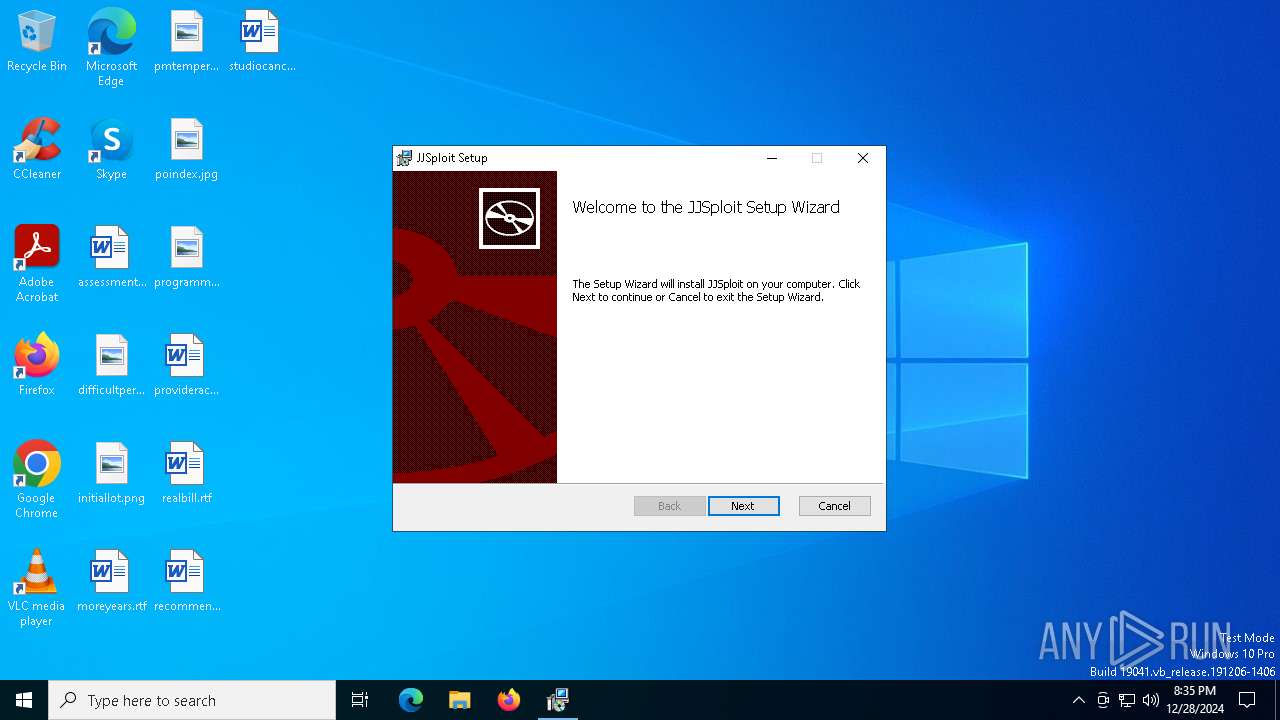
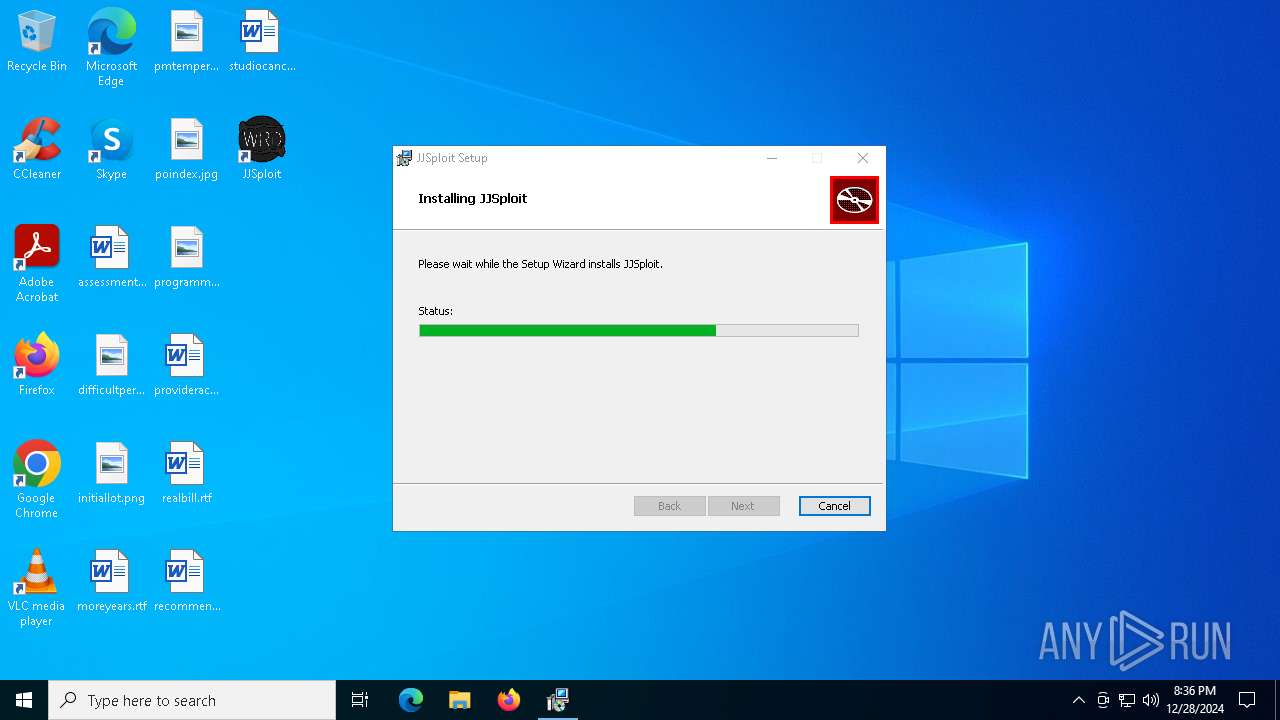
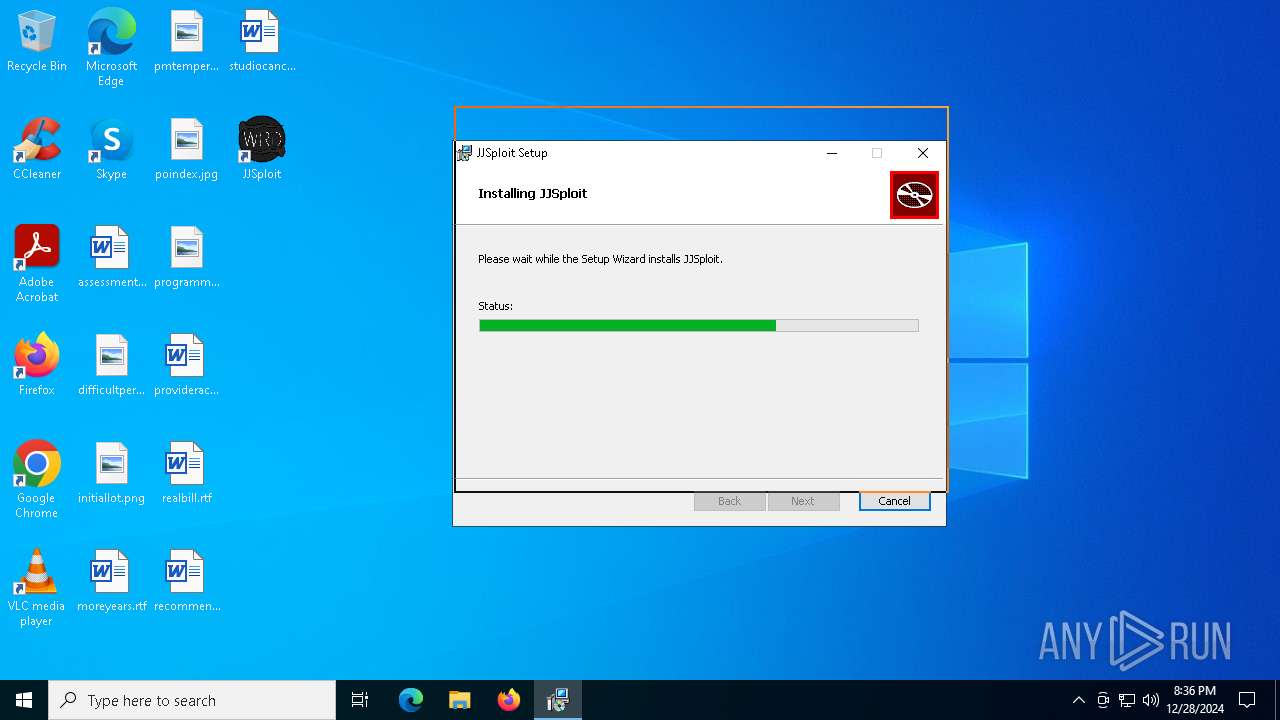
| File name: | JJSploit_8.10.15_x64_en-US.msi |
| Full analysis: | https://app.any.run/tasks/d248a989-b935-465f-aee6-c2b77c629728 |
| Verdict: | Malicious activity |
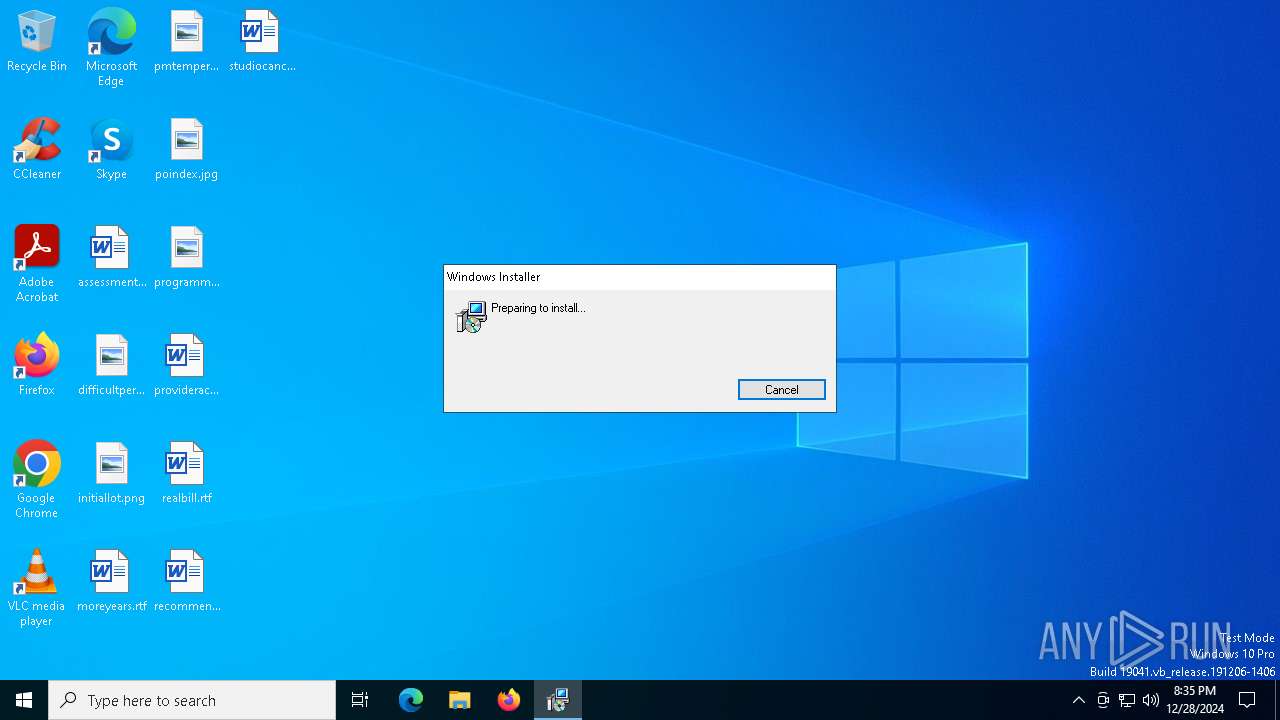
| Analysis date: | December 28, 2024, 20:35:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: JJSploit, Author: wearedevs, Keywords: Installer, Comments: This installer database contains the logic and data required to install JJSploit., Template: x64;0, Revision Number: {11619C15-6D7D-4951-9CF9-1136DA97AE6F}, Create Time/Date: Fri Dec 27 18:03:52 2024, Last Saved Time/Date: Fri Dec 27 18:03:52 2024, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | CC9626B9EB05FCC4F0A12616E2C23504 |
| SHA1: | 70EF30A35C8CD3CF2DBAFF4DCDF47C33FEDBEC85 |
| SHA256: | F468617180D78E999EAED9139FEF635874F0CB791D1CEB6642A364D7D366A32F |
| SSDEEP: | 98304:miOoqqI3cH66jZM4G9JCN+QVJAfWtkXUgAS88yuCrY5zbpEQq0Ka4PR92naE8lIb:AdRLwElkGr |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1580)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 6840)
SUSPICIOUS
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1580)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6484)
Executes as Windows Service
- VSSVC.exe (PID: 6968)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 6484)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 6484)
Manipulates environment variables
- powershell.exe (PID: 1580)
Downloads file from URI via Powershell
- powershell.exe (PID: 1580)
Starts process via Powershell
- powershell.exe (PID: 1580)
Process drops legitimate windows executable
- powershell.exe (PID: 1580)
- MicrosoftEdgeWebview2Setup.exe (PID: 5964)
- MicrosoftEdgeUpdate.exe (PID: 6840)
Executable content was dropped or overwritten
- powershell.exe (PID: 1580)
- MicrosoftEdgeWebview2Setup.exe (PID: 5964)
- MicrosoftEdgeUpdate.exe (PID: 6840)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 5964)
- MicrosoftEdgeUpdate.exe (PID: 6840)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 6840)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2996)
- MicrosoftEdgeUpdate.exe (PID: 6792)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6236)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6644)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 6840)
Potential Corporate Privacy Violation
- svchost.exe (PID: 6300)
INFO
Reads the computer name
- msiexec.exe (PID: 6484)
- msiexec.exe (PID: 6572)
- MicrosoftEdgeUpdate.exe (PID: 6792)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2996)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6236)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6644)
- MicrosoftEdgeUpdate.exe (PID: 6924)
- MicrosoftEdgeUpdate.exe (PID: 6840)
- MicrosoftEdgeUpdate.exe (PID: 6092)
- MicrosoftEdgeUpdate.exe (PID: 188)
An automatically generated document
- msiexec.exe (PID: 6332)
Disables trace logs
- powershell.exe (PID: 1580)
Checks proxy server information
- powershell.exe (PID: 1580)
- MicrosoftEdgeUpdate.exe (PID: 6924)
- MicrosoftEdgeUpdate.exe (PID: 188)
Checks supported languages
- msiexec.exe (PID: 6484)
- msiexec.exe (PID: 6572)
- MicrosoftEdgeWebview2Setup.exe (PID: 5964)
- MicrosoftEdgeUpdate.exe (PID: 6840)
- MicrosoftEdgeUpdate.exe (PID: 6792)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6236)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6644)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2996)
- MicrosoftEdgeUpdate.exe (PID: 6092)
- MicrosoftEdgeUpdate.exe (PID: 188)
- MicrosoftEdgeUpdate.exe (PID: 6924)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6332)
- msiexec.exe (PID: 6484)
Manages system restore points
- SrTasks.exe (PID: 6496)
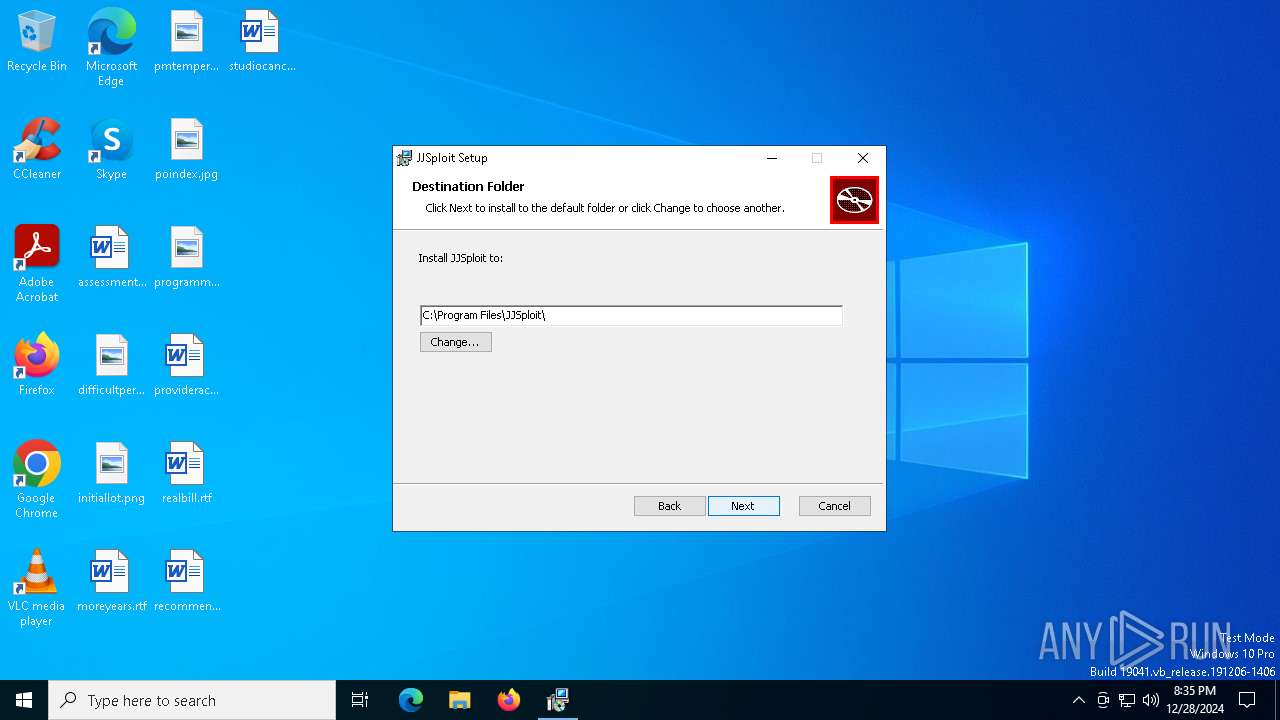
Creates a software uninstall entry
- msiexec.exe (PID: 6484)
The process uses the downloaded file
- powershell.exe (PID: 1580)
The sample compiled with english language support
- powershell.exe (PID: 1580)
- MicrosoftEdgeWebview2Setup.exe (PID: 5964)
- MicrosoftEdgeUpdate.exe (PID: 6840)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 5964)
Create files in a temporary directory
- MicrosoftEdgeWebview2Setup.exe (PID: 5964)
- MicrosoftEdgeUpdate.exe (PID: 6840)
- svchost.exe (PID: 6300)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 6840)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 6924)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 6840)
Reads the software policy settings
- MicrosoftEdgeUpdate.exe (PID: 6924)
- MicrosoftEdgeUpdate.exe (PID: 188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | JJSploit |
| Author: | wearedevs |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install JJSploit. |
| Template: | x64;0 |
| RevisionNumber: | {11619C15-6D7D-4951-9CF9-1136DA97AE6F} |
| CreateDate: | 2024:12:27 18:03:52 |
| ModifyDate: | 2024:12:27 18:03:52 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
Total processes
144
Monitored processes
18
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" -Embedding | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.43 Modules
| |||||||||||||||
| 1580 | powershell.exe -NoProfile -windowstyle hidden try { [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12 } catch {}; Invoke-WebRequest -Uri "https://go.microsoft.com/fwlink/p/?LinkId=2124703" -OutFile "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" ; Start-Process -FilePath "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" -ArgumentList ('/silent', '/install') -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2408 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.43\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.43\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.43 Modules
| |||||||||||||||
| 5536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5964 | "C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe" /silent /install | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Version: 1.3.195.43 Modules
| |||||||||||||||
| 6092 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource otherinstallcmd /sessionid "{3F375CB8-B7AF-46C4-95F1-742D23E68D1D}" /silent | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.43 Modules
| |||||||||||||||
| 6236 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.43\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.43\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.43 Modules
| |||||||||||||||
| 6300 | C:\WINDOWS\System32\svchost.exe -k netsvcs -p -s BITS | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6332 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\JJSploit_8.10.15_x64_en-US.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 578
Read events
11 417
Write events
1 118
Delete events
43
Modification events
| (PID) Process: | (6484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000001455C0136859DB0154190000281B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000B156FE136859DB0154190000281B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000B1B600146859DB0154190000281B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000001455C0136859DB0154190000281B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000AFEFFB136859DB0154190000281B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000AFEFFB136859DB0154190000281B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6484) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000DA5A6E146859DB0154190000281B0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6968) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6968) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (6968) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
204
Suspicious files
19
Text files
20
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6484 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6484 | msiexec.exe | C:\Windows\Installer\13abe3.msi | — | |
MD5:— | SHA256:— | |||
| 6484 | msiexec.exe | C:\Program Files\JJSploit\resources\luascripts\jailbreak\policeesp.lua | text | |
MD5:4F50FFCD1D3B9AE16550950CB634BA92 | SHA256:2BEB5CDC4FA2F8B7FBFE8F29DB19E0FBCA7A00D91835AB5257D84F2B042BABEF | |||
| 6484 | msiexec.exe | C:\Program Files\JJSploit\resources\luascripts\general\teleportto.lua | text | |
MD5:6F9AFF06C0F98D0410365578D2AD1DFB | SHA256:02BDF1C9CFACE7C7F710B4B538673B14B39BC824B1DB4EA4EC6376DD000535B4 | |||
| 6484 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:7B8E43EA12F5B70906A21D6DE6475D6C | SHA256:DE4BADC96285E08A5AAE909CF6F276F97B99220AEB7A72D3613F23E34329B4A6 | |||
| 6484 | msiexec.exe | C:\Program Files\JJSploit\resources\luascripts\jailbreak\removewalls.lua | text | |
MD5:00BC897C4BCBDF5660C3B1F703602F0B | SHA256:A477FFE6D4C769E2E859417AF43ED4E21107E174DF8274BC9487963659462F31 | |||
| 6484 | msiexec.exe | C:\Program Files\JJSploit\resources\luascripts\general\fly.lua | binary | |
MD5:54A3C002B2B1E311B6488B5796094457 | SHA256:4F4098A0CCAD434E7CF4684DF559858BDDD5D17768F4C8BF89B0BED072575A47 | |||
| 6484 | msiexec.exe | C:\Program Files\JJSploit\resources\luascripts\general\noclip.lua | text | |
MD5:D6A6EE15AE62C9922EBFA6DB81263288 | SHA256:9F4EFC279D94977F92BD52165DFDA141A43AFF9149E044ED44742F7EF39CFE4F | |||
| 6484 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{930a5c4d-1fed-4188-8a95-7e3d4a0adfa5}_OnDiskSnapshotProp | binary | |
MD5:7B8E43EA12F5B70906A21D6DE6475D6C | SHA256:DE4BADC96285E08A5AAE909CF6F276F97B99220AEB7A72D3613F23E34329B4A6 | |||
| 6332 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6C4A.tmp | executable | |
MD5:CFBB8568BD3711A97E6124C56FCFA8D9 | SHA256:7F47D98AB25CFEA9B3A2E898C3376CC9BA1CD893B4948B0C27CAA530FD0E34CC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
41
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6188 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3420 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.164:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.177:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6300 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |