| File name: | Fab_x64.exe |
| Full analysis: | https://app.any.run/tasks/559acba5-dcd1-4c25-bc98-4a1209ef4fd9 |
| Verdict: | Malicious activity |
| Analysis date: | September 08, 2024, 19:27:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 970B29465D8118BF8038A42C92BF90DF |
| SHA1: | B22D955115F4142198A288550D3592927B1B9460 |
| SHA256: | F44A6998DBC040397C68348FE3F2925C92FB9370A9BB554B6BB4A168E4EB5E89 |
| SSDEEP: | 49152:+Ysfoqnq9daZsz94PrFw+kpBiLXQB2VqcIujPWsXLkuwCOMSebnnZ0JAYhdV:ofmgIujOsXQuSMSebnZMAYhX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Fab_x64.exe (PID: 3728)
- OfficeC2RClient.exe (PID: 6852)
Reads the date of Windows installation
- Fab_x64.exe (PID: 3728)
INFO
Checks supported languages
- Fab_x64.exe (PID: 3728)
- OfficeC2RClient.exe (PID: 6852)
Reads mouse settings
- Fab_x64.exe (PID: 3728)
Create files in a temporary directory
- Fab_x64.exe (PID: 3728)
- OfficeC2RClient.exe (PID: 6852)
The process uses the downloaded file
- Fab_x64.exe (PID: 3728)
Reads the computer name
- Fab_x64.exe (PID: 3728)
- OfficeC2RClient.exe (PID: 6852)
Process checks computer location settings
- Fab_x64.exe (PID: 3728)
- OfficeC2RClient.exe (PID: 6852)
The process uses AutoIt
- Fab_x64.exe (PID: 3728)
Reads Microsoft Office registry keys
- OfficeC2RClient.exe (PID: 6852)
Checks proxy server information
- OfficeC2RClient.exe (PID: 6852)
Creates files or folders in the user directory
- OfficeC2RClient.exe (PID: 6852)
Reads the software policy settings
- OfficeC2RClient.exe (PID: 6852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2010:04:16 07:47:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 9 |
| CodeSize: | 613376 |
| InitializedDataSize: | 258560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d47c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.9.0.0 |
| ProductVersionNumber: | 1.9.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 1.9.0.0 |
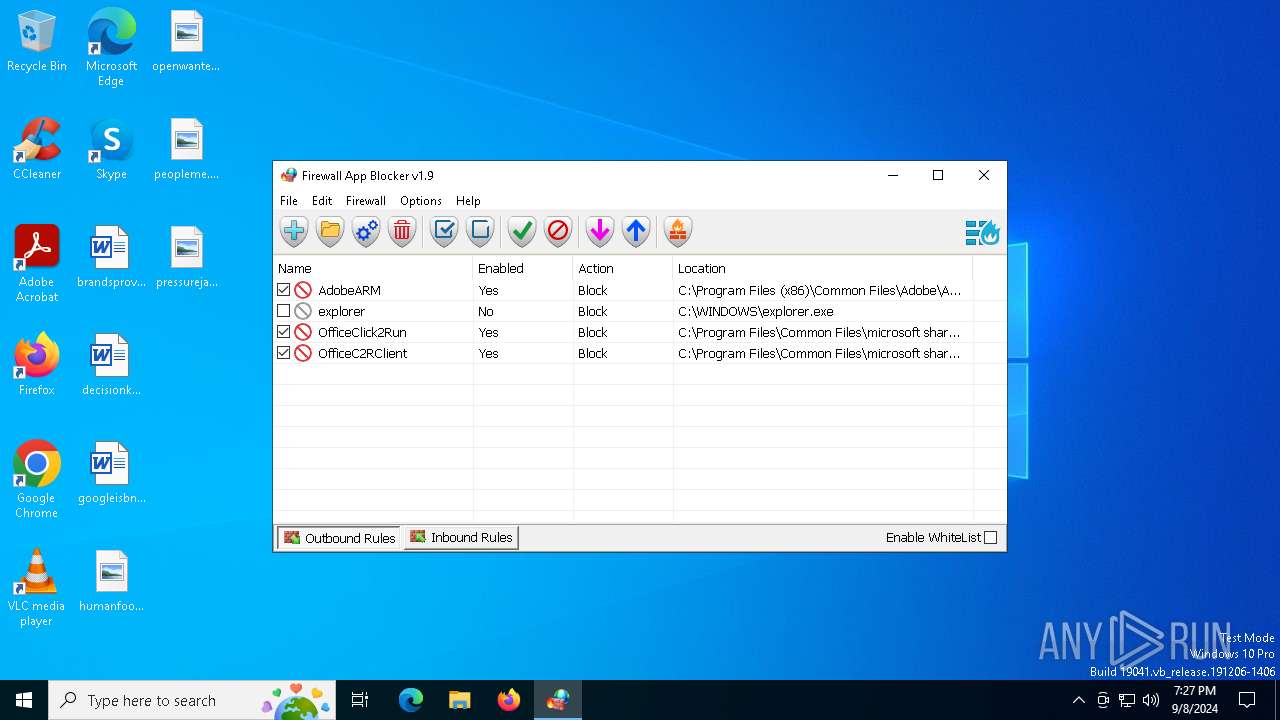
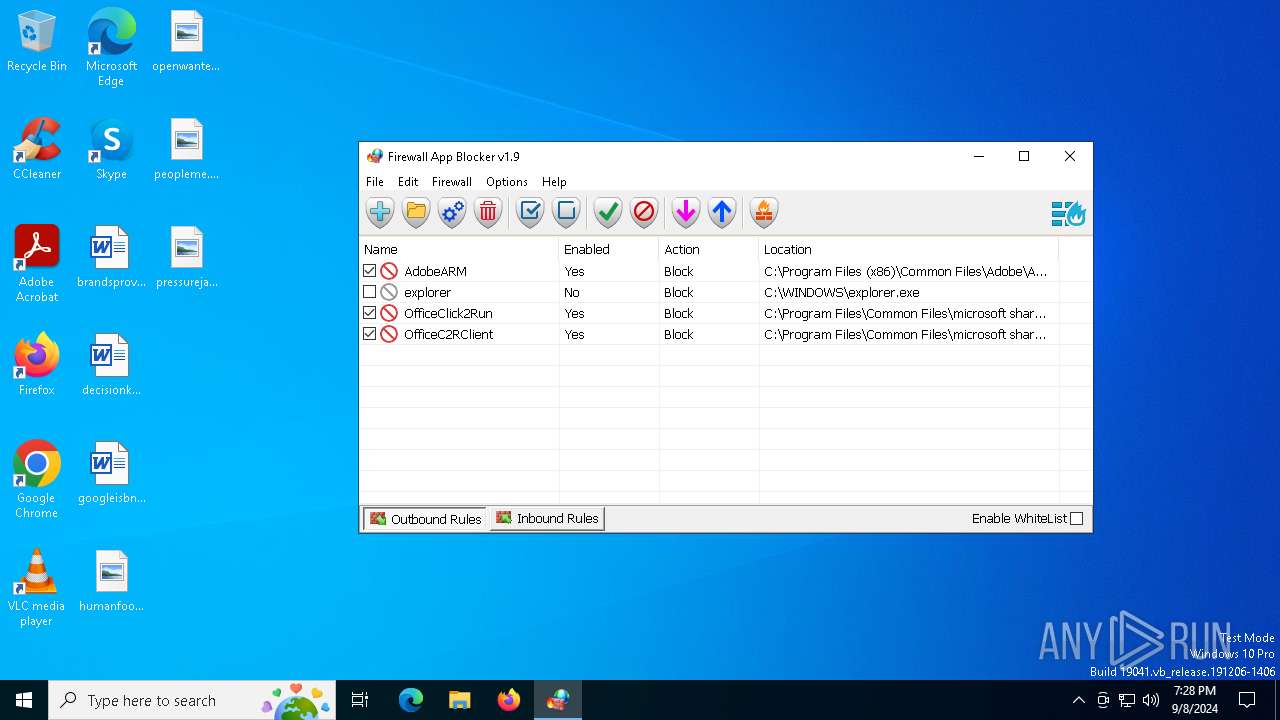
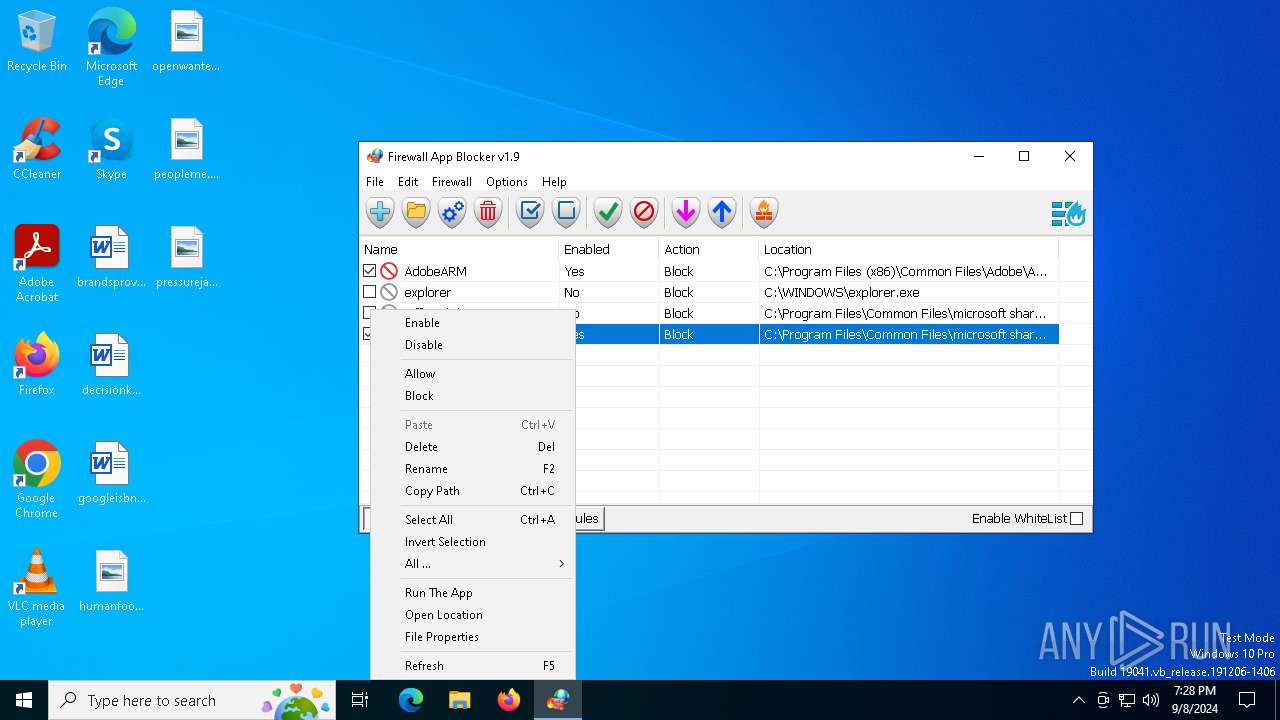
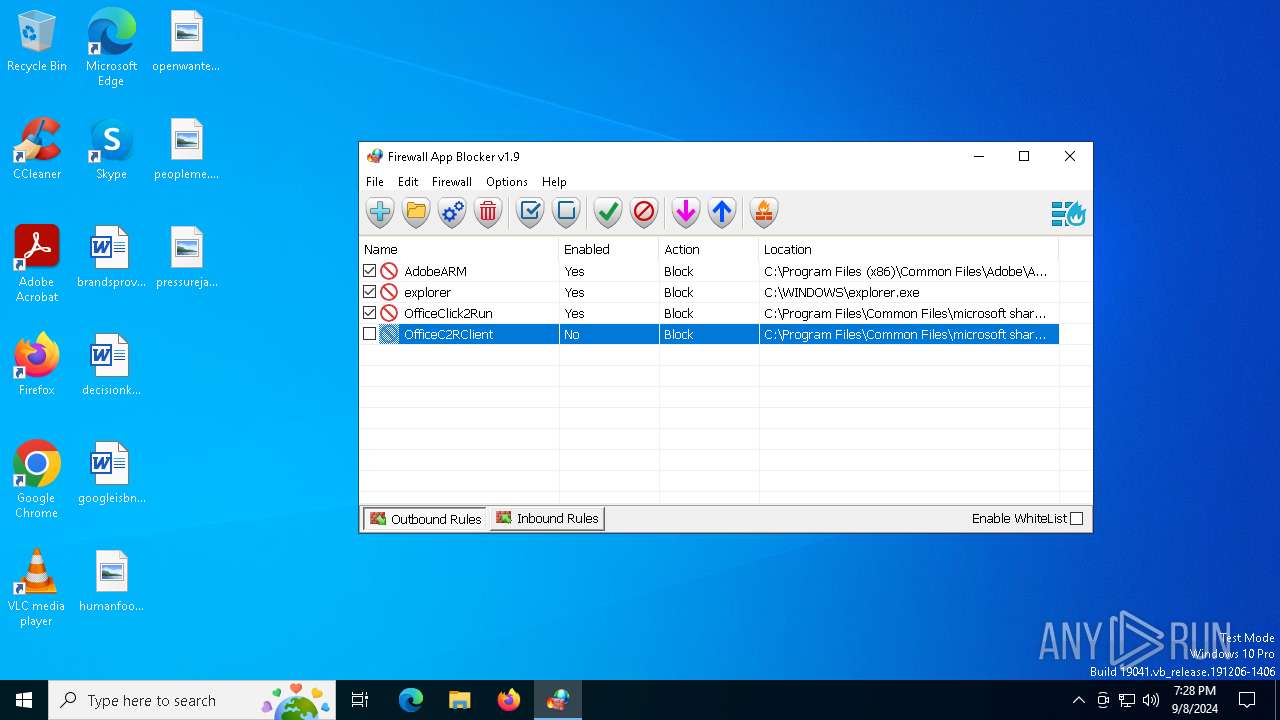
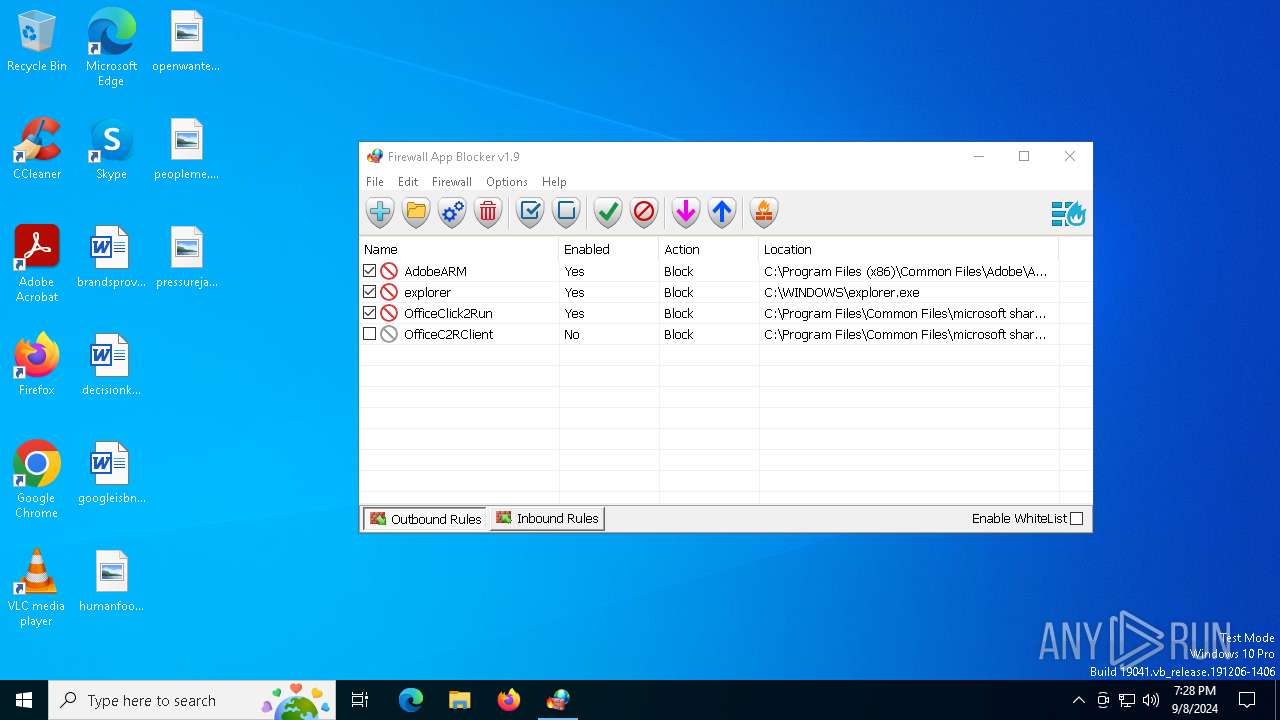
| Comments: | Firewall App Blocker |
| FileDescription: | Firewall App Blocker |
| LegalCopyright: | Copyright © 2012-2022 www.sordum.org All Rights Reserved. |
| Coder: | By BlueLife |
| CompanyName: | www.sordum.org |
Total processes
131
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | "C:\Users\admin\AppData\Local\Temp\Fab_x64.exe" | C:\Users\admin\AppData\Local\Temp\Fab_x64.exe | — | explorer.exe | |||||||||||
User: admin Company: www.sordum.org Integrity Level: MEDIUM Description: Firewall App Blocker Exit code: 3221226540 Version: 1.9.0.0 Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\Fab_x64.exe" | C:\Users\admin\AppData\Local\Temp\Fab_x64.exe | explorer.exe | ||||||||||||
User: admin Company: www.sordum.org Integrity Level: HIGH Description: Firewall App Blocker Exit code: 0 Version: 1.9.0.0 Modules
| |||||||||||||||
| 6852 | "C:\Program Files\Common Files\microsoft shared\ClickToRun\OfficeC2RClient.exe" | C:\Program Files\Common Files\microsoft shared\ClickToRun\OfficeC2RClient.exe | Fab_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Click-to-Run Client Exit code: 1 Version: 16.0.16026.20140 Modules
| |||||||||||||||
Total events
2 382
Read events
2 364
Write events
17
Delete events
1
Modification events
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ru-ru |
Value: 2 | |||
| (PID) Process: | (6852) OfficeC2RClient.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | tr-tr |
Value: 2 | |||
Executable files
0
Suspicious files
3
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | Fab_x64.exe | C:\Users\admin\AppData\Local\Temp\aut9E5B.tmp | binary | |
MD5:D00A13063A731530EF544E2E99FDE5D7 | SHA256:BF8A82EC4036860099164BBAB67EFCD6AF372D6B0F236A7B9542AB5D6AE4F2EB | |||
| 6852 | OfficeC2RClient.exe | C:\Users\admin\AppData\Local\Temp\DESKTOP-JGLLJLD-20240908-1928.log | text | |
MD5:B0F6F72E7F0FC1D844A75D06FD982C78 | SHA256:D21CFA1BA51FB55C3E040E9A775A3786C6435EA8B086180D9A3CD0E2631653B4 | |||
| 6852 | OfficeC2RClient.exe | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\436979C4-FC5E-4FB0-9E1A-1D8B1D0F4463 | xml | |
MD5:7F63A788B22D09A88B5C9988B42C4A17 | SHA256:F55BA3EB23943EC67AD2D7386FE5810A25F64866CB5FBFCB11DE58BD903FF29D | |||
| 3728 | Fab_x64.exe | C:\Users\admin\AppData\Local\Temp\3g7a2p8g.tmp | text | |
MD5:024A4E333E14D21B6E9D42C13E0E5031 | SHA256:5FBEBA760FAF061D6A96F8832337BA777B312B8954D50E452520616C502DB668 | |||
| 3728 | Fab_x64.exe | C:\Users\admin\AppData\Local\Temp\aut9E6D.tmp | binary | |
MD5:B317C1848DA062443BD5C817D50FD2F0 | SHA256:5DA50BB4C9A49B28F09DBCC67CCC77824400A8E0400F3B761310D7E18CC1FD65 | |||
| 3728 | Fab_x64.exe | C:\Users\admin\AppData\Local\Temp\aut9E6C.tmp | binary | |
MD5:057B345B27676D8574E2DDA134802A58 | SHA256:498D306CEC1E13E88198B16119898FFCA84964C3C637BDFFA52474E56ADDE7B8 | |||
| 3728 | Fab_x64.exe | C:\Users\admin\AppData\Local\Temp\Fab.ini | text | |
MD5:D1BF21B3FFFC02DF3AD46977E44B153B | SHA256:753CB1C7514CE5A67B25FDCECD751D4C5A17497D559368A9AACABFECDD7B7B7E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
31
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6056 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
2148 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
2108 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2148 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6056 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6412 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6056 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6056 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6852 | OfficeC2RClient.exe | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2108 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |