| File name: | phish_alert_sp2_2.0.0.0 - 2022-01-24T124219.332.eml |
| Full analysis: | https://app.any.run/tasks/35b1bff1-db03-4bdd-9124-48f949ab1bf3 |
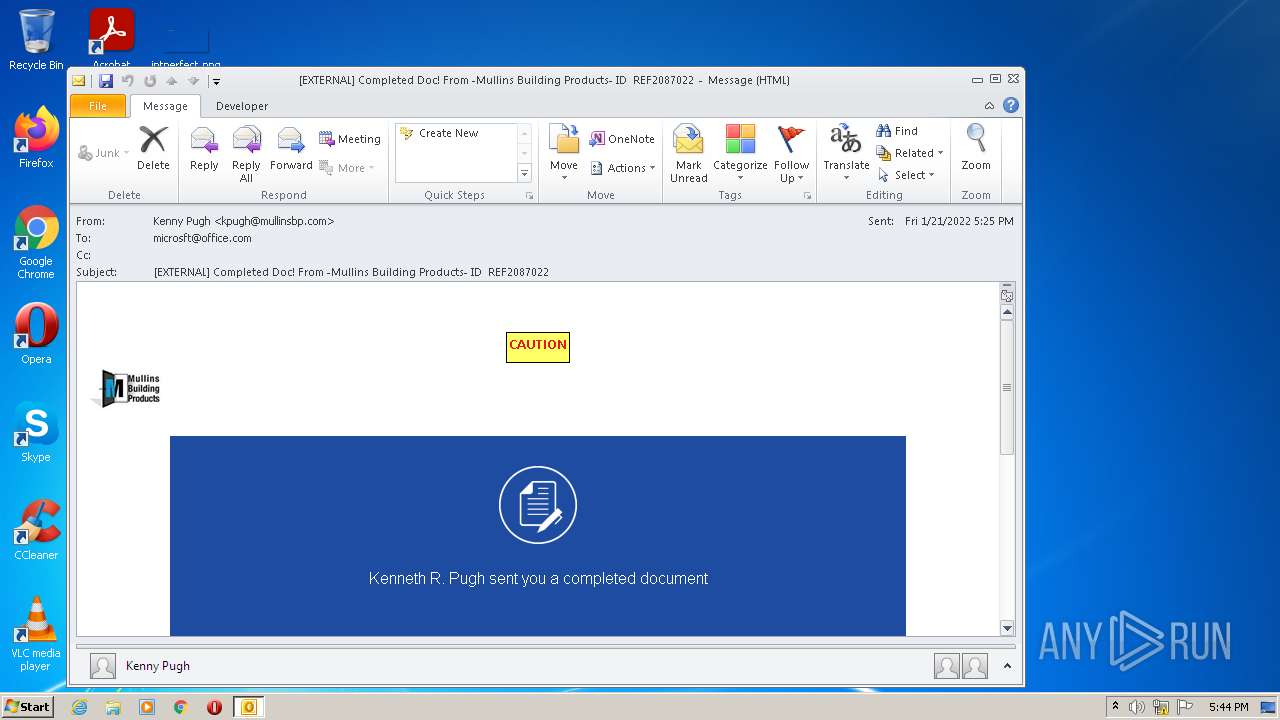
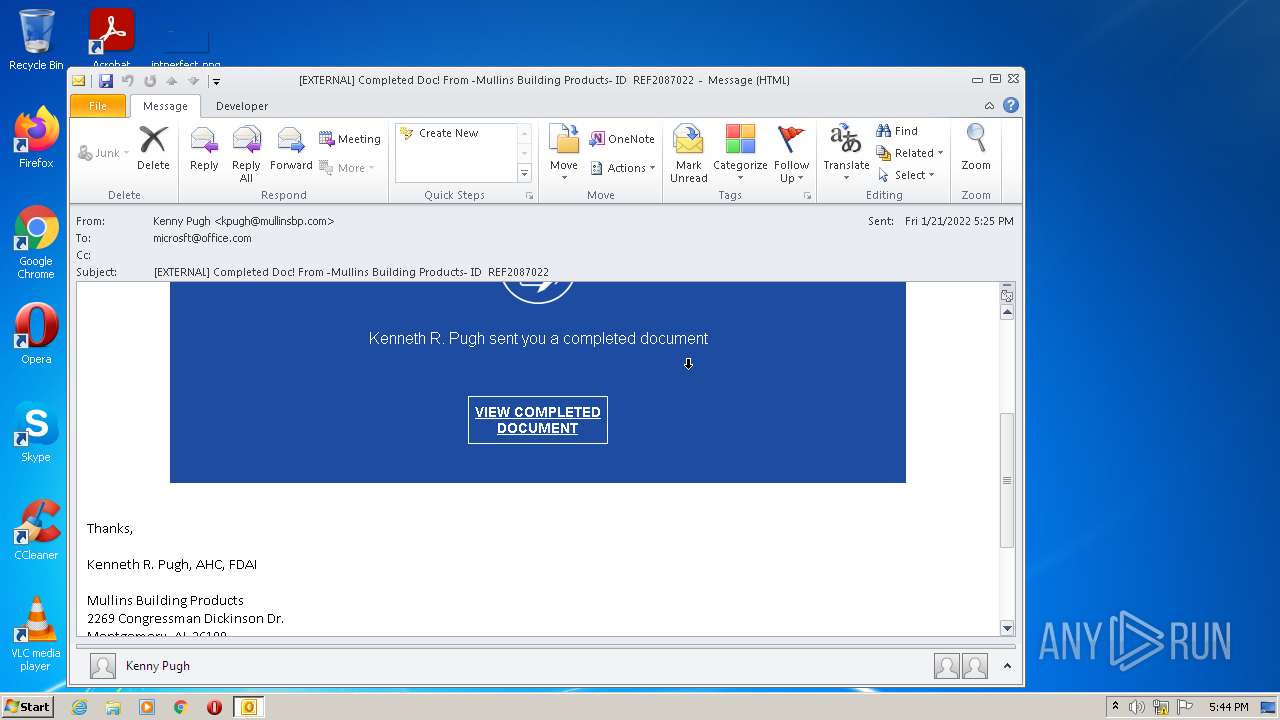
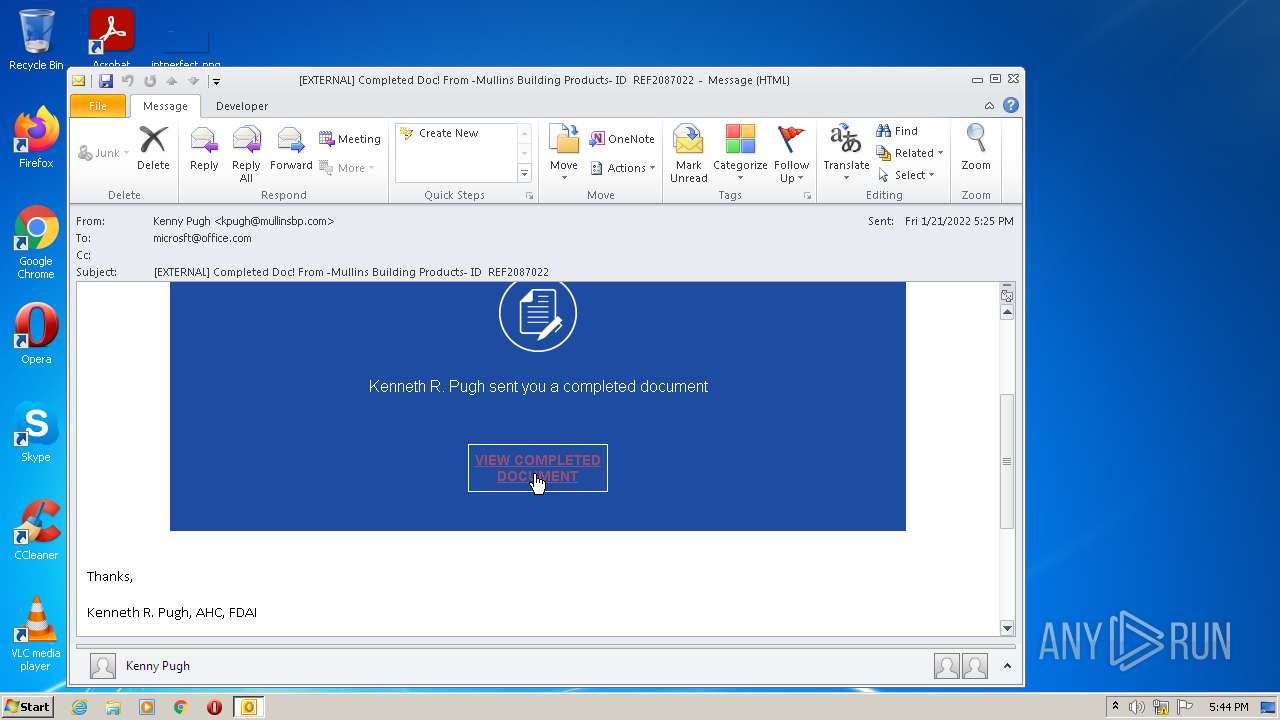
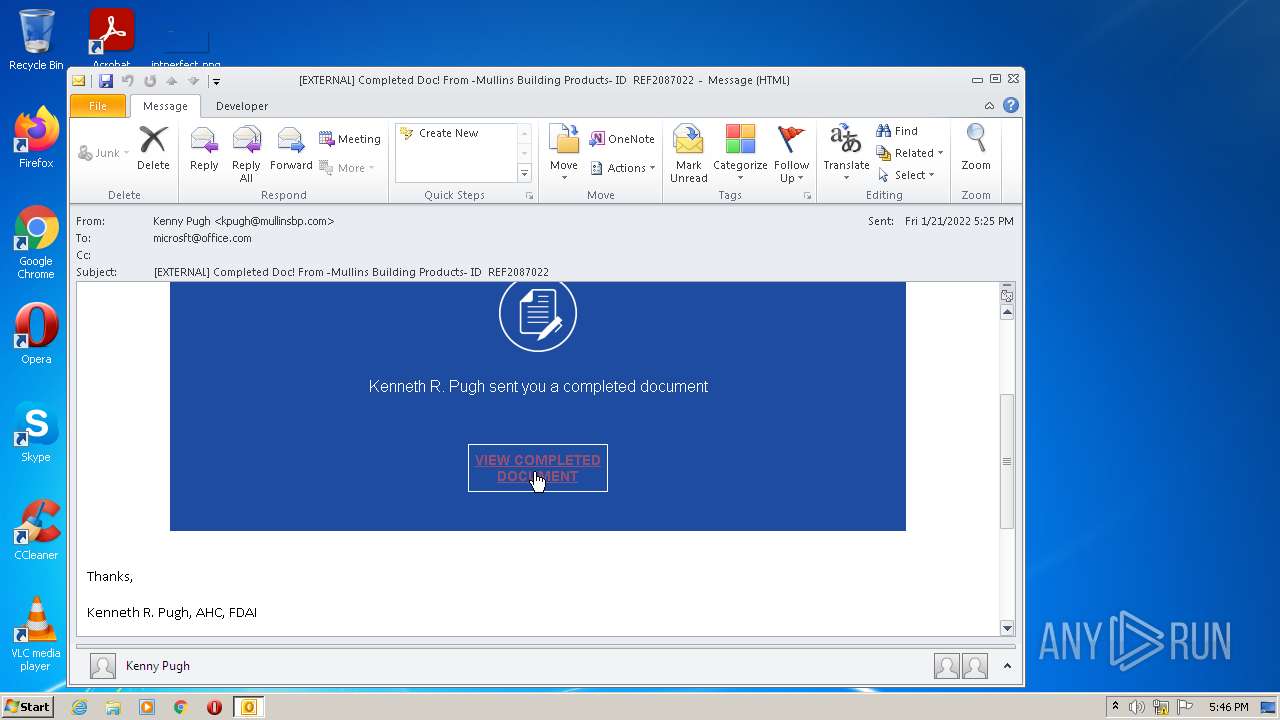
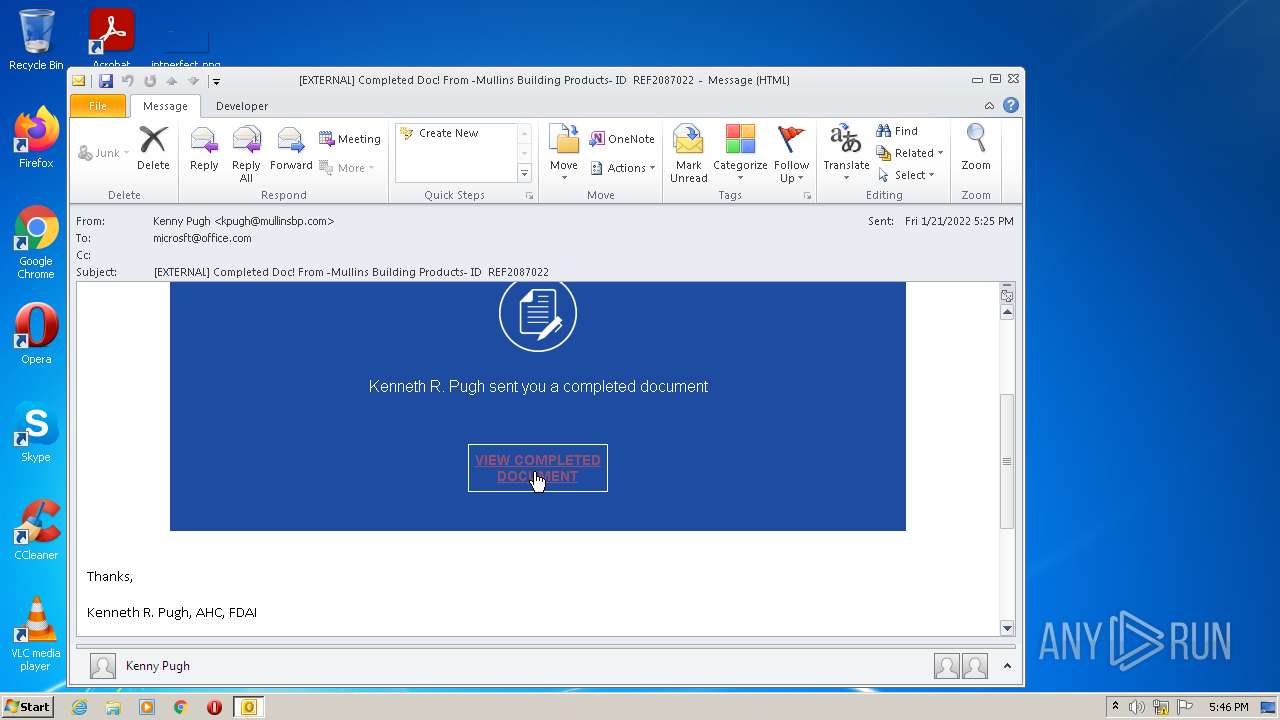
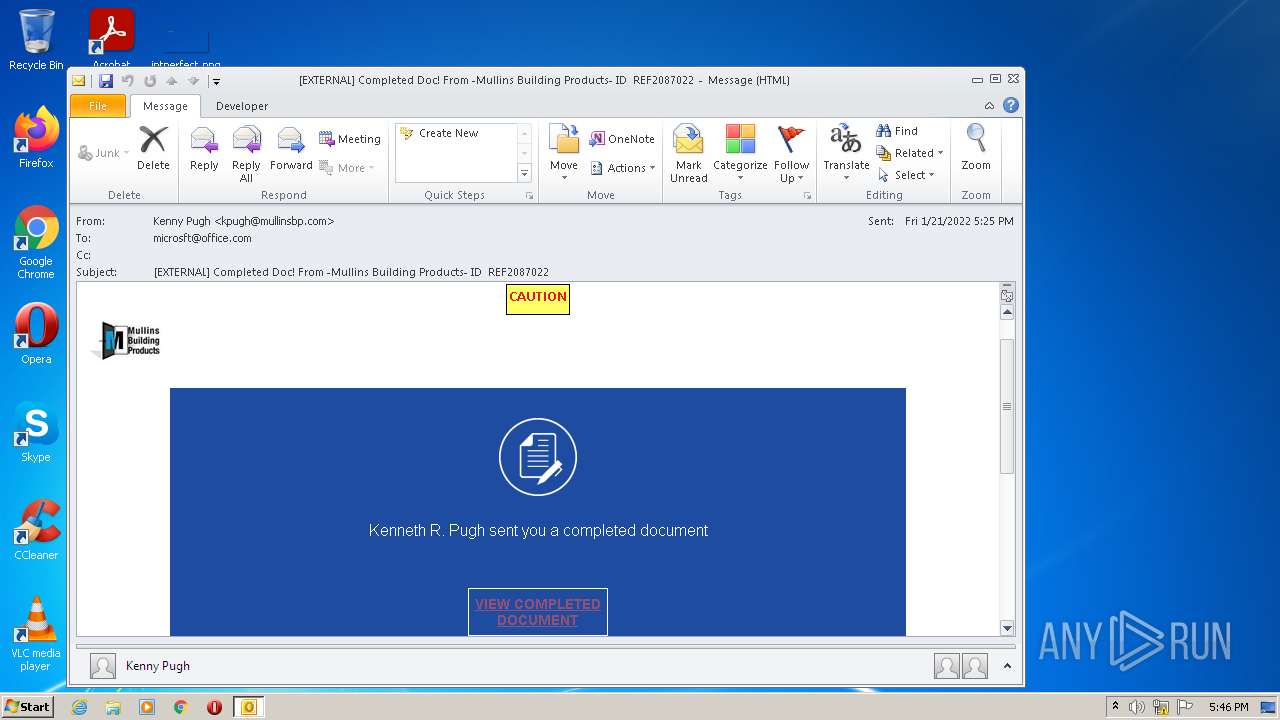
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 17:44:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | A986246E0534DC0DDCF813FC65F4AFF5 |
| SHA1: | 6E59C7A76EC47B865DE1FEDCB31F512C45A2A8F9 |
| SHA256: | F44DFC10F2B25716788B12E1B666BF4C6E5625BDFDC1F06CDB1D4867DE45D640 |
| SSDEEP: | 1536:zZ/1jUa1YiOQN93P+VpMJqCekagyiF4aMbRrg2v/3ReYMW:zZ/1wa1YiOQNVPtJlekbqbRrZv/3UXW |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 2288)
Searches for installed software
- OUTLOOK.EXE (PID: 2288)
Reads the computer name
- OUTLOOK.EXE (PID: 2288)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2288)
INFO
Manual execution by user
- chrome.exe (PID: 2540)
Checks supported languages
- chrome.exe (PID: 3752)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 700)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 1444)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 1864)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 3752)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 2096)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 1436)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 1508)
- chrome.exe (PID: 1168)
- chrome.exe (PID: 1760)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 1808)
- chrome.exe (PID: 3608)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 1000)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 636)
- chrome.exe (PID: 1800)
- chrome.exe (PID: 1784)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 3452)
Reads the computer name
- chrome.exe (PID: 2696)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 2252)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 1508)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 1760)
- chrome.exe (PID: 636)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 3452)
Application launched itself
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 636)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 3452)
Reads the hosts file
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 636)
- chrome.exe (PID: 3452)
- chrome.exe (PID: 3200)
Changes default file association
- chrome.exe (PID: 2540)
Reads settings of System Certificates
- chrome.exe (PID: 2696)
- chrome.exe (PID: 2136)
Reads the date of Windows installation
- chrome.exe (PID: 1508)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
84
Monitored processes
45
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
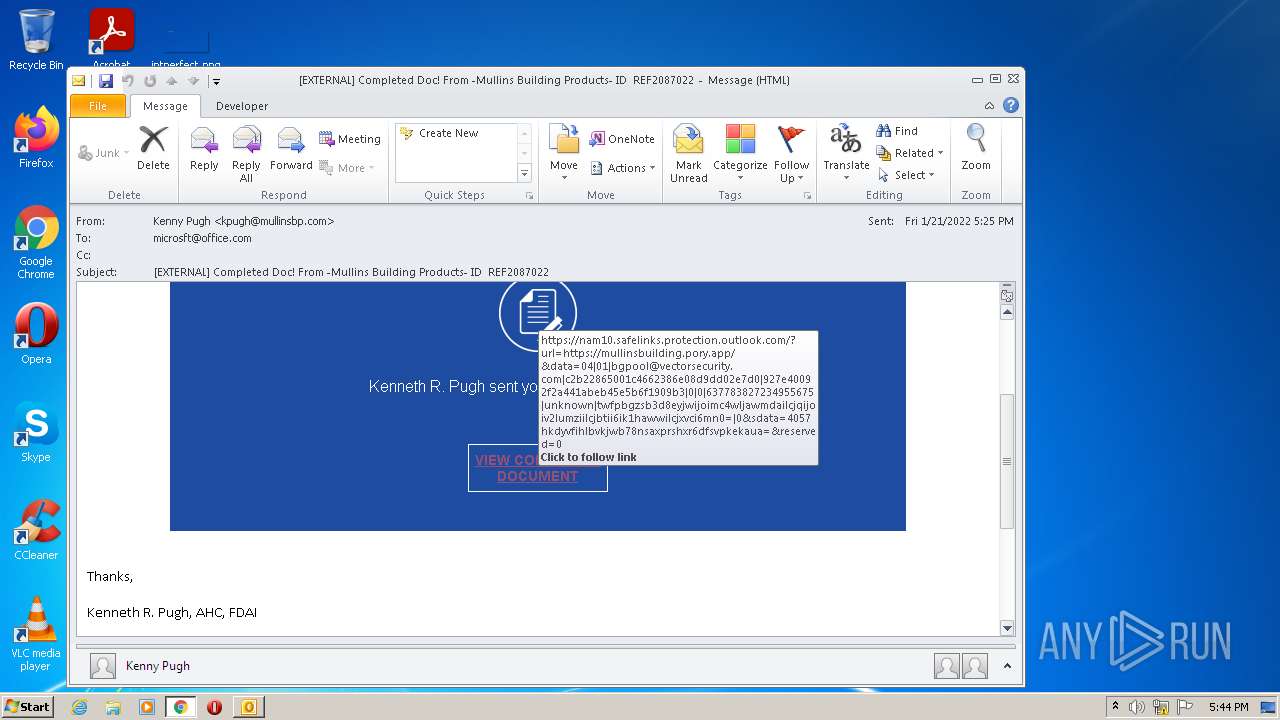
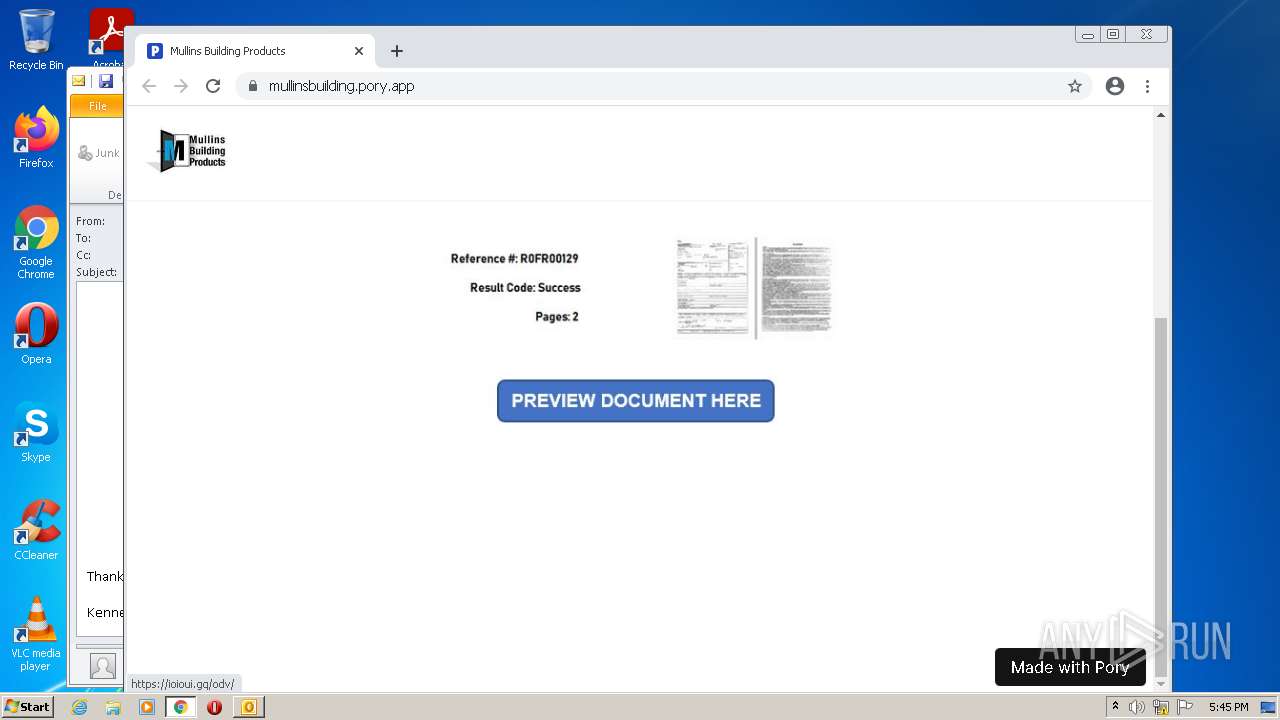
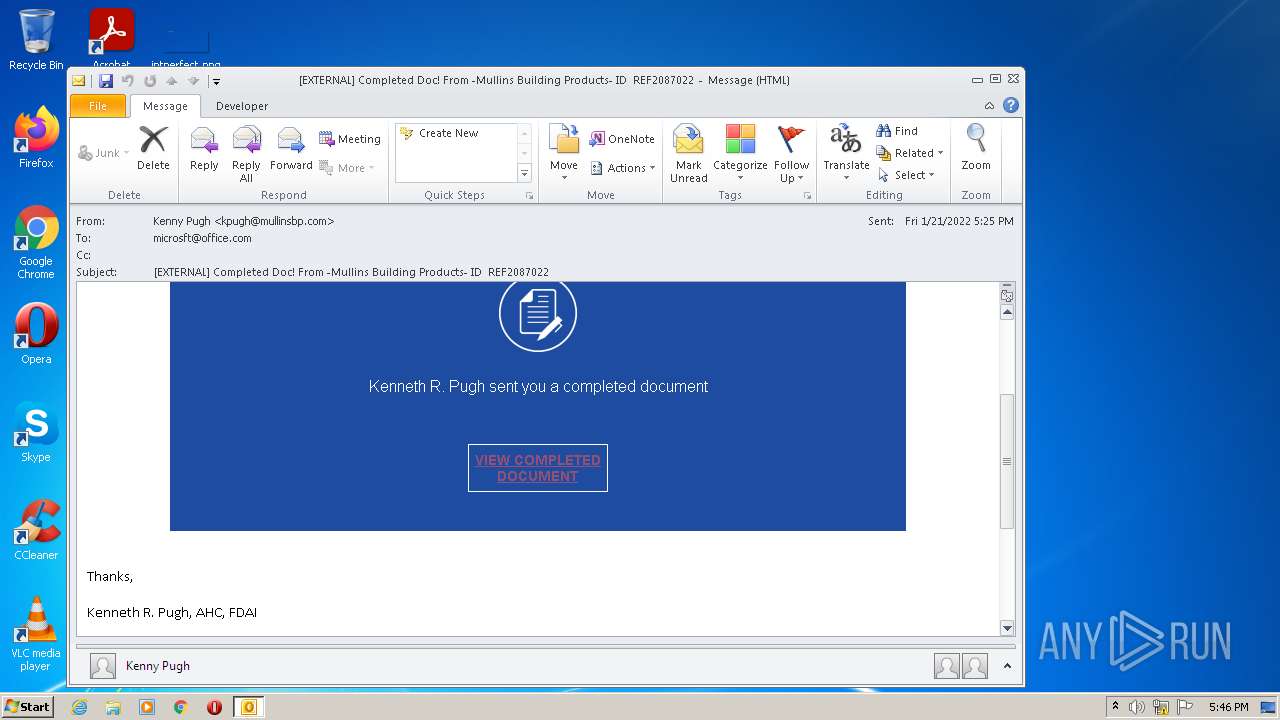
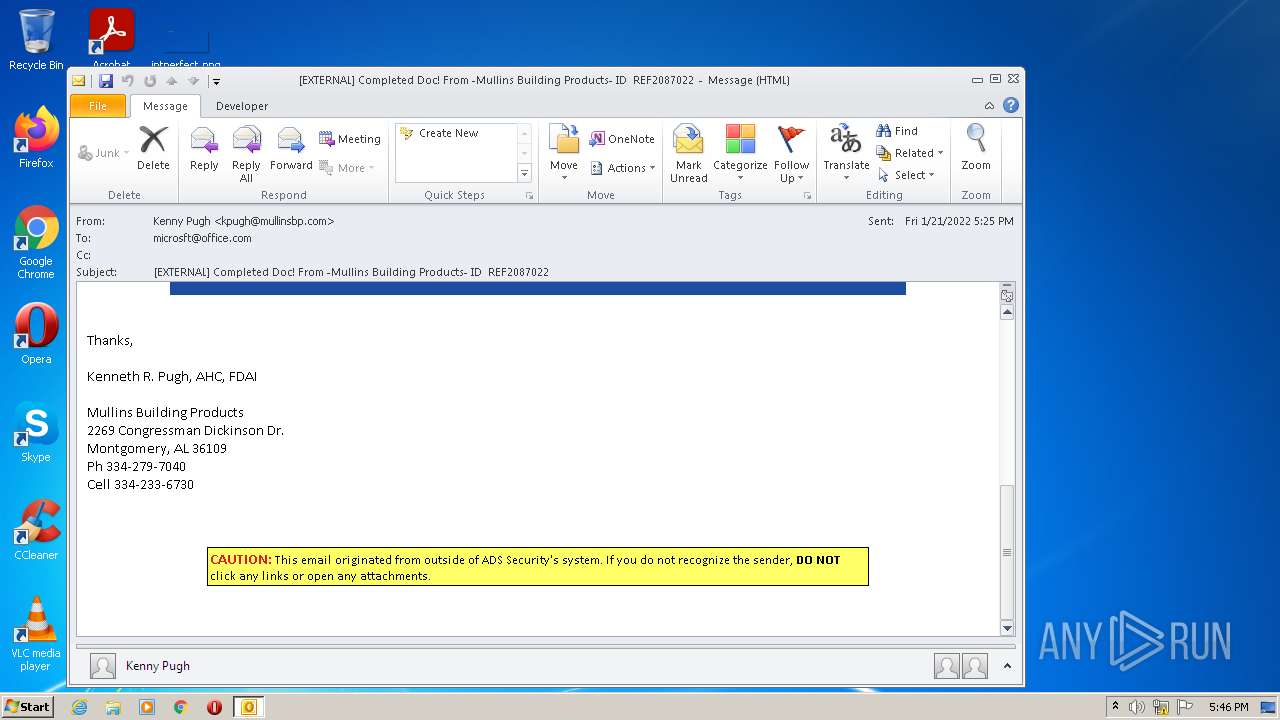
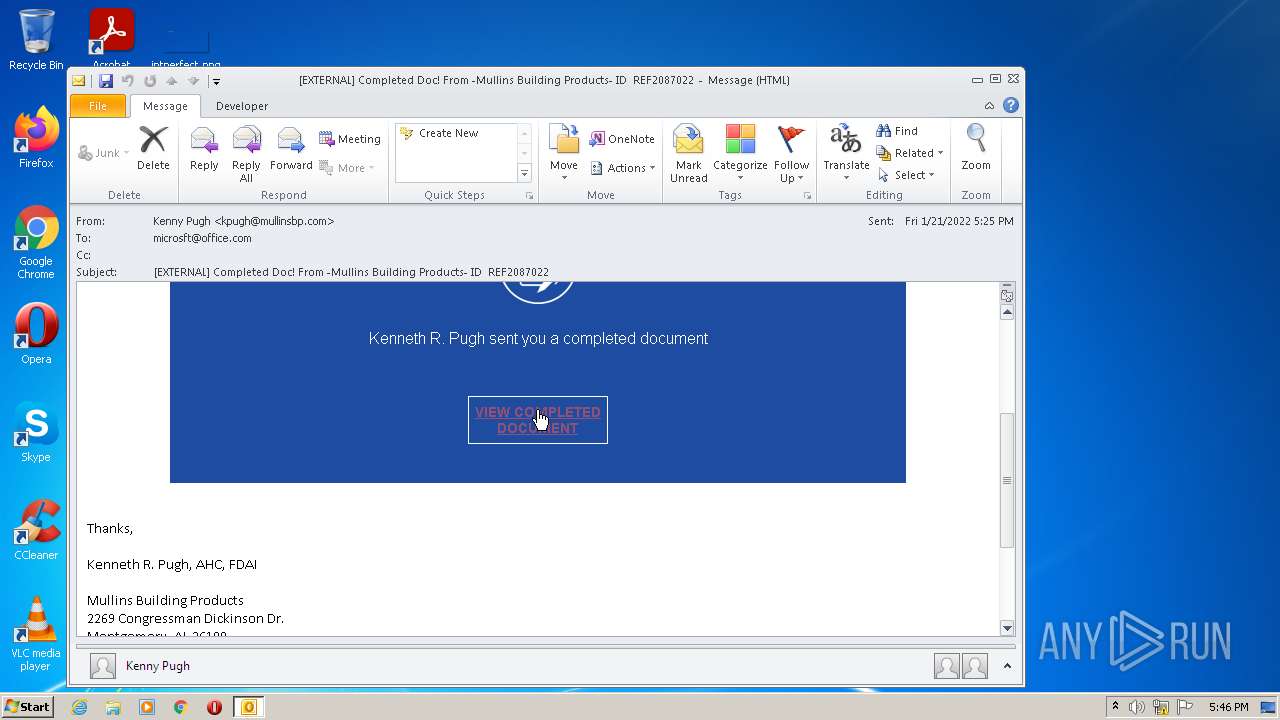
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --single-argument https://nam10.safelinks.protection.outlook.com/?url=https%3A%2F%2Fmullinsbuilding.pory.app%2F&data=04%7C01%7Cbgpool%40vectorsecurity.com%7Cc2b22865001c4662386e08d9dd02e7d0%7C927e40092f2a441abeb45e5b6f1909b3%7C0%7C0%7C637783827234955675%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C0&sdata=4057hKDyVfiHlBvkjwb78nsaxPRsHXr6dFSVPKEKAuA%3D&reserved=0 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6919d988,0x6919d998,0x6919d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1064 