| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/1a6ab41e-e748-4f00-a351-5dcb8c531d8e |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2024, 22:00:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9C973EECAEFE165E1BB7F0095B8D7A3A |
| SHA1: | 2E3BDCEF1064AD0895BFF2E123B13248B294E7CF |
| SHA256: | F3C6C126F64957FFA2AEB6595F81D7A377EABCCDEA962AAF27F5CADD8AA4F726 |
| SSDEEP: | 98304:9m/SMPUQ+/uMLYOCFpAOLX46e/h//oShmxel+YxjyqcQmJQoUa2X8zJneB+peJNi:mRgmLvD4y9dOQ |
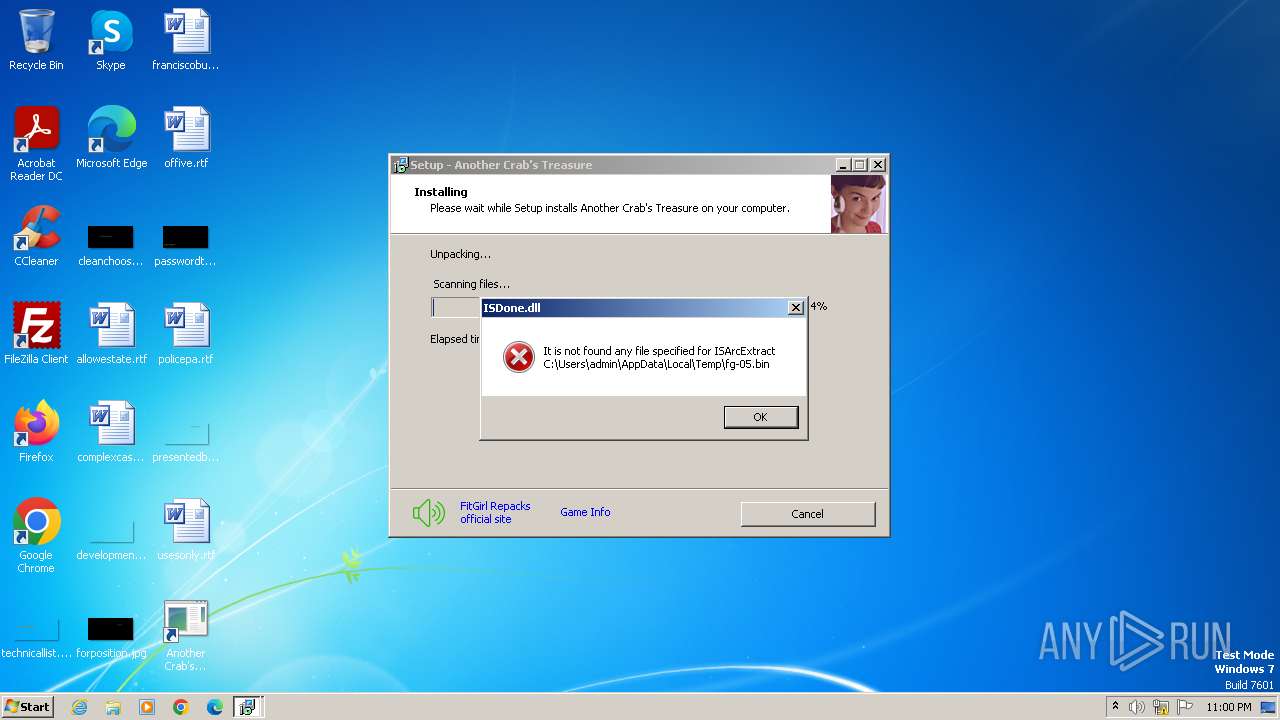
MALICIOUS
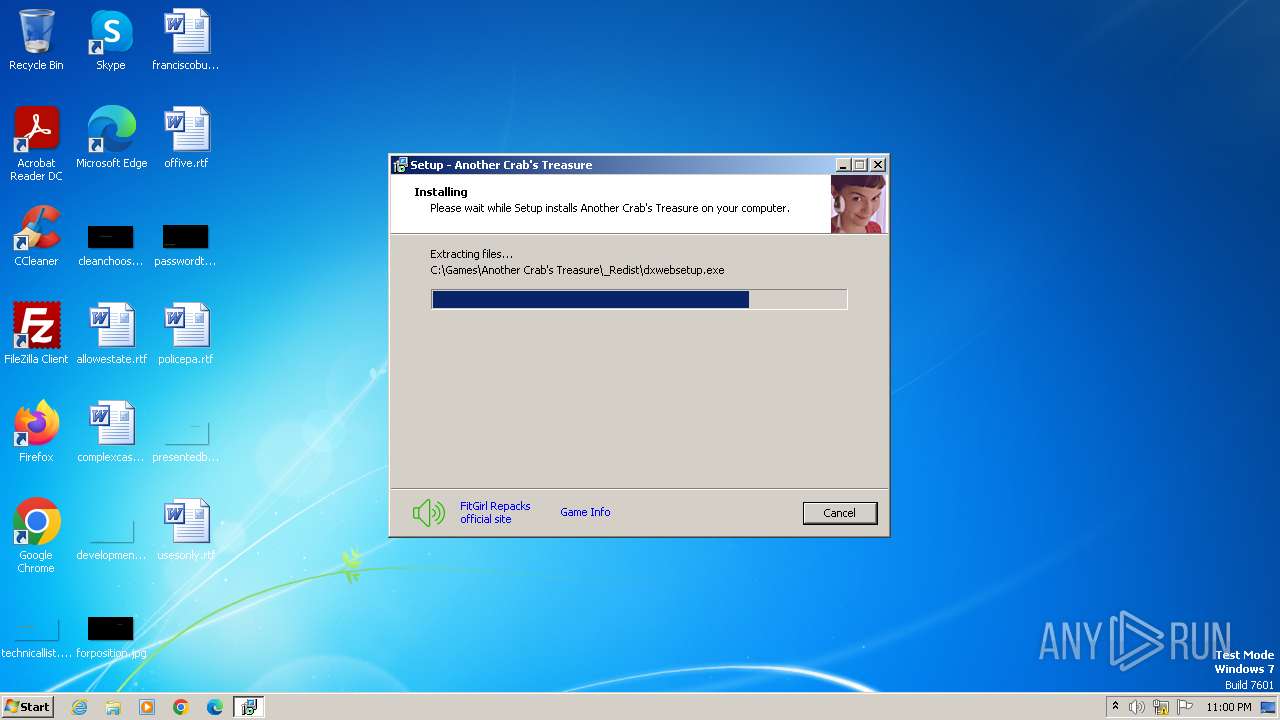
Drops the executable file immediately after the start
- setup.exe (PID: 4076)
- setup.tmp (PID: 4092)
- unins000.exe (PID: 1592)
- _iu14D2N.tmp (PID: 1604)
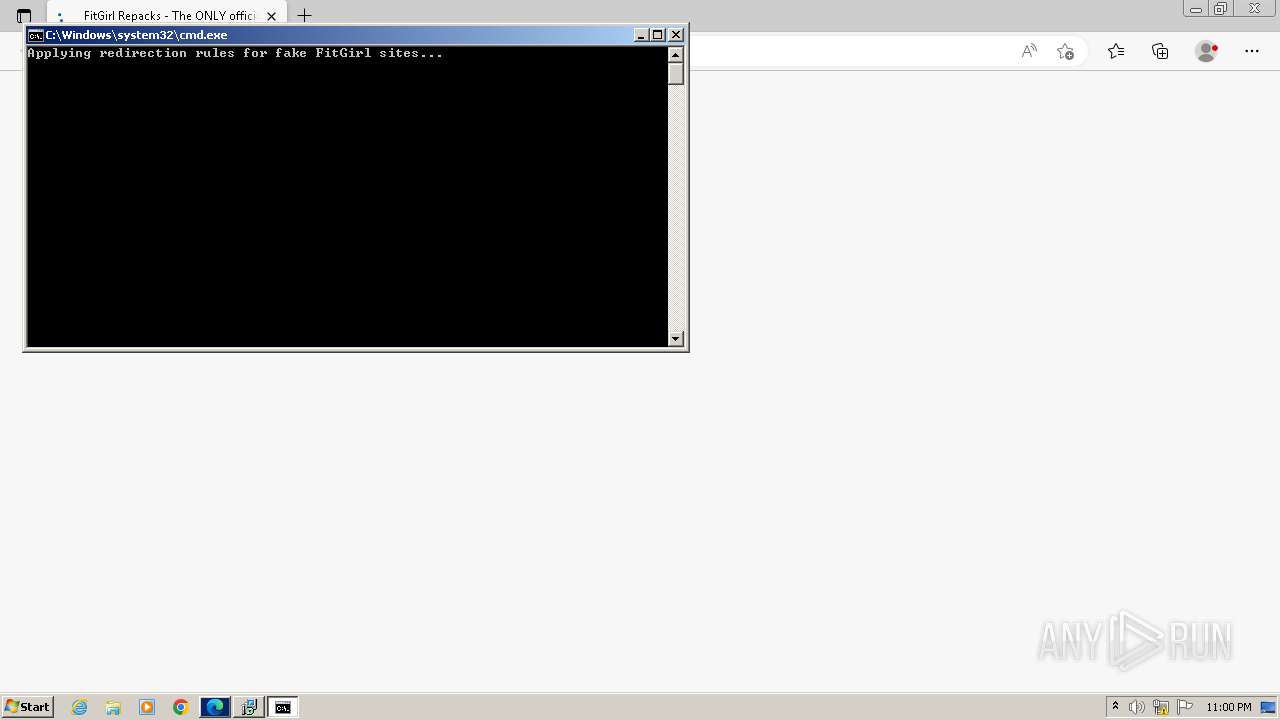
Creates a writable file in the system directory
- hosts.exe (PID: 1932)
- hosts.exe (PID: 2232)
- hosts.exe (PID: 2256)
- hosts.exe (PID: 2196)
- hosts.exe (PID: 1072)
- hosts.exe (PID: 1940)
- hosts.exe (PID: 2516)
- hosts.exe (PID: 992)
- hosts.exe (PID: 1012)
- hosts.exe (PID: 1576)
- hosts.exe (PID: 2660)
- hosts.exe (PID: 2780)
- hosts.exe (PID: 2768)
- hosts.exe (PID: 2792)
- hosts.exe (PID: 3008)
- hosts.exe (PID: 2896)
- hosts.exe (PID: 2940)
- hosts.exe (PID: 2736)
- hosts.exe (PID: 3044)
- hosts.exe (PID: 3256)
- hosts.exe (PID: 3260)
- hosts.exe (PID: 3400)
- hosts.exe (PID: 3440)
- hosts.exe (PID: 3808)
- hosts.exe (PID: 3572)
- hosts.exe (PID: 3908)
- hosts.exe (PID: 3828)
- hosts.exe (PID: 3640)
- hosts.exe (PID: 4016)
- hosts.exe (PID: 4044)
- hosts.exe (PID: 1020)
- hosts.exe (PID: 4000)
- hosts.exe (PID: 1440)
- hosts.exe (PID: 588)
- hosts.exe (PID: 552)
- hosts.exe (PID: 1080)
- hosts.exe (PID: 2364)
- hosts.exe (PID: 2368)
- hosts.exe (PID: 736)
- hosts.exe (PID: 1804)
SUSPICIOUS
Process drops legitimate windows executable
- setup.tmp (PID: 4092)
- _iu14D2N.tmp (PID: 1604)
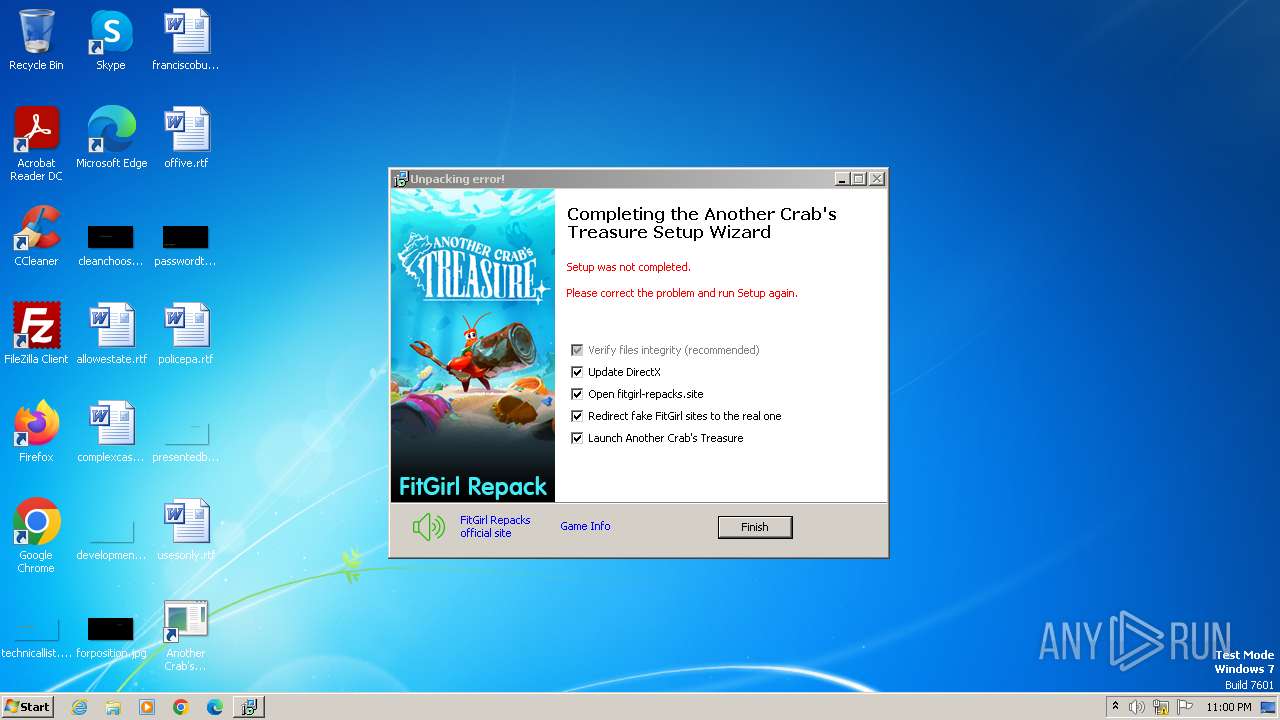
Executable content was dropped or overwritten
- setup.exe (PID: 4076)
- setup.tmp (PID: 4092)
- unins000.exe (PID: 1592)
- _iu14D2N.tmp (PID: 1604)
Reads the Windows owner or organization settings
- setup.tmp (PID: 4092)
- _iu14D2N.tmp (PID: 1604)
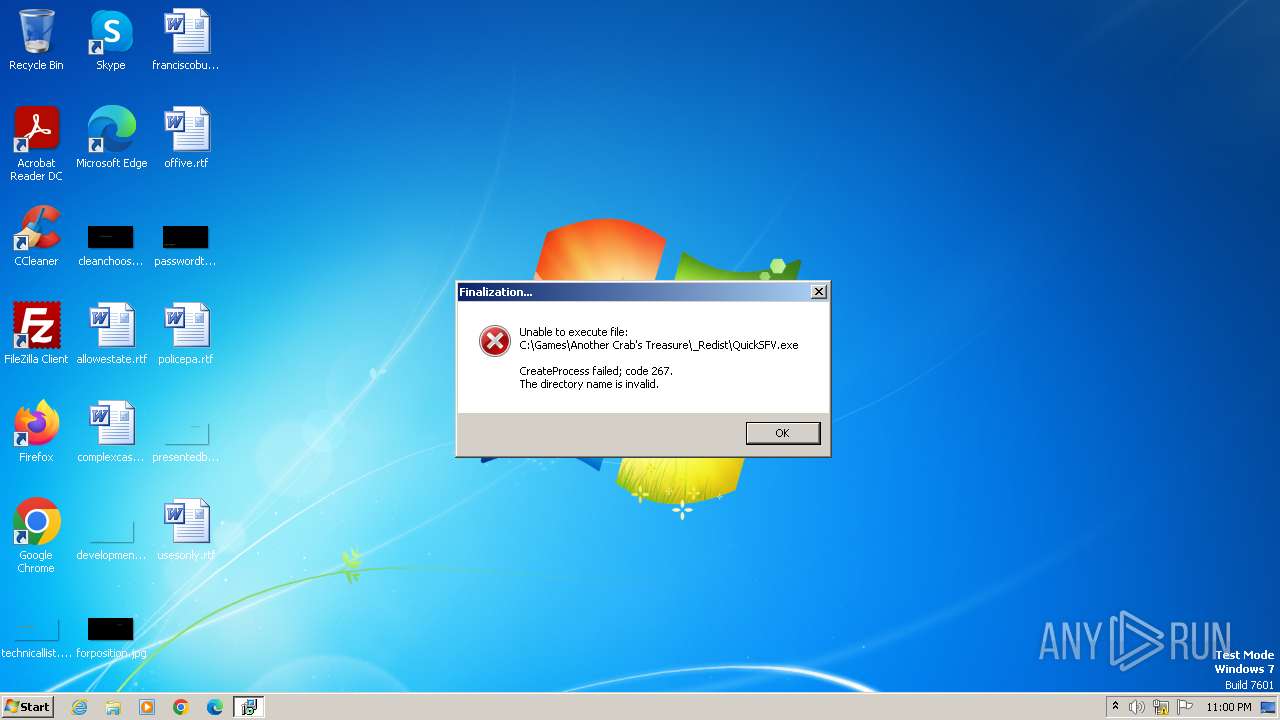
Starts itself from another location
- unins000.exe (PID: 1592)
Starts application with an unusual extension
- unins000.exe (PID: 1592)
The executable file from the user directory is run by the CMD process
- hosts.exe (PID: 1932)
- hosts.exe (PID: 2256)
- hosts.exe (PID: 2196)
- hosts.exe (PID: 1072)
- hosts.exe (PID: 2232)
- hosts.exe (PID: 1940)
- hosts.exe (PID: 2516)
- hosts.exe (PID: 992)
- hosts.exe (PID: 1012)
- hosts.exe (PID: 1576)
- hosts.exe (PID: 2660)
- hosts.exe (PID: 2768)
- hosts.exe (PID: 2780)
- hosts.exe (PID: 2792)
- hosts.exe (PID: 2940)
- hosts.exe (PID: 3008)
- hosts.exe (PID: 2896)
- hosts.exe (PID: 2736)
- hosts.exe (PID: 3260)
- hosts.exe (PID: 3044)
- hosts.exe (PID: 3440)
- hosts.exe (PID: 3256)
- hosts.exe (PID: 3400)
- hosts.exe (PID: 3808)
- hosts.exe (PID: 3572)
- hosts.exe (PID: 3640)
- hosts.exe (PID: 3828)
- hosts.exe (PID: 4000)
- hosts.exe (PID: 3908)
- hosts.exe (PID: 4016)
- hosts.exe (PID: 4044)
- hosts.exe (PID: 1020)
- hosts.exe (PID: 1440)
- hosts.exe (PID: 588)
- hosts.exe (PID: 552)
- hosts.exe (PID: 1080)
- hosts.exe (PID: 2364)
- hosts.exe (PID: 2368)
- hosts.exe (PID: 736)
- hosts.exe (PID: 1804)
Reads the Internet Settings
- setup.tmp (PID: 4092)
Reads the date of Windows installation
- _iu14D2N.tmp (PID: 1604)
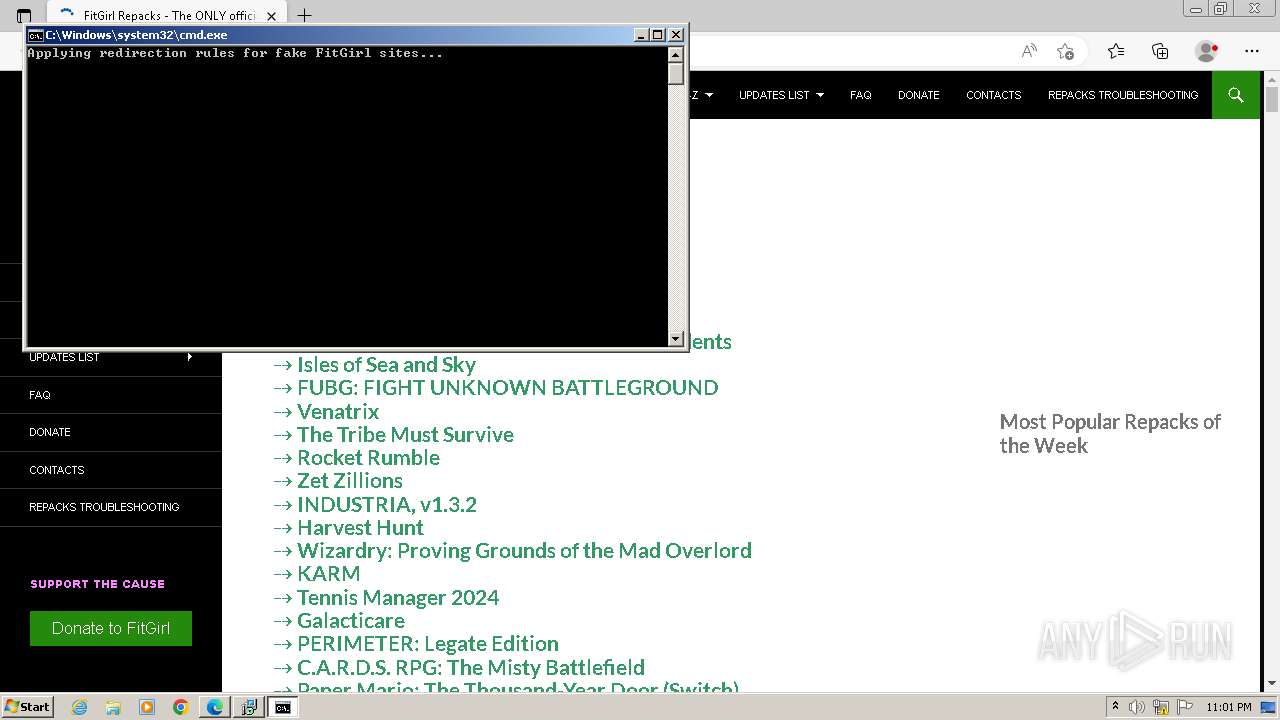
Starts CMD.EXE for commands execution
- setup.tmp (PID: 4092)
Executing commands from ".cmd" file
- setup.tmp (PID: 4092)
Creates files in the driver directory
- hosts.exe (PID: 1932)
- hosts.exe (PID: 2232)
- hosts.exe (PID: 2256)
- hosts.exe (PID: 2196)
- hosts.exe (PID: 1072)
- hosts.exe (PID: 1940)
- hosts.exe (PID: 2516)
- hosts.exe (PID: 992)
- hosts.exe (PID: 1012)
- hosts.exe (PID: 1576)
- hosts.exe (PID: 2660)
- hosts.exe (PID: 2768)
- hosts.exe (PID: 2780)
- hosts.exe (PID: 2792)
- hosts.exe (PID: 2940)
- hosts.exe (PID: 3008)
- hosts.exe (PID: 2896)
- hosts.exe (PID: 2736)
- hosts.exe (PID: 3044)
- hosts.exe (PID: 3256)
- hosts.exe (PID: 3260)
- hosts.exe (PID: 3440)
- hosts.exe (PID: 3400)
- hosts.exe (PID: 3808)
- hosts.exe (PID: 3572)
- hosts.exe (PID: 3908)
- hosts.exe (PID: 3828)
- hosts.exe (PID: 3640)
- hosts.exe (PID: 4016)
- hosts.exe (PID: 1020)
- hosts.exe (PID: 4000)
- hosts.exe (PID: 1440)
- hosts.exe (PID: 588)
- hosts.exe (PID: 552)
- hosts.exe (PID: 4044)
- hosts.exe (PID: 1080)
- hosts.exe (PID: 2364)
- hosts.exe (PID: 2368)
- hosts.exe (PID: 736)
- hosts.exe (PID: 1804)
INFO
Checks supported languages
- setup.exe (PID: 4076)
- setup.tmp (PID: 4092)
- FlushFileCache.exe (PID: 1056)
- unins000.exe (PID: 1592)
- _iu14D2N.tmp (PID: 1604)
- hosts.exe (PID: 1932)
- hosts.exe (PID: 2256)
- hosts.exe (PID: 2196)
- hosts.exe (PID: 2232)
- hosts.exe (PID: 1940)
- hosts.exe (PID: 2516)
- hosts.exe (PID: 1072)
- hosts.exe (PID: 1012)
- hosts.exe (PID: 1576)
- hosts.exe (PID: 992)
- hosts.exe (PID: 2660)
- hosts.exe (PID: 2780)
- hosts.exe (PID: 2768)
- hosts.exe (PID: 2792)
- hosts.exe (PID: 2940)
- hosts.exe (PID: 3008)
- hosts.exe (PID: 2896)
- hosts.exe (PID: 3260)
- hosts.exe (PID: 3044)
- hosts.exe (PID: 2736)
- hosts.exe (PID: 3440)
- hosts.exe (PID: 3256)
- hosts.exe (PID: 3400)
- hosts.exe (PID: 3808)
- hosts.exe (PID: 3572)
- hosts.exe (PID: 3640)
- hosts.exe (PID: 3908)
- hosts.exe (PID: 3828)
- hosts.exe (PID: 4000)
- hosts.exe (PID: 4016)
- hosts.exe (PID: 1020)
- hosts.exe (PID: 4044)
- hosts.exe (PID: 1440)
- hosts.exe (PID: 588)
- hosts.exe (PID: 552)
- hosts.exe (PID: 1080)
- hosts.exe (PID: 2364)
- hosts.exe (PID: 2368)
- hosts.exe (PID: 736)
- hosts.exe (PID: 1804)
- wmpnscfg.exe (PID: 1676)
Create files in a temporary directory
- setup.exe (PID: 4076)
- setup.tmp (PID: 4092)
- unins000.exe (PID: 1592)
- _iu14D2N.tmp (PID: 1604)
Reads the computer name
- setup.tmp (PID: 4092)
- FlushFileCache.exe (PID: 1056)
- hosts.exe (PID: 1932)
- _iu14D2N.tmp (PID: 1604)
- hosts.exe (PID: 2232)
- hosts.exe (PID: 2256)
- hosts.exe (PID: 2196)
- hosts.exe (PID: 1072)
- hosts.exe (PID: 1940)
- hosts.exe (PID: 2516)
- hosts.exe (PID: 1012)
- hosts.exe (PID: 1576)
- hosts.exe (PID: 992)
- hosts.exe (PID: 2660)
- hosts.exe (PID: 2768)
- hosts.exe (PID: 2780)
- hosts.exe (PID: 2792)
- hosts.exe (PID: 2940)
- hosts.exe (PID: 3008)
- hosts.exe (PID: 2896)
- hosts.exe (PID: 3044)
- hosts.exe (PID: 2736)
- hosts.exe (PID: 3440)
- hosts.exe (PID: 3260)
- hosts.exe (PID: 3256)
- hosts.exe (PID: 3400)
- hosts.exe (PID: 3640)
- hosts.exe (PID: 3808)
- hosts.exe (PID: 3572)
- hosts.exe (PID: 3908)
- hosts.exe (PID: 3828)
- hosts.exe (PID: 4000)
- hosts.exe (PID: 4016)
- hosts.exe (PID: 1020)
- hosts.exe (PID: 4044)
- hosts.exe (PID: 552)
- hosts.exe (PID: 1440)
- hosts.exe (PID: 588)
- hosts.exe (PID: 2368)
- hosts.exe (PID: 1080)
- hosts.exe (PID: 2364)
- hosts.exe (PID: 736)
- hosts.exe (PID: 1804)
- wmpnscfg.exe (PID: 1676)
Creates a software uninstall entry
- setup.tmp (PID: 4092)
Application launched itself
- msedge.exe (PID: 1948)
- msedge.exe (PID: 2640)
Reads the machine GUID from the registry
- hosts.exe (PID: 1932)
- hosts.exe (PID: 2232)
- hosts.exe (PID: 2256)
- hosts.exe (PID: 2196)
- hosts.exe (PID: 1072)
- hosts.exe (PID: 1940)
- hosts.exe (PID: 2516)
- hosts.exe (PID: 992)
- hosts.exe (PID: 1012)
- hosts.exe (PID: 1576)
- hosts.exe (PID: 2660)
- hosts.exe (PID: 2768)
- hosts.exe (PID: 2780)
- hosts.exe (PID: 2792)
- hosts.exe (PID: 2940)
- hosts.exe (PID: 3008)
- hosts.exe (PID: 2896)
- hosts.exe (PID: 3044)
- hosts.exe (PID: 2736)
- hosts.exe (PID: 3256)
- hosts.exe (PID: 3260)
- hosts.exe (PID: 3440)
- hosts.exe (PID: 3400)
- hosts.exe (PID: 3808)
- hosts.exe (PID: 3572)
- hosts.exe (PID: 3908)
- hosts.exe (PID: 3828)
- hosts.exe (PID: 3640)
- hosts.exe (PID: 4000)
- hosts.exe (PID: 4016)
- hosts.exe (PID: 1020)
- hosts.exe (PID: 4044)
- hosts.exe (PID: 1440)
- hosts.exe (PID: 588)
- hosts.exe (PID: 1080)
- hosts.exe (PID: 2364)
- hosts.exe (PID: 2368)
- hosts.exe (PID: 552)
- hosts.exe (PID: 736)
- hosts.exe (PID: 1804)
Manual execution by a user
- msedge.exe (PID: 2640)
- wmpnscfg.exe (PID: 1676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
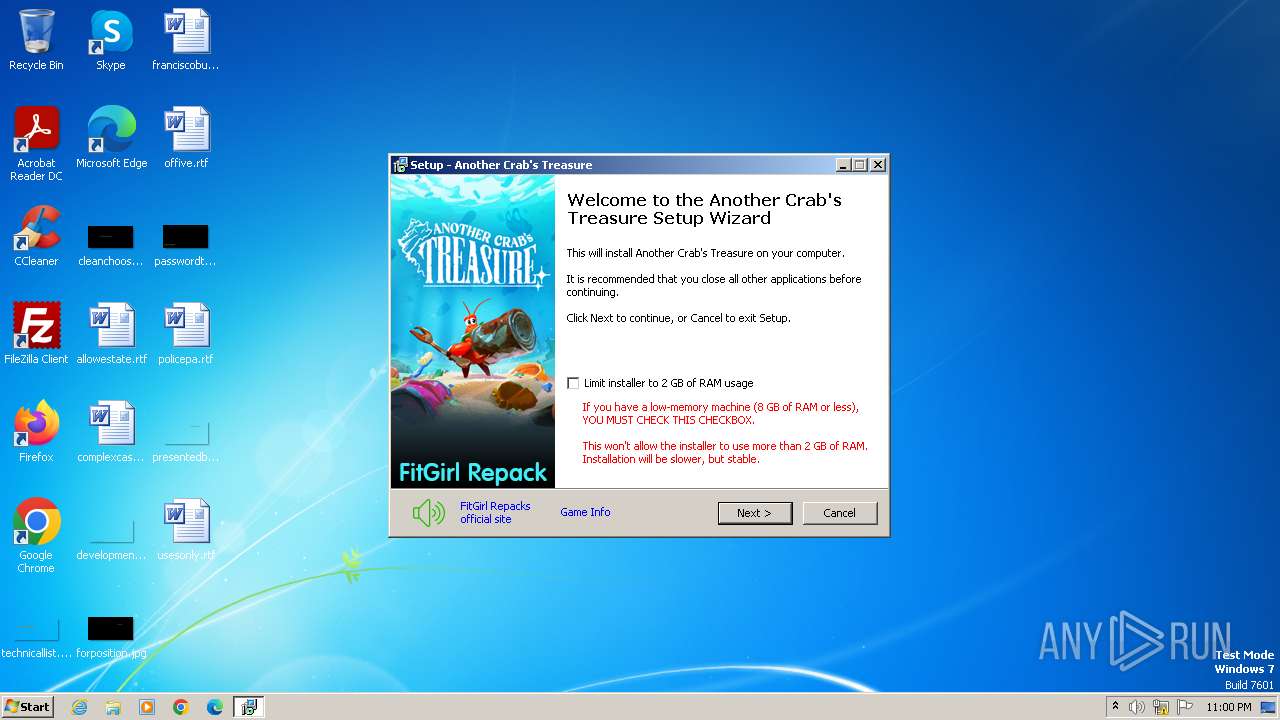
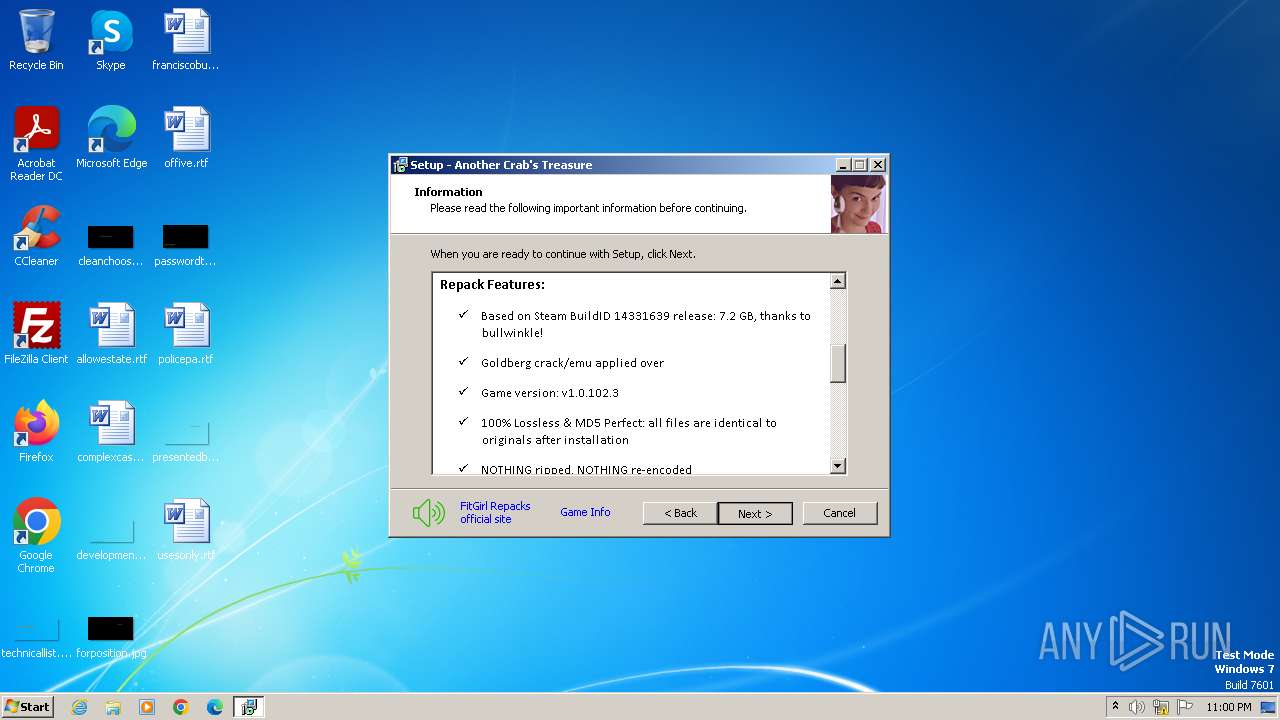
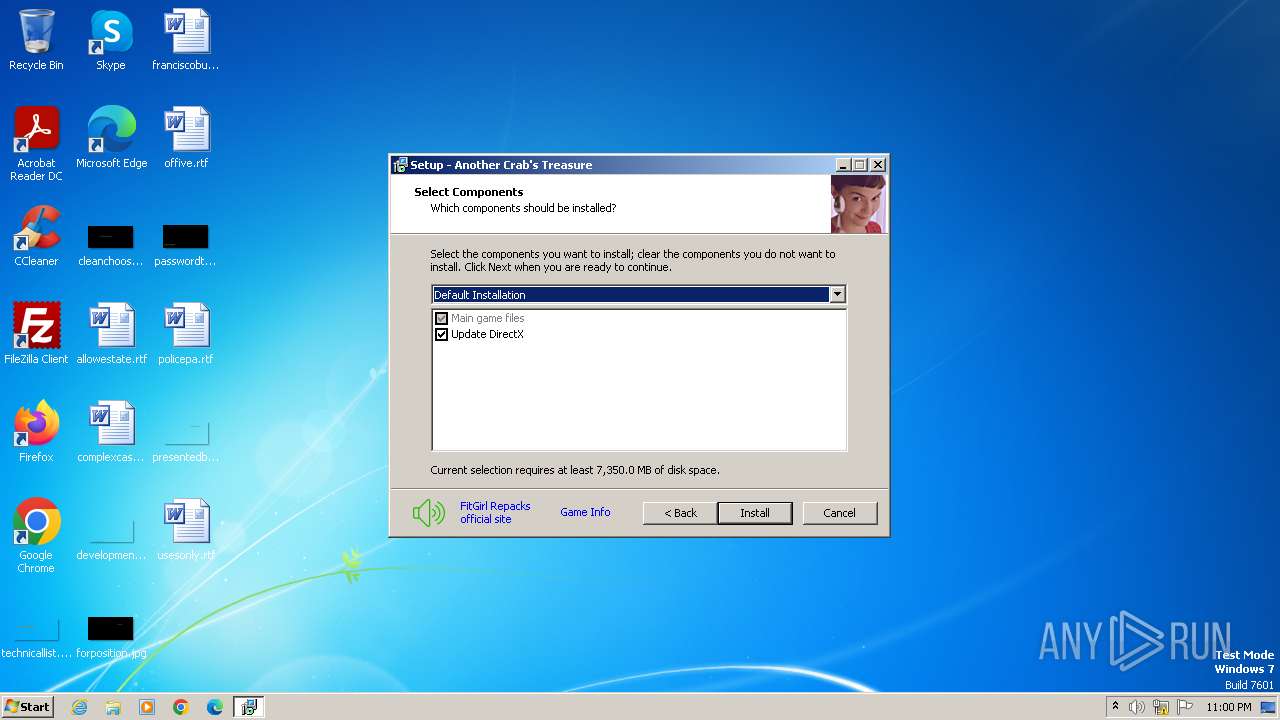
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 05:04:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Another Crab's Treasure Setup |
| FileVersion: | |
| LegalCopyright: | FitGirl |
| ProductName: | Another Crab's Treasure |
| ProductVersion: |
Total processes
110
Monitored processes
71
Malicious processes
5
Suspicious processes
40
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 524 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=1452 --field-trial-handle=1292,i,206442813257584355,16124661650137324458,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
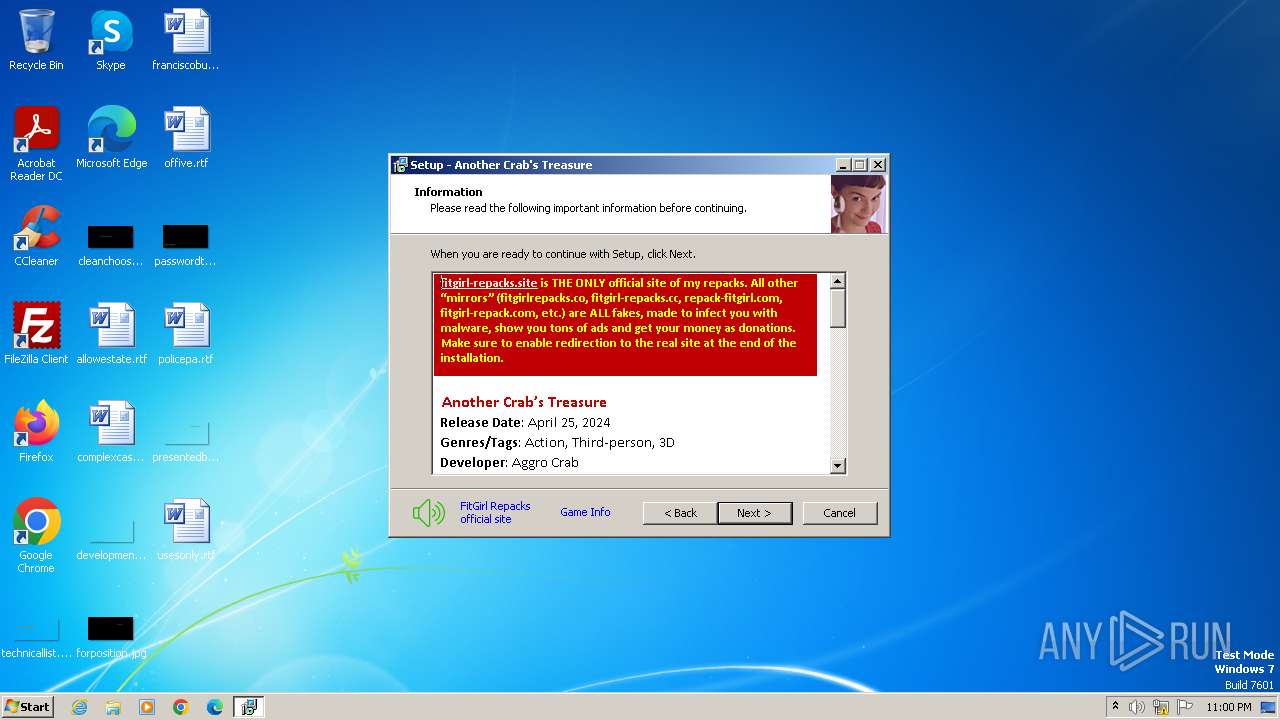
| 552 | hosts.exe add www.fitgirlrepacks.org 109.94.209.70 # Fake FitGirl site | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\hosts.exe | — | cmd.exe | |||||||||||
User: admin Company: Vegalogic Software Integrity Level: HIGH Description: Hosts Commander Exit code: 0 Version: 1.6.1.0 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6c28f598,0x6c28f5a8,0x6c28f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 588 | hosts.exe add www.fitgirlrepack.cc 109.94.209.70 # Fake FitGirl site | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\hosts.exe | — | cmd.exe | |||||||||||
User: admin Company: Vegalogic Software Integrity Level: HIGH Description: Hosts Commander Exit code: 0 Version: 1.6.1.0 Modules
| |||||||||||||||
| 736 | hosts.exe add www.fitgirl-repacks.net 109.94.209.70 # Fake FitGirl site | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\hosts.exe | — | cmd.exe | |||||||||||
User: admin Company: Vegalogic Software Integrity Level: HIGH Description: Hosts Commander Exit code: 0 Version: 1.6.1.0 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1392 --field-trial-handle=1328,i,2223132274783823181,6698391975792226295,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1196 --field-trial-handle=1328,i,2223132274783823181,6698391975792226295,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1244 --field-trial-handle=1292,i,206442813257584355,16124661650137324458,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 992 | hosts.exe add fitgirlrepack.games 109.94.209.70 # Fake FitGirl site | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\hosts.exe | — | cmd.exe | |||||||||||
User: admin Company: Vegalogic Software Integrity Level: HIGH Description: Hosts Commander Exit code: 0 Version: 1.6.1.0 Modules
| |||||||||||||||
| 1012 | hosts.exe add www.fitgirlrepacks.co 109.94.209.70 # Fake FitGirl site | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\hosts.exe | — | cmd.exe | |||||||||||
User: admin Company: Vegalogic Software Integrity Level: HIGH Description: Hosts Commander Exit code: 0 Version: 1.6.1.0 Modules
| |||||||||||||||
Total events
21 746
Read events
21 497
Write events
231
Delete events
18
Modification events
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: FC0F00004E161E4281B0DA01 | |||
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 2199E461B88739958FA0A3727F34DCECCDBE065DECB4210E9EA830EEE8808E59 | |||
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
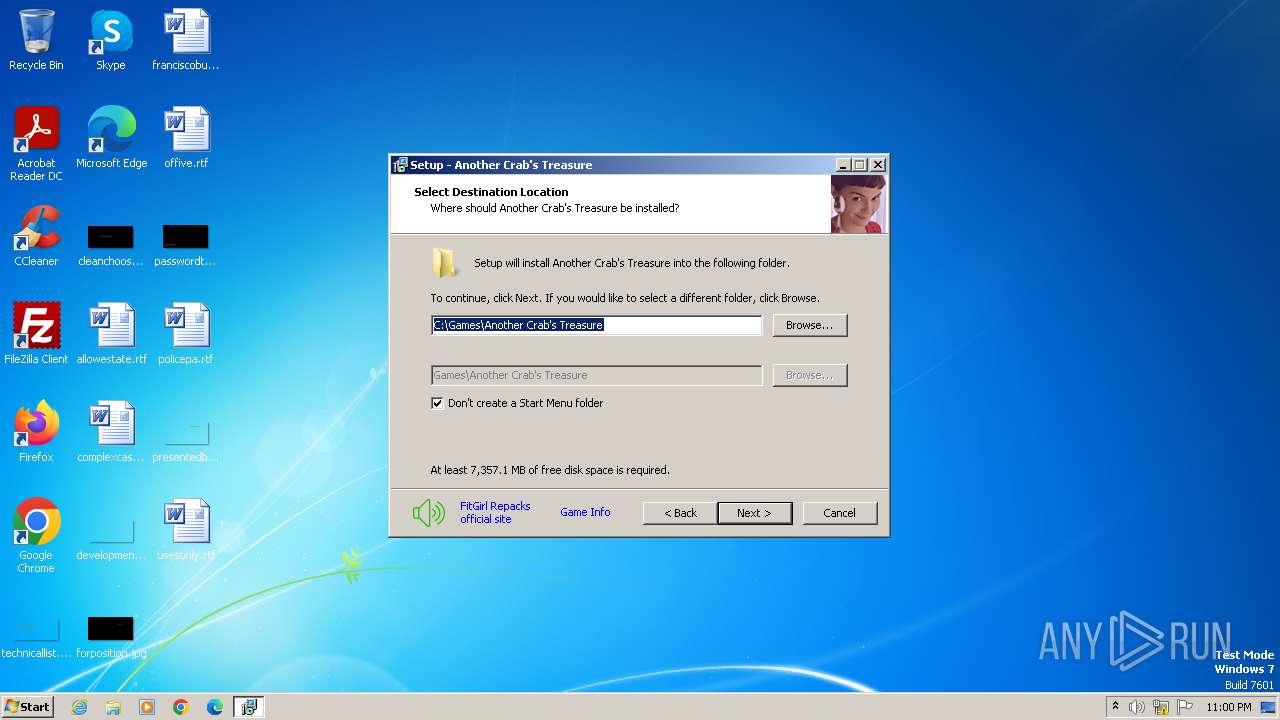
Value: C:\Games\Another Crab's Treasure\_Redist\dxwebsetup.exe | |||
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 119778309048AD8410E676E717A8EAC6DA015F7AB9A1C51F1AB49CEEB57F2BB7 | |||
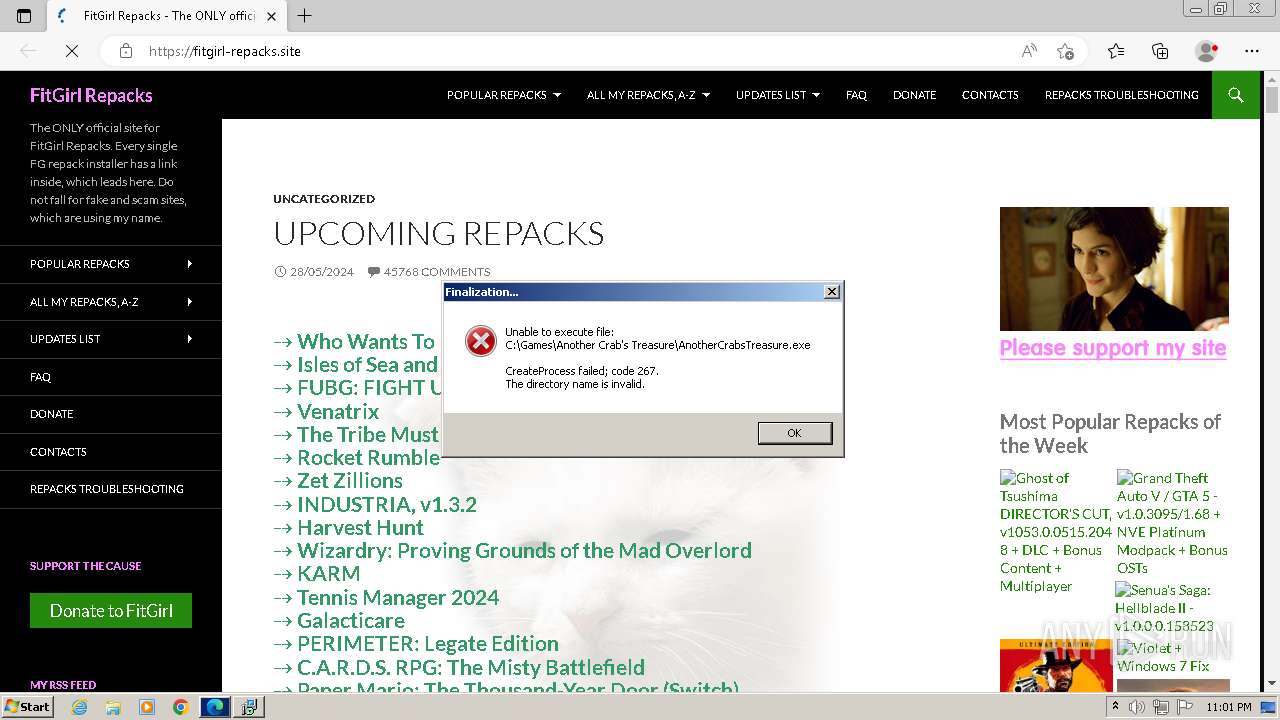
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Games\Another Crab's Treasure\AnotherCrabsTreasure.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Games\Another Crab's Treasure\AnotherCrabsTreasure.exe |
Value: RUNASADMIN | |||
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Another Crab's Treasure_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1.ee2 (u) | |||
| (PID) Process: | (4092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Another Crab's Treasure_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Games\Another Crab's Treasure | |||
Executable files
41
Suspicious files
81
Text files
108
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4076 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-D8O36.tmp\setup.tmp | executable | |
MD5:AE9890548F2FCAB56A4E9AE446F55B3F | SHA256:09AF8004B85478E1ECA09FA4CB5E3081DDDCB2F68A353F3EF6849D92BE47B449 | |||
| 4092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\cls-lollypop_x86.exe | executable | |
MD5:3527C6739C46F4EE1CFB6B48E1407883 | SHA256:724C6E07180E321298B4EA4405C3F7536C524D9826D24F5D6FC50BCB0EF8F723 | |||
| 4092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\idp.dll | executable | |
MD5:AF555AC9C073F88FE5BF0D677F085025 | SHA256:F4FC0187491A9CB89E233197FF72C2405B5EC02E8B8EA640EE68D034DDBC44BB | |||
| 4092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\wintb.dll | executable | |
MD5:9436DF49E08C83BAD8DDC906478C2041 | SHA256:1910537AA95684142250CA0C7426A0B5F082E39F6FBDBDBA649AECB179541435 | |||
| 4092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\BASS.dll | executable | |
MD5:8005750EC63EB5292884AD6183AE2E77 | SHA256:DF9F56C4DA160101567B0526845228EE481EE7D2F98391696FA27FE41F8ACF15 | |||
| 4092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\cls-lollypop.dll | executable | |
MD5:0EF04BC15FD1B28975AFF2951B857F03 | SHA256:F84677643D9977AA1E8A4AA8C85A12665D29A4E8292485A0B4DF846DD161F824 | |||
| 4092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\cls-lollypop_x64.exe | executable | |
MD5:5B848A24126F54A2C3C7B7393B536D33 | SHA256:2D32C4F4522BC62F63C7949313434F6CA0EAA6B65B44EE5AA8B6B877988B1AA8 | |||
| 4092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 4092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\cls-magic2_x86.exe | executable | |
MD5:7CBE7DB7FC9258B6A43551140C343BB3 | SHA256:6EA07AA4F5565AC289402ADE3B2E52BF8089AD6185E0ECF0E1F36CEA39C091A9 | |||
| 4092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-6REA4.tmp\cls-srep_x86.exe | executable | |
MD5:FC7DD2CA9F47D64EDD3B2061CD8DB1B3 | SHA256:4004BA624F8CE381C61C82ABA26E246D93E833357930C17CD4B02058EA31FAD4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
65
DNS requests
90
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2732 | msedge.exe | GET | 301 | 67.199.248.10:80 | http://bit.ly/fitgirl-repacks-site | unknown | — | — | unknown |
2732 | msedge.exe | GET | 301 | 190.115.31.179:80 | http://fitgirl-repacks.site/ | unknown | — | — | unknown |
2732 | msedge.exe | GET | 200 | 2.23.197.184:80 | http://r3.i.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
2640 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
2732 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2732 | msedge.exe | 67.199.248.10:80 | bit.ly | GOOGLE-CLOUD-PLATFORM | US | shared |
2732 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2732 | msedge.exe | 67.199.248.11:80 | bit.ly | GOOGLE-CLOUD-PLATFORM | US | shared |
2732 | msedge.exe | 190.115.31.179:80 | fitgirl-repacks.site | DDOS-GUARD CORP. | BZ | unknown |
2732 | msedge.exe | 190.115.31.179:443 | fitgirl-repacks.site | DDOS-GUARD CORP. | BZ | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
bit.ly |
| shared |
edge.microsoft.com |
| whitelisted |
fitgirl-repacks.site |
| unknown |
stats.wp.com |
| whitelisted |
www.youtube.com |
| whitelisted |
i4.imageban.ru |
| unknown |
i2.imageban.ru |
| unknown |
i5.imageban.ru |
| unknown |
i1.imageban.ru |
| unknown |