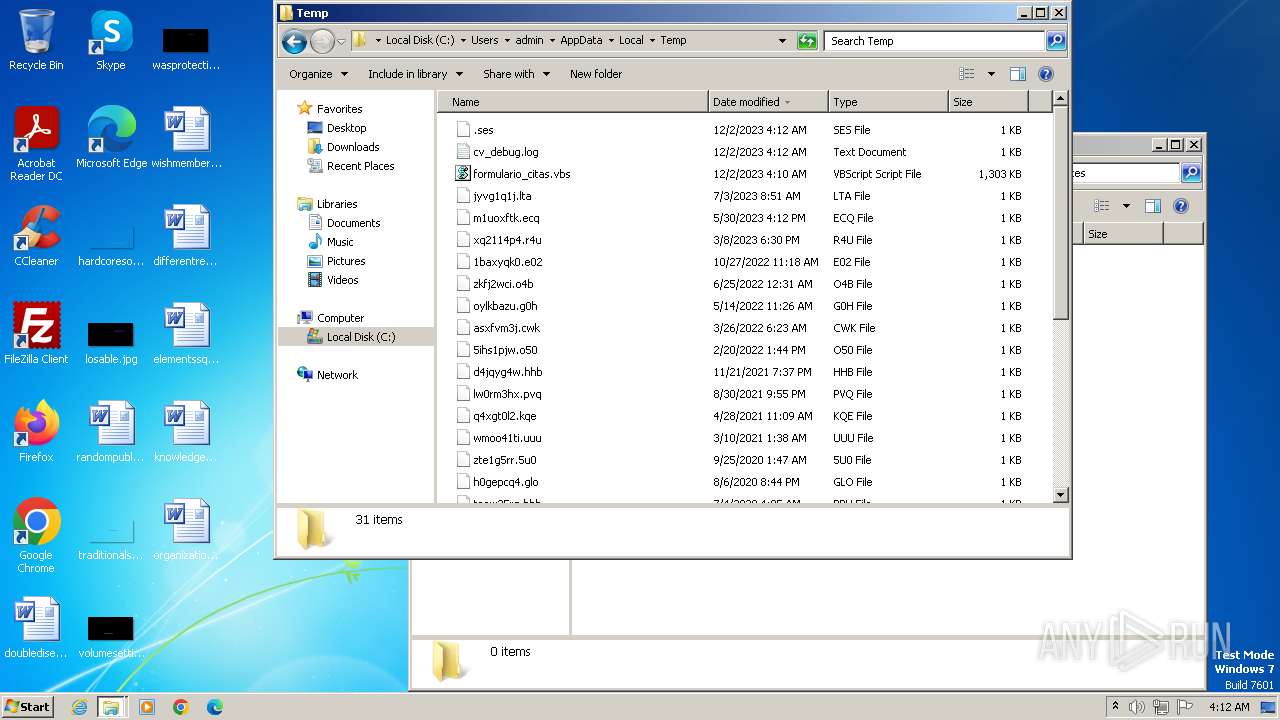
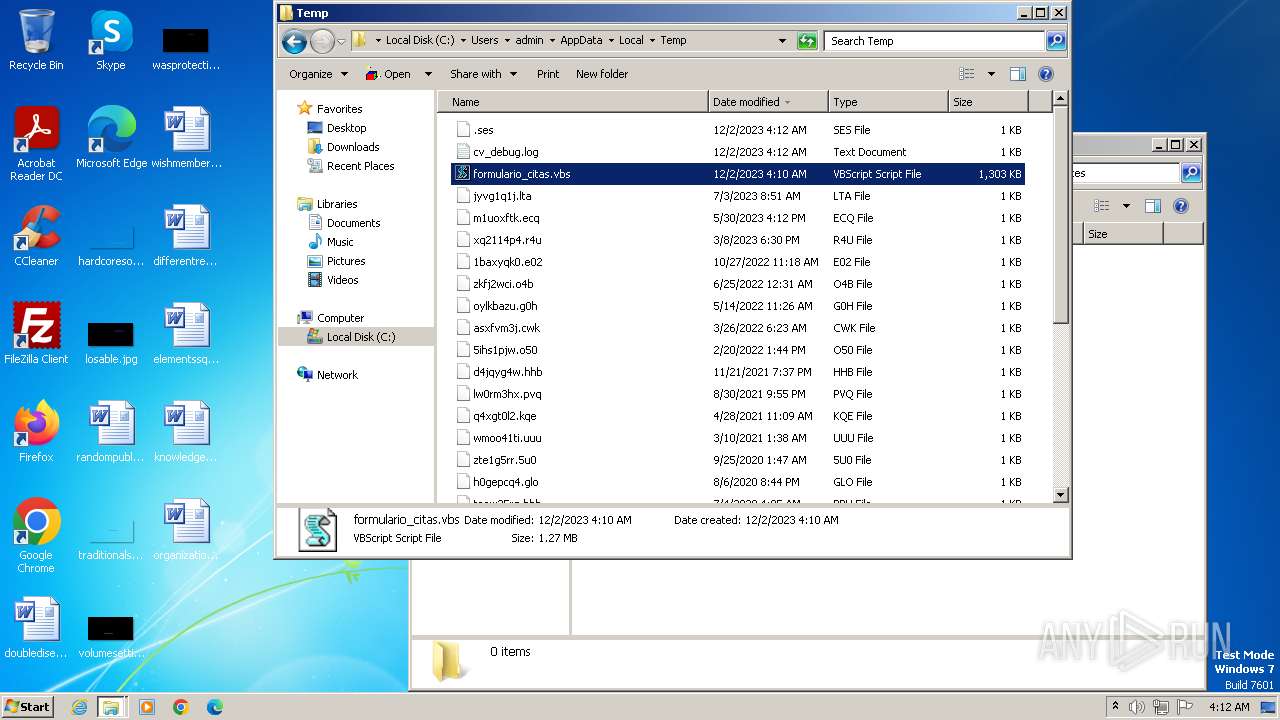
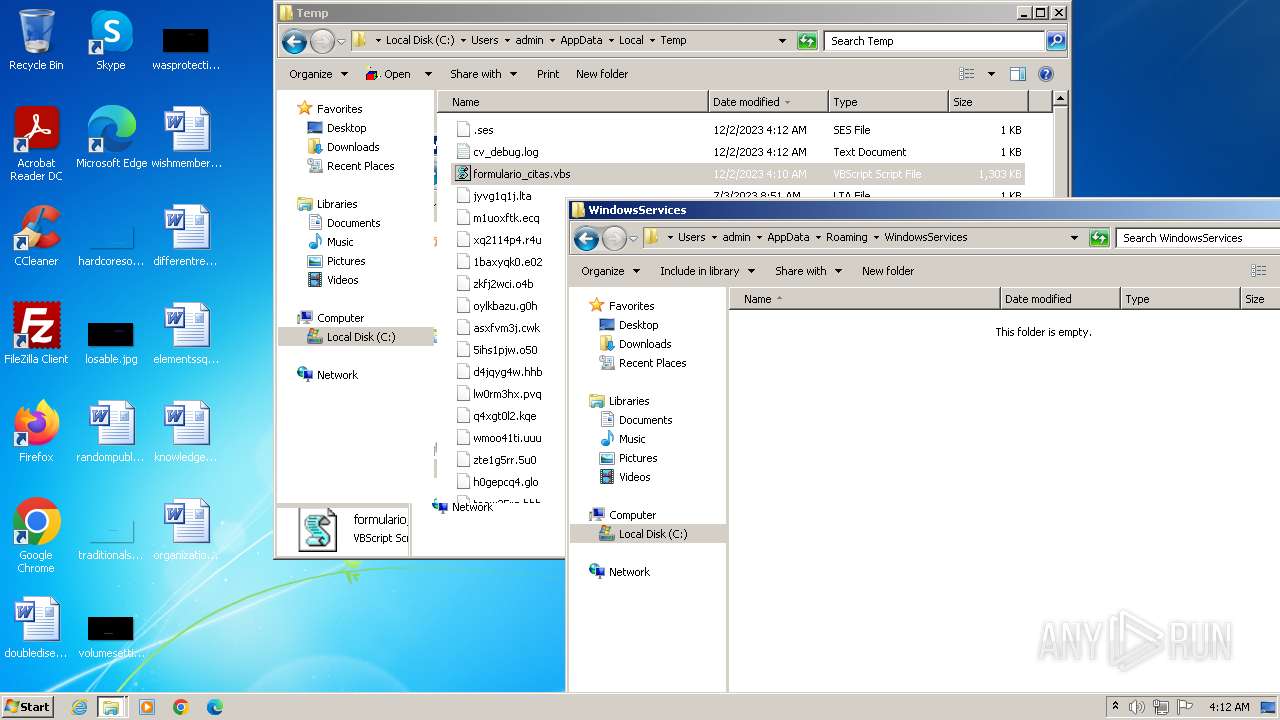
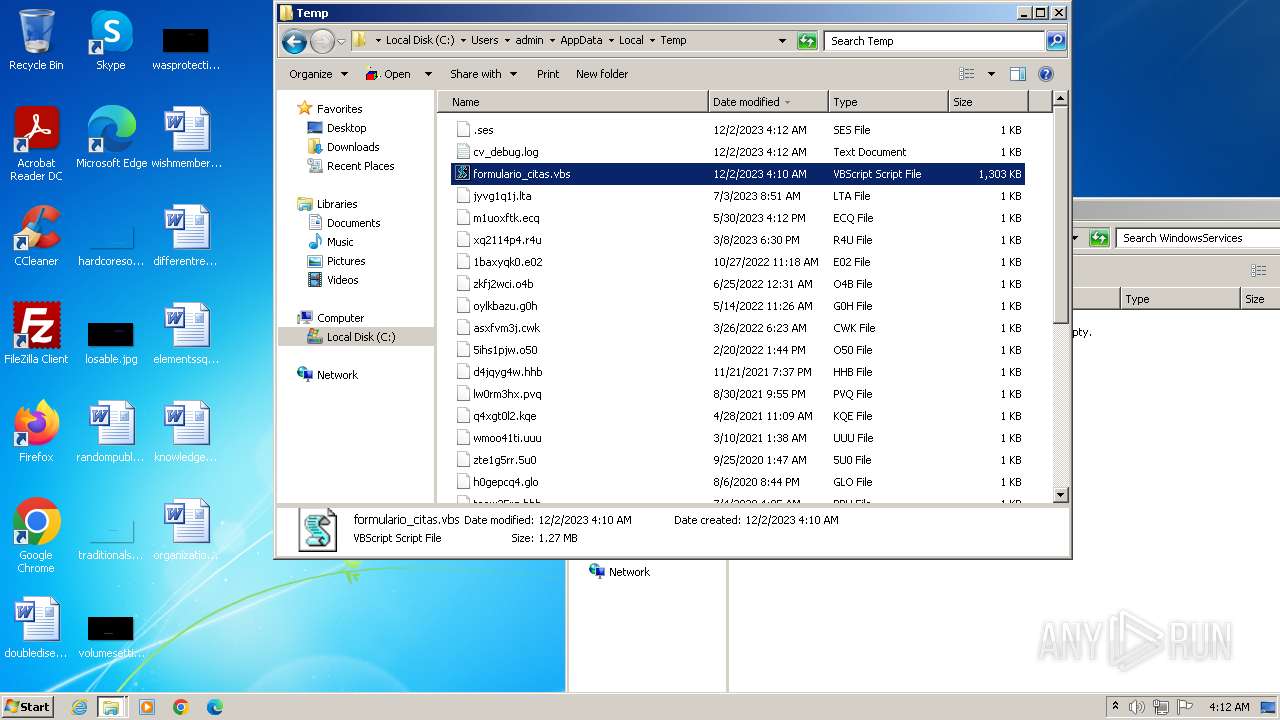
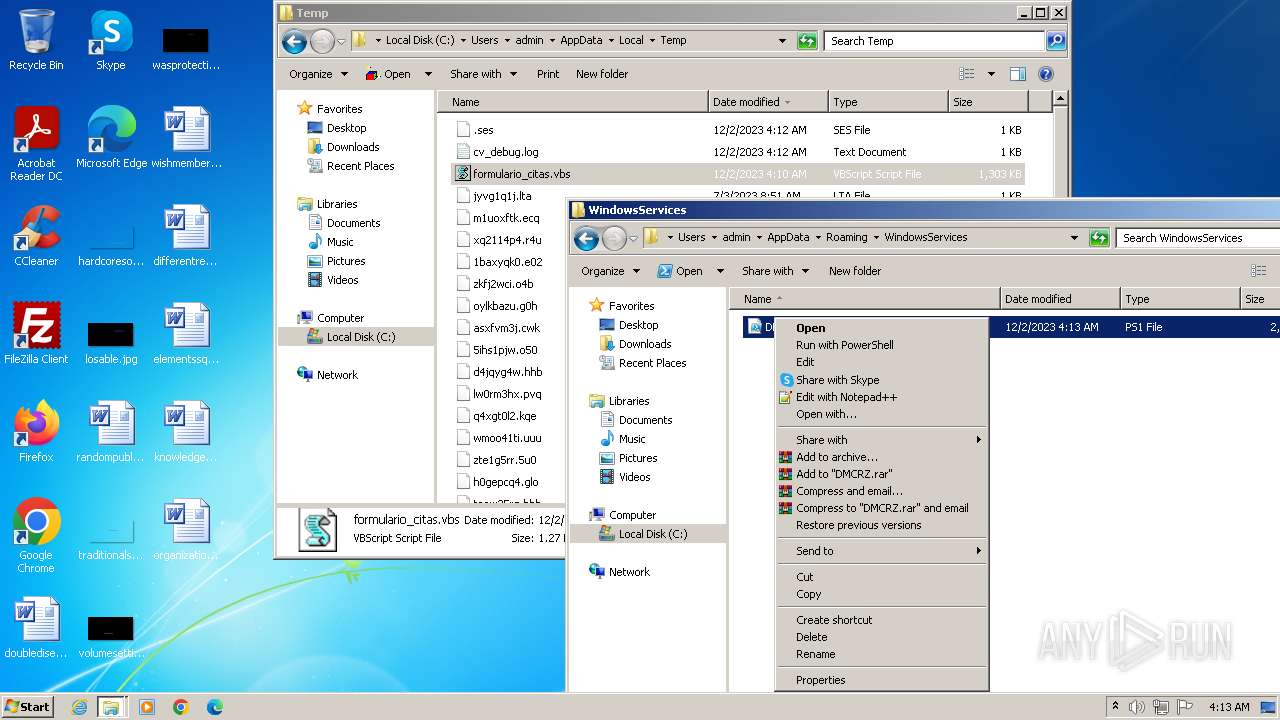
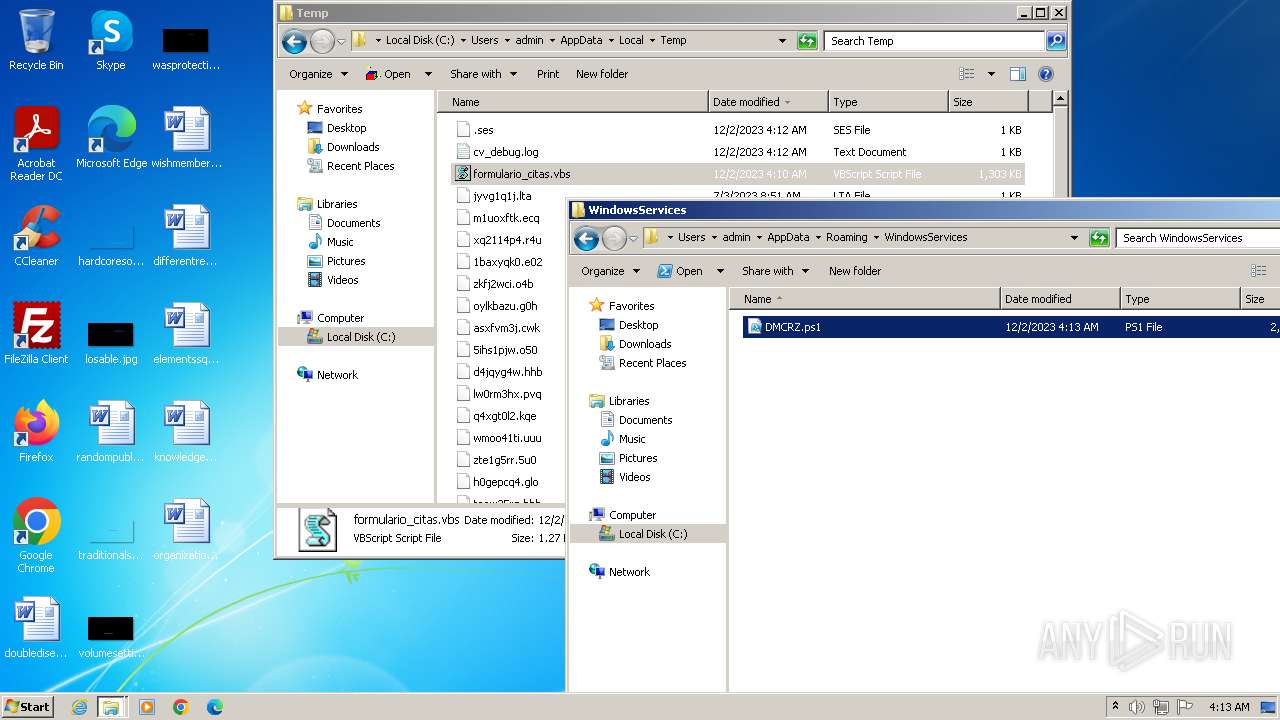
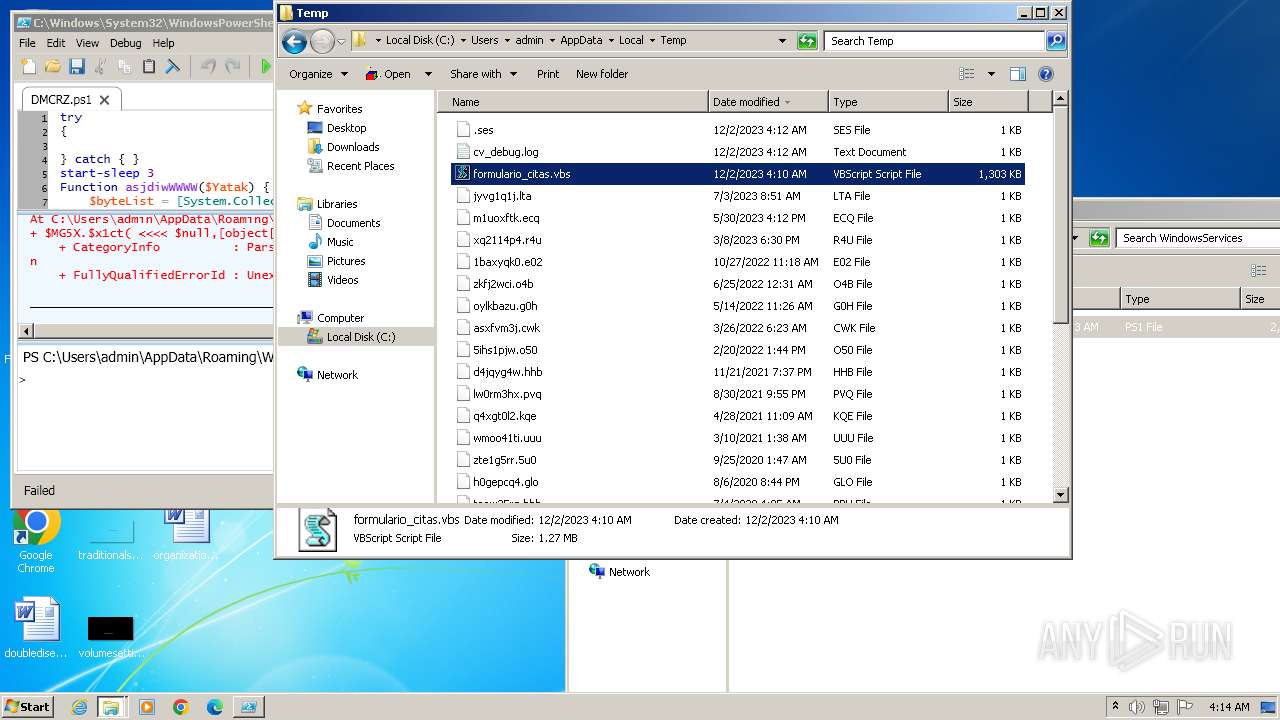
| File name: | formulario_citas.vbs |
| Full analysis: | https://app.any.run/tasks/a2df31a1-e709-469d-9017-4ddf9945876a |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 04:09:54 |
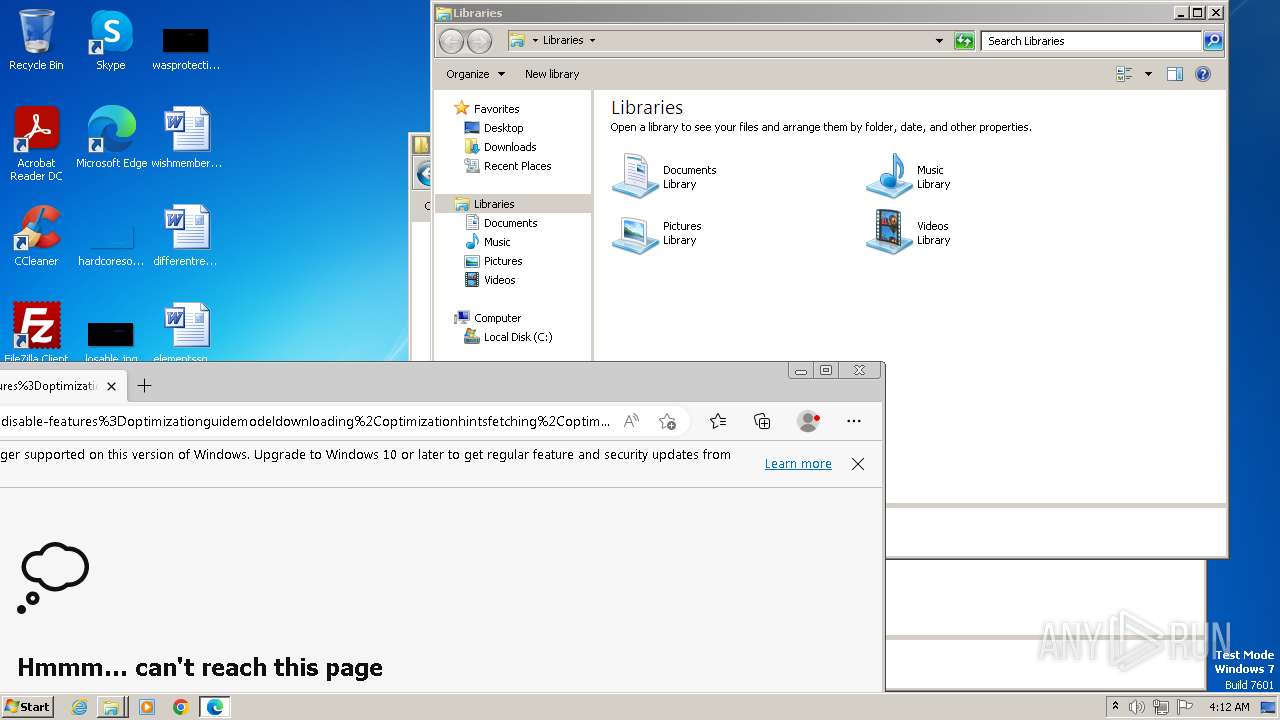
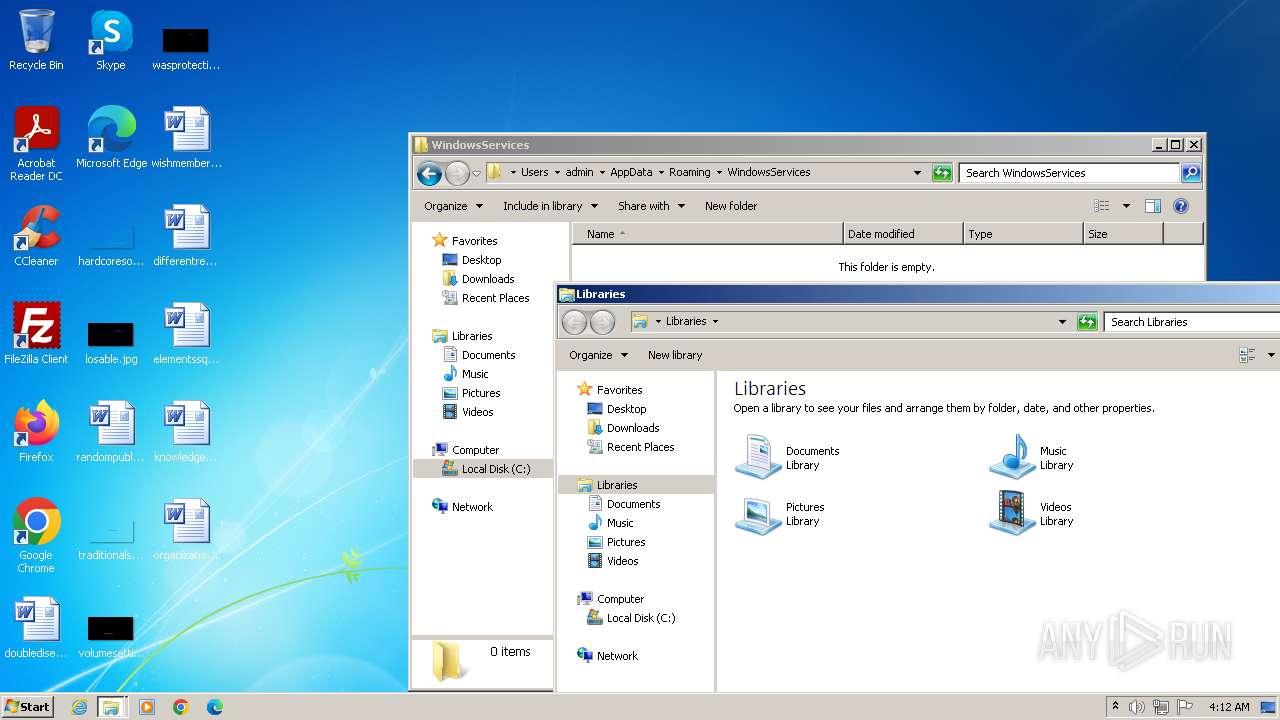
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | UTF-8 Unicode text, with very long lines, with CRLF line terminators |
| MD5: | 4E1C6CA17D6564BB8CDA7D81F9D45704 |
| SHA1: | 4490FCA0E2AA8F973216E2FF91FEC98086293BAC |
| SHA256: | F487C290DEEECCF8CD33AA0A7B6B9316F590A293C7601EFEACA63E07737362AF |
| SSDEEP: | 12288:1jm4G1OGVq0yQ378MPHtm/JTses02bLzYFXrzptZSUYzyzgB:1jaOGVq0yS7kyb6fpsy8B |
MALICIOUS
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
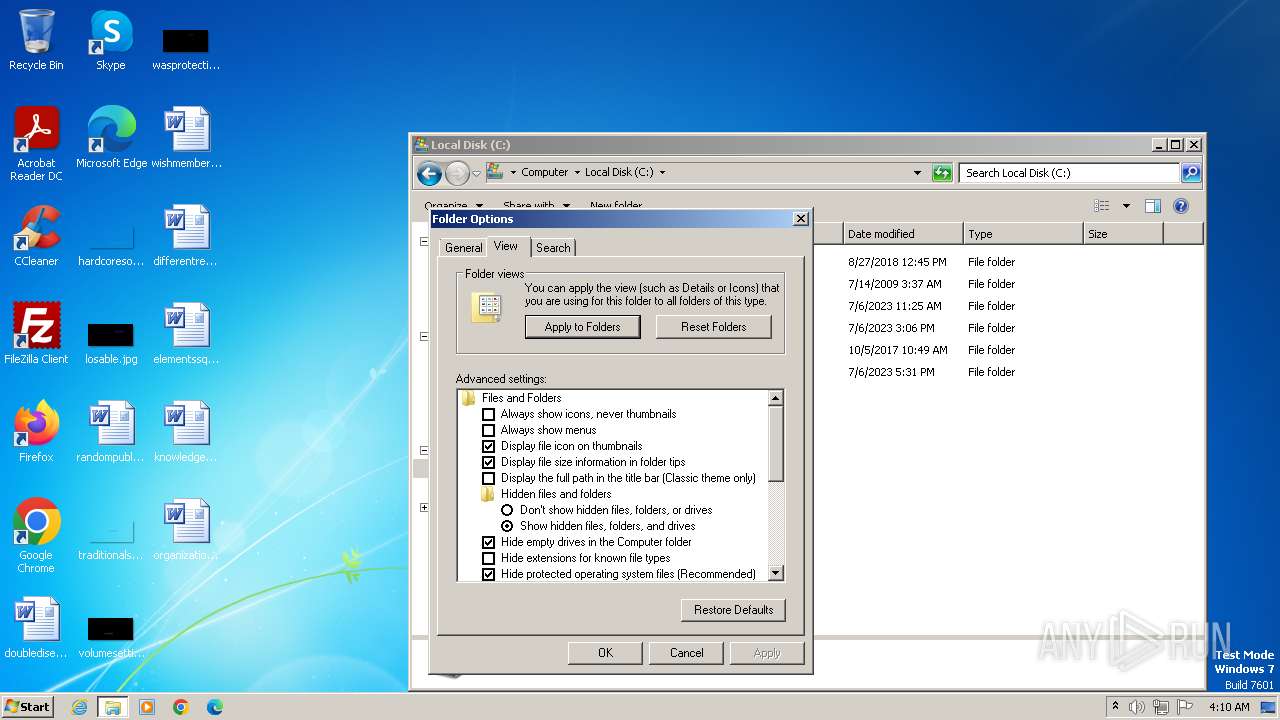
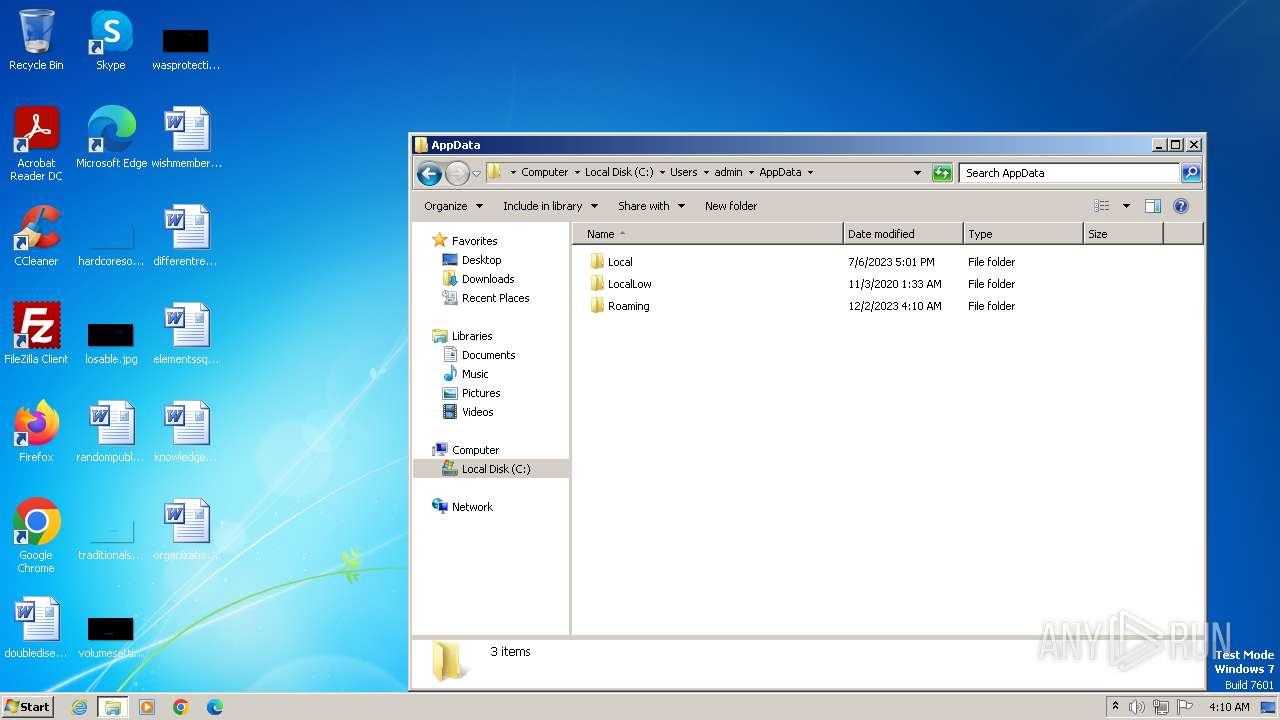
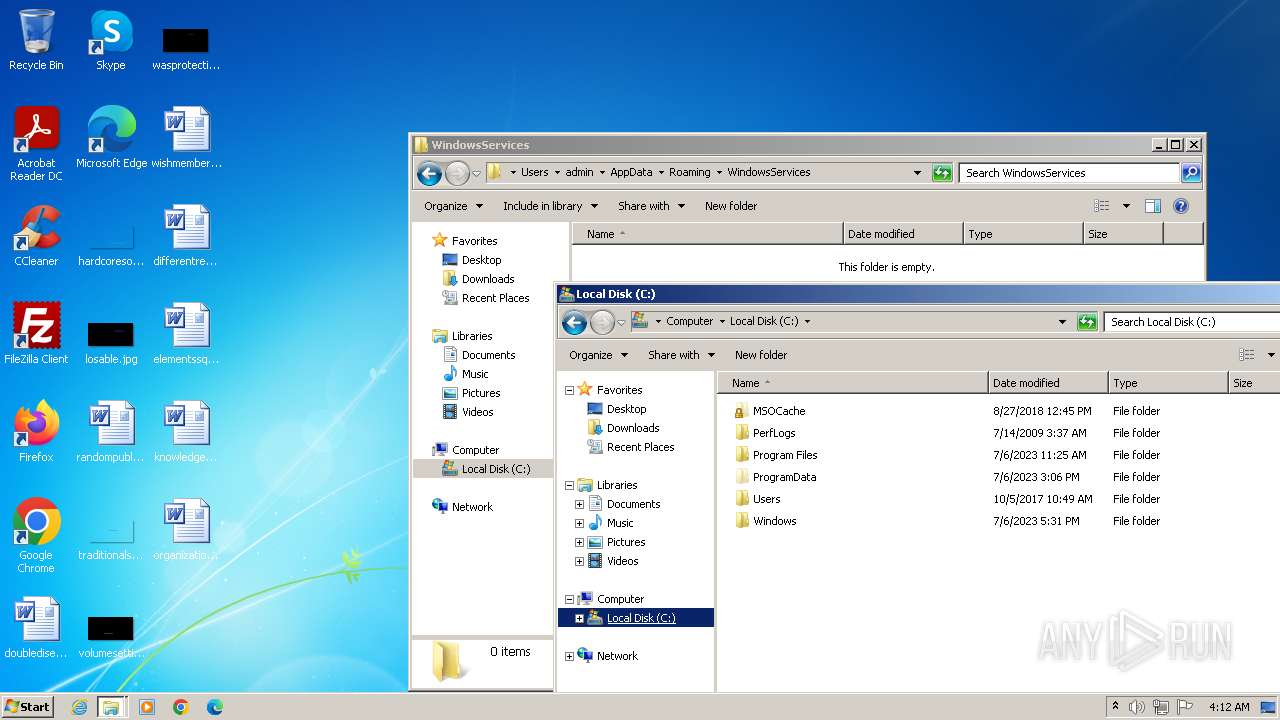
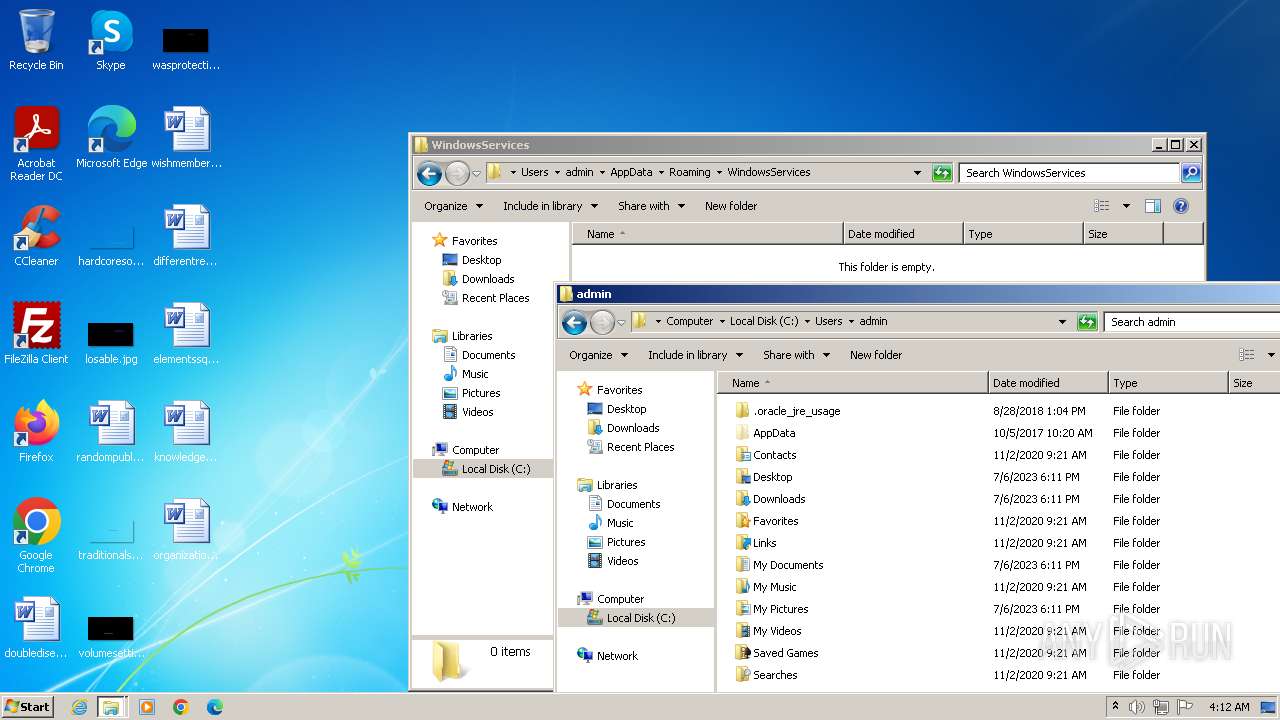
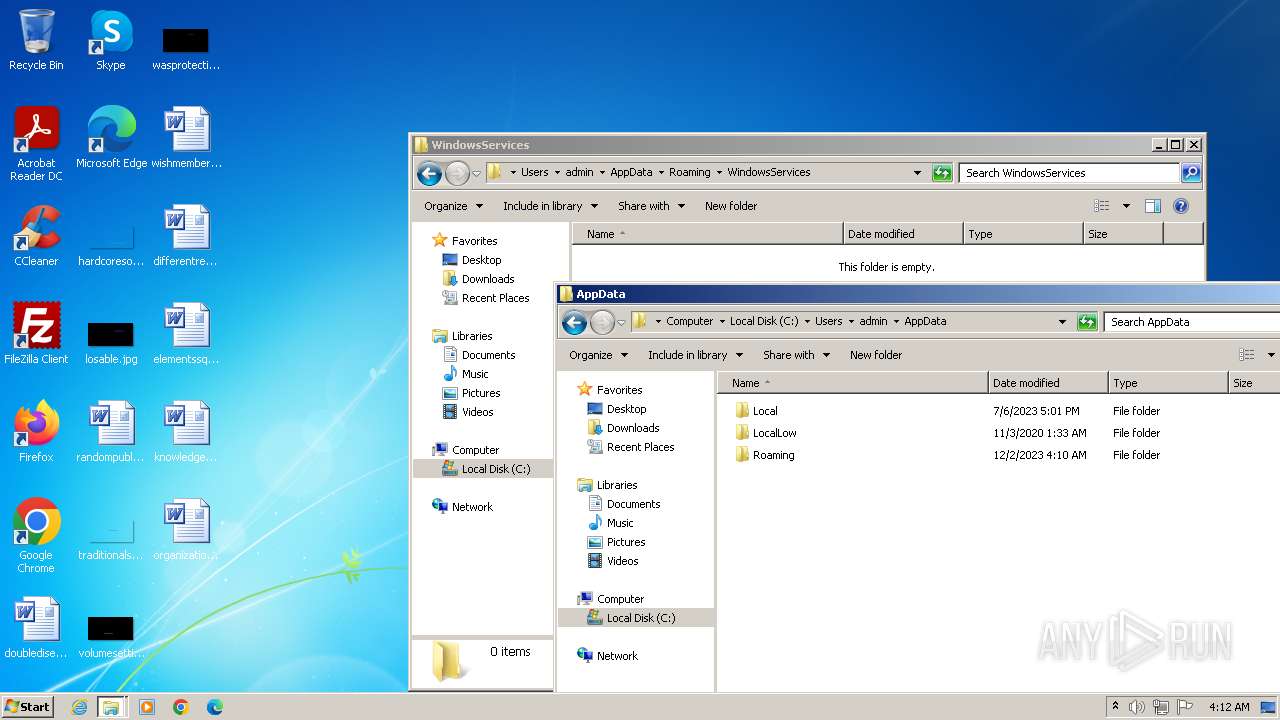
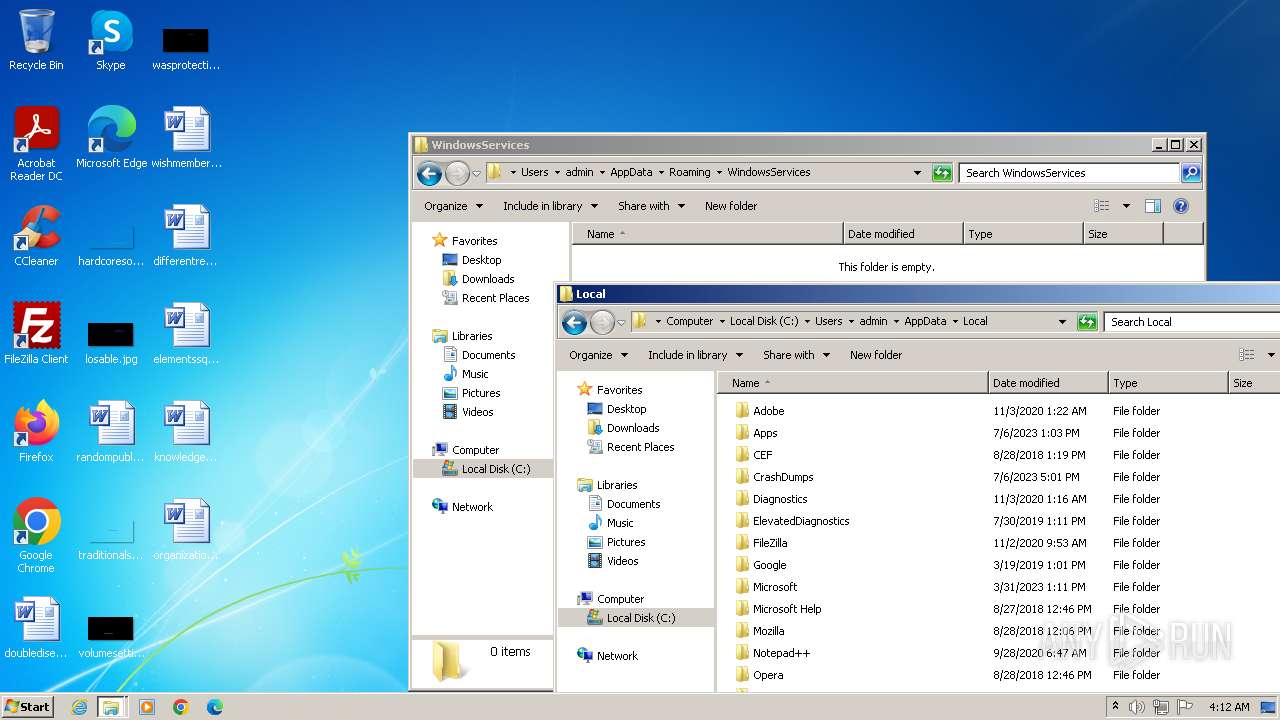
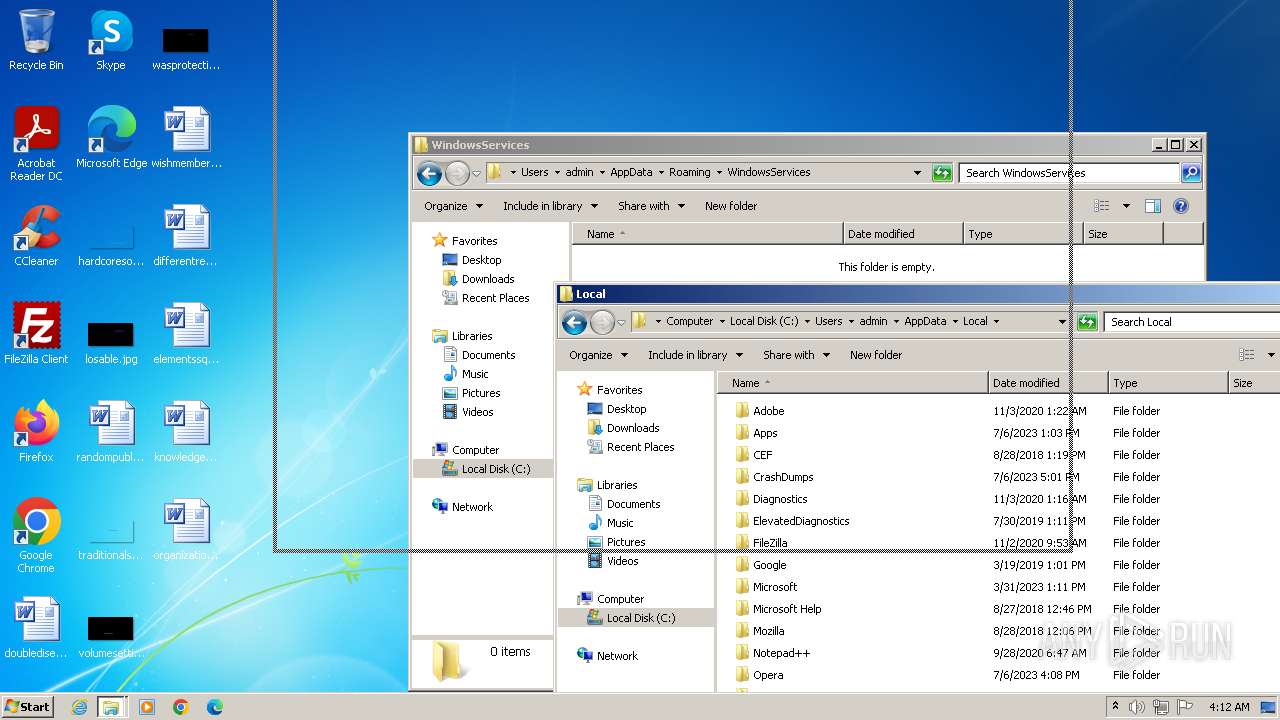