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,924970079887997232,7444838911236217365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --single-argument https://nam10.safelinks.protection.outlook.com/?url=https%3A%2F%2Fmullinsbuilding.pory.app%2F&data=04%7C01%7Cbgpool%40vectorsecurity.com%7Cc2b22865001c4662386e08d9dd02e7d0%7C927e40092f2a441abeb45e5b6f1909b3%7C0%7C0%7C637783827234955675%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C0&sdata=4057hKDyVfiHlBvkjwb78nsaxPRsHXr6dFSVPKEKAuA%3D&reserved=0 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,924970079887997232,7444838911236217365,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3288 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,17524753977986483709,14021339972605514642,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,924970079887997232,7444838911236217365,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,924970079887997232,7444838911236217365,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
20 073
Read events
19 268
Write events
781
Delete events
24
Modification events
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2288) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
79
Text files
179
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE6C9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2288 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EEE57E-9EC.pma | — | |
MD5:— | SHA256:— | |||
| 2288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7FCD002C.dat | image | |
MD5:— | SHA256:— | |||
| 2288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_62DD007A3AE23B4EAE3FFA322B839090.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 2288 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2FC68A3D.dat | image | |
MD5:— | SHA256:— | |||
| 2288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{94D44678-B138-49CA-AE91-854C416D0092}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 2288 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_6CF295D2BADE744AA4C133547BBBF6DC.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
58
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | — | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | — | — | whitelisted |
2136 | chrome.exe | GET | — | 74.125.104.201:80 | http://r4---sn-ixh7rn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=196.244.192.6&mm=28&mn=sn-ixh7rn76&ms=nvh&mt=1643046020&mv=m&mvi=4&pl=27&rmhost=r3---sn-ixh7rn76.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
2136 | chrome.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 556 b | whitelisted |
2136 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f098b311d81d9a28 | US | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2288 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2696 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 142.250.184.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 142.250.181.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 142.250.181.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2696 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
2696 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2136 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
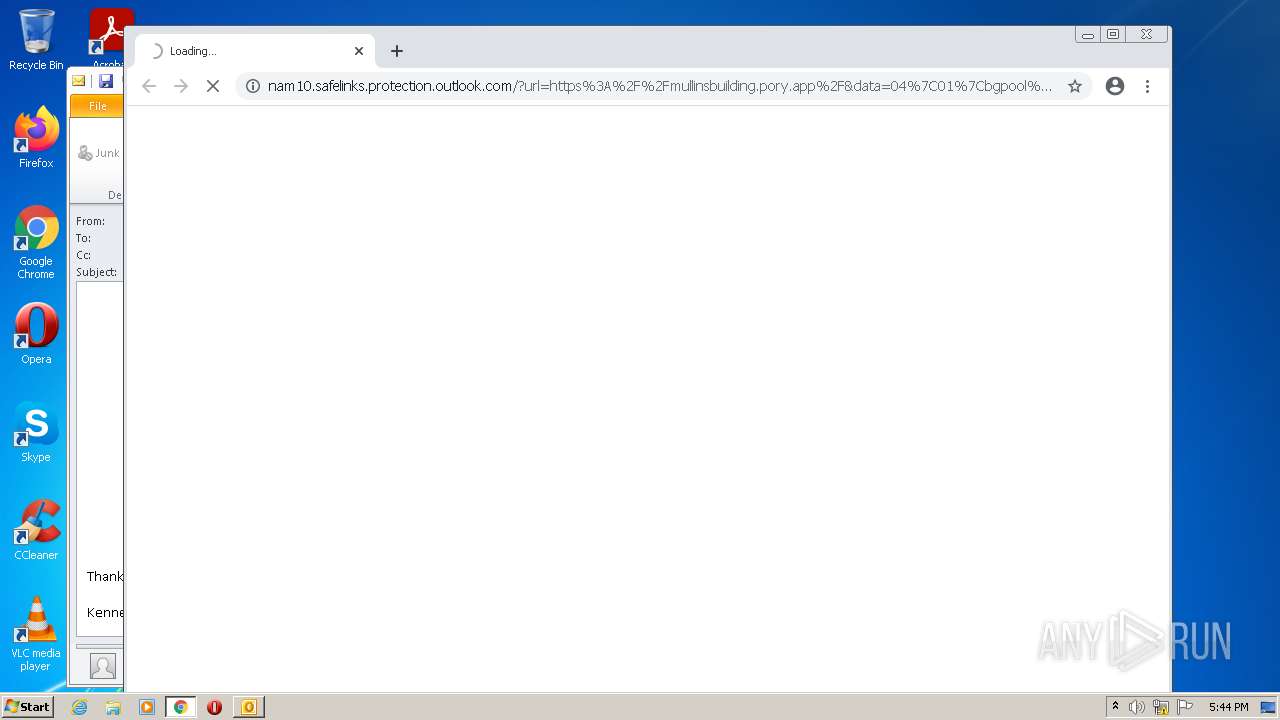
2136 | chrome.exe | 104.47.70.28:443 | nam10.safelinks.protection.outlook.com | Microsoft Corporation | US | suspicious |
2136 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
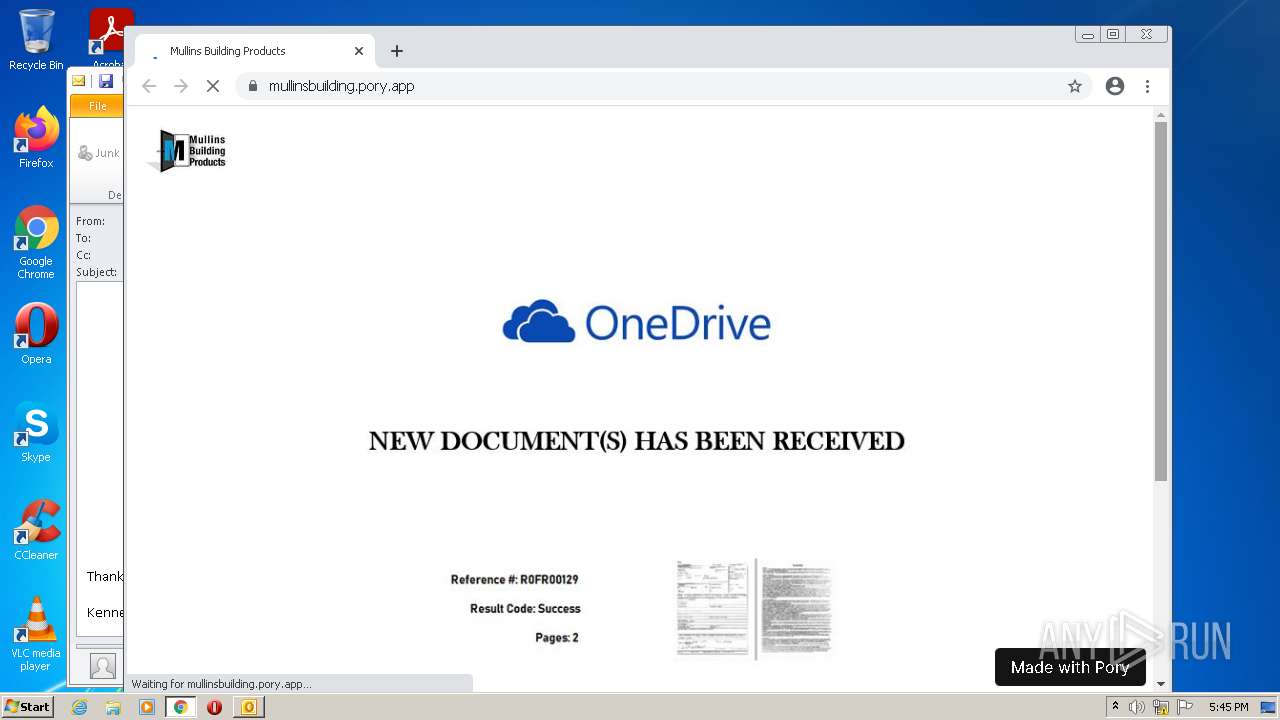
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
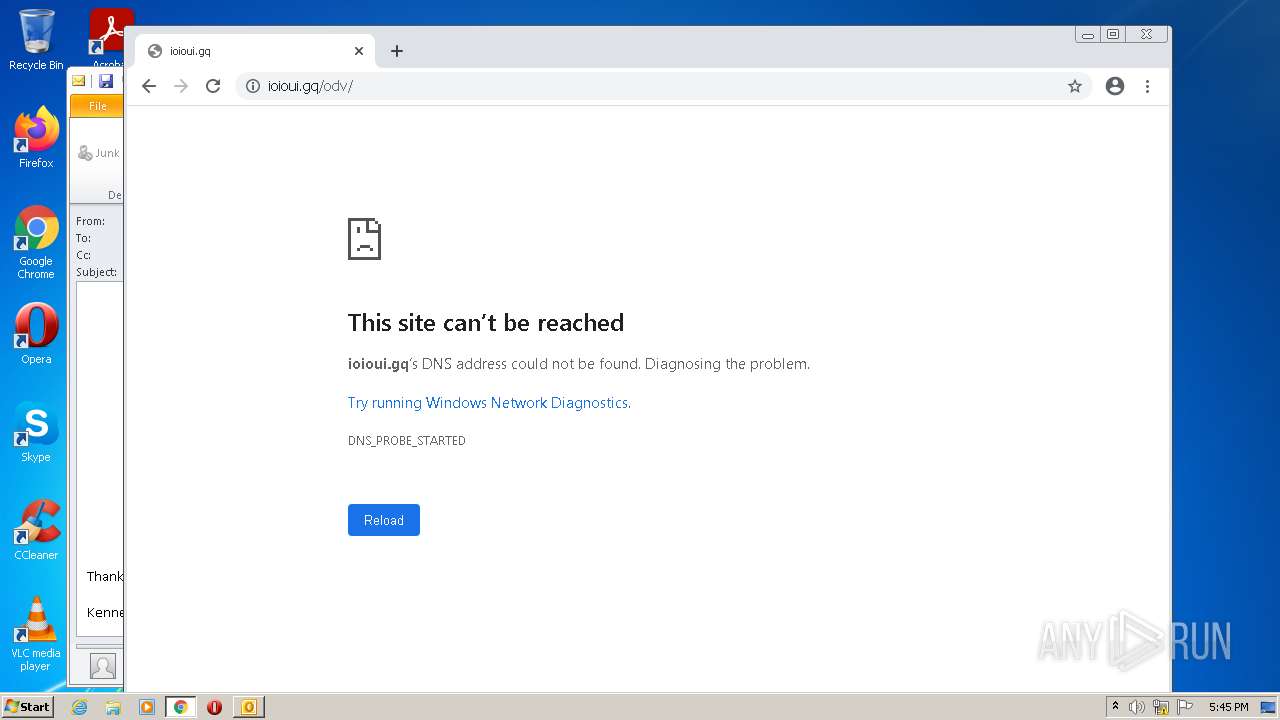
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |