| File name: | f473474711885867b6c6b98c2076f99dd284afffe90b2db861d35c47669e1170 |
| Full analysis: | https://app.any.run/tasks/a8d3fe49-bd5d-4724-ba0d-d51172f2a76e |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2018, 14:11:16 |
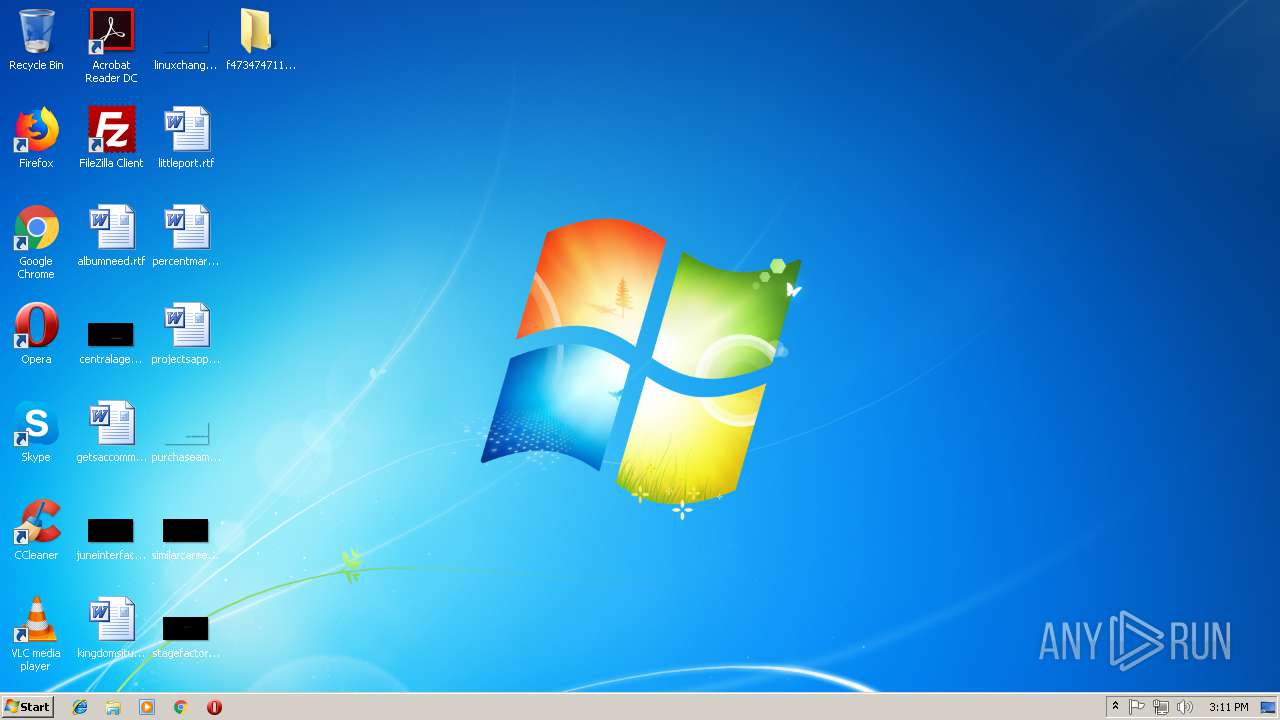
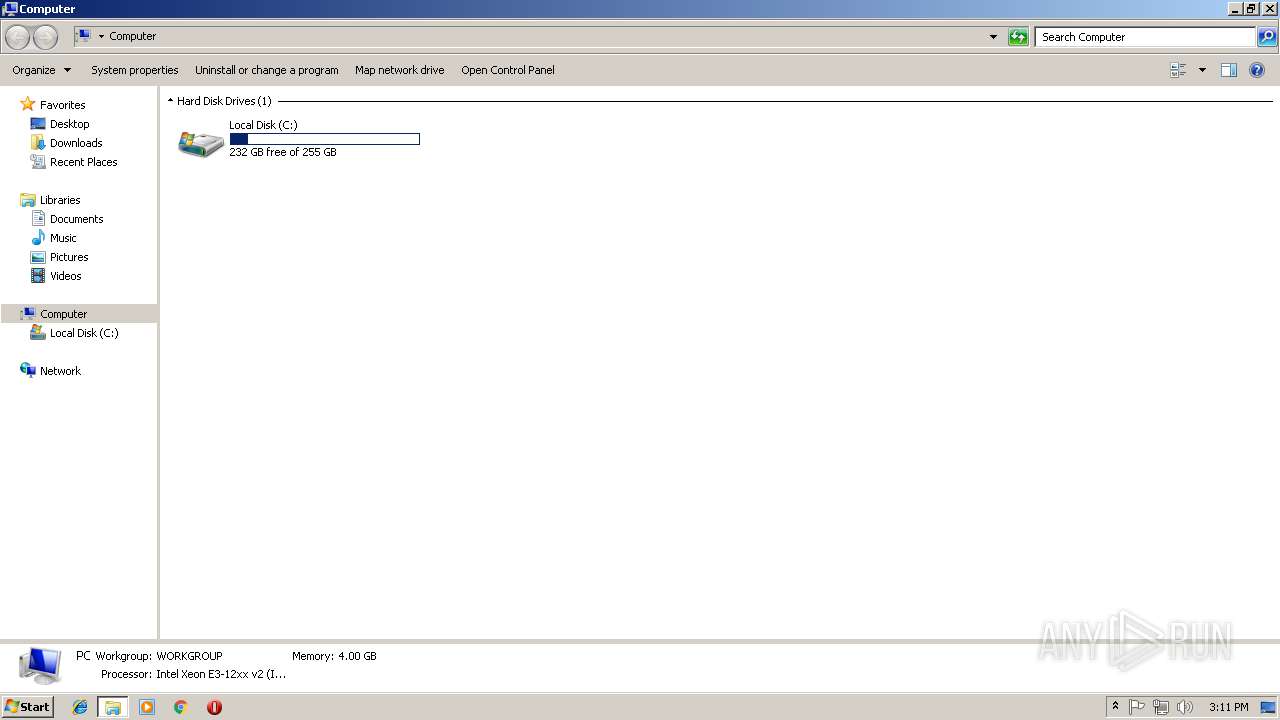
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | A7631A73CEC7A1D6EFF78D57CB933643 |
| SHA1: | 403CF8983383D720683FA36E7609AF45A450E244 |
| SHA256: | F473474711885867B6C6B98C2076F99DD284AFFFE90B2DB861D35C47669E1170 |
| SSDEEP: | 12288:P1/aGLDCMNpNAkoSzZWD8ayX2MQCw7D0FoWxJpcEi0/3IWV//7cSdb94VIfYvEDs:P1/aGLDCM4D8ayGMZo8/aV4iZ |
MALICIOUS
Changes the autorun value in the registry
- kerynu.exe (PID: 2052)
- kerynu.exe (PID: 2020)
Application was dropped or rewritten from another process
- kerynu.exe (PID: 2052)
- kerynu.exe (PID: 2020)
SUSPICIOUS
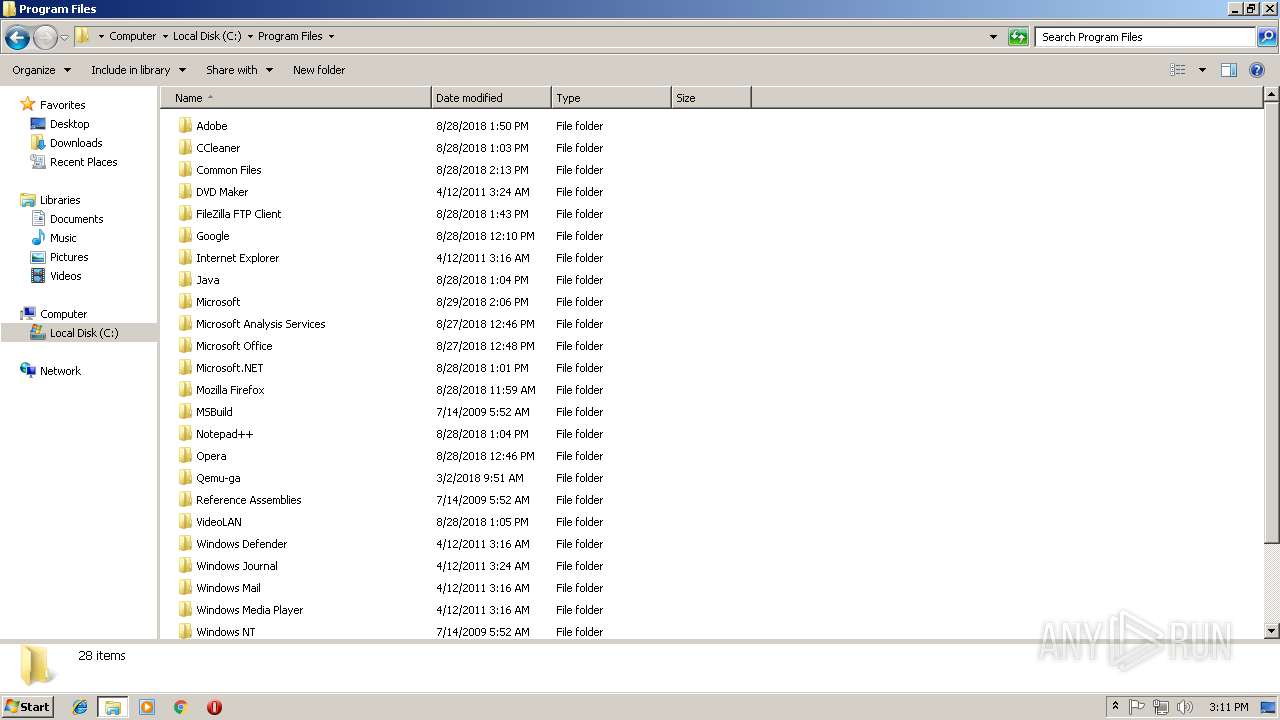
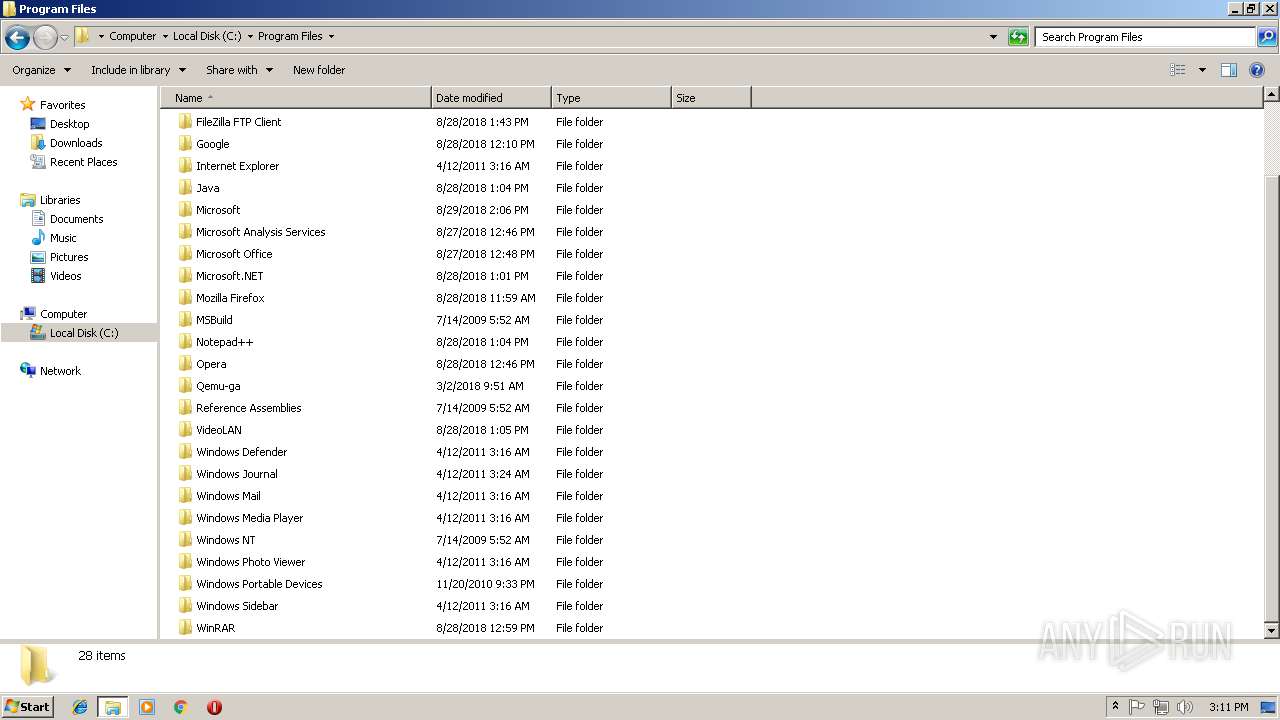
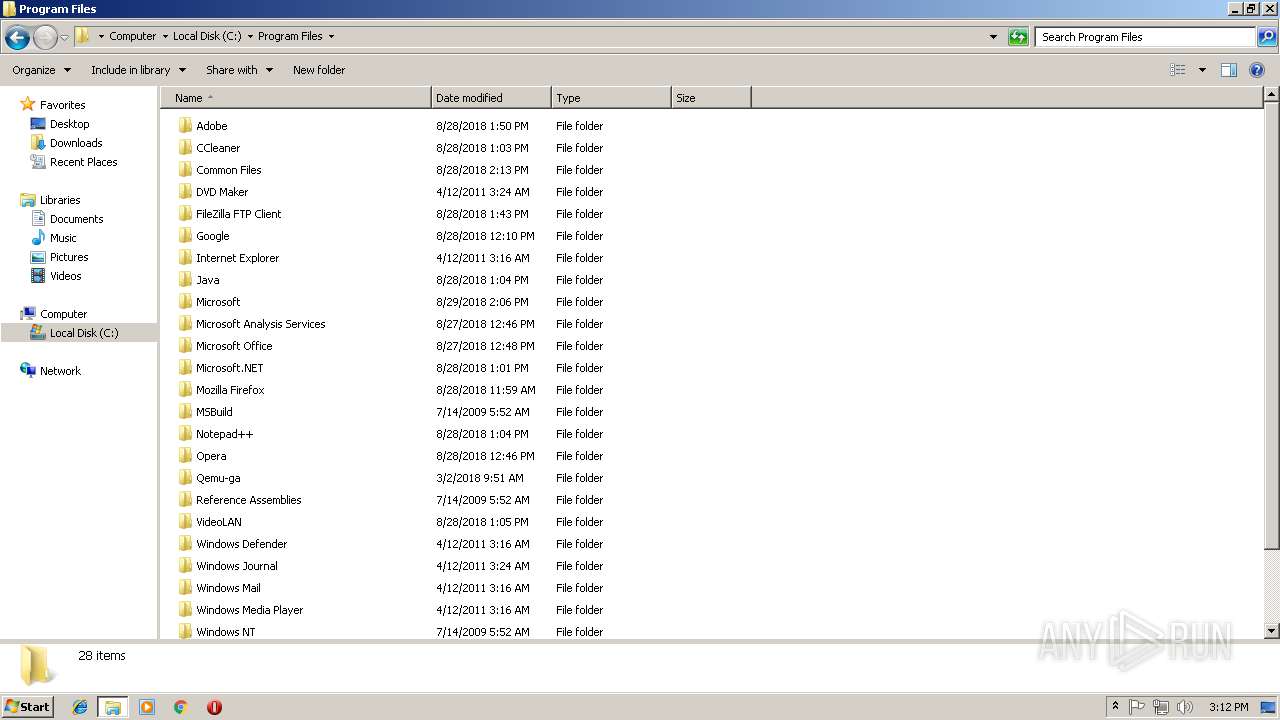
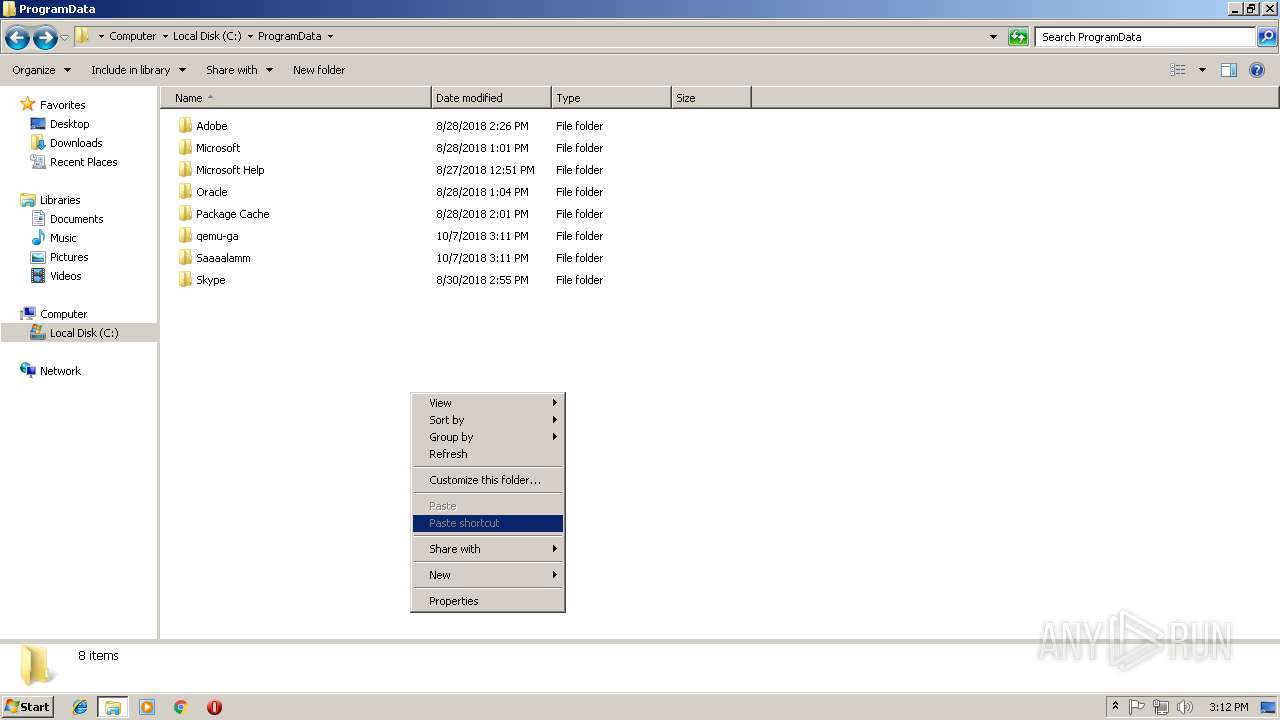
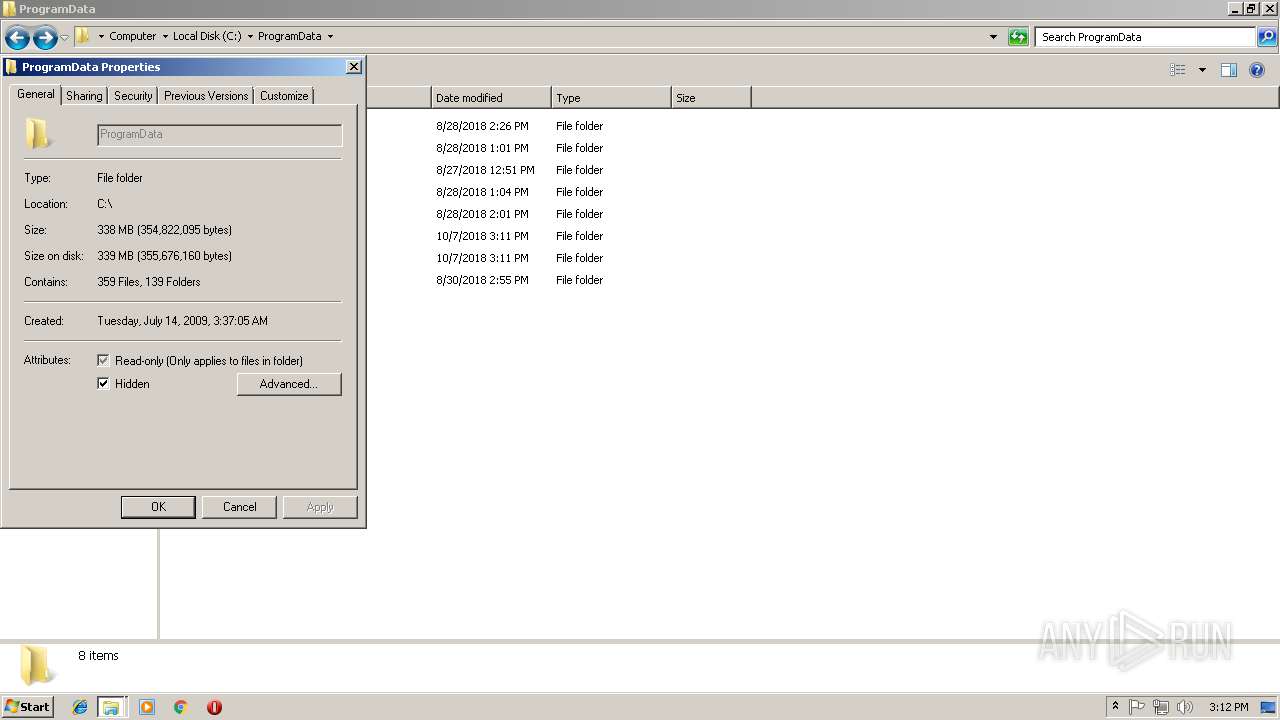
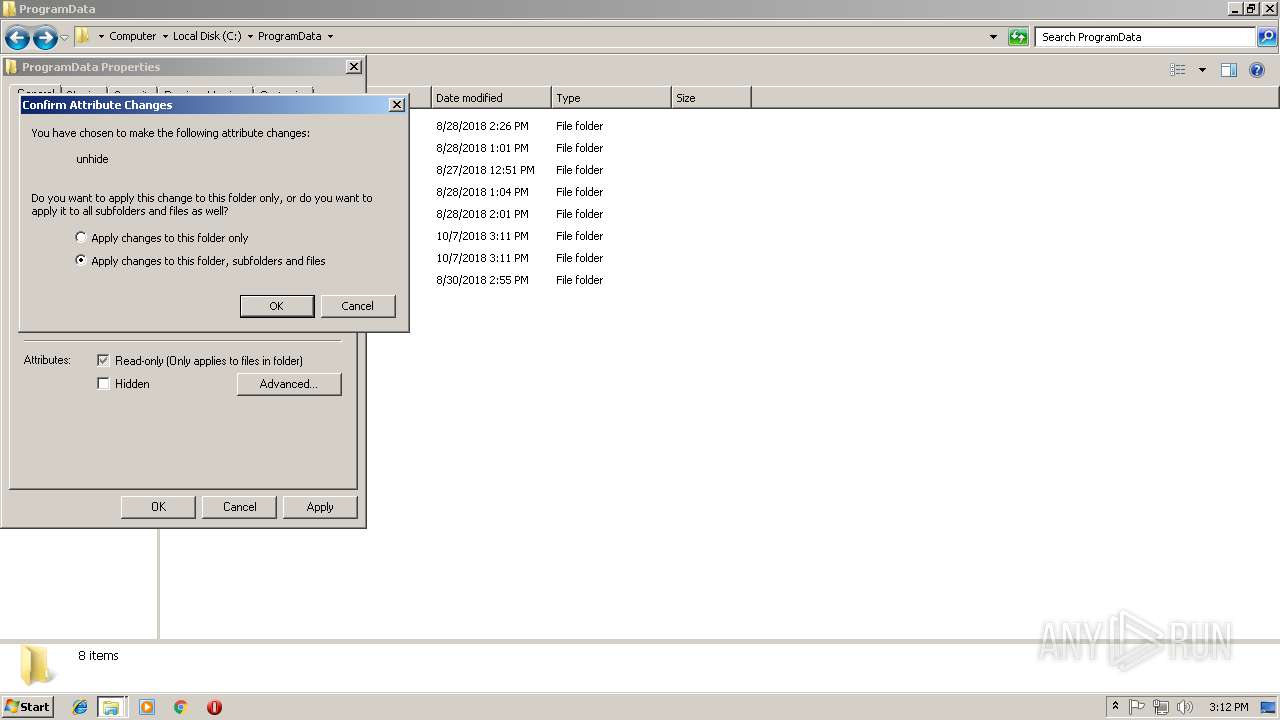
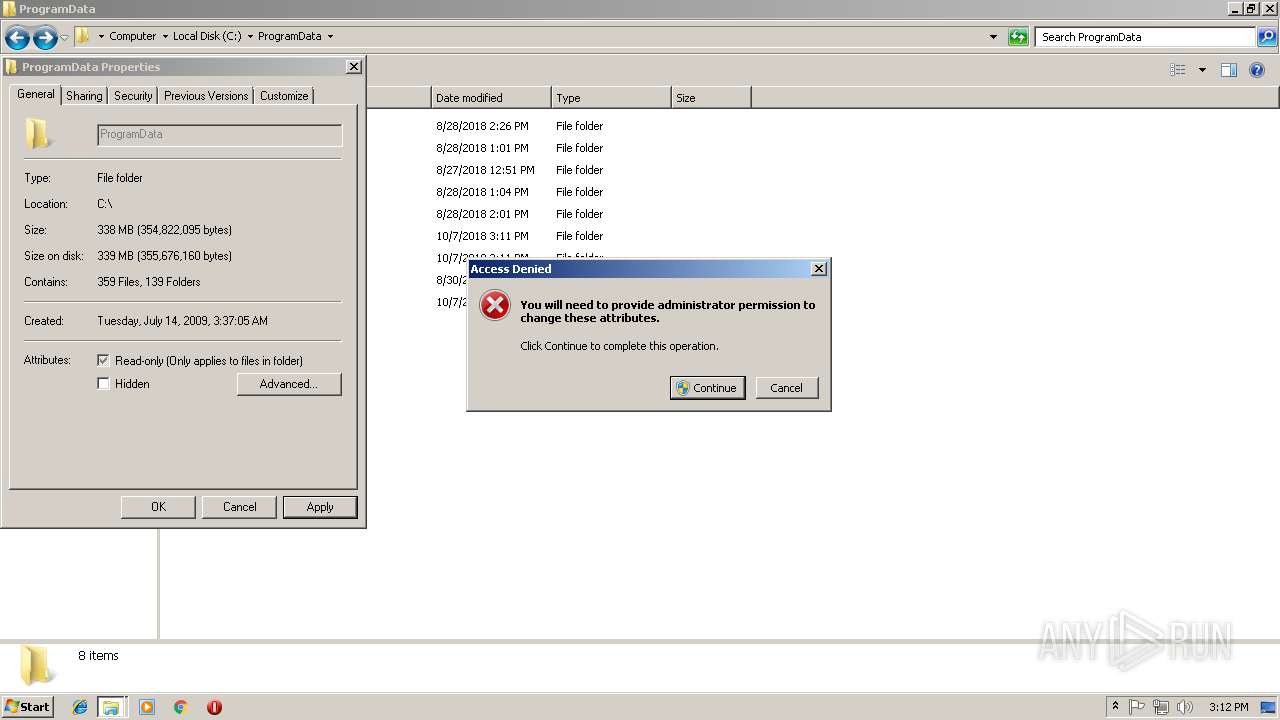
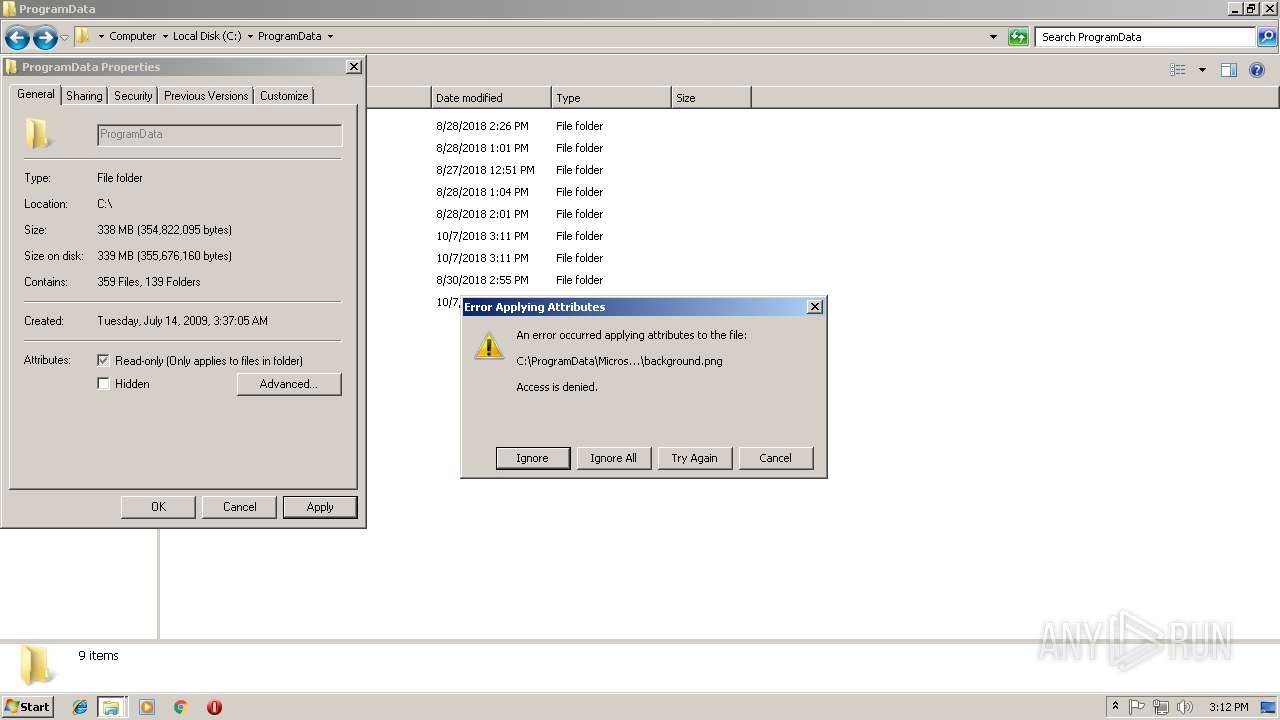
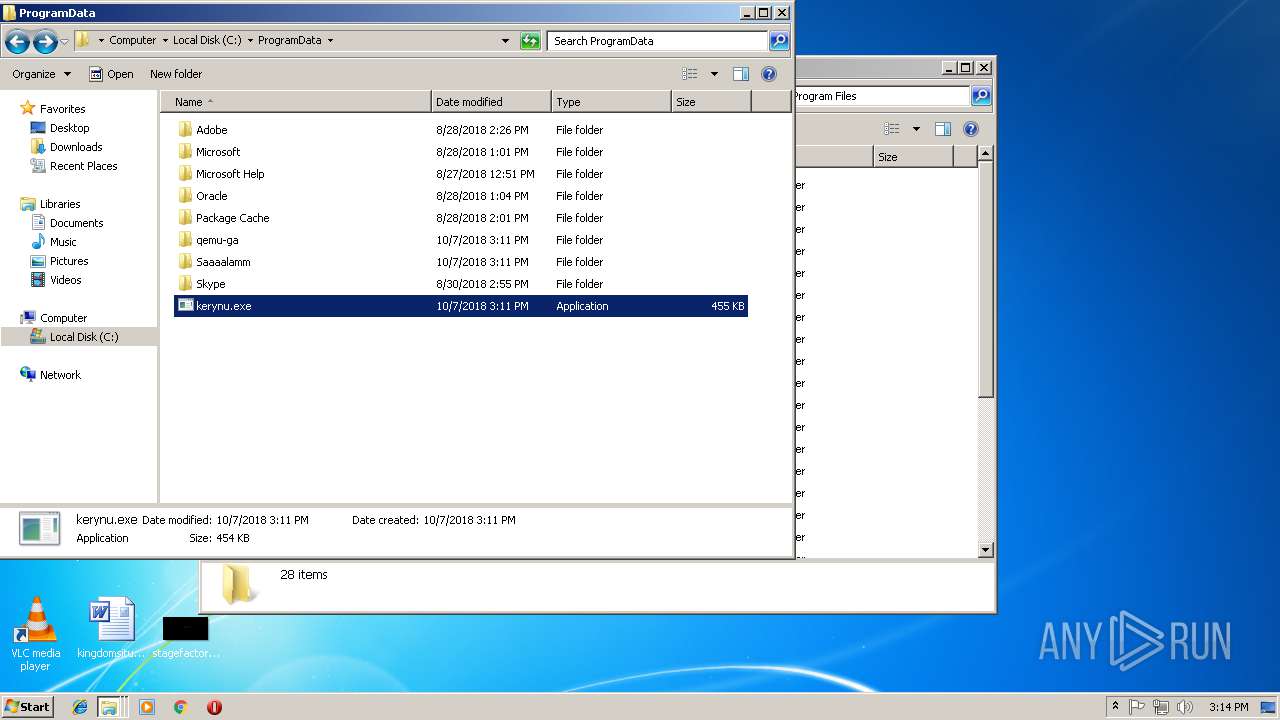
