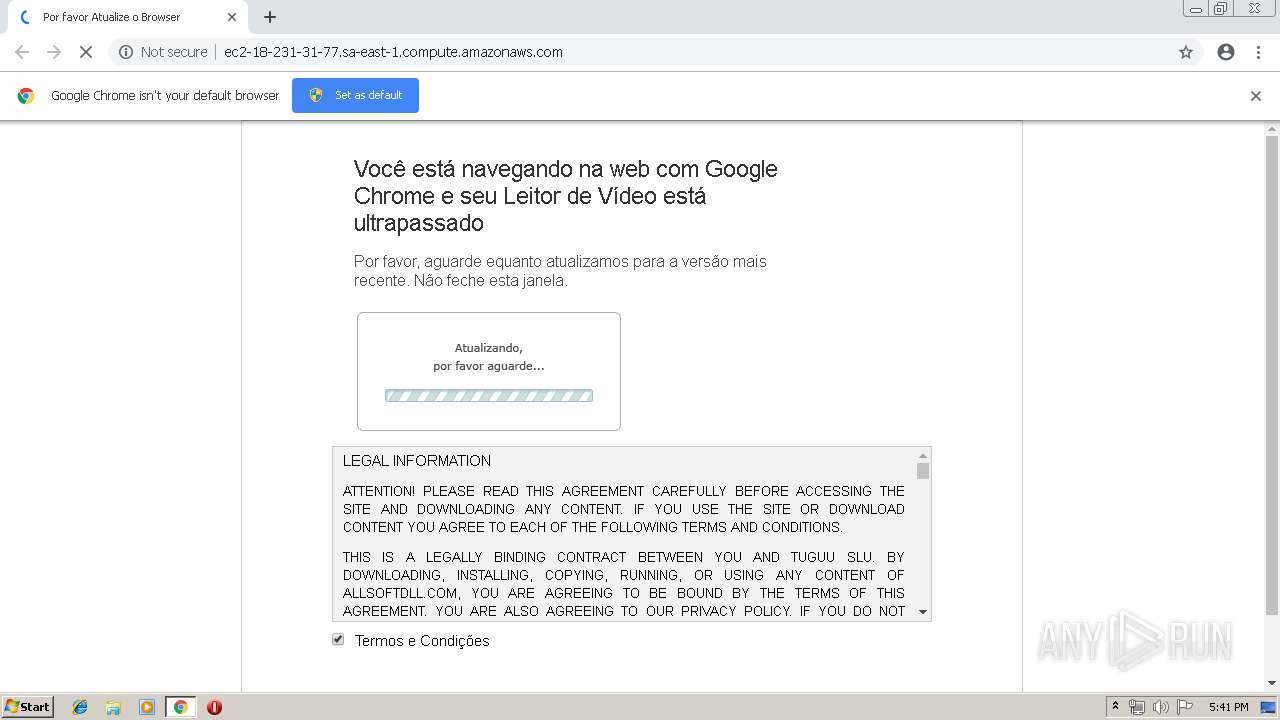
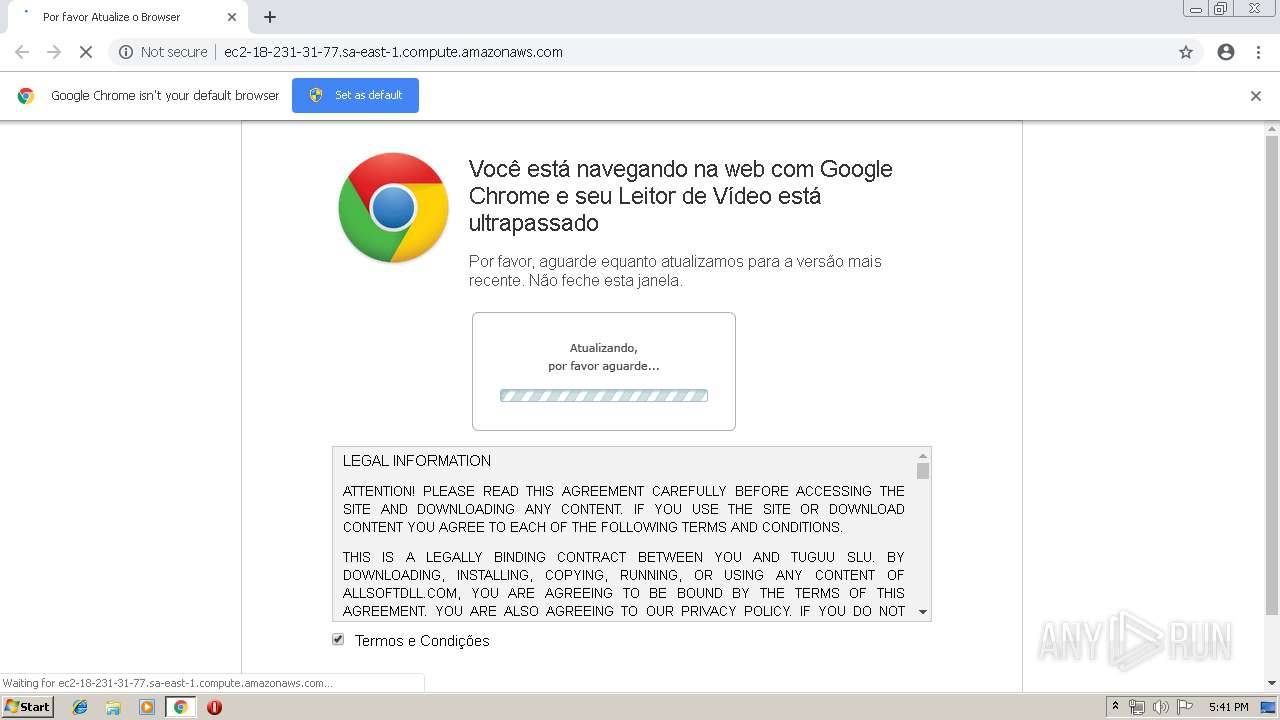
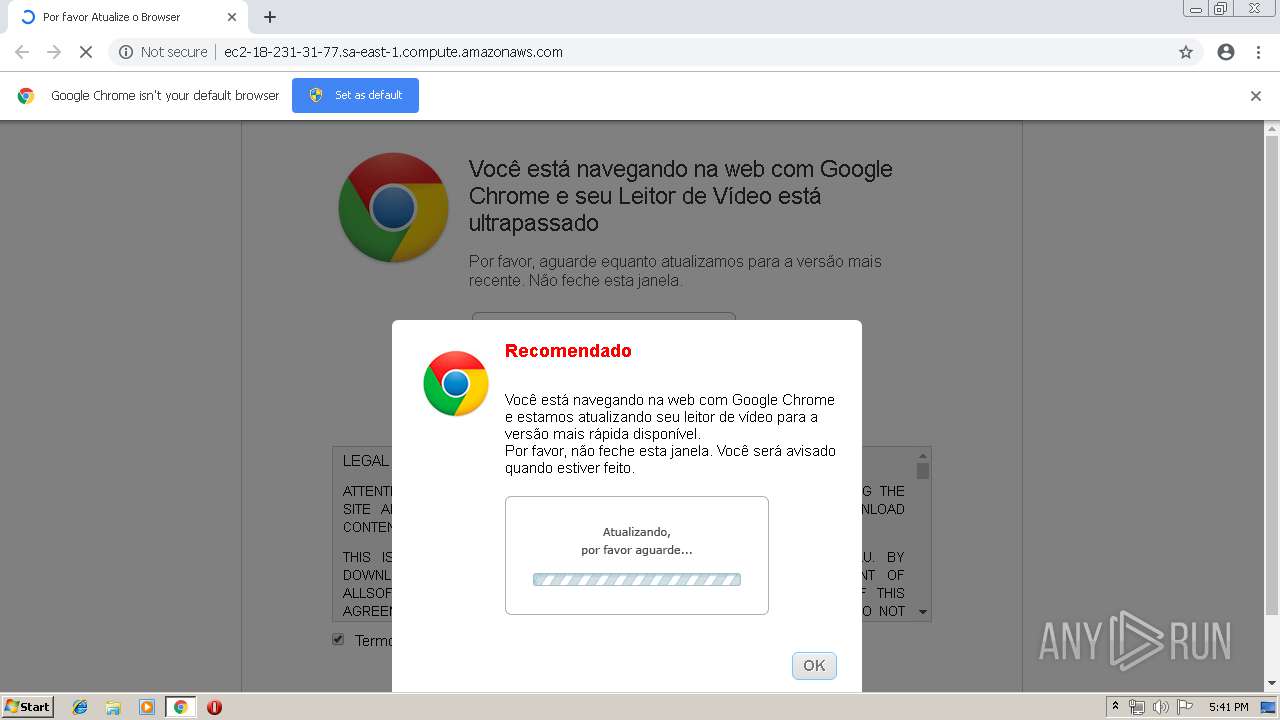
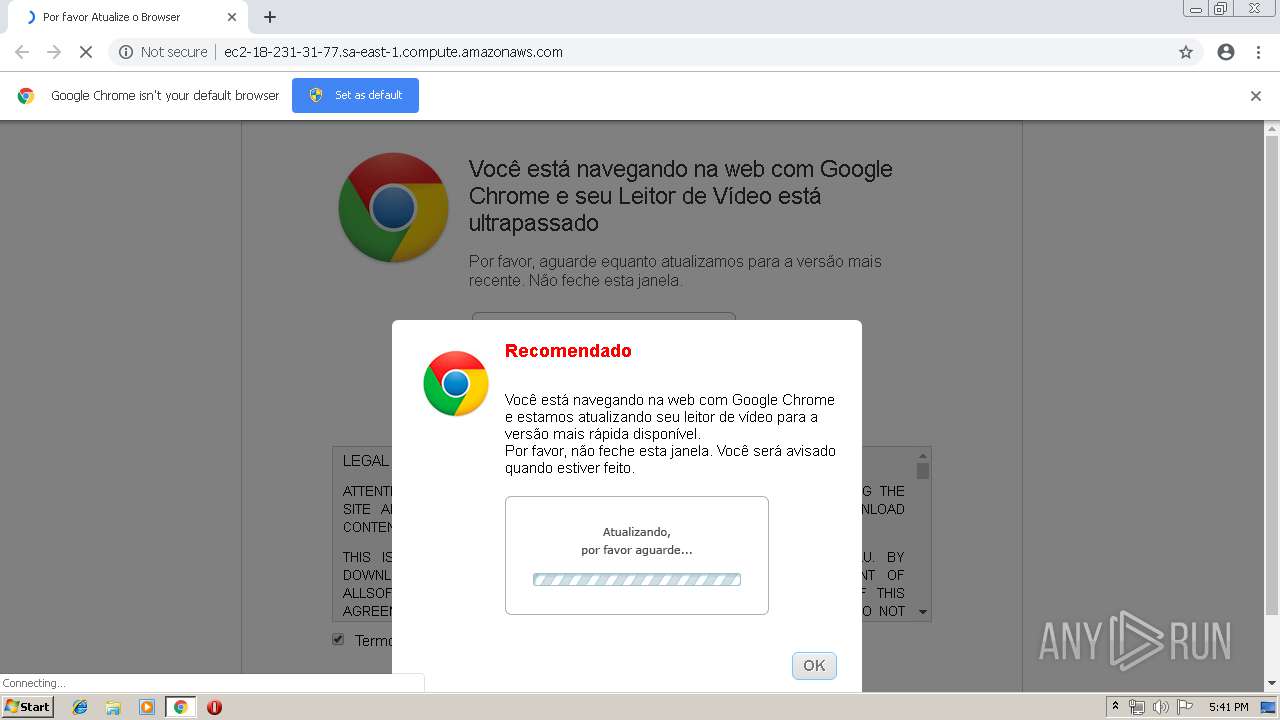
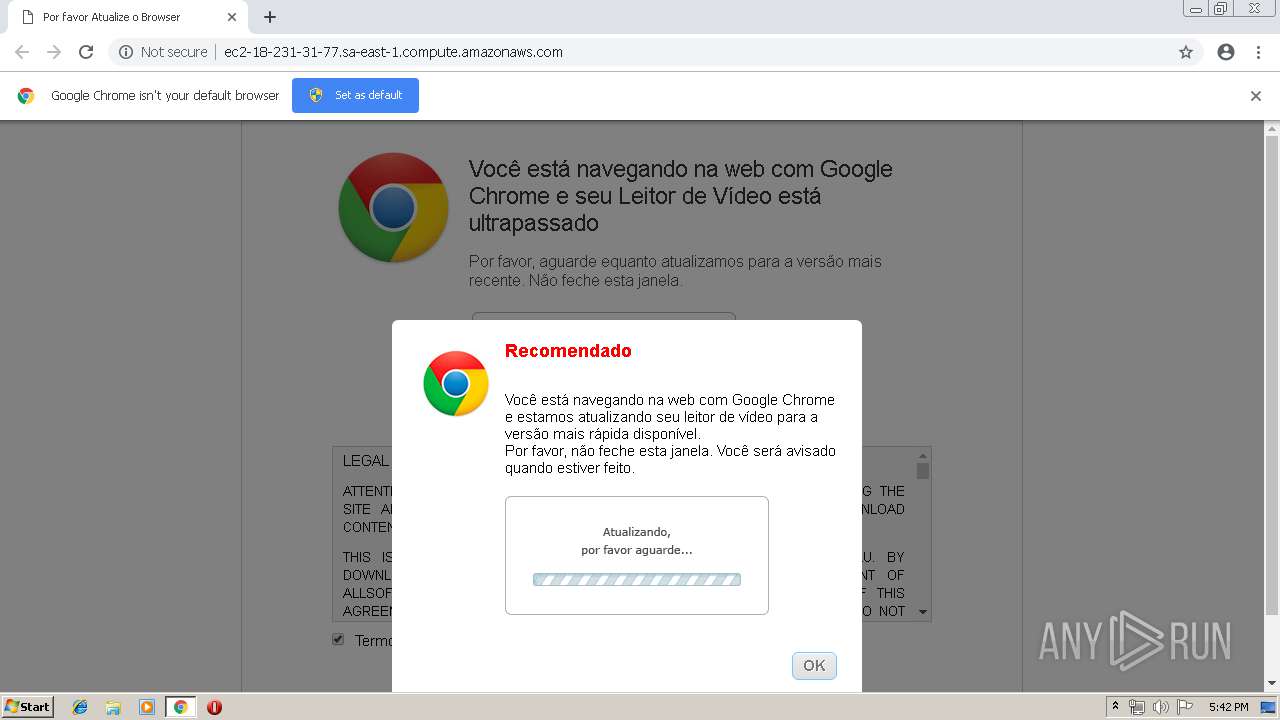
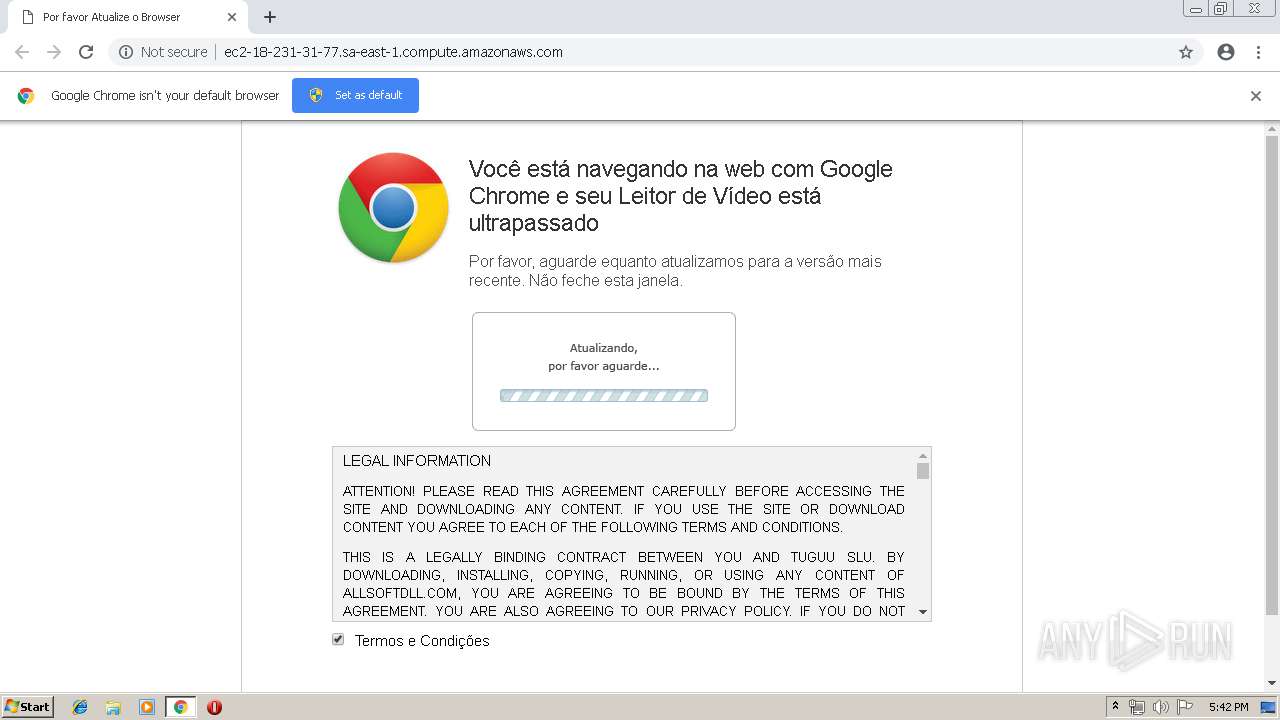
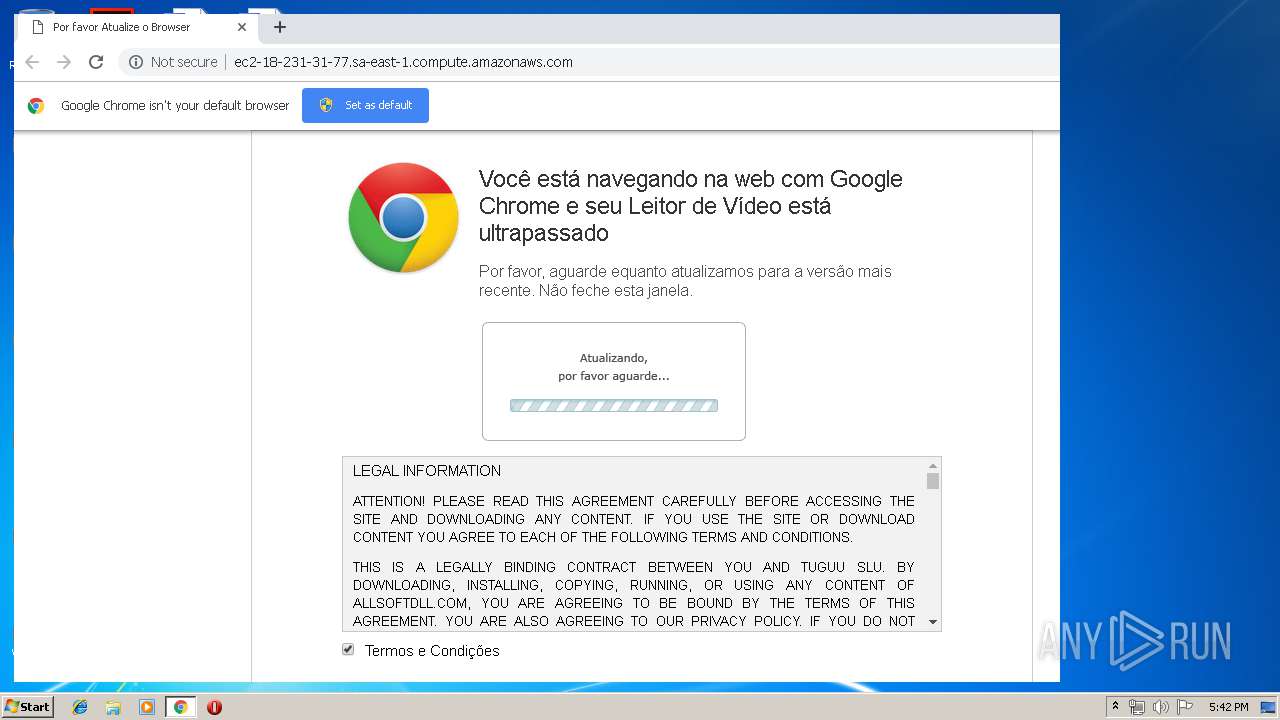
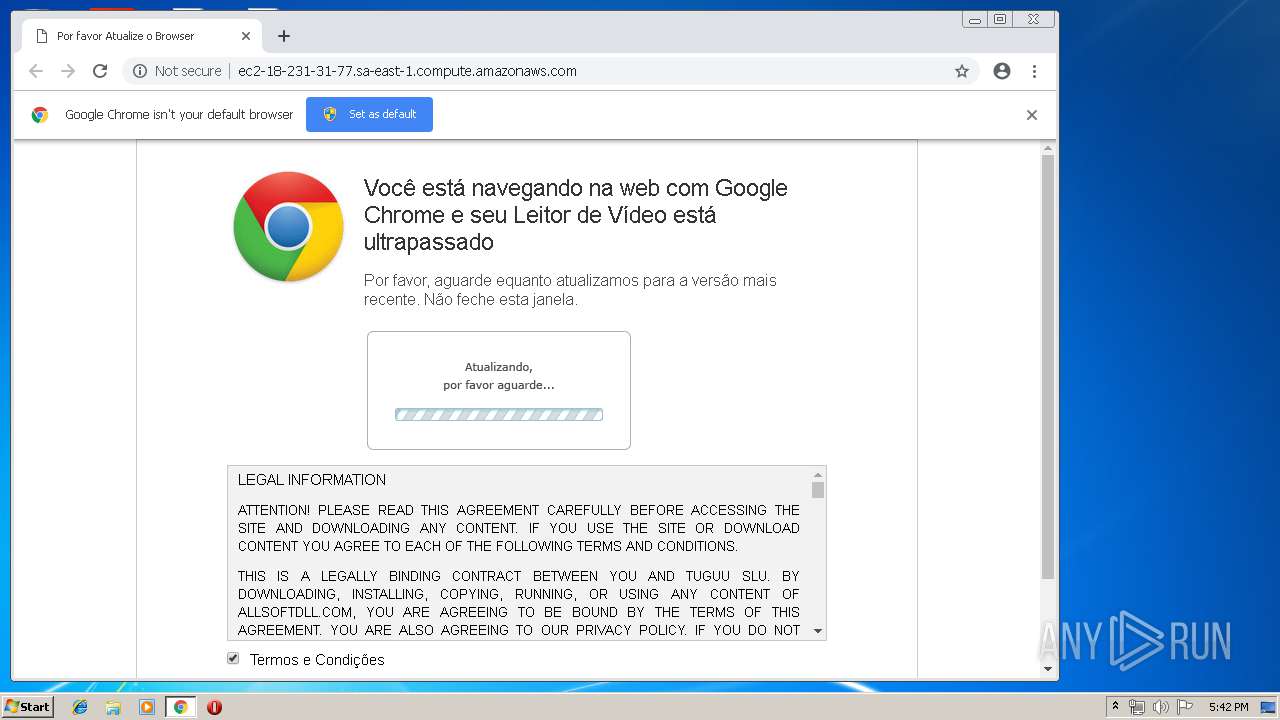
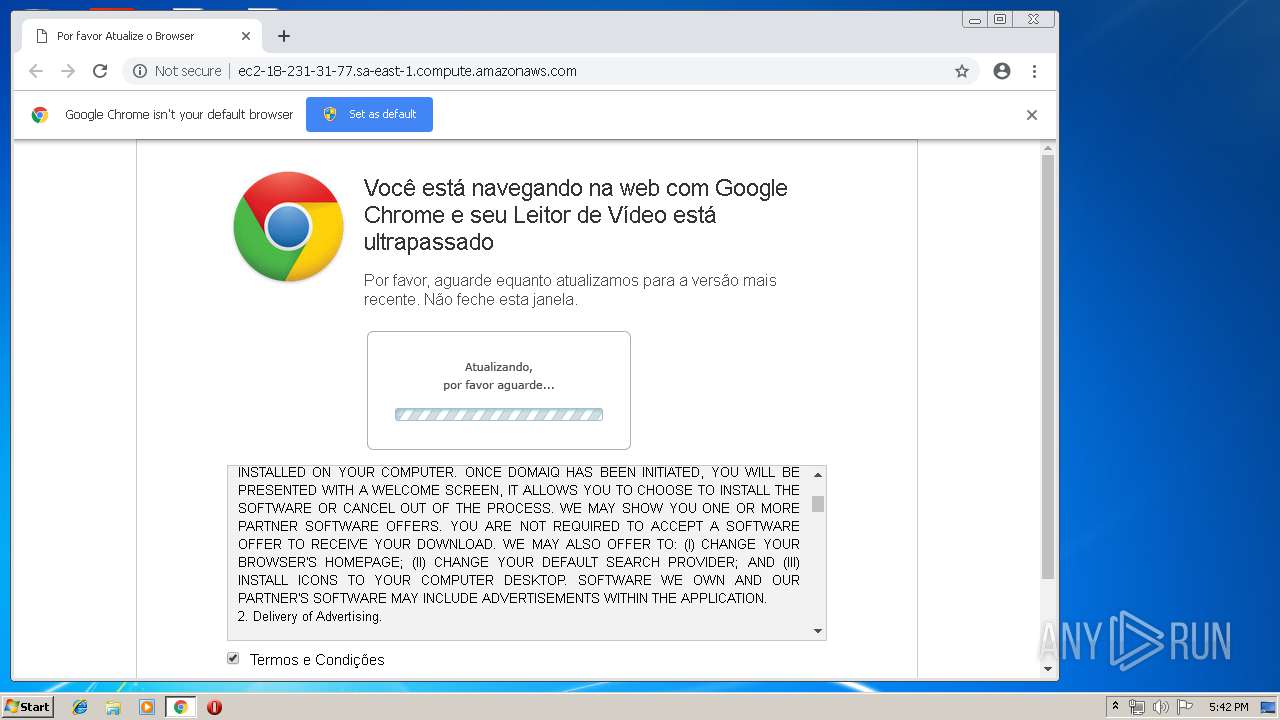
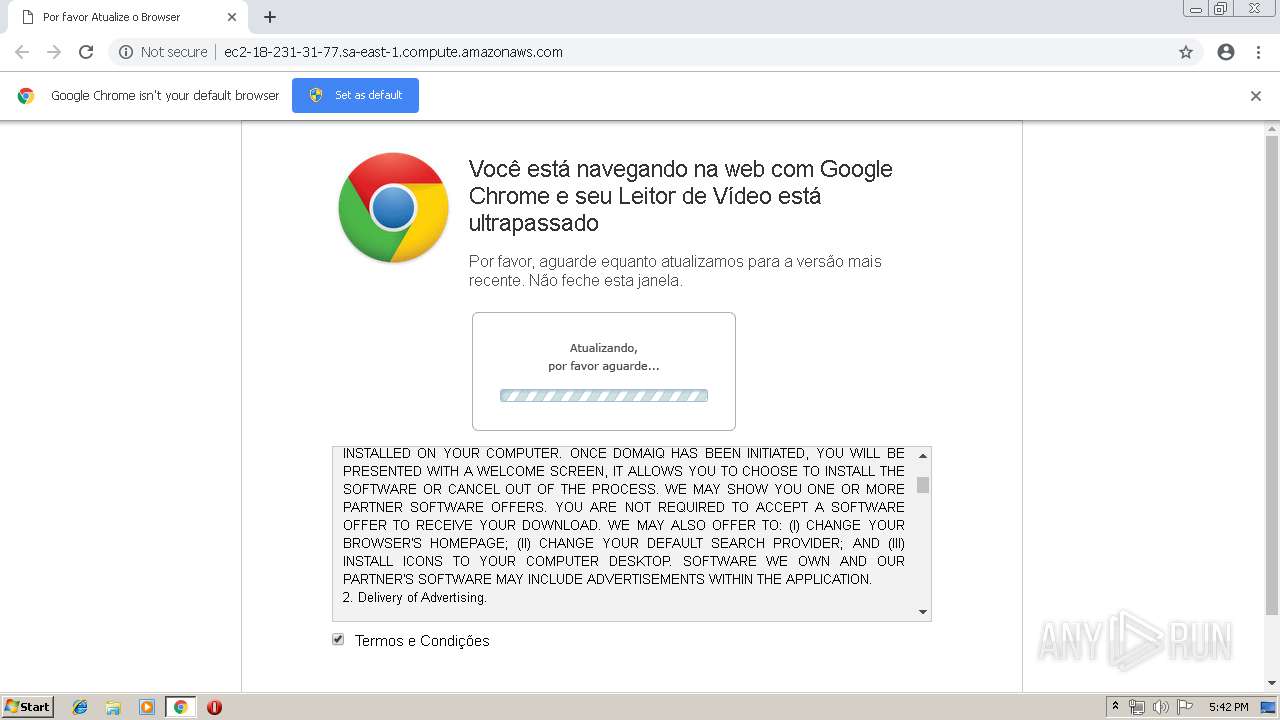
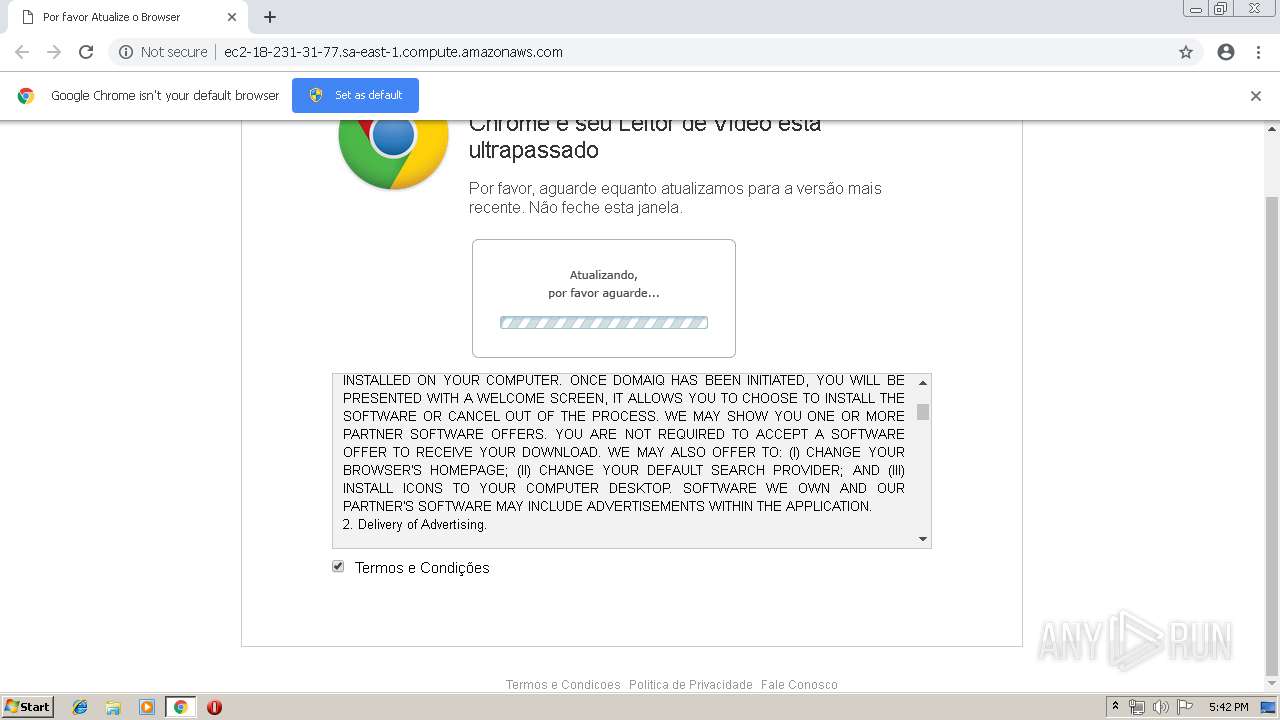
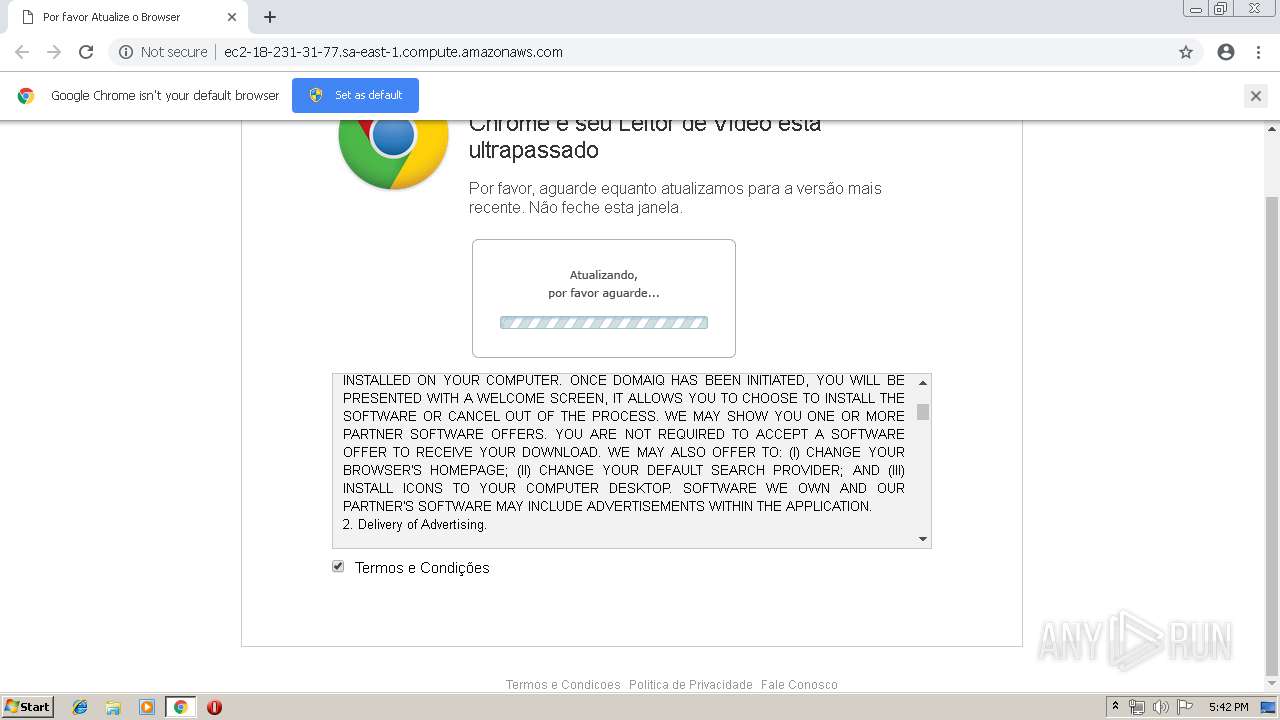
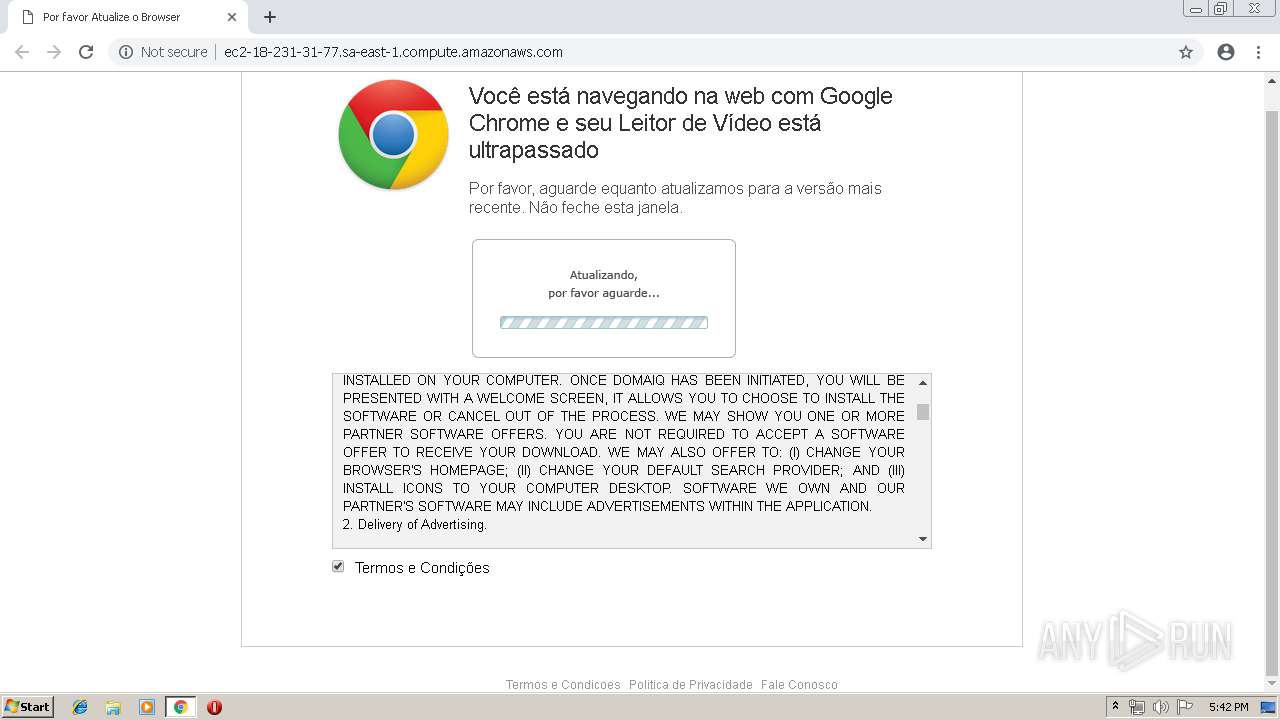
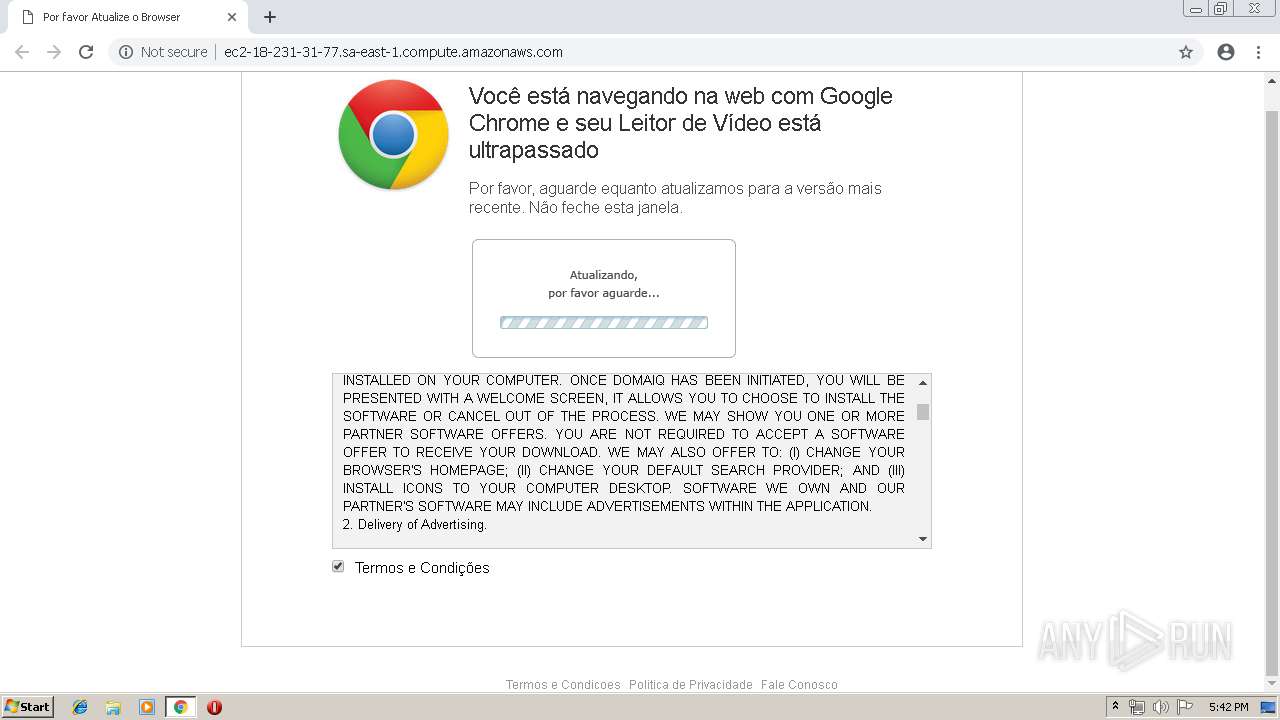
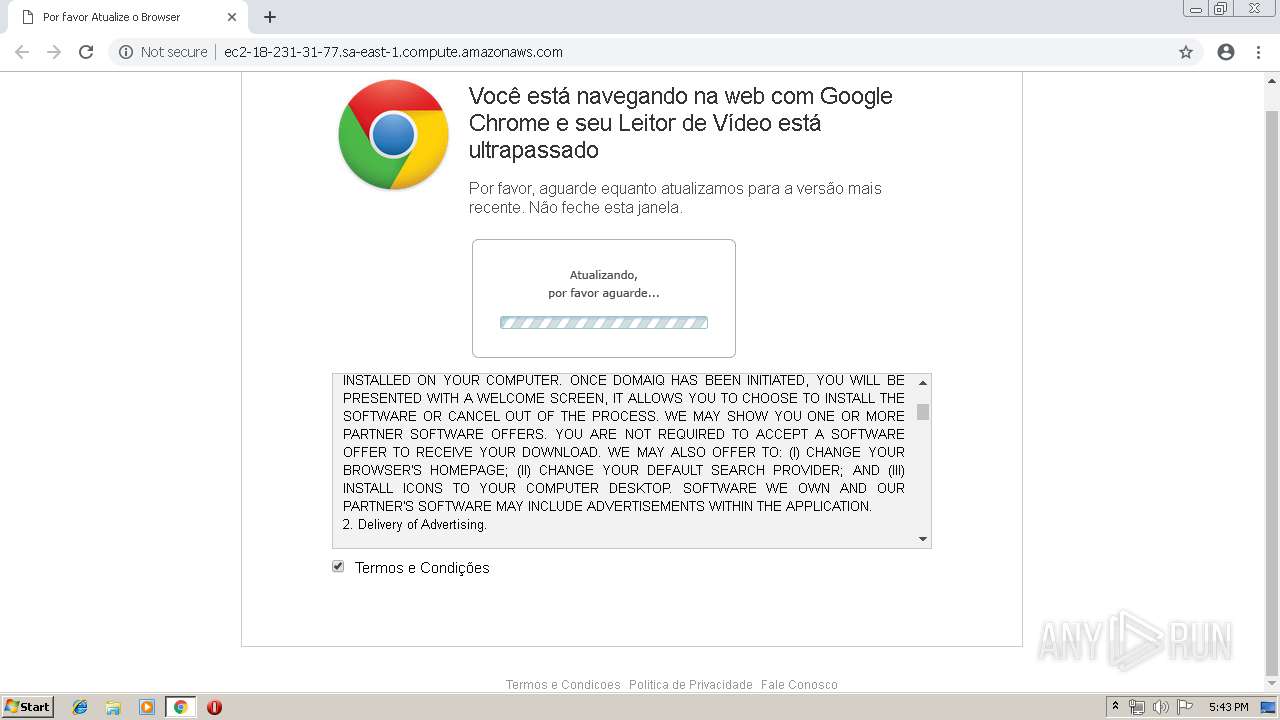
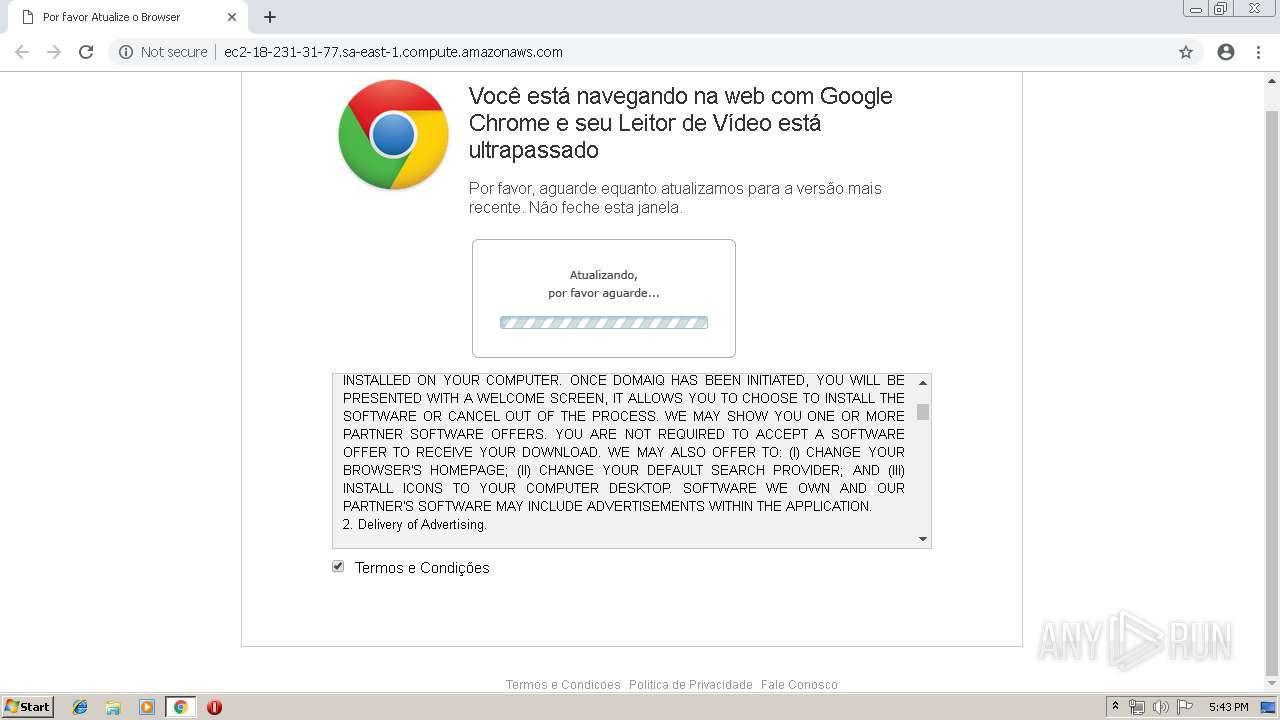
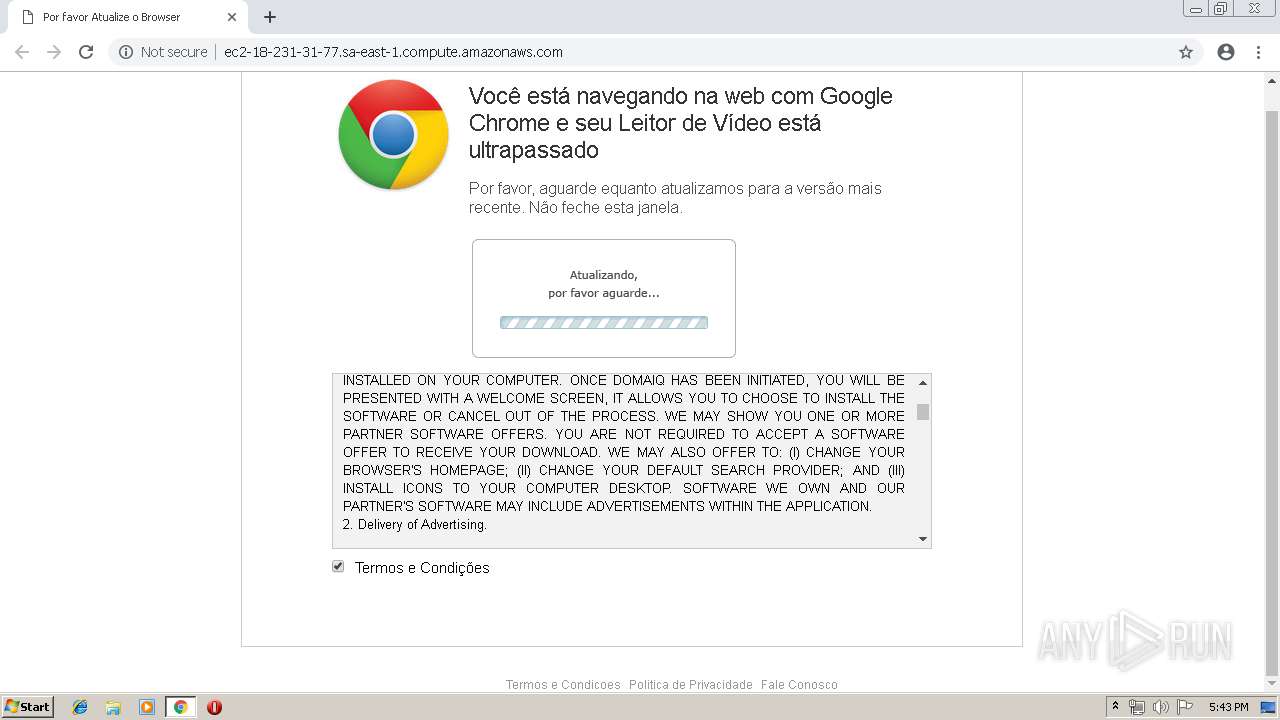
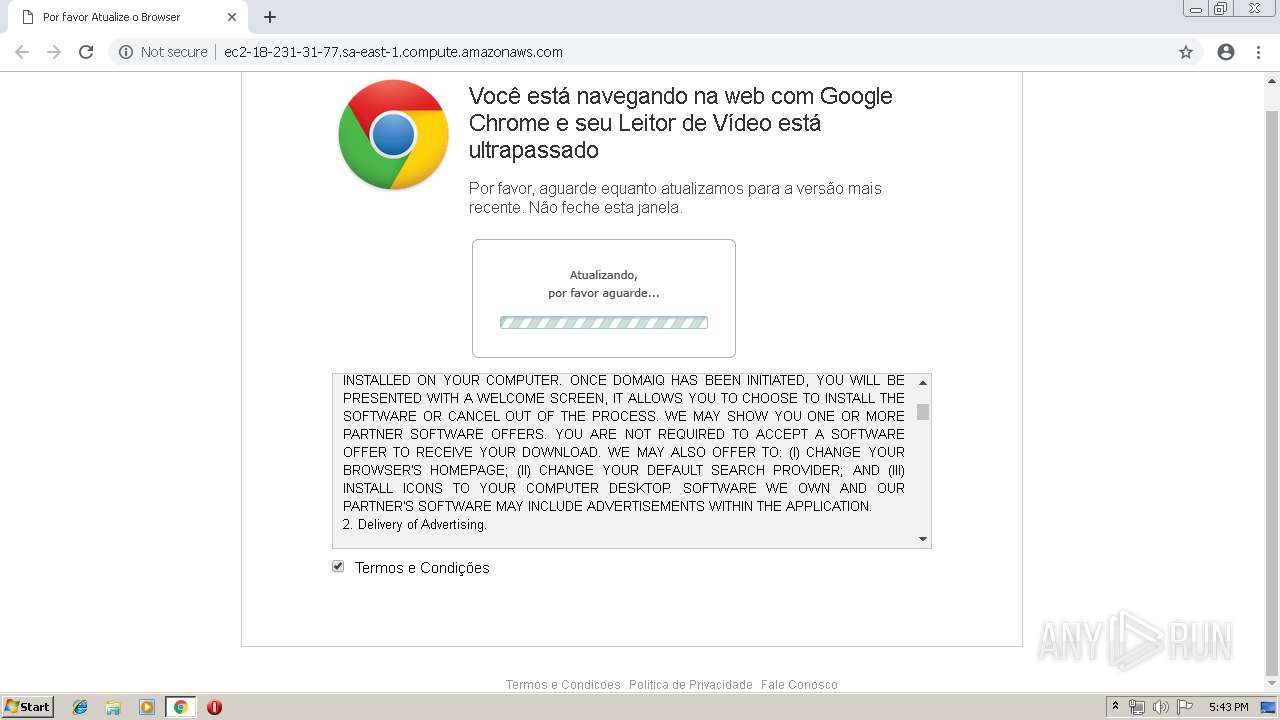
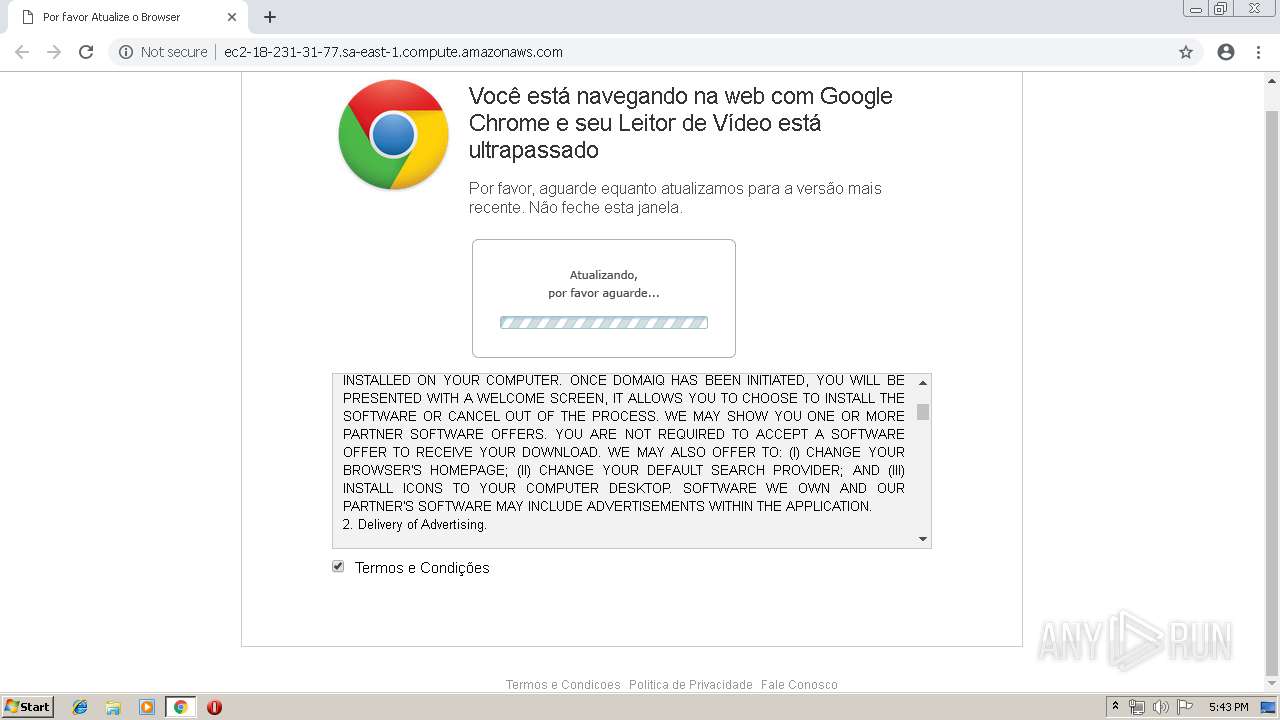
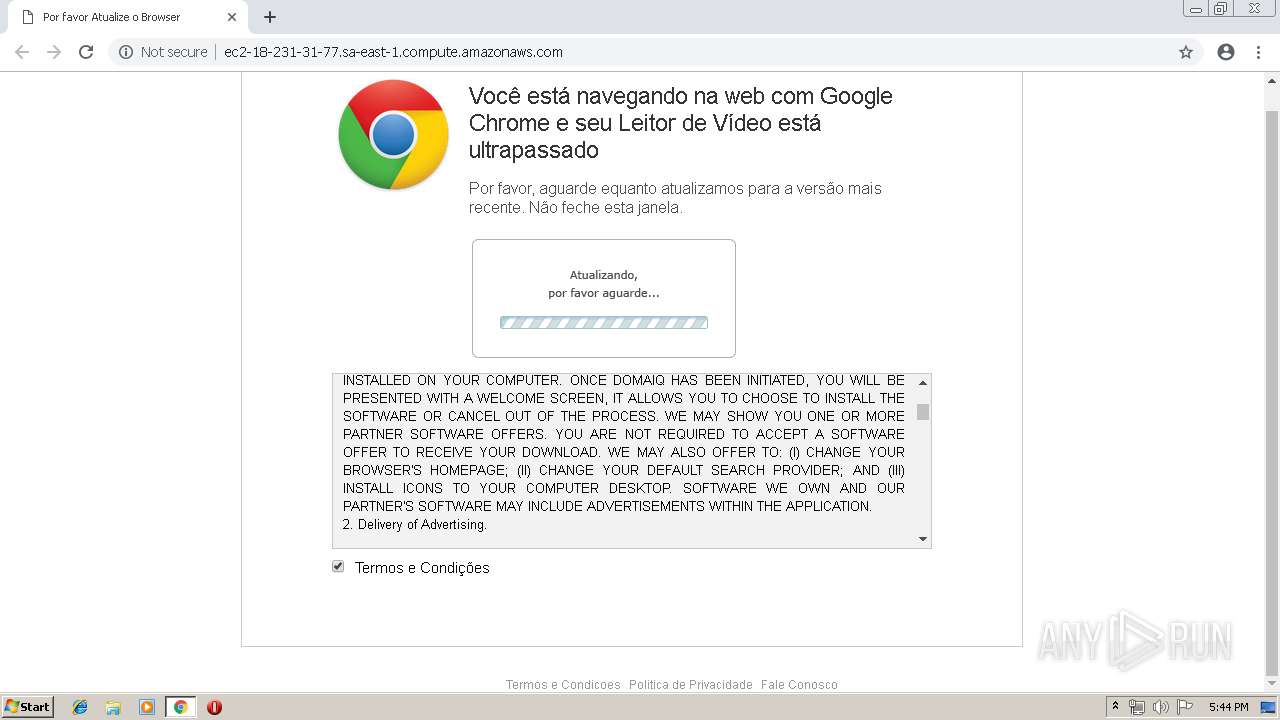
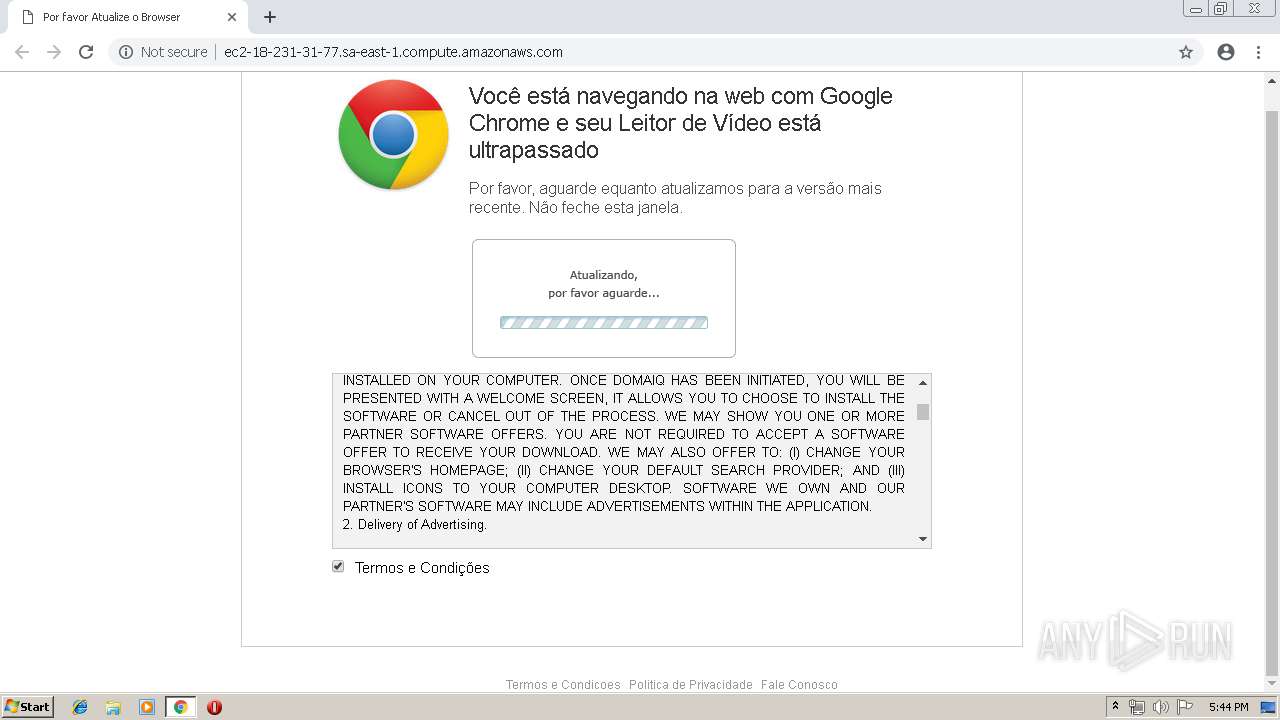
