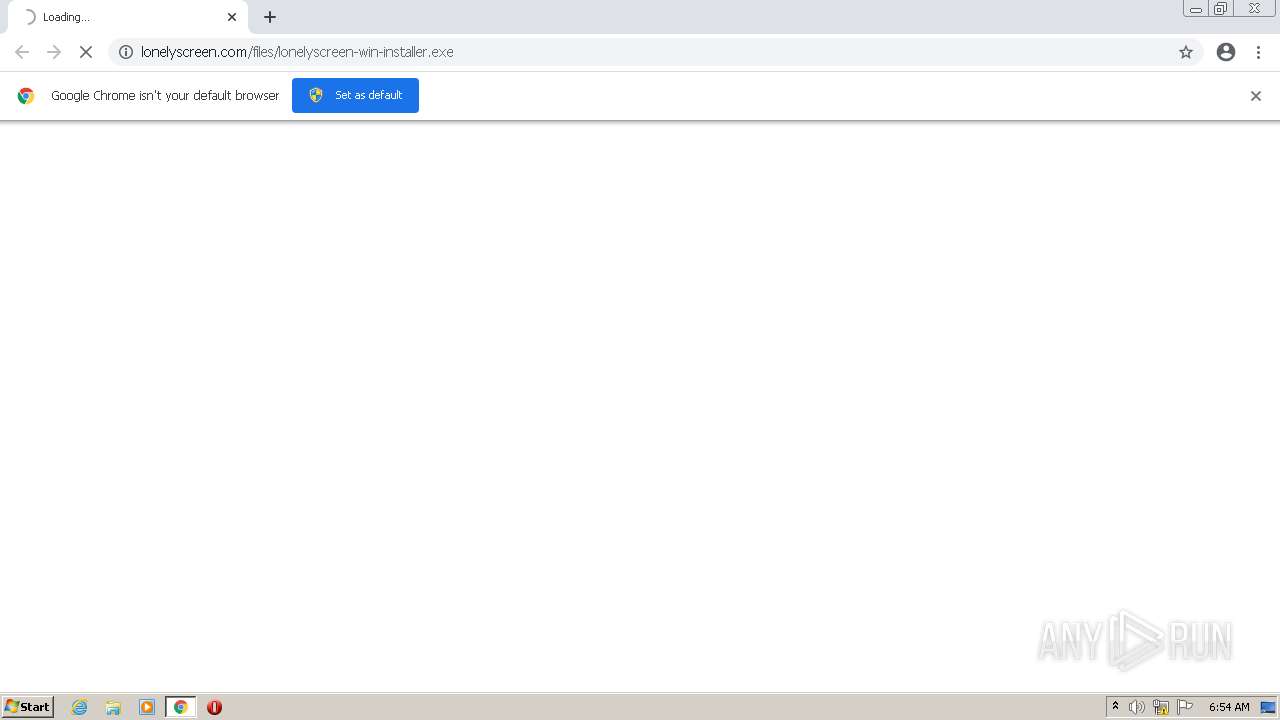
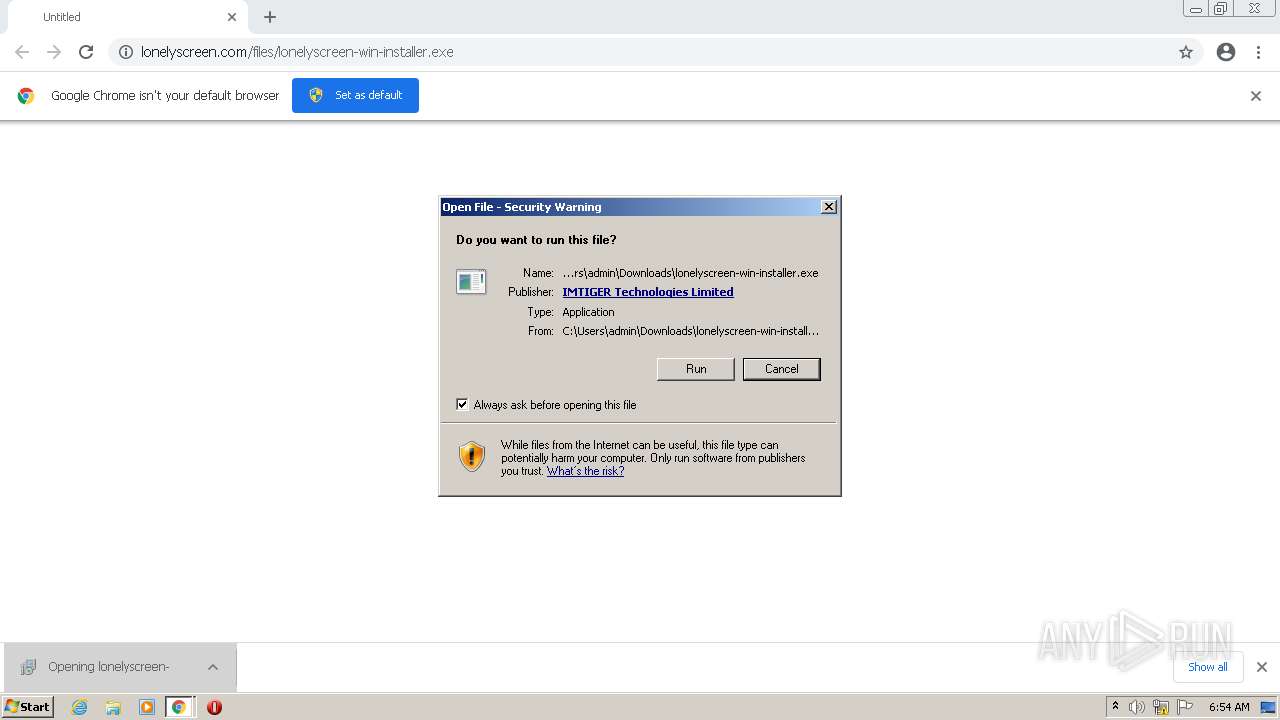
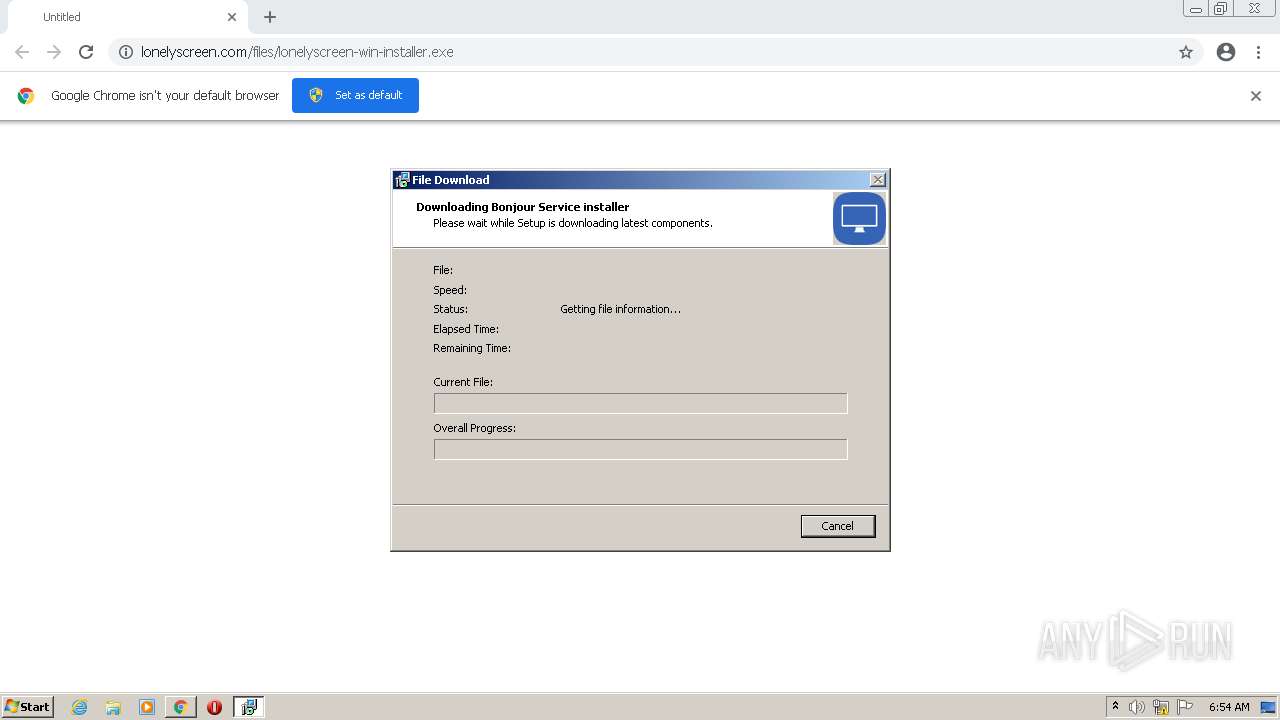
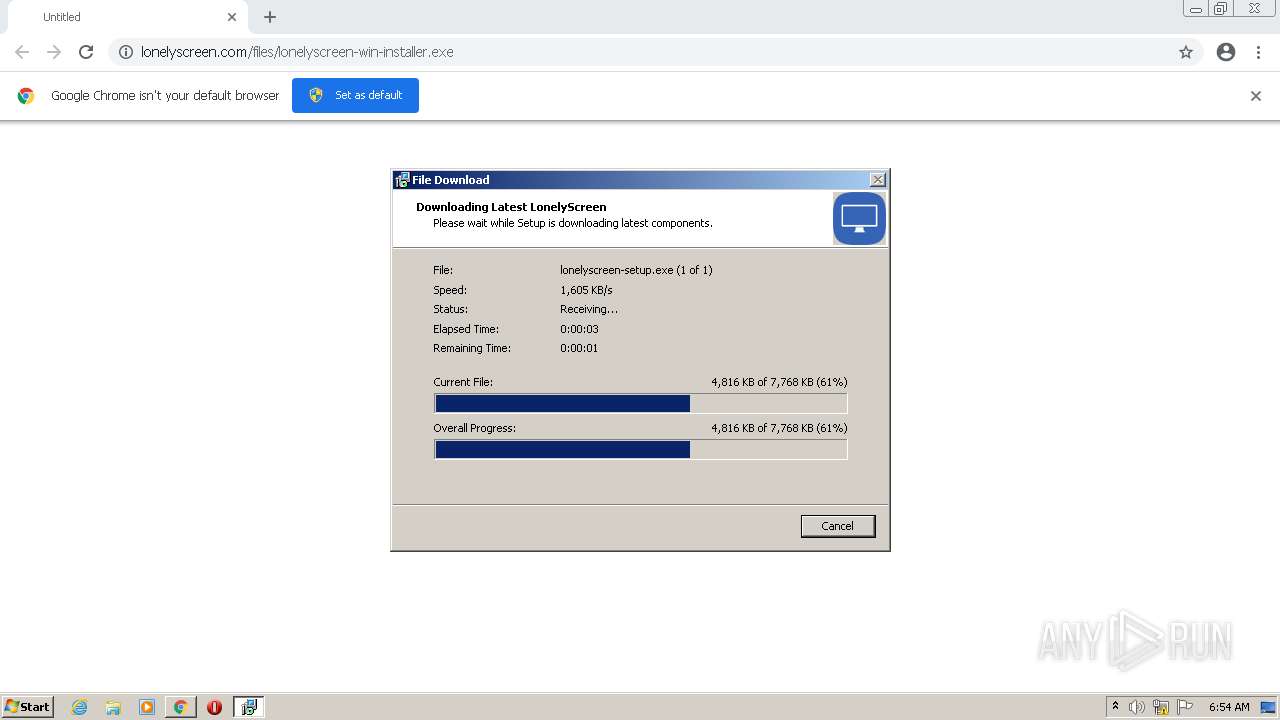
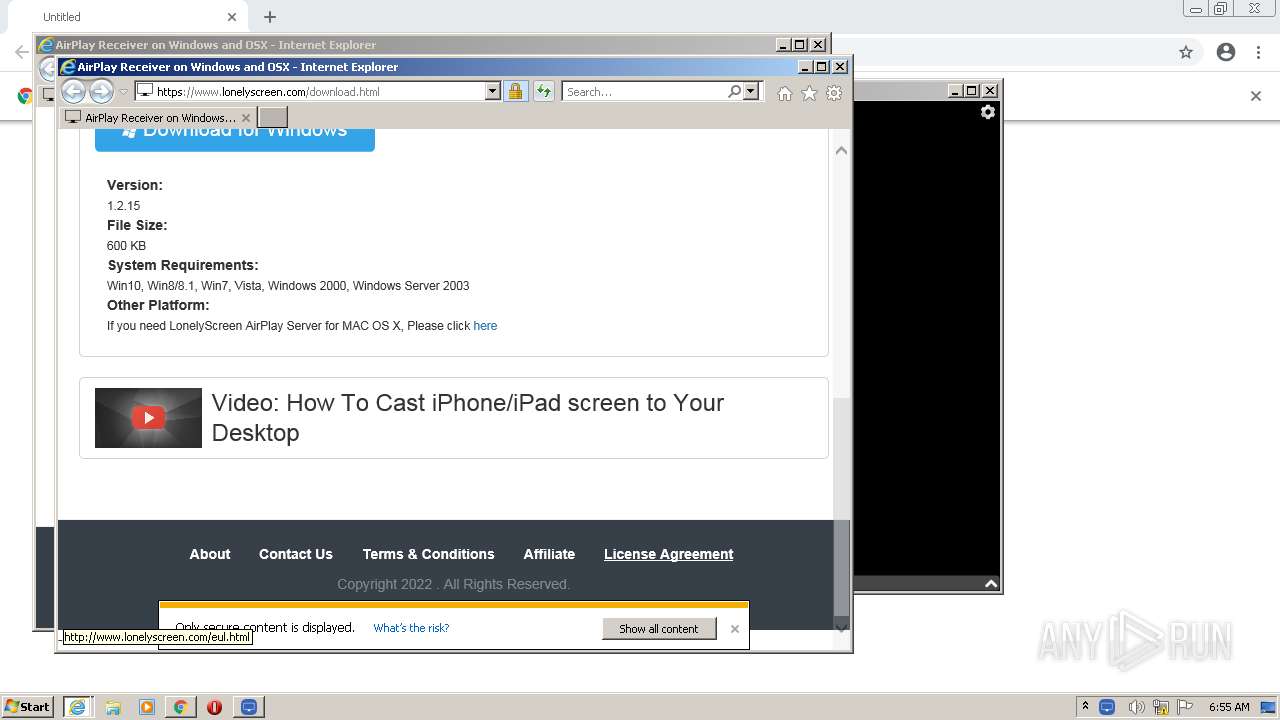
| URL: | https://www.lonelyscreen.com/files/lonelyscreen-win-installer.exe |
| Full analysis: | https://app.any.run/tasks/a48455c7-a7ac-4778-b91c-e35bb16598cf |
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2022, 06:54:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EBB34224EC503E155248DECEE1219FD6 |
| SHA1: | 7A3337FE1C305D357DAF812828791CA5CFFE7A88 |
| SHA256: | F472A3652E7E5F7236CEDF29D2339D9796B7DC7F902A29EDA21BDC329DC878C7 |
| SSDEEP: | 3:N8DSL1lEdz0KioHSTNTXLNn:2OLmKGSZTXLN |
MALICIOUS
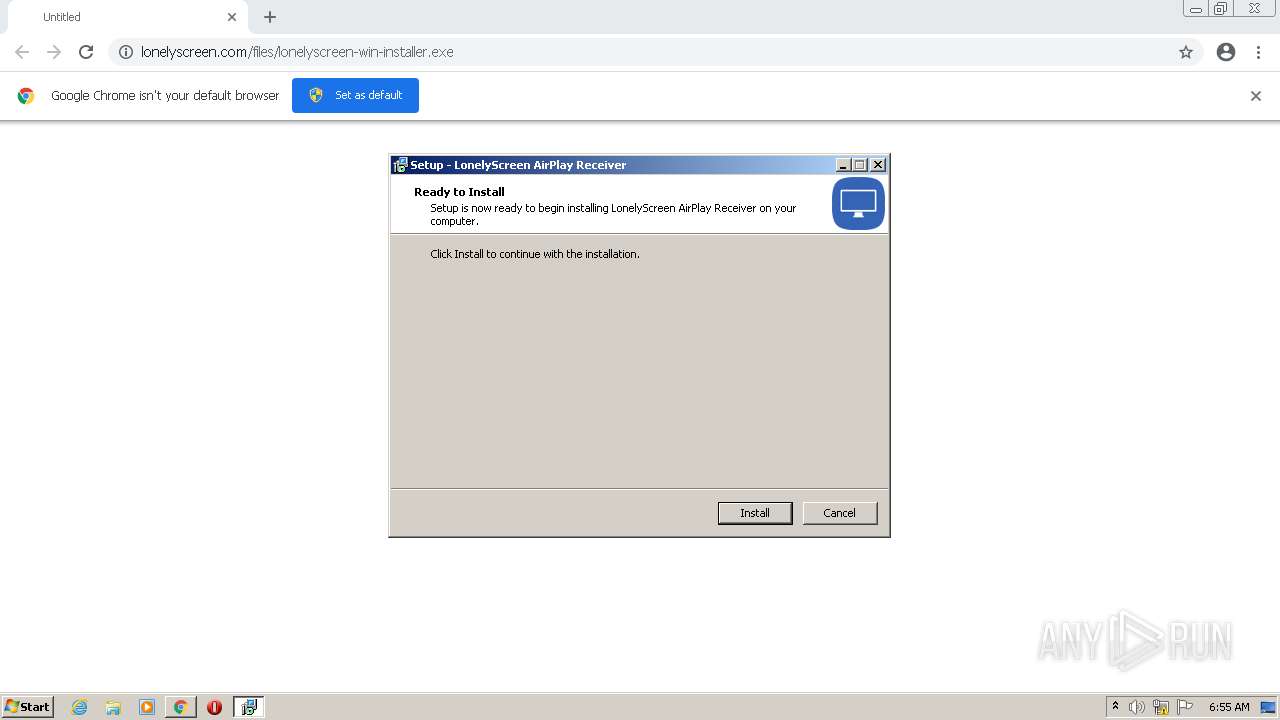
Application was dropped or rewritten from another process
- lonelyscreen-win-installer.exe (PID: 3144)
- lonelyscreen-win-installer.exe (PID: 1984)
- lonelyscreen.exe (PID: 3152)
- mDNSResponder.exe (PID: 4024)
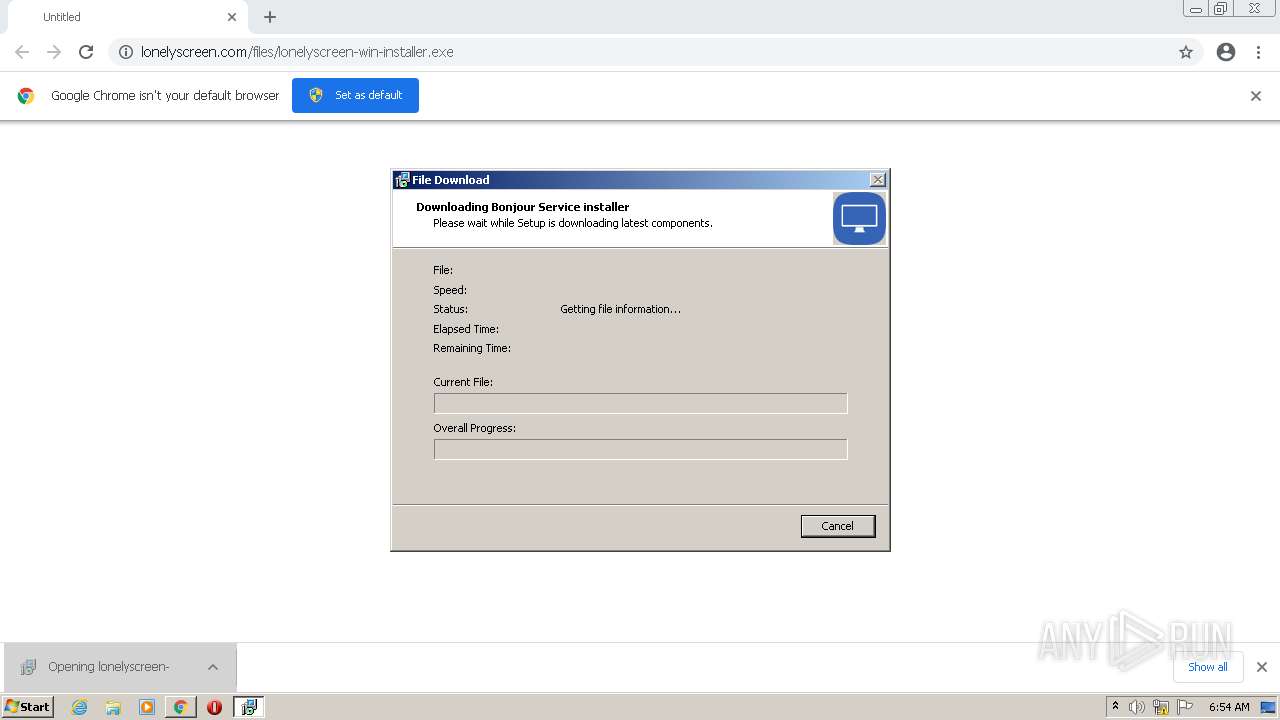
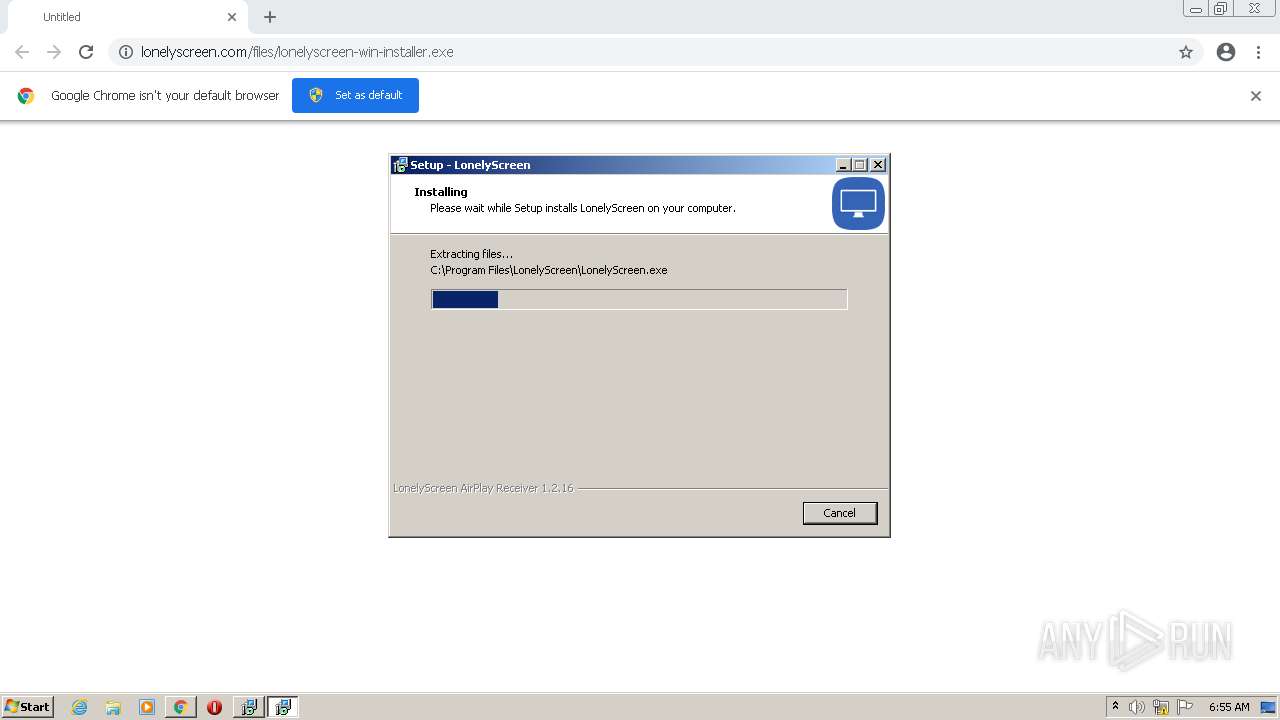
Drops executable file immediately after starts
- lonelyscreen-win-installer.exe (PID: 3144)
- lonelyscreen-win-installer.exe (PID: 1984)
- lonelyscreen-win-installer.tmp (PID: 1408)
- setup.exe (PID: 1124)
- setup.tmp (PID: 2408)
Changes settings of System certificates
- lonelyscreen-win-installer.tmp (PID: 1408)
Actions looks like stealing of personal data
- lonelyscreen-win-installer.tmp (PID: 1408)
Changes the autorun value in the registry
- setup.tmp (PID: 2408)
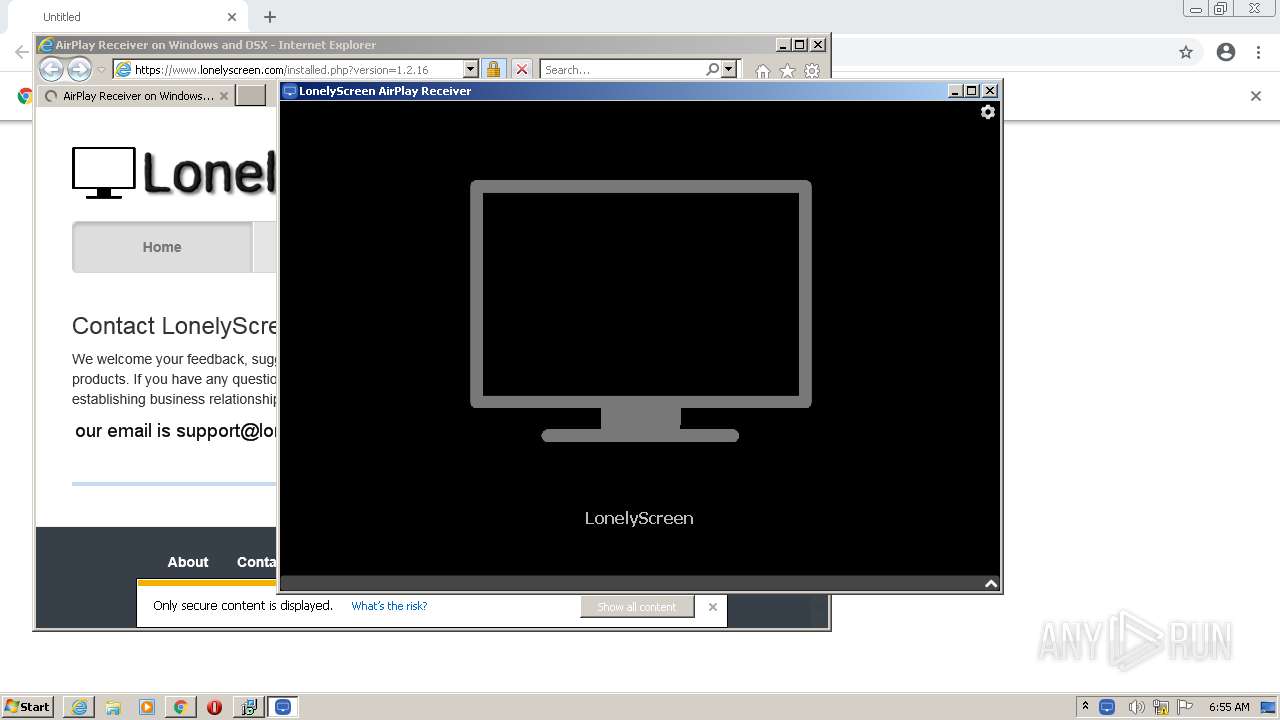
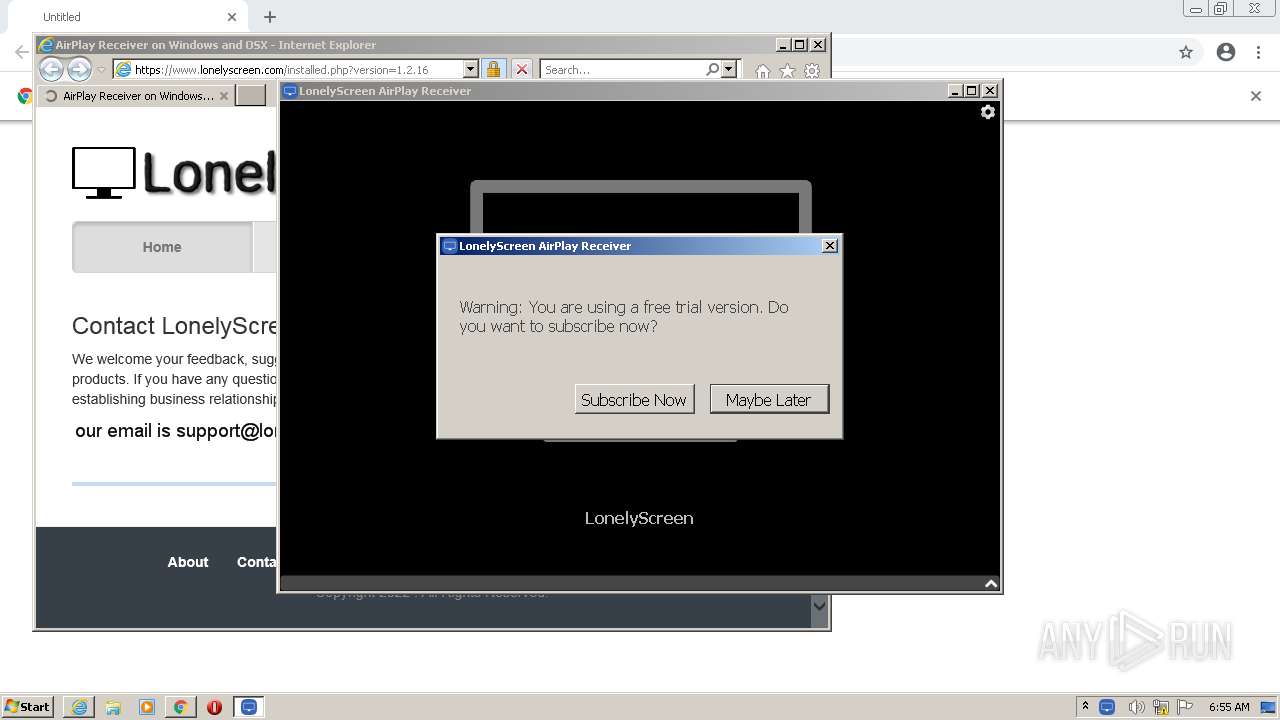
Loads dropped or rewritten executable
- lonelyscreen.exe (PID: 3152)
- iexplore.exe (PID: 2764)
- MsiExec.exe (PID: 2380)
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 3384)
- svchost.exe (PID: 696)
- svchost.exe (PID: 924)
- chrome.exe (PID: 3680)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1324)
- lonelyscreen-win-installer.exe (PID: 1984)
- lonelyscreen-win-installer.exe (PID: 3144)
- lonelyscreen-win-installer.tmp (PID: 1408)
- setup.tmp (PID: 2408)
- setup.exe (PID: 1124)
- msiexec.exe (PID: 2848)
Checks supported languages
- lonelyscreen-win-installer.exe (PID: 3144)
- lonelyscreen-win-installer.tmp (PID: 3088)
- lonelyscreen-win-installer.tmp (PID: 1408)
- lonelyscreen-win-installer.exe (PID: 1984)
- setup.tmp (PID: 2408)
- setup.exe (PID: 1124)
- lonelyscreen.exe (PID: 3152)
- mDNSResponder.exe (PID: 4024)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 352)
Drops a file with too old compile date
- lonelyscreen-win-installer.tmp (PID: 1408)
- setup.tmp (PID: 2408)
- msiexec.exe (PID: 2848)
Reads the computer name
- lonelyscreen-win-installer.tmp (PID: 3088)
- lonelyscreen-win-installer.tmp (PID: 1408)
- setup.tmp (PID: 2408)
- lonelyscreen.exe (PID: 3152)
- mDNSResponder.exe (PID: 4024)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 352)
Drops a file that was compiled in debug mode
- lonelyscreen-win-installer.tmp (PID: 1408)
- setup.tmp (PID: 2408)
- msiexec.exe (PID: 2848)
Reads the Windows organization settings
- lonelyscreen-win-installer.tmp (PID: 1408)
- setup.tmp (PID: 2408)
- msiexec.exe (PID: 2848)
Reads Windows owner or organization settings
- lonelyscreen-win-installer.tmp (PID: 1408)
- setup.tmp (PID: 2408)
- msiexec.exe (PID: 2848)
Adds / modifies Windows certificates
- lonelyscreen-win-installer.tmp (PID: 1408)
Creates a directory in Program Files
- setup.tmp (PID: 2408)
- msiexec.exe (PID: 2848)
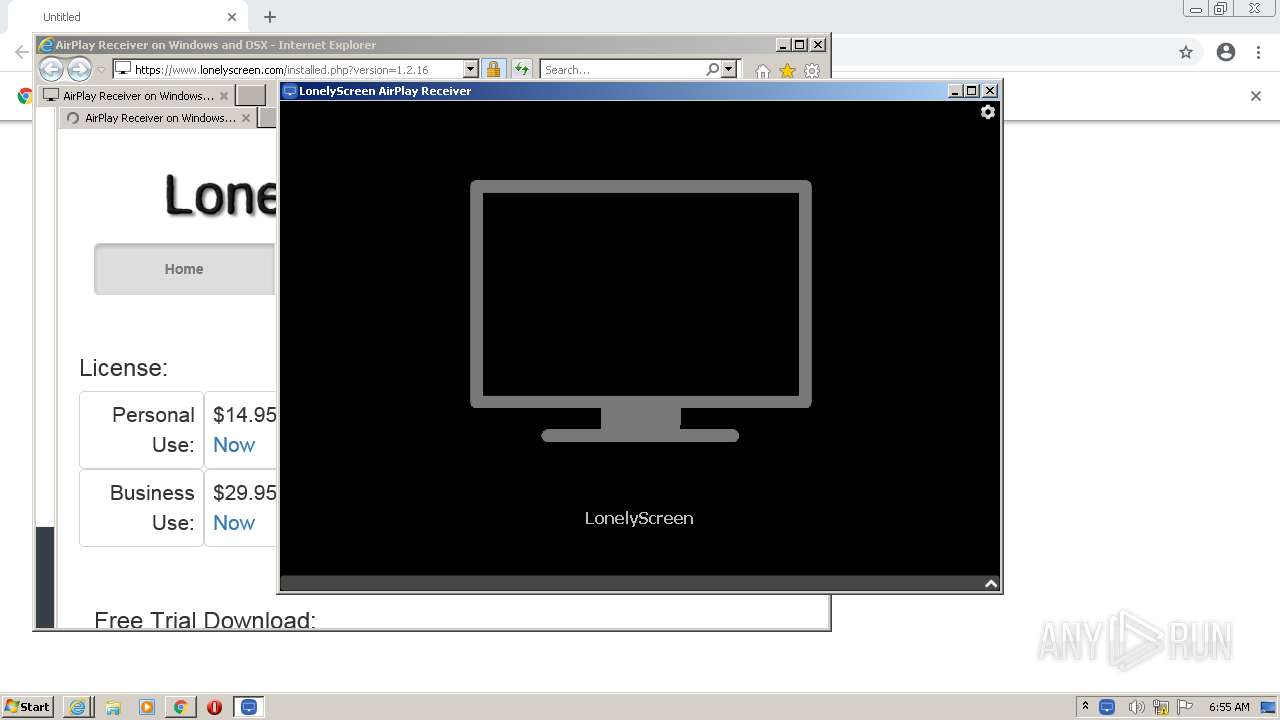
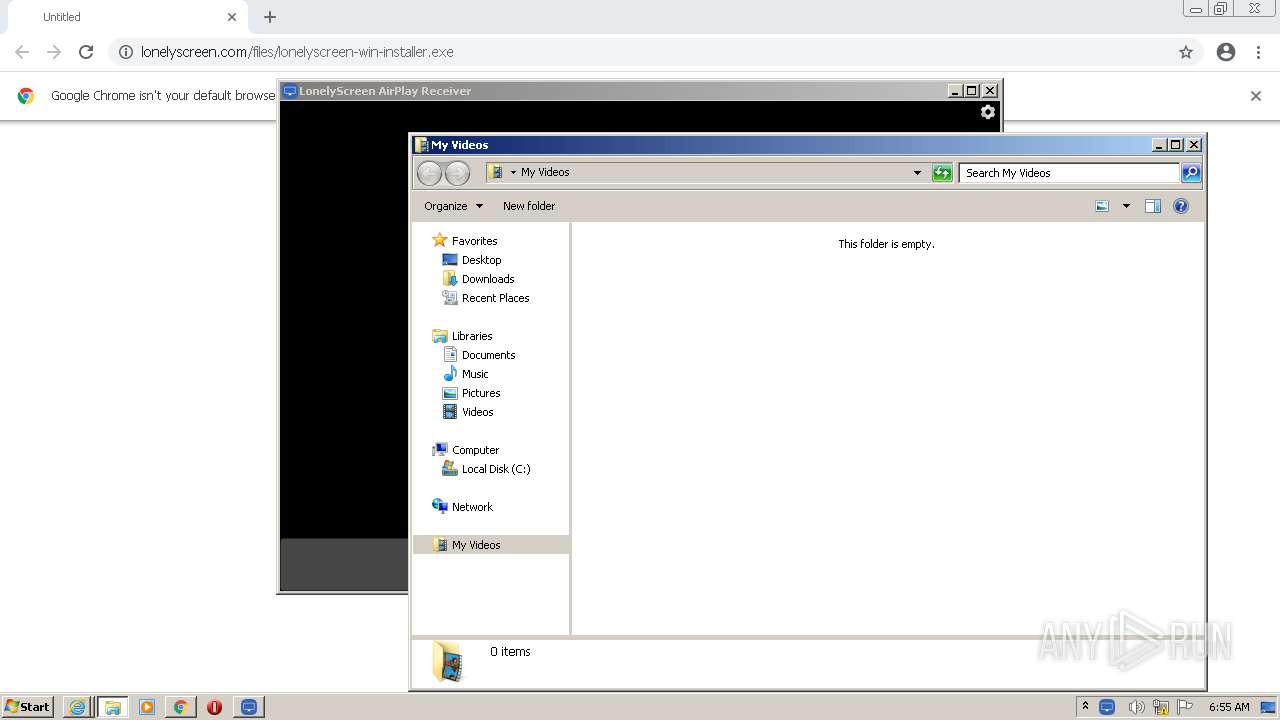
Starts Internet Explorer
- setup.tmp (PID: 2408)
- lonelyscreen.exe (PID: 3152)
Starts Microsoft Installer
- lonelyscreen-win-installer.tmp (PID: 1408)
Executed as Windows Service
- msiexec.exe (PID: 2848)
- mDNSResponder.exe (PID: 4024)
Application launched itself
- msiexec.exe (PID: 2848)
Creates files in the program directory
- msiexec.exe (PID: 2848)
Creates files in the Windows directory
- msiexec.exe (PID: 2848)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 3384)
Creates a software uninstall entry
- msiexec.exe (PID: 2848)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 2848)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 352)
- explorer.exe (PID: 2948)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 352)
INFO
Application launched itself
- chrome.exe (PID: 1324)
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 636)
Reads the hosts file
- chrome.exe (PID: 1324)
- chrome.exe (PID: 3680)
Checks supported languages
- chrome.exe (PID: 1324)
- chrome.exe (PID: 628)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 1740)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 3652)
- iexplore.exe (PID: 3976)
- msiexec.exe (PID: 3276)
- msiexec.exe (PID: 2848)
- iexplore.exe (PID: 2764)
- MsiExec.exe (PID: 3272)
- MsiExec.exe (PID: 2380)
- MsiExec.exe (PID: 1116)
- chrome.exe (PID: 688)
- chrome.exe (PID: 3932)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 3384)
- chrome.exe (PID: 3184)
- svchost.exe (PID: 924)
- explorer.exe (PID: 1236)
- explorer.exe (PID: 2948)
Reads the computer name
- chrome.exe (PID: 1324)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 3520)
- iexplore.exe (PID: 3976)
- msiexec.exe (PID: 3276)
- msiexec.exe (PID: 2848)
- iexplore.exe (PID: 2764)
- MsiExec.exe (PID: 3272)
- MsiExec.exe (PID: 1116)
- chrome.exe (PID: 688)
- chrome.exe (PID: 3932)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 3384)
- chrome.exe (PID: 3184)
- explorer.exe (PID: 1236)
- explorer.exe (PID: 2948)
Reads settings of System Certificates
- chrome.exe (PID: 3680)
- chrome.exe (PID: 1324)
- lonelyscreen-win-installer.tmp (PID: 1408)
- iexplore.exe (PID: 2764)
- msiexec.exe (PID: 2848)
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 3384)
- iexplore.exe (PID: 636)
Checks Windows Trust Settings
- chrome.exe (PID: 1324)
- lonelyscreen-win-installer.tmp (PID: 1408)
- msiexec.exe (PID: 2848)
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 3384)
- iexplore.exe (PID: 636)
Application was dropped or rewritten from another process
- lonelyscreen-win-installer.tmp (PID: 3088)
- lonelyscreen-win-installer.tmp (PID: 1408)
- setup.exe (PID: 1124)
- setup.tmp (PID: 2408)
Loads dropped or rewritten executable
- lonelyscreen-win-installer.tmp (PID: 1408)
- setup.tmp (PID: 2408)
Creates files in the program directory
- setup.tmp (PID: 2408)
- lonelyscreen-win-installer.tmp (PID: 1408)
Creates a software uninstall entry
- setup.tmp (PID: 2408)
- lonelyscreen-win-installer.tmp (PID: 1408)
Changes internet zones settings
- iexplore.exe (PID: 3976)
- iexplore.exe (PID: 636)
Check for Java to be installed
- MsiExec.exe (PID: 3272)
Changes settings of System certificates
- iexplore.exe (PID: 2764)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2764)
Reads internet explorer settings
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 3384)
Reads the date of Windows installation
- chrome.exe (PID: 3932)
Creates files in the user directory
- iexplore.exe (PID: 2764)
- iexplore.exe (PID: 3384)
Reads CPU info
- iexplore.exe (PID: 3384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
39
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x71a3d988,0x71a3d998,0x71a3d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.lonelyscreen.com/download.html | C:\Program Files\Internet Explorer\iexplore.exe | lonelyscreen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,12789247222725056308,7122092396385876185,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 696 | C:\Windows\system32\svchost.exe -k LocalService | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 924 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1116 | C:\Windows\system32\MsiExec.exe -Embedding 0E8CA1E920D485533C71B7CEC7DC9F64 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1124 | "C:\Users\admin\AppData\Local\Temp\is-IBIRV.tmp\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-IBIRV.tmp\setup.exe | lonelyscreen-win-installer.tmp | ||||||||||||
User: admin Company: IMTIGER Technologies Inc. Integrity Level: HIGH Description: IMTIGER Technologies Inc. Exit code: 0 Version: 1.2.16 Modules
| |||||||||||||||
| 1236 | explorer.exe /root,C:\Users\admin\Videos | C:\Windows\explorer.exe | — | lonelyscreen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://www.lonelyscreen.com/files/lonelyscreen-win-installer.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
52 735
Read events
51 829
Write events
878
Delete events
28
Modification events
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1324) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
36
Suspicious files
52
Text files
158
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-621C71A9-52C.pma | — | |
MD5:— | SHA256:— | |||
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7a93b754-7aad-4c72-ac03-bdd039f90201.tmp | text | |
MD5:— | SHA256:— | |||
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF13e88e.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF13e85f.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 1324 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
101
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1408 | lonelyscreen-win-installer.tmp | HEAD | 301 | 50.116.44.52:80 | http://www.lonelyscreen.com/files/bonjour32.msi | US | — | — | malicious |
3680 | chrome.exe | GET | 200 | 2.16.186.56:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3e45d8dbc11db84d | unknown | compressed | 59.5 Kb | whitelisted |
2764 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFJXl5%2FOUoVICgAAAAE3h2s%3D | US | der | 471 b | whitelisted |
2764 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEA8gPY0sxYKDCgAAAAE3ij4%3D | US | der | 471 b | whitelisted |
3384 | iexplore.exe | GET | 200 | 93.184.220.66:80 | http://platform.twitter.com/widgets.js | US | text | 28.4 Kb | whitelisted |
2764 | iexplore.exe | GET | 200 | 199.232.136.157:80 | http://platform.twitter.com/widgets.js | US | text | 28.4 Kb | whitelisted |
3976 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
2764 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2764 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAnu3eMBLtnhgG7vgWYv3Pw%3D | US | der | 471 b | whitelisted |
2764 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
3680 | chrome.exe | 50.116.44.52:443 | www.lonelyscreen.com | Linode, LLC | US | unknown |
3680 | chrome.exe | 2.16.186.56:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1408 | lonelyscreen-win-installer.tmp | 50.116.44.52:80 | www.lonelyscreen.com | Linode, LLC | US | unknown |
3680 | chrome.exe | 142.250.185.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1408 | lonelyscreen-win-installer.tmp | 50.116.44.52:443 | www.lonelyscreen.com | Linode, LLC | US | unknown |
1408 | lonelyscreen-win-installer.tmp | 2.16.186.56:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1408 | lonelyscreen-win-installer.tmp | 104.90.178.254:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | unknown |
2764 | iexplore.exe | 50.116.44.52:80 | www.lonelyscreen.com | Linode, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.lonelyscreen.com |
| malicious |
clients2.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
platform.twitter.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |