| File name: | Ativador office_365.exe |
| Full analysis: | https://app.any.run/tasks/2fc26e8a-c8dc-4f11-9b6c-497748bab9e6 |
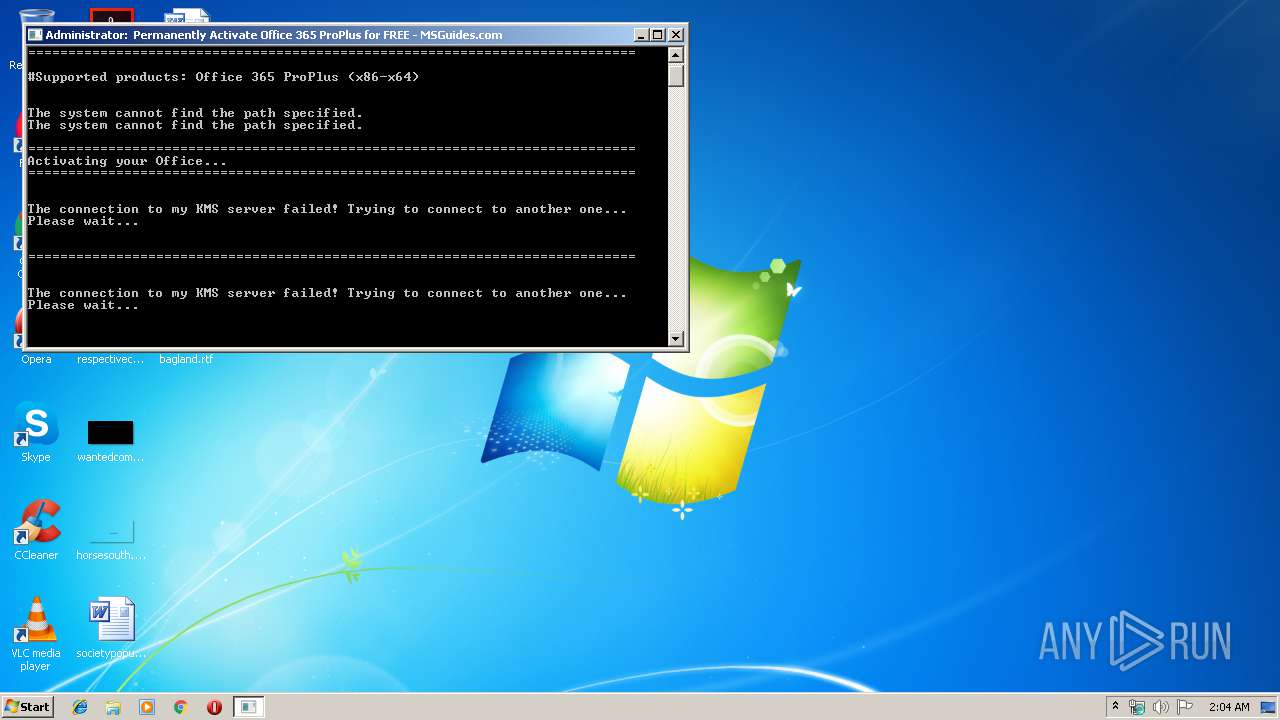
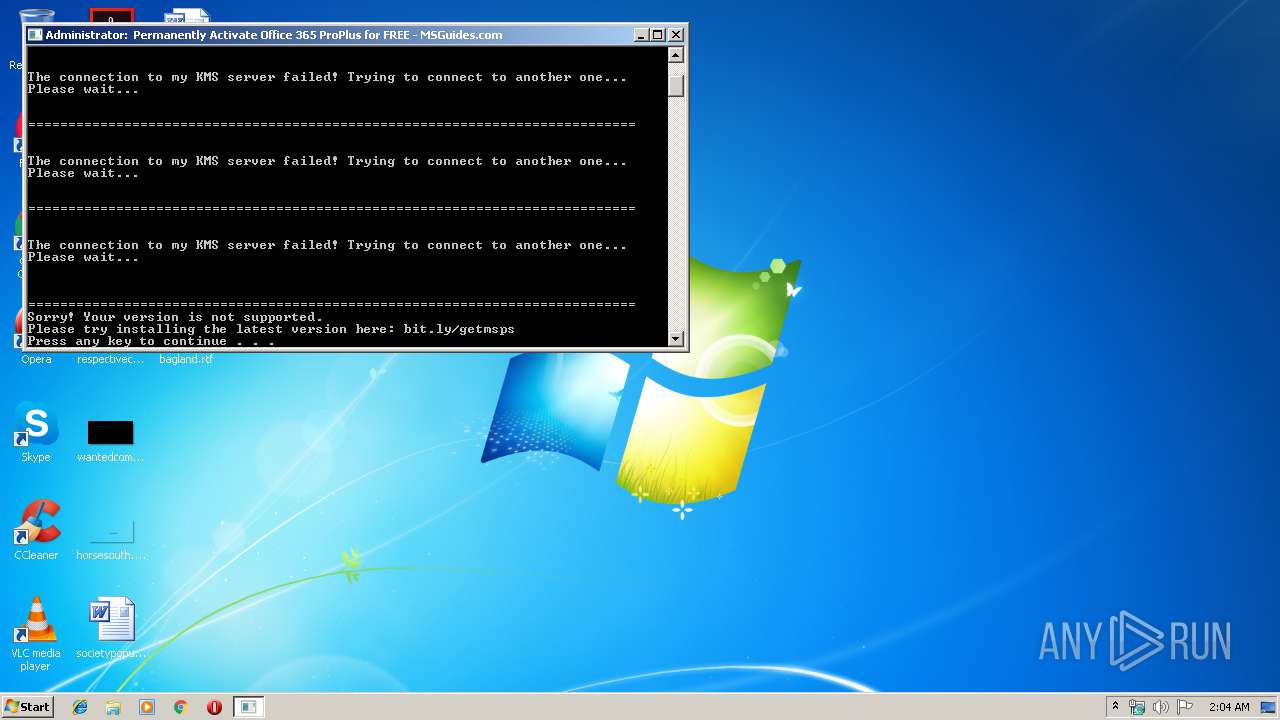
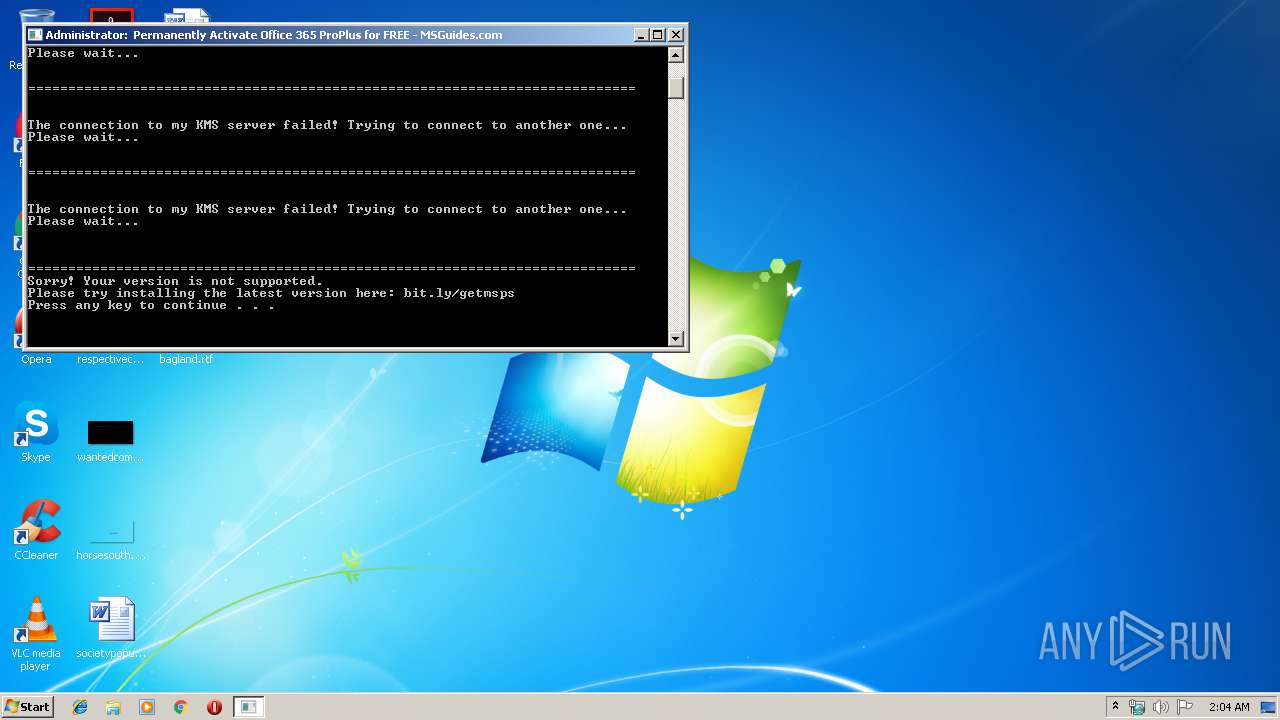
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 01:04:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C30B1FE0636647F1358336F333AA134A |
| SHA1: | A00887A03B339E864E01352C11FB4254A2F46982 |
| SHA256: | F400DF2D0BBF8BBC3B5E30327CE95C80DE44FB5CA6DE75A58BB2CA364498D9D9 |
| SSDEEP: | 24576:GTT51DZjYqEidimLZY8E4dgQu3X9r3J2rSLFeHDXDnCIjKmb7zu+IuQAsEa0j4QR:gT7DZjYWVPEXlOjrd2YxIuQAa0j7R |
MALICIOUS
Application was dropped or rewritten from another process
- 7za.exe (PID: 3000)
- nssm.exe (PID: 3636)
- nssm.exe (PID: 3200)
- nssm.exe (PID: 2984)
- nssm.exe (PID: 2316)
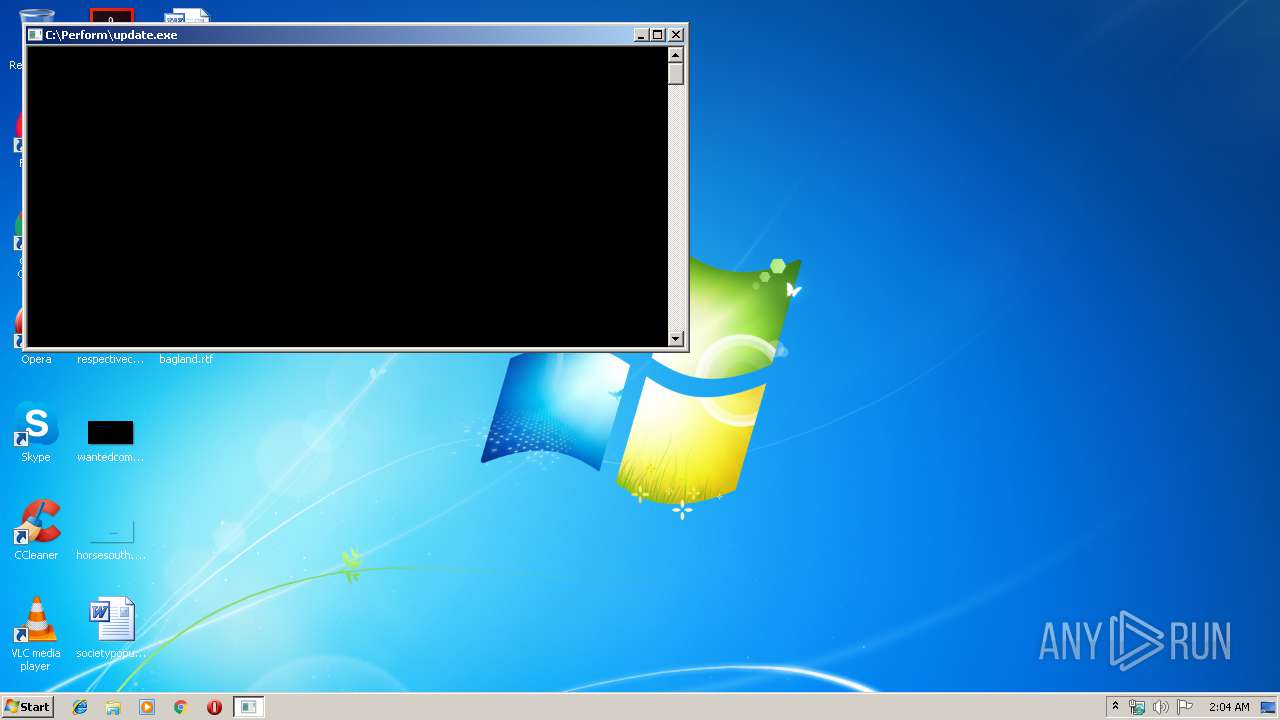
- update.exe (PID: 3548)
SUSPICIOUS
Executable content was dropped or overwritten
- cmd.exe (PID: 2252)
- Ativador office_365.exe (PID: 3416)
- 7za.exe (PID: 3000)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2252)
Starts CMD.EXE for commands execution
- Ativador office_365.exe (PID: 3416)
- update.exe (PID: 3548)
- cmd.exe (PID: 2252)
- cmd.exe (PID: 2184)
Application launched itself
- cmd.exe (PID: 2252)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2252)
Reads CPU info
- reg.exe (PID: 2256)
Executed as Windows Service
- nssm.exe (PID: 2984)
Creates files in the Windows directory
- chrome.exe (PID: 1908)
- chrome.exe (PID: 2352)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2352)
Executes scripts
- cmd.exe (PID: 2184)
Removes files from Windows directory
- chrome.exe (PID: 2352)
INFO
Application launched itself
- chrome.exe (PID: 2352)
Changes settings of System certificates
- chrome.exe (PID: 2352)
Adds / modifies Windows certificates
- chrome.exe (PID: 2352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 21:18:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 67584 |
| InitializedDataSize: | 1854976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2018 20:18:00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Feb-2018 20:18:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x000037F0 | 0x00003800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.61236 |
.text | 0x00005000 | 0x0000CFA2 | 0x0000D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58582 |
.rdata | 0x00012000 | 0x000033A0 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11024 |
.data | 0x00016000 | 0x00001724 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93749 |
.rsrc | 0x00018000 | 0x001C0644 | 0x001C0800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.94452 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08821 | 672 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
499EAC9E2C932885FC00CDCD69FA881EED886541 | 4.58496 | 24 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
50BB4E42A9904E8849FA4D5E242CD61D | 7.92369 | 2156 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
61E371062064F5FC3C50F44BDA918A88 | 3.41938 | 18 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
64C020C886 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
C7EF0516E9FC026BB00C6636BBAD84993451A52E | 7.99948 | 381856 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
CAD1E16F664191773BB760AA42ADBD80 | 6.17235 | 90 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
DAA49F67841EF1772D19B9C474CBB432586EA8C6 | 7.99988 | 1383082 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
127
Monitored processes
87
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2714827248300939912,10343784185842613901,131072 --service-pipe-token=10374514192270922083 --lang=ru --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10374514192270922083 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,2714827248300939912,10343784185842613901,131072 --lang=ru --service-sandbox-type=utility --service-request-channel-token=10707796348388176574 --mojo-platform-channel-handle=4392 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,2714827248300939912,10343784185842613901,131072 --lang=ru --service-sandbox-type=utility --service-request-channel-token=10407703429198340244 --mojo-platform-channel-handle=5560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x80,0x84,0x88,0x7c,0x8c,0x6de60f18,0x6de60f28,0x6de60f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: SYSTEM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,2714827248300939912,10343784185842613901,131072 --lang=ru --service-sandbox-type=utility --service-request-channel-token=12455332956433863278 --mojo-platform-channel-handle=5180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2714827248300939912,10343784185842613901,131072 --service-pipe-token=980009227239647376 --lang=ru --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=980009227239647376 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2168 | C:\Windows\system32\cmd.exe /c dir /b ..\root\Licenses16\proplusvl_mak*.xrm-ms | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2184 | cmd /c ""C:\Users\admin\AppData\Local\Temp\F21F.tmp\Ativador office +365.bat" C:\Perform\update.exe" | C:\Windows\system32\cmd.exe | — | update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2188 | wmic cpu get numberofcores | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,2714827248300939912,10343784185842613901,131072 --lang=ru --service-sandbox-type=utility --service-request-channel-token=17872269934530735332 --mojo-platform-channel-handle=5864 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
713
Read events
584
Write events
126
Delete events
3
Modification events
| (PID) Process: | (3416) Ativador office_365.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3416) Ativador office_365.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3636) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Perform\nssm.exe | |||
| (PID) Process: | (3636) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
| (PID) Process: | (3636) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Advanced Systemcare Security\Parameters |
| Operation: | write | Name: | Application |
Value: C:\Program Files\Google\Chrome\Application\chrome.exe | |||
| (PID) Process: | (3636) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Advanced Systemcare Security\Parameters |
| Operation: | write | Name: | AppParameters |
Value: http://maiscurso.net/ | |||
| (PID) Process: | (3636) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Advanced Systemcare Security\Parameters |
| Operation: | write | Name: | AppDirectory |
Value: C:\Program Files\Google\Chrome\Application | |||
| (PID) Process: | (3636) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\Advanced Systemcare Security\Parameters\AppExit |
| Operation: | write | Name: | |
Value: Restart | |||
| (PID) Process: | (2984) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Perform\nssm.exe | |||
| (PID) Process: | (2984) nssm.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\NSSM |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
Executable files
9
Suspicious files
17
Text files
532
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2352 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2352 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2352 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2352 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2352 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2352 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3416 | Ativador office_365.exe | C:\Users\admin\AppData\Local\Temp\EE75.tmp\EE76.tmp\EE87.bat | text | |
MD5:— | SHA256:— | |||
| 2352 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
| 2352 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2352 | chrome.exe | C:\Windows\system32\config\systemprofile\AppData\Local\Google\Chrome\User Data\First Run | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
13
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2352 | chrome.exe | GET | 200 | 108.179.193.143:80 | http://maiscurso.net/ | US | html | 7.59 Kb | unknown |
2352 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
2352 | chrome.exe | GET | 200 | 173.194.183.72:80 | http://r3---sn-aigl6ned.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYzU3QUFWbnlGT3kzQWtjM3lqNzVJallBUQ/1.0.0.4_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=217.147.89.18&mm=28&mn=sn-aigl6ned&ms=nvh&mt=1560906202&mv=m&pl=22&shardbypass=yes | US | crx | 184 Kb | whitelisted |
2352 | chrome.exe | GET | 200 | 173.194.5.41:80 | http://r4---sn-aigzrn7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=217.147.89.18&mm=28&mn=sn-aigzrn7e&ms=nvh&mt=1560906202&mv=m&pl=22&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2352 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYzU3QUFWbnlGT3kzQWtjM3lqNzVJallBUQ/1.0.0.4_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 499 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2352 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 108.179.193.143:80 | maiscurso.net | CyrusOne LLC | US | unknown |
2352 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 173.194.5.41:80 | r4---sn-aigzrn7e.gvt1.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 216.58.207.42:443 | www.googleapis.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.23.142:443 | docs.google.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 173.194.183.72:80 | r3---sn-aigl6ned.gvt1.com | Google Inc. | US | whitelisted |
2352 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
maiscurso.net |
| unknown |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-aigl6ned.gvt1.com |
| whitelisted |
r4---sn-aigzrn7e.gvt1.com |
| whitelisted |
www.googleapis.com |
| whitelisted |