| File name: | Fantom.exe |
| Full analysis: | https://app.any.run/tasks/7764b113-af1a-46bc-a19e-e3363034cedc |
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2024, 09:17:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7D80230DF68CCBA871815D68F016C282 |
| SHA1: | E10874C6108A26CEEDFC84F50881824462B5B6B6 |
| SHA256: | F4234A501EDCD30D3BC15C983692C9450383B73BDD310059405C5E3A43CC730B |
| SSDEEP: | 6144:vDKW1Lgbdl0TBBvjc/M8n35nYgvKjdzi:rh1Lk70TnvjcbphQi |
MALICIOUS
Drops the executable file immediately after the start
- Fantom.exe (PID: 1380)
Modifies files in the Chrome extension folder
- Fantom.exe (PID: 1380)
Actions looks like stealing of personal data
- Fantom.exe (PID: 1380)
SUSPICIOUS
Executable content was dropped or overwritten
- Fantom.exe (PID: 1380)
Reads the Internet Settings
- Fantom.exe (PID: 1380)
INFO
Reads the computer name
- Fantom.exe (PID: 1380)
- WindowsUpdate.exe (PID: 2028)
- wmpnscfg.exe (PID: 3612)
Checks supported languages
- Fantom.exe (PID: 1380)
- WindowsUpdate.exe (PID: 2028)
- wmpnscfg.exe (PID: 3612)
Reads the machine GUID from the registry
- Fantom.exe (PID: 1380)
- WindowsUpdate.exe (PID: 2028)
Create files in a temporary directory
- Fantom.exe (PID: 1380)
Reads Environment values
- Fantom.exe (PID: 1380)
Creates files in the program directory
- Fantom.exe (PID: 1380)
Creates files or folders in the user directory
- Fantom.exe (PID: 1380)
Manual execution by a user
- wmpnscfg.exe (PID: 3612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:07:14 00:47:16+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 162304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcd2f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.1.0 |
| ProductVersionNumber: | 3.2.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
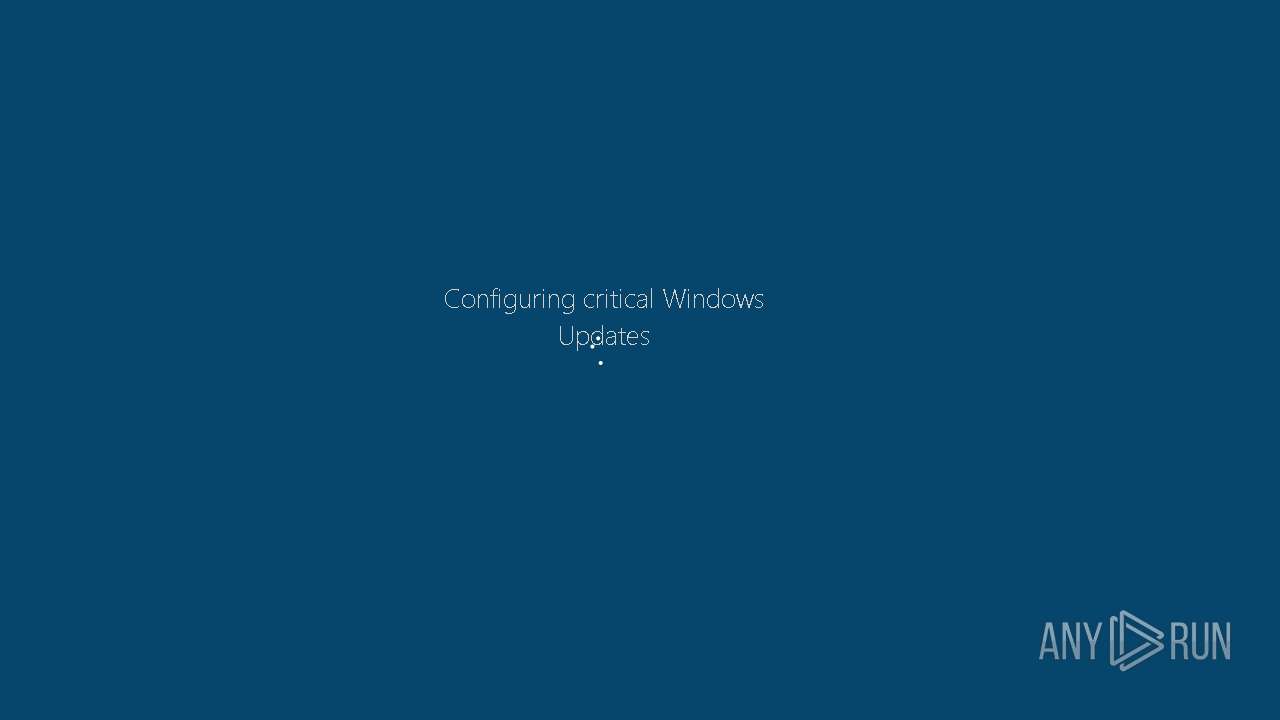
| Comments: | system critical updates |
| CompanyName: | Microsoft |
| FileDescription: | critical update |
| FileVersion: | 3.2.1.0 |
| InternalName: | criticalupdate01.exe |
| LegalCopyright: | Copyright Microsoft © 2016 |
| LegalTrademarks: | Microsoft corporation © |
| OriginalFileName: | criticalupdate01.exe |
| ProductName: | critical update kb01 |
| ProductVersion: | 3.2.1.0 |
| AssemblyVersion: | 3.2.1.0 |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1380 | "C:\Users\admin\AppData\Local\Temp\Fantom.exe" | C:\Users\admin\AppData\Local\Temp\Fantom.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: critical update Exit code: 0 Version: 3.2.1.0 Modules
| |||||||||||||||
| 2028 | "C:\Users\admin\AppData\Local\Temp\WindowsUpdate.exe" | C:\Users\admin\AppData\Local\Temp\WindowsUpdate.exe | — | Fantom.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApplication5 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 109
Read events
1 101
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1380) Fantom.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1380) Fantom.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1380) Fantom.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1380) Fantom.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
1 055
Text files
449
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\DECRYPT_YOUR_FILES.HTML | html | |
MD5:0792A13AAB2A01F2EB30EE3F970B84B2 | SHA256:A945C05483D5AC83B745735B7823A481B4B3FB3B8AB4B87ED2C5F63762BFC47C | |||
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\branding.xml.fantom | binary | |
MD5:3BD5871EB576A209B2BF80C19E4862B4 | SHA256:07CF3D2E9E9407EA907A073F486990E2C33969367A2C5530D8D79FC9A6B1BD51 | |||
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.xml.fantom | binary | |
MD5:7C1C6FA4A9369000F1A0A44A9969659D | SHA256:206EA6E69B3C8323062D9976CF69DDEC4A2C3ECE5766DD8A887866403FC49B4A | |||
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.xml | binary | |
MD5:7C1C6FA4A9369000F1A0A44A9969659D | SHA256:206EA6E69B3C8323062D9976CF69DDEC4A2C3ECE5766DD8A887866403FC49B4A | |||
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml.fantom | binary | |
MD5:E2EEA8270B45E20C6EB9EA9A72D24DCF | SHA256:C897EFDE1B00CCD703549DFBFE4582EE47301EB2925F3357FD7F0B5F12F86734 | |||
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml | binary | |
MD5:E2EEA8270B45E20C6EB9EA9A72D24DCF | SHA256:C897EFDE1B00CCD703549DFBFE4582EE47301EB2925F3357FD7F0B5F12F86734 | |||
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml.fantom | binary | |
MD5:083196D6BA8F53B89837A7AE2AF1CE72 | SHA256:68A80A66C41AA15D2996A400B97C764C15153B15639FEFF9F57AFD902D5B3640 | |||
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\branding.xml | binary | |
MD5:5B006C424F969291A7A7079C8FF05B09 | SHA256:5A5F5A57BFE0B7E9952957CCB68DF5ED7AA3A559804A840838395A642230D478 | |||
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\branding.xml.fantom | binary | |
MD5:5B006C424F969291A7A7079C8FF05B09 | SHA256:5A5F5A57BFE0B7E9952957CCB68DF5ED7AA3A559804A840838395A642230D478 | |||
| 1380 | Fantom.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\Setup.xml.fantom | binary | |
MD5:F0CD444B91CDAA750D81FBF02C1070F5 | SHA256:B8D0C433B6A1957E607D106A37B7C02C8112DB71881A9977C4C5D8D9D9917442 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
powertoolsforyou.com |
| unknown |