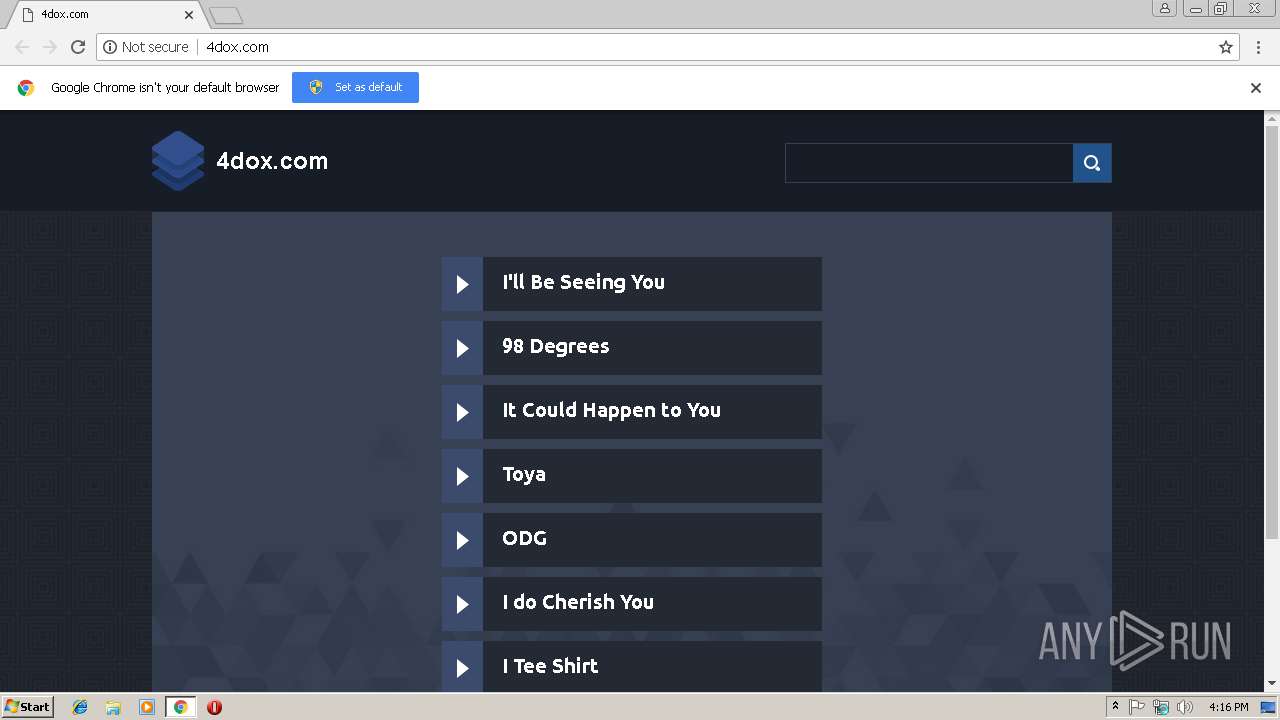
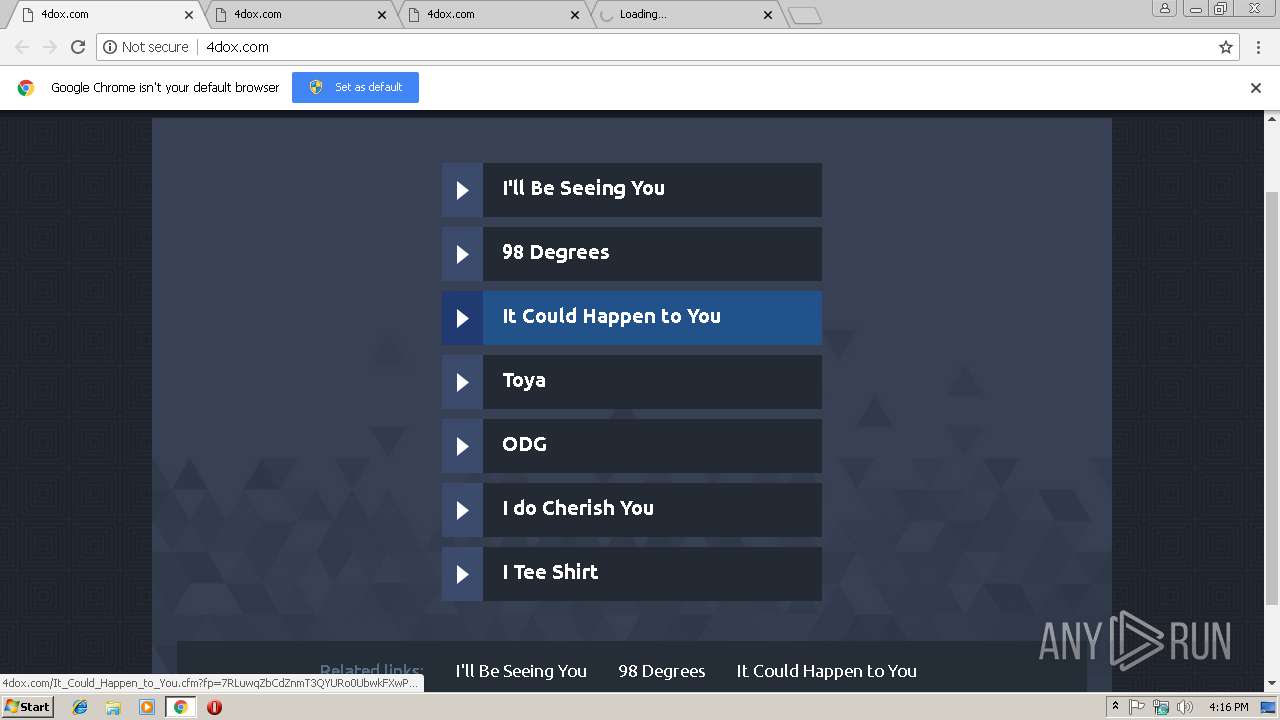
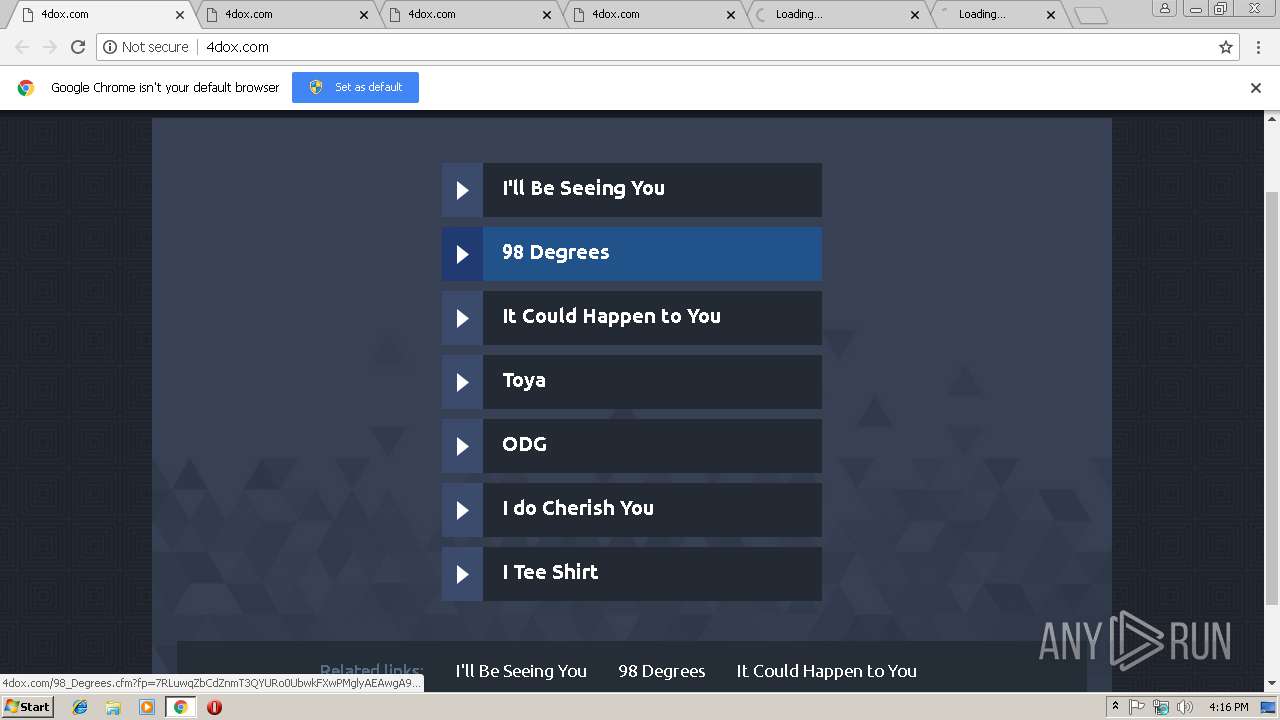
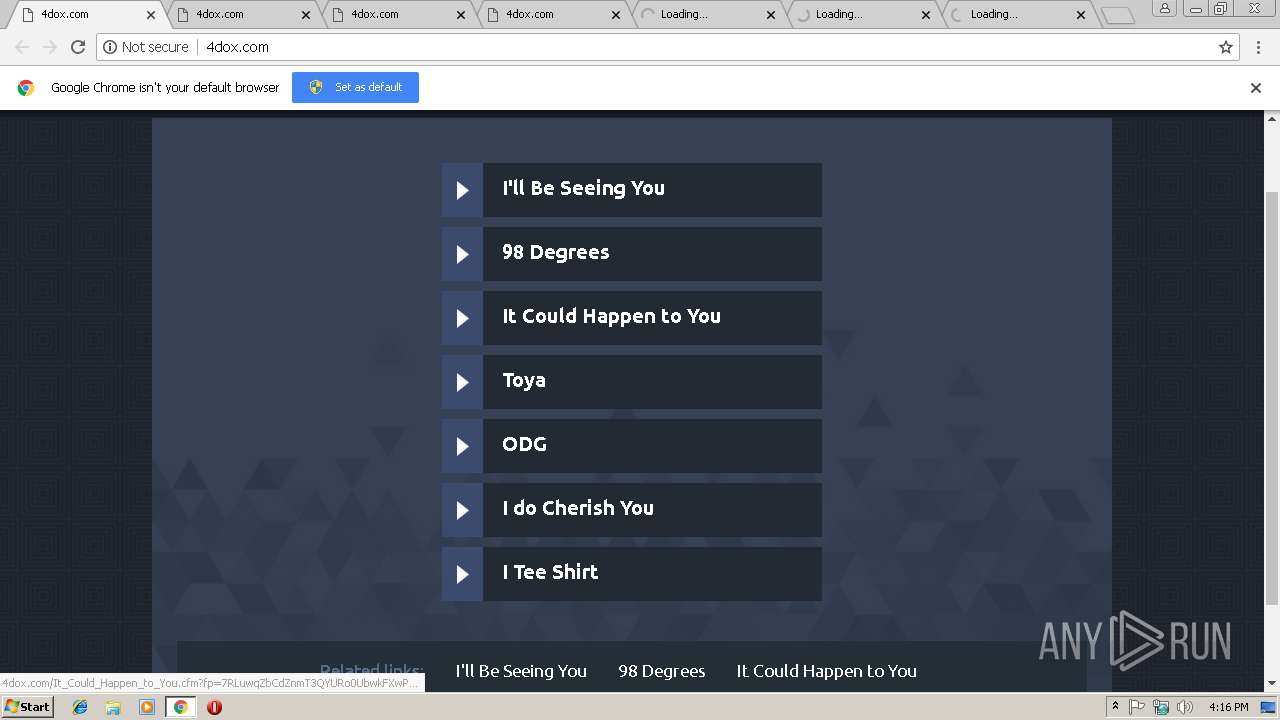
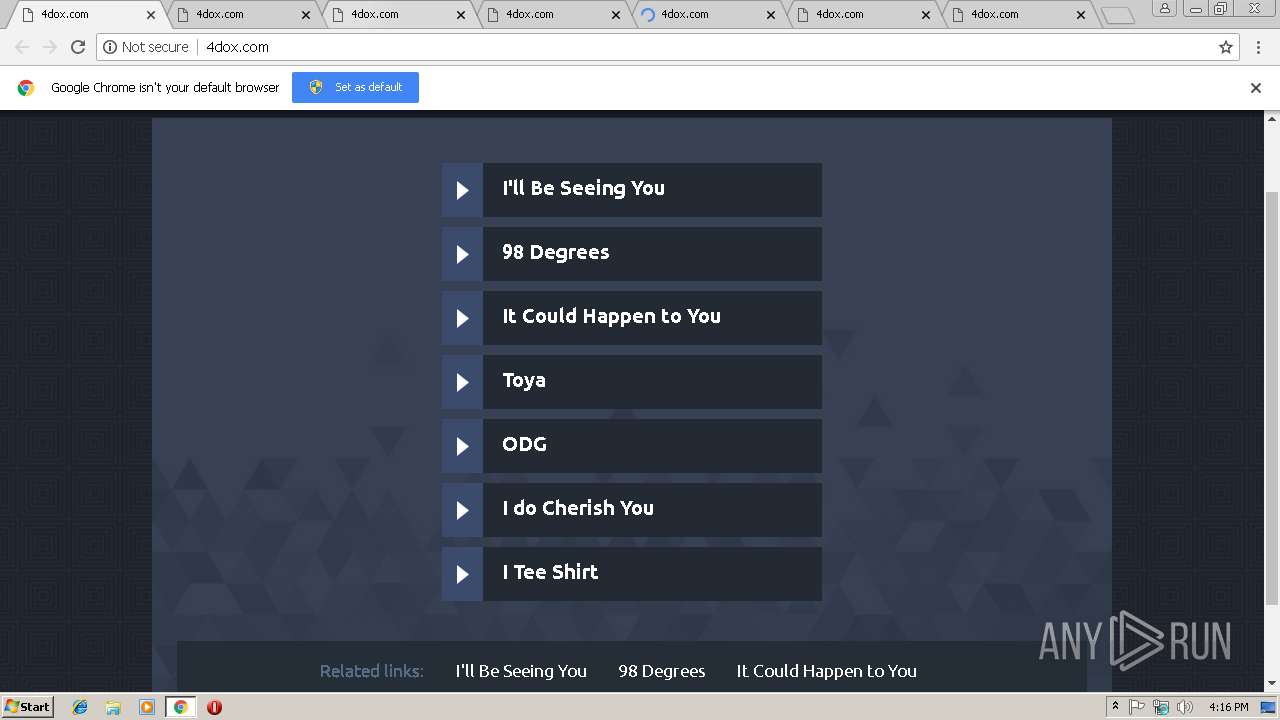
| URL: | http://4dox.com |
| Full analysis: | https://app.any.run/tasks/38e36c48-3481-4f97-9226-8243c705b561 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 16:16:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DA7AD6BBAF5564C471512165874D0852 |
| SHA1: | EBA4EA950A4A0AFEA77B8D01A8FD840035A4FD8C |
| SHA256: | F480CB16D8051034D6A9CF8644C35E1EF3873ADD6C032811055400384572862F |
| SSDEEP: | 3:N1KBdLK:CfK |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes settings of System certificates
- chrome.exe (PID: 3000)
Reads settings of System Certificates
- chrome.exe (PID: 3000)
Application launched itself
- chrome.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
28
Malicious processes
0
Suspicious processes
0
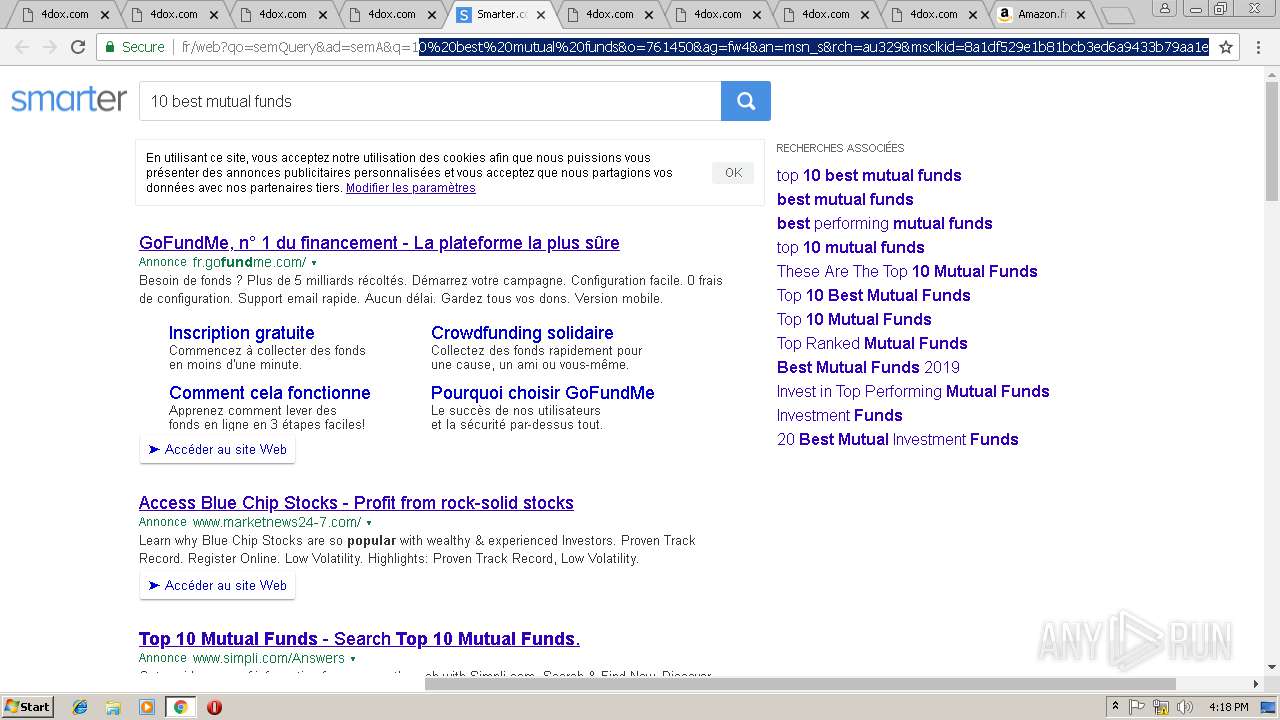
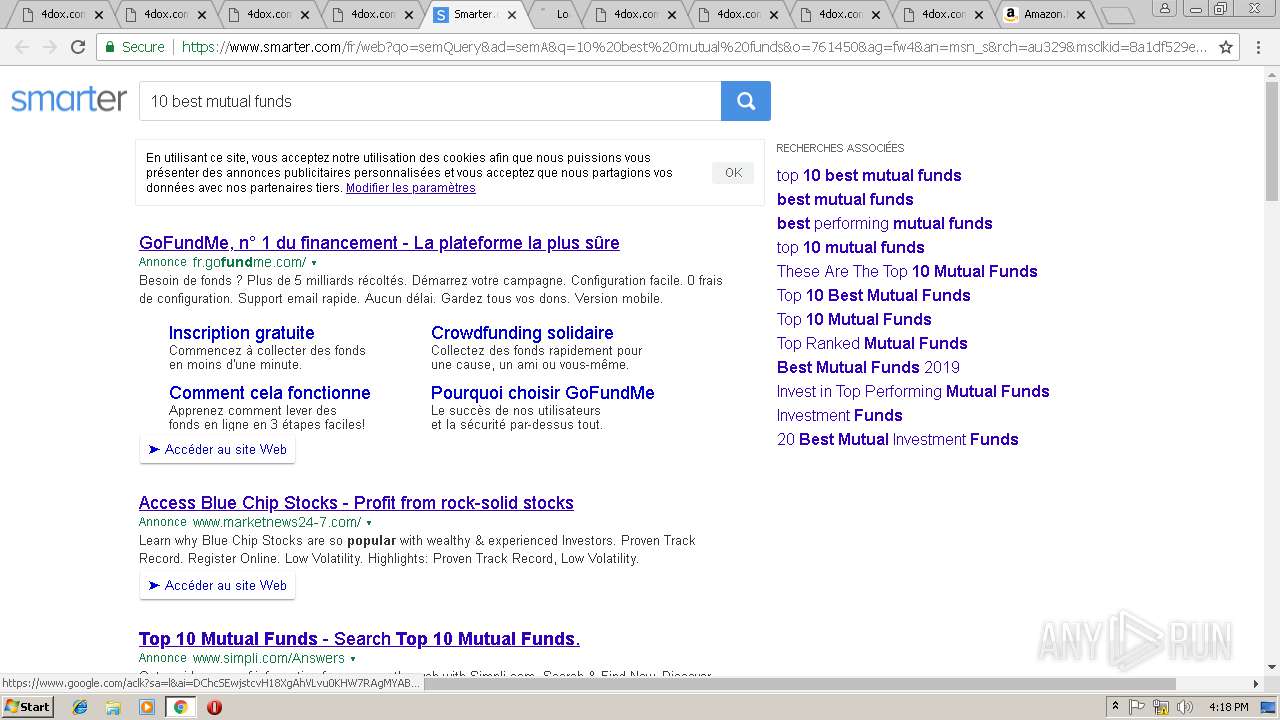
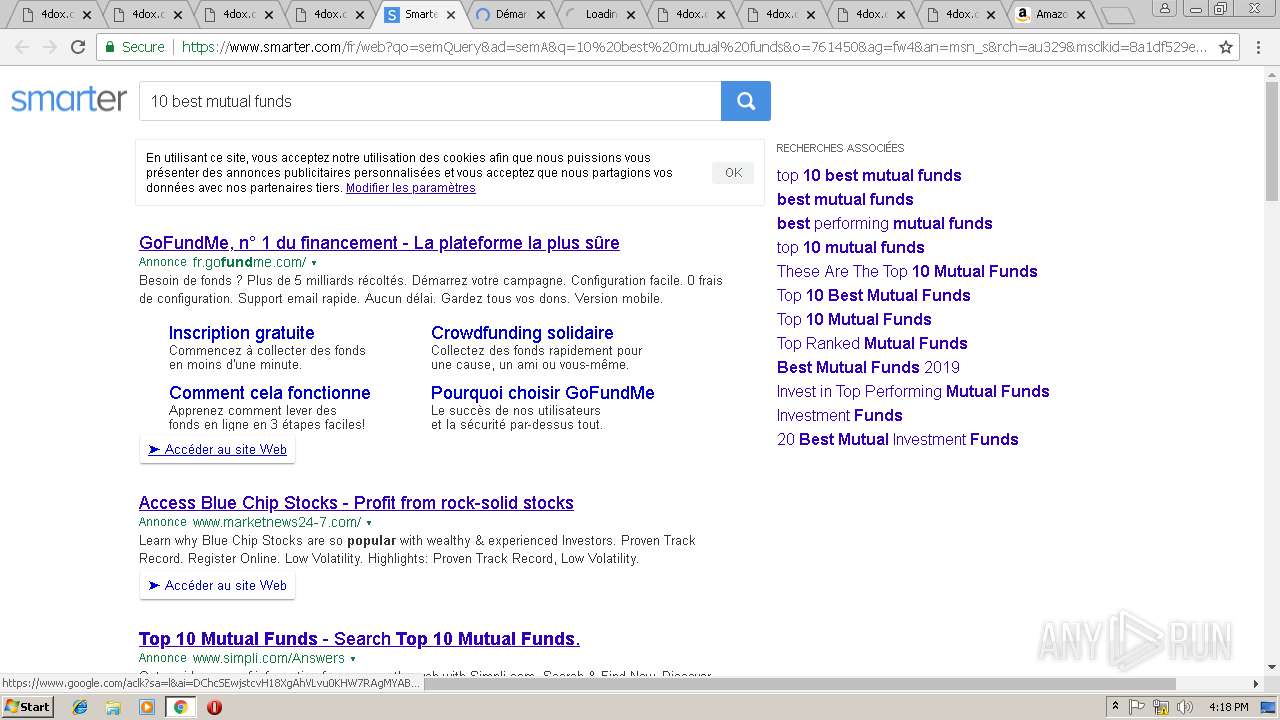
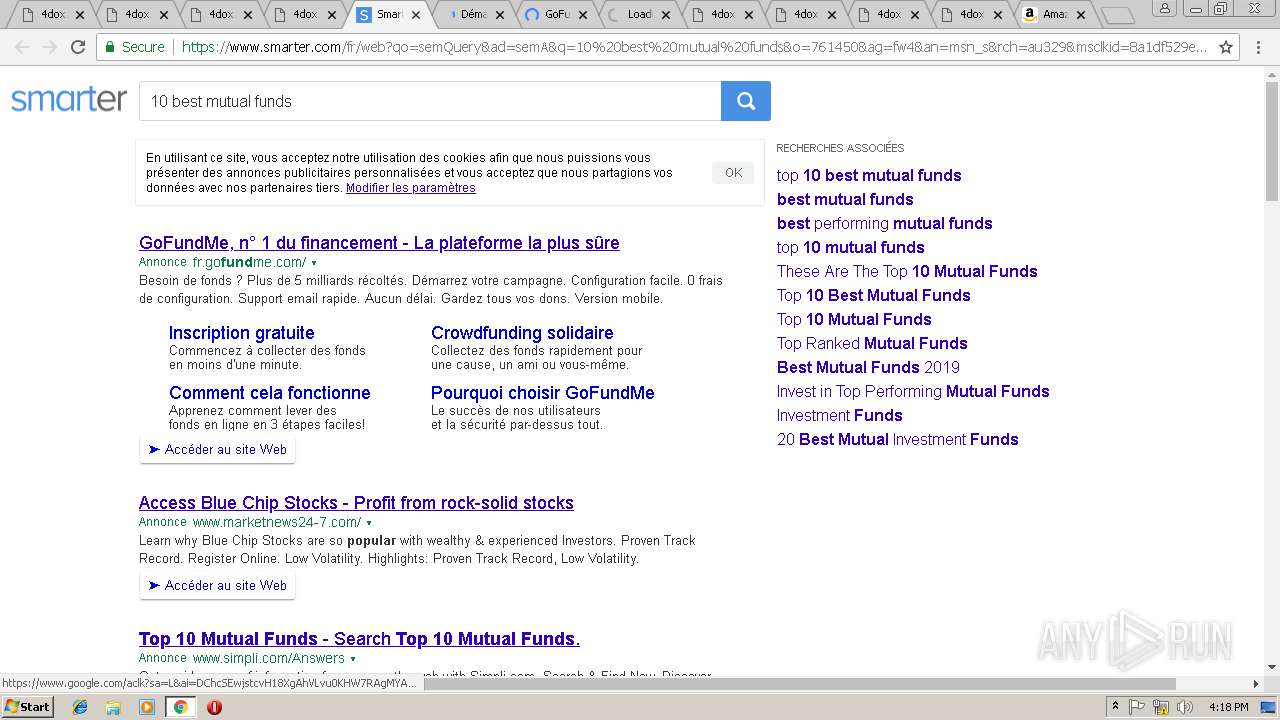
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0C628E31A4D985B7844DAE0A663A8E95 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0C628E31A4D985B7844DAE0A663A8E95 --renderer-client-id=25 --mojo-platform-channel-handle=7248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6CFB99394C85365BA6FA85AC13AB929E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6CFB99394C85365BA6FA85AC13AB929E --renderer-client-id=22 --mojo-platform-channel-handle=6124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=20398B2C5BE89BFCFF4791D51FDA5D9D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=20398B2C5BE89BFCFF4791D51FDA5D9D --renderer-client-id=24 --mojo-platform-channel-handle=7068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AA494380577D90A2CDEFA9D0D1E41C19 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=DF1E1107E9712096F55E4D57DE4E7685 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DF1E1107E9712096F55E4D57DE4E7685 --renderer-client-id=11 --mojo-platform-channel-handle=4452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A78B10E24AC0D5001B1E1EADE2241F45 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A78B10E24AC0D5001B1E1EADE2241F45 --renderer-client-id=12 --mojo-platform-channel-handle=4736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C0D8AC2263500EB4D2FB5516F1851E1D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C0D8AC2263500EB4D2FB5516F1851E1D --renderer-client-id=10 --mojo-platform-channel-handle=4268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=588791F39D873F0CC9C3AAA90E6876F4 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=588791F39D873F0CC9C3AAA90E6876F4 --renderer-client-id=26 --mojo-platform-channel-handle=7844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=EC2502F243DE9CE628CE3686FB6B310A --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=EC2502F243DE9CE628CE3686FB6B310A --renderer-client-id=8 --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=7902E1C7612ABD71EF83087B4AAD65DB --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7902E1C7612ABD71EF83087B4AAD65DB --renderer-client-id=4 --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
529
Read events
461
Write events
65
Delete events
3
Modification events
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3000-13194980185999500 |
Value: 259 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3000-13194980185999500 |
Value: 259 | |||
Executable files
0
Suspicious files
73
Text files
167
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\92506415-6389-4975-a826-27677d824e32.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d7b34b8c-176f-41a6-a676-59d4949b2845.tmp | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF20e9a8.TMP | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF20e9a8.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
180
DNS requests
120
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
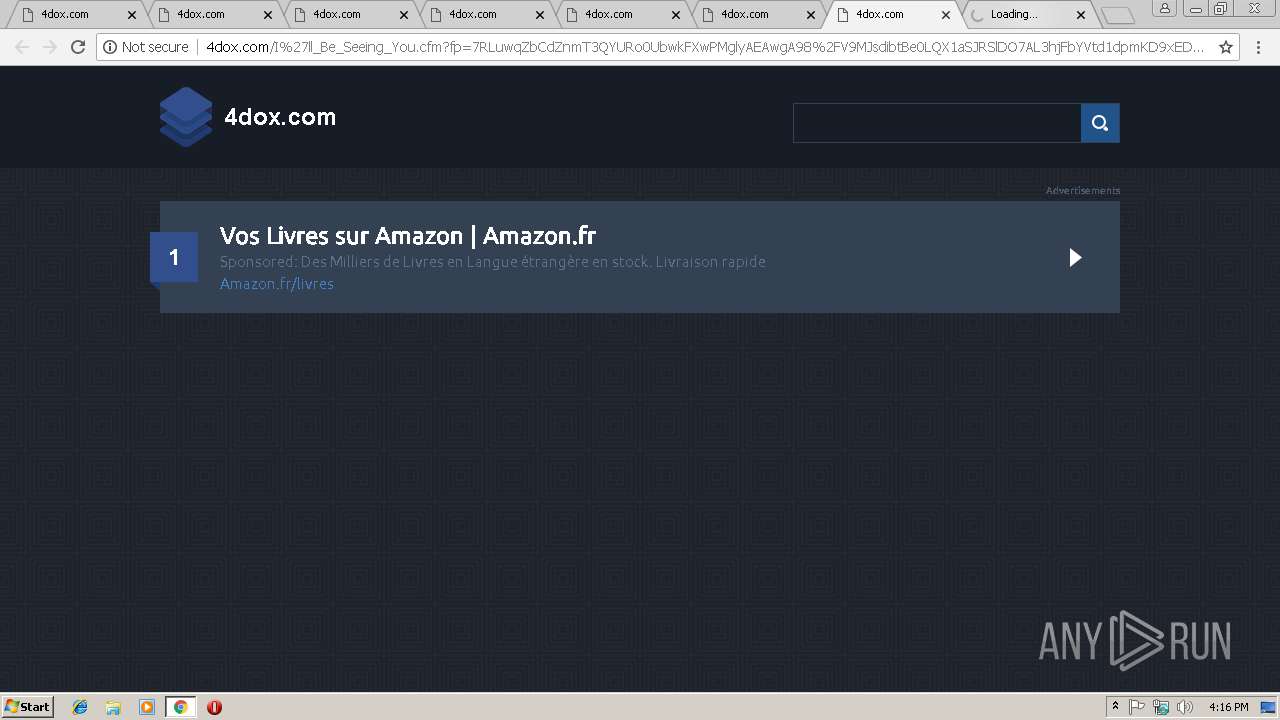
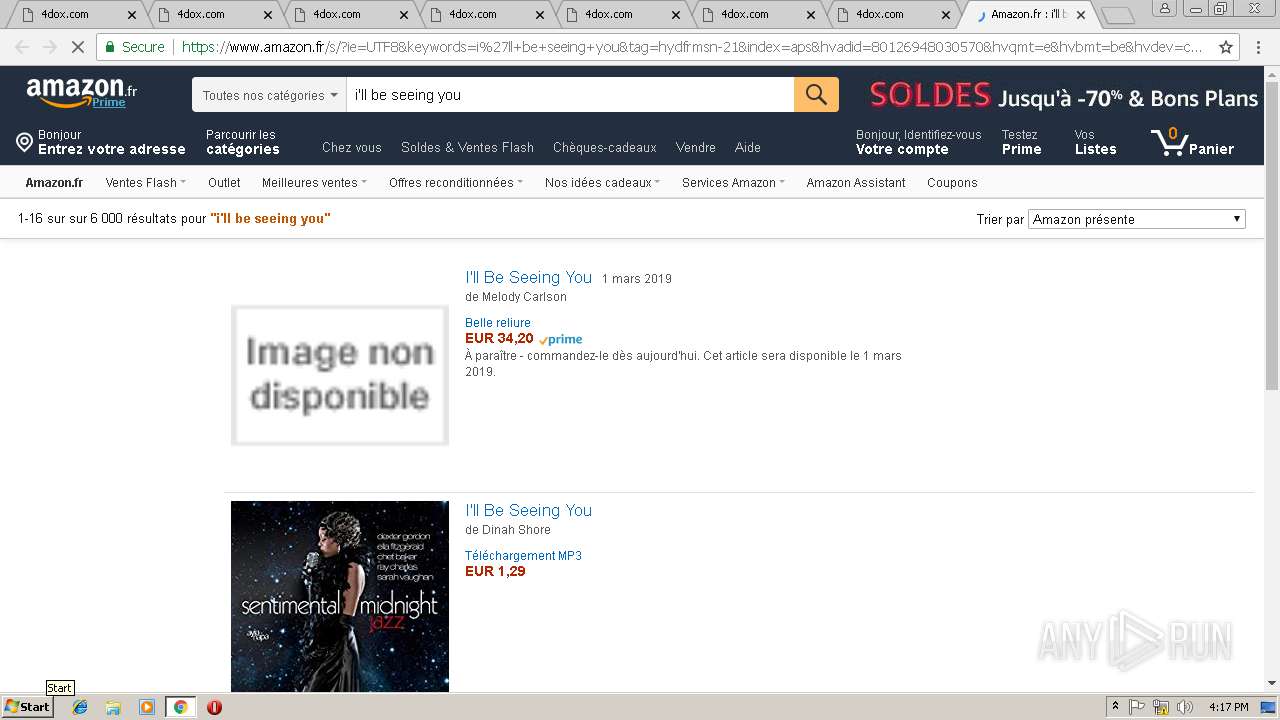
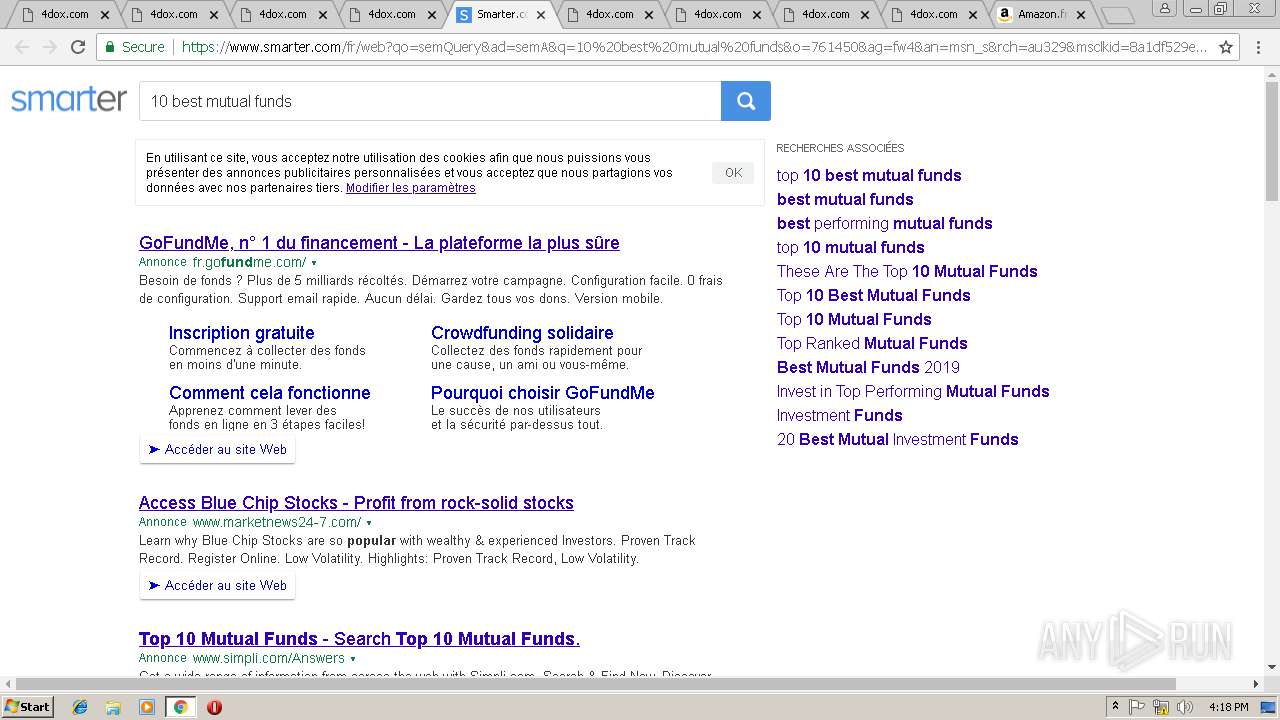
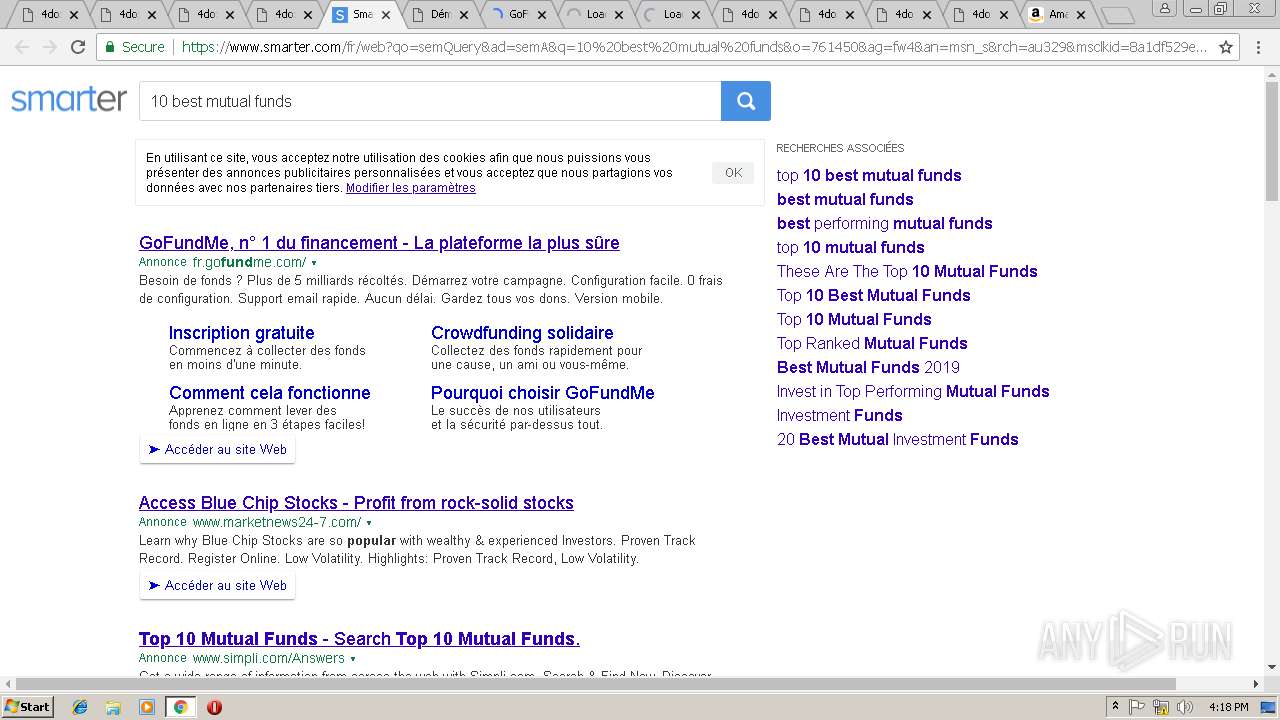
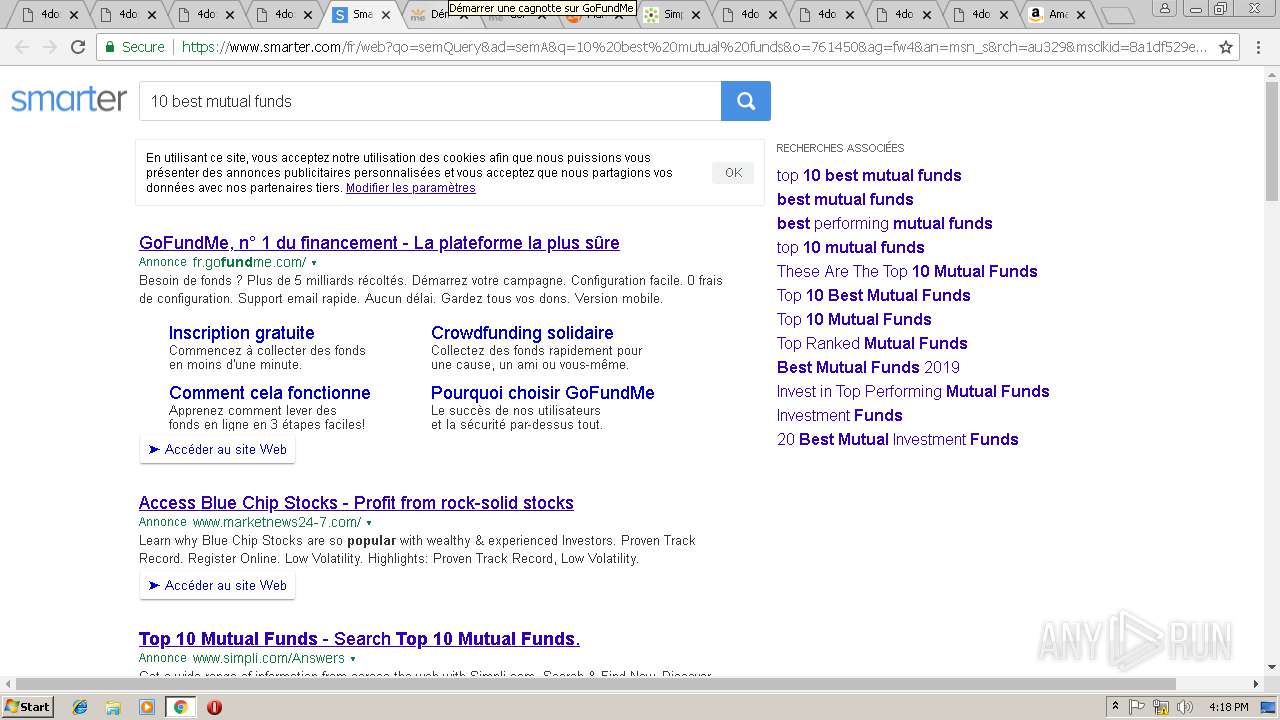
3000 | chrome.exe | GET | 200 | 208.91.197.91:80 | http://4dox.com/ | VG | html | 1.05 Kb | malicious |
3000 | chrome.exe | GET | 200 | 208.91.197.91:80 | http://4dox.com/?fp=mmnMb26GSZTS0SQm22nY%2BQXkT8KCNAsEwOeEf0eje5P61lhjJUMSHldu5KegRxztwyxHh4a1YmECkbQukIWq6IOOwJgBfd%2BCSiT8rETA%2BbUH7tfsKDoaXw1Tq0a8sfP%2B0YJcbTV56q5pBIcr%2FVjKGSi9ElN75nEs5YIdRp5eiK8%3D&prvtof=G7g%2BOW%2FeGnY9Ku39HhN5y9RIgiClkvSVdD5QOPtv%2FUU%3D&poru=ak5TwHabq4jdHpzZVWtO4WBJJNiyk23TWfCpdpppd9IM4zDjsRJgtynNhMiJ6IDD& | VG | html | 6.21 Kb | malicious |
3000 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i2.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
3000 | chrome.exe | GET | 200 | 208.91.197.91:80 | http://4dox.com/I_Tee_Shirt.cfm?fp=7RLuwqZbCdZnmT3QYURo0UbwkFXwPMglyAEAwgA98%2FV9MJsdibtBe0LQX1aSJRSlDO7AL3hjFbYVtd1dpmKD9xED8TpBWgdeKDHI0J9buJxbEj%2BV1iimIdydhRAHgr5Zq4IEaWTeWdviG07oKsHLOj%2ByDTgoKOhVaWz6megqVYWYhwlhww3hFyqg2M6ZP2Vpj9CAjdv5GtiaLwDaih5viw%3D%3D&yep=OQJ%2FZqSWECHD9PmzThfI2qtYhG5u6eyjy3iwfzg4wm4wIMBr5%2BfWTBzzMTdPNP8L6gATgf3hJks3vq3JWrNHnhTKGfrK8ucCffTkZGo4P3BNlkzsp6%2F5zq2i4P%2FJ5%2FpJhKJfehZKvb4Is6OcF44kPVl3HldOIai1uzS1K62JNuy4HYhRW88q3xdexa6LJIfWY2fN4I%2Bd%2FCPObDpCGgGRiR%2BSMErOqHOr%2B3enRdZ%2FvfGUuCc1KLh2EIdWOUU08pGZUQUDkhkYMgX3Pg46G9fQMvpP%2FQpfn69JwuhZjdj7CJZ7HGF0CiZV8RfgBfoYvdF666CemYP2kzdTClGrvFDCZpVuiynF3s8cCzohzoUCfrYwf3SfTt2K5XRfDFsr2uQjGnstlSKqd7sAapSkW4YjS3RQgA5oU6TBFKi7Es59PP4aaZHDC73uo%2BOi9VmAnH322D9Lbcqgdfm377os%2B9trDXO5ZakzwJTF11c2EggPT68o2eNQRFvhoDbTeSxzpJbUiY2PAUSxvwyB8G2wAHTzzHWkV5recLqZAoPyu9MXtltNmtv5rix2CTXL6RRJnBJ5YZgJpbgVISv6EbvIXNFwfw%3D%3D>np=0>pp=0&maxads=0&kld=1042&yprpnd=Se8VbQEDfj5cIjWEuZtG6GpbOj5MBU9dD2SNmtR%2B%2Bew%3D&prvtof=G7g%2BOW%2FeGnY9Ku39HhN5y9RIgiClkvSVdD5QOPtv%2FUU%3D&>np=0>pp=0&kt=362&&kbc=doi&ki=209384882&ktd=0&kld=1042&kp=7&bd=0%23720%231280%231%230 | VG | html | 12.0 Kb | malicious |
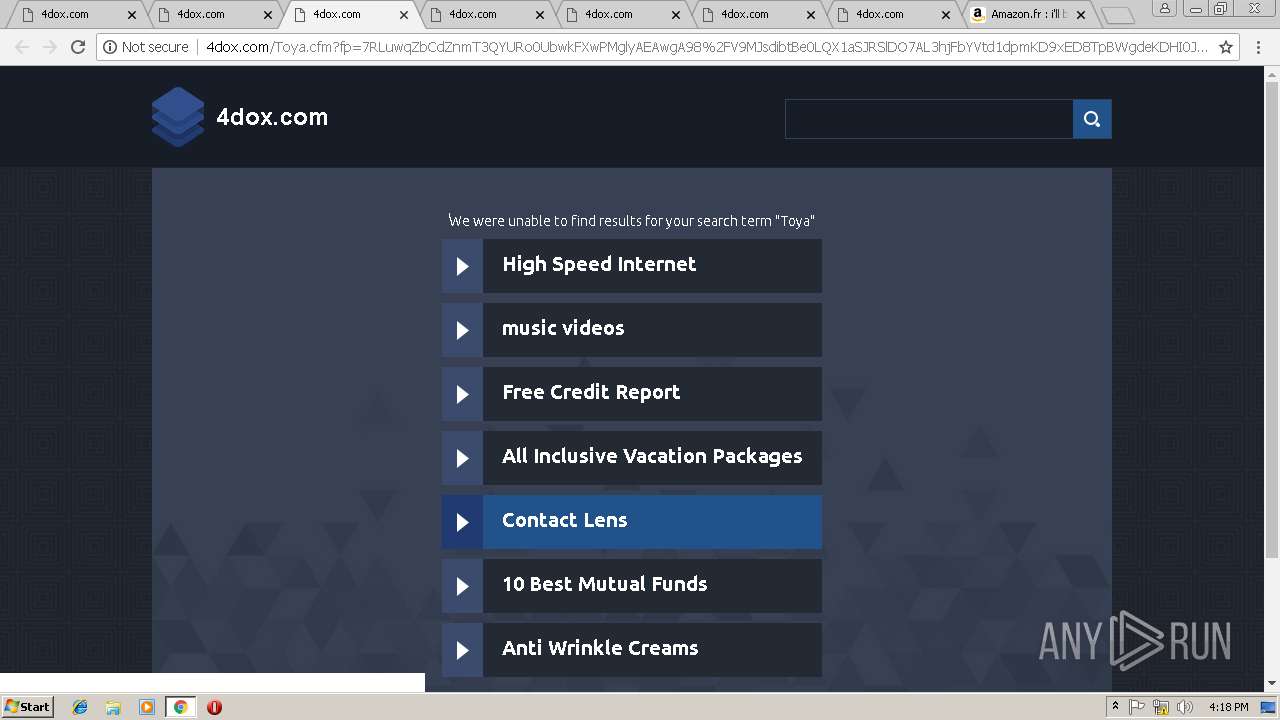
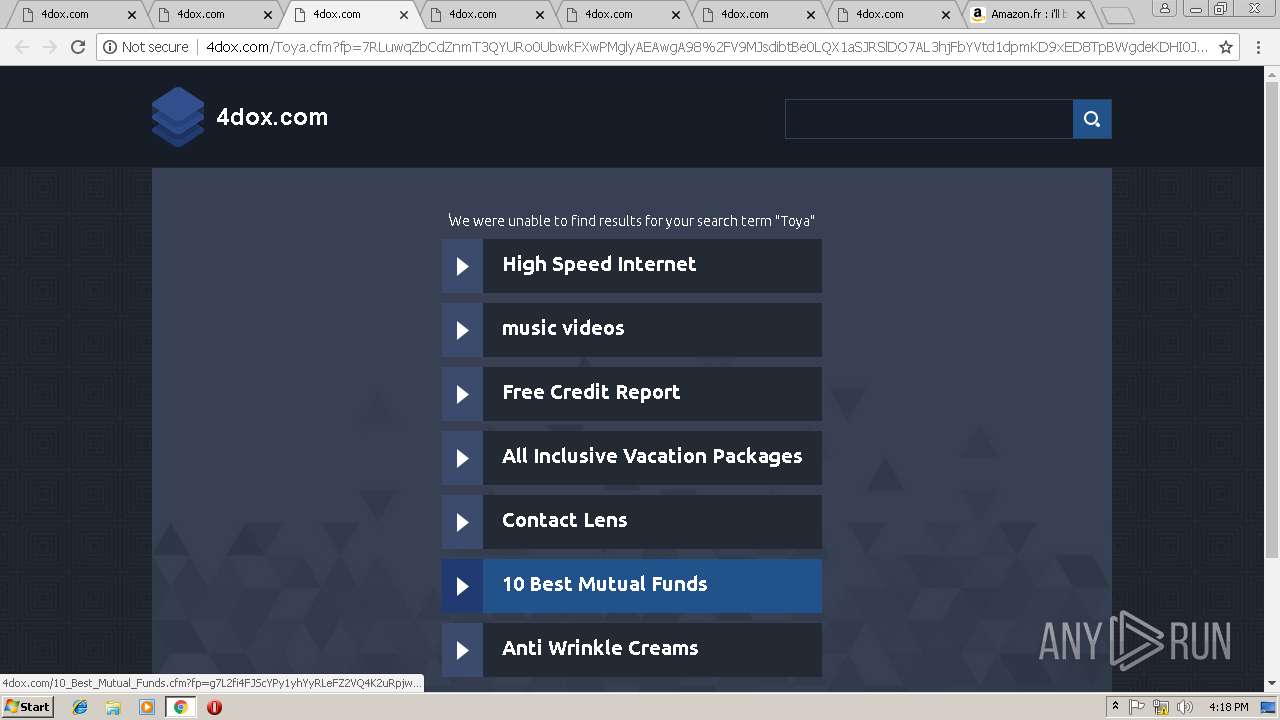
3000 | chrome.exe | GET | 200 | 208.91.197.91:80 | http://4dox.com/Toya.cfm?fp=7RLuwqZbCdZnmT3QYURo0UbwkFXwPMglyAEAwgA98%2FV9MJsdibtBe0LQX1aSJRSlDO7AL3hjFbYVtd1dpmKD9xED8TpBWgdeKDHI0J9buJxbEj%2BV1iimIdydhRAHgr5Zq4IEaWTeWdviG07oKsHLOj%2ByDTgoKOhVaWz6megqVYWYhwlhww3hFyqg2M6ZP2Vpj9CAjdv5GtiaLwDaih5viw%3D%3D&yep=OQJ%2FZqSWECHD9PmzThfI2qtYhG5u6eyjy3iwfzg4wm4wIMBr5%2BfWTBzzMTdPNP8L6gATgf3hJks3vq3JWrNHnhTKGfrK8ucCffTkZGo4P3BNlkzsp6%2F5zq2i4P%2FJ5%2FpJhKJfehZKvb4Is6OcF44kPVl3HldOIai1uzS1K62JNuy4HYhRW88q3xdexa6LJIfWY2fN4I%2Bd%2FCPObDpCGgGRiR%2BSMErOqHOr%2B3enRdZ%2FvfGUuCc1KLh2EIdWOUU08pGZUQUDkhkYMgX3Pg46G9fQMvpP%2FQpfn69JwuhZjdj7CJZ7HGF0CiZV8RfgBfoYvdF666CemYP2kzdTClGrvFDCZpVuiynF3s8cCzohzoUCfrYwf3SfTt2K5XRfDFsr2uQjGnstlSKqd7sAapSkW4YjS3RQgA5oU6TBFKi7Es59PP4aaZHDC73uo%2BOi9VmAnH322D9Lbcqgdfm377os%2B9trDXO5ZakzwJTF11c2EggPT68o2eNQRFvhoDbTeSxzpJbUiY2PAUSxvwyB8G2wAHTzzHWkV5recLqZAoPyu9MXtltNmtv5rix2CTXL6RRJnBJ5YZgJpbgVISv6EbvIXNFwfw%3D%3D>np=0>pp=0&maxads=0&kld=1042&yprpnd=Se8VbQEDfj5cIjWEuZtG6GpbOj5MBU9dD2SNmtR%2B%2Bew%3D&prvtof=G7g%2BOW%2FeGnY9Ku39HhN5y9RIgiClkvSVdD5QOPtv%2FUU%3D&>np=0>pp=0&kt=362&&kbc=doi&ki=28758601&ktd=0&kld=1042&kp=4&bd=0%23720%231280%231%230 | VG | html | 6.23 Kb | malicious |
3000 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i3.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
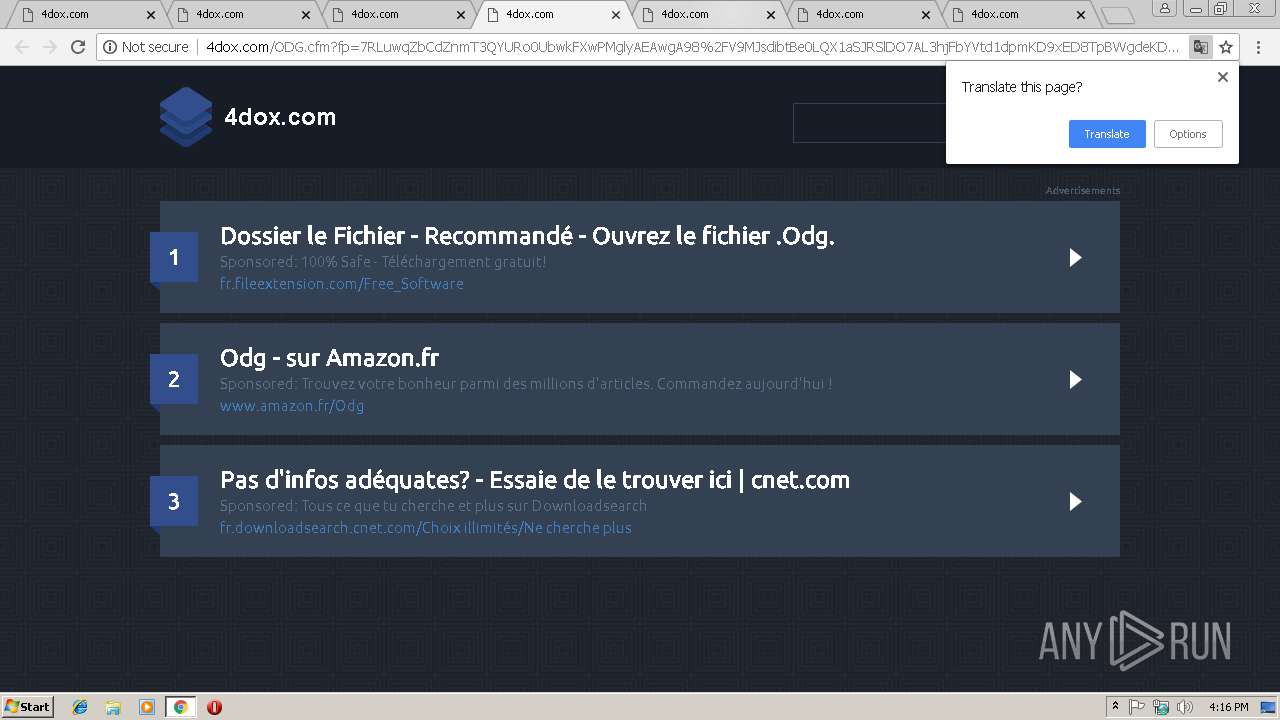
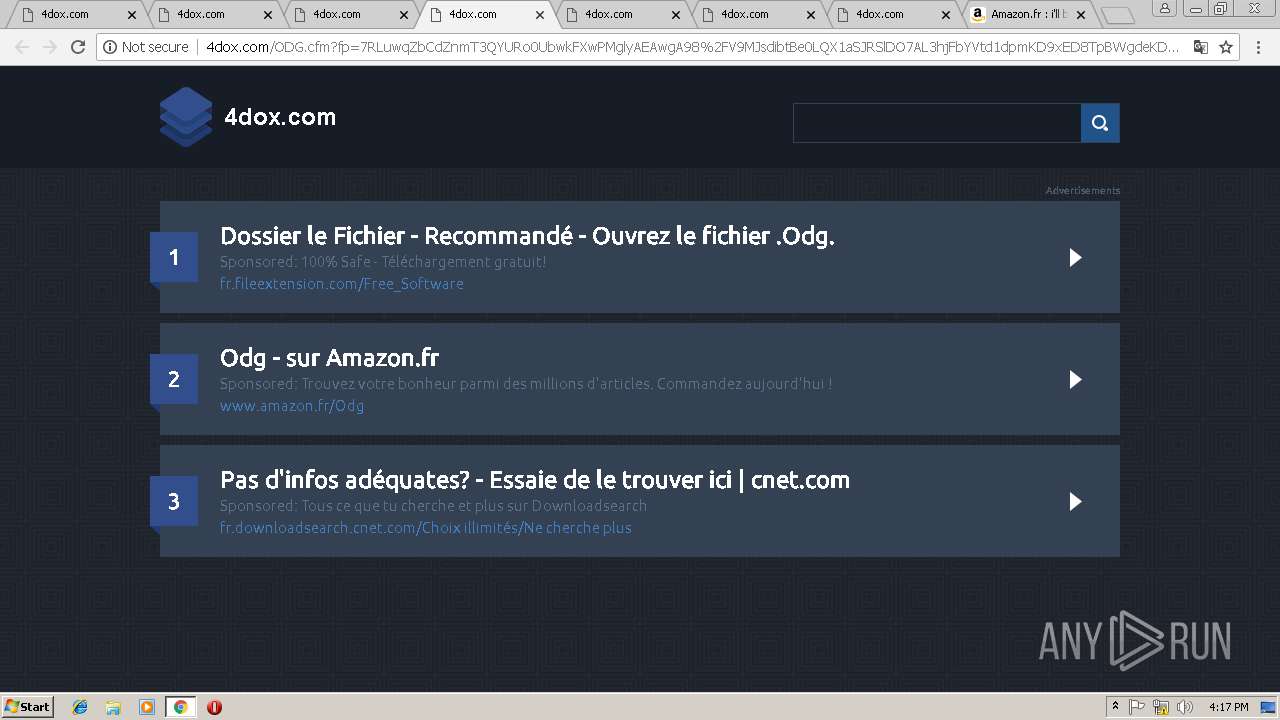
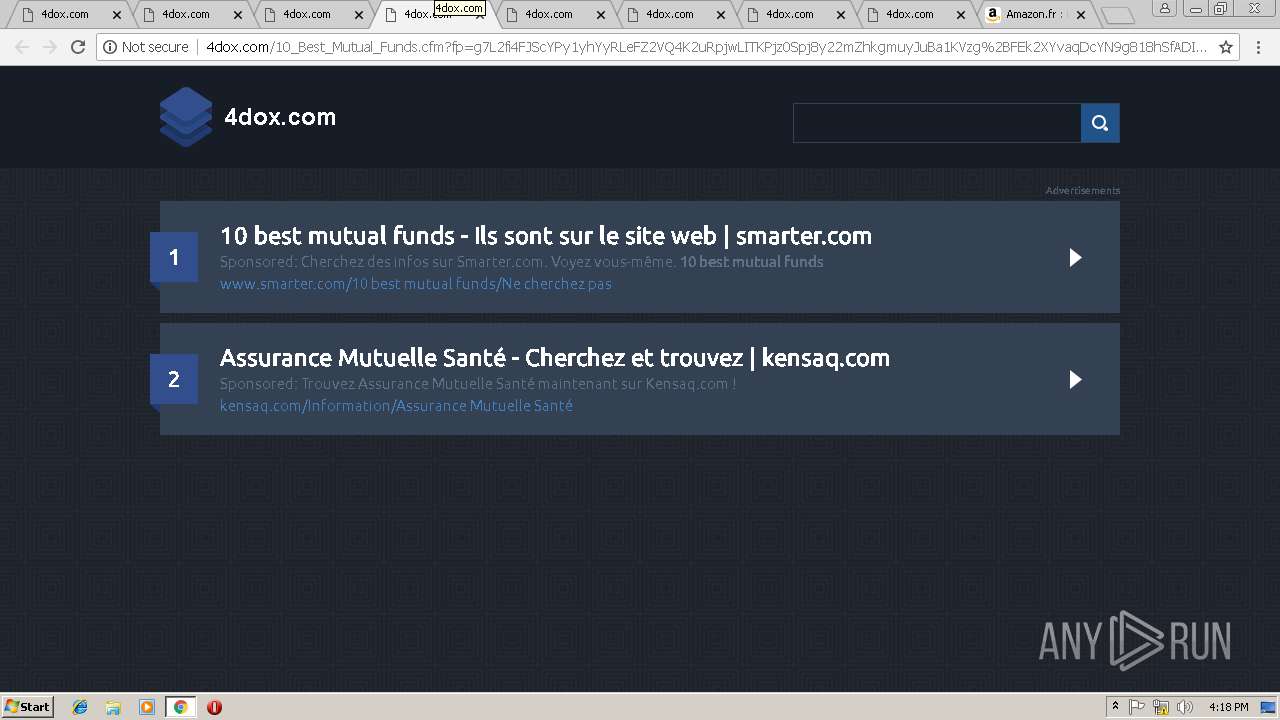
3000 | chrome.exe | GET | 200 | 208.91.197.91:80 | http://4dox.com/ODG.cfm?fp=7RLuwqZbCdZnmT3QYURo0UbwkFXwPMglyAEAwgA98%2FV9MJsdibtBe0LQX1aSJRSlDO7AL3hjFbYVtd1dpmKD9xED8TpBWgdeKDHI0J9buJxbEj%2BV1iimIdydhRAHgr5Zq4IEaWTeWdviG07oKsHLOj%2ByDTgoKOhVaWz6megqVYWYhwlhww3hFyqg2M6ZP2Vpj9CAjdv5GtiaLwDaih5viw%3D%3D&yep=OQJ%2FZqSWECHD9PmzThfI2qtYhG5u6eyjy3iwfzg4wm4wIMBr5%2BfWTBzzMTdPNP8L6gATgf3hJks3vq3JWrNHnhTKGfrK8ucCffTkZGo4P3BNlkzsp6%2F5zq2i4P%2FJ5%2FpJhKJfehZKvb4Is6OcF44kPVl3HldOIai1uzS1K62JNuy4HYhRW88q3xdexa6LJIfWY2fN4I%2Bd%2FCPObDpCGgGRiR%2BSMErOqHOr%2B3enRdZ%2FvfGUuCc1KLh2EIdWOUU08pGZUQUDkhkYMgX3Pg46G9fQMvpP%2FQpfn69JwuhZjdj7CJZ7HGF0CiZV8RfgBfoYvdF666CemYP2kzdTClGrvFDCZpVuiynF3s8cCzohzoUCfrYwf3SfTt2K5XRfDFsr2uQjGnstlSKqd7sAapSkW4YjS3RQgA5oU6TBFKi7Es59PP4aaZHDC73uo%2BOi9VmAnH322D9Lbcqgdfm377os%2B9trDXO5ZakzwJTF11c2EggPT68o2eNQRFvhoDbTeSxzpJbUiY2PAUSxvwyB8G2wAHTzzHWkV5recLqZAoPyu9MXtltNmtv5rix2CTXL6RRJnBJ5YZgJpbgVISv6EbvIXNFwfw%3D%3D>np=0>pp=0&maxads=0&kld=1042&yprpnd=Se8VbQEDfj5cIjWEuZtG6GpbOj5MBU9dD2SNmtR%2B%2Bew%3D&prvtof=G7g%2BOW%2FeGnY9Ku39HhN5y9RIgiClkvSVdD5QOPtv%2FUU%3D&>np=0>pp=0&kt=362&&kbc=doi&ki=20995376&ktd=0&kld=1042&kp=5&bd=0%23720%231280%231%230 | VG | html | 9.38 Kb | malicious |
3000 | chrome.exe | GET | 200 | 208.91.197.91:80 | http://4dox.com/px.js?ch=1 | VG | text | 346 b | malicious |
3000 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i1.cdn-image.com/__media__/pics/12471/kwbg.jpg | unknown | image | 36.3 Kb | whitelisted |
3000 | chrome.exe | GET | 200 | 208.91.197.91:80 | http://4dox.com/sk-logabpstatus.php?a=anBBYVJhV3NCSmlKc2FIVVlxMmVVZjlCVjRDRUM4MWZ6bEx3Vi9POUpGd1lhRmJhdUtqNnJHSHRCR1BNM0hiSEtYN0d3OVBrYkt0dy9TSitHOTlwRTdSK3RnbVkwRGp1WFBuV3RSL0VrQzA9&b=false | VG | text | 346 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | chrome.exe | 52.85.188.197:80 | x.ss2.us | Amazon.com, Inc. | US | suspicious |
3000 | chrome.exe | 52.94.220.16:443 | aax-eu.amazon-adsystem.com | Amazon.com, Inc. | IE | unknown |
3000 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 208.91.197.91:80 | 4dox.com | Confluence Networks Inc | VG | malicious |
3000 | chrome.exe | 2.16.186.106:80 | i2.cdn-image.com | Akamai International B.V. | — | whitelisted |
3000 | chrome.exe | 2.16.186.64:80 | i2.cdn-image.com | Akamai International B.V. | — | whitelisted |
3000 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 216.58.207.74:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
4dox.com |
| malicious |
accounts.google.com |
| shared |
i2.cdn-image.com |
| whitelisted |
i1.cdn-image.com |
| whitelisted |
i3.cdn-image.com |
| whitelisted |
i4.cdn-image.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |