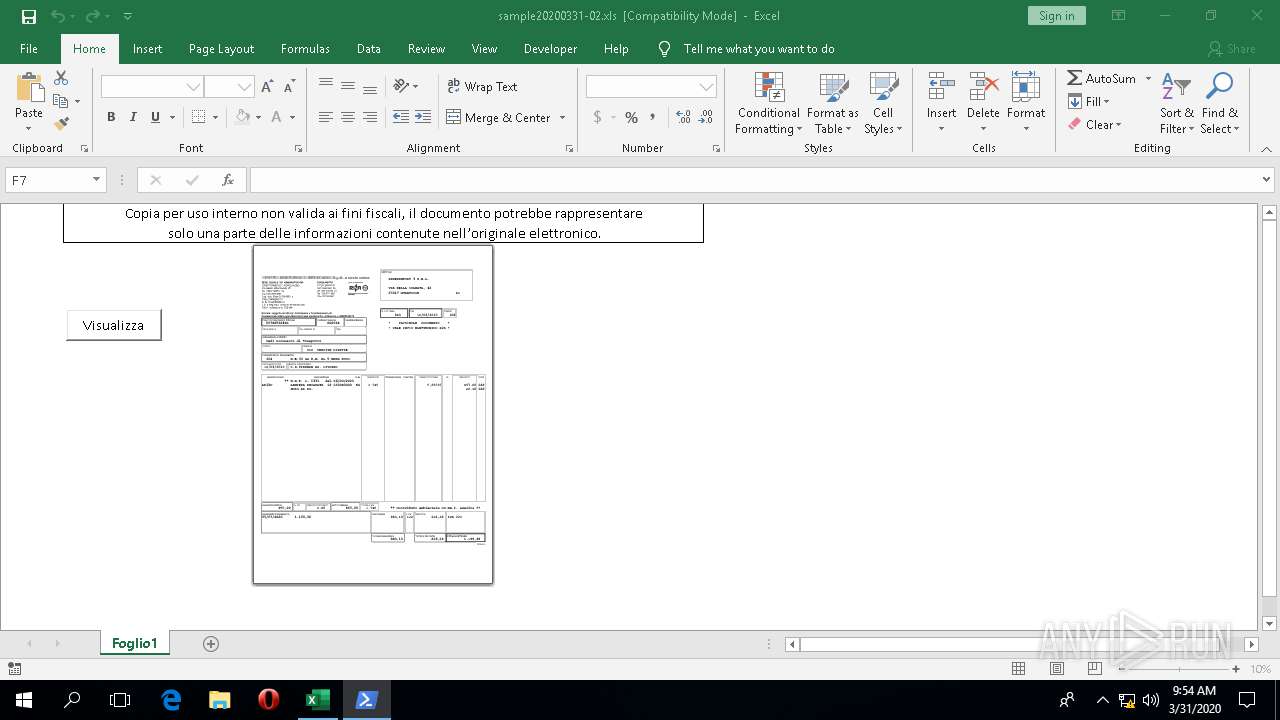
| File name: | sample20200331-02.xls |
| Full analysis: | https://app.any.run/tasks/fbb7ea00-d957-4f5a-9916-379d540dfedc |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 09:53:56 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Name of Creating Application: Microsoft Excel, Create Time/Date: Sat Feb 29 08:17:24 2020, Last Saved Time/Date: Sat Feb 29 08:18:02 2020, Security: 0 |
| MD5: | AD7677318E9FF63FA0ACE3AB445D036F |
| SHA1: | F8705B9F5FA84A9DF85320680B1430329664EABC |
| SHA256: | F424B6EB3B855C89E4D2329115E1C43B8DA179D40750B7AEE1D192D700610331 |
| SSDEEP: | 768:+hY+aZoMlYkEIbSkKBEqEXPgsRZmbaoFhZhR0cixIHm0L0QC5MC8F0K2YWdI:+hY+olYkEIbSkKBEqEXPgsRZmbaoFhZx |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3384)
Executes PowerShell scripts
- EXCEL.EXE (PID: 3384)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 4544)
Checks supported languages
- powershell.exe (PID: 4544)
Executes PowerShell scripts
- powershell.exe (PID: 4544)
Reads the machine GUID from the registry
- powershell.exe (PID: 896)
- powershell.exe (PID: 4544)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 3384)
Reads Environment values
- EXCEL.EXE (PID: 3384)
Scans artifacts that could help determine the target
- EXCEL.EXE (PID: 3384)
Reads the software policy settings
- powershell.exe (PID: 4544)
- powershell.exe (PID: 896)
Reads settings of System Certificates
- powershell.exe (PID: 4544)
- powershell.exe (PID: 896)
Reads the machine GUID from the registry
- EXCEL.EXE (PID: 3384)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2020:03:31 08:17:24 |
| ModifyDate: | 2020:03:31 08:18:02 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Foglio1 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 42 |
| CompObjUserType: | (Foglio di lavoro di Microsoft Excel 2003 |
Total processes
87
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" | C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\Desktop\sample20200331-02.xls" | C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 4544 | powershell | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 701
Read events
3 375
Write events
295
Delete events
31
Modification events
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 1 |
Value: 01D014000000001000284FFA2E01000000000000000400000000000000 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\CrashPersistence\EXCEL\3384 |
| Operation: | write | Name: | 0 |
Value: 0B0E102AA7954BD2EF5940A448E532A440D43323004680D4D7B4A5E881EB016A0410240044FA5D64A89E01008500A907556E6B6E6F776EC9062E226D2B484F4D616659574A5464337373702B3165327141506A326C775347586F6C4A7635624B6E337449506B3D2200 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (3384) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
0
Suspicious files
1
Text files
11
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\I61XUSILLTTG2WKSG5Z5.temp | — | |
MD5:— | SHA256:— | |||
| 4544 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zjrxjwxz.04o.ps1 | — | |
MD5:— | SHA256:— | |||
| 4544 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_np1idxxo.mpx.psm1 | — | |
MD5:— | SHA256:— | |||
| 3384 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF67D5F3FCA6E5C5EB.TMP | — | |
MD5:— | SHA256:— | |||
| 3384 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF6A6CCC0C1BC19AD9.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p52mqxdw.seb.ps1 | — | |
MD5:— | SHA256:— | |||
| 896 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dzvptuba.14v.psm1 | — | |
MD5:— | SHA256:— | |||
| 3384 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\excel.exe.db-shm | — | |
MD5:— | SHA256:— | |||
| 3384 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\excel.exe.db-wal | — | |
MD5:— | SHA256:— | |||
| 3384 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3384 | EXCEL.EXE | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
3384 | EXCEL.EXE | 52.114.36.3:443 | self.events.data.microsoft.com | Microsoft Corporation | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |