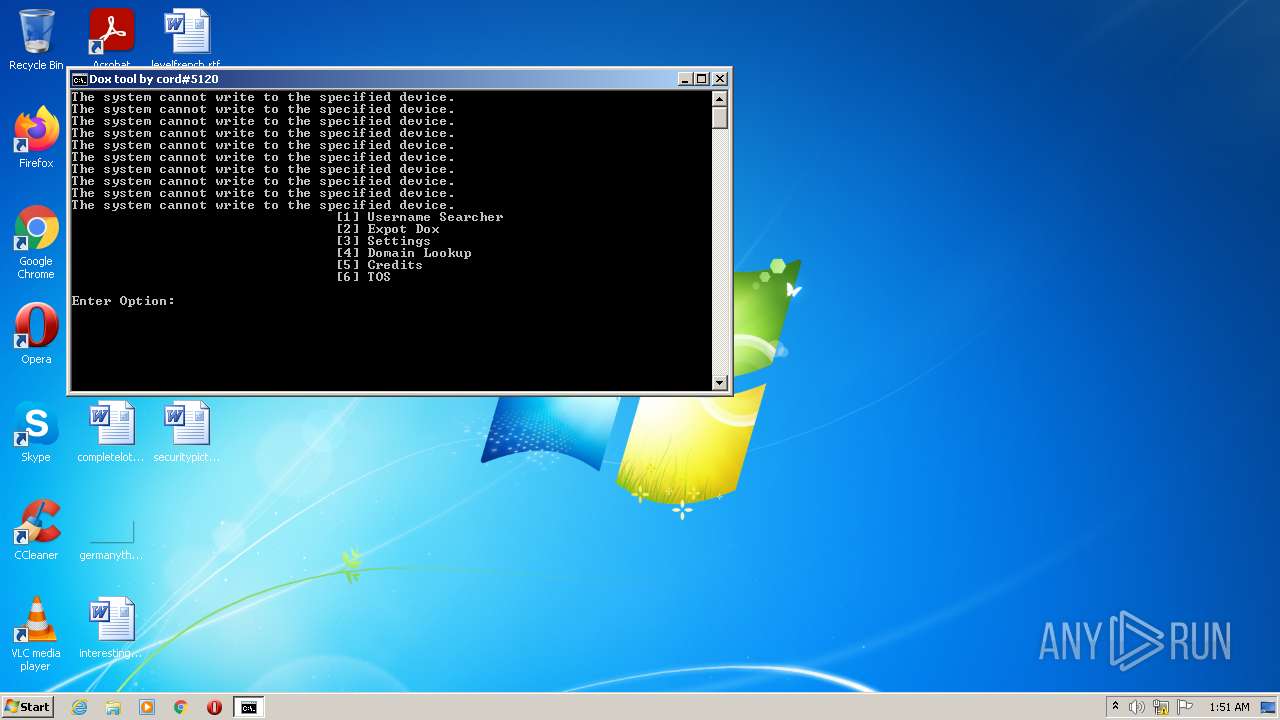
| File name: | Dox_tool_v2.bat |
| Full analysis: | https://app.any.run/tasks/3467a9ad-ff3e-4d6d-aa34-3079ca54e56d |
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2022, 01:51:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | UTF-8 Unicode text, with CRLF line terminators, with escape sequences |
| MD5: | D3DE62041584B4BCF9A4EB5C42425068 |
| SHA1: | 8204122569203DE4BA11A54A91E848AC400276D6 |
| SHA256: | F465CFDF9B36F890CAAAF3AF736D4B4197E98B409943036BD0352F3C0884E6F5 |
| SSDEEP: | 1536:t0B5LCbWnyIa6xo1WYUMygqCDjFALCfnyIEBo1pYUiygq3Dd:jD/Dd |
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1252)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 1252)
Checks supported languages
- chcp.com (PID: 1068)
- cmd.exe (PID: 1252)
INFO
Checks supported languages
- PING.EXE (PID: 2872)
- PING.EXE (PID: 2844)
- PING.EXE (PID: 2840)
- PING.EXE (PID: 3172)
- PING.EXE (PID: 4060)
- PING.EXE (PID: 3552)
- PING.EXE (PID: 2076)
- PING.EXE (PID: 2468)
- PING.EXE (PID: 1044)
- PING.EXE (PID: 2968)
- PING.EXE (PID: 4048)
- PING.EXE (PID: 2284)
- PING.EXE (PID: 2616)
- PING.EXE (PID: 760)
- PING.EXE (PID: 1500)
- PING.EXE (PID: 1472)
- PING.EXE (PID: 2888)
- PING.EXE (PID: 4084)
- PING.EXE (PID: 3092)
- PING.EXE (PID: 2376)
- PING.EXE (PID: 3448)
- PING.EXE (PID: 3960)
- PING.EXE (PID: 3196)
- PING.EXE (PID: 1000)
- PING.EXE (PID: 3876)
- PING.EXE (PID: 3012)
- PING.EXE (PID: 2836)
- PING.EXE (PID: 1260)
- PING.EXE (PID: 880)
- PING.EXE (PID: 2928)
- PING.EXE (PID: 3644)
- PING.EXE (PID: 1524)
- PING.EXE (PID: 1292)
- PING.EXE (PID: 2280)
- PING.EXE (PID: 3192)
- PING.EXE (PID: 4048)
- PING.EXE (PID: 3324)
- PING.EXE (PID: 2284)
- PING.EXE (PID: 2112)
- PING.EXE (PID: 2524)
- PING.EXE (PID: 2512)
- PING.EXE (PID: 3000)
- PING.EXE (PID: 3568)
- PING.EXE (PID: 3268)
- PING.EXE (PID: 2212)
- PING.EXE (PID: 3916)
- PING.EXE (PID: 1148)
- PING.EXE (PID: 1304)
- PING.EXE (PID: 3064)
- PING.EXE (PID: 188)
- PING.EXE (PID: 2084)
- PING.EXE (PID: 1588)
- PING.EXE (PID: 1068)
- PING.EXE (PID: 2392)
- PING.EXE (PID: 3860)
- PING.EXE (PID: 2844)
- PING.EXE (PID: 3520)
Reads the computer name
- PING.EXE (PID: 2872)
- PING.EXE (PID: 2844)
- PING.EXE (PID: 2840)
- PING.EXE (PID: 3172)
- PING.EXE (PID: 4060)
- PING.EXE (PID: 3552)
- PING.EXE (PID: 2468)
- PING.EXE (PID: 2076)
- PING.EXE (PID: 4048)
- PING.EXE (PID: 2284)
- PING.EXE (PID: 2616)
- PING.EXE (PID: 1044)
- PING.EXE (PID: 2888)
- PING.EXE (PID: 4084)
- PING.EXE (PID: 2968)
- PING.EXE (PID: 1500)
- PING.EXE (PID: 1472)
- PING.EXE (PID: 3876)
- PING.EXE (PID: 2376)
- PING.EXE (PID: 760)
- PING.EXE (PID: 3448)
- PING.EXE (PID: 3960)
- PING.EXE (PID: 3196)
- PING.EXE (PID: 3092)
- PING.EXE (PID: 1000)
- PING.EXE (PID: 1524)
- PING.EXE (PID: 2836)
- PING.EXE (PID: 1260)
- PING.EXE (PID: 880)
- PING.EXE (PID: 2928)
- PING.EXE (PID: 3012)
- PING.EXE (PID: 1292)
- PING.EXE (PID: 2280)
- PING.EXE (PID: 3644)
- PING.EXE (PID: 4048)
- PING.EXE (PID: 2284)
- PING.EXE (PID: 2524)
- PING.EXE (PID: 2512)
- PING.EXE (PID: 3000)
- PING.EXE (PID: 3192)
- PING.EXE (PID: 3064)
- PING.EXE (PID: 1148)
- PING.EXE (PID: 3268)
- PING.EXE (PID: 2112)
- PING.EXE (PID: 3916)
- PING.EXE (PID: 3568)
- PING.EXE (PID: 2212)
- PING.EXE (PID: 3324)
- PING.EXE (PID: 188)
- PING.EXE (PID: 2084)
- PING.EXE (PID: 2392)
- PING.EXE (PID: 3520)
- PING.EXE (PID: 1304)
- PING.EXE (PID: 1068)
- PING.EXE (PID: 2844)
- PING.EXE (PID: 3860)
- PING.EXE (PID: 1588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
59
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | ping 127.0.0.1 -n 1 -w 10000 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 760 | ping 127.0.0.1 -n 1 -w 10000 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | ping 127.0.0.1 -n 1 -w 10000 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1000 | ping 127.0.0.1 -n 1 -w 10000 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | ping 127.0.0.1 -n 1 -w 10000 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1068 | chcp 65001 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1068 | ping 127.0.0.1 -n 1 -w 10000 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1148 | ping 127.0.0.1 -n 1 -w 10000 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Dox_tool_v2.bat" " | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1260 | ping 127.0.0.1 -n 1 -w 10000 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 066
Read events
8 066
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1252 | cmd.exe | C:\Users\admin\AppData\Local\Temp\nu1 | text | |
MD5:D38306034A39FBDFDAC172946D5EF53F | SHA256:2B06CDF30ADE079C57F6E8EC16FA27563855265463BEDE417A2DD63A631B6A21 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report