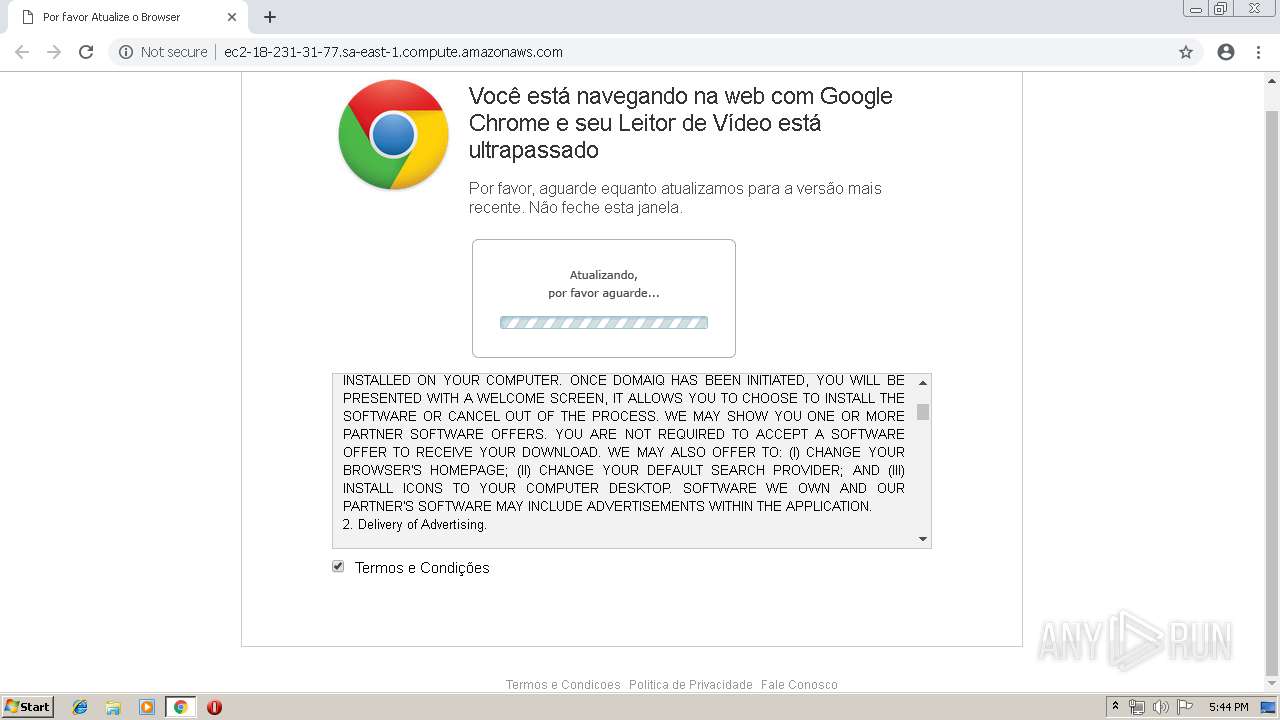
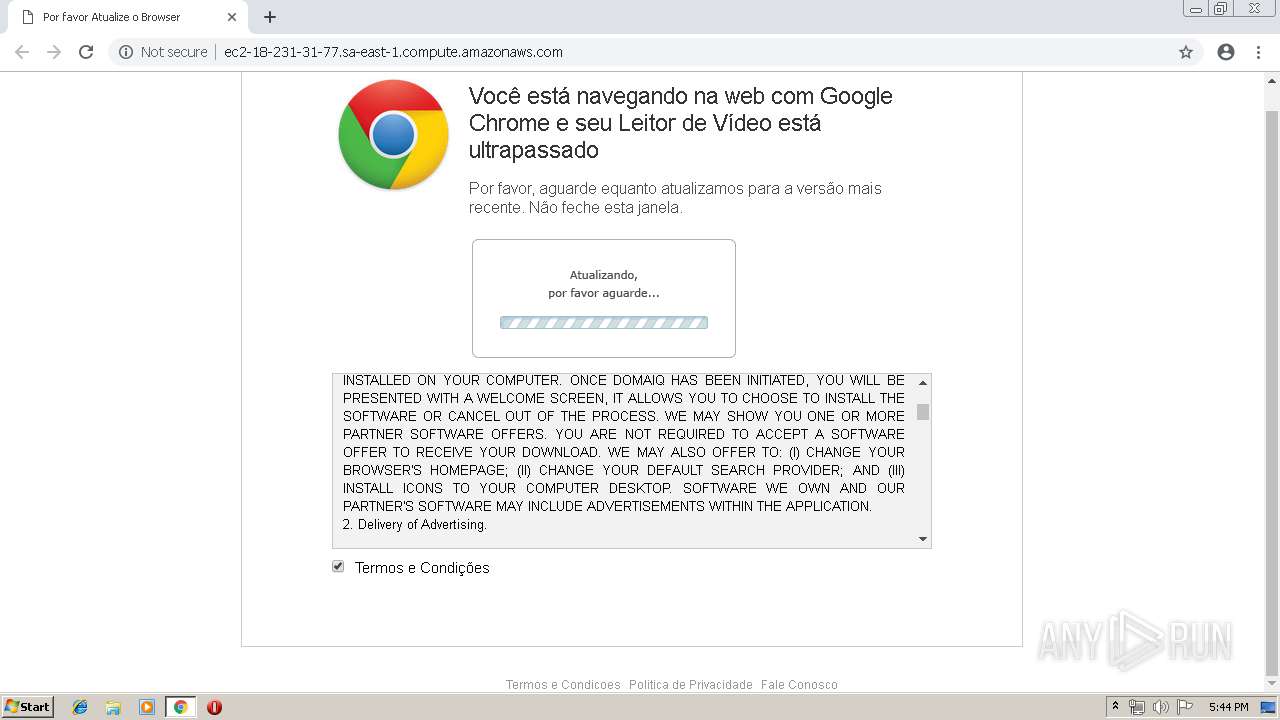
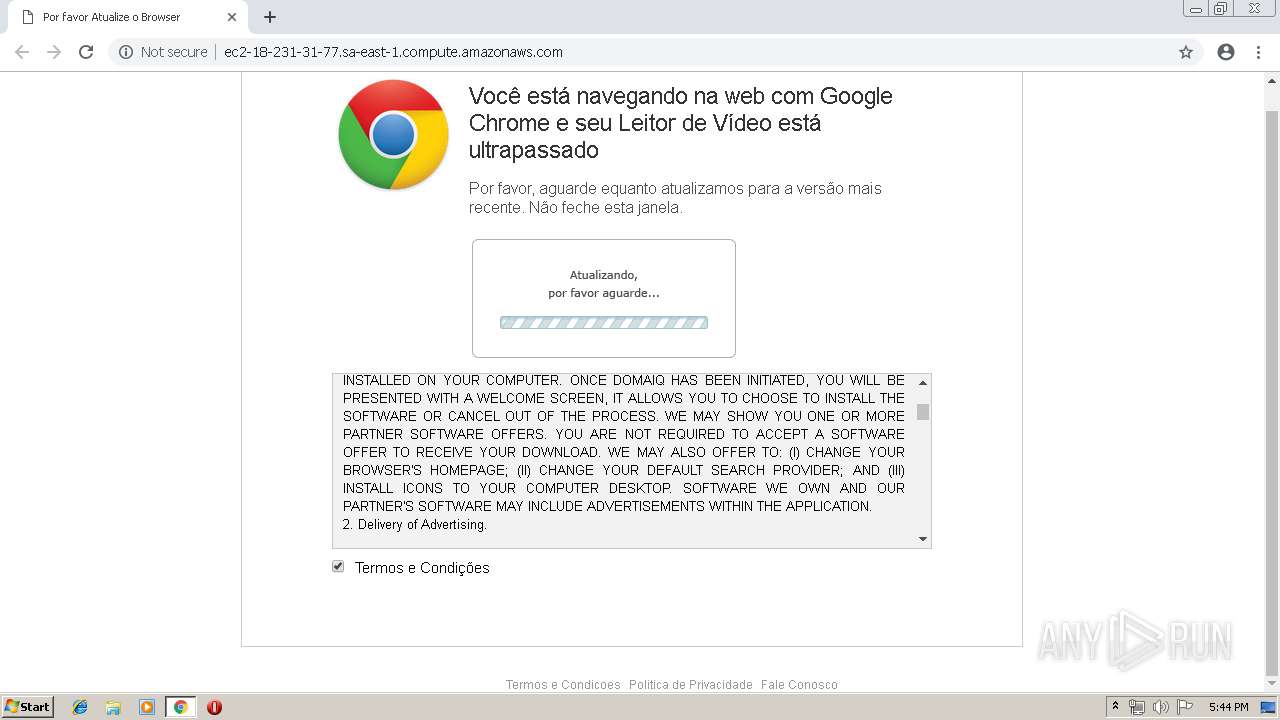
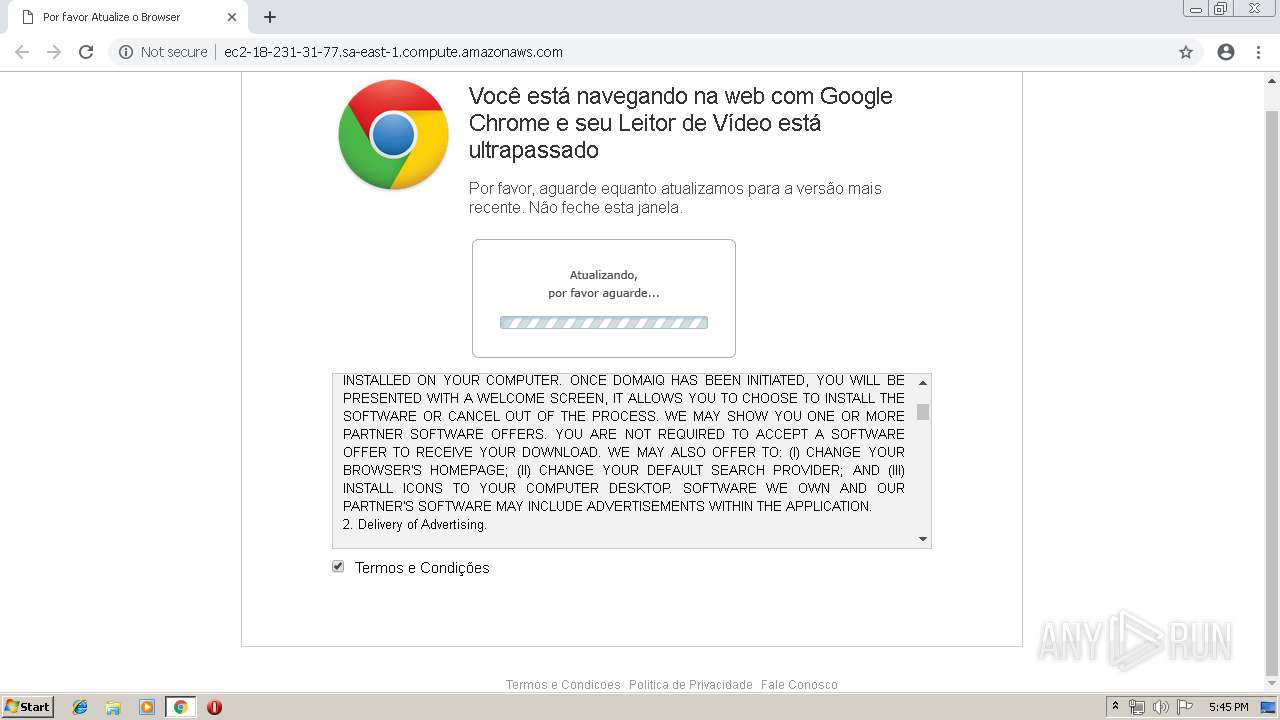
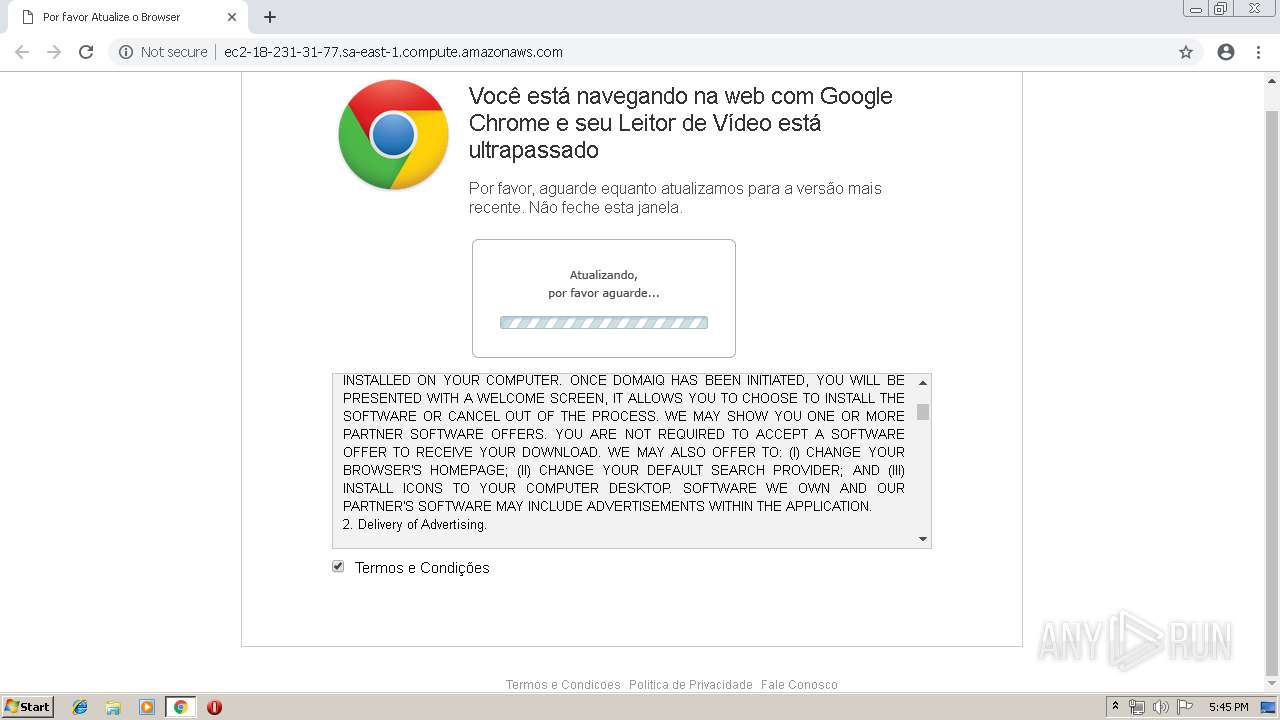
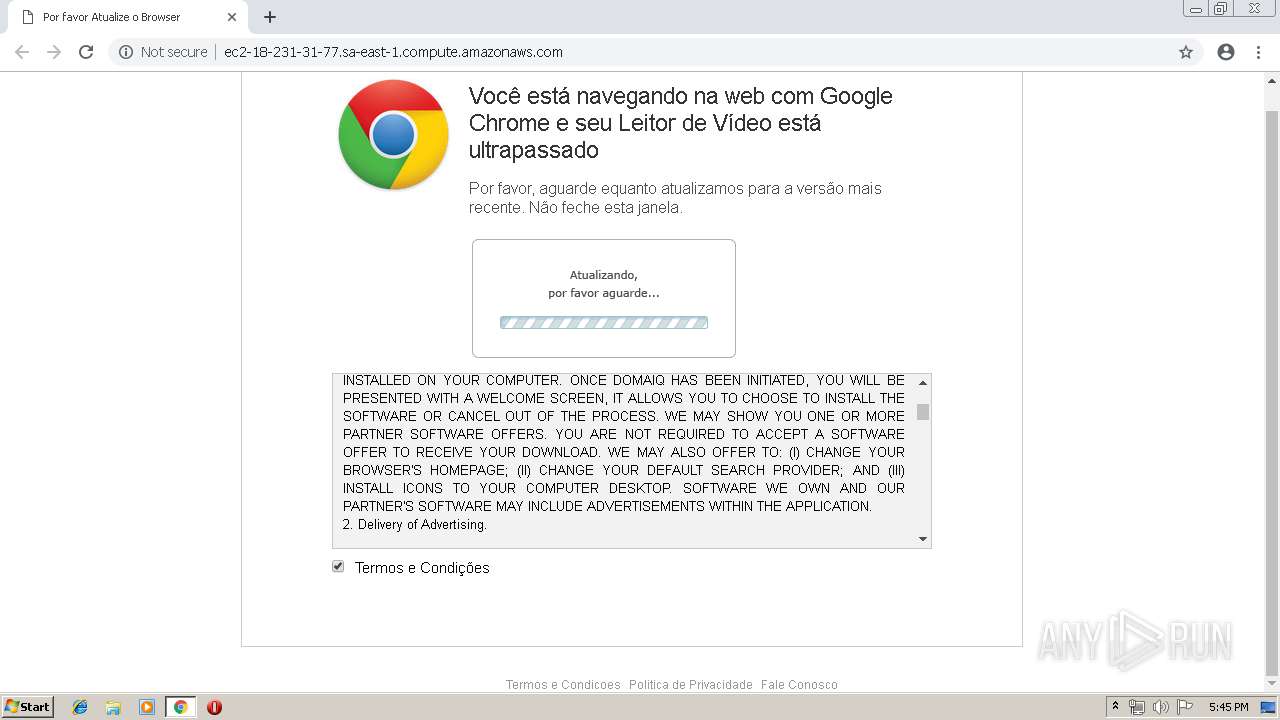
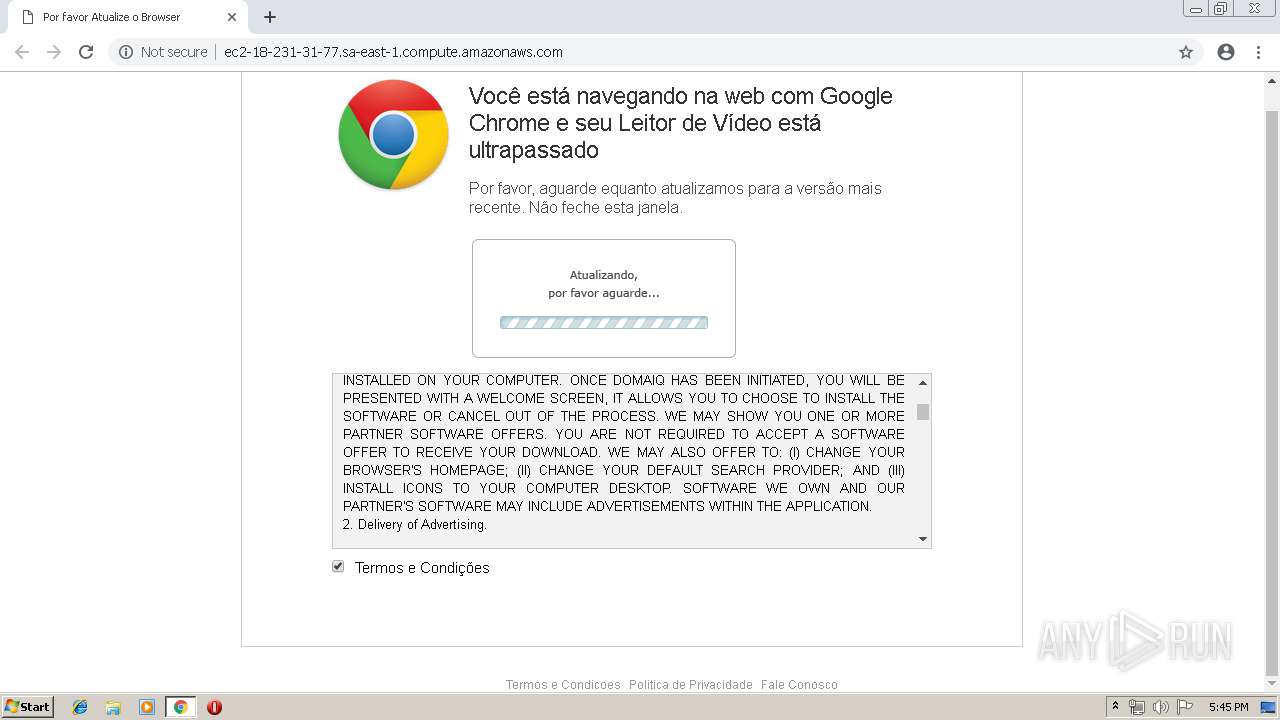
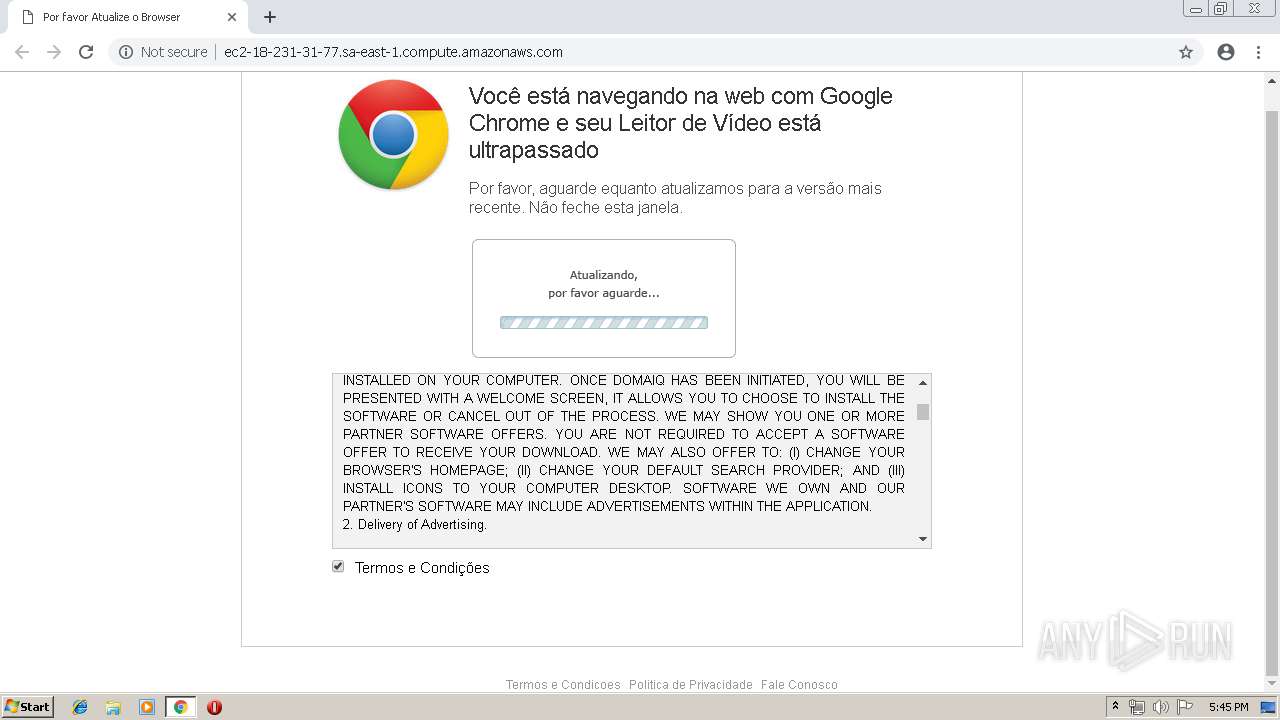
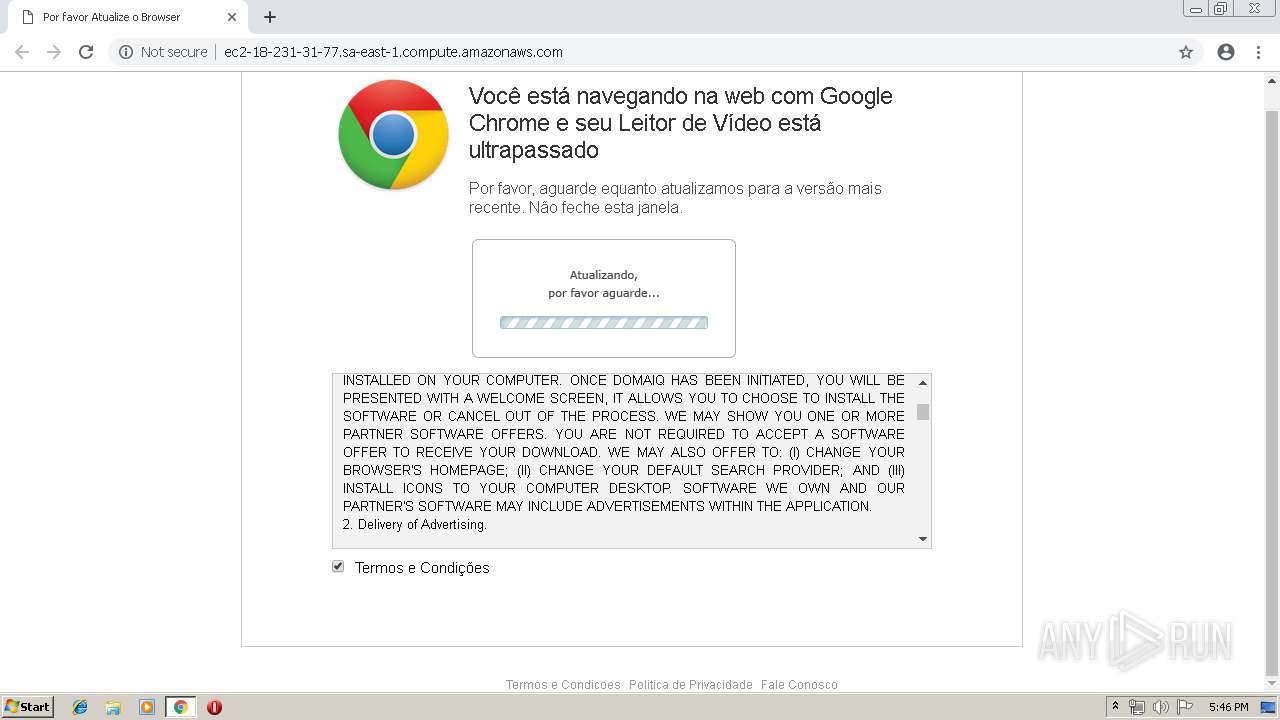
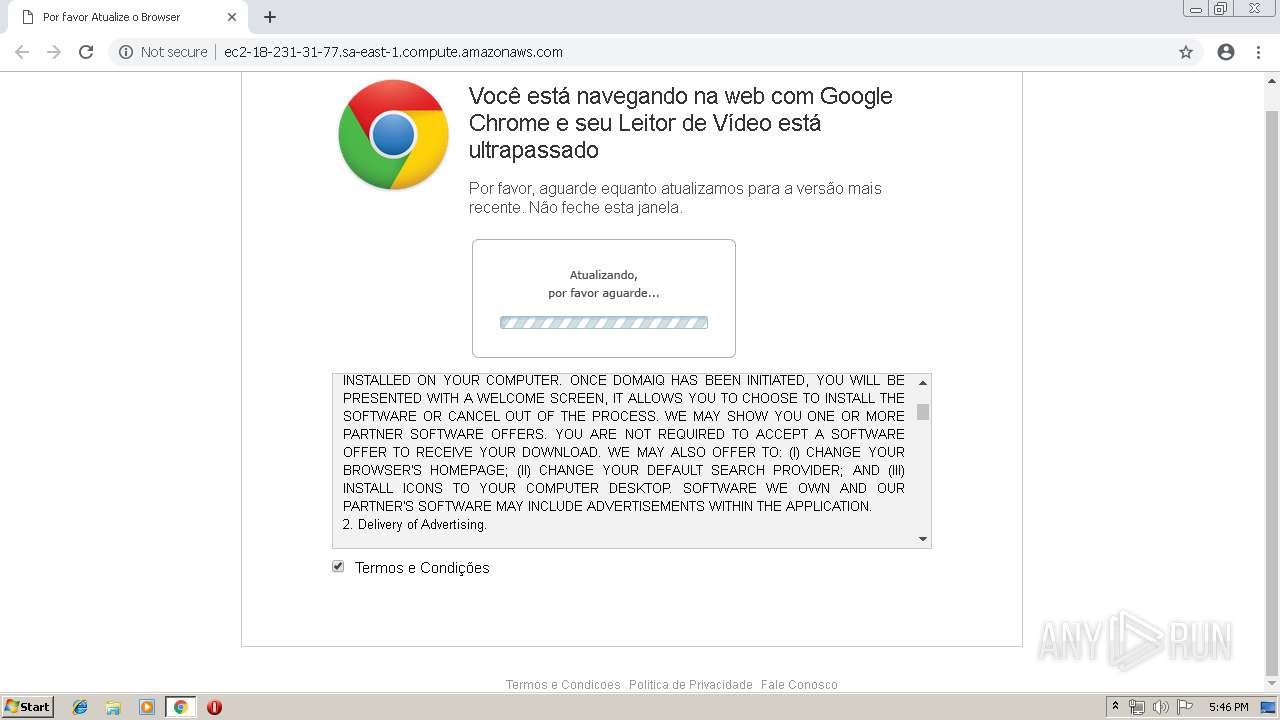
| URL: | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com |
| Full analysis: | https://app.any.run/tasks/3bbdca77-4e81-47d8-b020-aa99e60e3b82 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 16:41:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | ACEDAD998450FF5C965EB8261F50D8CC |
| SHA1: | 2F951EFABC0C3FA77AFDFA3D55683412A8BC9C98 |
| SHA256: | F3C54D655909D108745DEE2E9169BBEF148866C223FC1C55721FF4D7730D32CA |
| SSDEEP: | 3:N1KbmXRRhqKr9Eo7W2:CkhVX3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2568)
INFO
Application launched itself
- chrome.exe (PID: 2568)
Reads settings of System Certificates
- chrome.exe (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4253821814394230140 --mojo-platform-channel-handle=6952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5544295237201077993 --mojo-platform-channel-handle=8108 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=66203899630775436 --mojo-platform-channel-handle=948 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4508334576603921602 --mojo-platform-channel-handle=7036 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=15540309883557182829 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15540309883557182829 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=11241831320230325795 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11241831320230325795 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17683060591771388308 --mojo-platform-channel-handle=3572 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=42457163427674833 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=42457163427674833 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ea50f18,0x6ea50f28,0x6ea50f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
535
Read events
462
Write events
69
Delete events
4
Modification events
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2568-13202844092791375 |
Value: 259 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
338
Text files
186
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\acc19783-d2a2-4a95-a6cf-cd80f801ffa0.tmp | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
109
TCP/UDP connections
29
DNS requests
18
Threats
155
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/atualizavideo_arquivos/msgbox.css | BR | text | 1.45 Kb | shared |
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/ | BR | html | 23.4 Kb | shared |
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/atualizavideo_arquivos/style.css | BR | text | 5.98 Kb | shared |
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/atualizavideo_arquivos/sb.css | BR | text | 6.36 Kb | shared |
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/atualizavideo_arquivos/download.js | BR | text | 1.01 Kb | shared |
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/atualizavideo_arquivos/firefox68.jpg | BR | image | 4.67 Kb | shared |
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/atualizavideo_arquivos/ga.js | BR | text | 39.9 Kb | shared |
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/atualizavideo_arquivos/browserdetector.js | BR | text | 2.68 Kb | shared |
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/atualizavideo_arquivos/msgbox.js | BR | text | 7.22 Kb | shared |
2568 | chrome.exe | GET | 200 | 18.231.31.77:80 | http://ec2-18-231-31-77.sa-east-1.compute.amazonaws.com/atualizavideo_arquivos/ie68.jpg | BR | image | 4.17 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2568 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2568 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2568 | chrome.exe | 18.231.31.77:80 | ec2-18-231-31-77.sa-east-1.compute.amazonaws.com | Amazon.com, Inc. | BR | shared |
2568 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
2568 | chrome.exe | 172.217.22.110:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2568 | chrome.exe | 10.0.0.138:80 | — | — | — | unknown |
2568 | chrome.exe | 10.0.0.1:80 | — | — | — | unknown |
2568 | chrome.exe | 10.0.0.3:80 | — | — | — | unknown |
2568 | chrome.exe | 10.0.0.2:80 | — | — | — | unknown |
2568 | chrome.exe | 10.1.1.1:80 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ec2-18-231-31-77.sa-east-1.compute.amazonaws.com |
| shared |
accounts.google.com |
| shared |
www.google.com |
| malicious |
www.google-analytics.com |
| whitelisted |
code.jquery.com |
| whitelisted |
ddnsmngr.cmd |
| unknown |
prim.htm |
| unknown |
dnscfg.cgi |
| unknown |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2568 | chrome.exe | A Network Trojan was detected | ET INFO Possible Phish - Mirrored Website Comment Observed |
2568 | chrome.exe | Attempted Administrator Privilege Gain | ET EXPLOIT TP-LINK TL-WR340G Router DNS Change GET Request |
2568 | chrome.exe | Attempted Administrator Privilege Gain | ET EXPLOIT TP-LINK TL-WR340G Router DNS Change GET Request |
2568 | chrome.exe | Attempted Administrator Privilege Gain | ET EXPLOIT TP-LINK TL-WR340G Router DNS Change GET Request |
2568 | chrome.exe | Attempted Administrator Privilege Gain | ET EXPLOIT TP-LINK DNS Change GET Request (DNSChanger EK) |
2568 | chrome.exe | Attempted Administrator Privilege Gain | ET EXPLOIT TP-LINK TL-WR340G Router DNS Change GET Request |
2568 | chrome.exe | Attempted Administrator Privilege Gain | ET EXPLOIT TP-LINK TL-WR340G Router DNS Change GET Request |
2568 | chrome.exe | Attempted Administrator Privilege Gain | ET EXPLOIT TP-LINK TL-WR340G Router DNS Change GET Request |
2568 | chrome.exe | Attempted Administrator Privilege Gain | ET EXPLOIT COMTREND ADSL Router CT-5367 Remote DNS Change Attempt |
2568 | chrome.exe | Attempted Administrator Privilege Gain | ET EXPLOIT TP-LINK Known Malicious Router DNS Change GET Request |
3 ETPRO signatures available at the full report