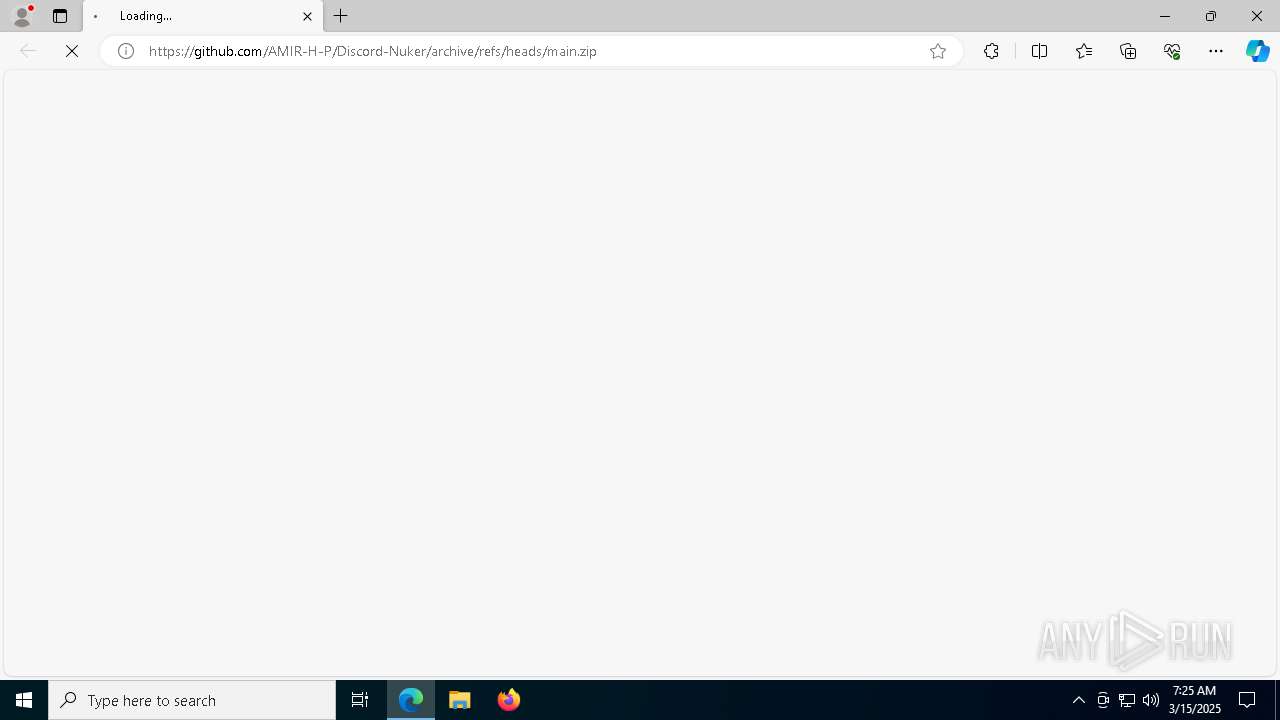
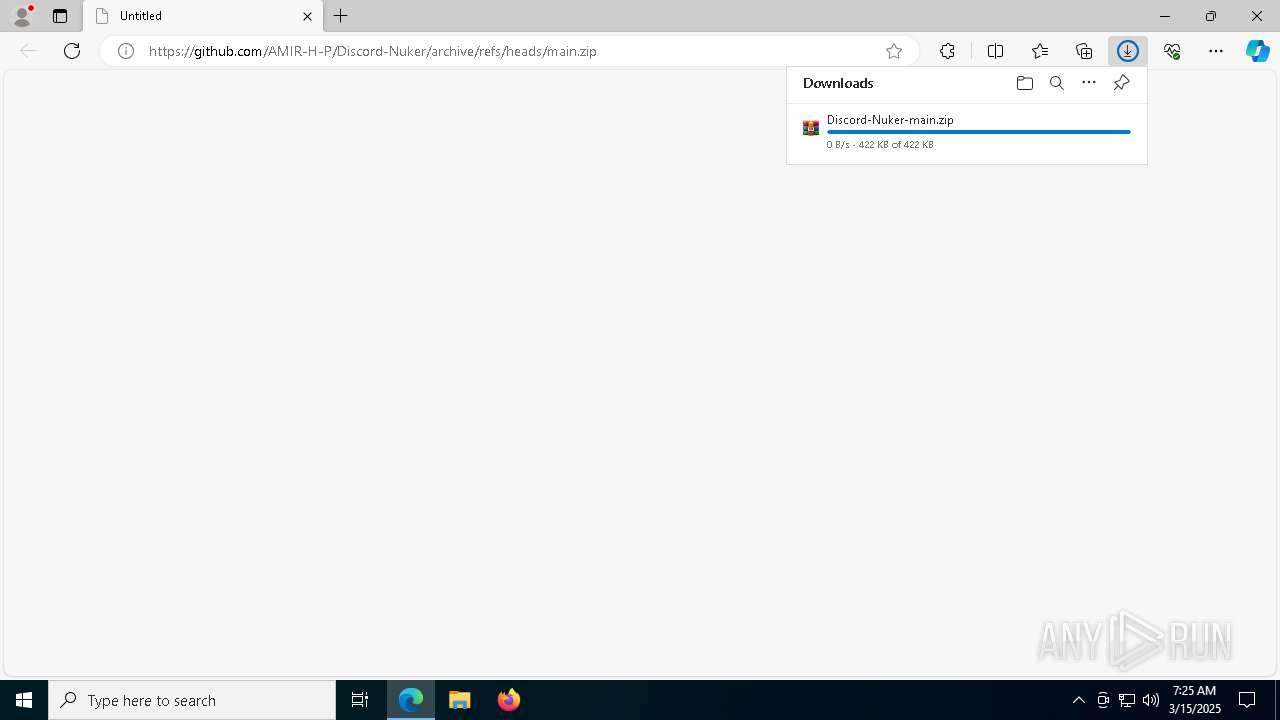
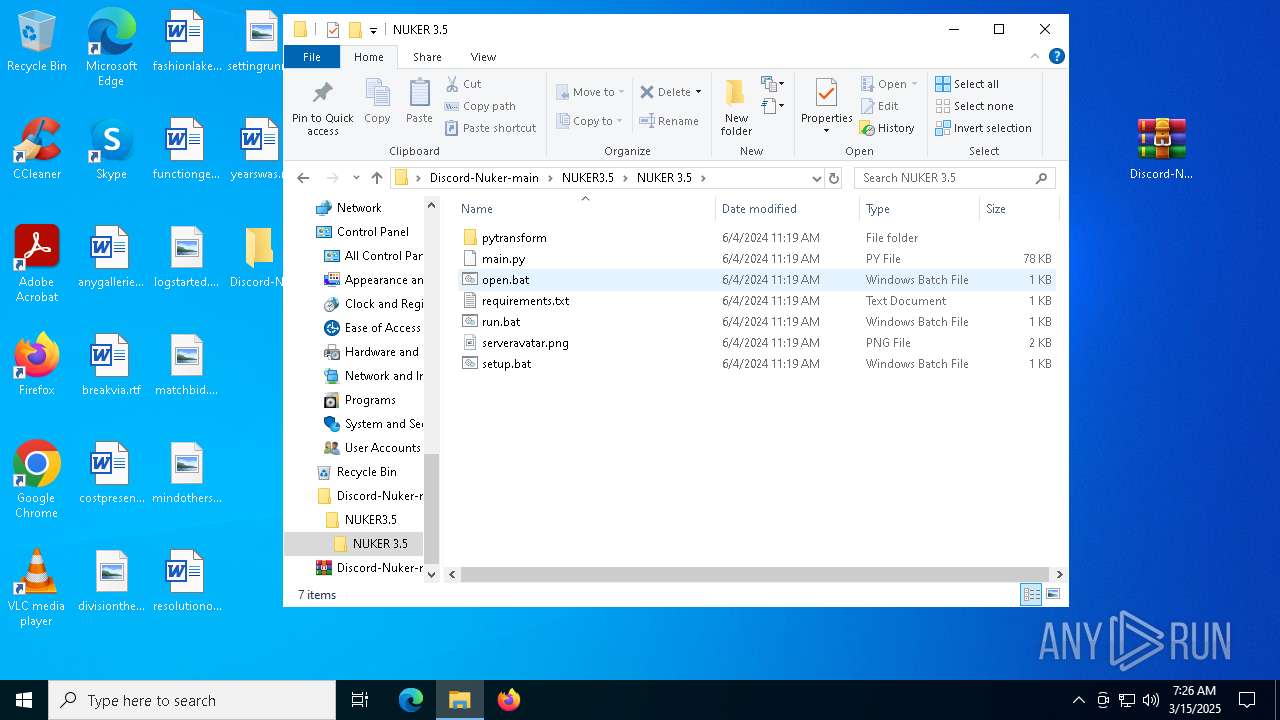
| URL: | https://github.com/AMIR-H-P/Discord-Nuker/archive/refs/heads/main.zip |
| Full analysis: | https://app.any.run/tasks/7eb8dc85-6429-4981-82df-b062757e105d |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2025, 07:25:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 04325E3118B70C411C58F73319FBCFDF |
| SHA1: | 6671212B897AFB51955423CD3A77FCDDE0B1DB7B |
| SHA256: | F49C35A79978D894523D39EF4E870B302CBD0C56439272F7CC3490F356492105 |
| SSDEEP: | 3:N8tEdq36dG2aED4RSLNLc:2u66Z4ULN4 |
MALICIOUS
Changes the autorun value in the registry
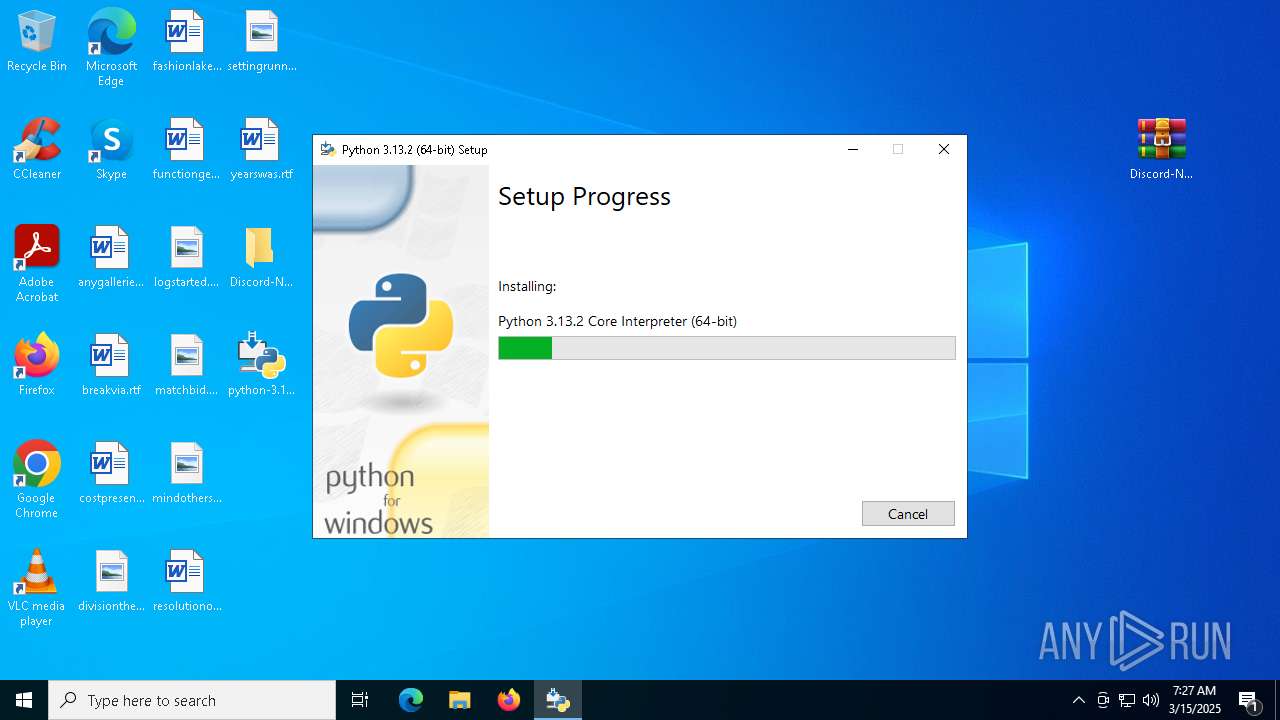
- python-3.13.2-amd64.exe (PID: 2904)
- python-3.13.2-amd64.exe (PID: 5392)
SUSPICIOUS
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 7560)
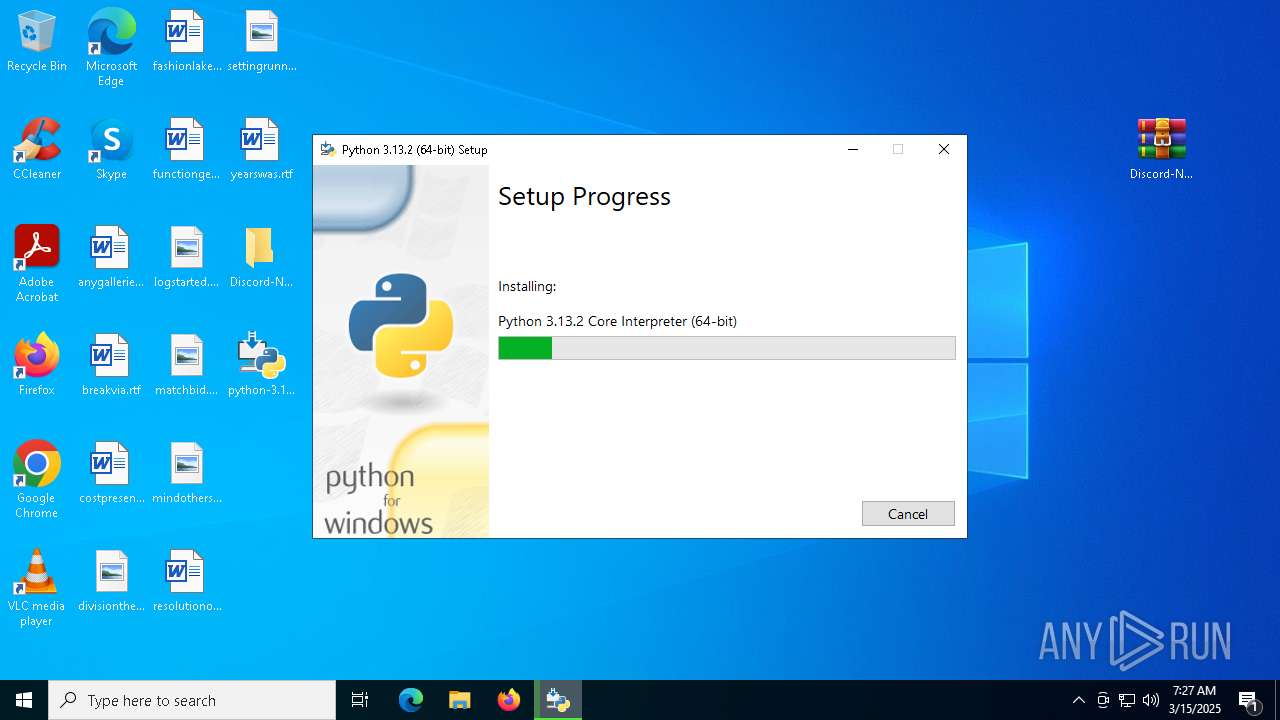
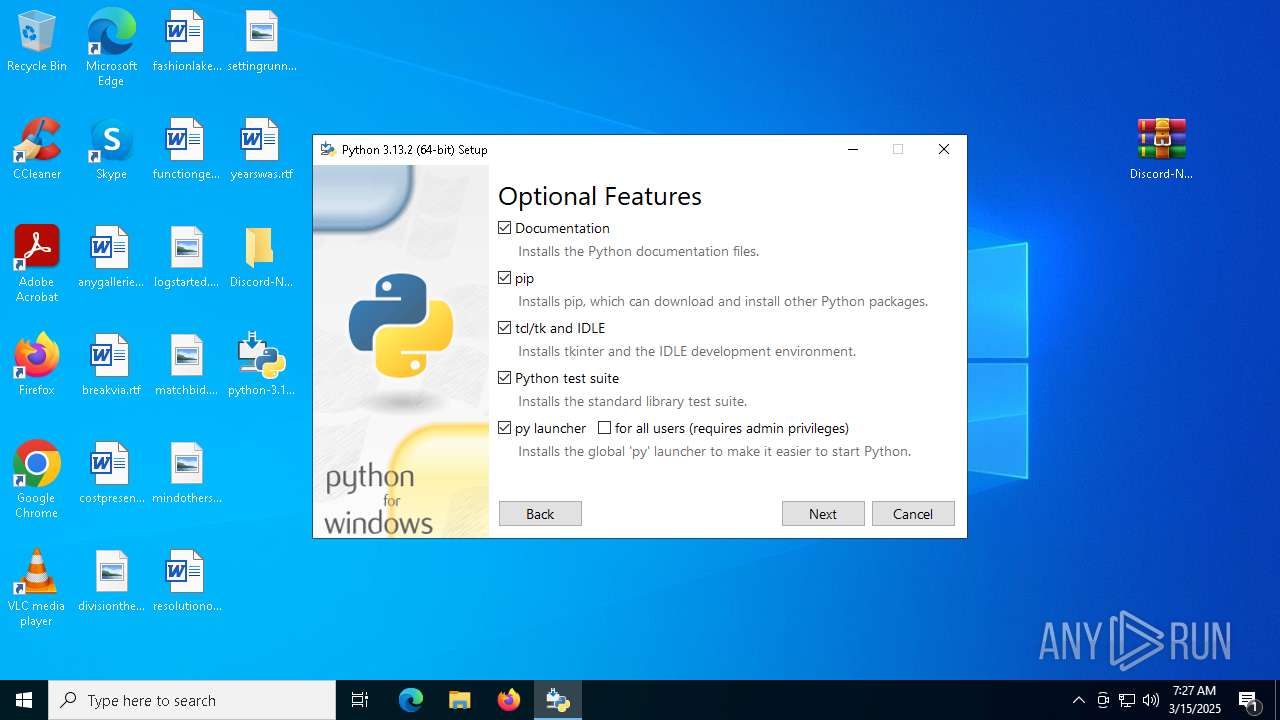
Executable content was dropped or overwritten
- python-3.13.2-amd64.exe (PID: 7412)
- python-3.13.2-amd64.exe (PID: 2904)
- python-3.13.2-amd64.exe (PID: 2064)
- python-3.13.2-amd64.exe (PID: 5392)
Searches for installed software
- python-3.13.2-amd64.exe (PID: 2904)
- python-3.13.2-amd64.exe (PID: 5392)
The process drops C-runtime libraries
- python-3.13.2-amd64.exe (PID: 2904)
- python-3.13.2-amd64.exe (PID: 5392)
Process drops legitimate windows executable
- python-3.13.2-amd64.exe (PID: 2904)
- python-3.13.2-amd64.exe (PID: 5392)
Creates a software uninstall entry
- python-3.13.2-amd64.exe (PID: 5392)
- python-3.13.2-amd64.exe (PID: 2904)
INFO
Application launched itself
- msedge.exe (PID: 6032)
- msedge.exe (PID: 6872)
Checks supported languages
- identity_helper.exe (PID: 8780)
- identity_helper.exe (PID: 9012)
- python-3.13.2-amd64.exe (PID: 2904)
- ShellExperienceHost.exe (PID: 7560)
- python-3.13.2-amd64.exe (PID: 7412)
- python-3.13.2-amd64.exe (PID: 2064)
- python-3.13.2-amd64.exe (PID: 5392)
Reads Environment values
- identity_helper.exe (PID: 8780)
- identity_helper.exe (PID: 9012)
Reads the computer name
- identity_helper.exe (PID: 9012)
- identity_helper.exe (PID: 8780)
- python-3.13.2-amd64.exe (PID: 2904)
- ShellExperienceHost.exe (PID: 7560)
- python-3.13.2-amd64.exe (PID: 2064)
- python-3.13.2-amd64.exe (PID: 5392)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 2096)
- BackgroundTransferHost.exe (PID: 7864)
- BackgroundTransferHost.exe (PID: 7608)
- BackgroundTransferHost.exe (PID: 8436)
- BackgroundTransferHost.exe (PID: 7412)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 7864)
- slui.exe (PID: 5024)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7864)
- slui.exe (PID: 5024)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7864)
- python-3.13.2-amd64.exe (PID: 5392)
- python-3.13.2-amd64.exe (PID: 2904)
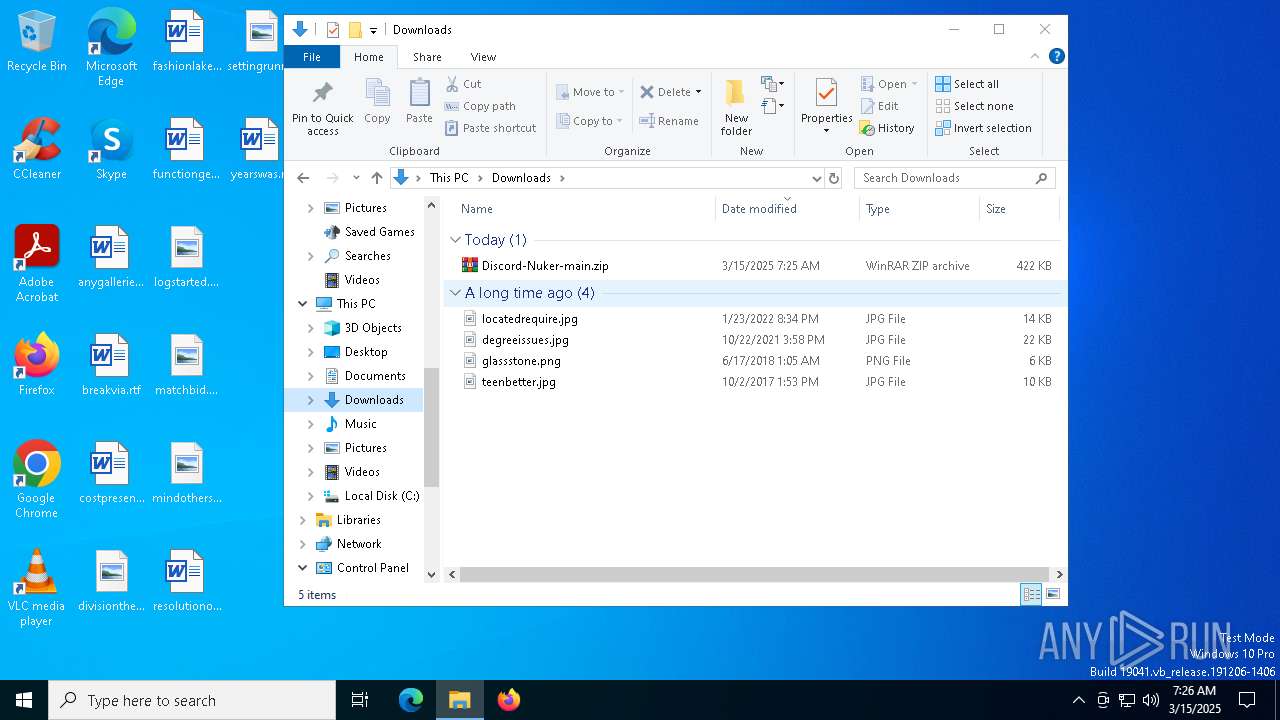
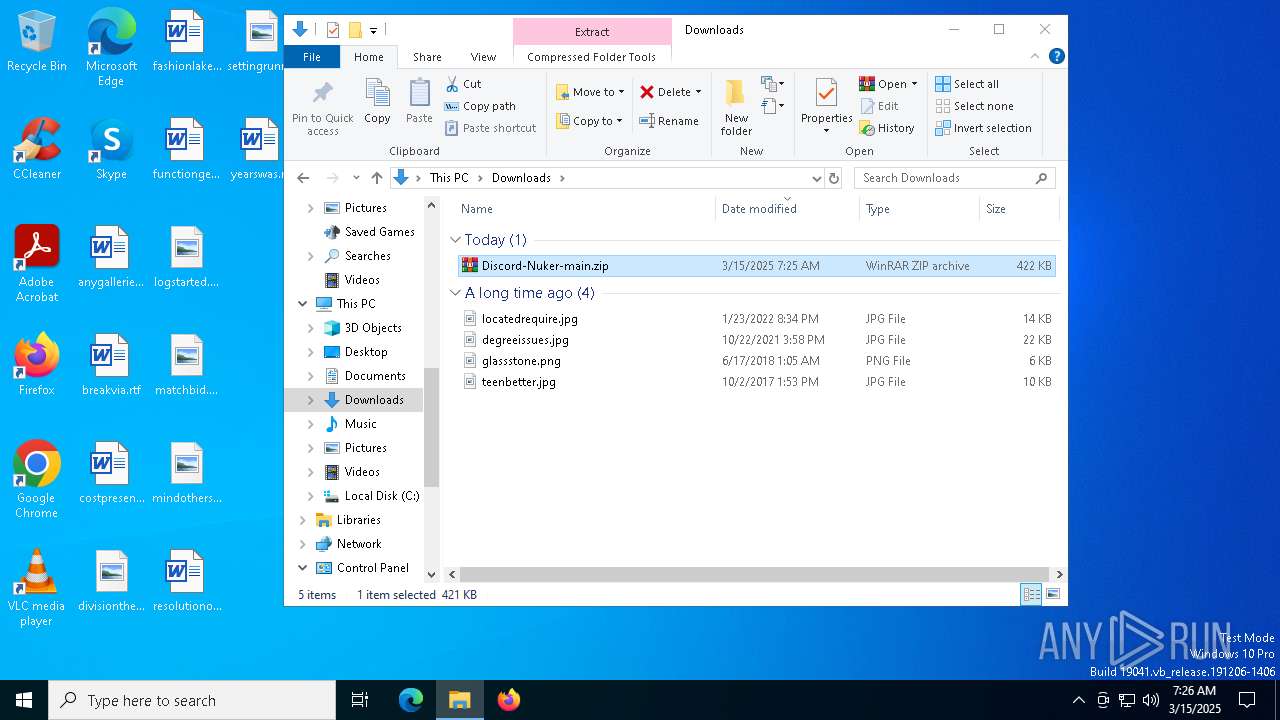
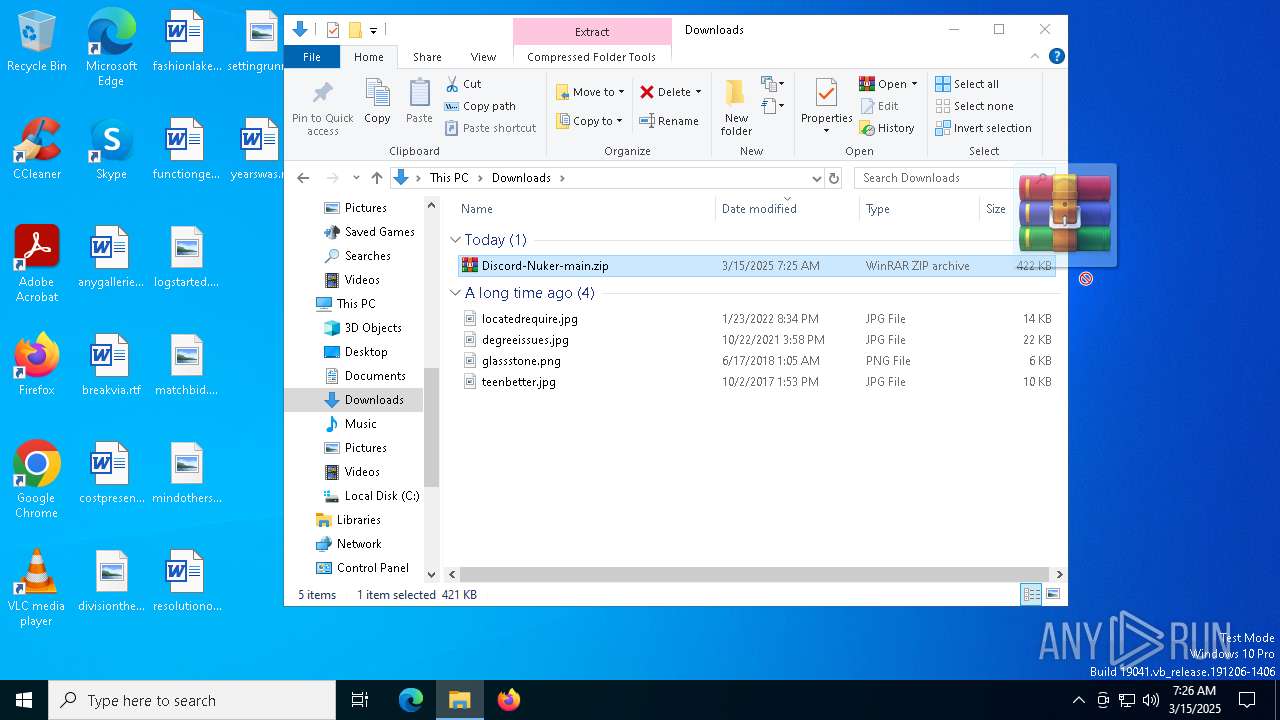
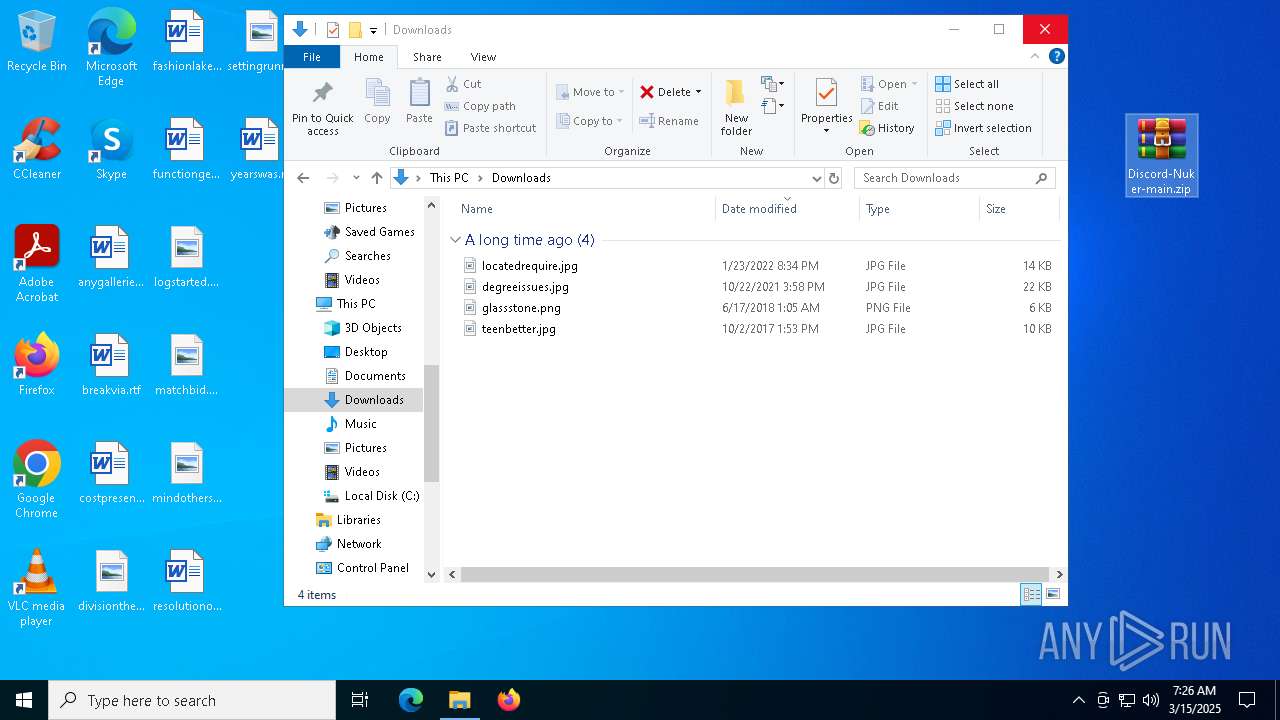
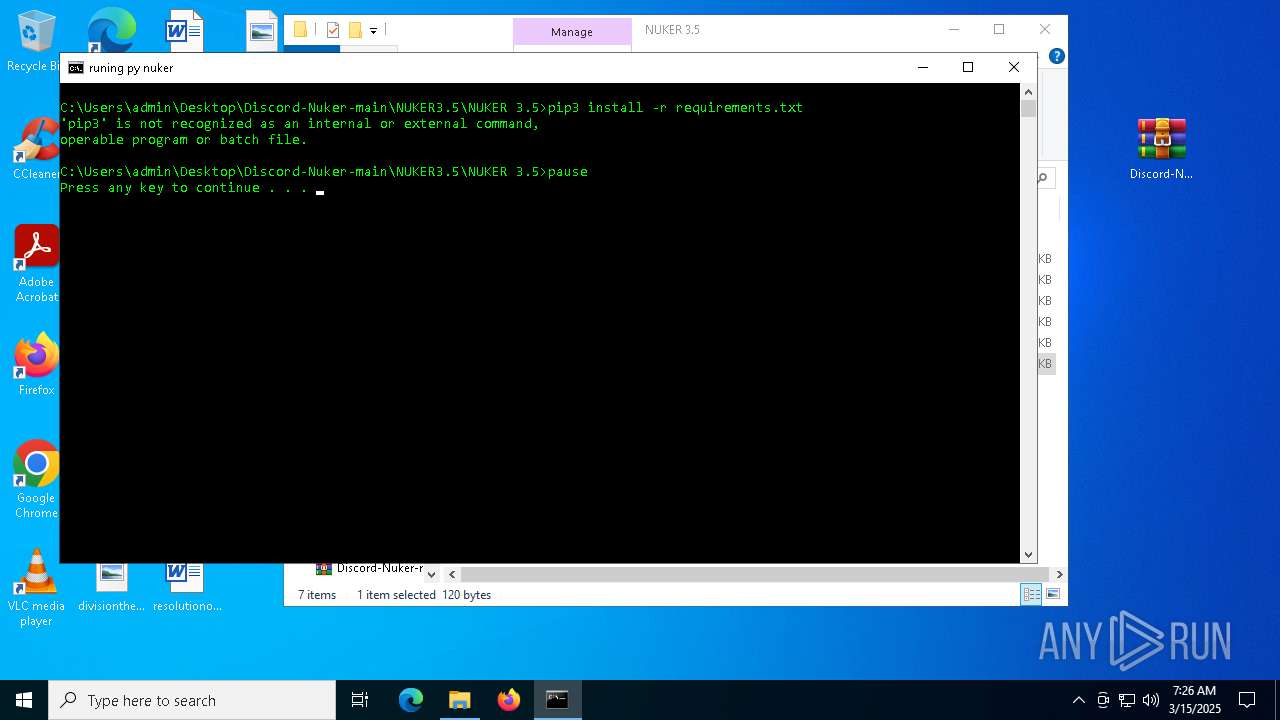
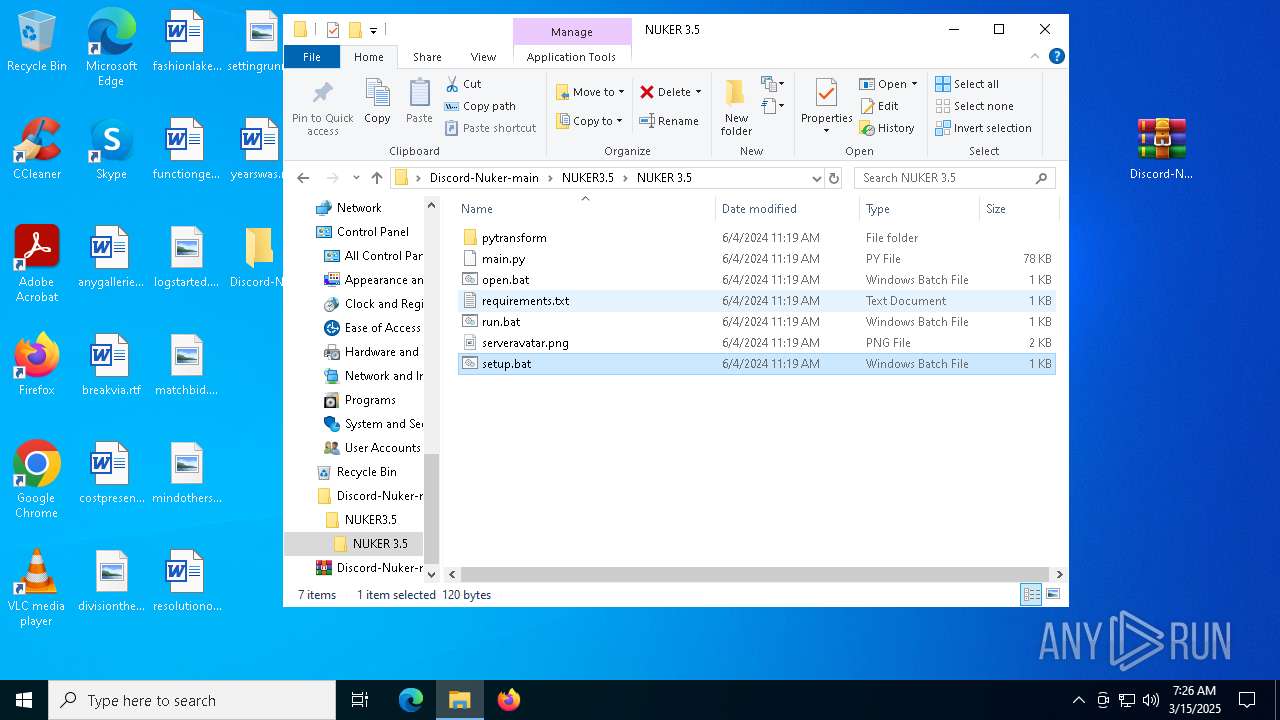
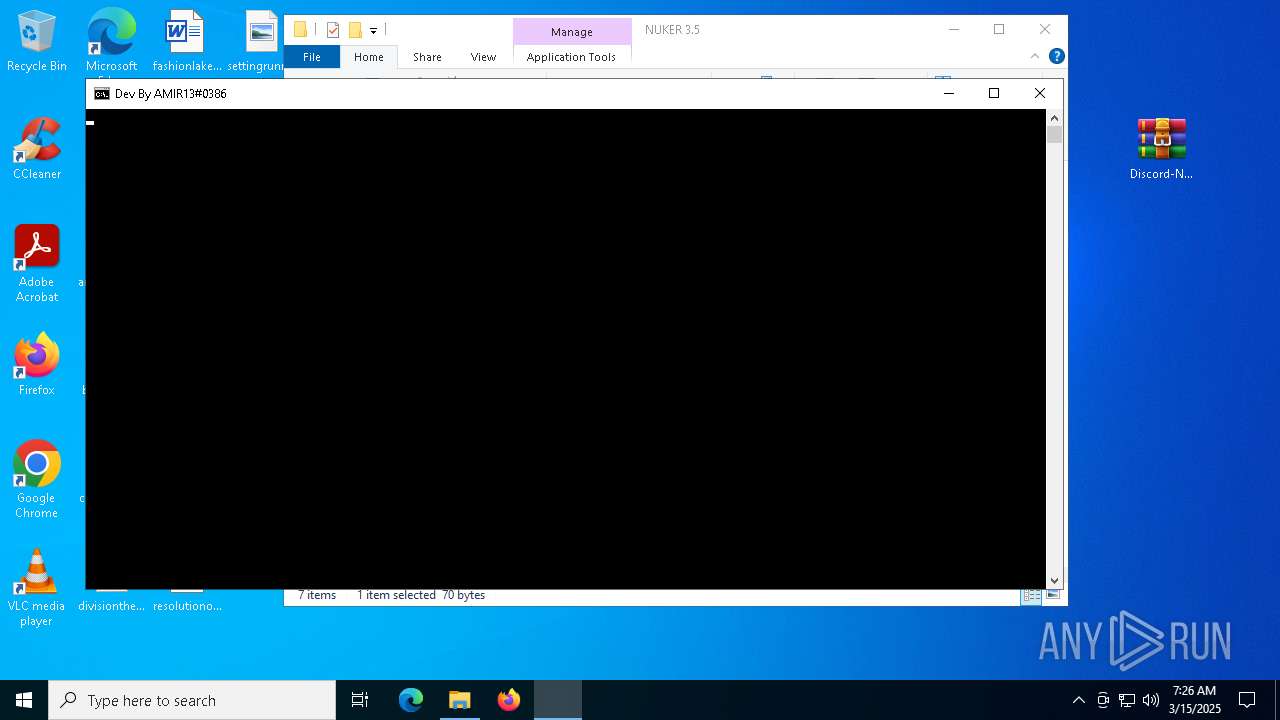
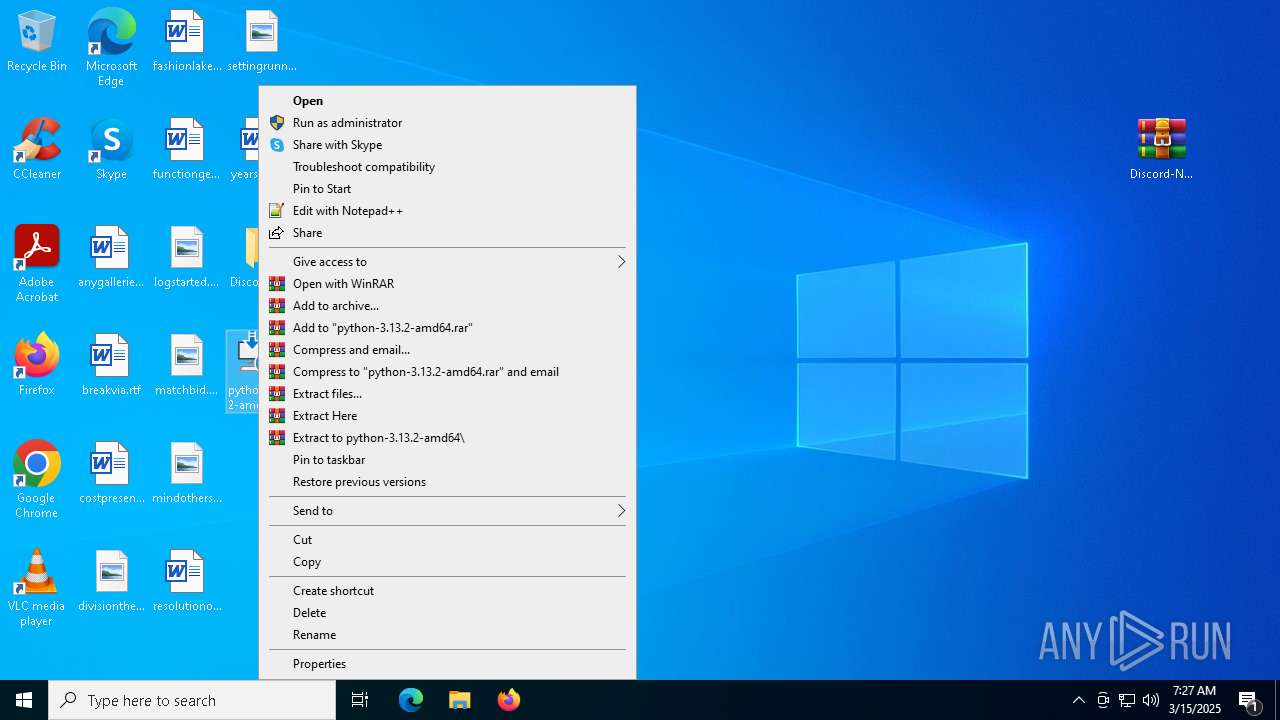
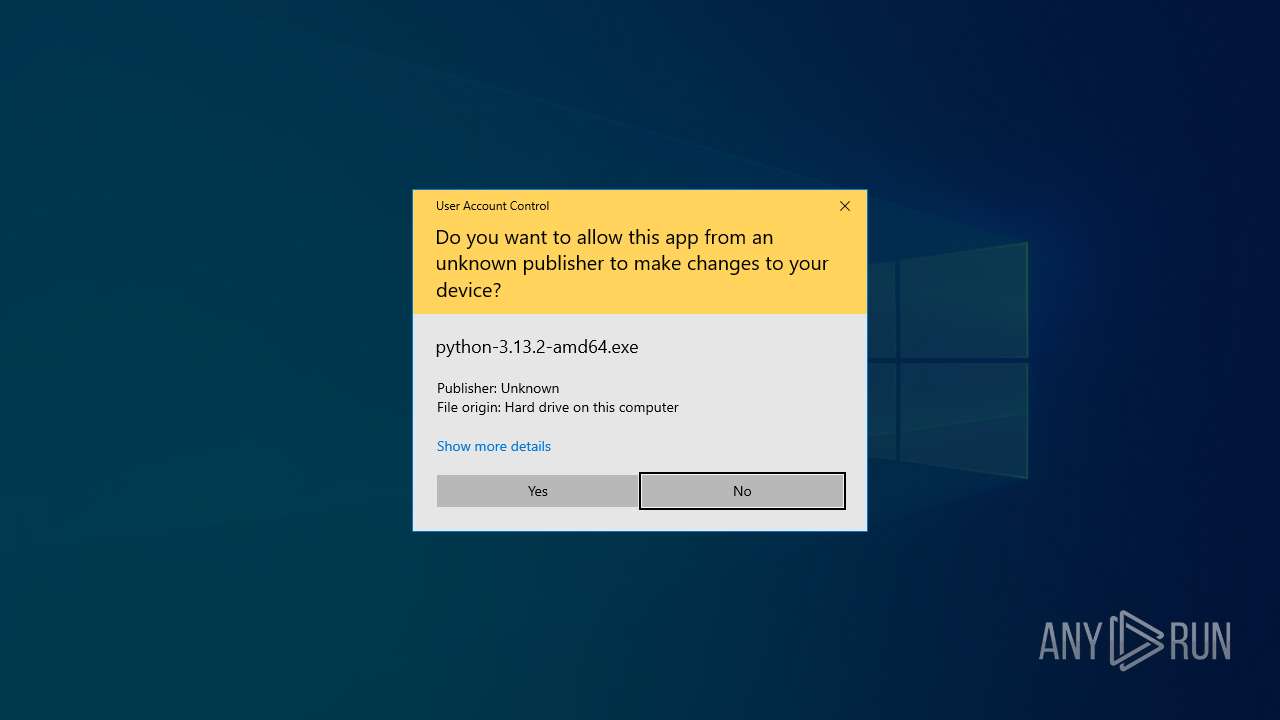
Manual execution by a user
- WinRAR.exe (PID: 8780)
- cmd.exe (PID: 8564)