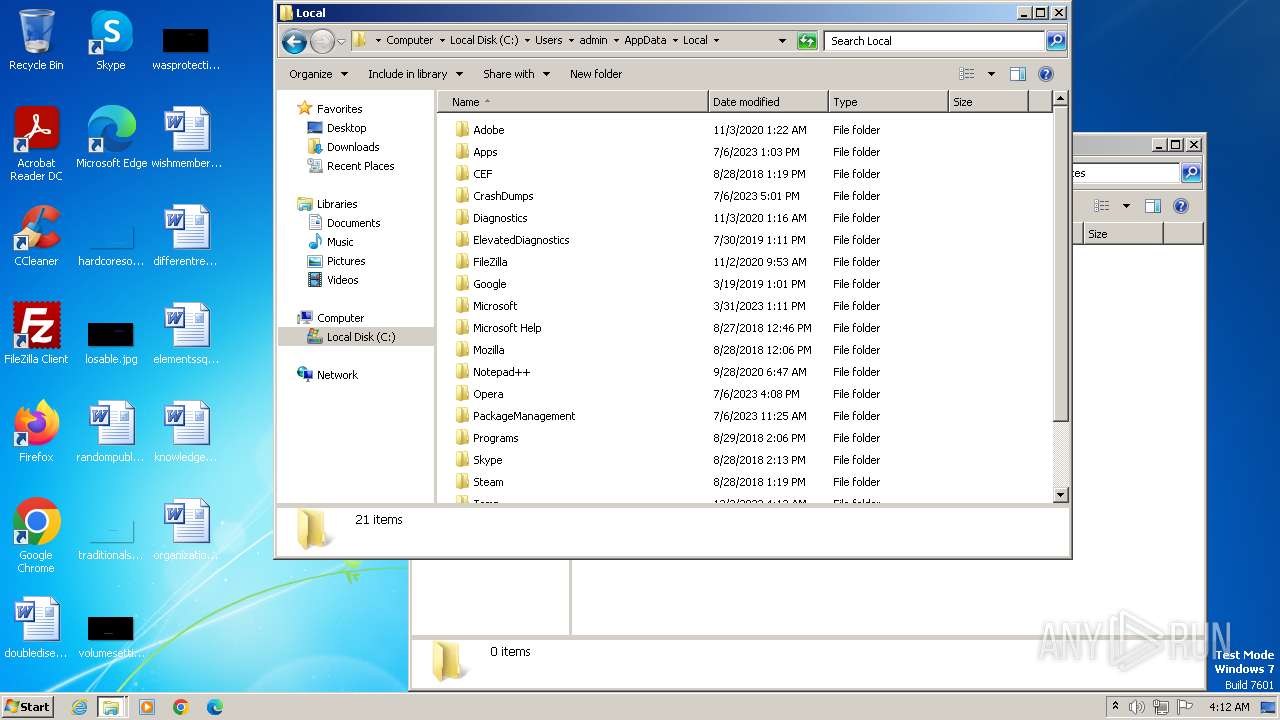
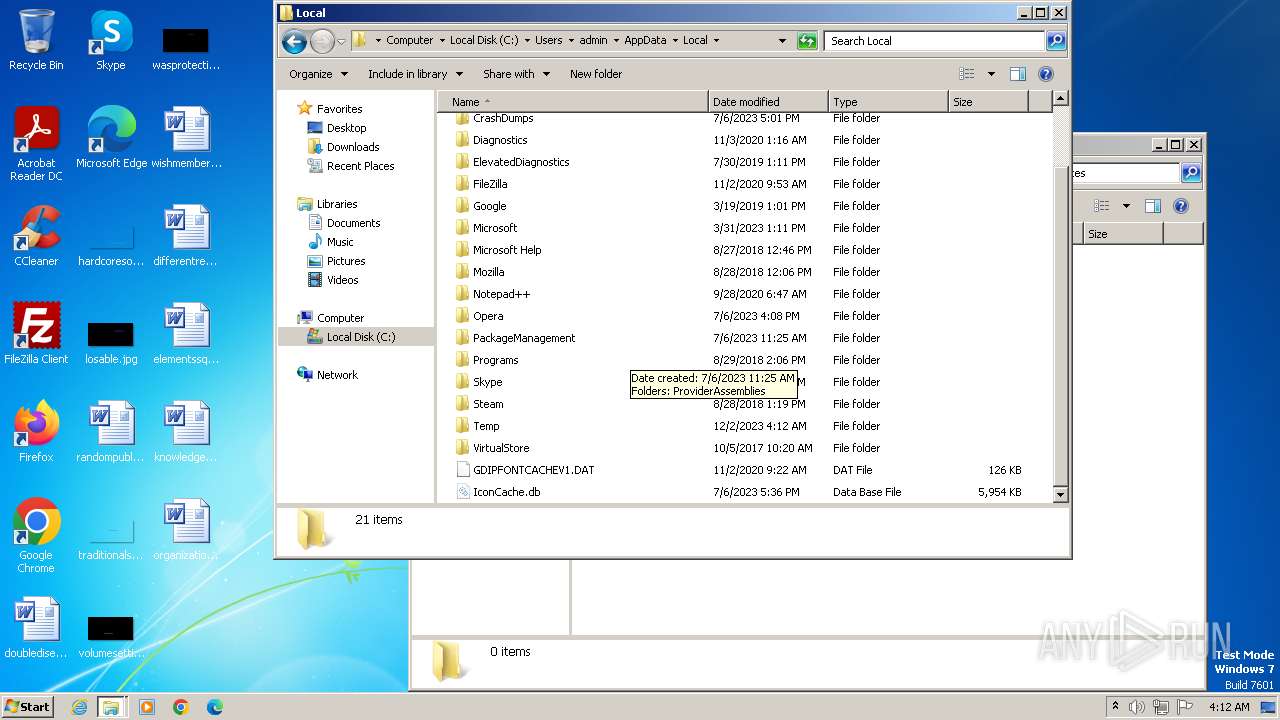
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Deletes a file (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
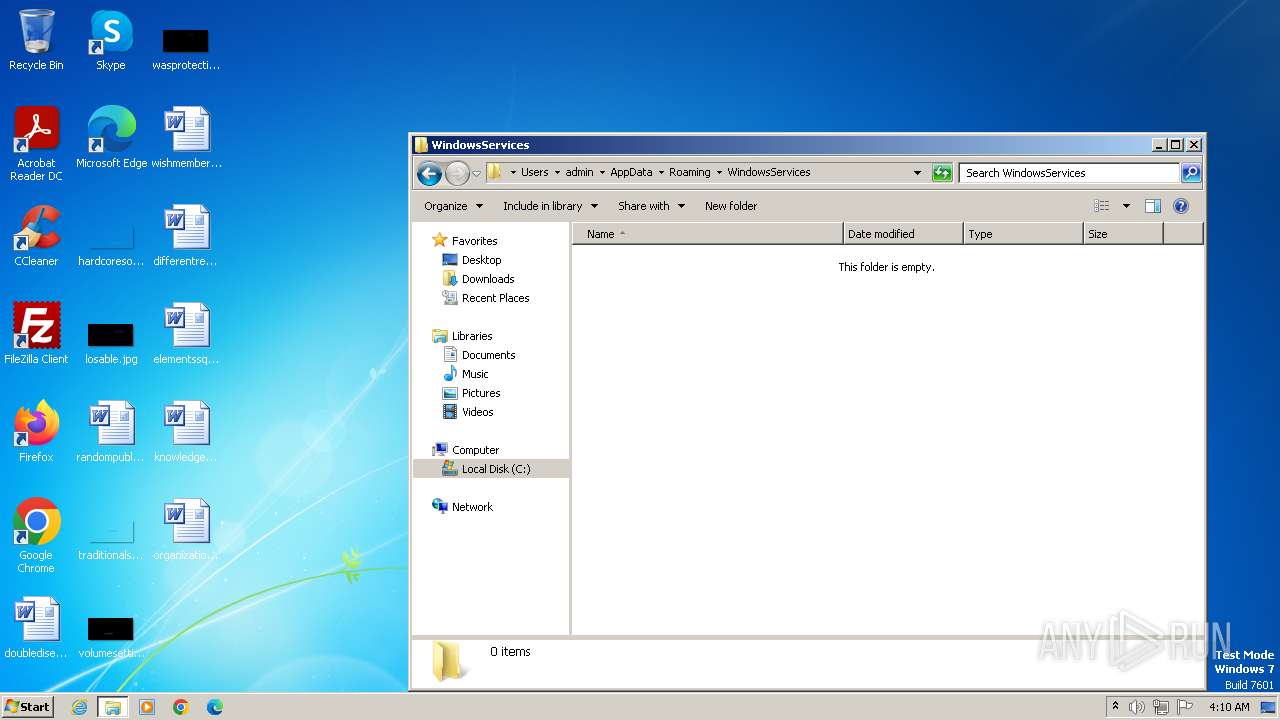
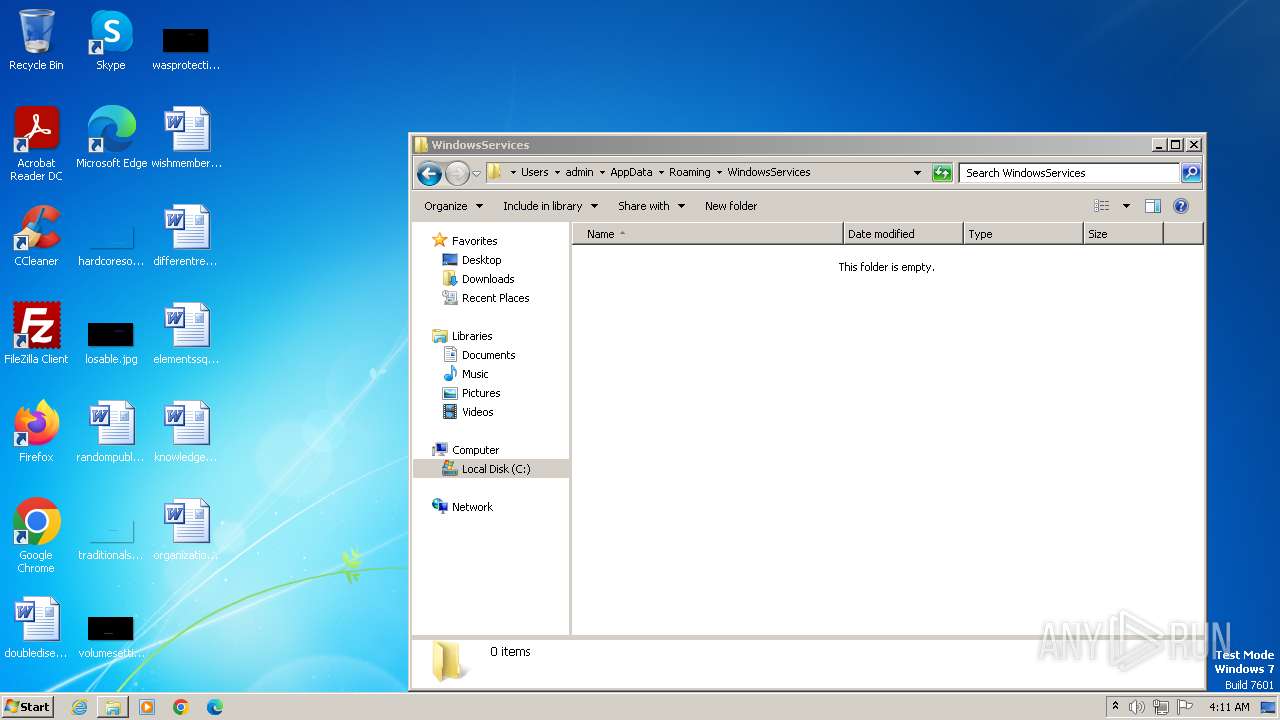
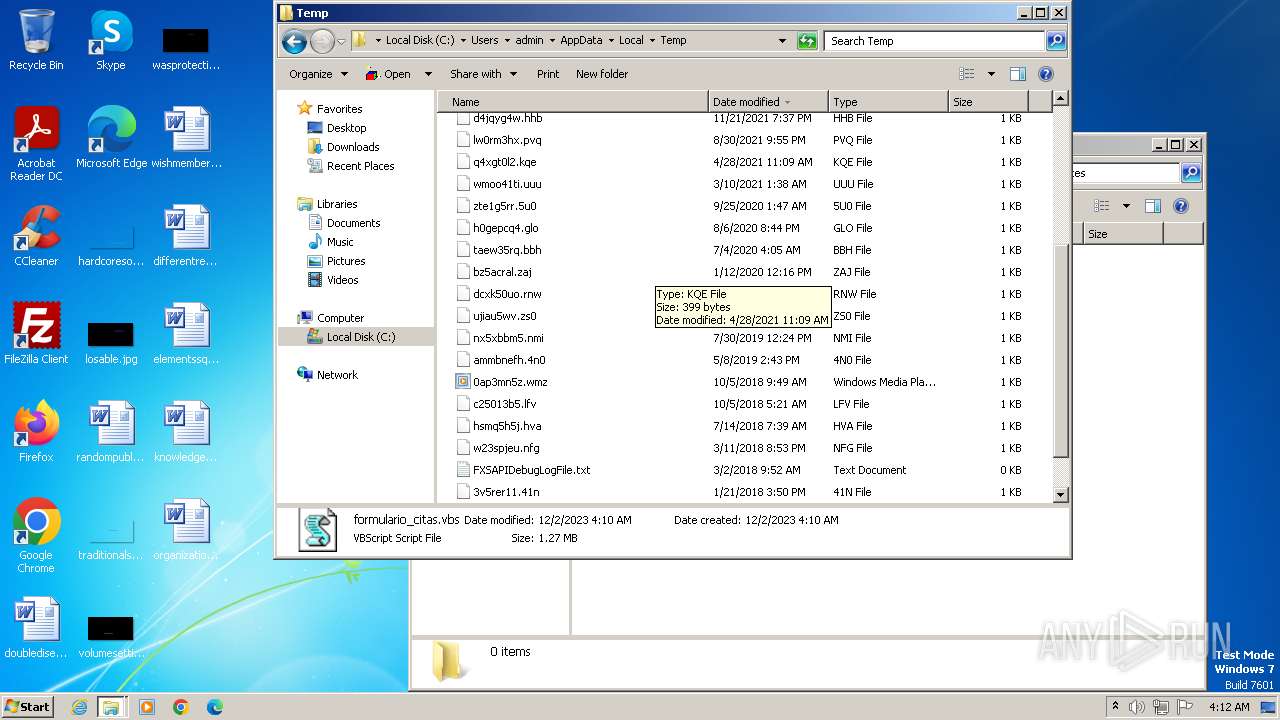
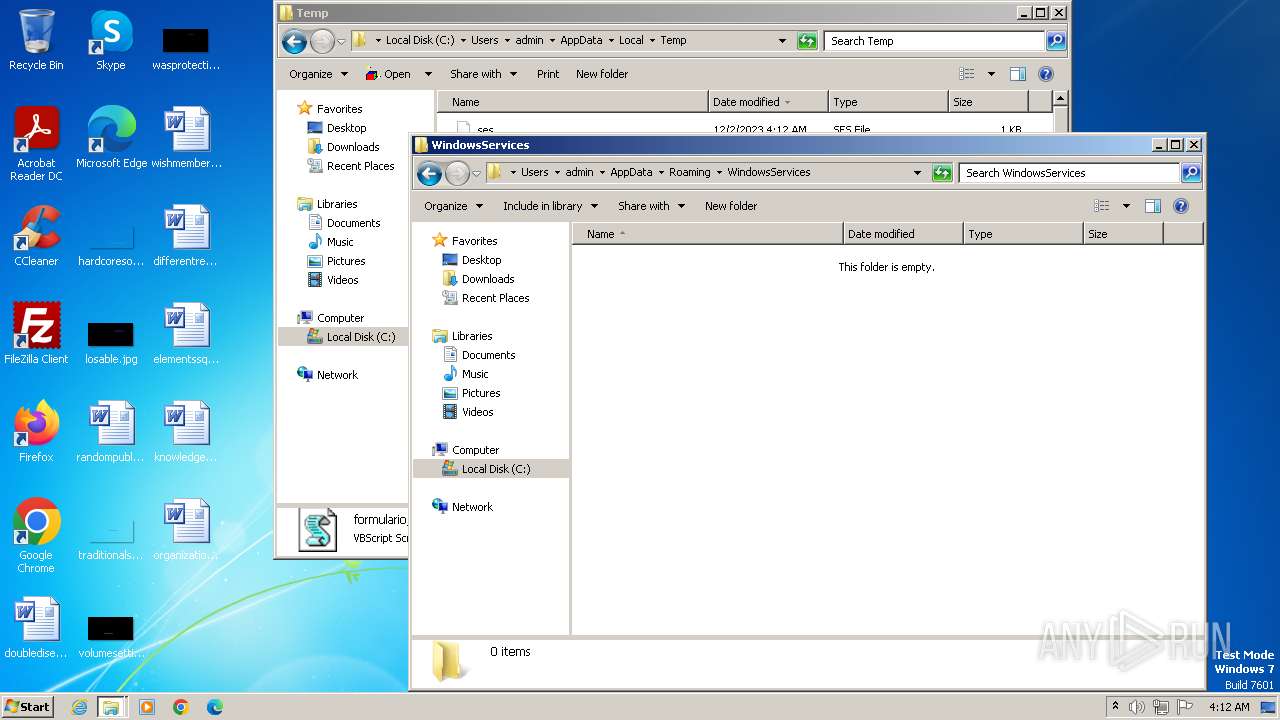
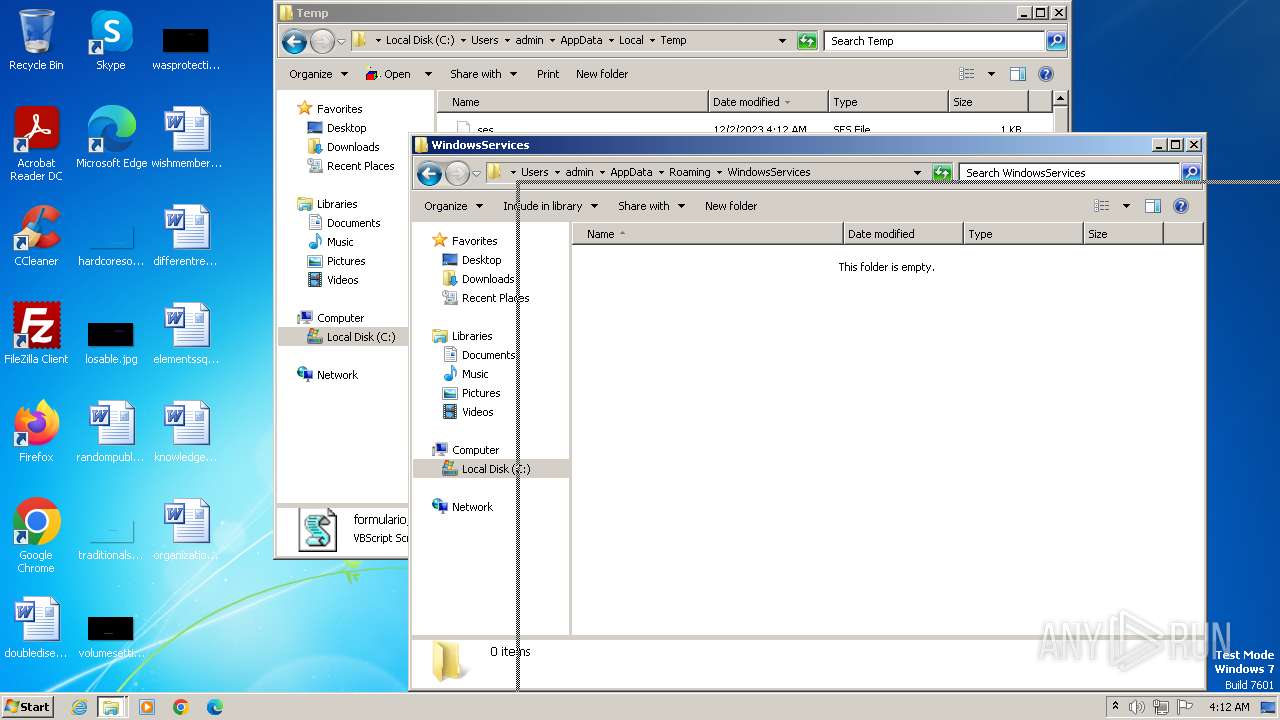
Creates a new folder (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
- wscript.exe (PID: 1840)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 600)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Unusual connection from system programs
- wscript.exe (PID: 564)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
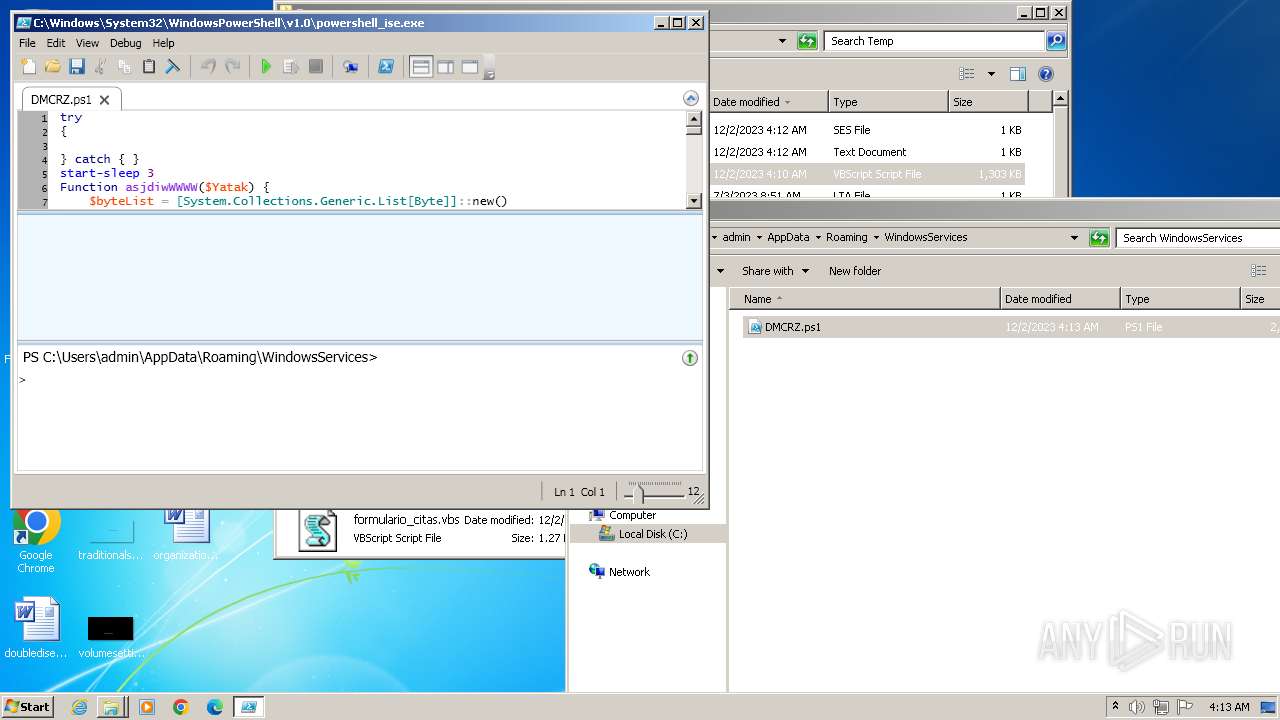
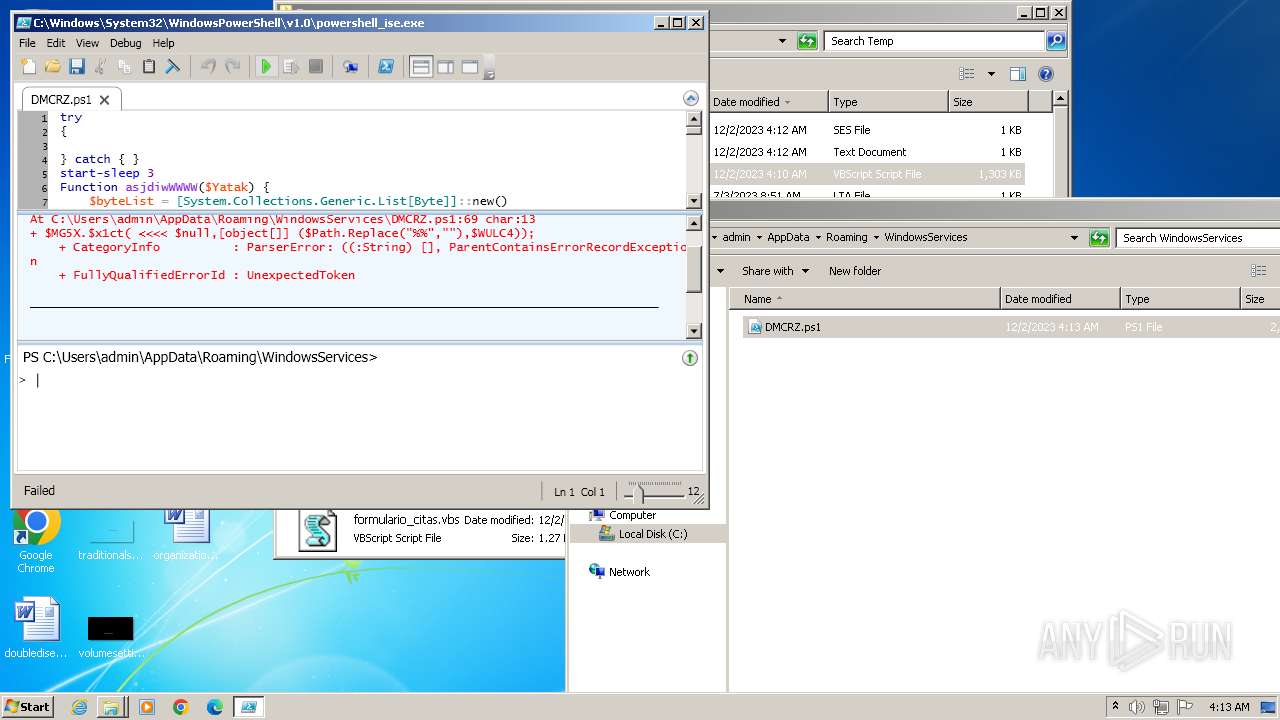
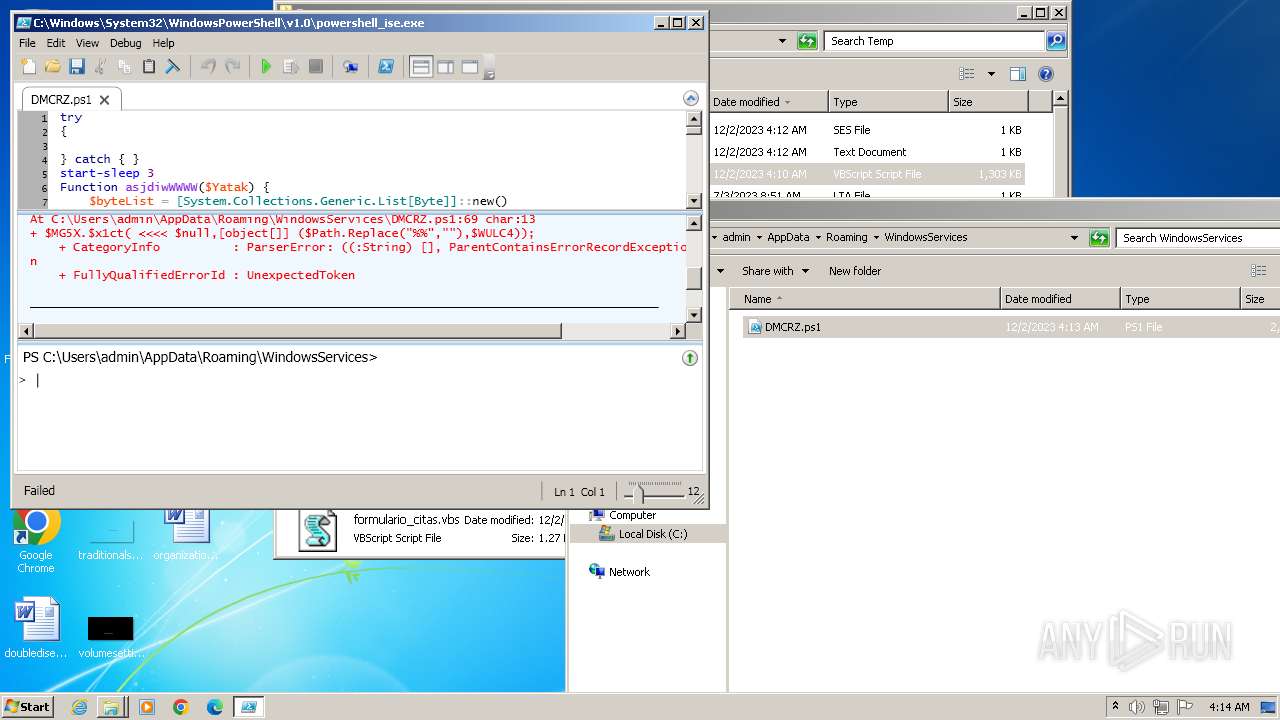
Bypass execution policy to execute commands
- powershell.exe (PID: 2132)
- powershell.exe (PID: 4024)
- powershell.exe (PID: 2428)
- powershell.exe (PID: 2396)
- powershell.exe (PID: 292)
- powershell.exe (PID: 3164)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 3756)
- powershell.exe (PID: 4048)
- powershell.exe (PID: 1444)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1556)
- cmd.exe (PID: 3368)
