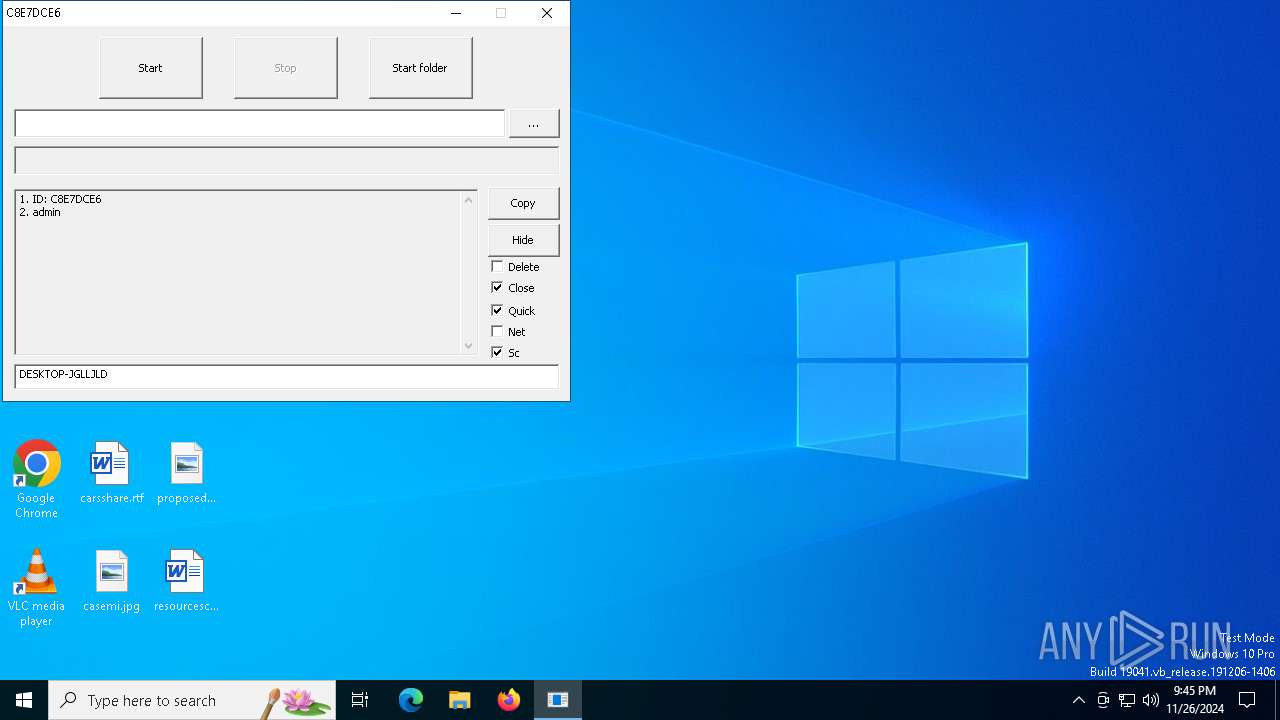
| File name: | _mc_hand.exe |
| Full analysis: | https://app.any.run/tasks/fcad3d41-d037-45ad-805f-466246220f05 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2024, 21:44:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 2FC890BD08C4B1C5EC458317EBE653C6 |
| SHA1: | 2901219D0ECAD5FFB23952575DE78496A11B5DF7 |
| SHA256: | F43B86FF363F19F26CC7D80AA64FA0894A264A736AE0ABD013D98E344637E4D8 |
| SSDEEP: | 768:IpJCEeOidQQ3N9lPeOMQyhOziFzeh0jSIYrW0G28um1vhJjHVucY8:rHNveOMQziFy6to8/vPTkcY8 |
MALICIOUS
Deletes shadow copies
- cmd.exe (PID: 6532)
SUSPICIOUS
Application launched itself
- _mc_hand.exe (PID: 5652)
Starts CMD.EXE for commands execution
- _mc_hand.exe (PID: 6268)
Executes as Windows Service
- VSSVC.exe (PID: 6624)
- vds.exe (PID: 7016)
- wbengine.exe (PID: 6912)
INFO
Executes as Windows Service
- OfficeClickToRun.exe (PID: 5560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:19 17:28:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 32768 |
| InitializedDataSize: | 99328 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6800 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
140
Monitored processes
12
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5560 | "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe" /service | C:\Program Files\Common Files\microsoft shared\ClickToRun\OfficeClickToRun.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Click-to-Run (SxS) Version: 16.0.16026.20140 Modules
| |||||||||||||||
| 5652 | "C:\Users\admin\AppData\Local\Temp\_mc_hand.exe" | C:\Users\admin\AppData\Local\Temp\_mc_hand.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6228 | wmic shadowcopy delete | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6268 | "C:\Users\admin\AppData\Local\Temp\_mc_hand.exe" e | C:\Users\admin\AppData\Local\Temp\_mc_hand.exe | _mc_hand.