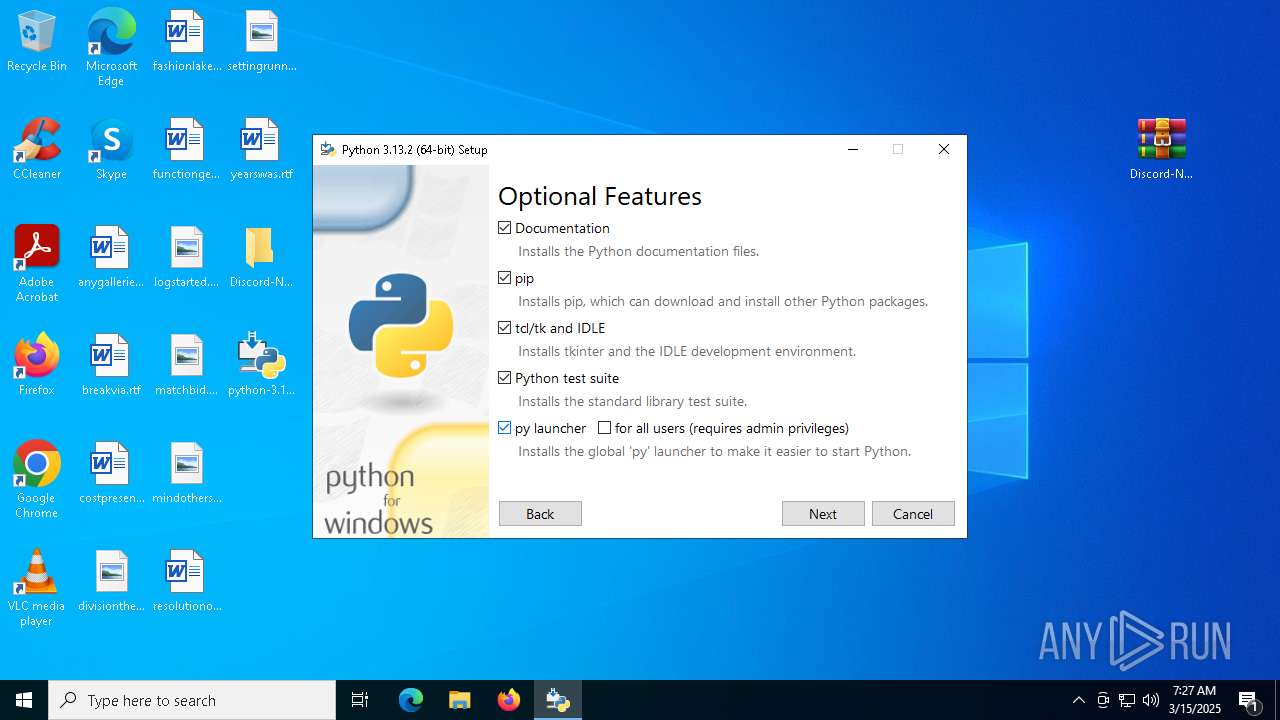
- python-3.13.2-amd64.exe (PID: 7412)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 7984)
- python-3.13.2-amd64.exe (PID: 2064)
Create files in a temporary directory
- python-3.13.2-amd64.exe (PID: 7412)
- python-3.13.2-amd64.exe (PID: 2904)
- python-3.13.2-amd64.exe (PID: 5392)
The sample compiled with english language support
- python-3.13.2-amd64.exe (PID: 7412)
- python-3.13.2-amd64.exe (PID: 2904)
- python-3.13.2-amd64.exe (PID: 2064)
- python-3.13.2-amd64.exe (PID: 5392)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8780)
Autorun file from Registry key
- python-3.13.2-amd64.exe (PID: 5392)
- python-3.13.2-amd64.exe (PID: 2904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
213
Monitored processes
71
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3484 --field-trial-handle=2344,i,6183669929474142632,13429043926303600310,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\Desktop\python-3.13.2-amd64.exe" | C:\Users\admin\Desktop\python-3.13.2-amd64.exe | explorer.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: HIGH Description: Python 3.13.2 (64-bit) Exit code: 1392 Version: 3.13.2150.0 Modules
| |||||||||||||||
| 2096 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x298,0x29c,0x2a0,0x290,0x294,0x7ffc881e5fd8,0x7ffc881e5fe4,0x7ffc881e5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
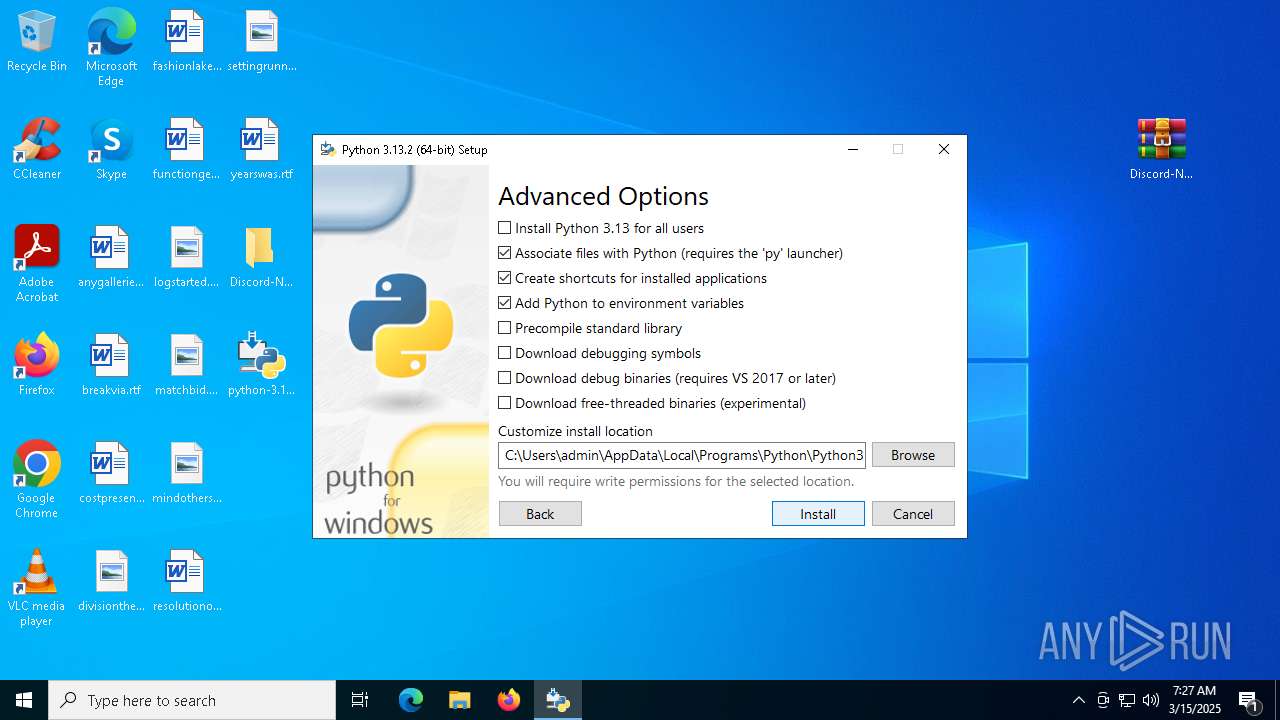
| 2904 | "C:\Users\admin\AppData\Local\Temp\{5DD578FC-15BA-47E3-93F0-AFB635018D0A}\.cr\python-3.13.2-amd64.exe" -burn.clean.room="C:\Users\admin\Desktop\python-3.13.2-amd64.exe" -burn.filehandle.attached=572 -burn.filehandle.self=580 | C:\Users\admin\AppData\Local\Temp\{5DD578FC-15BA-47E3-93F0-AFB635018D0A}\.cr\python-3.13.2-amd64.exe | python-3.13.2-amd64.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python 3.13.2 (64-bit) Exit code: 1392 Version: 3.13.2150.0 Modules
| |||||||||||||||
| 3008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5456 --field-trial-handle=2344,i,6183669929474142632,13429043926303600310,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4608 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3456 --field-trial-handle=2344,i,6183669929474142632,13429043926303600310,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5024 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5392 | "C:\WINDOWS\Temp\{62640439-ADC6-438B-B3AE-42D77D2B7A7C}\.cr\python-3.13.2-amd64.exe" -burn.clean.room="C:\Users\admin\Desktop\python-3.13.2-amd64.exe" -burn.filehandle.attached=588 -burn.filehandle.self=716 | C:\Windows\Temp\{62640439-ADC6-438B-B3AE-42D77D2B7A7C}\.cr\python-3.13.2-amd64.exe | python-3.13.2-amd64.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: HIGH Description: Python 3.13.2 (64-bit) Exit code: 1392 Version: 3.13.2150.0 Modules
| |||||||||||||||
Total events
10 935
Read events
10 828
Write events
93
Delete events
14
Modification events
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4D41FBBEF28E2F00 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AB5104BFF28E2F00 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262792 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {82735147-3DAA-4D1A-89E2-AD85DF72845E} | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262792 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {38F7B6FB-2B74-43BB-8F4E-32E2D934B3D8} | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
34
Suspicious files
566
Text files
123
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c073.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c073.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c073.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c083.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c0e1.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
56
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2516 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0cd04ea6-f2d8-46ef-8173-46a29bb98c18?P1=1742349639&P2=404&P3=2&P4=Uyj2hOHdkAaokgYNE0Y2oBb1vvZgOqPTSGryuOY9i%2b4WDAKvkn8CQknDBAcrKhIq4MioTNIpytSazw3N2MHhNQ%3d%3d | unknown | — | — | whitelisted |
2516 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0cd04ea6-f2d8-46ef-8173-46a29bb98c18?P1=1742349639&P2=404&P3=2&P4=Uyj2hOHdkAaokgYNE0Y2oBb1vvZgOqPTSGryuOY9i%2b4WDAKvkn8CQknDBAcrKhIq4MioTNIpytSazw3N2MHhNQ%3d%3d | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8360 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
9140 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7864 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
9140 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2516 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742411385&P2=404&P3=2&P4=VCBGfq%2bxWP5qz9nrvD6TUNRLzC%2fDhxF%2b3O8QZzVFueRASl1WxlMISl0Bav3jLsucjenU9H6k88c6vKCco2CZoQ%3d%3d | unknown | — | — | whitelisted |
2516 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1742411385&P2=404&P3=2&P4=VCBGfq%2bxWP5qz9nrvD6TUNRLzC%2fDhxF%2b3O8QZzVFueRASl1WxlMISl0Bav3jLsucjenU9H6k88c6vKCco2CZoQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4380 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7436 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6032 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7436 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7436 | msedge.exe | 13.107.253.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7436 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
codeload.github.com |
| whitelisted |