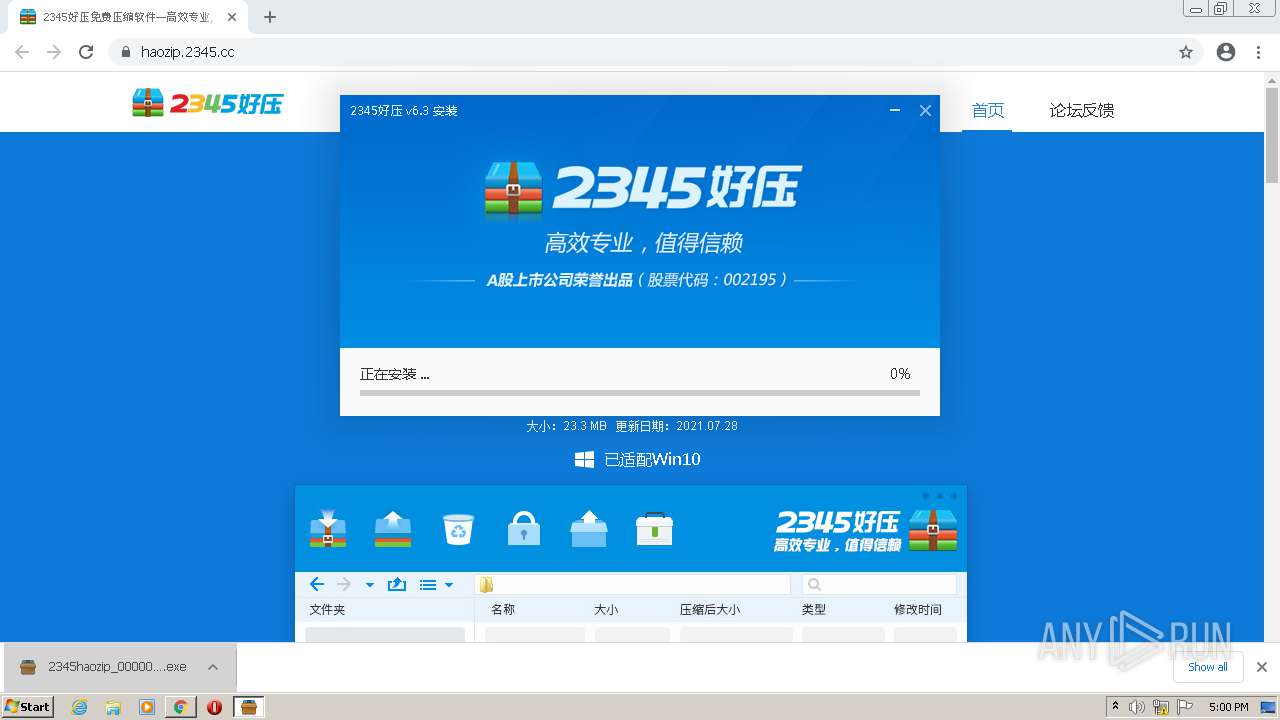
| URL: | http://haozip.2345.com |
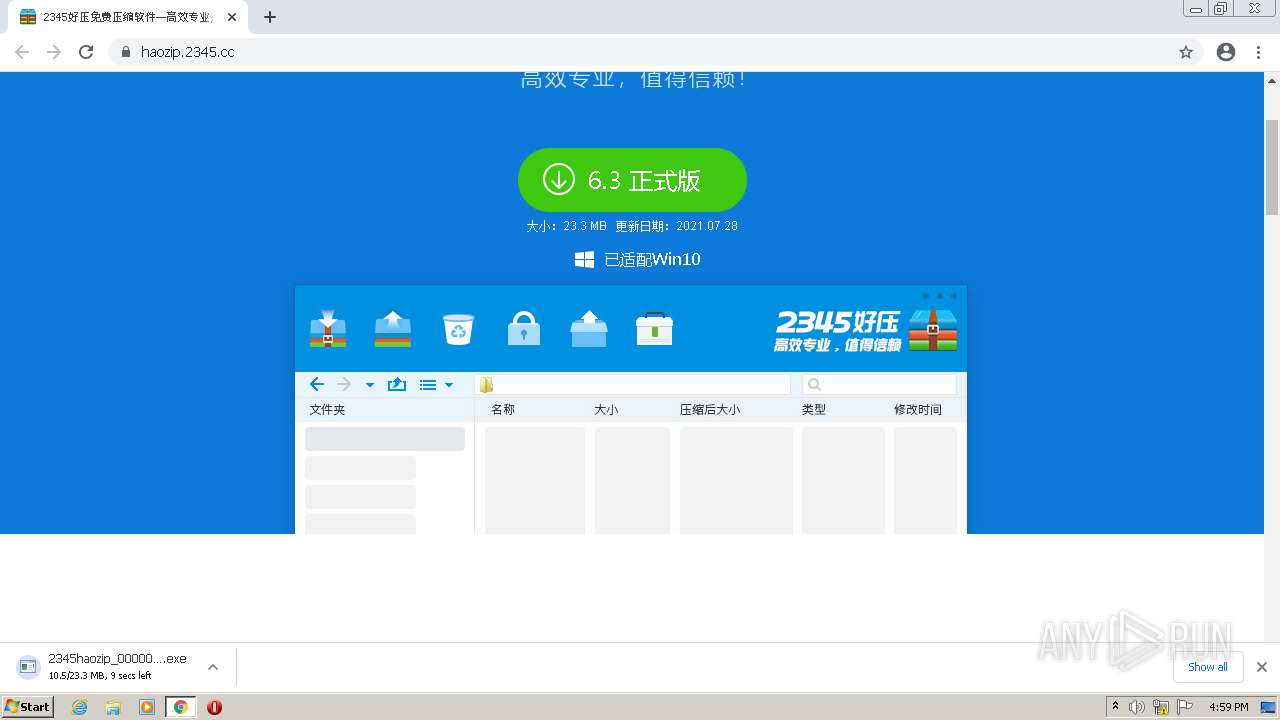
| Full analysis: | https://app.any.run/tasks/0a9bef14-306e-4fff-80c4-f9e195a3d1f7 |
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2021, 15:58:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 357213FBC332DCCA5B9E14E778137A8E |
| SHA1: | 83A0C8F5747927BACEA25940D56E4DDDBC3380FB |
| SHA256: | F40D6677DF5A9C5F58D8C48A34AFE25EE28BEC6FDCCBB86983719D4F413F775A |
| SSDEEP: | 3:N1KWElVqRZKI:CWwgnT |
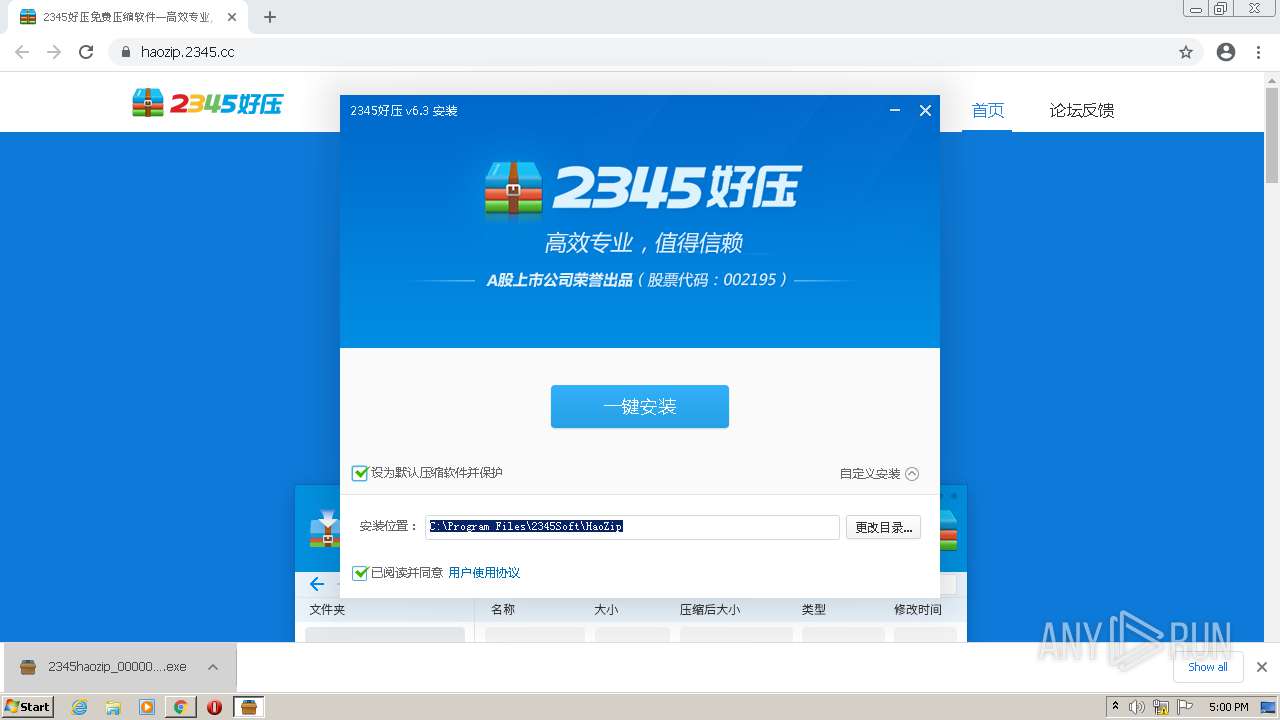
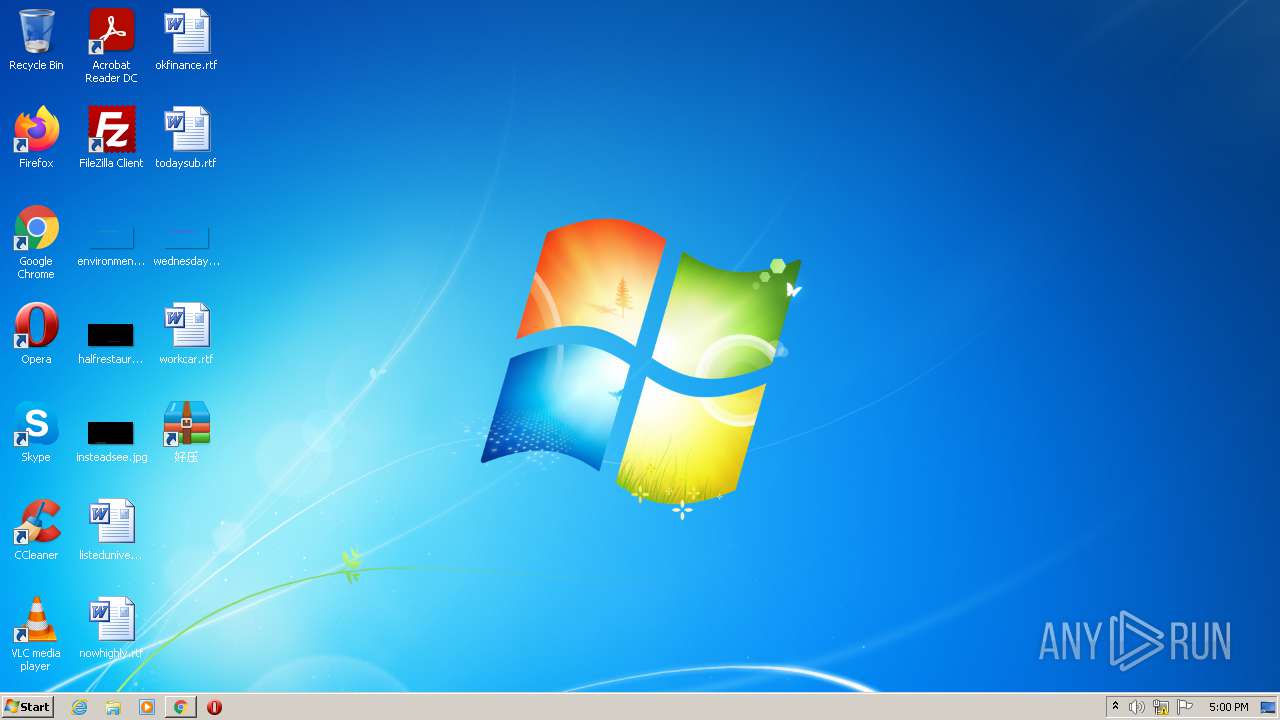
MALICIOUS
Application was dropped or rewritten from another process
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- 2345haozip_000000_6.3.1.11106.exe (PID: 1808)
- HaoZipLoader.exe (PID: 3316)
- HaoZipLoader.exe (PID: 444)
- HaoZipLoader.exe (PID: 3952)
- HaoZipUpdate.exe (PID: 1232)
- HaoZipLoader.exe (PID: 1920)
- HaoZipLoader.exe (PID: 2680)
- HaoZipLoader.exe (PID: 3864)
- HaoZipLoader.exe (PID: 2660)
- HaoZipLoader.exe (PID: 3224)
- HaoZipLoader.exe (PID: 3628)
- HaoZipUpdate.exe (PID: 2664)
- 2345SafeCenterInstaller.exe (PID: 3760)
- HaoZipLoader.exe (PID: 2896)
- HaoZipLoader.exe (PID: 1444)
- ServiceManager.exe (PID: 2200)
- HaozipSvc.exe (PID: 2432)
- HaoZip.exe (PID: 4064)
- HaoZipUpdate.exe (PID: 1892)
- 2345SafeCenterSvc.exe (PID: 2396)
- 2345RTProtect.exe (PID: 2588)
- HaoZipUpdate.exe (PID: 3320)
- 2345SafeCenterCrashReport.exe (PID: 3032)
- 2345SafeCenterInstaller.exe (PID: 2564)
Loads dropped or rewritten executable
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 444)
- HaoZipLoader.exe (PID: 3952)
- HaoZipUpdate.exe (PID: 1232)
- HaoZipLoader.exe (PID: 1920)
- HaoZipLoader.exe (PID: 2680)
- 2345SafeCenterInstaller.exe (PID: 3760)
- HaoZipLoader.exe (PID: 3316)
- HaoZipLoader.exe (PID: 2660)
- HaoZipLoader.exe (PID: 3864)
- HaoZipLoader.exe (PID: 3224)
- HaoZipLoader.exe (PID: 3628)
- HaoZipUpdate.exe (PID: 2664)
- HaoZipLoader.exe (PID: 1444)
- HaozipSvc.exe (PID: 2432)
- HaoZip.exe (PID: 4064)
- HaoZipUpdate.exe (PID: 3320)
- 2345SafeCenterSvc.exe (PID: 2396)
- HaoZipUpdate.exe (PID: 1892)
- 2345RTProtect.exe (PID: 2588)
- 2345SafeCenterCrashReport.exe (PID: 3032)
- HaoZipLoader.exe (PID: 2896)
- Explorer.EXE (PID: 356)
- iexplore.exe (PID: 2408)
- iexplore.exe (PID: 2488)
Drops executable file immediately after starts
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 1920)
Loads the Task Scheduler COM API
- HaoZipLoader.exe (PID: 444)
Changes settings of System certificates
- 2345SafeCenterInstaller.exe (PID: 3760)
Steals credentials from Web Browsers
- 2345RTProtect.exe (PID: 2588)
Runs injected code in another process
- 2345RTProtect.exe (PID: 2588)
Application was injected by another process
- Explorer.EXE (PID: 356)
Actions looks like stealing of personal data
- 2345RTProtect.exe (PID: 2588)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2468)
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 1920)
- 2345SafeCenterInstaller.exe (PID: 3760)
Checks supported languages
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 3316)
- HaoZipLoader.exe (PID: 444)
- HaoZipLoader.exe (PID: 3952)
- HaoZipUpdate.exe (PID: 1232)
- HaoZipLoader.exe (PID: 1920)
- 2345SafeCenterInstaller.exe (PID: 3760)
- HaoZipLoader.exe (PID: 2680)
- HaoZipLoader.exe (PID: 3864)
- HaoZipLoader.exe (PID: 2660)
- HaoZipLoader.exe (PID: 3224)
- HaoZipLoader.exe (PID: 3628)
- HaoZipUpdate.exe (PID: 2664)
- HaoZipLoader.exe (PID: 2896)
- HaoZipLoader.exe (PID: 1444)
- ServiceManager.exe (PID: 2200)
- HaozipSvc.exe (PID: 2432)
- HaoZip.exe (PID: 4064)
- HaoZipUpdate.exe (PID: 1892)
- HaoZipUpdate.exe (PID: 3320)
- 2345SafeCenterSvc.exe (PID: 2396)
- 2345SafeCenterCrashReport.exe (PID: 3032)
- 2345RTProtect.exe (PID: 2588)
- 2345SafeCenterInstaller.exe (PID: 2564)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3260)
Reads the computer name
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 444)
- HaoZipLoader.exe (PID: 3952)
- HaoZipUpdate.exe (PID: 1232)
- HaoZipLoader.exe (PID: 1920)
- HaoZipLoader.exe (PID: 3316)
- 2345SafeCenterInstaller.exe (PID: 3760)
- HaoZipLoader.exe (PID: 2680)
- HaoZipLoader.exe (PID: 3864)
- HaoZipLoader.exe (PID: 2660)
- HaoZipLoader.exe (PID: 3224)
- HaoZipLoader.exe (PID: 3628)
- HaoZipUpdate.exe (PID: 2664)
- HaoZipLoader.exe (PID: 2896)
- HaoZipLoader.exe (PID: 1444)
- HaozipSvc.exe (PID: 2432)
- ServiceManager.exe (PID: 2200)
- HaoZip.exe (PID: 4064)
- HaoZipUpdate.exe (PID: 1892)
- HaoZipUpdate.exe (PID: 3320)
- 2345SafeCenterSvc.exe (PID: 2396)
- 2345RTProtect.exe (PID: 2588)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3260)
Drops a file with too old compile date
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- 2345SafeCenterInstaller.exe (PID: 3760)
Drops a file with a compile date too recent
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- 2345SafeCenterInstaller.exe (PID: 3760)
Creates/Modifies COM task schedule object
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 444)
Drops a file that was compiled in debug mode
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 1920)
- 2345SafeCenterInstaller.exe (PID: 3760)
Creates a directory in Program Files
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- 2345SafeCenterInstaller.exe (PID: 3760)
- 2345RTProtect.exe (PID: 2588)
Creates files in the user directory
- HaoZipLoader.exe (PID: 3316)
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 444)
- HaoZipLoader.exe (PID: 3952)
- HaoZipUpdate.exe (PID: 1232)
- 2345SafeCenterInstaller.exe (PID: 3760)
- HaoZipLoader.exe (PID: 2680)
- HaoZipLoader.exe (PID: 3864)
- HaoZipLoader.exe (PID: 2660)
- HaoZipLoader.exe (PID: 3224)
- HaoZipLoader.exe (PID: 3628)
- HaoZipUpdate.exe (PID: 2664)
- HaoZipLoader.exe (PID: 2896)
- HaoZipLoader.exe (PID: 1444)
- HaoZip.exe (PID: 4064)
- 2345RTProtect.exe (PID: 2588)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3260)
Creates a software uninstall entry
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- 2345RTProtect.exe (PID: 2588)
Changes default file association
- HaoZipLoader.exe (PID: 444)
- 2345RTProtect.exe (PID: 2588)
- 2345SafeCenterInstaller.exe (PID: 3760)
Application launched itself
- HaoZipLoader.exe (PID: 444)
Creates files in the program directory
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 1920)
- HaozipSvc.exe (PID: 2432)
- 2345SafeCenterInstaller.exe (PID: 3760)
- 2345RTProtect.exe (PID: 2588)
Executed as Windows Service
- HaozipSvc.exe (PID: 2432)
- 2345SafeCenterSvc.exe (PID: 2396)
Searches for installed software
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 2896)
- 2345SafeCenterInstaller.exe (PID: 3760)
- 2345RTProtect.exe (PID: 2588)
Reads default file associations for system extensions
- Explorer.EXE (PID: 356)
Adds / modifies Windows certificates
- 2345SafeCenterInstaller.exe (PID: 3760)
Creates or modifies windows services
- 2345SafeCenterInstaller.exe (PID: 3760)
Reads the date of Windows installation
- 2345SafeCenterInstaller.exe (PID: 3760)
- HaoZipUpdate.exe (PID: 2664)
Creates files in the Windows directory
- 2345SafeCenterInstaller.exe (PID: 3760)
Removes files from Windows directory
- 2345RTProtect.exe (PID: 2588)
Uses IPCONFIG.EXE to discover IP address
- 2345RTProtect.exe (PID: 2588)
Creates files in the driver directory
- 2345SafeCenterInstaller.exe (PID: 3760)
Starts Internet Explorer
- HaoZip.exe (PID: 4064)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2488)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3260)
INFO
Reads the computer name
- chrome.exe (PID: 2468)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 1556)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 3692)
- ipconfig.exe (PID: 1428)
- iexplore.exe (PID: 2408)
- iexplore.exe (PID: 2488)
Checks supported languages
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 1708)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 1556)
- chrome.exe (PID: 956)
- chrome.exe (PID: 1148)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 2724)
- chrome.exe (PID: 3952)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 368)
- chrome.exe (PID: 1516)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 3936)
- ipconfig.exe (PID: 1428)
- chrome.exe (PID: 3260)
- iexplore.exe (PID: 2408)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 1324)
- iexplore.exe (PID: 2488)
- chrome.exe (PID: 1916)
- chrome.exe (PID: 1156)
- chrome.exe (PID: 2116)
Application launched itself
- chrome.exe (PID: 2468)
- iexplore.exe (PID: 2408)
Reads the hosts file
- chrome.exe (PID: 2468)
- chrome.exe (PID: 2616)
Reads settings of System Certificates
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2468)
- HaoZipLoader.exe (PID: 3316)
- HaoZipLoader.exe (PID: 444)
- HaoZipLoader.exe (PID: 3952)
- HaoZipLoader.exe (PID: 1920)
- 2345SafeCenterInstaller.exe (PID: 3760)
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 1444)
- ServiceManager.exe (PID: 2200)
- HaozipSvc.exe (PID: 2432)
- HaoZip.exe (PID: 4064)
- iexplore.exe (PID: 2488)
- iexplore.exe (PID: 2408)
Reads the date of Windows installation
- chrome.exe (PID: 2432)
Checks Windows Trust Settings
- chrome.exe (PID: 2468)
- HaoZipLoader.exe (PID: 3316)
- HaoZipLoader.exe (PID: 444)
- HaoZipLoader.exe (PID: 3952)
- HaoZipLoader.exe (PID: 1920)
- 2345SafeCenterInstaller.exe (PID: 3760)
- 2345haozip_000000_6.3.1.11106.exe (PID: 1324)
- HaoZipLoader.exe (PID: 1444)
- ServiceManager.exe (PID: 2200)
- HaozipSvc.exe (PID: 2432)
- HaoZip.exe (PID: 4064)
- iexplore.exe (PID: 2488)
- iexplore.exe (PID: 2408)
Manual execution by user
- HaoZip.exe (PID: 4064)
Changes internet zones settings
- iexplore.exe (PID: 2408)
Creates files in the user directory
- iexplore.exe (PID: 2488)
Reads internet explorer settings
- iexplore.exe (PID: 2488)
Reads CPU info
- iexplore.exe (PID: 2488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
58
Malicious processes
26
Suspicious processes
0
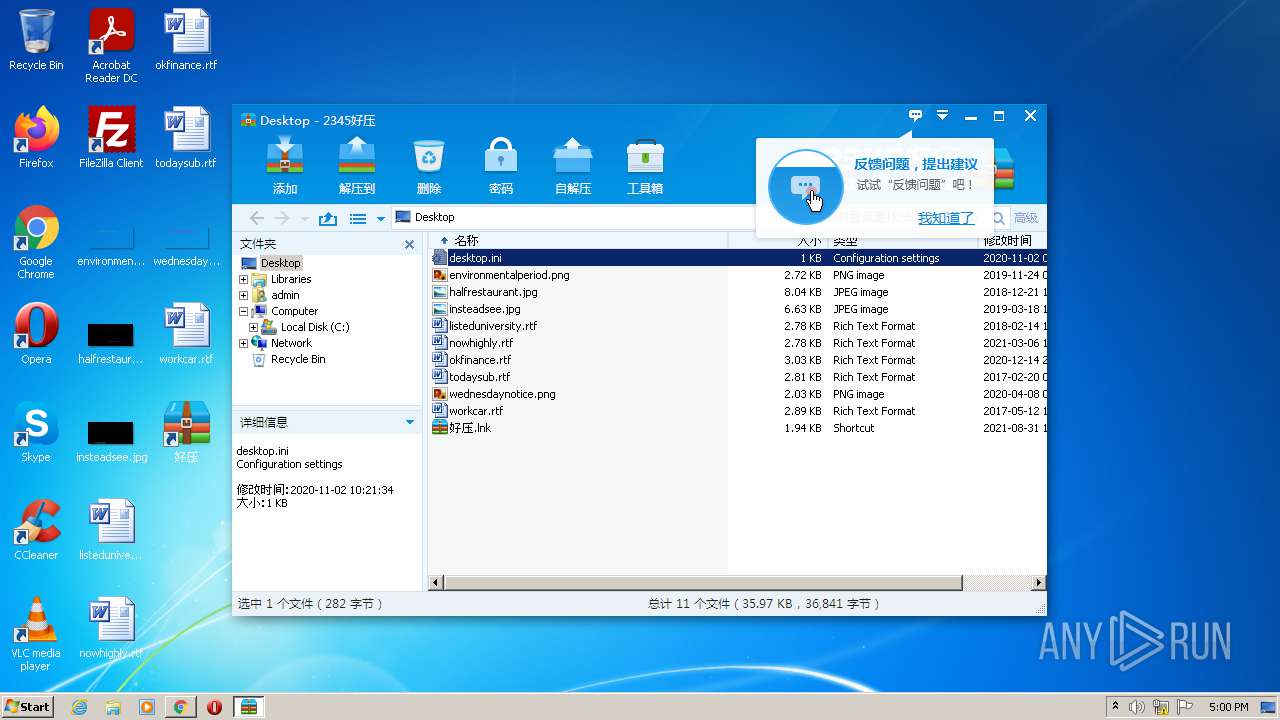
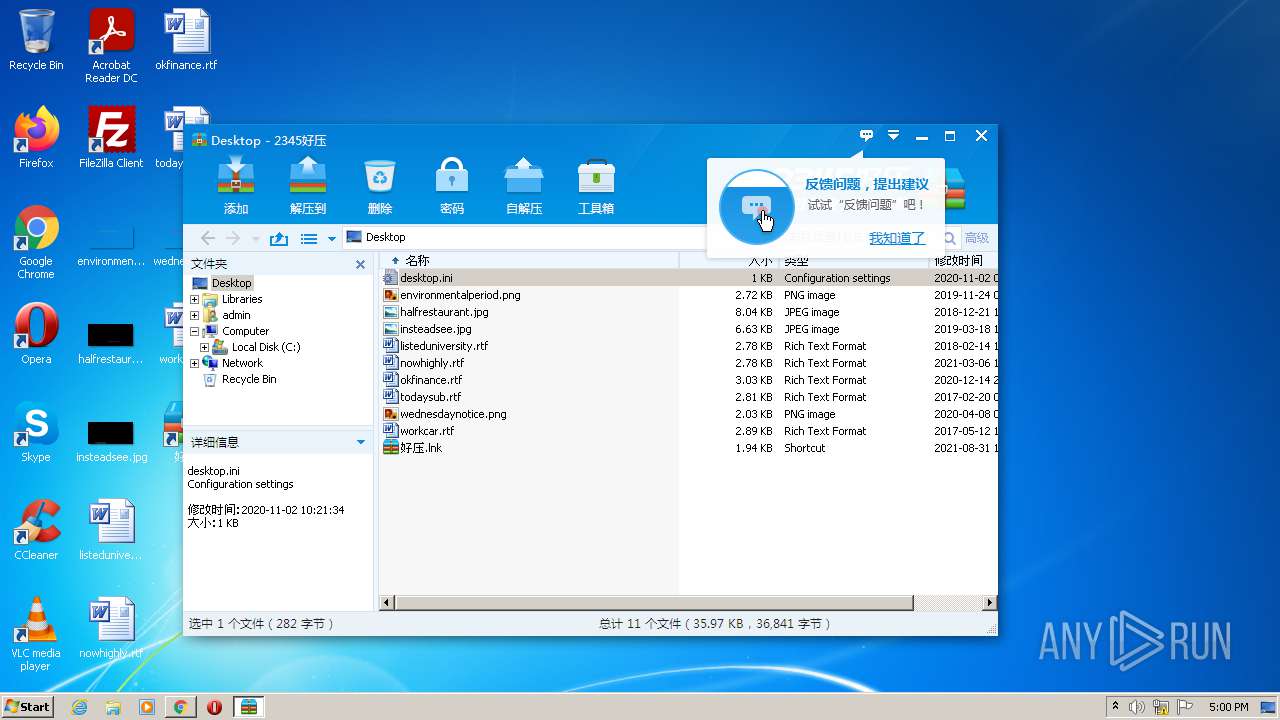
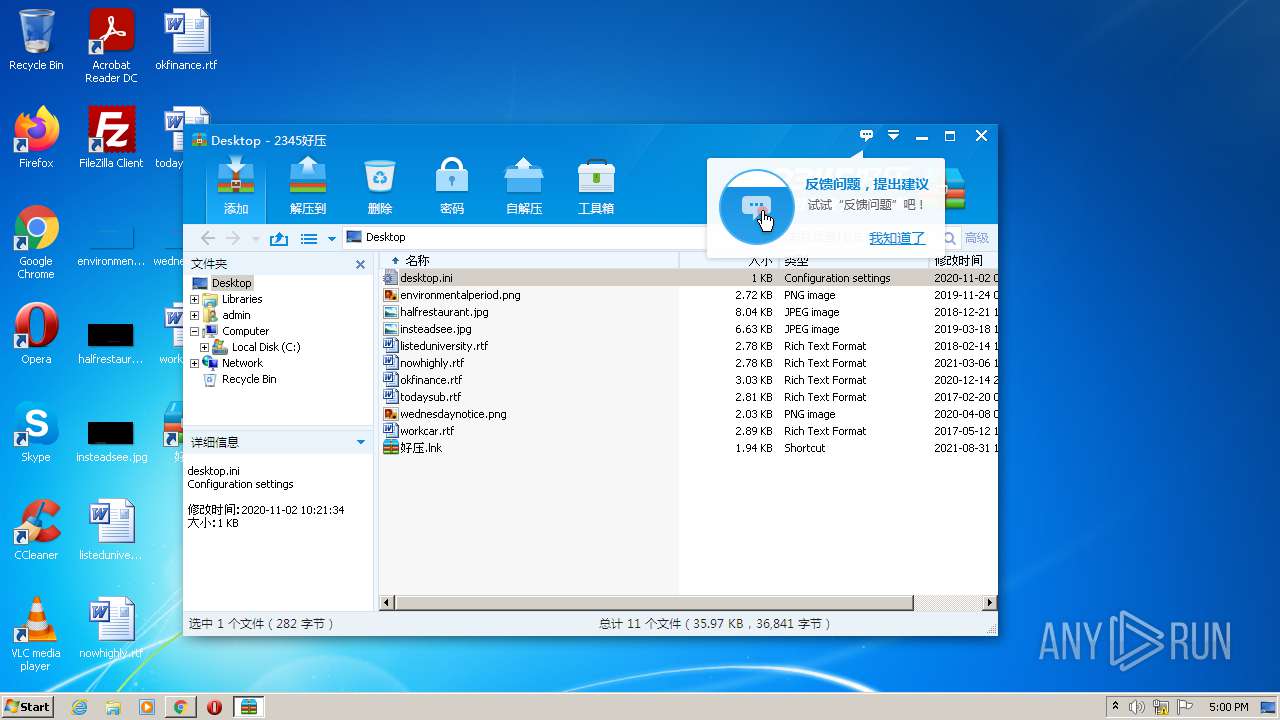
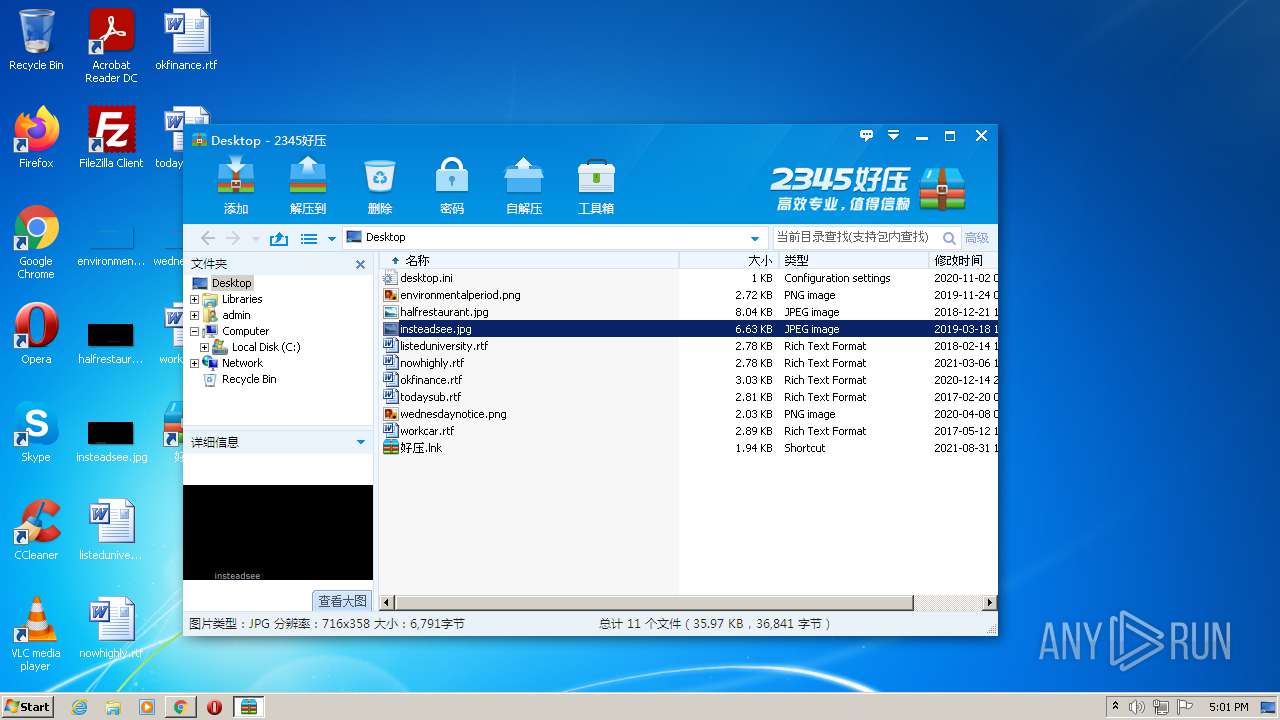
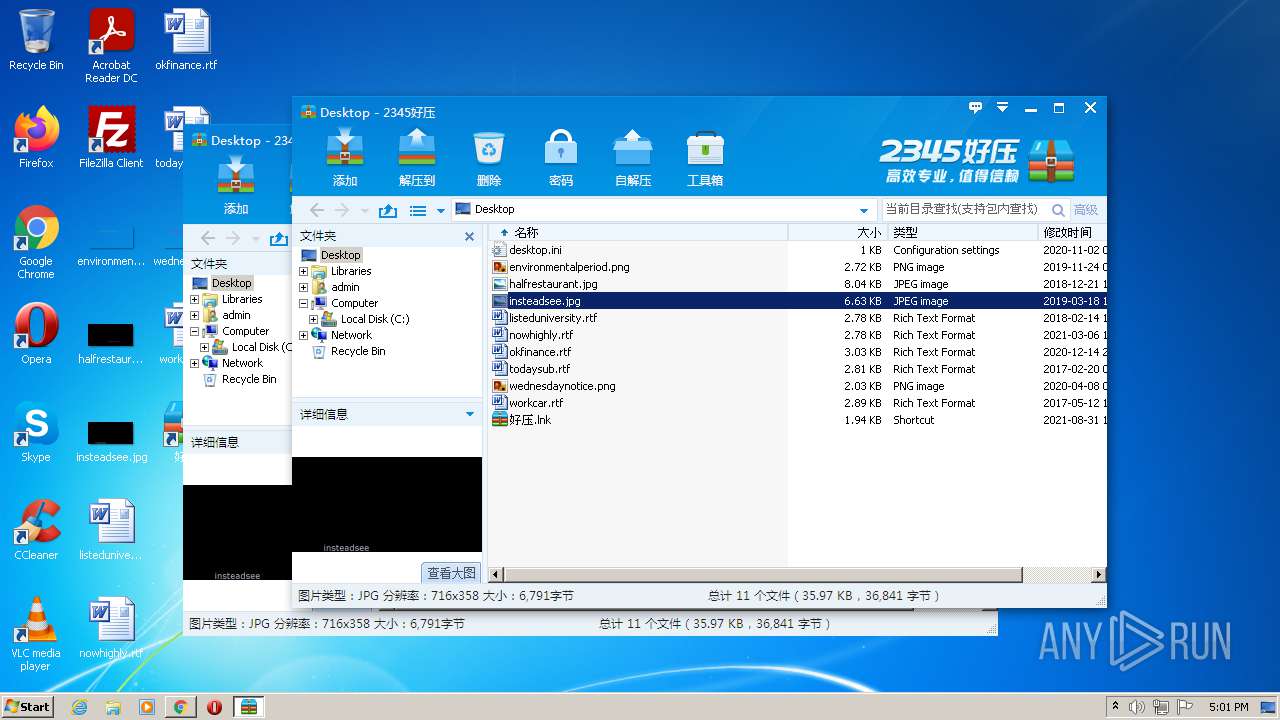
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1036,14503869676262605503,12532320340891677051,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2864 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 444 | "C:\Program Files\2345Soft\HaoZip\HaoZipLoader.exe" -install02 0 7 | C:\Program Files\2345Soft\HaoZip\HaoZipLoader.exe | — | 2345haozip_000000_6.3.1.11106.exe | |||||||||||
User: admin Company: 2345???? Integrity Level: HIGH Description: 2345??-Windows?????? Exit code: 0 Version: 6.3.1.11106 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,14503869676262605503,12532320340891677051,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,14503869676262605503,12532320340891677051,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,14503869676262605503,12532320340891677051,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\2345Soft\HaoZip\HaoZipUpdate.exe" -update-force-config | C:\Program Files\2345Soft\HaoZip\HaoZipUpdate.exe | HaoZipLoader.exe | ||||||||||||
User: admin Company: 2345???? Integrity Level: HIGH Description: 2345??-?????? Exit code: 0 Version: 6.3.1.11106 Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\Downloads\2345haozip_000000_6.3.1.11106.exe" | C:\Users\admin\Downloads\2345haozip_000000_6.3.1.11106.exe | chrome.exe | ||||||||||||
User: admin Company: 2345???? Integrity Level: HIGH Description: 2345?? v6.3 ???? Exit code: 0 Version: 6.3.1.11106 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1036,14503869676262605503,12532320340891677051,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1428 | "C:\Windows\System32\ipconfig.exe" /flushdns | C:\Windows\System32\ipconfig.exe | — | 2345RTProtect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
88 396
Read events
86 585
Write events
1 751
Delete events
60
Modification events
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
238
Suspicious files
273
Text files
213
Unknown types
55
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-612E51B9-9A4.pma | — | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7636bf39-a23e-4d62-8be1-b7df8efff1b8.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\605b173d-a063-479c-9dcb-b0074df04326.tmp | text | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF9eaa2.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\000001.dbtmp | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF9eb9c.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2468 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
81
DNS requests
42
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2616 | chrome.exe | GET | 204 | 142.250.185.163:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
1784 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/f6kstflhl4dfivcv6vynummo7i_2687/jflookgnkcckhobaglndicnbbgbonegd_2687_all_gefkllbt7qjlyah5ohtslv7spe.crx3 | US | — | — | whitelisted |
1784 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/f6kstflhl4dfivcv6vynummo7i_2687/jflookgnkcckhobaglndicnbbgbonegd_2687_all_gefkllbt7qjlyah5ohtslv7spe.crx3 | US | binary | 5.67 Kb | whitelisted |
1232 | HaoZipUpdate.exe | GET | 200 | 58.215.122.241:80 | http://img1.2345.com/2345pic/img2020/haozip/KuGou_1.png | CN | image | 3.81 Kb | malicious |
3760 | 2345SafeCenterInstaller.exe | GET | 200 | 218.12.76.150:80 | http://pcsafe.2345cdn.net/2345safecenter/2345SafeCenter_v6.14.0.10262.7z | CN | compressed | 37.2 Mb | malicious |
1784 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | binary | 7.58 Kb | whitelisted |
2616 | chrome.exe | GET | 301 | 180.163.196.53:80 | http://haozip.2345.com/ | CN | html | 162 b | malicious |
1784 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/f6kstflhl4dfivcv6vynummo7i_2687/jflookgnkcckhobaglndicnbbgbonegd_2687_all_gefkllbt7qjlyah5ohtslv7spe.crx3 | US | binary | 7.51 Kb | whitelisted |
1324 | 2345haozip_000000_6.3.1.11106.exe | POST | 200 | 180.163.56.155:80 | http://update.inst.2345.com/nindex.php | CN | text | 14.2 Kb | malicious |
3760 | 2345SafeCenterInstaller.exe | GET | 200 | 47.246.43.209:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbJNRrm8KxusAb7DCqnMkE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2616 | chrome.exe | 142.250.186.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2616 | chrome.exe | 180.163.196.53:80 | haozip.2345.com | China Telecom (Group) | CN | unknown |
2616 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 180.163.196.53:443 | haozip.2345.com | China Telecom (Group) | CN | unknown |
2616 | chrome.exe | 142.250.186.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1784 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
2616 | chrome.exe | 58.215.122.243:443 | img1.2345.com | AS Number for CHINANET jiangsu province backbone | CN | suspicious |
2616 | chrome.exe | 218.12.76.151:443 | dl.2345.com | CHINA UNICOM China169 Backbone | CN | malicious |
2616 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
2616 | chrome.exe | 142.250.185.227:443 | update.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
haozip.2345.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
haozip.2345.cc |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
img1.2345.com |
| malicious |
dl.2345.com |
| malicious |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
Process | Message |
|---|---|
HaozipSvc.exe | RpcServerUseProtseqEpW 6cc
|
2345SafeCenterSvc.exe | RpcServerUseProtseqEpW 6cc
|
2345SafeCenterSvc.exe | RpcServerUseProtseqEpW 6cc
|