- cmd.exe (PID: 2884)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 1032)
- cmd.exe (PID: 2936)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2308)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 600)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Opens a text file (SCRIPT)
- wscript.exe (PID: 4032)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 600)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Reads the Internet Settings
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- powershell_ise.exe (PID: 3792)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
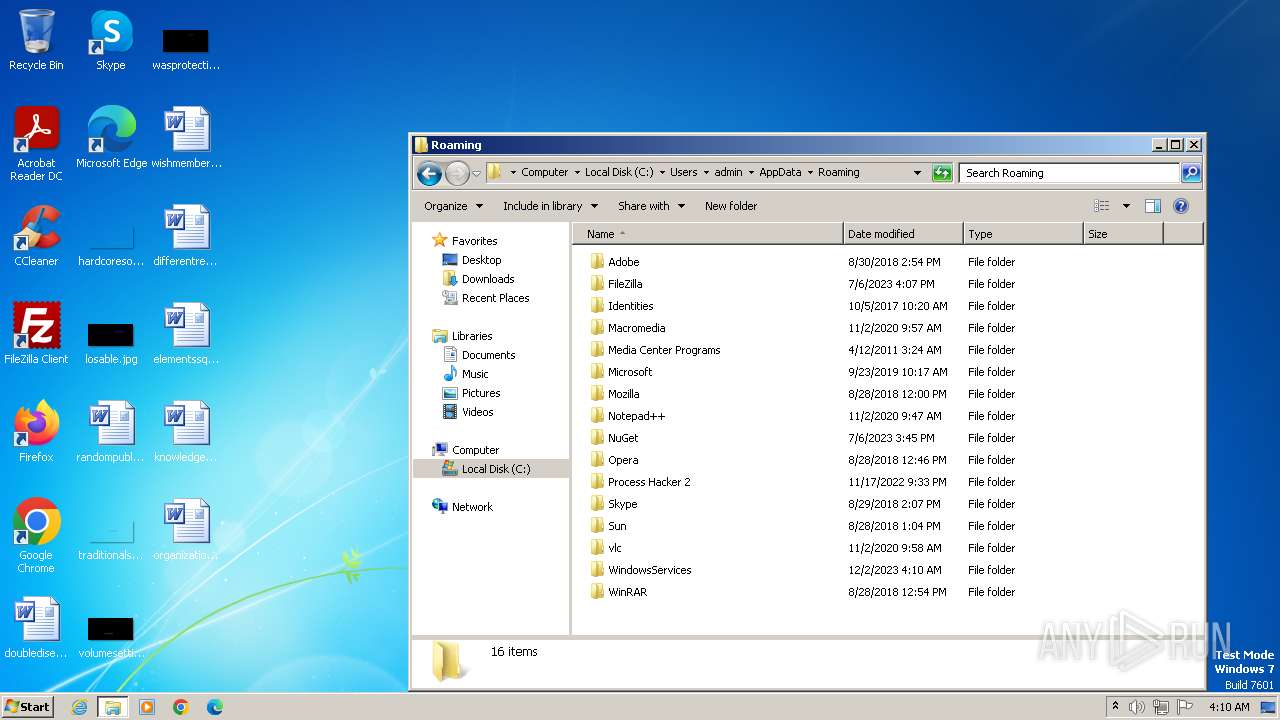
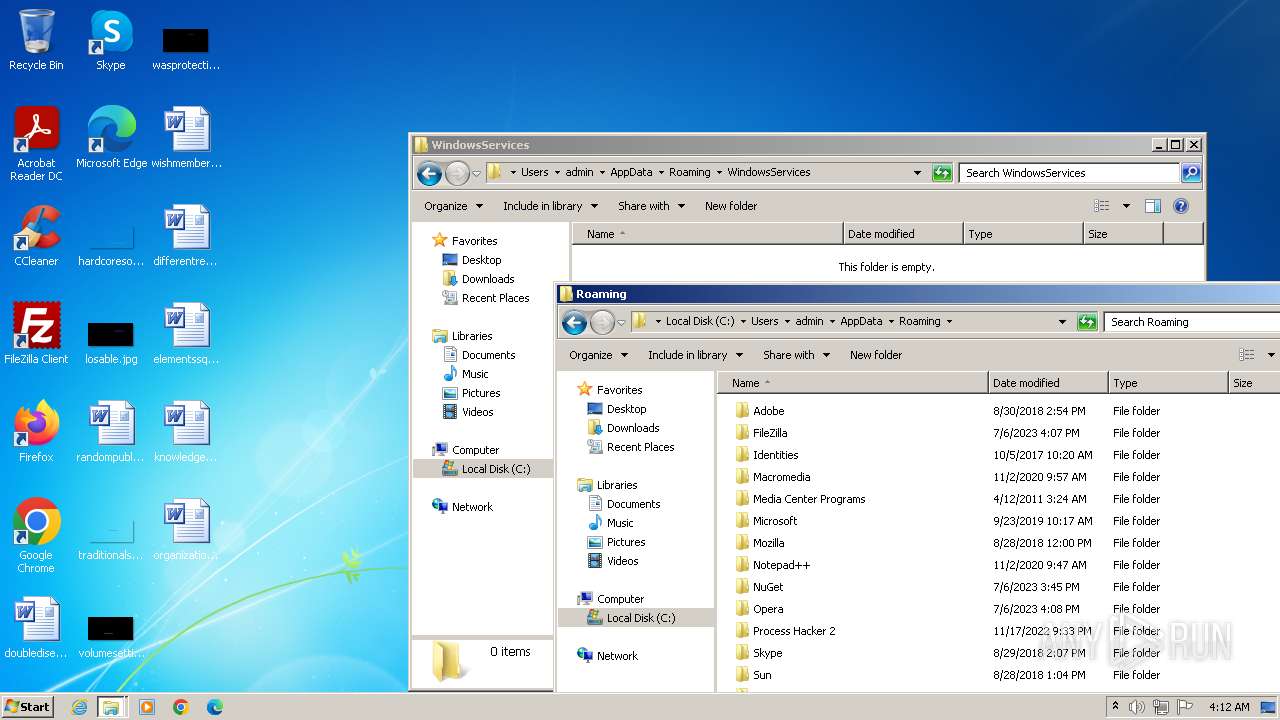
Executing commands from ".cmd" file
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
- wscript.exe (PID: 4032)
The process executes Powershell scripts
- cmd.exe (PID: 1556)
- cmd.exe (PID: 3368)
- cmd.exe (PID: 2884)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 1032)
- cmd.exe (PID: 2936)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2308)
Runs shell command (SCRIPT)
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1556)
- cmd.exe (PID: 3368)
- cmd.exe (PID: 2884)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 1032)
- cmd.exe (PID: 2936)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2308)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
- wscript.exe (PID: 4032)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1556)
- cmd.exe (PID: 3368)
- cmd.exe (PID: 2884)
- cmd.exe (PID: 3152)
- cmd.exe (PID: 1032)
- cmd.exe (PID: 2936)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 2364)
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2308)
Powershell version downgrade attack
- powershell.exe (PID: 2132)
- powershell.exe (PID: 4024)
- powershell.exe (PID: 2428)
- powershell.exe (PID: 2396)
- powershell.exe (PID: 292)
- powershell.exe (PID: 3164)
- powershell.exe (PID: 1352)
- powershell.exe (PID: 3756)
- powershell.exe (PID: 4048)
- powershell.exe (PID: 1444)
- powershell.exe (PID: 2092)
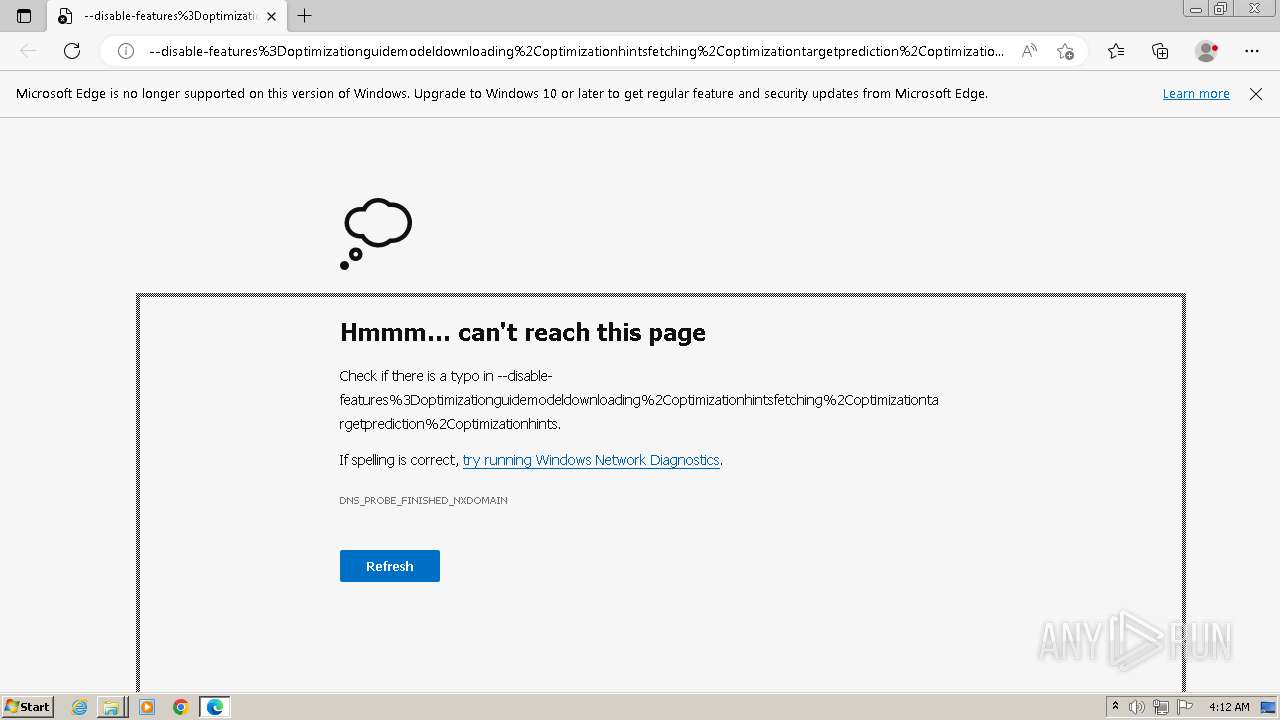
Block-list domains
- wscript.exe (PID: 564)
Executes as Windows Service
- PresentationFontCache.exe (PID: 4052)
INFO
Checks proxy server information
- wscript.exe (PID: 564)
- wscript.exe (PID: 3508)
- wscript.exe (PID: 600)
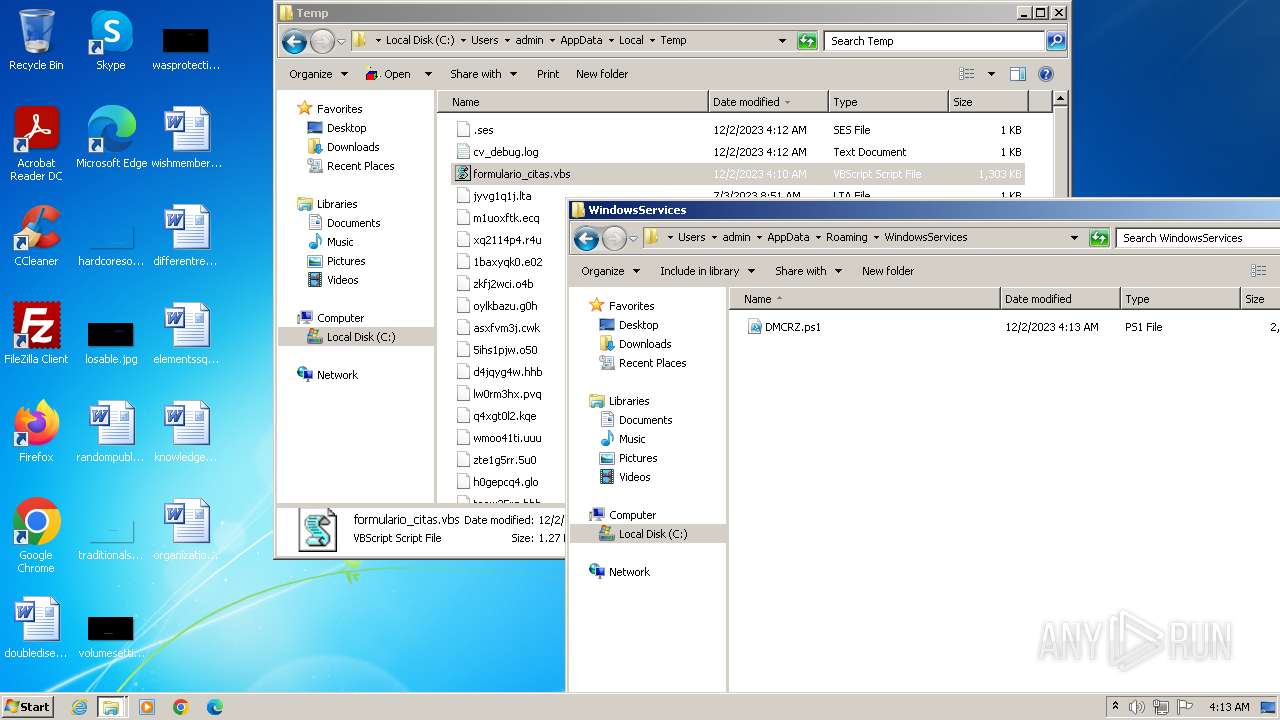
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Manual execution by a user
- wmpnscfg.exe (PID: 3064)
- explorer.exe (PID: 3516)
- wscript.exe (PID: 3508)
- msedge.exe (PID: 3536)
- explorer.exe (PID: 1560)
- wscript.exe (PID: 600)
- wscript.exe (PID: 3780)
- wscript.exe (PID: 2376)
- wscript.exe (PID: 296)
- wscript.exe (PID: 1128)
- wscript.exe (PID: 4032)
- powershell_ise.exe (PID: 3792)
- wscript.exe (PID: 1840)
- wscript.exe (PID: 1656)
- wscript.exe (PID: 3080)
Checks supported languages
- wmpnscfg.exe (PID: 3064)
- PresentationFontCache.exe (PID: 4052)
Reads the computer name
- wmpnscfg.exe (PID: 3064)
- PresentationFontCache.exe (PID: 4052)
Application launched itself
- msedge.exe (PID: 3536)
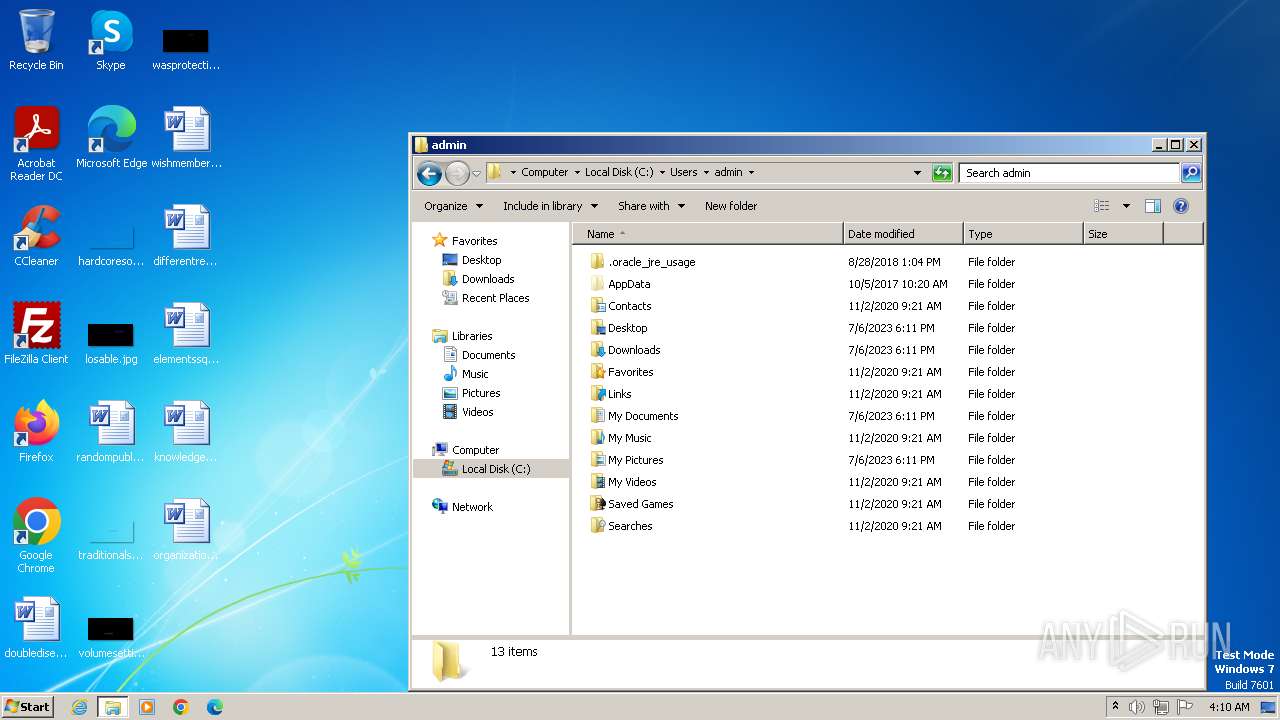
Creates files or folders in the user directory
- powershell_ise.exe (PID: 3792)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 3792)
Reads the machine GUID from the registry
- PresentationFontCache.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
110
Monitored processes
55
Malicious processes
33
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | PowerShell.exe -NoProfile -ExecutionPolicy Bypass -Command C:\Users\admin\AppData\Roaming\WindowsServices\DMCRZ.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 296 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\formulario_citas.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 564 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\formulario_citas.vbs" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 600 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\formulario_citas.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1604 --field-trial-handle=1300,i,17213568249812586339,473599596863128336,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1636 --field-trial-handle=1300,i,17213568249812586339,473599596863128336,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3276 --field-trial-handle=1300,i,17213568249812586339,473599596863128336,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1032 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\WindowsServices\MNBNJ.cmd" " | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1128 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\formulario_citas.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3252 --field-trial-handle=1300,i,17213568249812586339,473599596863128336,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
28 988
Read events
28 099
Write events
888
Delete events
1
Modification events
| (PID) Process: | (564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005A010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (564) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2132) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3536) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
0
Suspicious files
90
Text files
67
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF2240ad.TMP | — | |
MD5:— | SHA256:— | |||
| 3536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF2240dc.TMP | — | |
MD5:— | SHA256:— | |||
| 3536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF2240eb.TMP | — | |
MD5:— | SHA256:— | |||
| 2132 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1JMDVWLLXGL1ZN9X7X1M.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 3536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:C7352A0E98449CC8AEDC1D6954C4CCD9 | SHA256:3A1591F52AD31B5B0B48F97AB5E1361D0AD0FA0F584E8FE8EFD482801DC2B9B5 | |||
| 564 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\paste[1].txt | text | |
MD5:67A8459776D596C615239A17AA3BAC19 | SHA256:FF9BD9E62EAED82501E348259692AD3DAB0DCF1DFF7D482031FE069F294C97C4 | |||
| 3536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF22412a.TMP | — | |
MD5:— | SHA256:— | |||
| 3536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
14
DNS requests
13
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
564 | wscript.exe | GET | 200 | 197.205.250.64:80 | http://tiny24.duckdns.org/paste.txt | unknown | text | 115 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
564 | wscript.exe | 197.205.250.64:80 | tiny24.duckdns.org | Telecom Algeria | DZ | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2448 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3536 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2448 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2448 | msedge.exe | 23.48.23.62:443 | msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com | Akamai International B.V. | DE | unknown |
3536 | msedge.exe | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tiny24.duckdns.org |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
564 | wscript.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.duckdns .org Domain |
Process | Message |
|---|---|
powershell_ise.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
powershell_ise.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
powershell_ise.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
powershell_ise.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
powershell_ise.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
powershell_ise.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
powershell_ise.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
powershell_ise.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
powershell_ise.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
powershell_ise.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|