| File name: | psiphon.exe |
| Full analysis: | https://app.any.run/tasks/8a9cc0cb-c29b-4ec5-aecf-afc2f74e9723 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2019, 07:11:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 5E0D619BB76A510F753339E65FE74BCA |
| SHA1: | 3B07122688960DBD9074A5808898F305FCE763F1 |
| SHA256: | F4253233BB34A10B538F5CE75AA45C0B54AF8D77CA98F0A7F0C031FBAA9FD101 |
| SSDEEP: | 196608:f4+HUDMS6BL5upfWVJyEblT4B+YSMQEh5uaX:z0DMy0lTtY5QUcI |
MALICIOUS
Application was dropped or rewritten from another process
- psiphon-tunnel-core.exe (PID: 1248)
SUSPICIOUS
Executable content was dropped or overwritten
- psiphon.exe (PID: 2208)
Reads internet explorer settings
- psiphon.exe (PID: 2208)
Reads Internet Cache Settings
- rundll32.exe (PID: 2524)
- psiphon.exe (PID: 2208)
Uses RUNDLL32.EXE to load library
- psiphon.exe (PID: 2208)
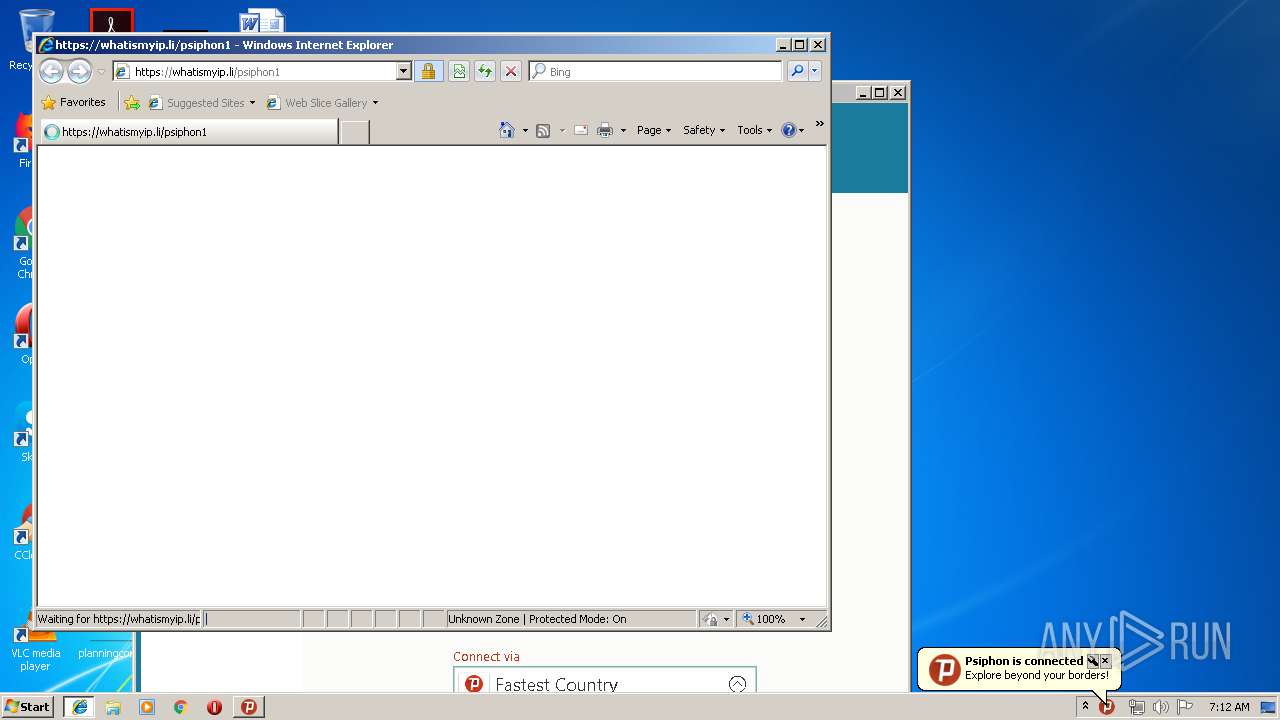
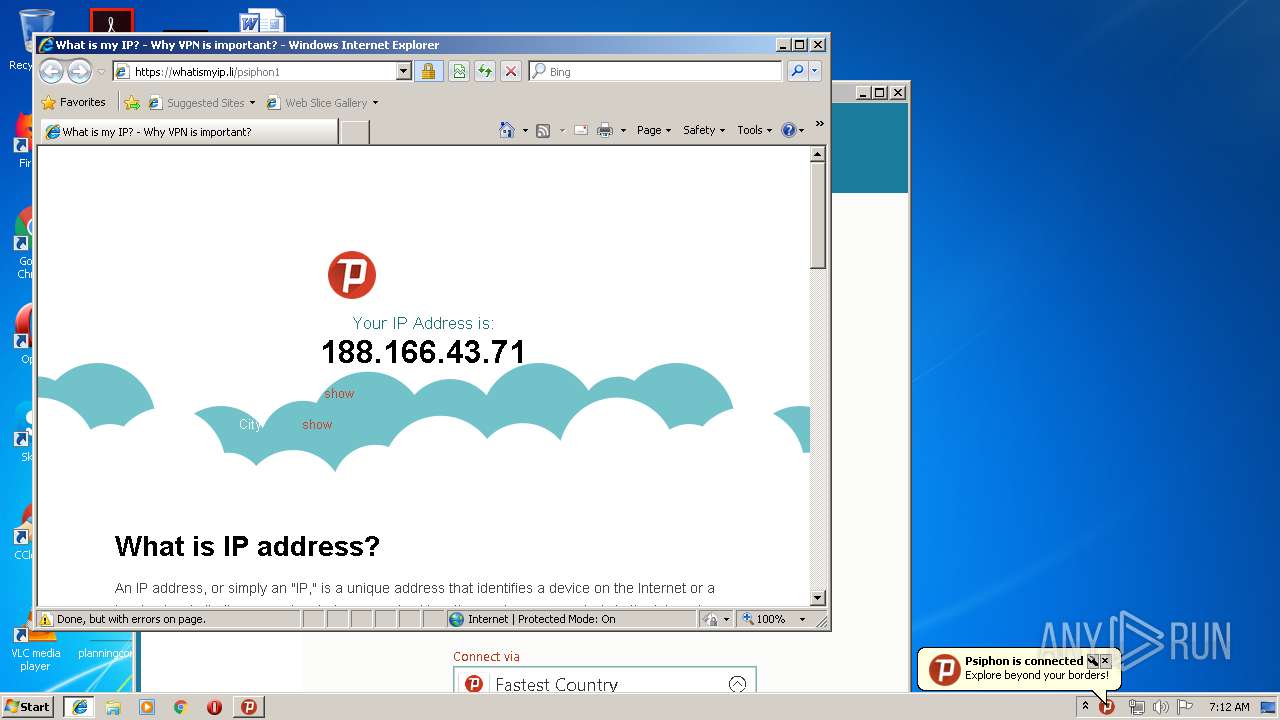
Starts Internet Explorer
- psiphon.exe (PID: 2208)
Creates files in the user directory
- psiphon-tunnel-core.exe (PID: 1248)
- psiphon.exe (PID: 2208)
Connects to unusual port
- psiphon-tunnel-core.exe (PID: 1248)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3932)
INFO
Changes internet zones settings
- iexplore.exe (PID: 788)
Application launched itself
- iexplore.exe (PID: 788)
Reads Internet Cache Settings
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 788)
Creates files in the user directory
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 788)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3932)
Reads settings of System Certificates
- psiphon.exe (PID: 2208)
Reads internet explorer settings
- iexplore.exe (PID: 3848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:11:23 22:06:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 6660096 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | 13152256 |
| EntryPoint: | 0x12e5880 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Nov-2019 21:06:59 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 23-Nov-2019 21:06:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00C8B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00C8C000 | 0x0065A000 | 0x00659C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93199 |
.rsrc | 0x012E6000 | 0x00016000 | 0x00015C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.49077 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.0192 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 5.62289 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 5.86281 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 5.32737 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 5.87817 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 5.82084 | 66 | UNKNOWN | English - United States | RT_STRING |
8 | 4.79539 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 7.96592 | 19543 | UNKNOWN | English - United States | RT_ICON |
10 | 7.94804 | 41745 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
42
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
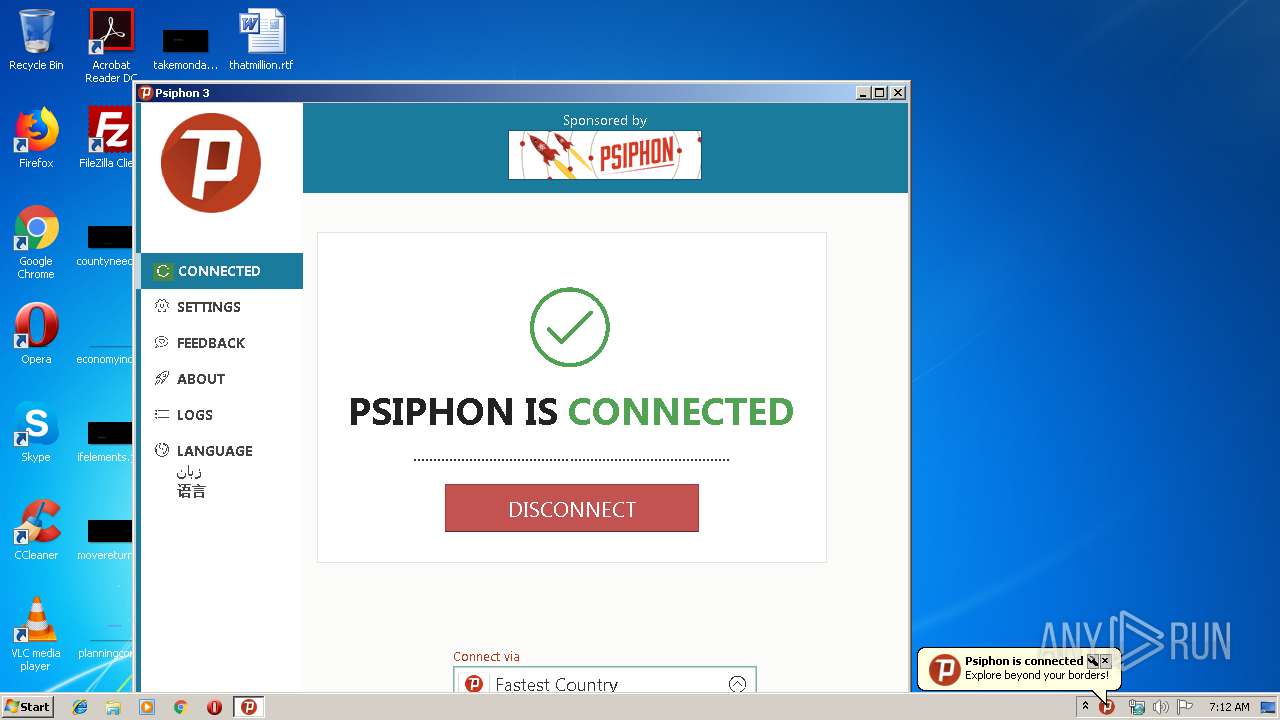
| 788 | "C:\Program Files\Internet Explorer\iexplore.exe" https://ipfounder.net/?sponsor_id=4BA4DEF917101460&sponsor=psiphon_bbg&client_region=AT&client_platform=windows&secret=580EfjEI29xL3hoyU6dgP4vSEVxdcGI7JDFkxgjds7PHulSEF0wmORpvzbqxyTwYtpowsY4xMFnfWEnTghe6l8jiV9K5QSZoir2i6fDeKJD6EhL6DkoYTEMu2EE9YJvy3LdCUZ7ncdVC6ipgWx06wznvDLbY1ajfcfRGCpfsQJei2q6tb0GSFh1QK3x3qXKwyjmNPc5J&psireason=connect#!psicash=eyJtZXRhZGF0YSI6eyJjbGllbnRfcmVnaW9uIjoiQVQiLCJjbGllbnRfdmVyc2lvbiI6IjE1MCIsInByb3BhZ2F0aW9uX2NoYW5uZWxfaWQiOiI5MkFBQ0M1QkFCRTA5NDRDIiwic3BvbnNvcl9pZCI6IjRCQTRERUY5MTcxMDE0NjAiLCJ1c2VyX2FnZW50IjoiUHNpcGhvbi1Qc2lDYXNoLVdpbmRvd3MifSwidG9rZW5zIjpudWxsLCJ2IjoxfQ | C:\Program Files\Internet Explorer\iexplore.exe | psiphon.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe --config "C:\Users\admin\AppData\Roaming\Psiphon3\psiphon.config" --serverList "C:\Users\admin\AppData\Roaming\Psiphon3\server_list.dat" | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe | psiphon.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\AppData\Local\Temp\psiphon.exe" | C:\Users\admin\AppData\Local\Temp\psiphon.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2524 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | psiphon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3848 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:788 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3932 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
654
Read events
528
Write events
124
Delete events
2
Modification events
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SkipProxySettings |
Value: 0 | |||
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SkipAutoConnect |
Value: 0 | |||
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2208) psiphon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
1
Suspicious files
5
Text files
53
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | psiphon.exe | C:\Users\admin\AppData\Roaming\Psiphon3\psicash\psicashdatastore.prod.temp | — | |
MD5:— | SHA256:— | |||
| 2208 | psiphon.exe | C:\Users\admin\AppData\Roaming\Psiphon3\psicash\psicashdatastore.prod.commit | — | |
MD5:— | SHA256:— | |||
| 2208 | psiphon.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\main[1] | html | |
MD5:— | SHA256:— | |||
| 2208 | psiphon.exe | C:\Users\admin\AppData\Roaming\Psiphon3\psicash\psicashdatastore.prod | text | |
MD5:— | SHA256:— | |||
| 2208 | psiphon.exe | C:\Users\admin\AppData\Local\Temp\CabF77.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | psiphon.exe | C:\Users\admin\AppData\Local\Temp\TarF88.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | psiphon.exe | C:\Users\admin\AppData\Local\Temp\CabFE7.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | psiphon.exe | C:\Users\admin\AppData\Local\Temp\TarFE8.tmp | — | |
MD5:— | SHA256:— | |||
| 2208 | psiphon.exe | C:\Users\admin\AppData\Local\Temp\psiphon-tunnel-core.exe | executable | |
MD5:— | SHA256:— | |||
| 2208 | psiphon.exe | C:\Users\admin\AppData\Roaming\Psiphon3\psiphon.config | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
13
DNS requests
7
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1248 | psiphon-tunnel-core.exe | 195.206.107.74:22 | — | — | — | unknown |
1248 | psiphon-tunnel-core.exe | 194.36.111.34:53 | — | — | — | suspicious |
1248 | psiphon-tunnel-core.exe | 85.204.124.186:53 | — | M247 Ltd | RO | unknown |
1248 | psiphon-tunnel-core.exe | 188.166.43.71:22 | — | Digital Ocean, Inc. | NL | unknown |
1248 | psiphon-tunnel-core.exe | 185.230.127.146:53 | — | — | — | suspicious |
1248 | psiphon-tunnel-core.exe | 173.230.131.249:80 | — | Linode, LLC | US | unknown |
1248 | psiphon-tunnel-core.exe | 109.232.240.14:443 | — | — | PL | unknown |
1248 | psiphon-tunnel-core.exe | 79.142.76.175:53 | — | AltusHost B.V. | SE | unknown |
1248 | psiphon-tunnel-core.exe | 198.58.118.6:53 | — | Linode, LLC | US | suspicious |
1248 | psiphon-tunnel-core.exe | 193.9.114.186:53 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1248 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 6 or 7 set |
1248 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 8 through 15 set |
1248 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 6 or 7 set |
1248 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Reserved Bit Set |
Process | Message |
|---|---|
psiphon.exe | Client Version: 150 |
psiphon.exe | Client Version: 150 |
psiphon.exe | |
psiphon.exe | 2019-11-25T07:12:28.394Z: |
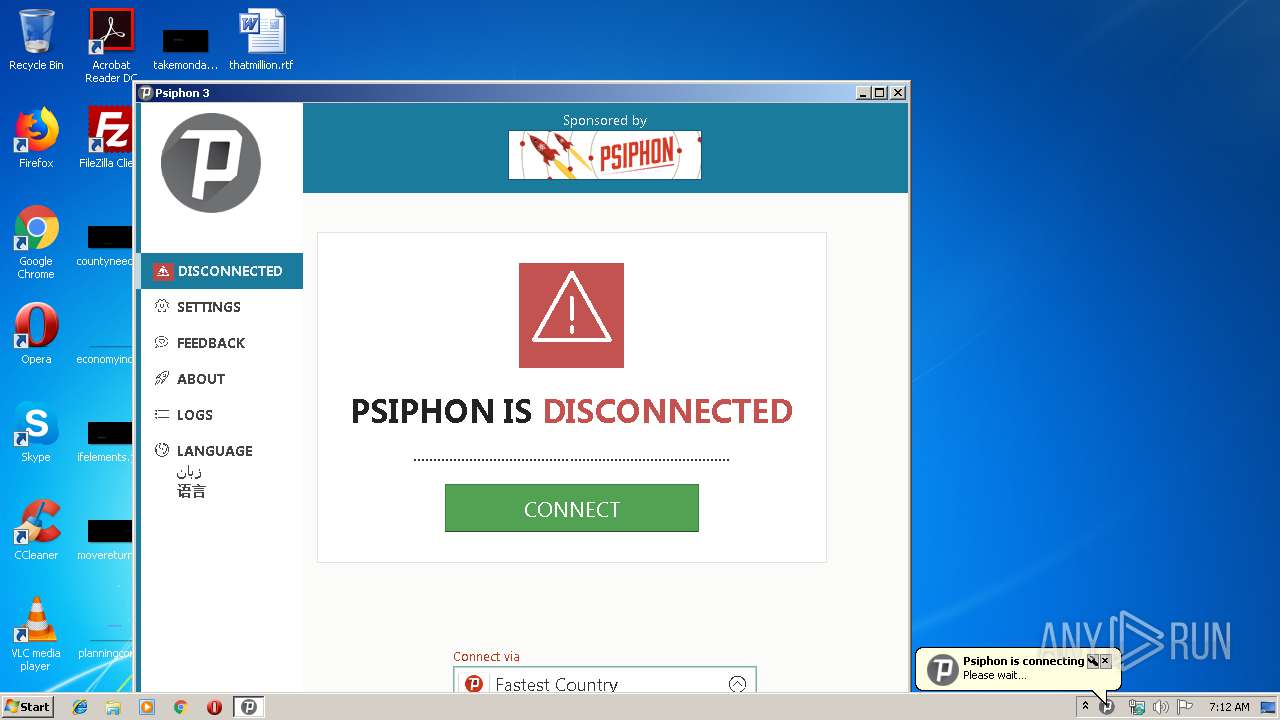
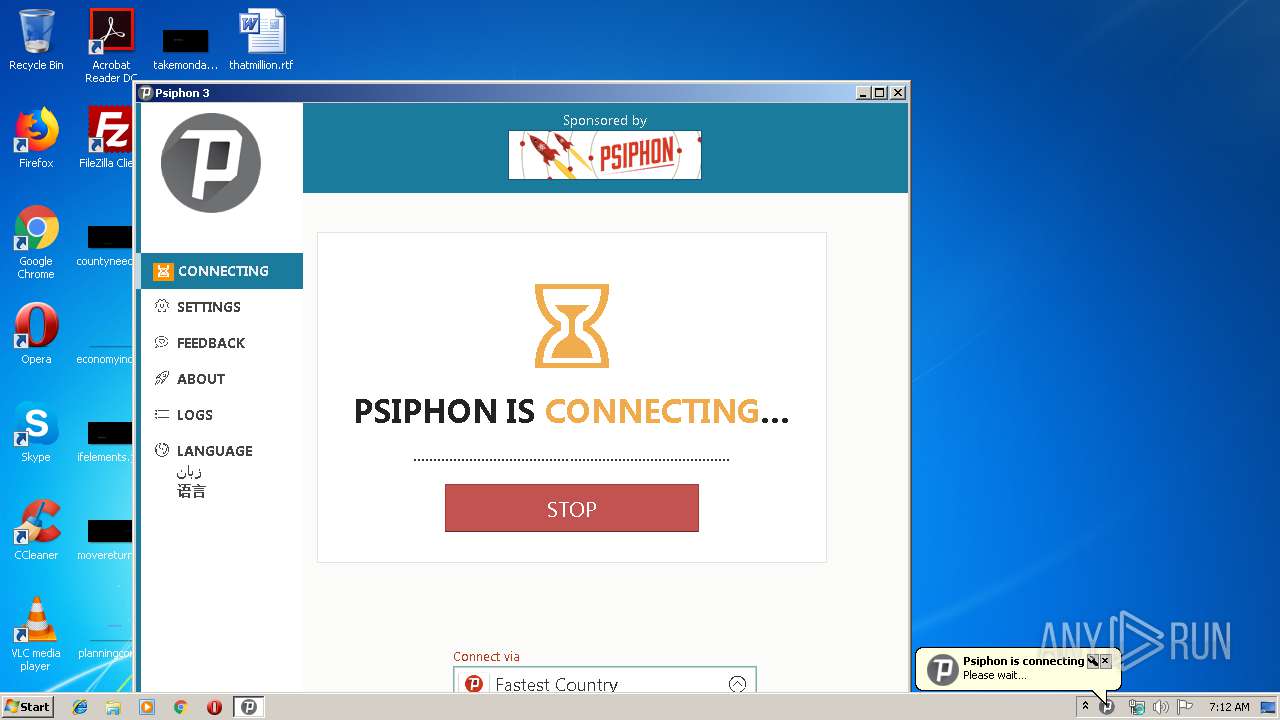
psiphon.exe | Psiphon Tunnel connecting... |
psiphon.exe | |
psiphon.exe | {"data":{"data":{"message":"applied [11] parameters with tag ''"},"noticeType":"Info","showUser":false,"timestamp":"2019-11-25T07:12:28.495Z"},"msg":"CoreNotice","timestamp!!timestamp":"2019-11-25T07:12:28.525Z"}
|
psiphon.exe | |
psiphon.exe | {"data":{"data":{"message":"NetworkLatencyMultiplier Min/Max/Lambda: 1.000000/3.000000/2.000000"},"noticeType":"Info","showUser":false,"timestamp":"2019-11-25T07:12:28.495Z"},"msg":"CoreNotice","timestamp!!timestamp":"2019-11-25T07:12:28.529Z"}
|
psiphon.exe | |