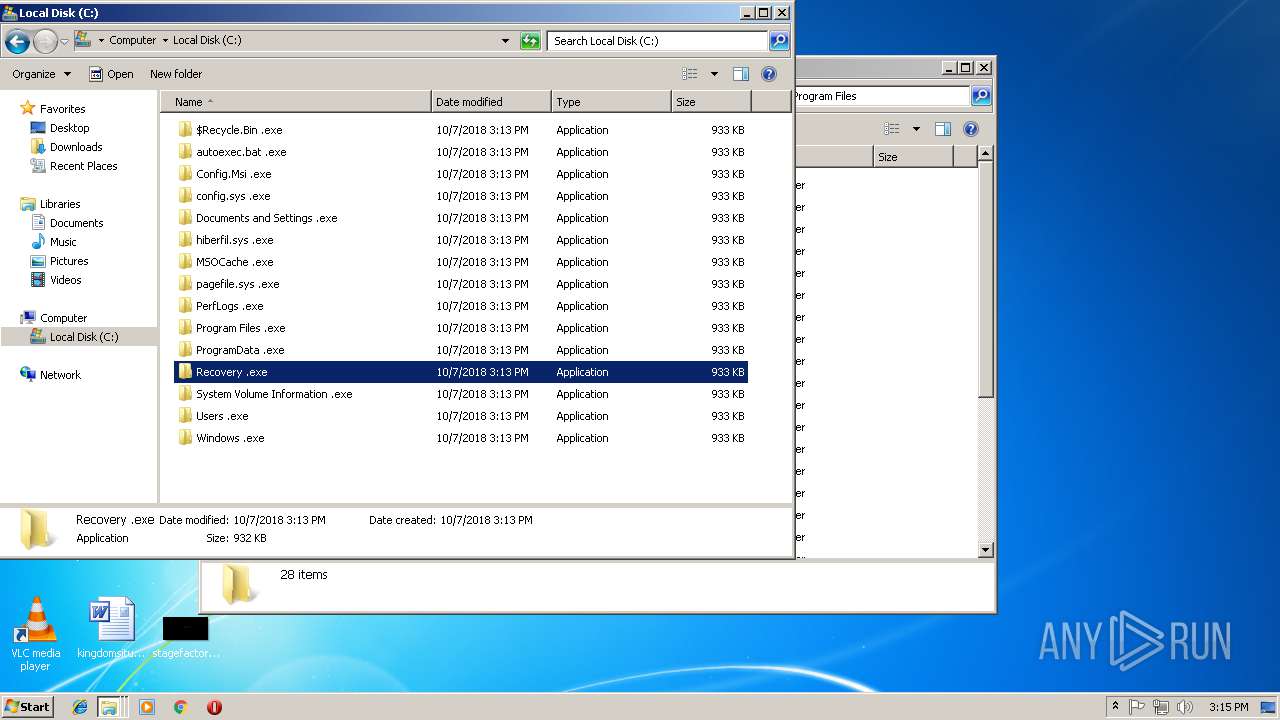
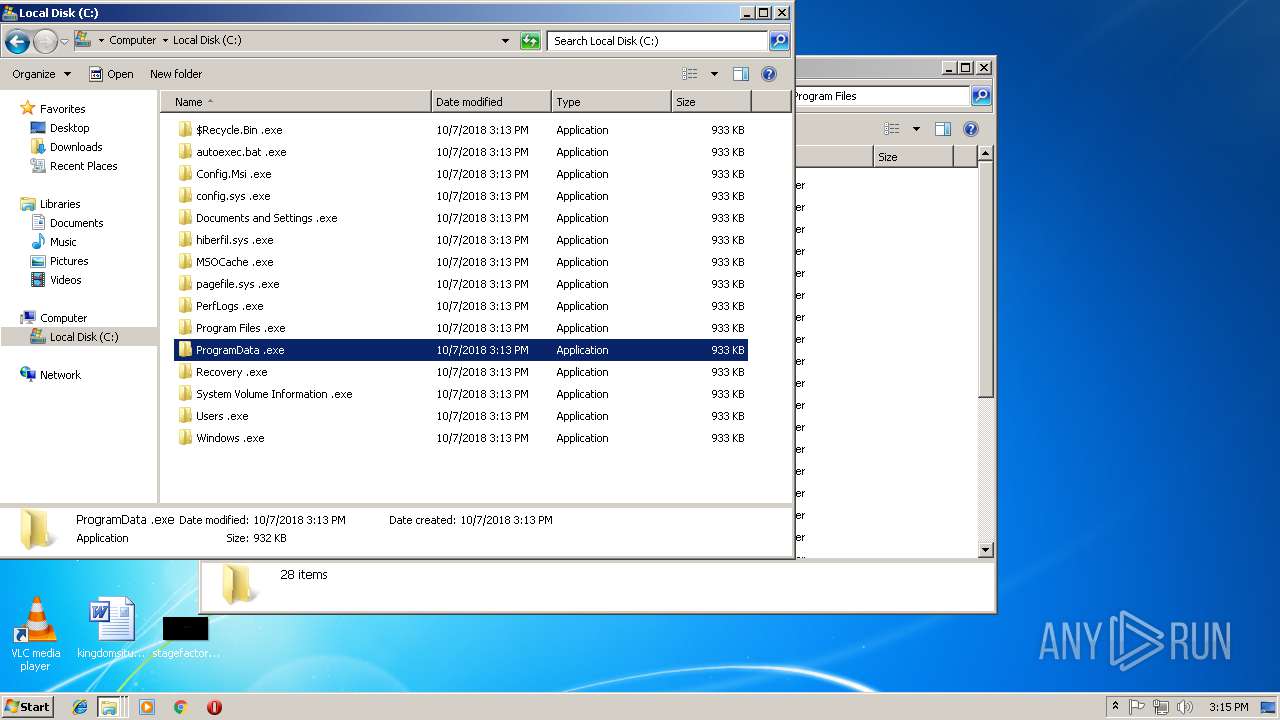
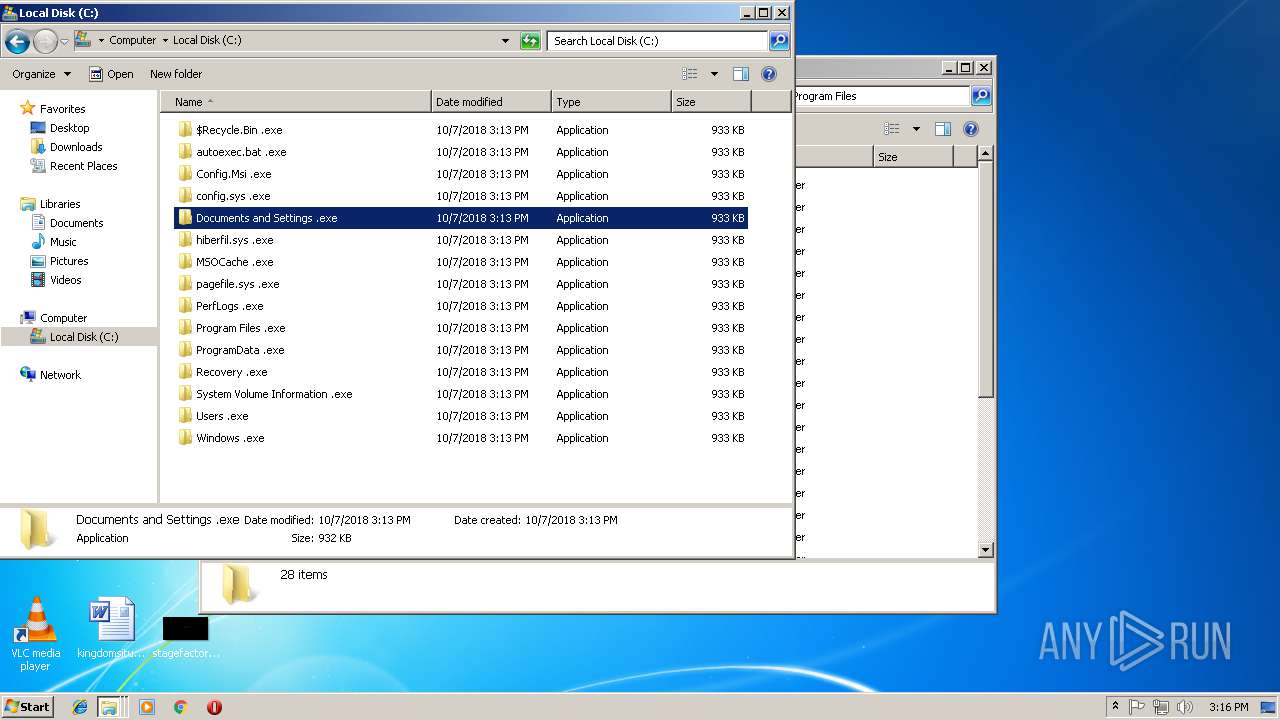
Creates files in the program directory
- f473474711885867b6c6b98c2076f99dd284afffe90b2db861d35c47669e1170.exe (PID: 3272)
- kerynu.exe (PID: 2020)
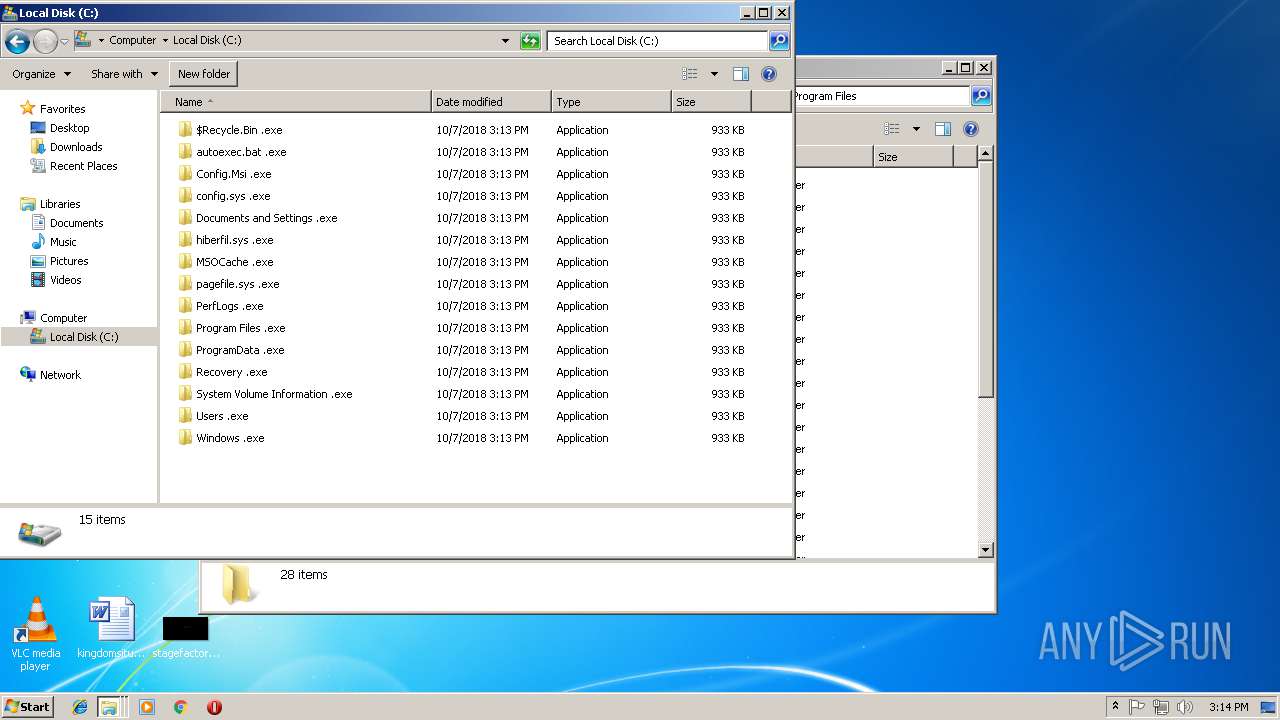
Executable content was dropped or overwritten
- f473474711885867b6c6b98c2076f99dd284afffe90b2db861d35c47669e1170.exe (PID: 3272)
- kerynu.exe (PID: 2020)
Creates files in the Windows directory
- kerynu.exe (PID: 2020)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | MinGW32 C/C++ Executable (76.3) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (9.7) |
| .exe | | | Win64 Executable (generic) (8.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (2) |
| .exe | | | Win32 Executable (generic) (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:02:27 07:41:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 245760 |
| InitializedDataSize: | 285696 |
| UninitializedDataSize: | 18944 |
| EntryPoint: | 0x1240 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.158 |
| ProductVersionNumber: | 1.0.0.158 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileVersion: | 1.0.0.155 |
| FileDescription: | Mira Malware |
| InternalName: | - |
| LegalCopyright: | Microsoft Corporation |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | Mira Malware |
| ProductVersion: | 1.0.0.155 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Feb-2014 06:41:59 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileVersion: | 1.0.0.155 |
| FileDescription: | Mira Malware |
| InternalName: | - |
| LegalCopyright: | Microsoft Corporation |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | Mira Malware |
| ProductVersion: | 1.0.0.155 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 27-Feb-2014 06:41:59 |
| Pointer to Symbol Table: | 0x00046000 |
| Number of symbols: | 5073 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003BE78 | 0x0003C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.08045 |
.data | 0x0003D000 | 0x00000260 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.705049 |
.rdata | 0x0003E000 | 0x000024A8 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00853 |
.bss | 0x00041000 | 0x00004890 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00046000 | 0x000008A4 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.29494 |
.rsrc | 0x00047000 | 0x000067B8 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.7327 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.23637 | 736 | UNKNOWN | English - United States | RT_VERSION |
2 | 2.87102 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 2.92944 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 4.88878 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 5.66607 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 3.91485 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 4.25726 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 4.82814 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 5.30461 | 1128 | UNKNOWN | English - United States | RT_ICON |
A | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
SHELL32.DLL |
msvcrt.dll |
Total processes
61
Monitored processes
12
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
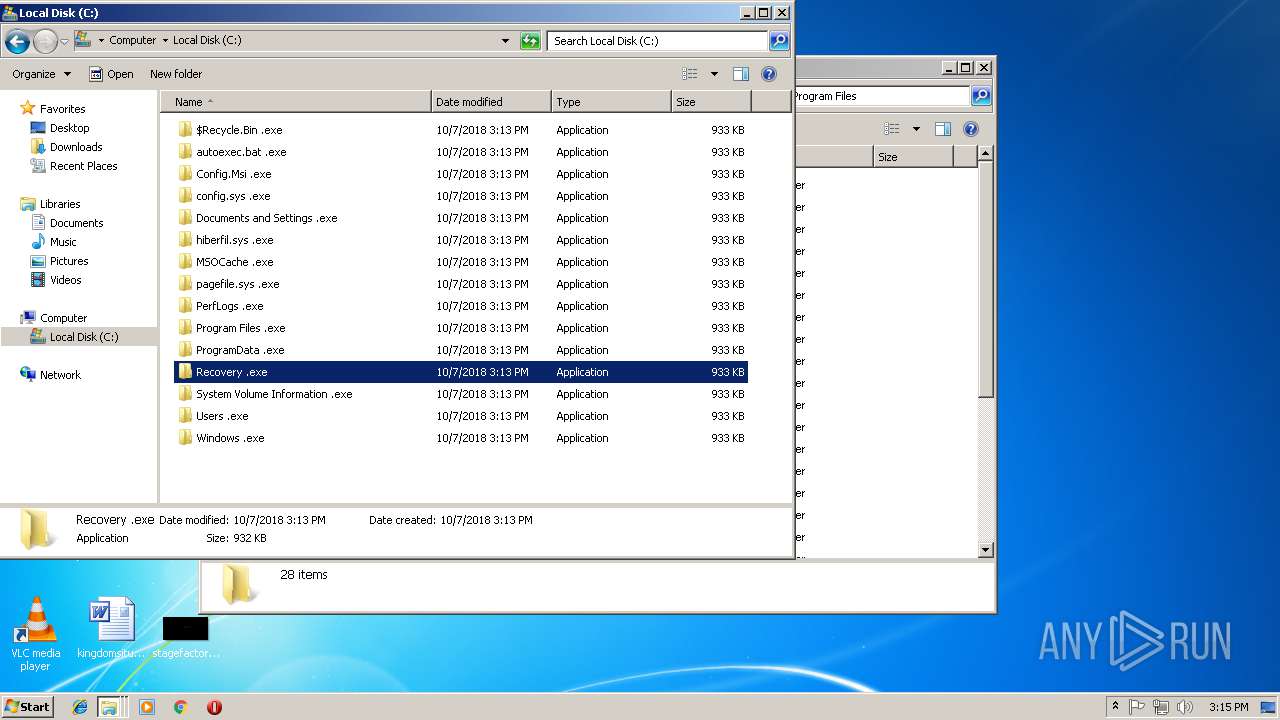
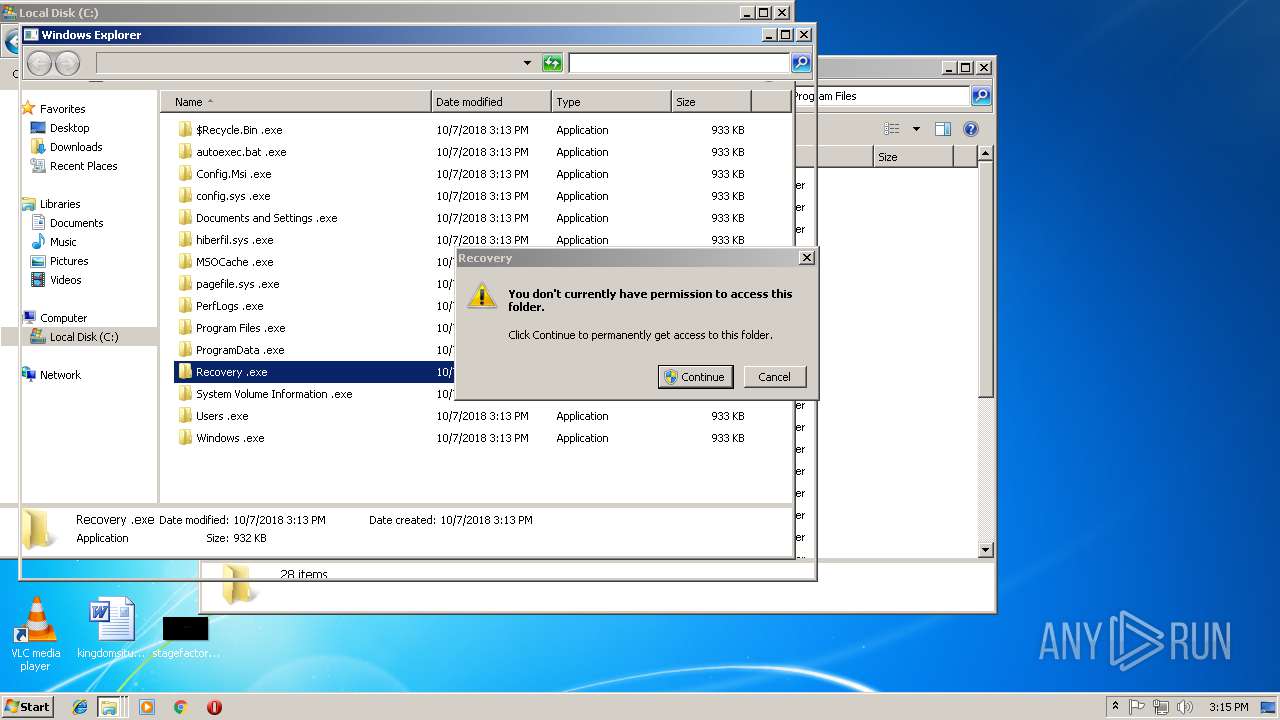
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
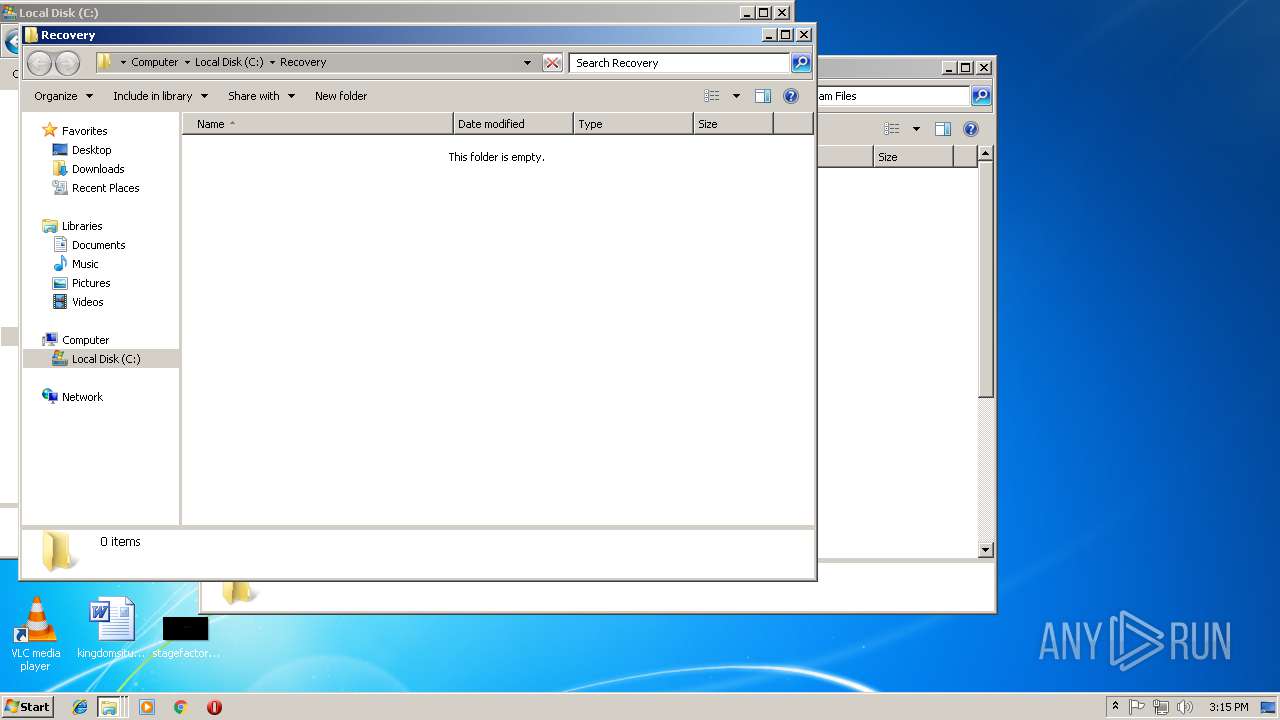
| 1152 | "C:\Recovery .exe" | C:\Recovery .exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Mira Malware Exit code: 0 Version: 1.0.0.155 Modules
| |||||||||||||||
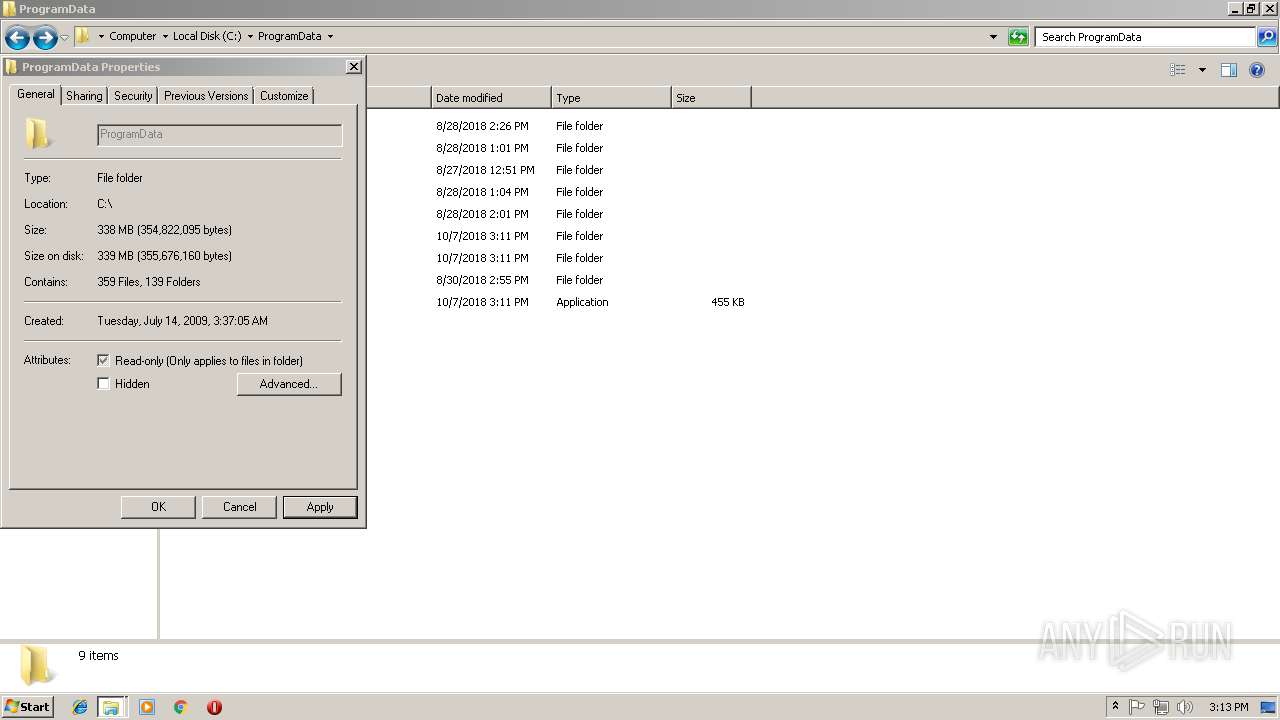
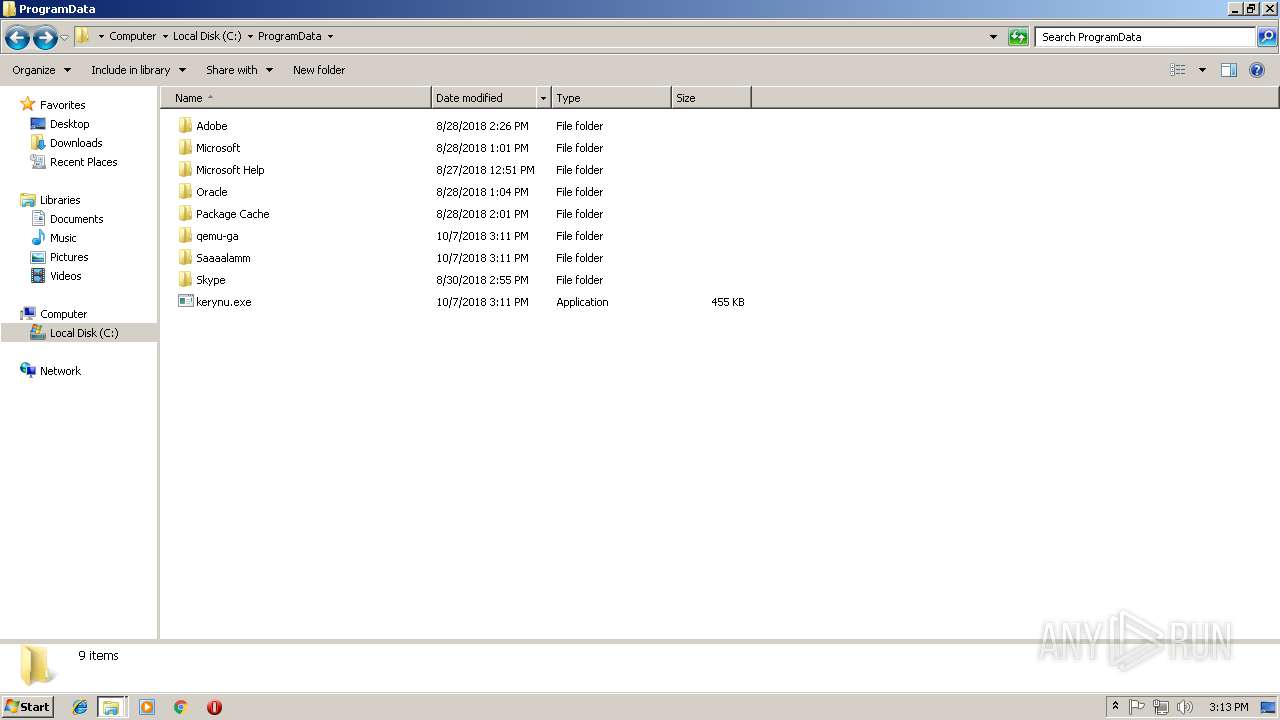
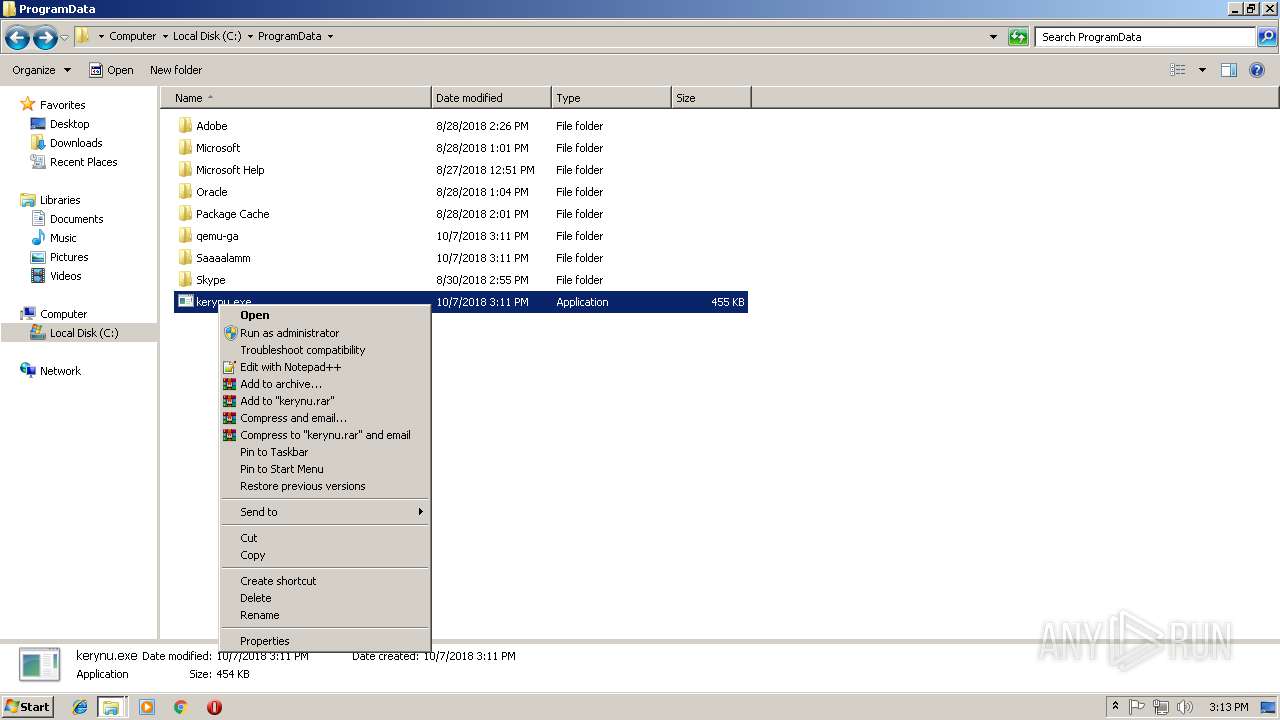
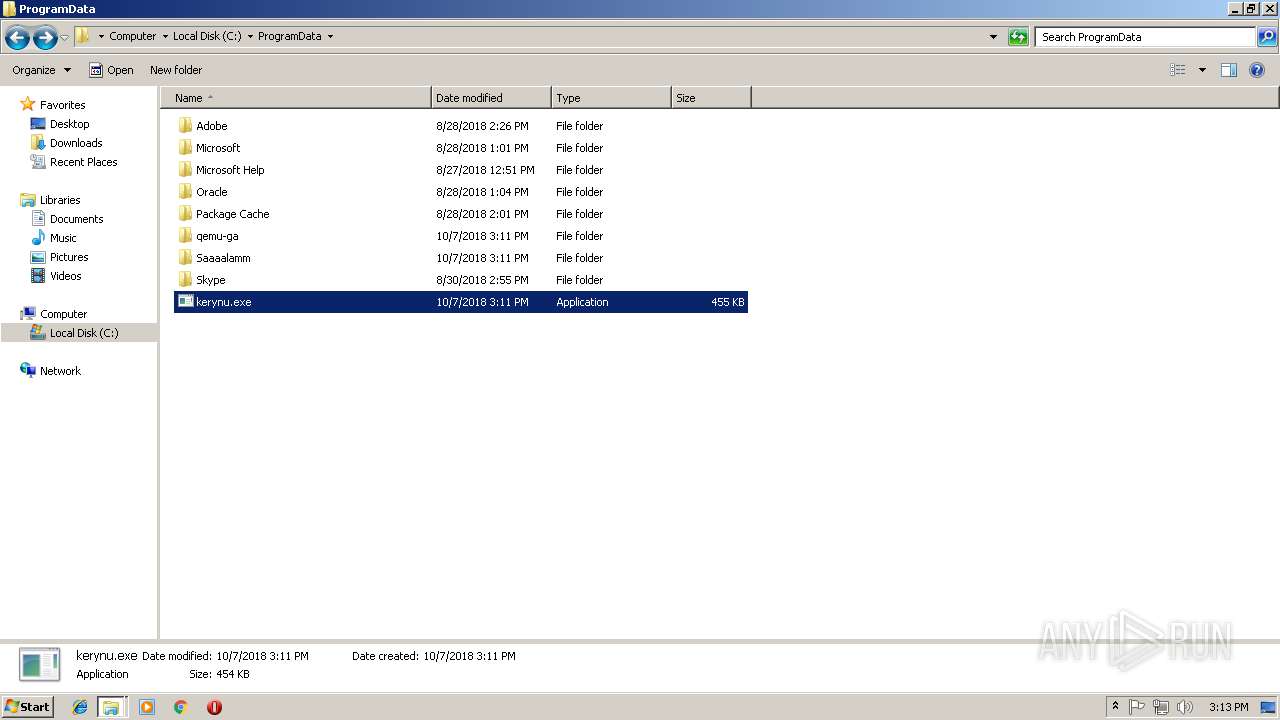
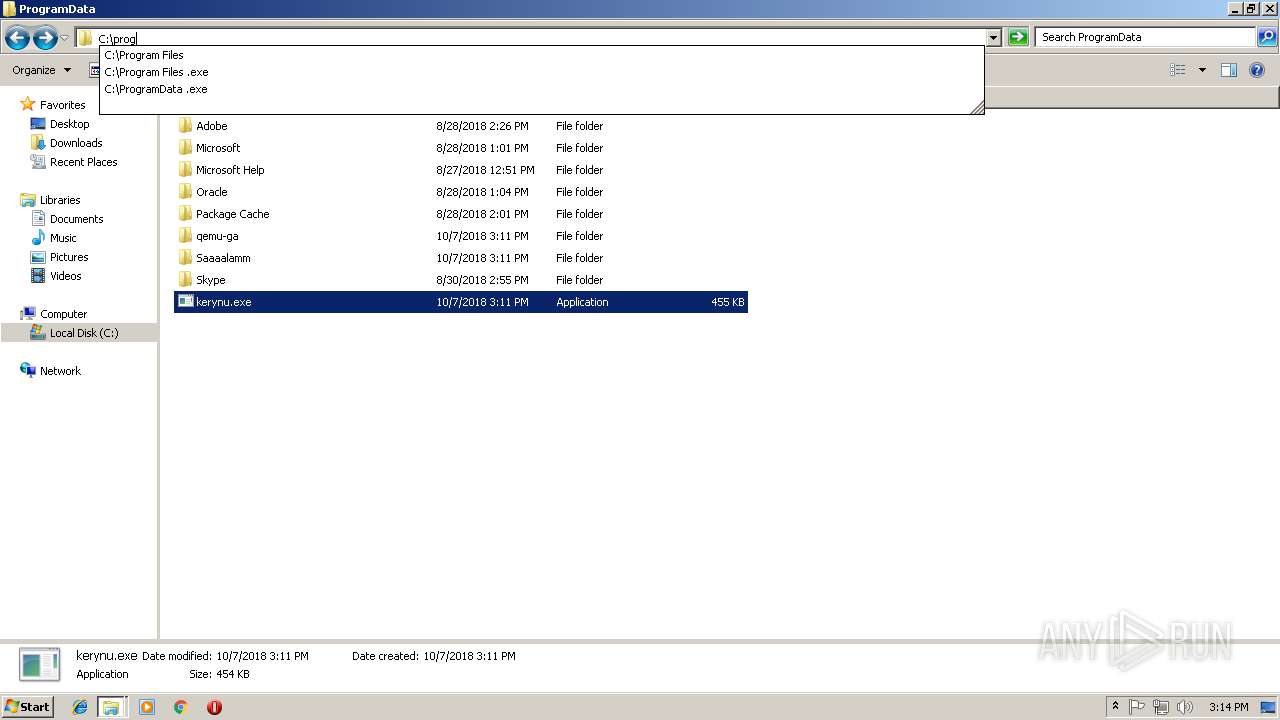
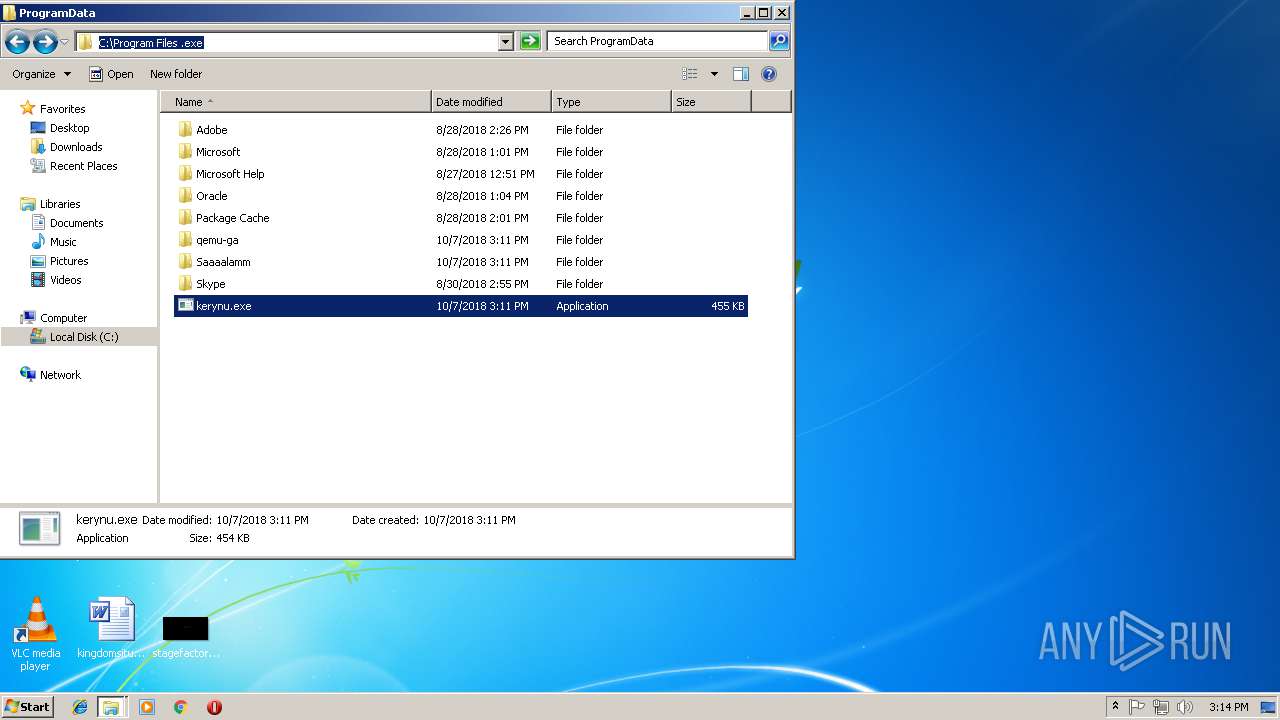
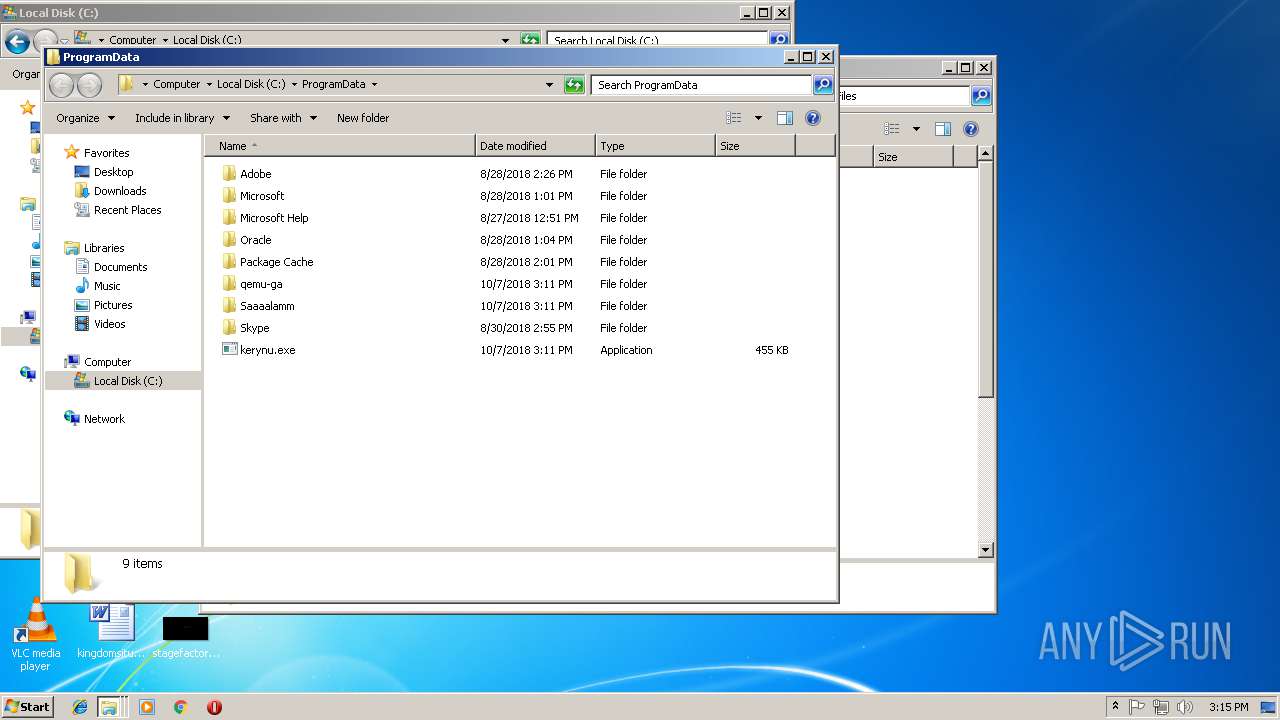
| 2020 | "C:\ProgramData\kerynu.exe" | C:\ProgramData\kerynu.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2052 | "C:\ProgramData\kerynu.exe" | C:\ProgramData\kerynu.exe | f473474711885867b6c6b98c2076f99dd284afffe90b2db861d35c47669e1170.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2396 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3272 | "C:\Users\admin\Desktop\f473474711885867b6c6b98c2076f99dd284afffe90b2db861d35c47669e1170.exe" | C:\Users\admin\Desktop\f473474711885867b6c6b98c2076f99dd284afffe90b2db861d35c47669e1170.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Mira Malware Exit code: 0 Version: 1.0.0.155 Modules
| |||||||||||||||
| 3296 | "C:\ProgramData .exe" | C:\ProgramData .exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Mira Malware Exit code: 0 Version: 1.0.0.155 Modules
| |||||||||||||||
| 3388 | "C:\hiberfil.sys .exe" | C:\hiberfil.sys .exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Mira Malware Exit code: 0 Version: 1.0.0.155 Modules
| |||||||||||||||
| 3452 | "C:\hiberfil.sys .exe" | C:\hiberfil.sys .exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Mira Malware Exit code: 0 Version: 1.0.0.155 Modules
| |||||||||||||||
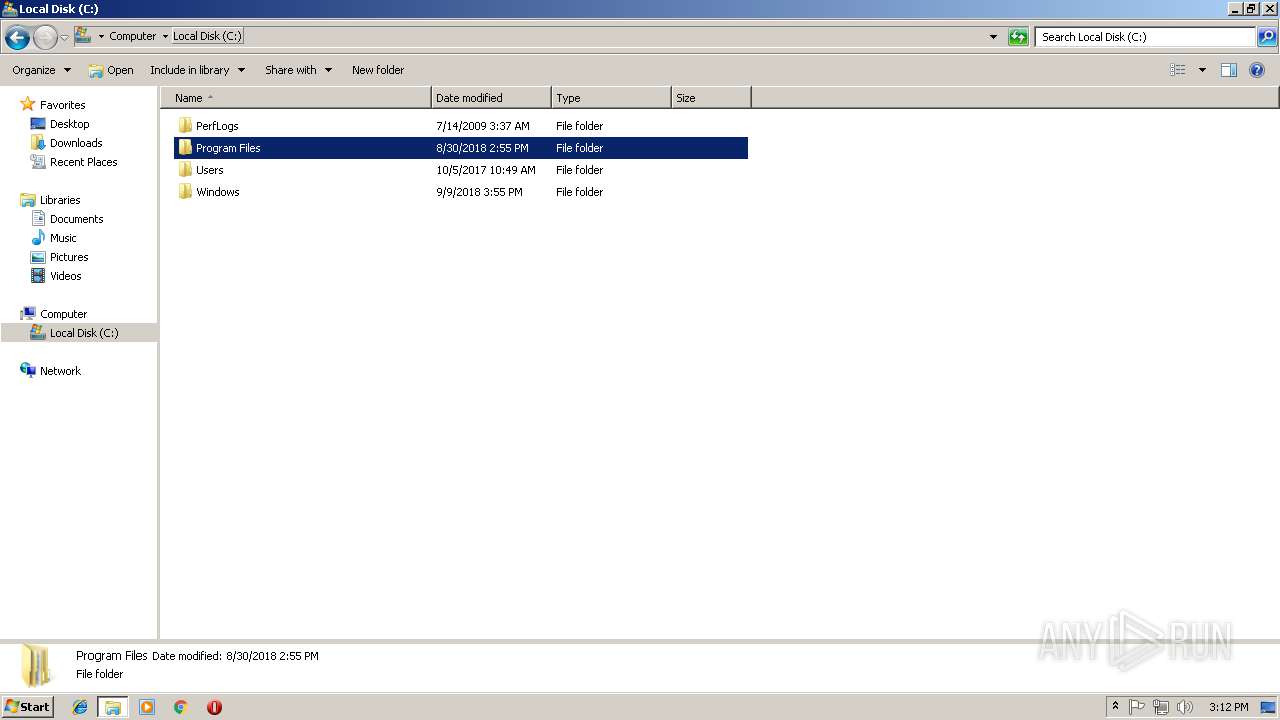
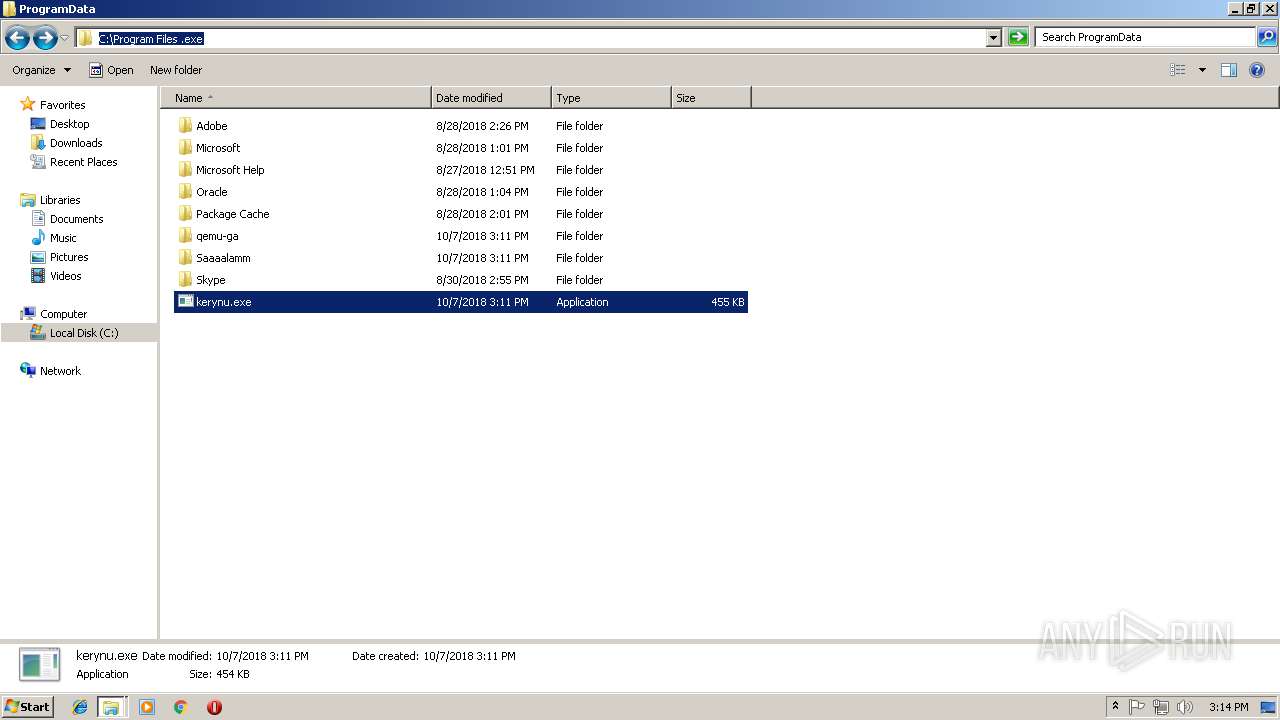
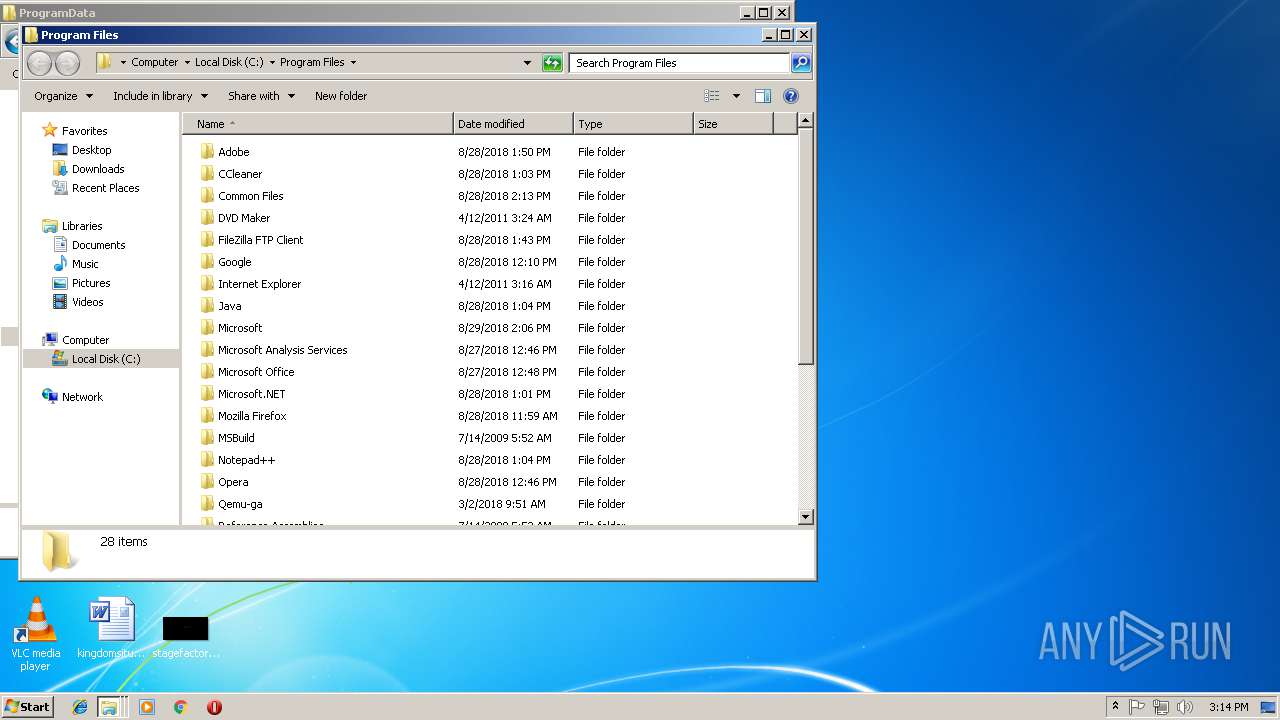
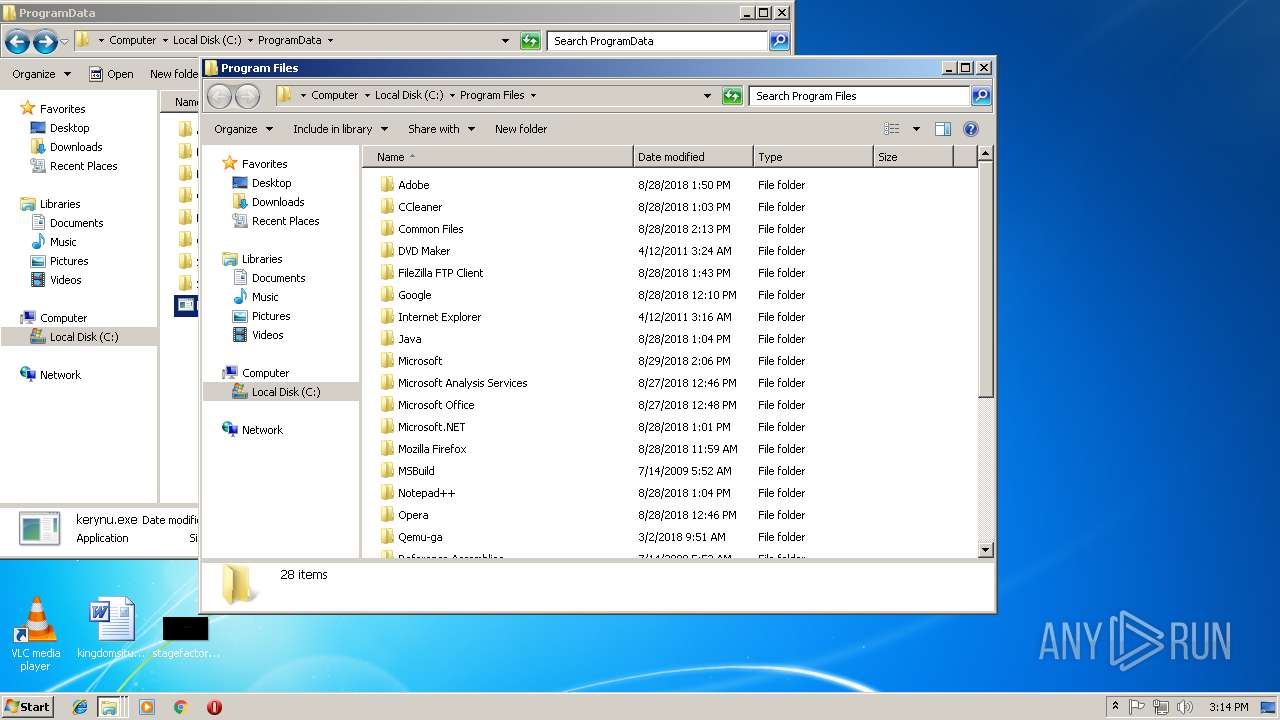
| 3664 | "C:\Program Files .exe" | C:\Program Files .exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Mira Malware Exit code: 0 Version: 1.0.0.155 Modules
| |||||||||||||||
| 3832 | C:\Windows\system32\DllHost.exe /Processid:{4D111E08-CBF7-4F12-A926-2C7920AF52FC} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 782
Read events
1 742
Write events
40
Delete events
0
Modification events
| (PID) Process: | (2052) kerynu.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft® Windows® Operating System |
Value: C:\ProgramData\kerynu.exe | |||
| (PID) Process: | (2020) kerynu.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft® Windows® Operating System |
Value: C:\ProgramData\kerynu.exe | |||
| (PID) Process: | (3664) Program Files .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3664) Program Files .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000002000000000000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3664) Program Files .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000004000000000000000200000003000000FFFFFFFF | |||
| (PID) Process: | (3664) Program Files .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1152) Recovery .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1152) Recovery .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000002000000000000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1152) Recovery .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0 |
| Operation: | write | Name: | 5 |
Value: 56003100000000000000000012005265636F7665727900003E0008000400EFBE00000000000000002A000000000000000000000000000000000000000000000000005200650063006F007600650072007900000018000000 | |||
| (PID) Process: | (1152) Recovery .exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0 |
| Operation: | write | Name: | MRUListEx |
Value: 050000000100000004000000000000000200000003000000FFFFFFFF | |||
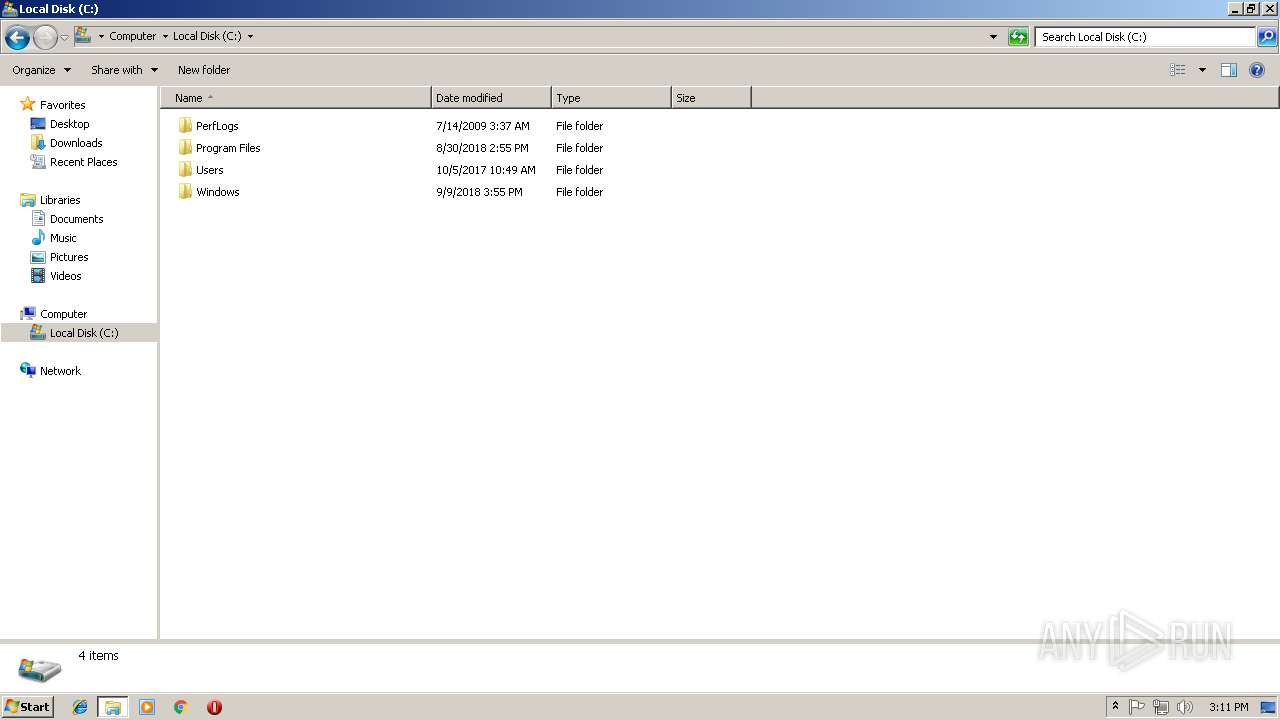
Executable files
17
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2020 | kerynu.exe | C:\config.sys .exe | executable | |
MD5:— | SHA256:— | |||
| 2020 | kerynu.exe | C:\Config.Msi .exe | executable | |
MD5:— | SHA256:— | |||
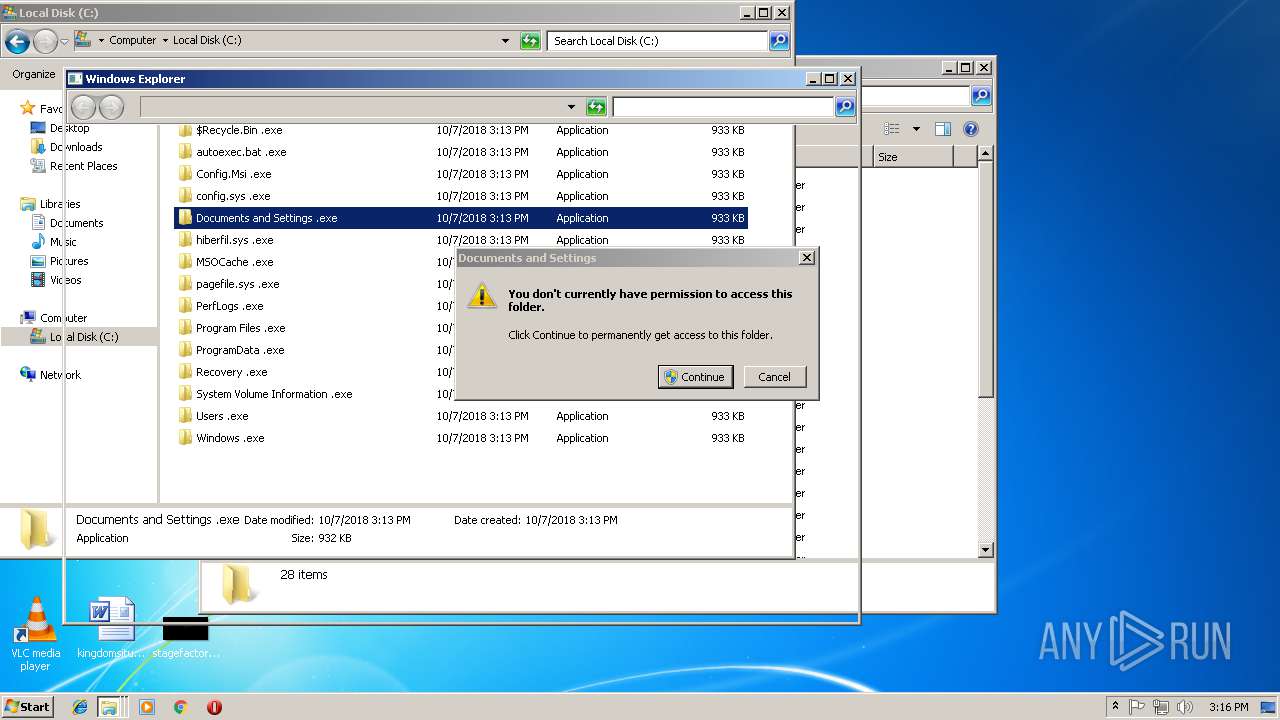
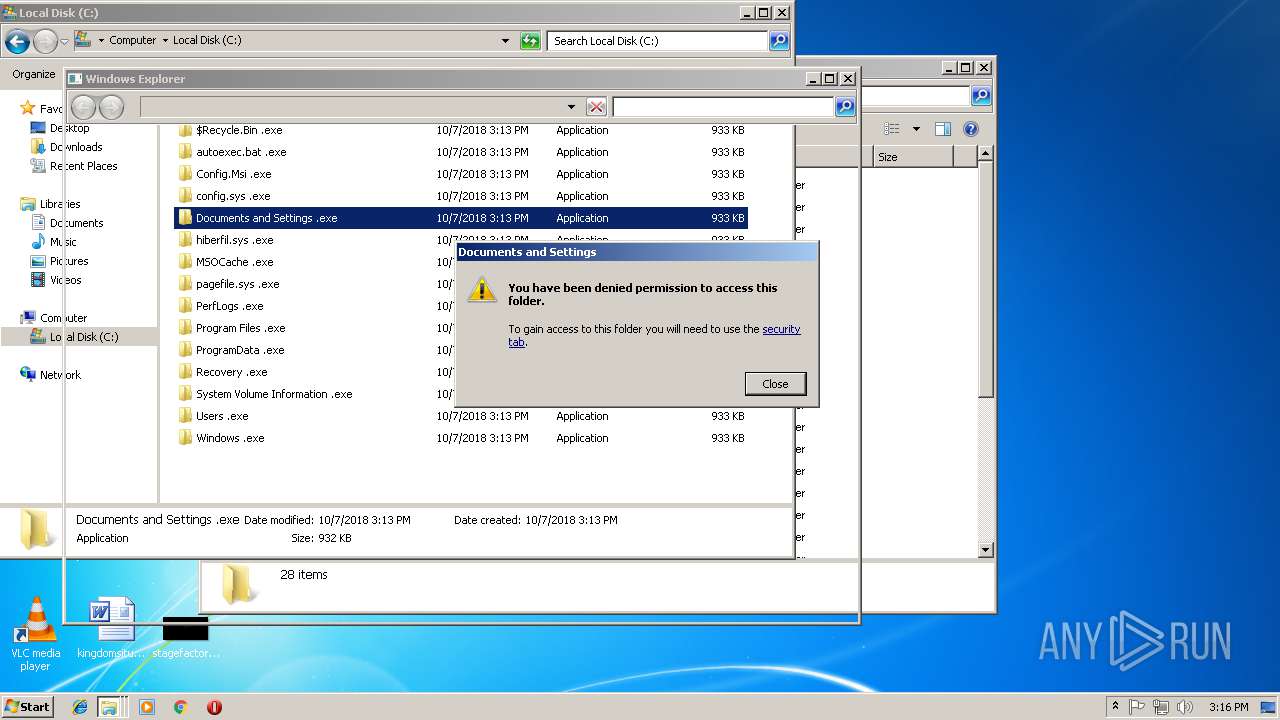
| 2020 | kerynu.exe | C:\Documents and Settings .exe | executable | |
MD5:— | SHA256:— | |||
| 2020 | kerynu.exe | C:\autoexec.bat .exe | executable | |
MD5:— | SHA256:— | |||
| 2020 | kerynu.exe | C:\$Recycle.Bin .exe | executable | |
MD5:— | SHA256:— | |||
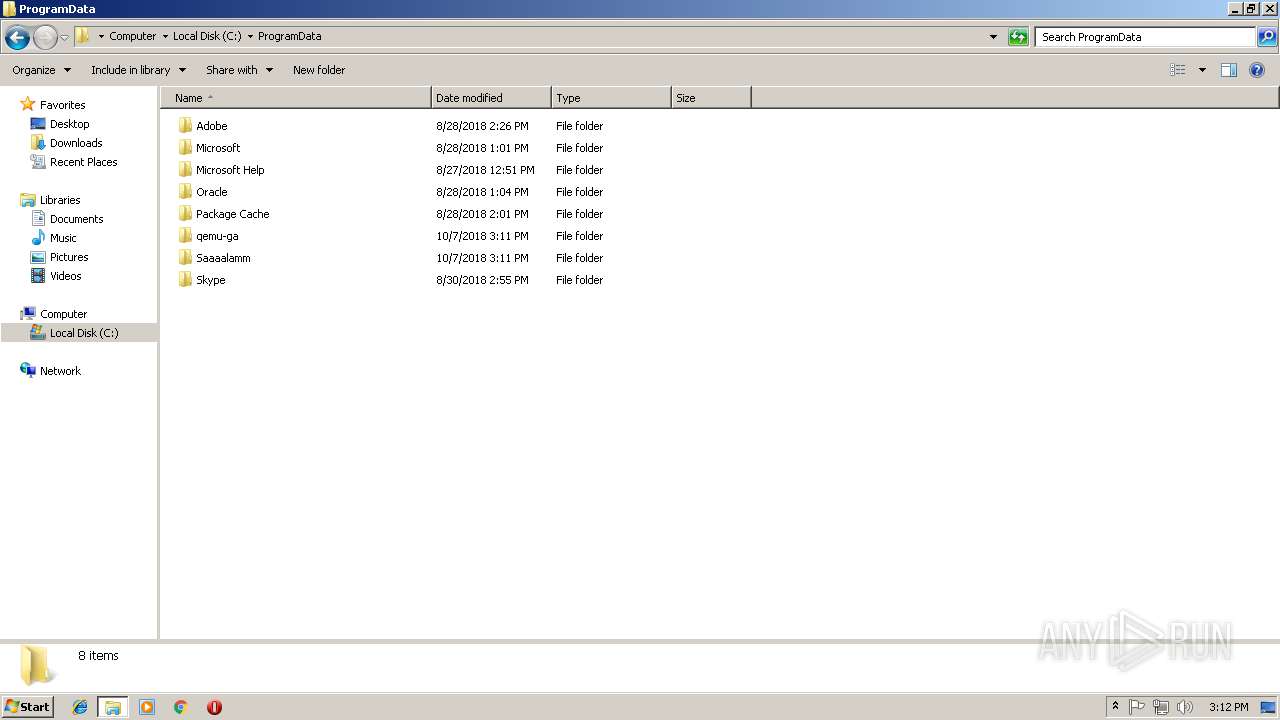
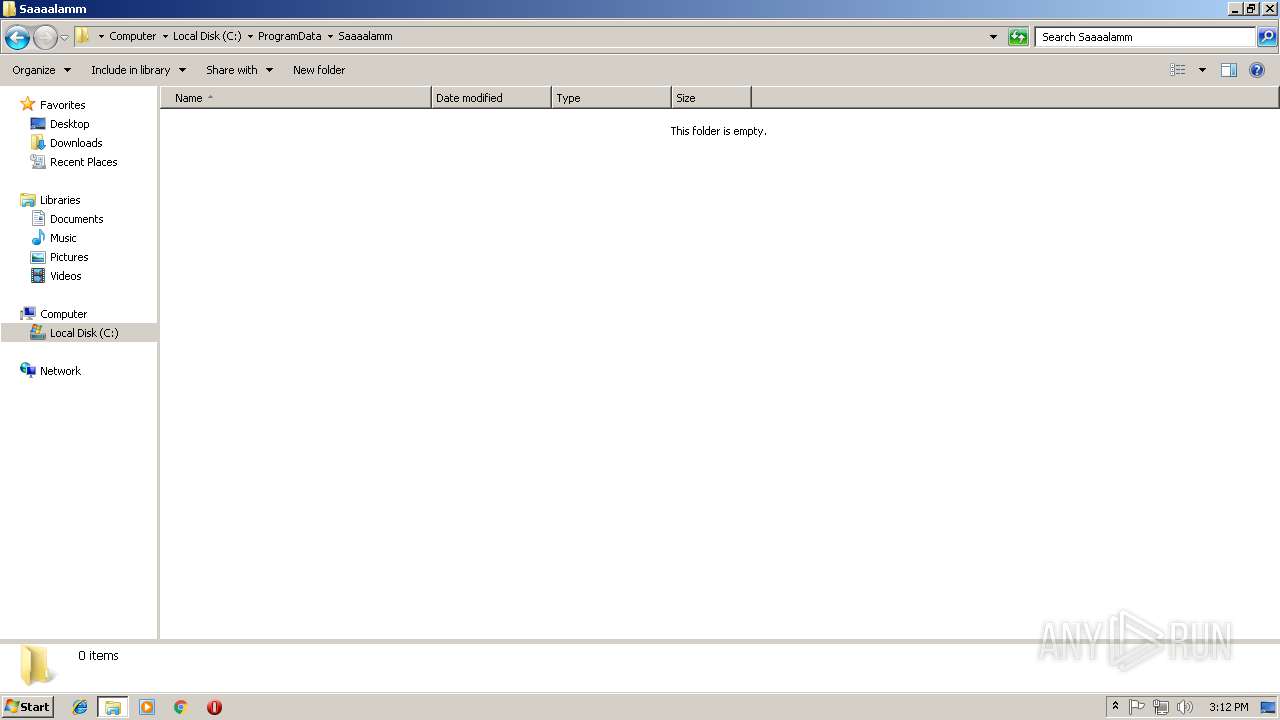
| 3272 | f473474711885867b6c6b98c2076f99dd284afffe90b2db861d35c47669e1170.exe | C:\ProgramData\Saaaalamm\Mira.h | executable | |
MD5:70D6CB7DD01EBD5A21AF02945D2AE12F | SHA256:136FB79A4B868976A011043345FBEF2CB088DD799757EC3970480EB99D9F2E92 | |||
| 3272 | f473474711885867b6c6b98c2076f99dd284afffe90b2db861d35c47669e1170.exe | C:\ProgramData\kerynu.exe | executable | |
MD5:12D437799C73EA8AA7A72405994FDDDF | SHA256:4CE62EE6996C73753D914B7A15ED0616FA7E9C341641D39D9E3D91B1E34050B2 | |||
| 2020 | kerynu.exe | C:\Windows .exe | executable | |
MD5:— | SHA256:— | |||
| 2020 | kerynu.exe | C:\PerfLogs .exe | executable | |
MD5:— | SHA256:— | |||
| 2020 | kerynu.exe | C:\ProgramData .exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report