| File name: | sample20200331-02.xls |
| Full analysis: | https://app.any.run/tasks/7f77e15c-6704-4ee7-8ec8-a2c7042d47e1 |
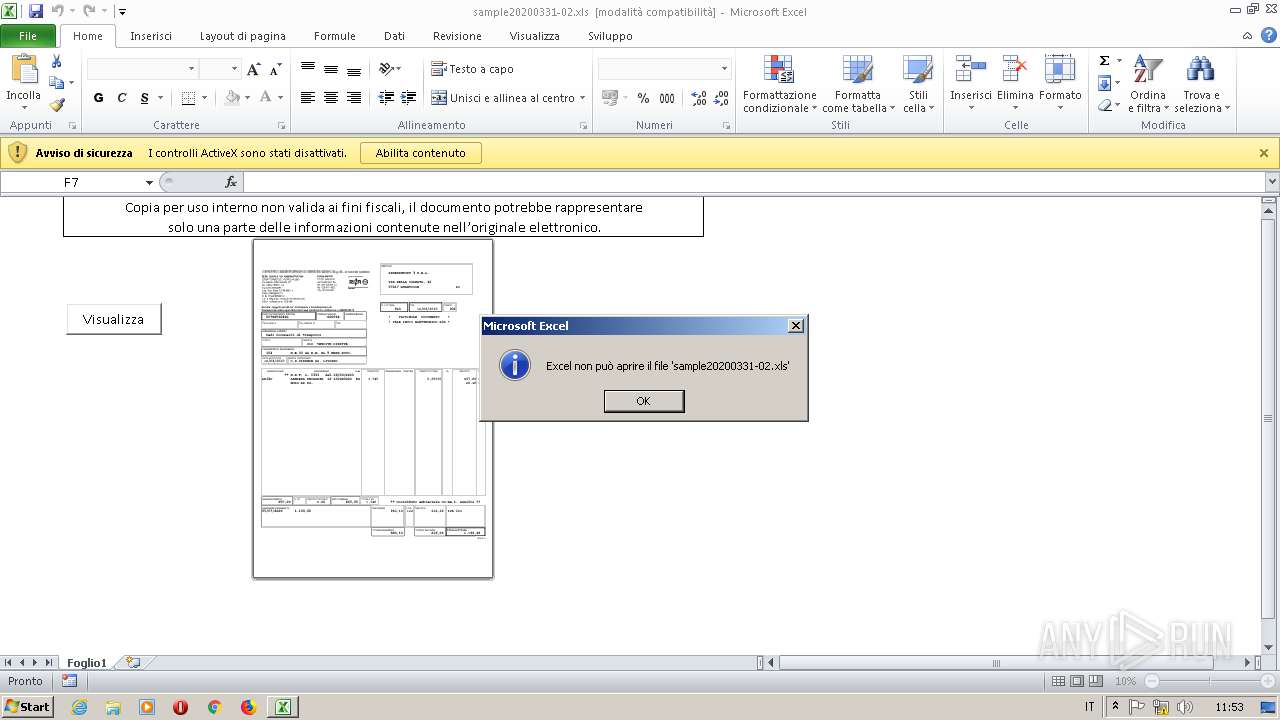
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 09:53:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Name of Creating Application: Microsoft Excel, Create Time/Date: Sat Feb 29 08:17:24 2020, Last Saved Time/Date: Sat Feb 29 08:18:02 2020, Security: 0 |
| MD5: | AD7677318E9FF63FA0ACE3AB445D036F |
| SHA1: | F8705B9F5FA84A9DF85320680B1430329664EABC |
| SHA256: | F424B6EB3B855C89E4D2329115E1C43B8DA179D40750B7AEE1D192D700610331 |
| SSDEEP: | 768:+hY+aZoMlYkEIbSkKBEqEXPgsRZmbaoFhZhR0cixIHm0L0QC5MC8F0K2YWdI:+hY+olYkEIbSkKBEqEXPgsRZmbaoFhZx |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2124)
Executes PowerShell scripts
- EXCEL.EXE (PID: 2124)
SUSPICIOUS
Executes PowerShell scripts
- powershell.exe (PID: 2456)
Creates files in the user directory
- powershell.exe (PID: 2156)
- powershell.exe (PID: 2456)
Reads the machine GUID from the registry
- powershell.exe (PID: 2456)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 2124)
Reads the machine GUID from the registry
- EXCEL.EXE (PID: 2124)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2020:03:31 08:17:24 |
| ModifyDate: | 2020:03:31 08:18:02 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Foglio1 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 42 |
| CompObjUserType: | (Foglio di lavoro di Microsoft Excel 2003 |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2124 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.4756.1000 Modules
| |||||||||||||||
| 2156 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2456 | powershell | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 047
Read events
875
Write events
161
Delete events
11
Modification events
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | l:6 |
Value: 6C3A36004C080000010000000000000000000000 | |||
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2124) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
Executable files
0
Suspicious files
3
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRD24C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2456 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LU7MK8HOXOAYUT30HUAC.temp | — | |
MD5:— | SHA256:— | |||
| 2156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K1UN3CSQ8HD1BS8QCOLS.temp | — | |
MD5:— | SHA256:— | |||
| 2124 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFBEEAFA45340FCAAA.TMP | — | |
MD5:— | SHA256:— | |||
| 2124 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\sample20200331-02.xls.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2124 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A00A499C.emf | emf | |
MD5:— | SHA256:— | |||
| 2124 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E2D7EC47.emf | emf | |
MD5:— | SHA256:— | |||
| 2124 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2456 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF12e42e.TMP | binary | |
MD5:— | SHA256:— | |||
| 2456 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
powershell.exe |
*** Status Originated: -1073741811
*** Source File: d:\iso_whid\amd64fre\base\ntos\rtl\lblob.cpp, line 1020
|
powershell.exe |
*** Status propagated: -1073741811
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\identityauthority.cpp, line 147
|
powershell.exe |
*** Status Originated: -1073741811
*** Source File: d:\iso_whid\amd64fre\base\ntos\rtl\lblob.cpp, line 1020
|
powershell.exe |
*** Status propagated: -1073741811
*** Source File: d:\iso_whid\amd64fre\base\isolation\com\identityauthority.cpp, line 147
|