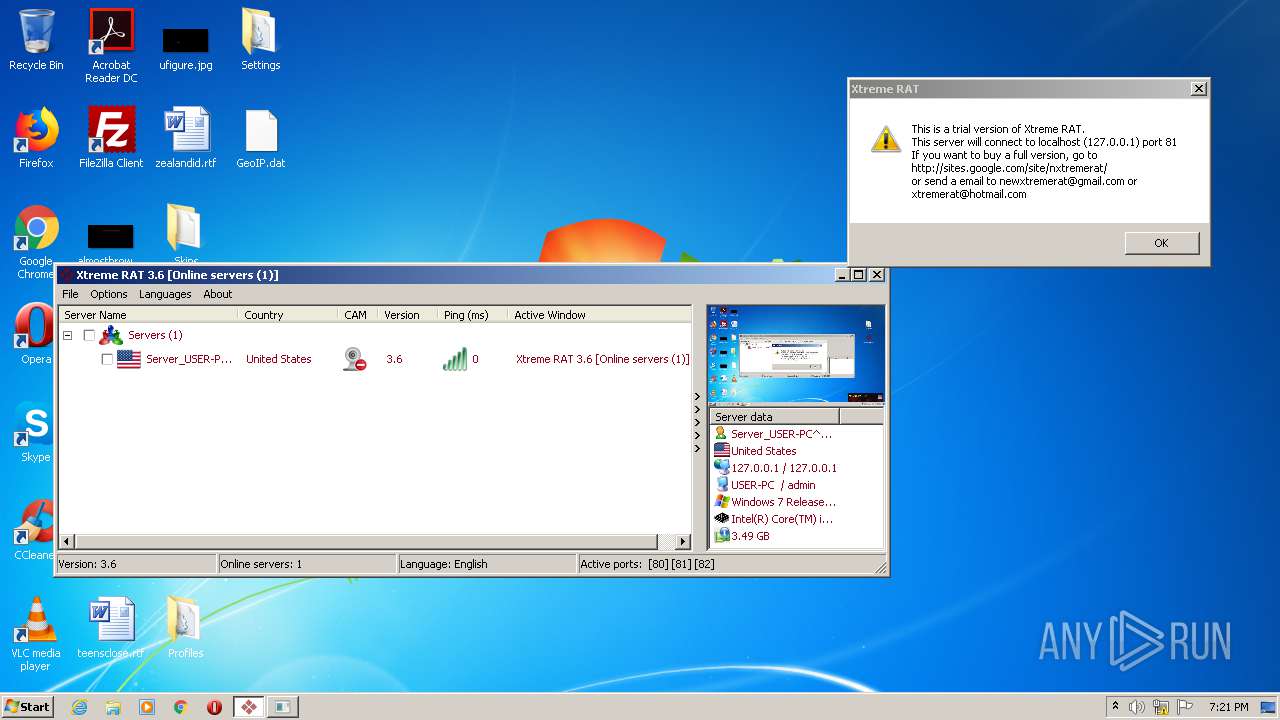
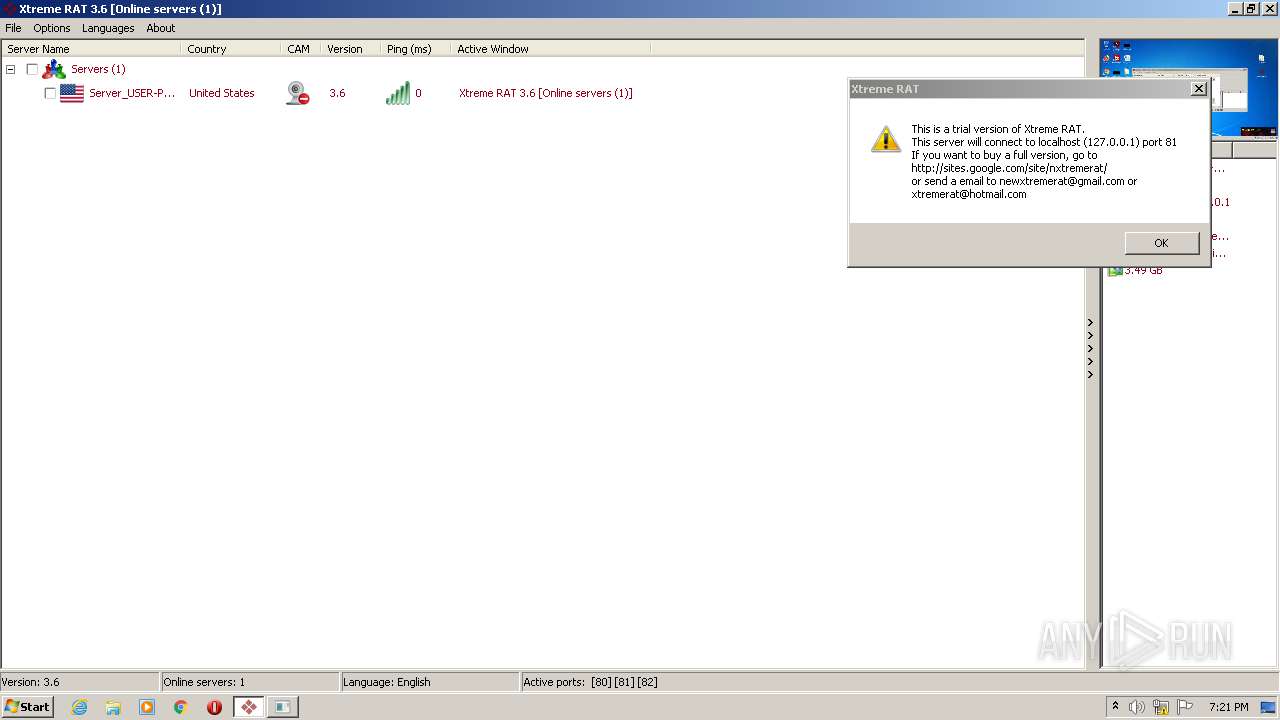
MALICIOUS
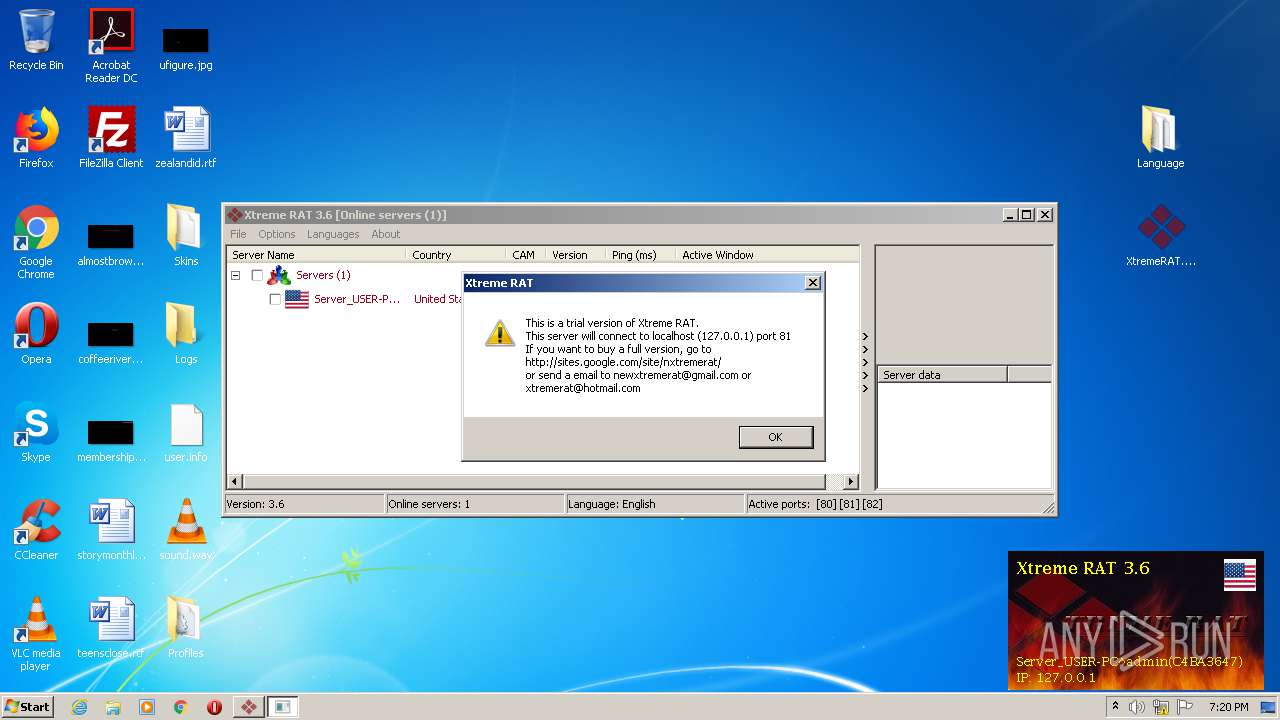
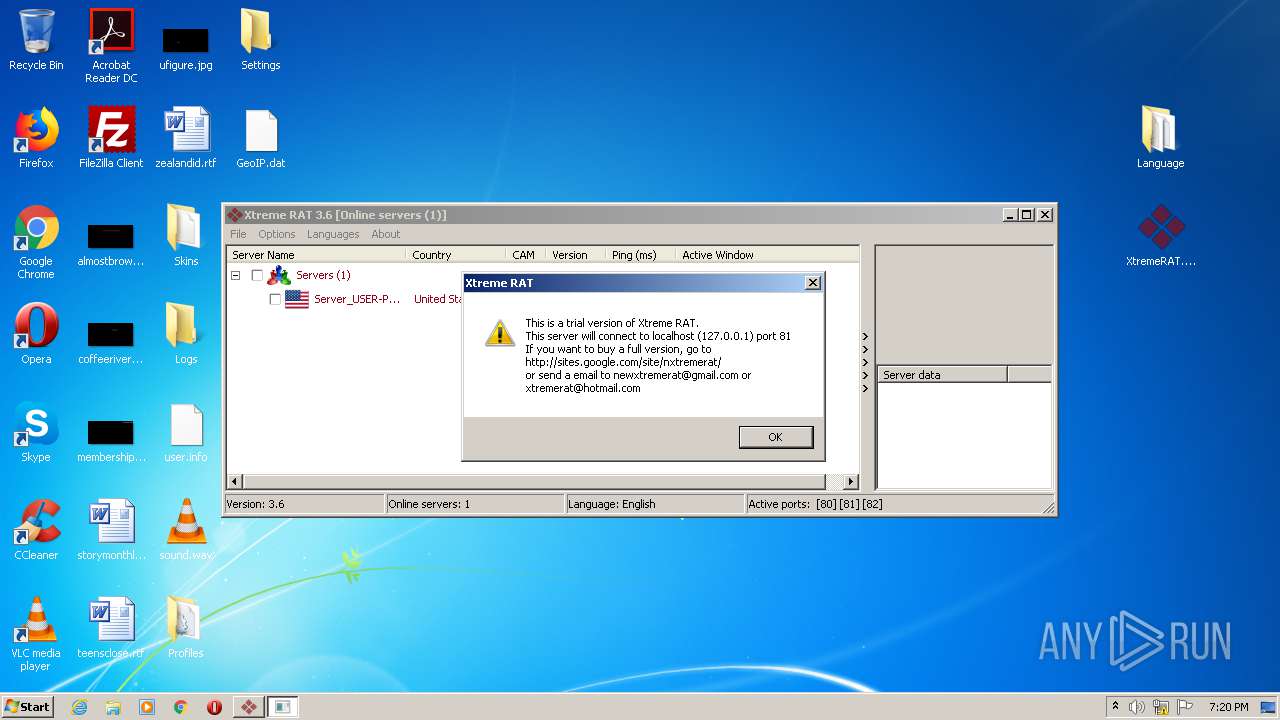
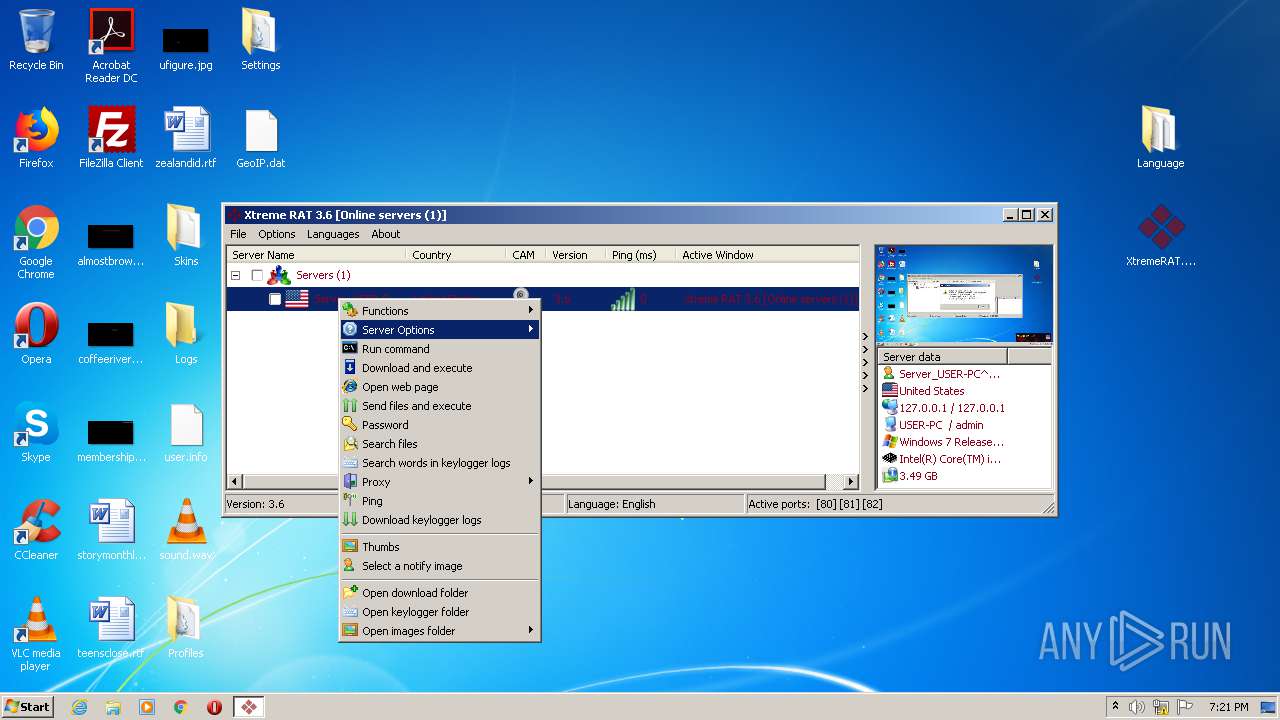
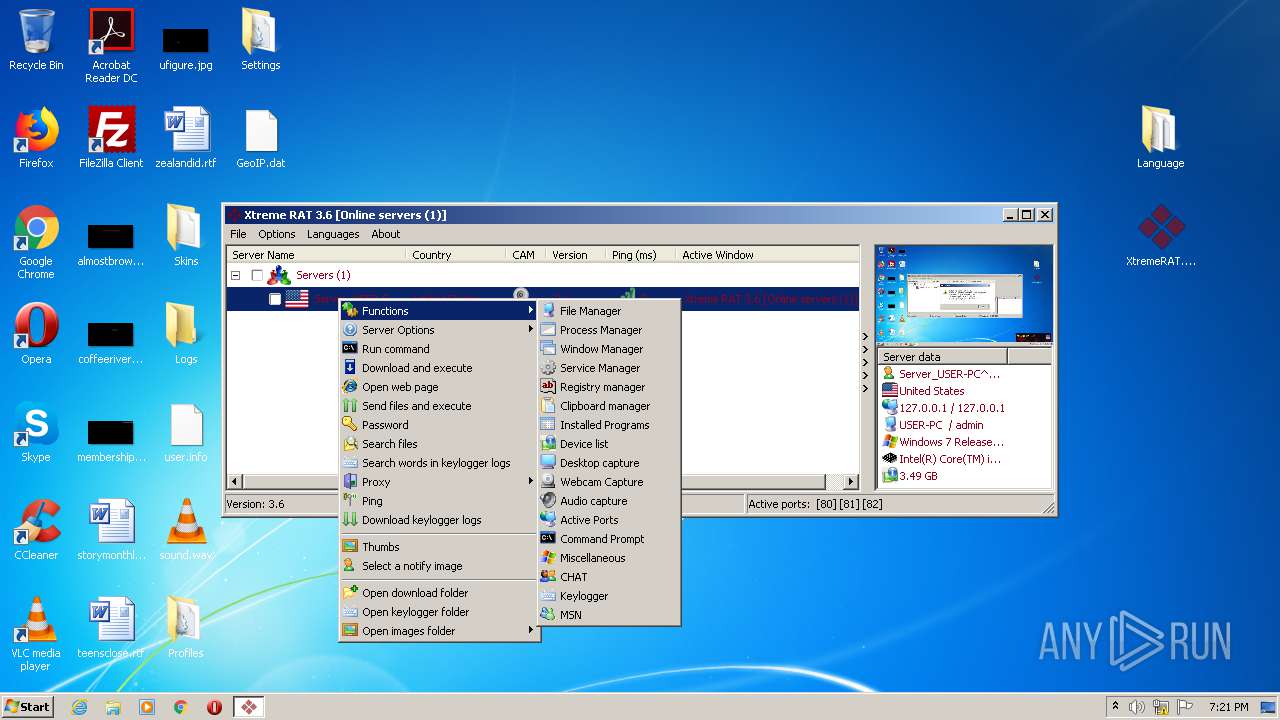
Application was dropped or rewritten from another process
- XtremeRAT.exe (PID: 3964)
- server.exe (PID: 3344)
- Server.exe (PID: 3016)
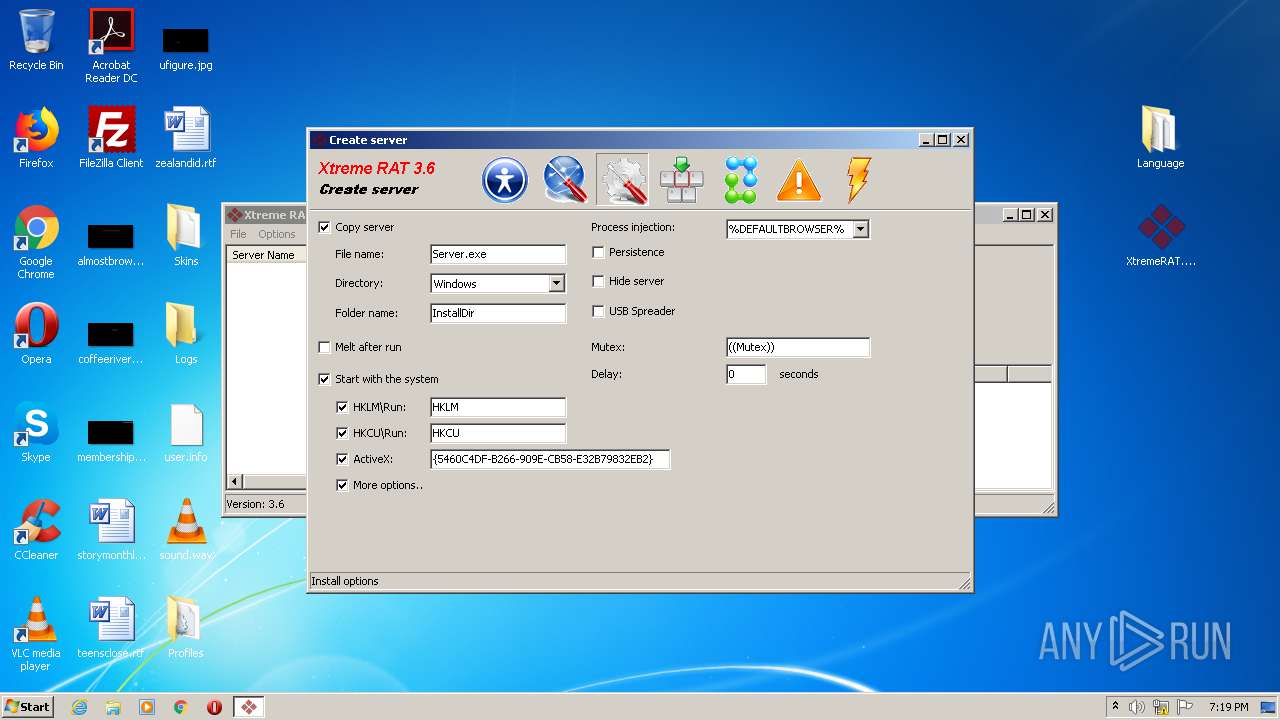
Changes the autorun value in the registry
- server.exe (PID: 3344)
- Server.exe (PID: 3016)
- iexplore.exe (PID: 3232)
SUSPICIOUS
Executable content was dropped or overwritten
- UPXfile.exe (PID: 3352)
- XtremeRAT.exe (PID: 3964)
- server.exe (PID: 3344)
Creates files in the user directory
- server.exe (PID: 3344)
- Server.exe (PID: 3016)
Starts Internet Explorer
- server.exe (PID: 3344)
- Server.exe (PID: 3016)
Reads CPU info
- iexplore.exe (PID: 3232)
INFO
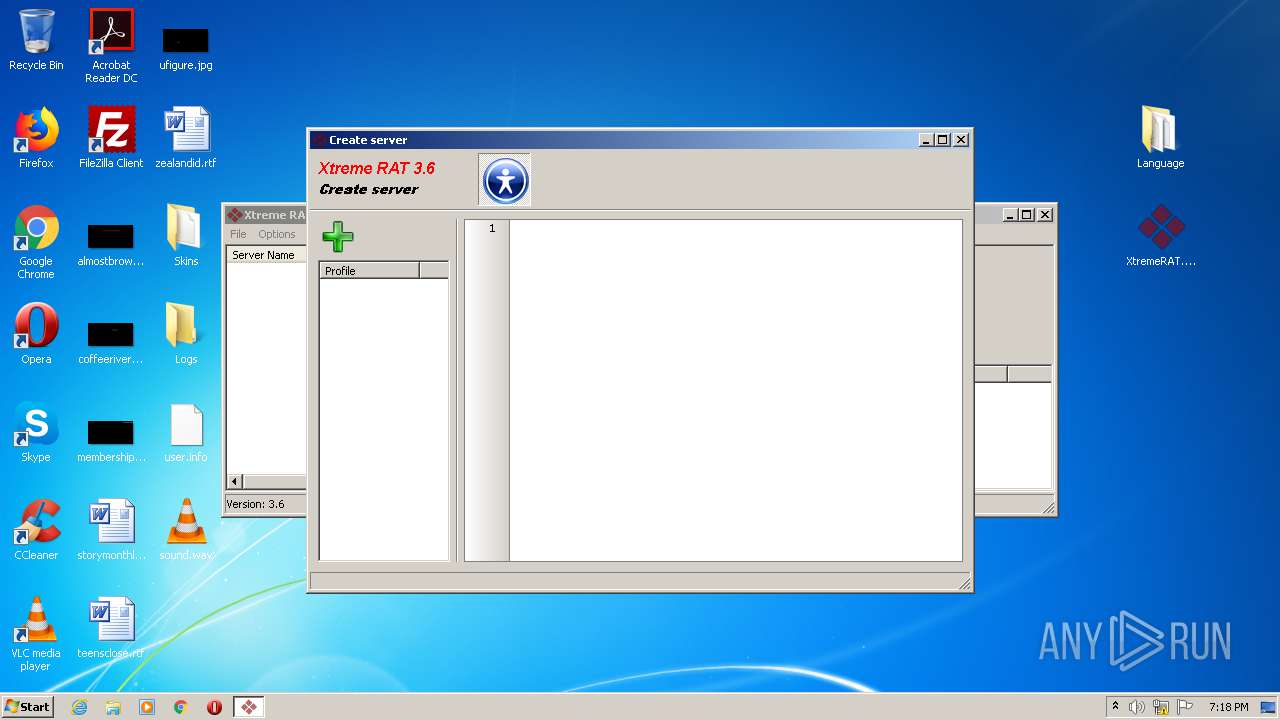
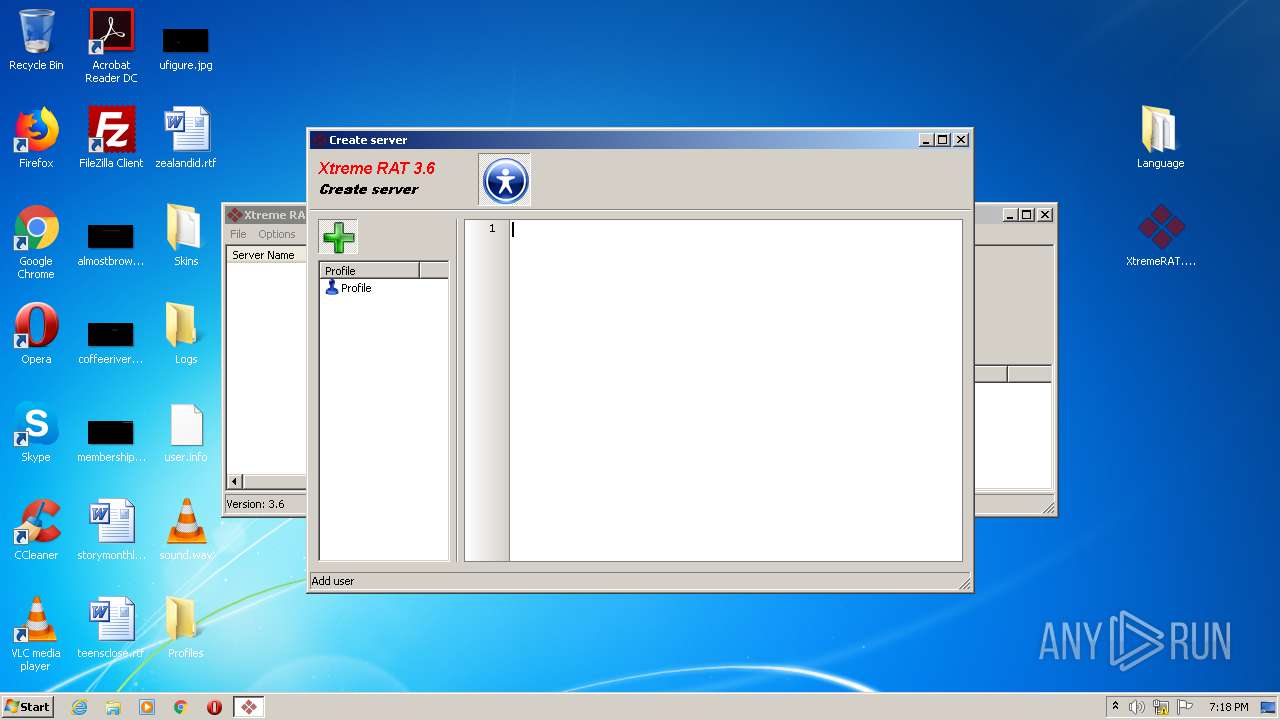
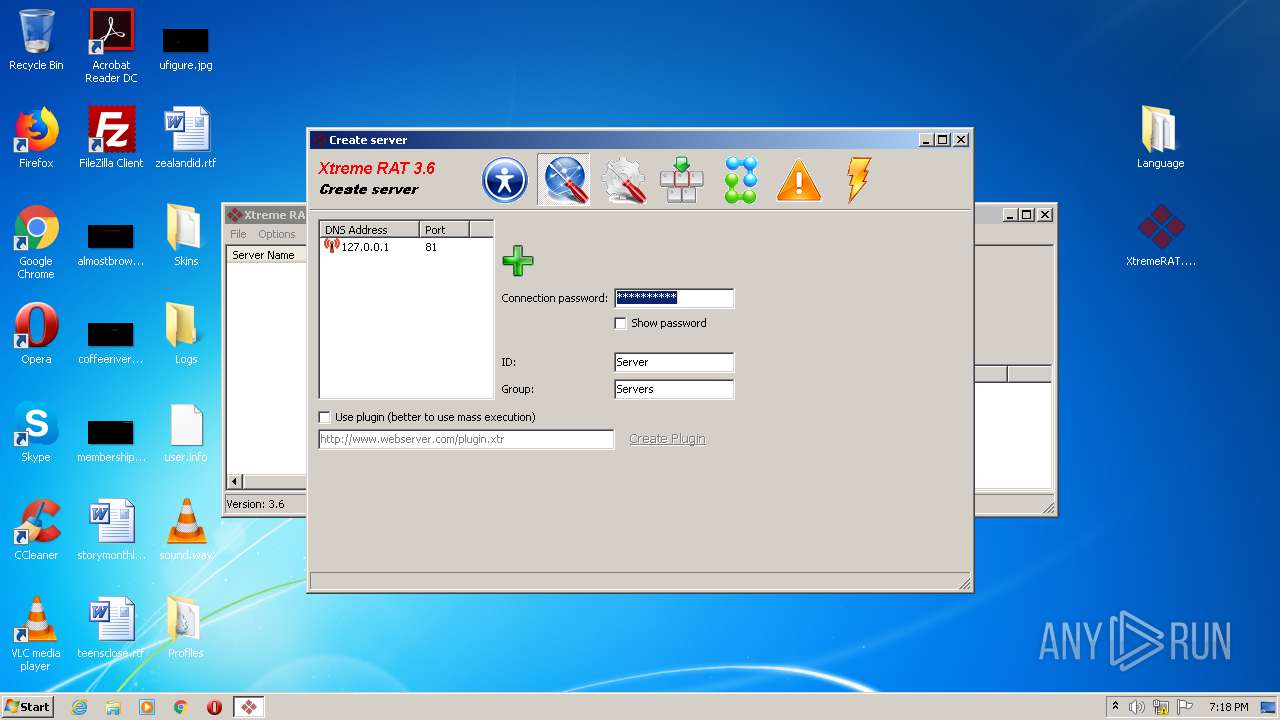
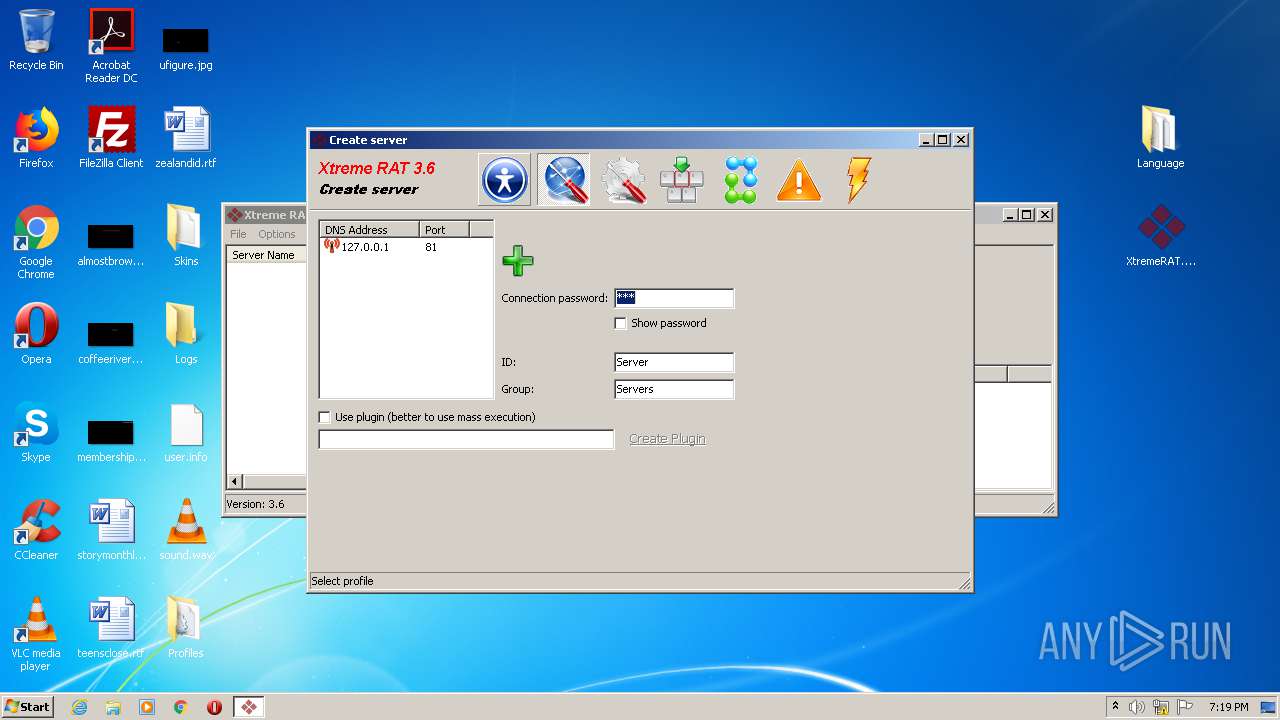
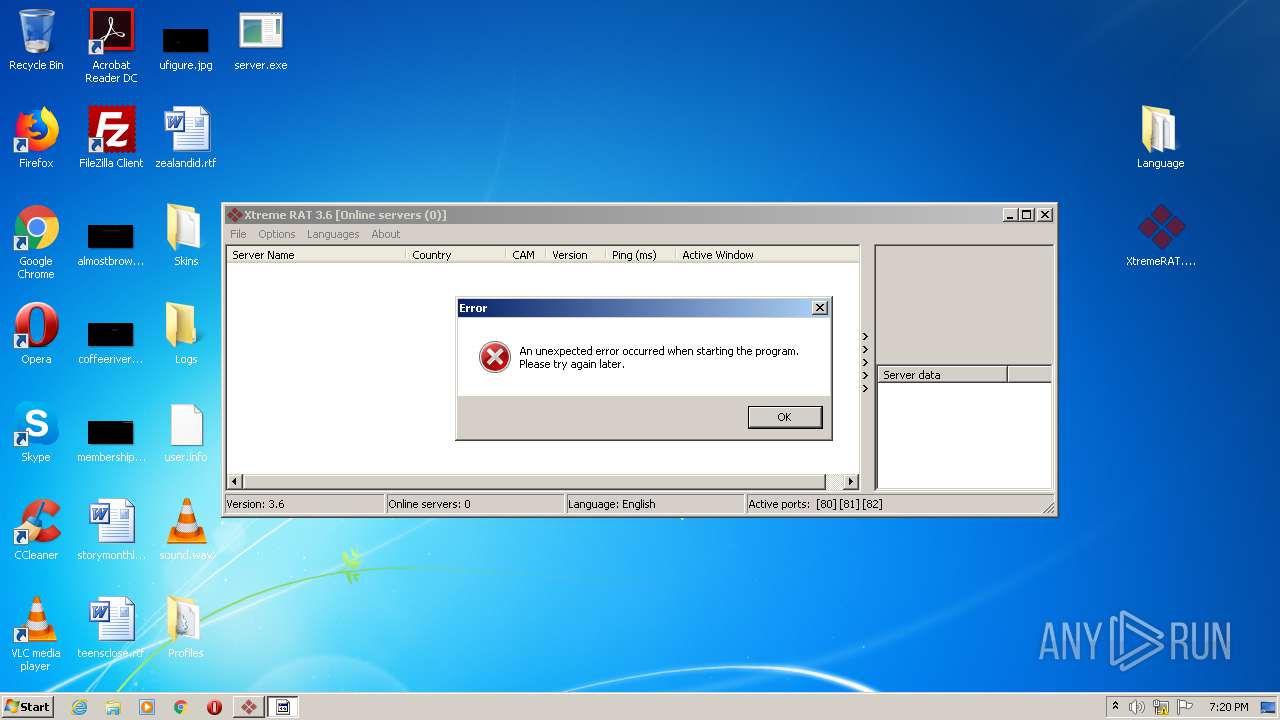
Manual execution by user
- XtremeRAT.exe (PID: 3964)
- server.exe (PID: 3344)
Creates files in the user directory
- iexplore.exe (PID: 2956)
Reads Internet Cache Settings
- iexplore.exe (PID: 2956)
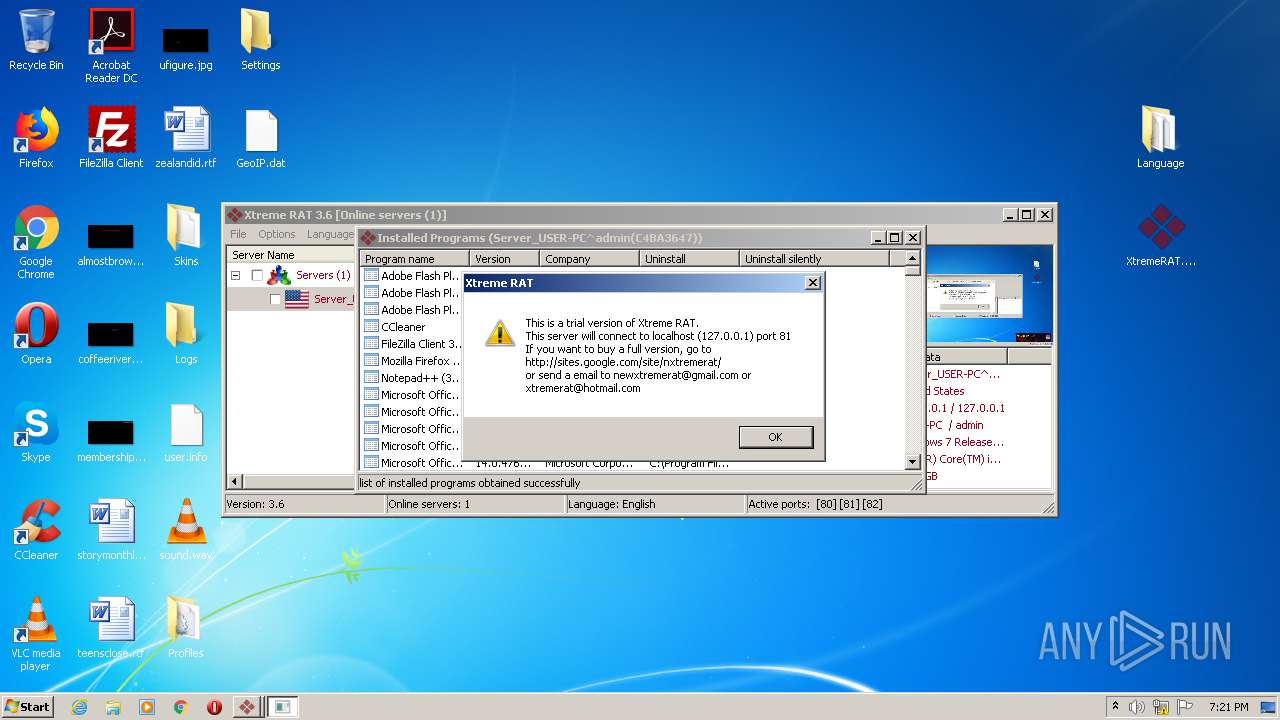
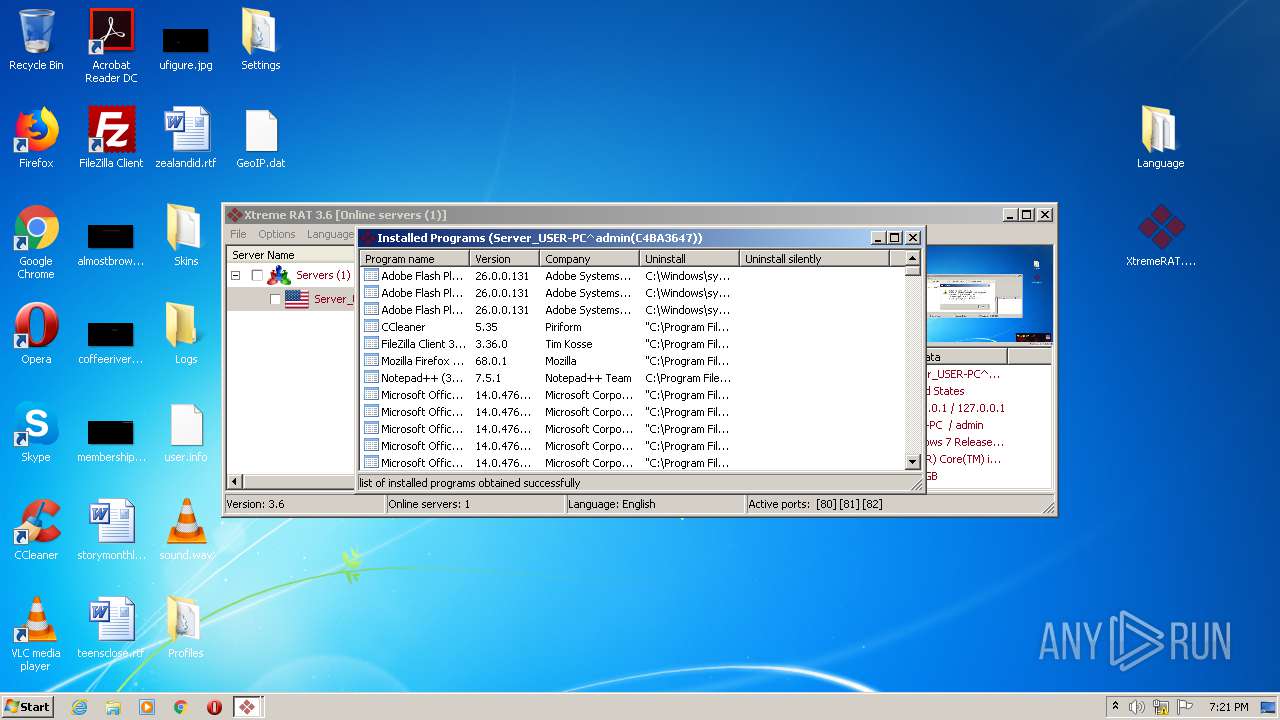
Searches for installed software
- iexplore.exe (PID: 3232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
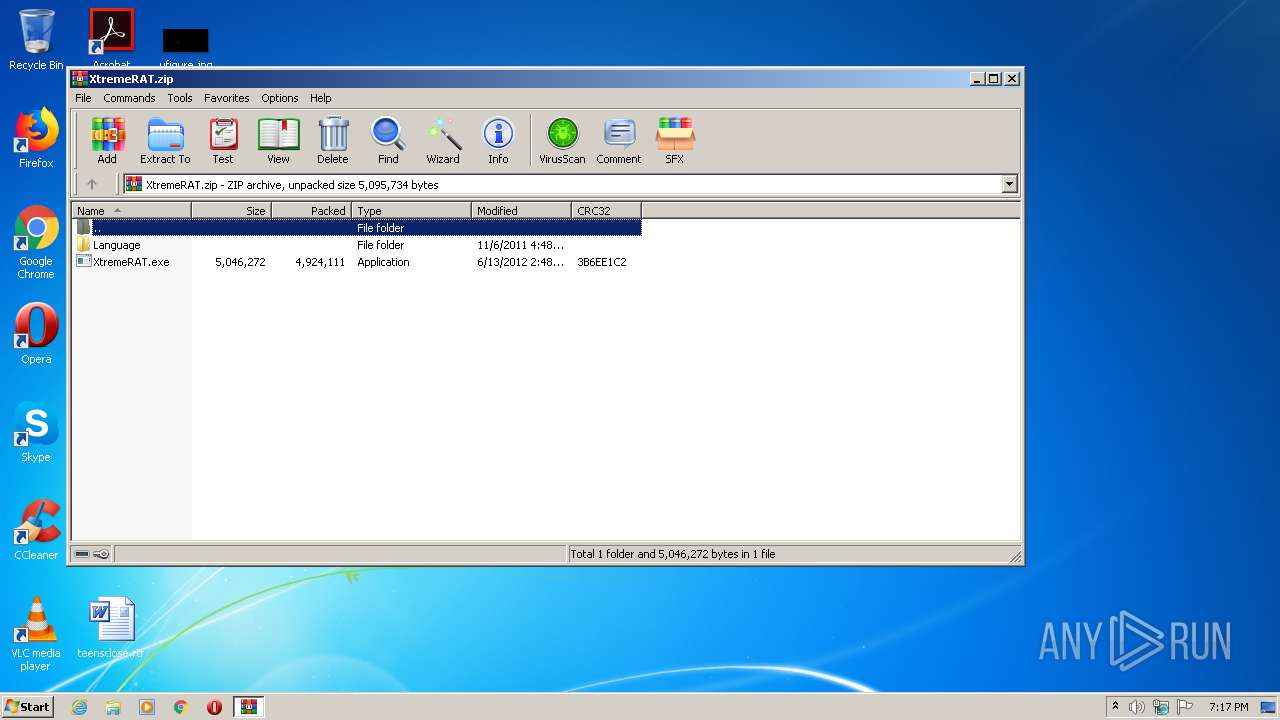
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2012:06:13 14:48:13 |
| ZipCRC: | 0x3b6ee1c2 |
| ZipCompressedSize: | 4924111 |
| ZipUncompressedSize: | 5046272 |
| ZipFileName: | XtremeRAT.exe |
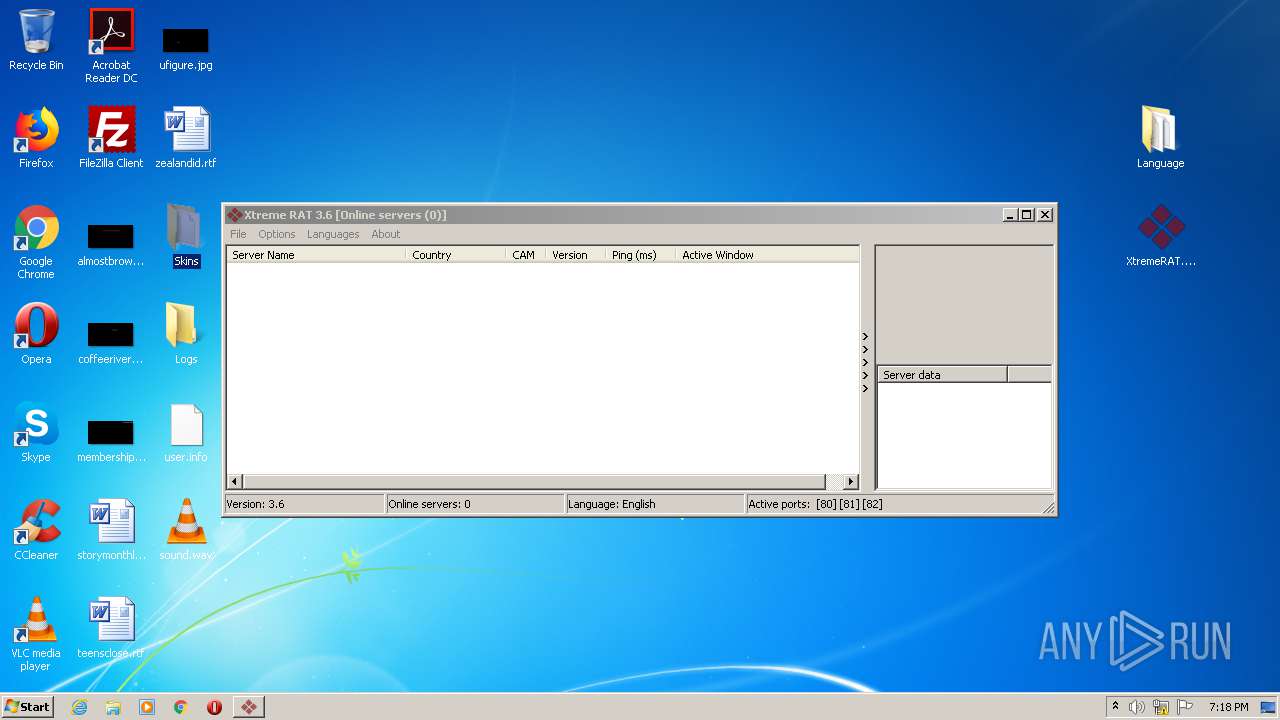
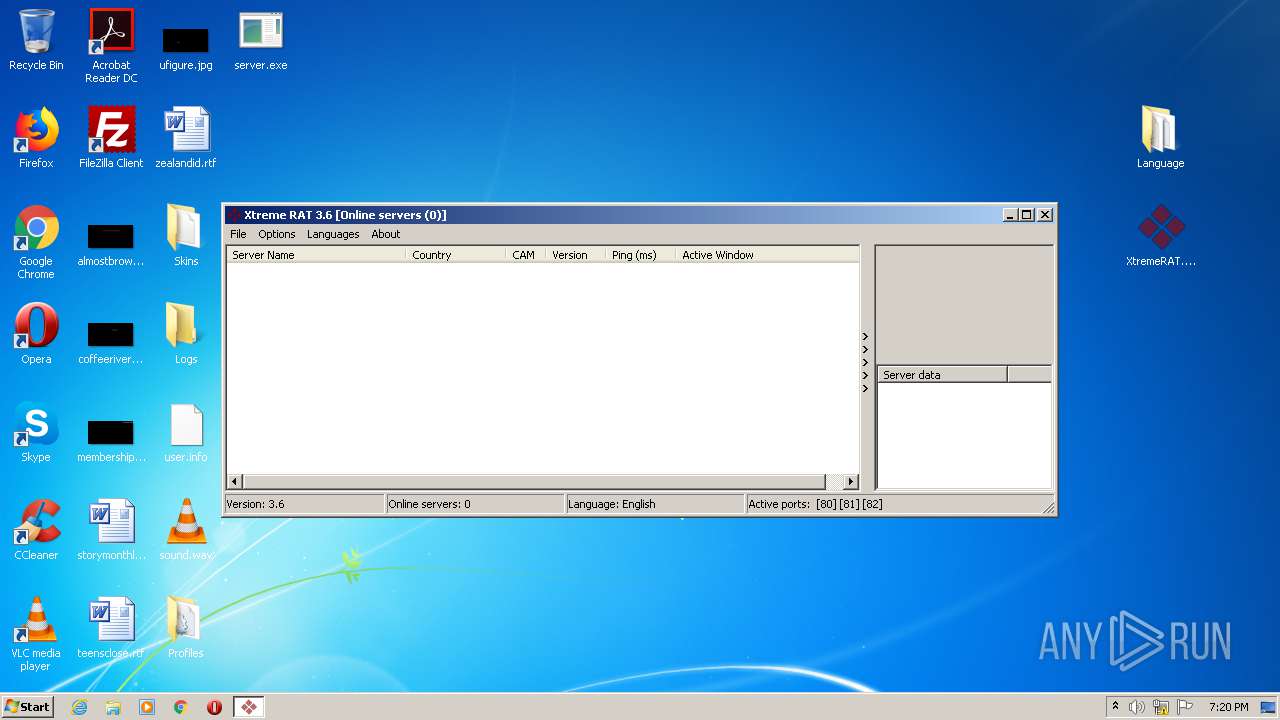
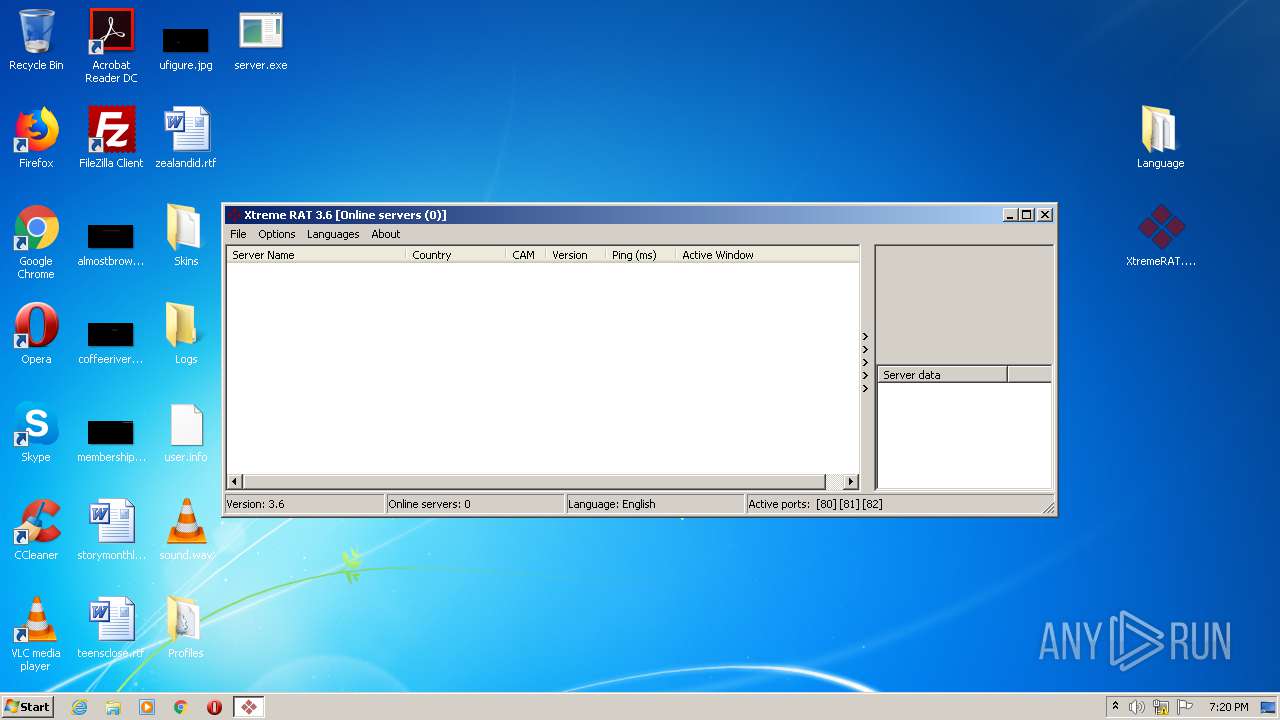
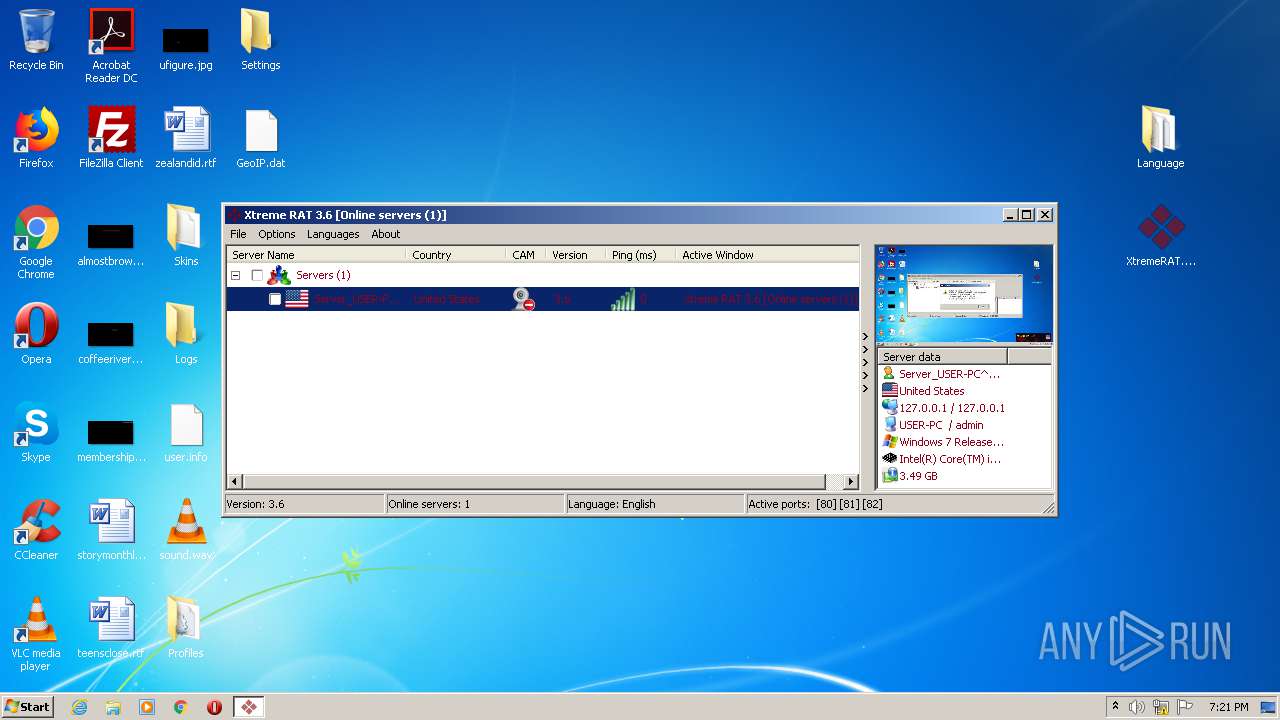
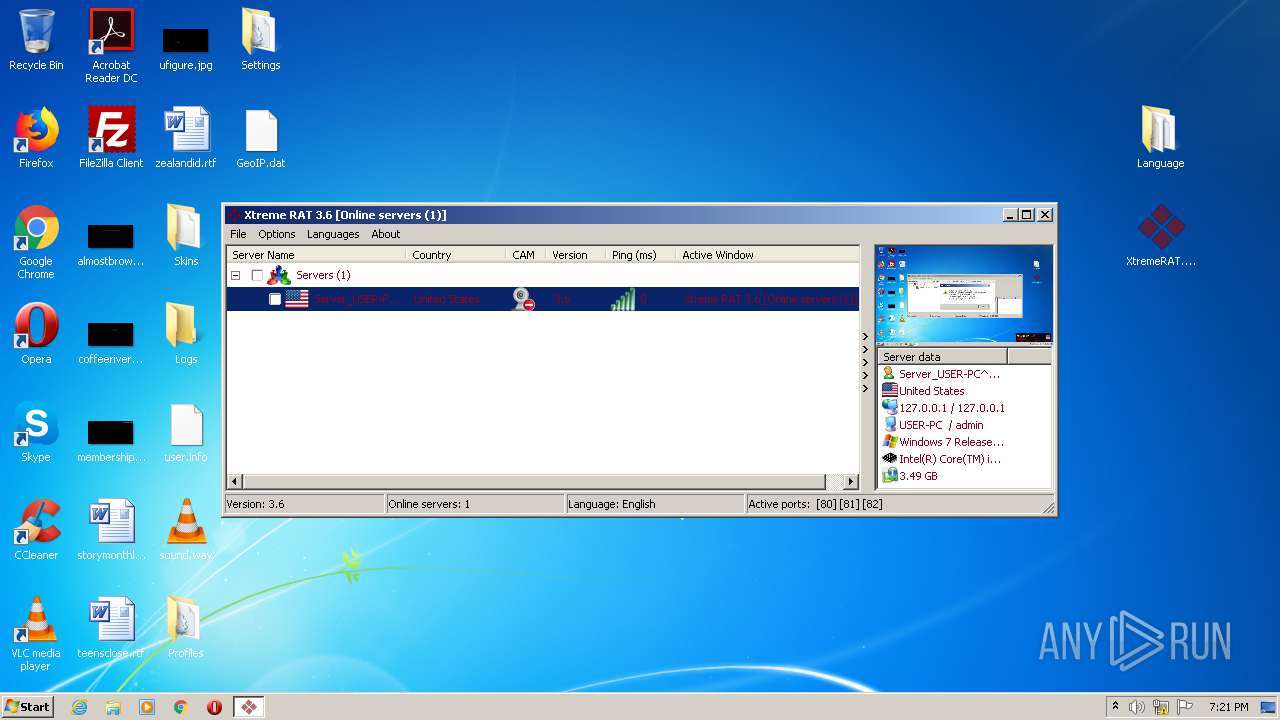
Total processes
55
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
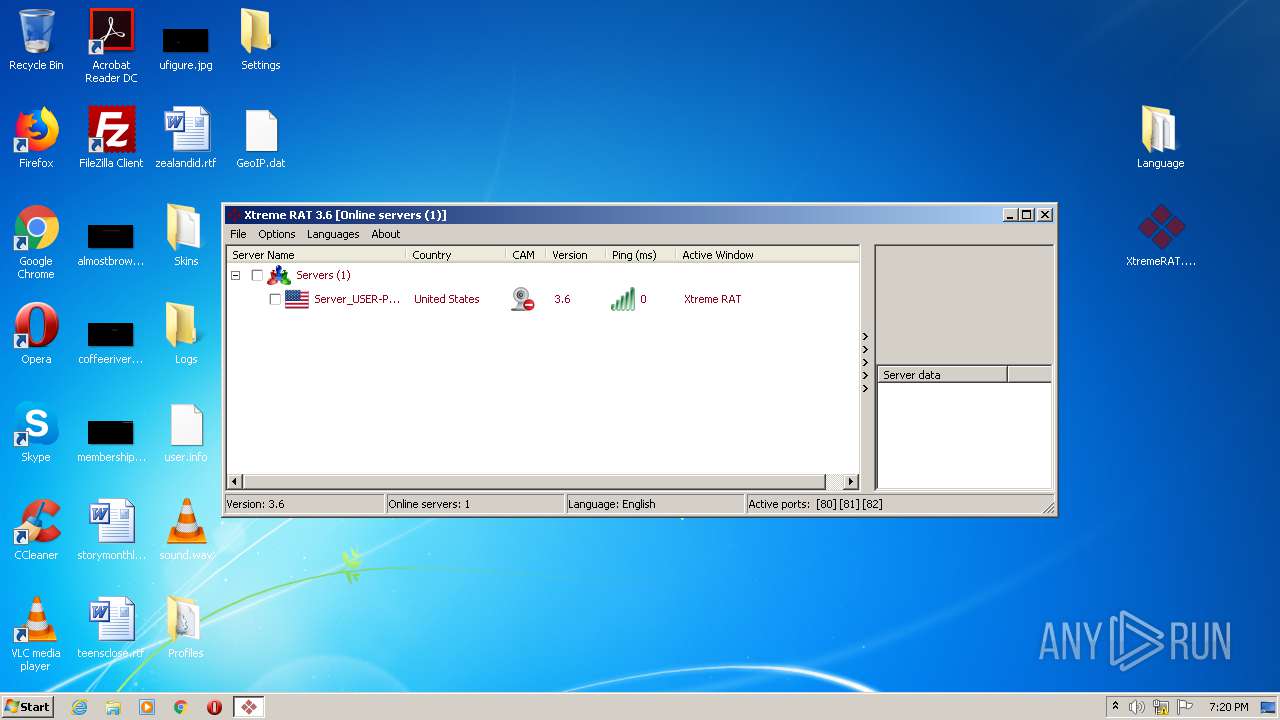
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2956 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | server.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3016 | "C:\InstallDir\Server.exe" | C:\InstallDir\Server.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3232 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | Server.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
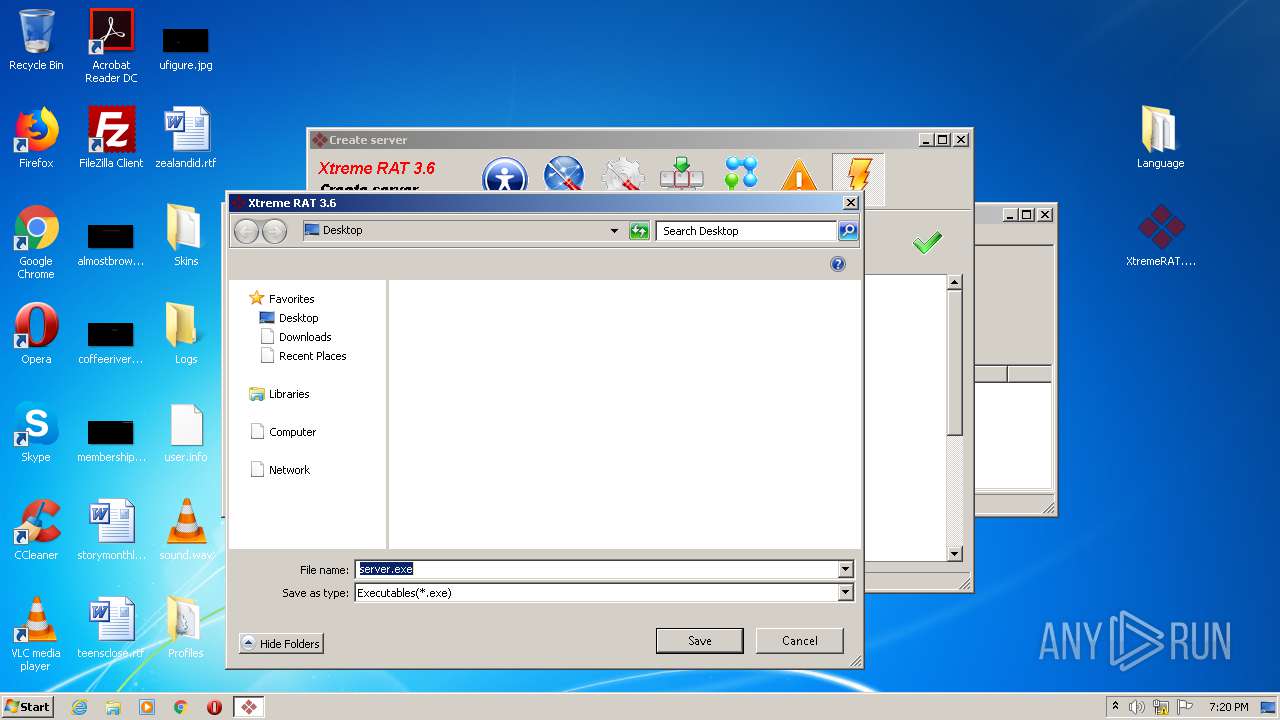
| 3344 | "C:\Users\admin\Desktop\server.exe" | C:\Users\admin\Desktop\server.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3352 | "C:\Users\admin\AppData\Local\Temp\UPXfile.exe" "C:\Users\admin\Desktop\server.exe" | C:\Users\admin\AppData\Local\Temp\UPXfile.exe | XtremeRAT.exe | ||||||||||||
User: admin Company: The UPX Team http://upx.sf.net Integrity Level: MEDIUM Description: UPX executable packer Exit code: 0 Version: 3.07 (2010-09-08) Modules
| |||||||||||||||
| 3552 | explorer.exe | C:\Windows\explorer.exe | — | server.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | "C:\Users\admin\Desktop\XtremeRAT.exe" | C:\Users\admin\Desktop\XtremeRAT.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
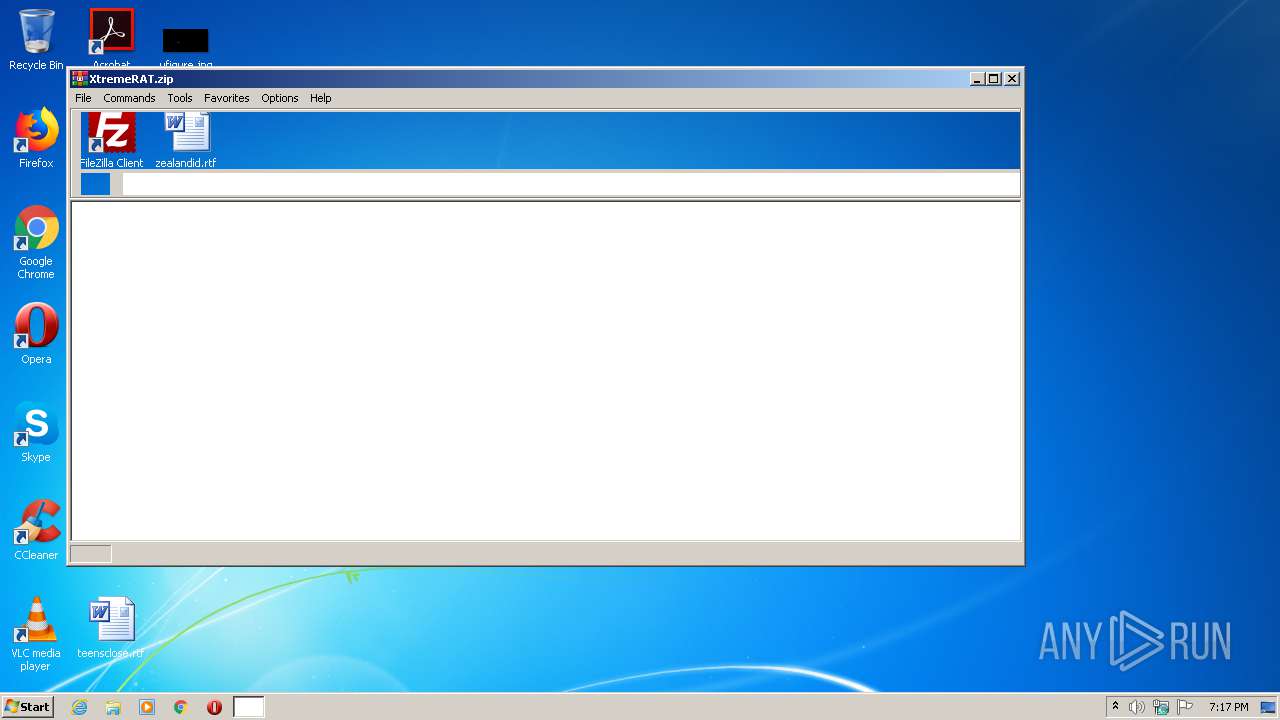
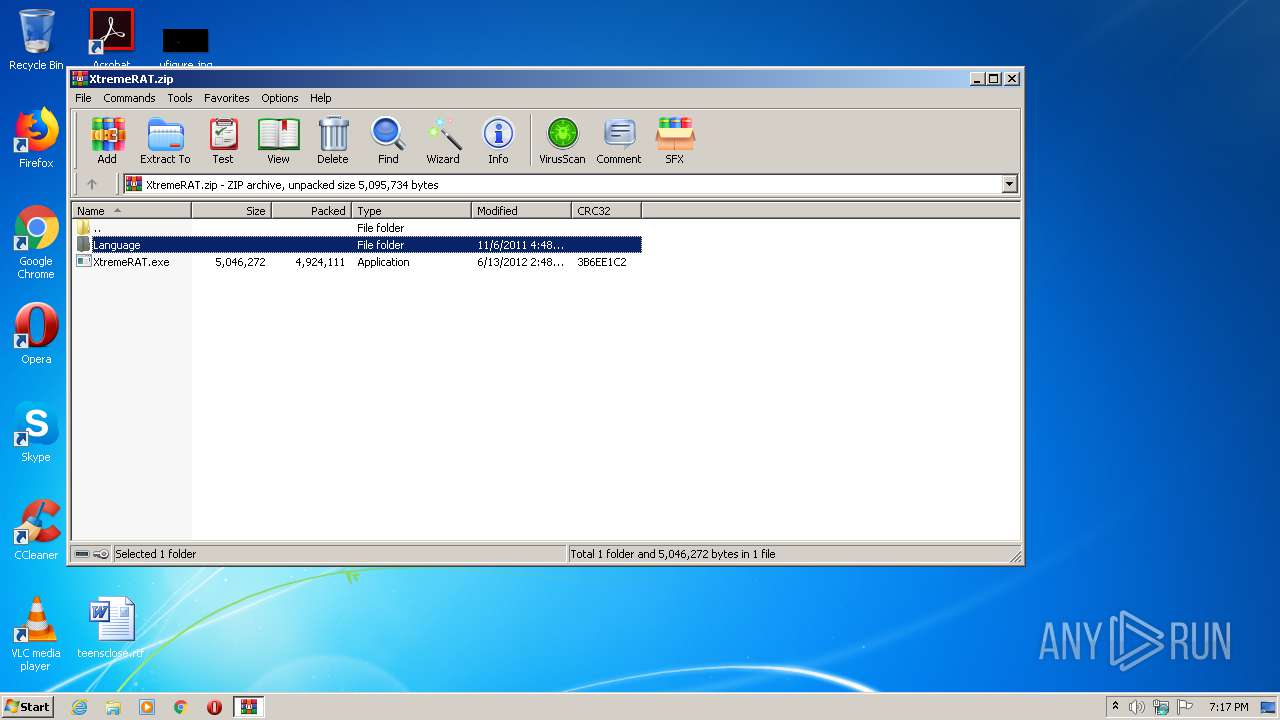
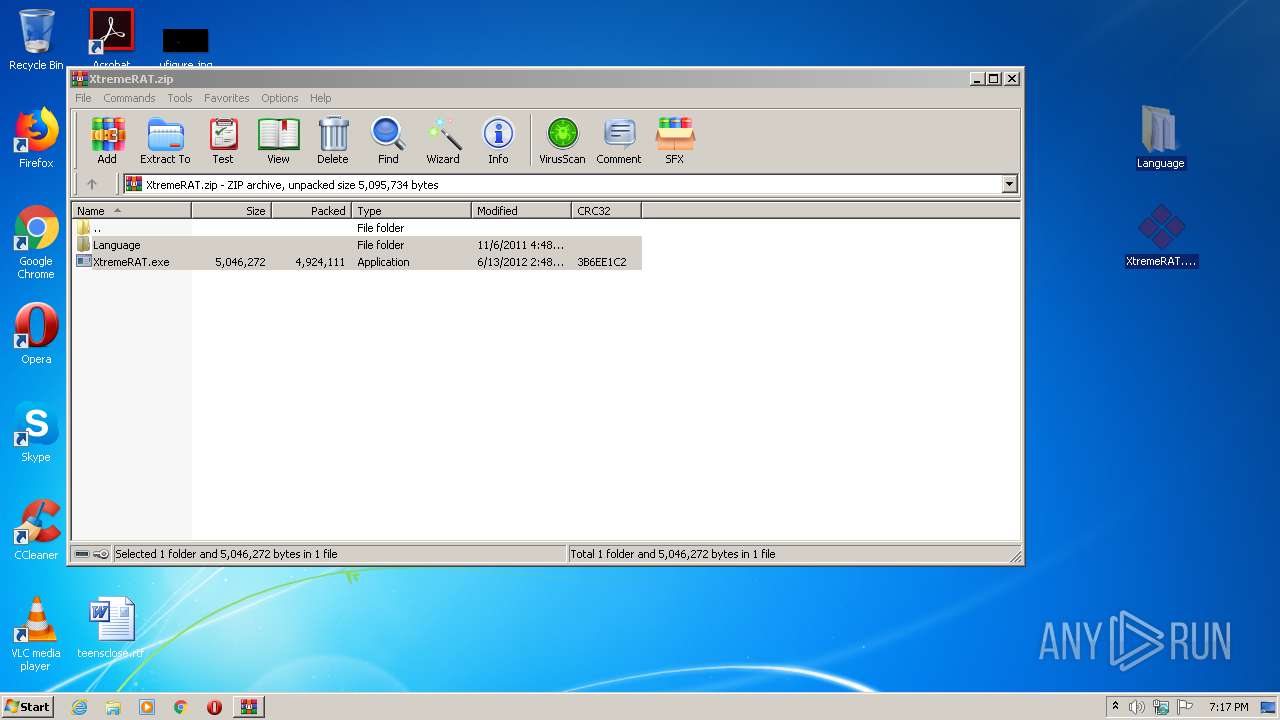
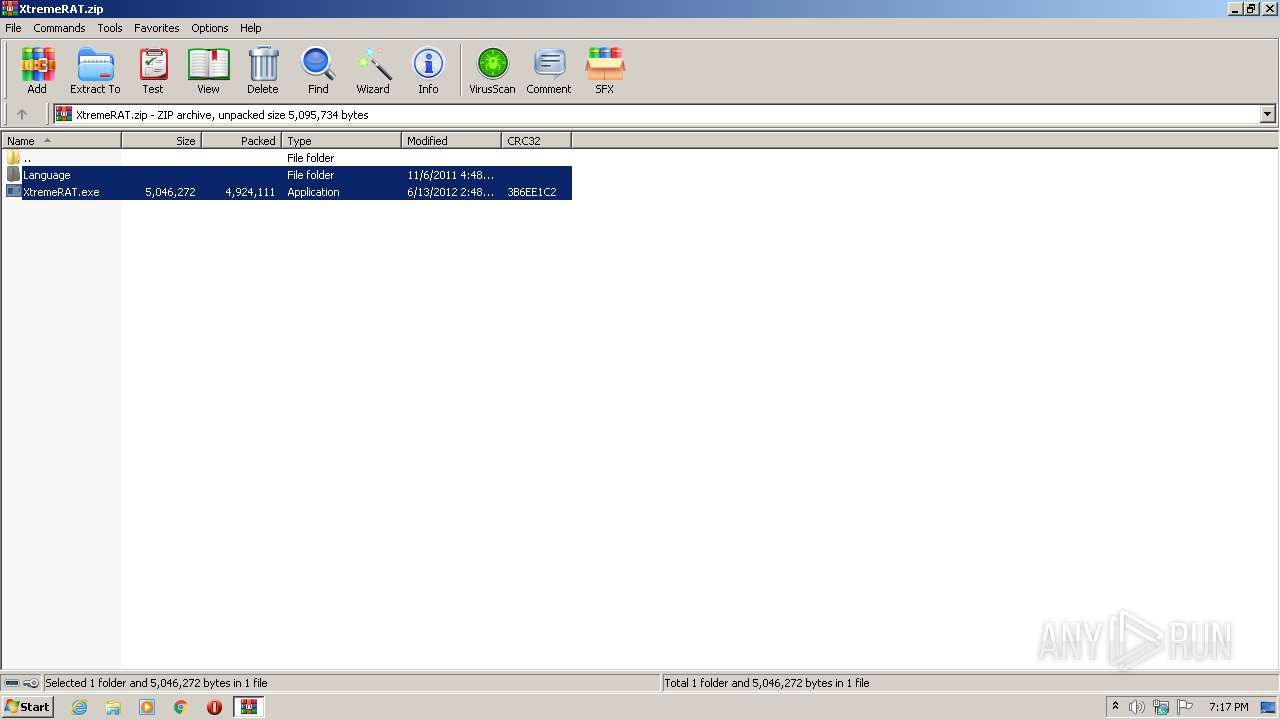
| 4012 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\XtremeRAT.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 163
Read events
1 069
Write events
91
Delete events
3
Modification events
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\XtremeRAT.zip | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
4
Suspicious files
125
Text files
2
Unknown types
1
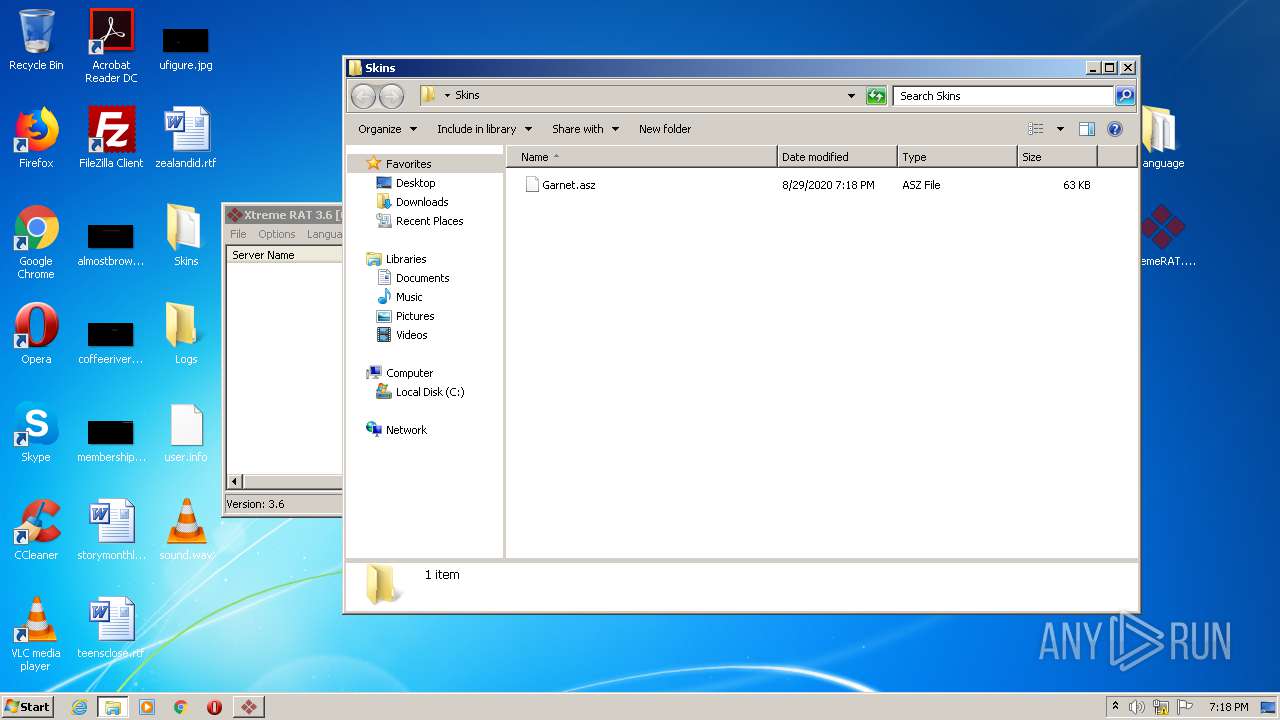
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4012.36245\XtremeRAT.exe | — | |
MD5:— | SHA256:— | |||
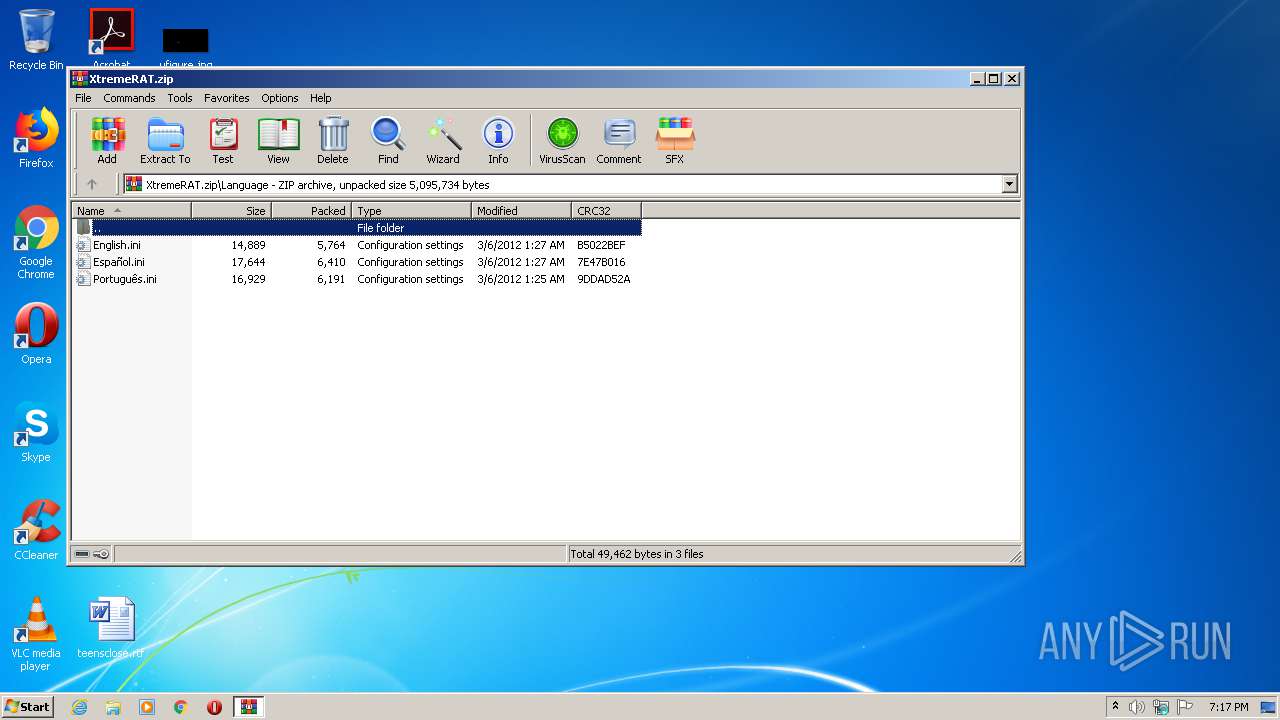
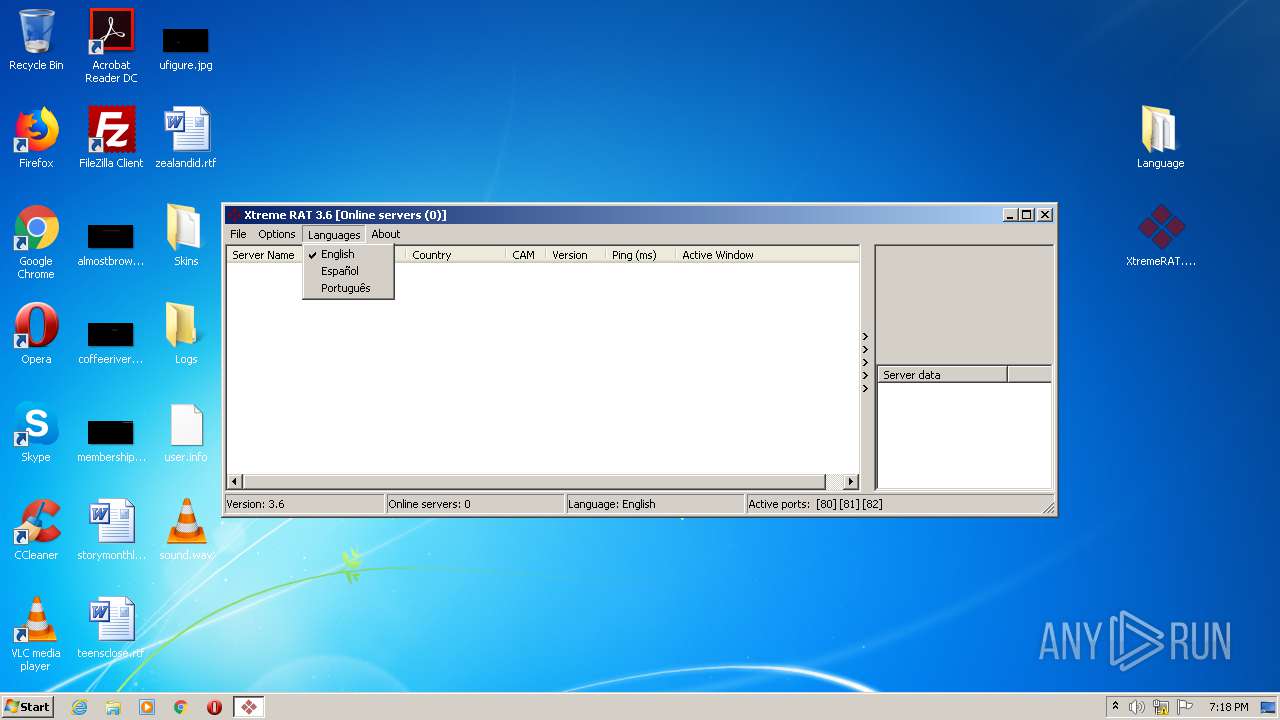
| 4012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4012.36245\Language\English.ini | — | |
MD5:— | SHA256:— | |||
| 4012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4012.36245\Language\Español.ini | — | |
MD5:— | SHA256:— | |||
| 4012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4012.36245\Language\Português.ini | — | |
MD5:— | SHA256:— | |||
| 3964 | XtremeRAT.exe | C:\Users\admin\Desktop\RCX6F51.tmp | — | |
MD5:— | SHA256:— | |||
| 3964 | XtremeRAT.exe | C:\Users\admin\AppData\Local\Temp\UPXfile.exe | — | |
MD5:— | SHA256:— | |||
| 3352 | UPXfile.exe | C:\Users\admin\Desktop\server.upx | — | |
MD5:— | SHA256:— | |||
| 3964 | XtremeRAT.exe | C:\Users\admin\Desktop\Profiles\Profile.ini | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\1234567890[1].htmctions | — | |
MD5:— | SHA256:— | |||
| 3964 | XtremeRAT.exe | C:\Users\admin\Desktop\Settings\Server_USER-PC^admin(C4BA3647).ini | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
XtremeRAT.exe | VCLFixPack patch installed: PageControlPaintingFix |
XtremeRAT.exe | VCLFixPack patch installed: GridFlickerFix |