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6532 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | _mc_hand.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6592 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6624 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6856 | wbadmin delete catalog -quiet | C:\Windows\System32\wbadmin.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6912 | "C:\WINDOWS\system32\wbengine.exe" | C:\Windows\System32\wbengine.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Block Level Backup Engine Service EXE Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
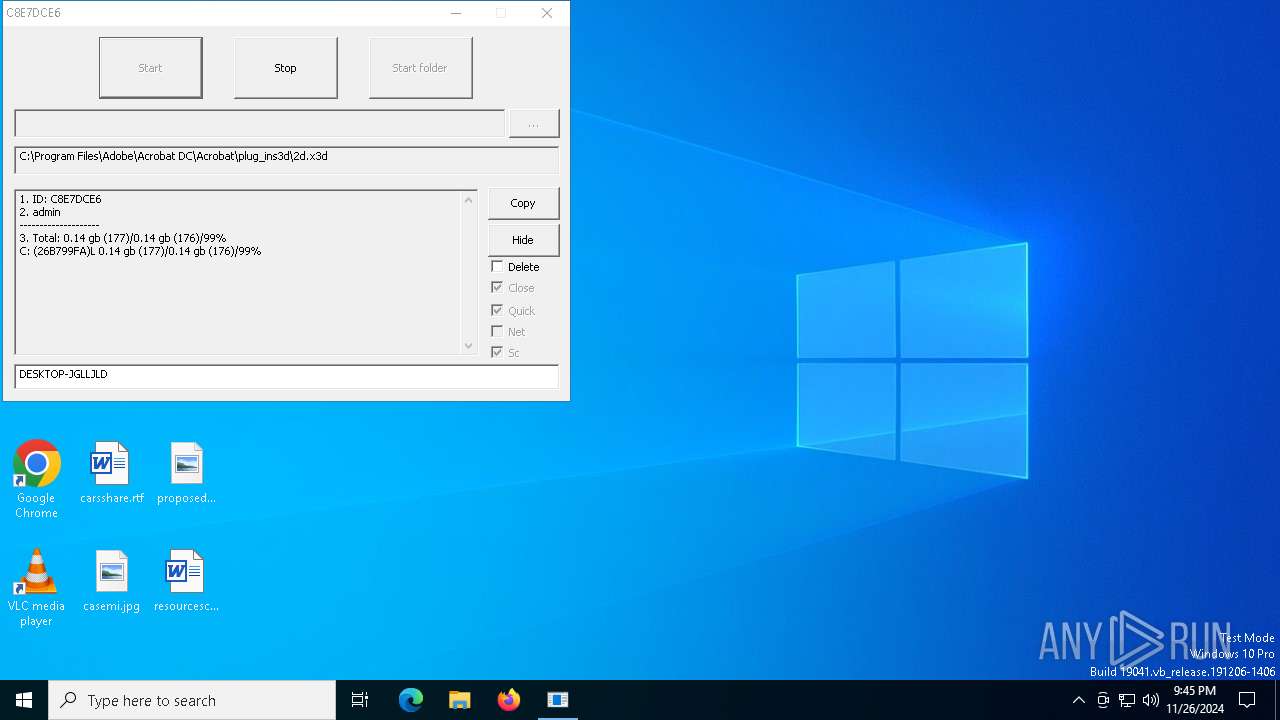
Total events
1 607
Read events
1 607
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
362
Text files
71
Unknown types
2
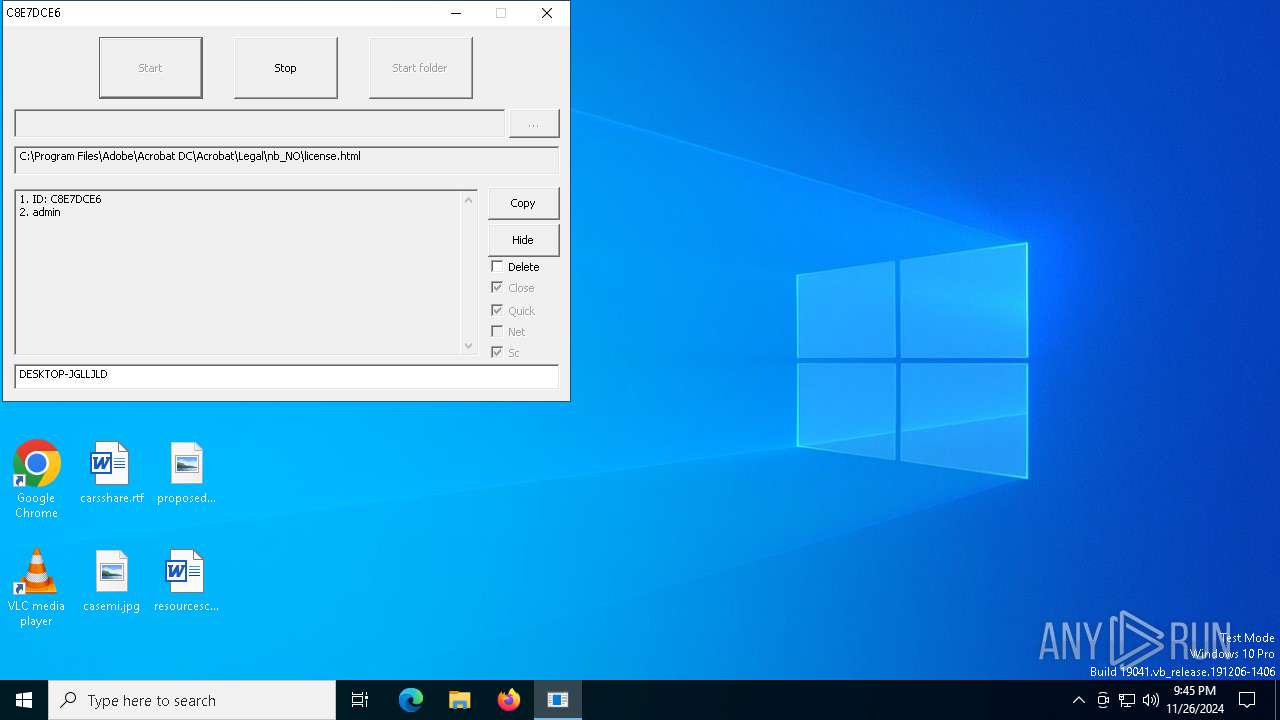
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\AdobeARM.log.[C8E7DCE6].[datastore@cyberfear.com].mkp | binary | |
MD5:ECE46C5A32CC08A8048FC6ABBD09016E | SHA256:C2B3AD8A90EEE87E6B553E1DDA7CA2105E7D7F79D40FEBD9FF6652597D12363C | |||
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\acrobat_sbx\+README-WARNING+.txt | text | |
MD5:5D377ADDD5FB119F9D200838847FF087 | SHA256:DD62F39B01CF2120C9E21ADD9E80396B44704D3D9E5499DE2EF26FA5824C10BB | |||
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\2piwomj5.ebl.[C8E7DCE6].[datastore@cyberfear.com].mkp | binary | |
MD5:AC2F6A8D9C87179BEA38E03C3EC0D514 | SHA256:96EDE36F1B4E998272C365C353F7DA9D02B494A13D5E06755AD2232FAAA10C74 | |||
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\b23k5hoi.vpb.[C8E7DCE6].[datastore@cyberfear.com].mkp | binary | |
MD5:672EA251E28ED5F9EF2C3256138ADA0D | SHA256:985B921ABBF471233730F5EE0C0B81933333D5DEFEACC4287869EAEB5B2CF326 | |||
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\bkzs50rg.bkl.[C8E7DCE6].[datastore@cyberfear.com].mkp | binary | |
MD5:42F51FDA84093AB26743CA8EEE609C10 | SHA256:7248EDF268C98A4083AA8CB4A4C9C2B6A10CA1CBED177A66BB75B2E7C2FFBF46 | |||
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\4cwoyrlk.wbw.[C8E7DCE6].[datastore@cyberfear.com].mkp | binary | |
MD5:8CFC1CFB2D4B0ECAAAD6DF93F8030FEA | SHA256:4F5FF601AA0E0ADD5FC53F73D830E99D2C2C9C7AE2F90DBFD443E170F201512C | |||
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\Diagnostics\OUTLOOK\App1721301366406819600_C3D8E96E-C1AF-4750-8D52-F4E28119C131.log.[C8E7DCE6].[datastore@cyberfear.com].mkp | — | |
MD5:— | SHA256:— | |||
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\Diagnostics\OUTLOOK\App1721301366407616900_C3D8E96E-C1AF-4750-8D52-F4E28119C131.log.[C8E7DCE6].[datastore@cyberfear.com].mkp | — | |
MD5:— | SHA256:— | |||
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\4522ioc5.sbm.[C8E7DCE6].[datastore@cyberfear.com].mkp | binary | |
MD5:9D43607AEF91085C70424970440DDF3E | SHA256:2B7D05770DBD90AC38EA2166DB7842832747D81920E78438130FC2D106821366 | |||
| 6268 | _mc_hand.exe | C:\Users\admin\AppData\Local\Temp\2gywpae0.x5n.[C8E7DCE6].[datastore@cyberfear.com].mkp | binary | |
MD5:395D1EDCC072DB2220DC4C5658990DFD | SHA256:4DD162DC9A2D7F53429F32DAE7BDF89B7A78B3746A3F5DC706AC5338666C6CF0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
28
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6776 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.187:443 | — | Akamai International B.V. | GB | unknown |
— | — | 2.16.164.106:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2092 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.179:443 | — | Akamai International B.V. | GB | unknown |
1176 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|