| File name: | Desktop.rar |
| Full analysis: | https://app.any.run/tasks/e6dc0527-0728-48d9-a2e2-55201bd9addc |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2019, 13:16:20 |
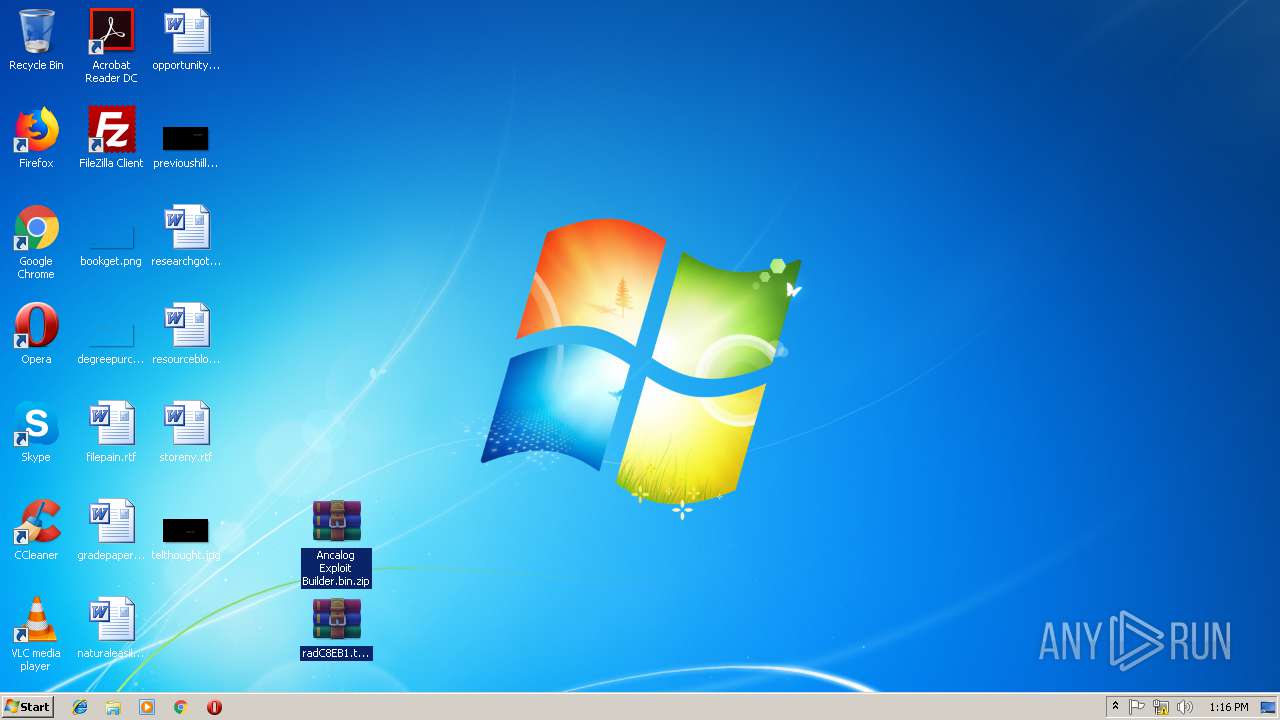
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
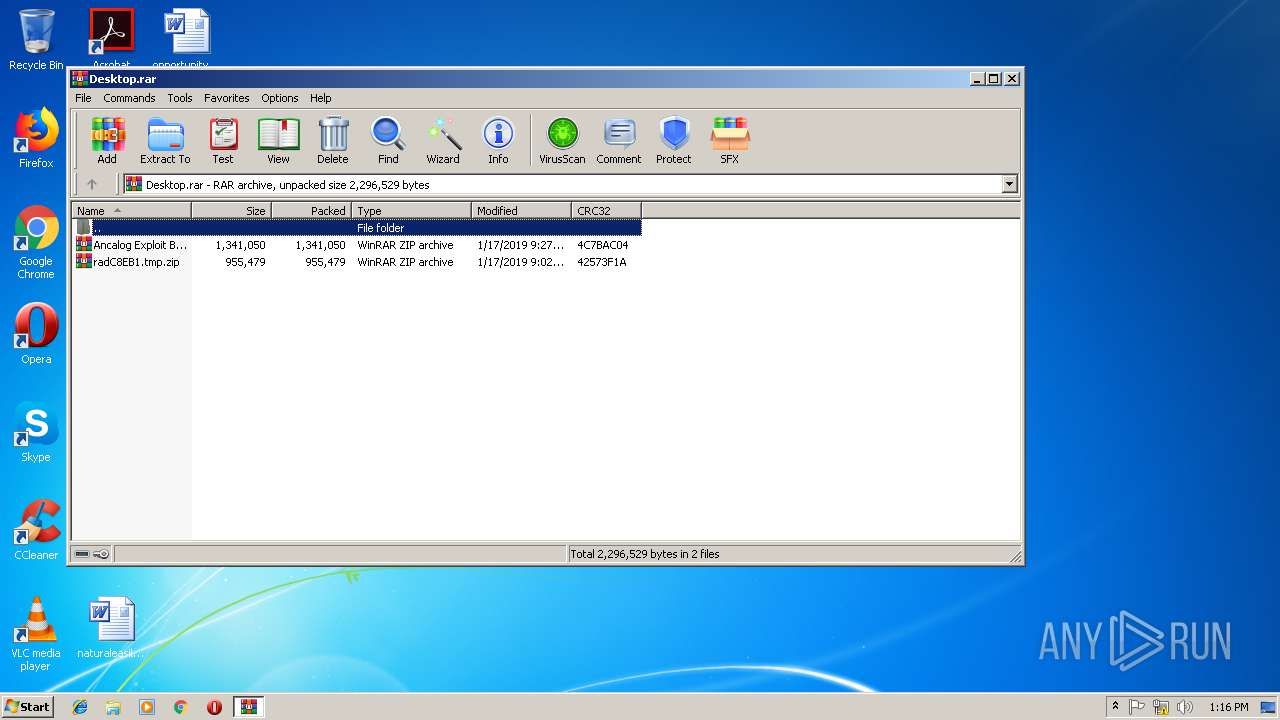
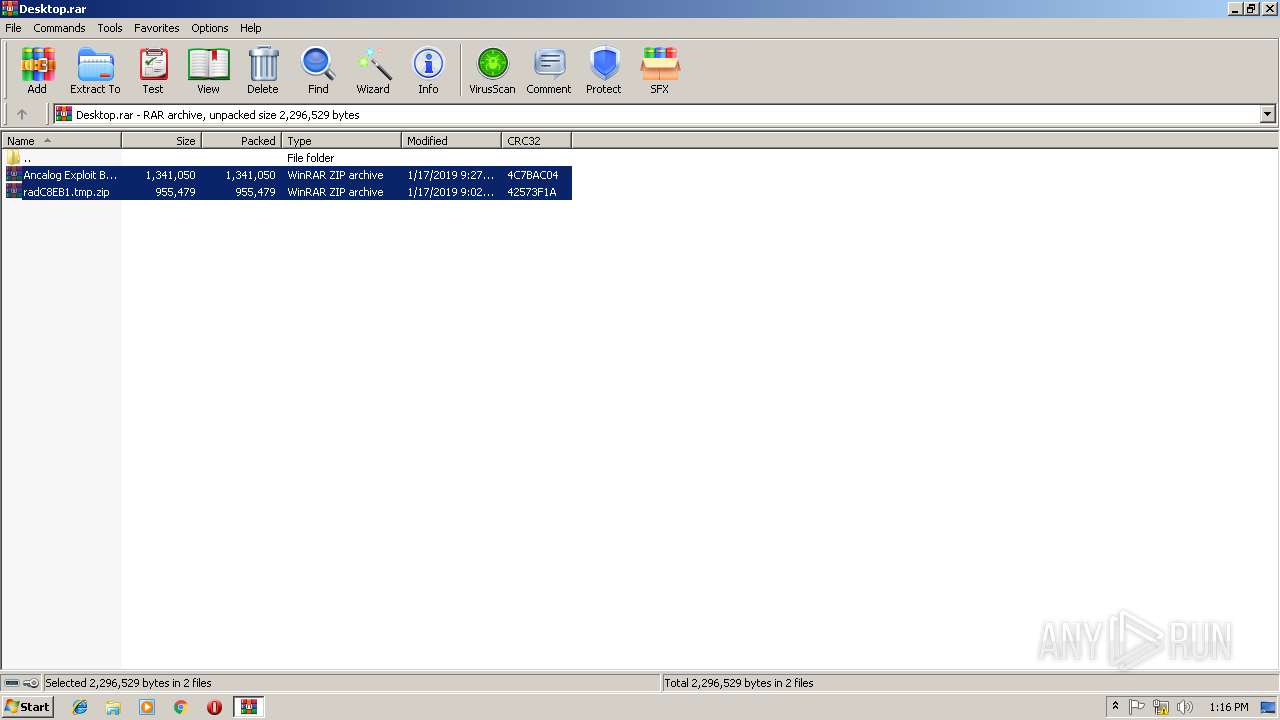
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | B343E43EDCCCDF468881138D6B3E25A4 |
| SHA1: | 87B19A345B854B7EFB8541594DC6D6840480F32F |
| SHA256: | F39DF8C28319F8531BAE1DB7DC4BEA6A0A78B0BD012B1756AAB08AC57C172C13 |
| SSDEEP: | 49152:bMNAMjZ2ZUXsx01fNkQrfeu0em7nhHVW0/opL:boAMMZbxsfNle0mrh1w |
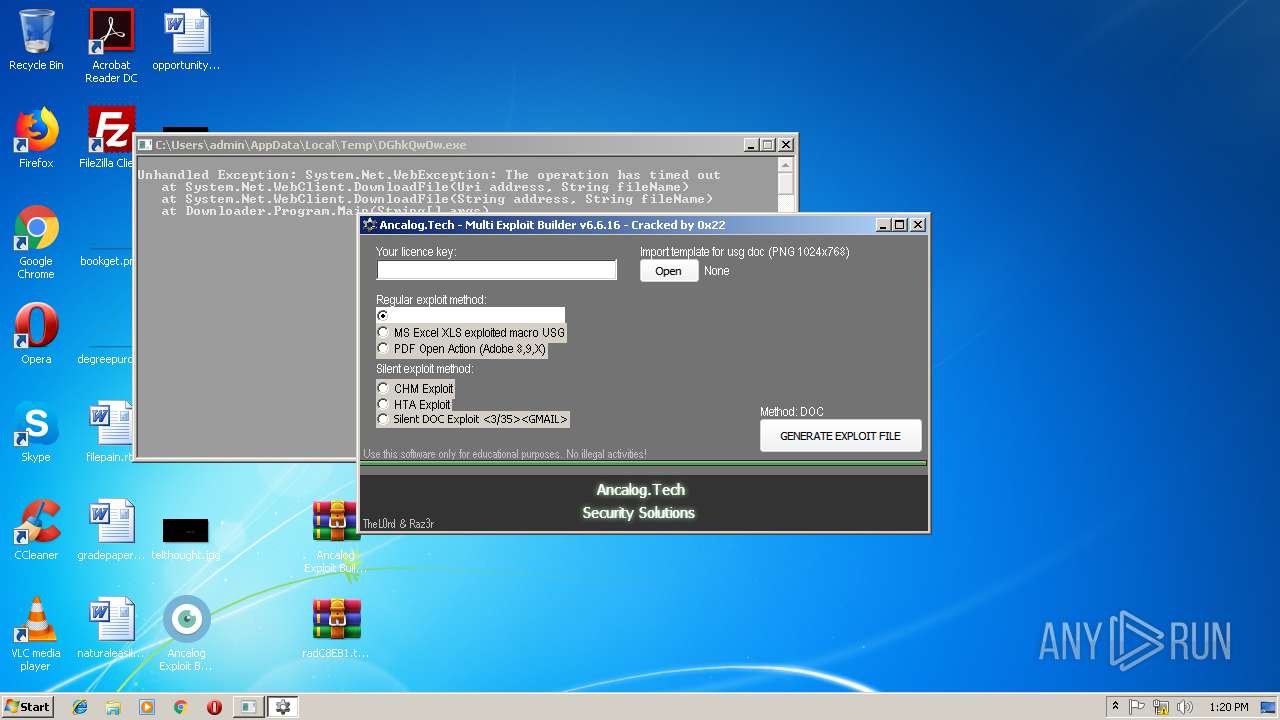
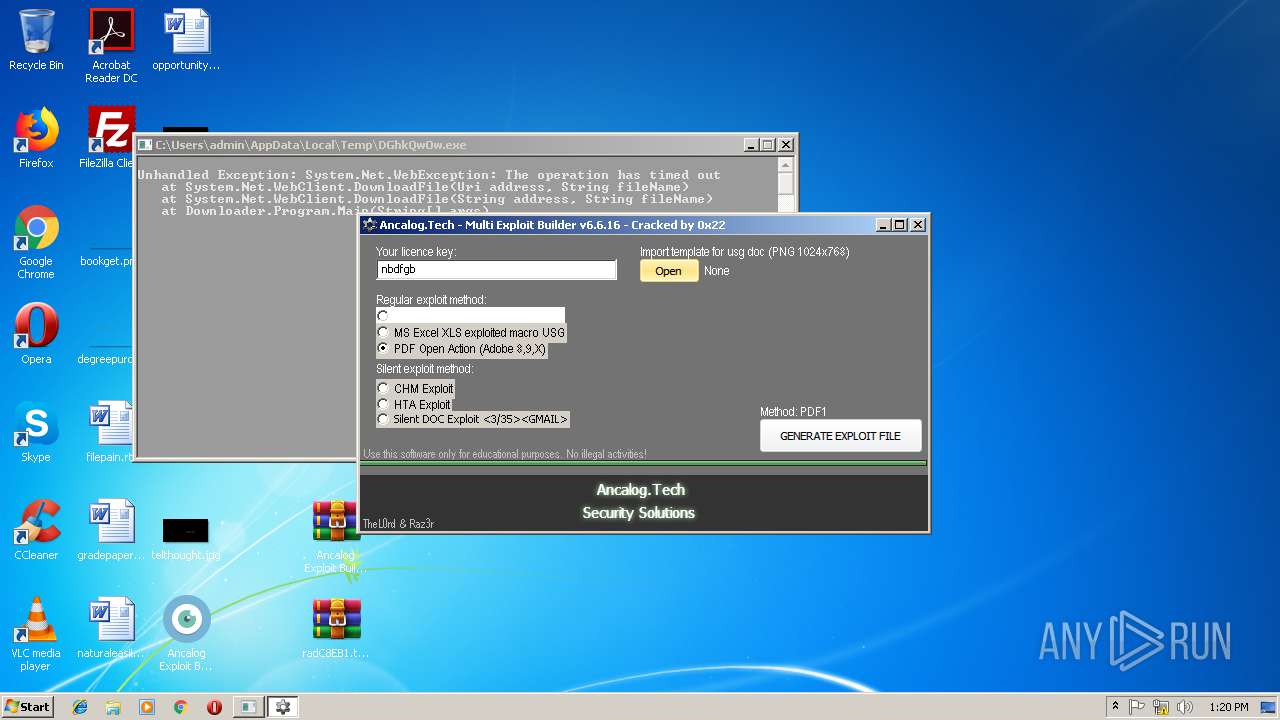
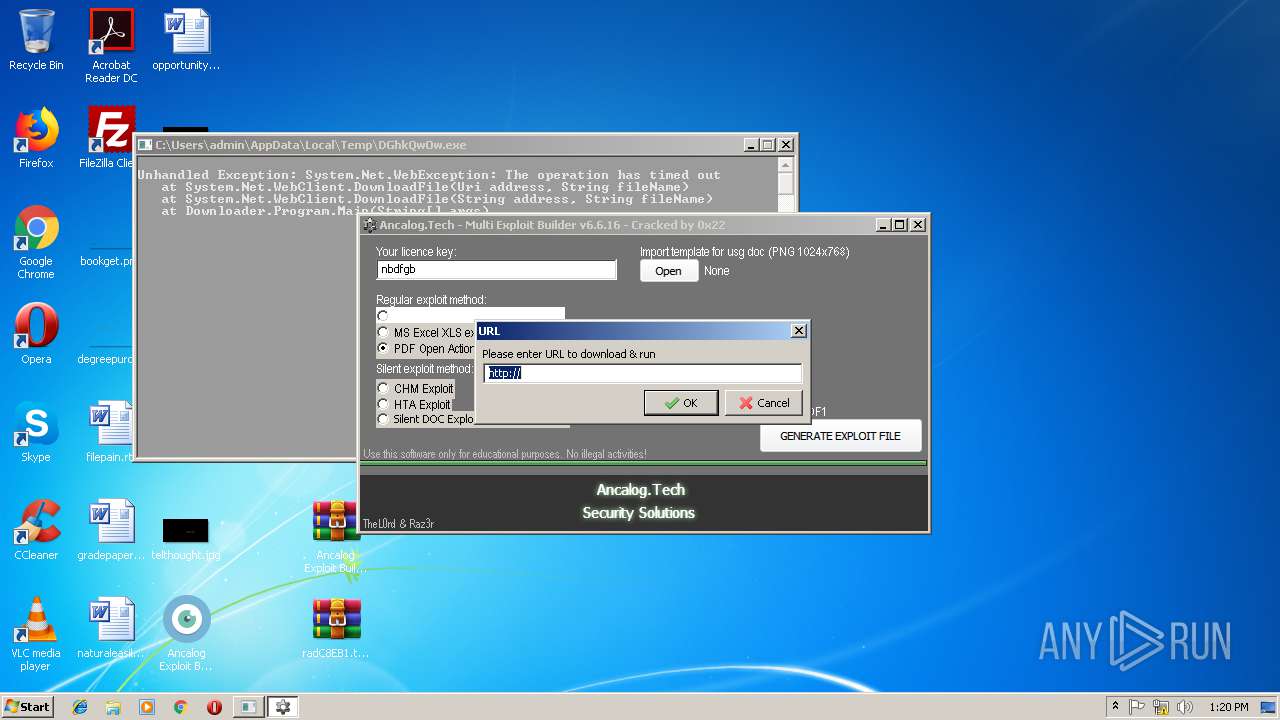
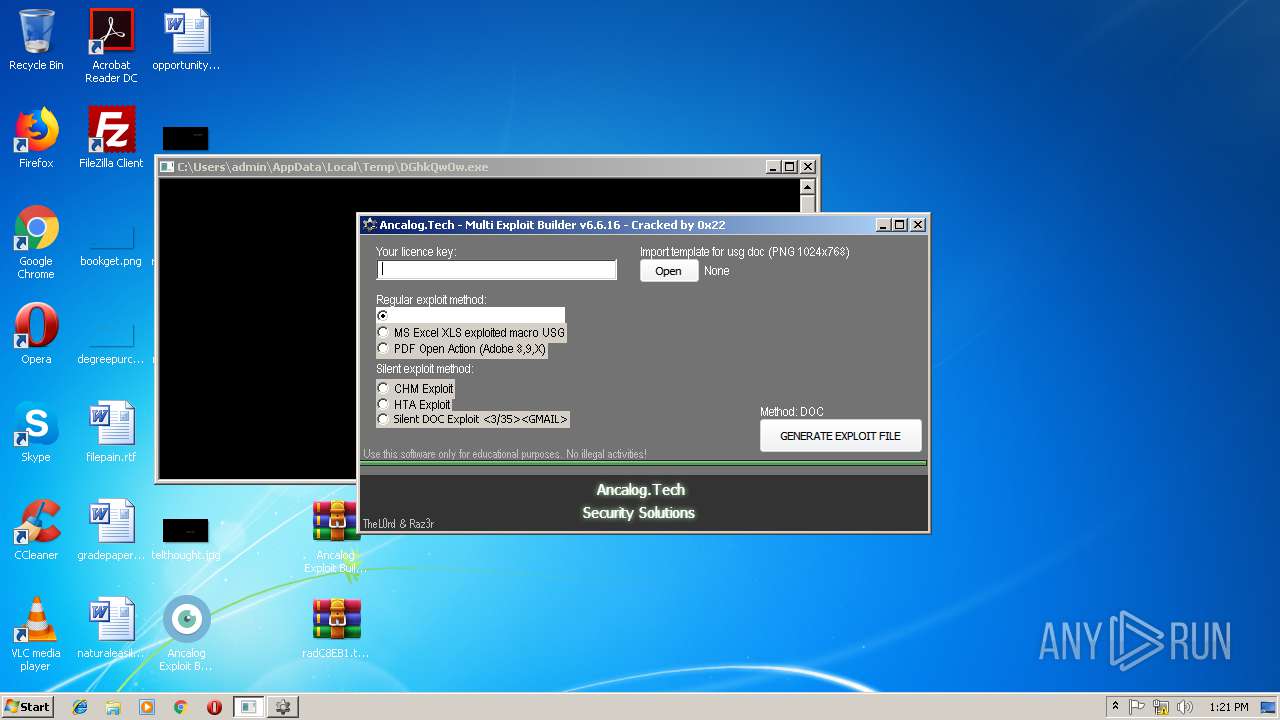
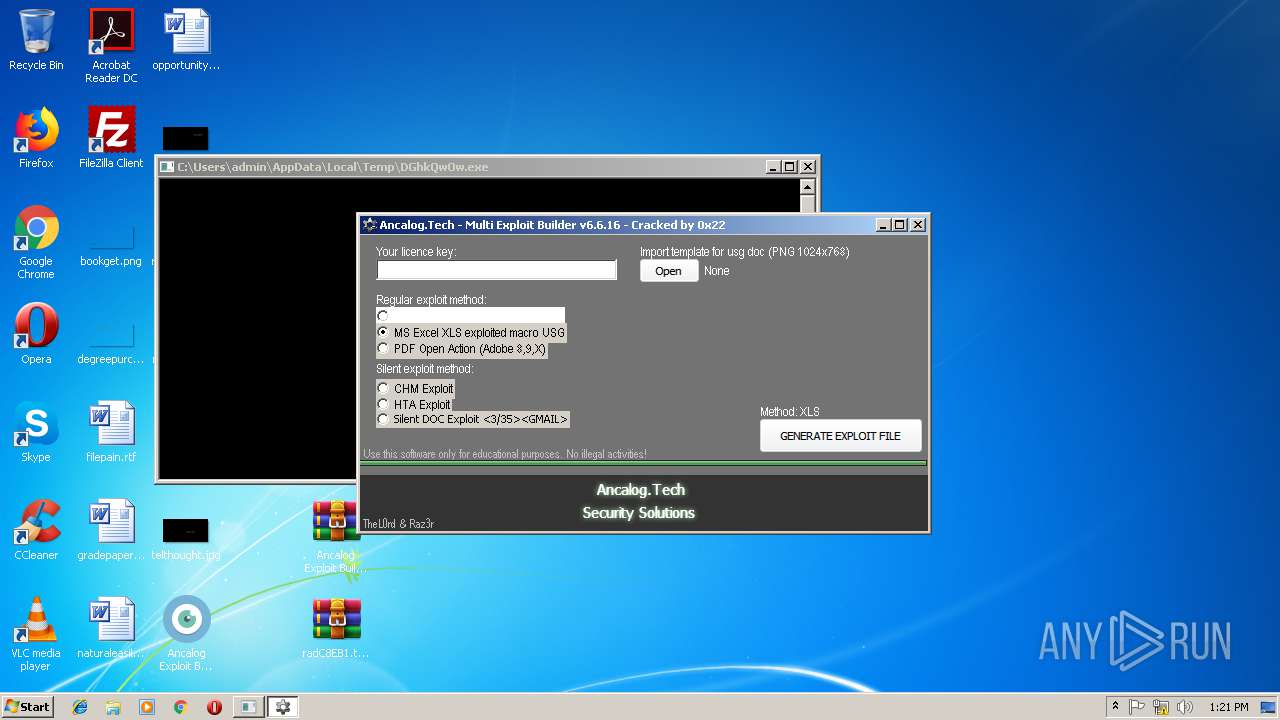
MALICIOUS
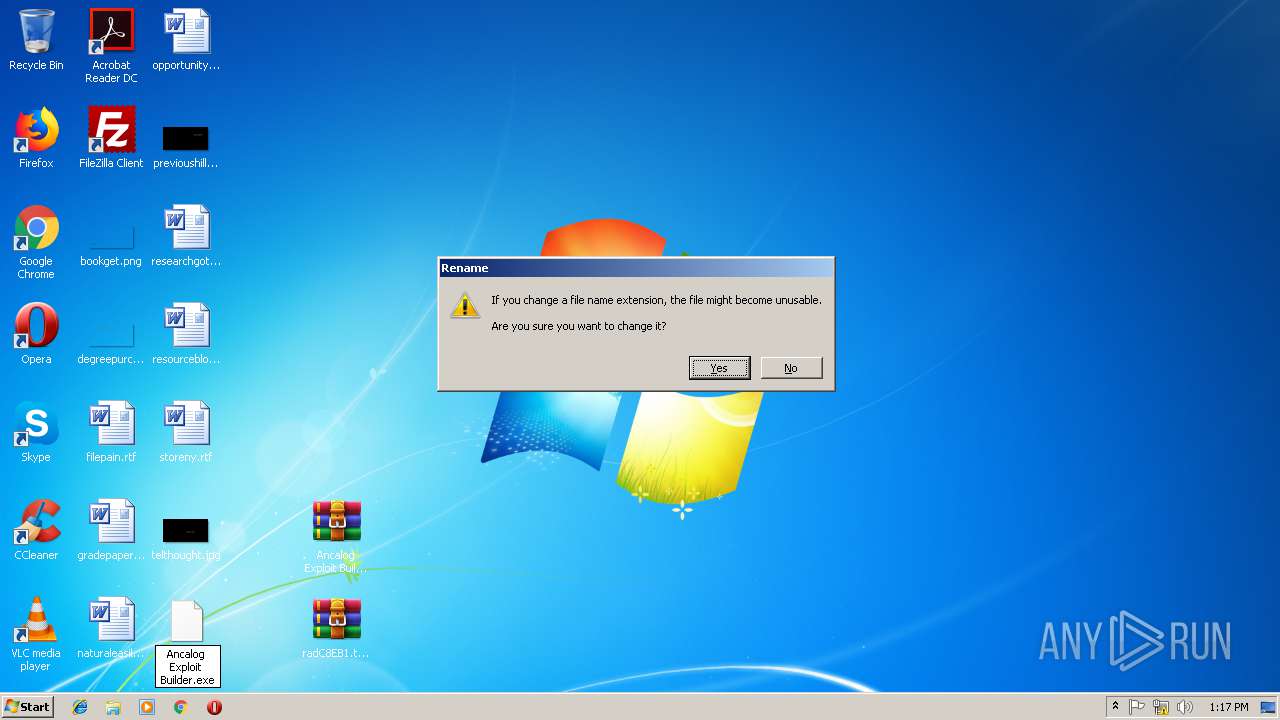
Application was dropped or rewritten from another process
- Ancalog Exploit Builder.exe (PID: 3632)
- JrCXudMk.exe (PID: 2848)
- JrCXudMk.exe (PID: 2724)
- DGhkQwOw.exe (PID: 3476)
- Ancalog Exploit Builder.exe (PID: 3428)
- JrCXudMk.exe (PID: 1728)
- JrCXudMk.exe (PID: 2660)
- DGhkQwOw.exe (PID: 2316)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2888)
- Ancalog Exploit Builder.exe (PID: 3632)
- Ancalog Exploit Builder.exe (PID: 3428)
Creates files in the user directory
- DGhkQwOw.exe (PID: 3476)
- DGhkQwOw.exe (PID: 2316)
INFO
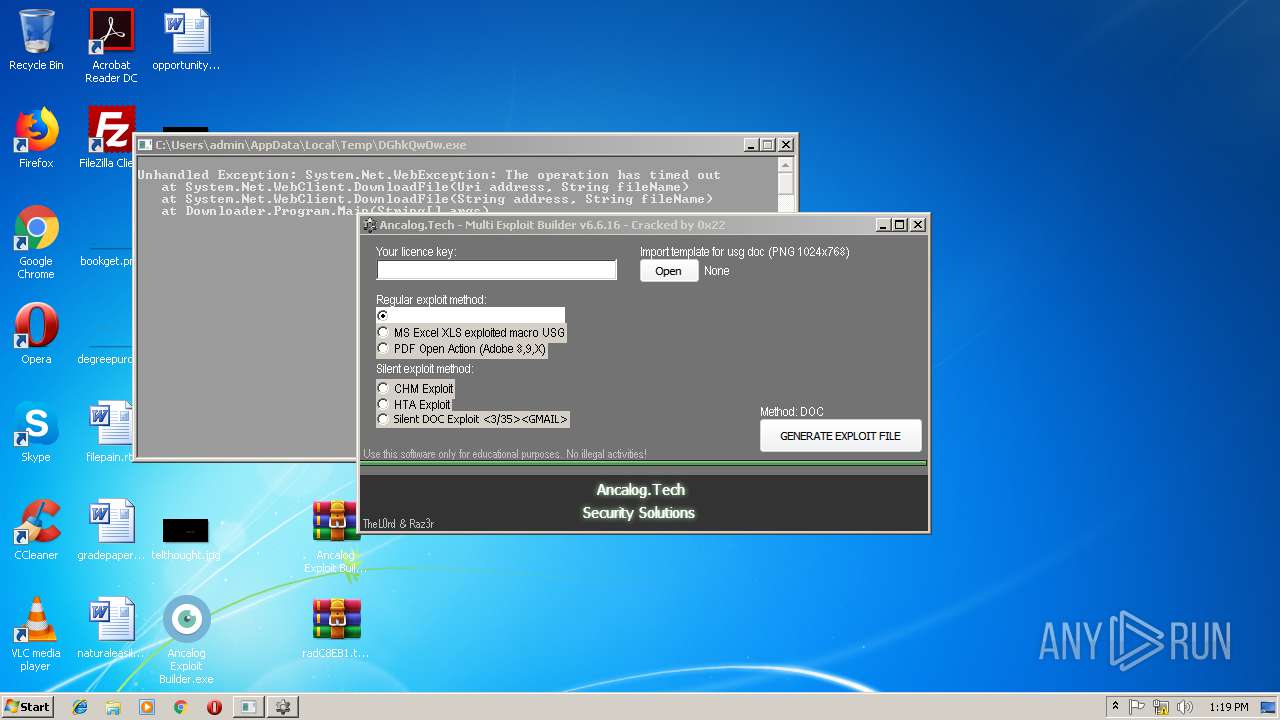
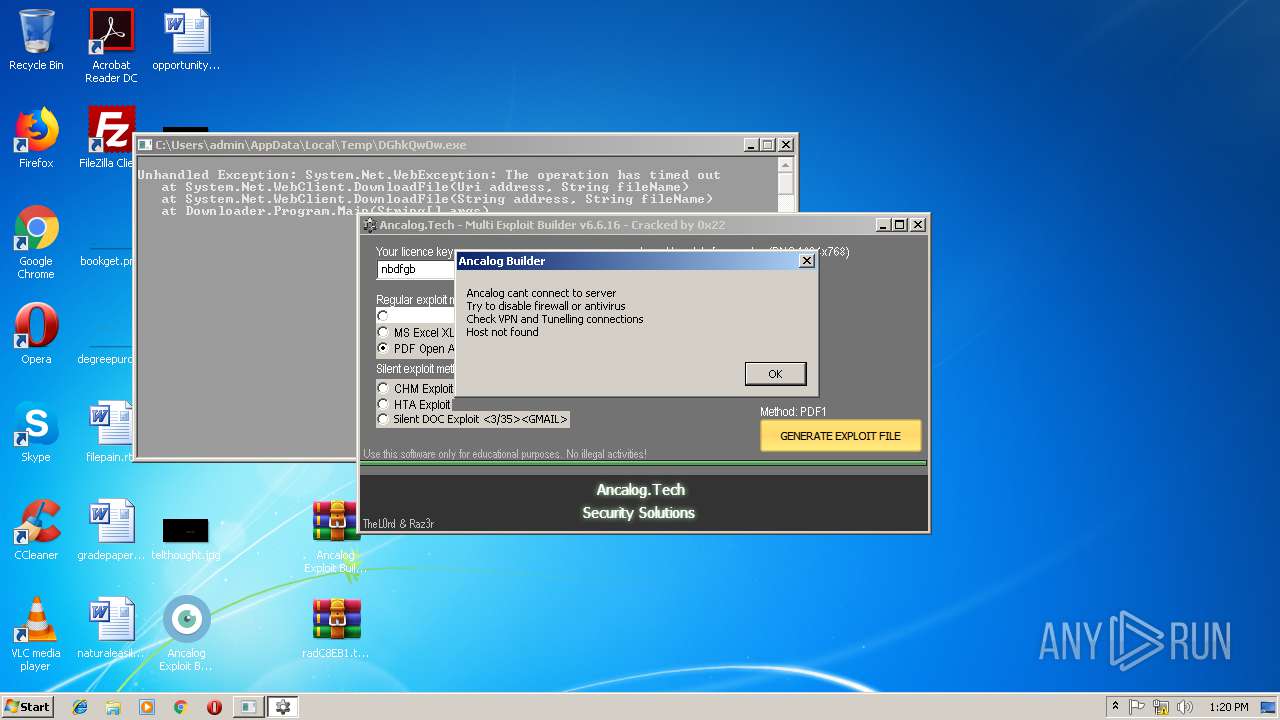
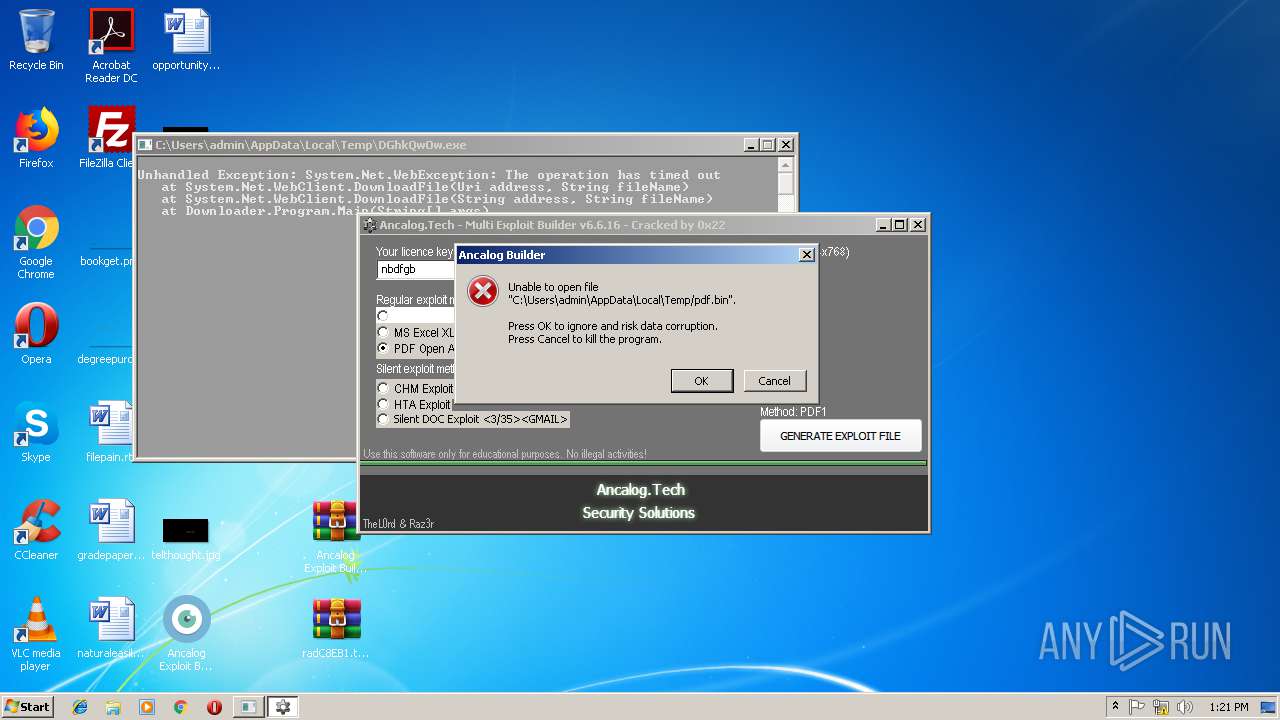
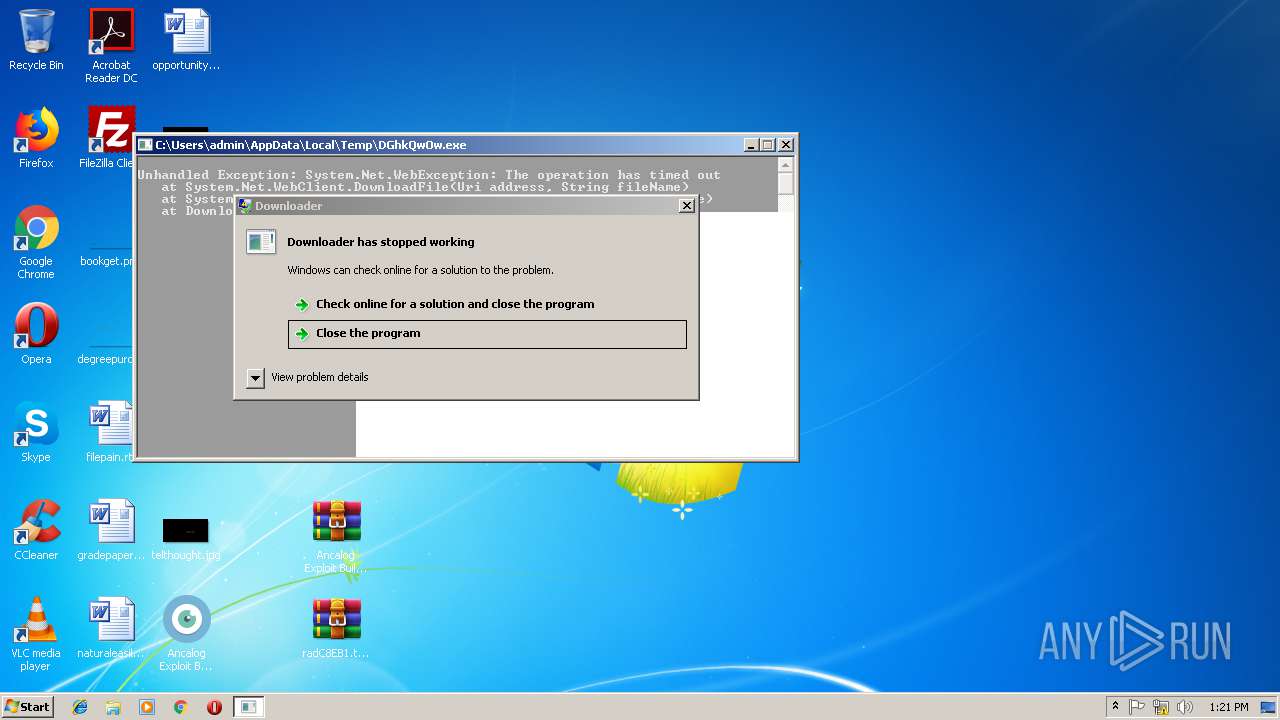
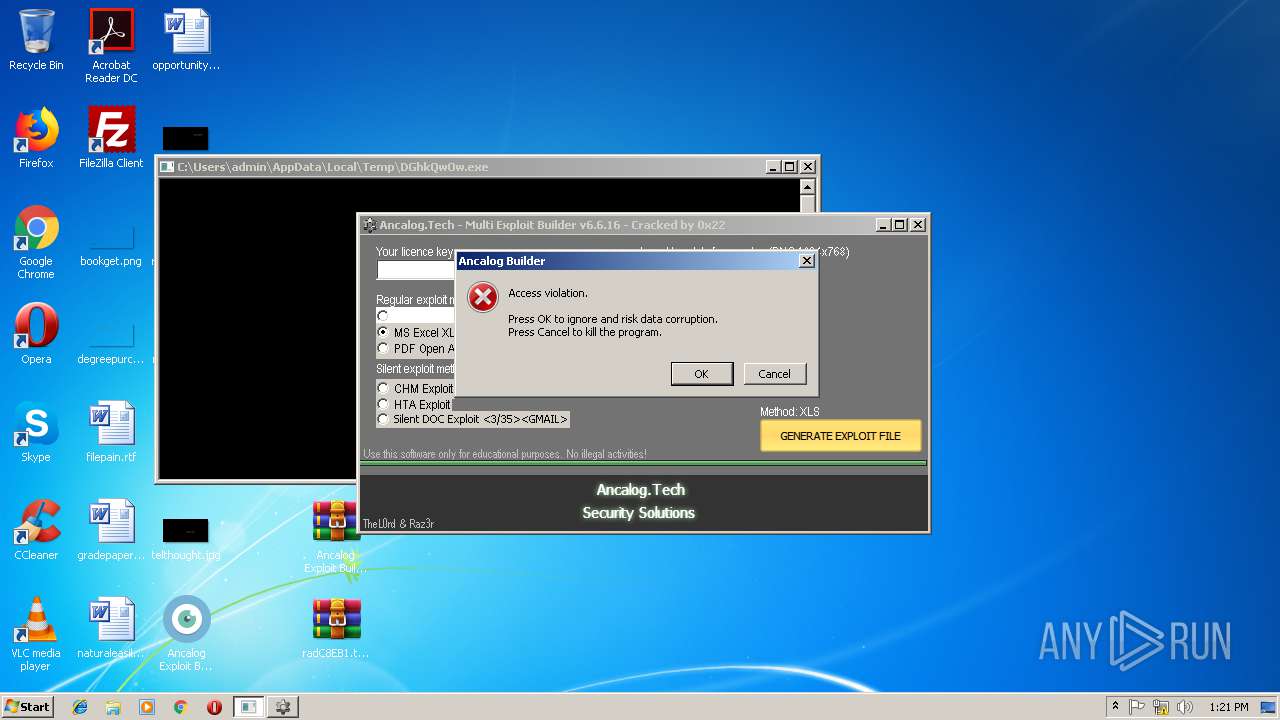
Application was crashed
- DGhkQwOw.exe (PID: 3476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
52
Monitored processes
10
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
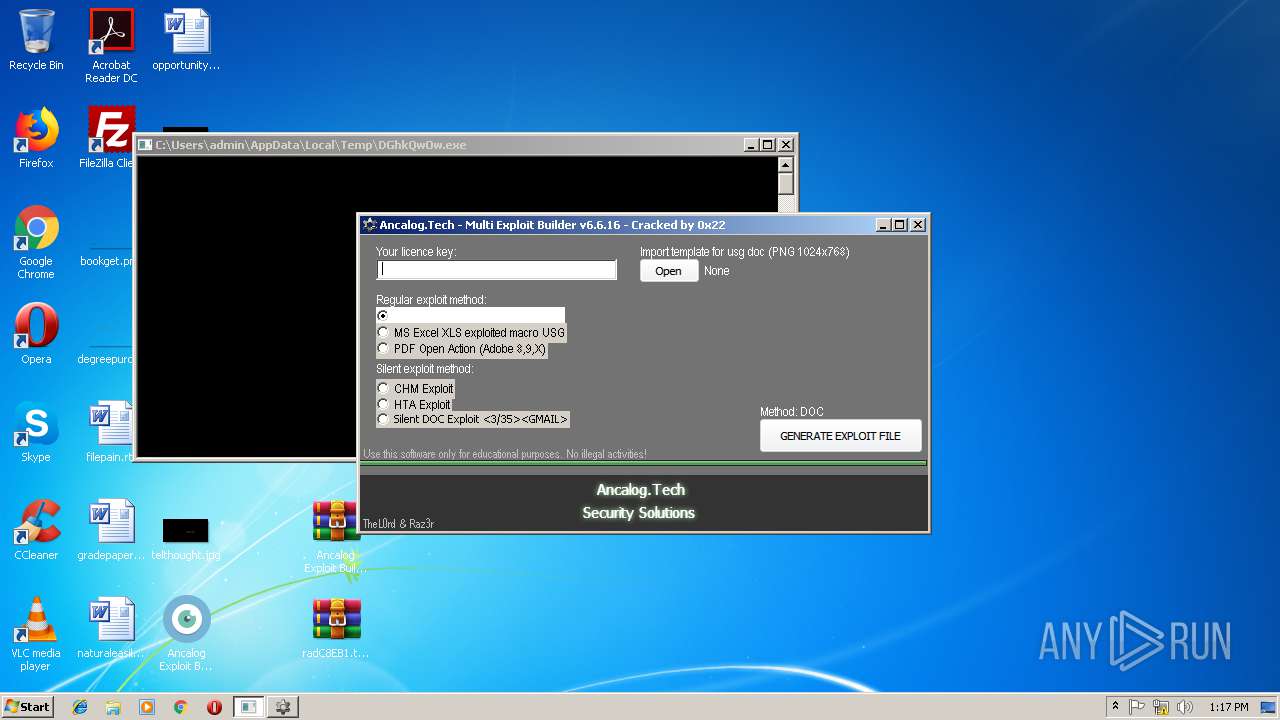
| 1728 | "C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe" | C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe | — | Ancalog Exploit Builder.exe | |||||||||||
User: admin Company: ancalog.tech Integrity Level: MEDIUM Description: Ancalog Multi Exploit Builder Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2316 | "C:\Users\admin\AppData\Local\Temp\DGhkQwOw.exe" | C:\Users\admin\AppData\Local\Temp\DGhkQwOw.exe | Ancalog Exploit Builder.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Downloader Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2660 | "C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe" | C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe | Ancalog Exploit Builder.exe | ||||||||||||
User: admin Company: ancalog.tech Integrity Level: HIGH Description: Ancalog Multi Exploit Builder Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2724 | "C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe" | C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe | Ancalog Exploit Builder.exe | ||||||||||||
User: admin Company: ancalog.tech Integrity Level: HIGH Description: Ancalog Multi Exploit Builder Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe" | C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe | — | Ancalog Exploit Builder.exe | |||||||||||
User: admin Company: ancalog.tech Integrity Level: MEDIUM Description: Ancalog Multi Exploit Builder Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
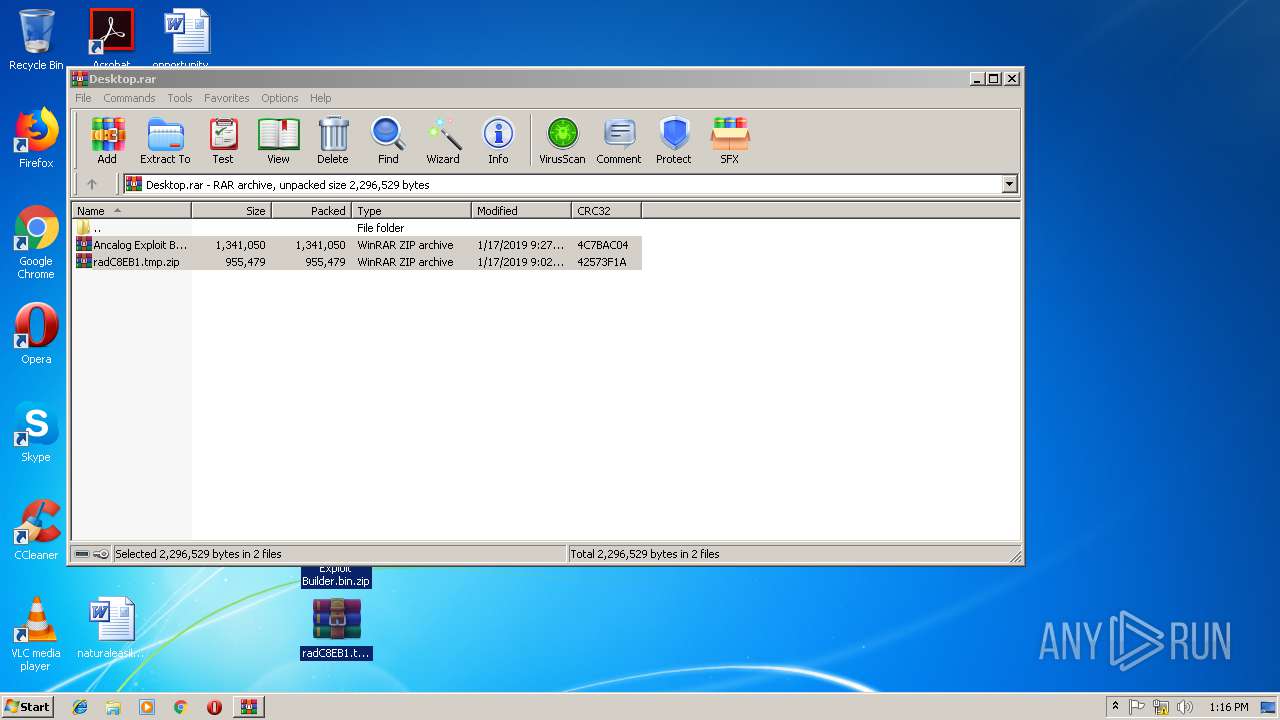
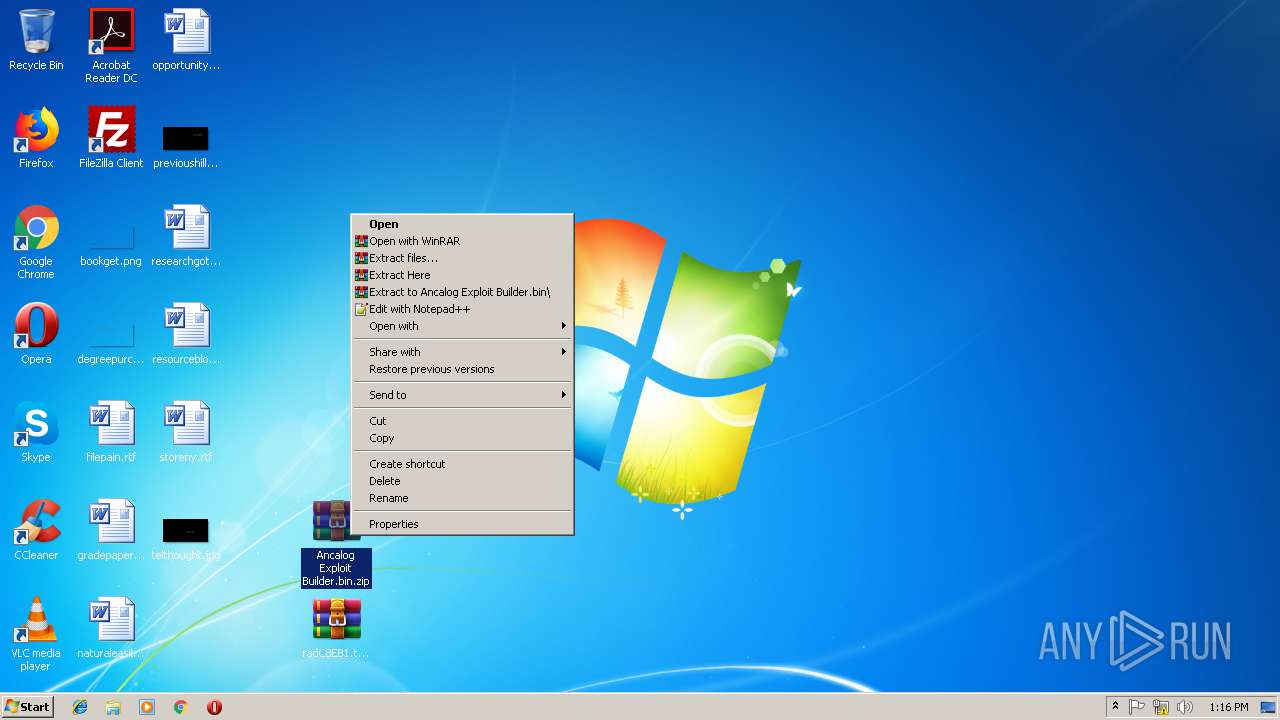
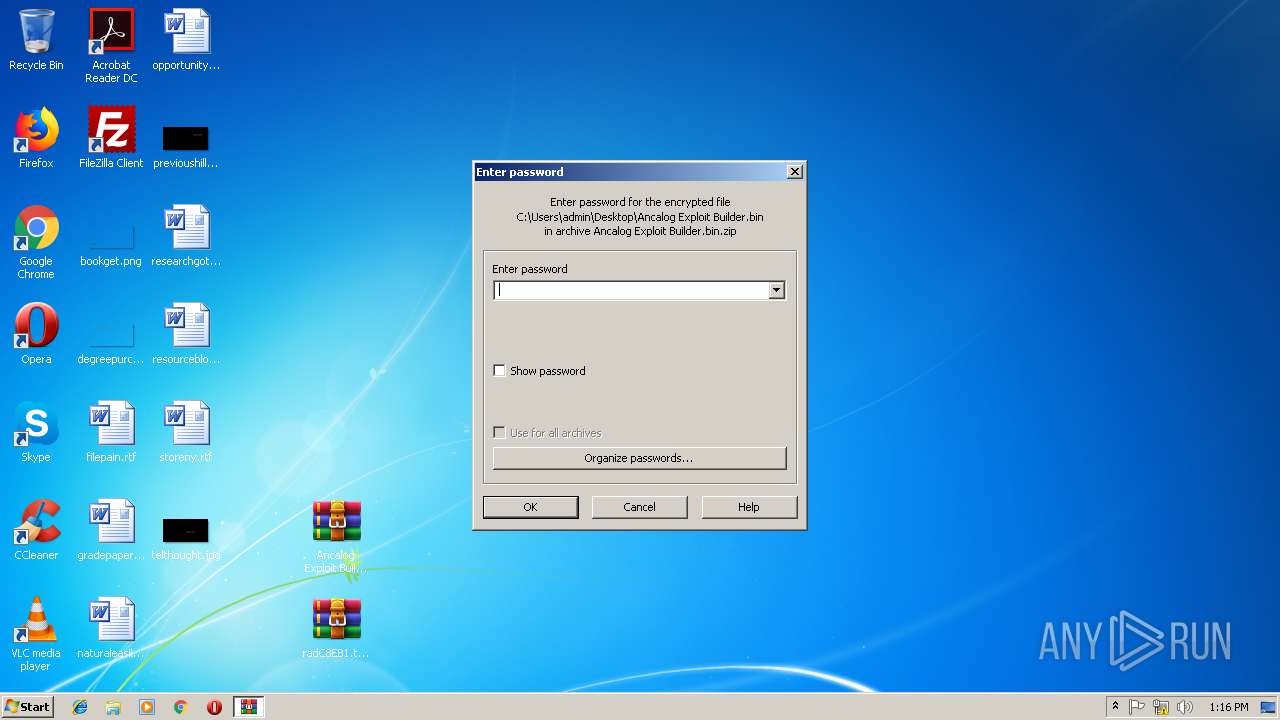
| 2888 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Ancalog Exploit Builder.bin.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Desktop.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
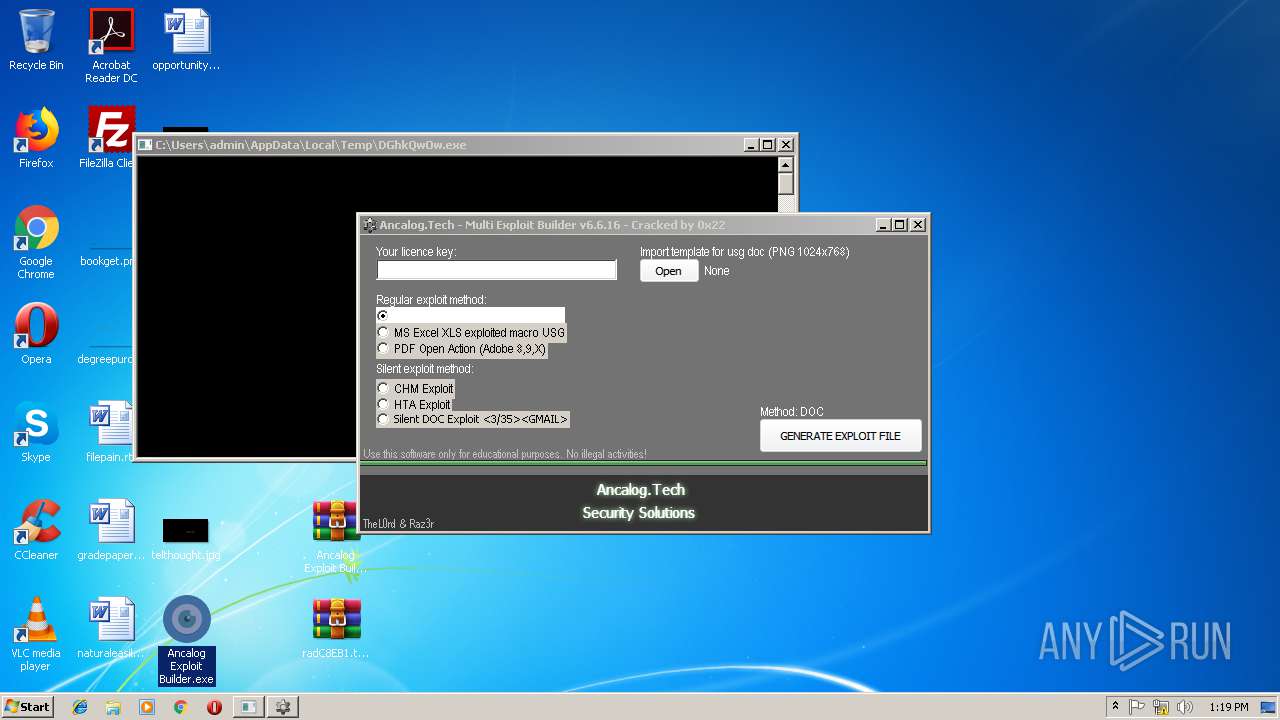
| 3428 | "C:\Users\admin\Desktop\Ancalog Exploit Builder.exe" | C:\Users\admin\Desktop\Ancalog Exploit Builder.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3476 | "C:\Users\admin\AppData\Local\Temp\DGhkQwOw.exe" | C:\Users\admin\AppData\Local\Temp\DGhkQwOw.exe | Ancalog Exploit Builder.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Downloader Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3632 | "C:\Users\admin\Desktop\Ancalog Exploit Builder.exe" | C:\Users\admin\Desktop\Ancalog Exploit Builder.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 765
Read events
1 691
Write events
73
Delete events
1
Modification events
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Desktop.rar | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3024) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
5
Suspicious files
2
Text files
0
Unknown types
0
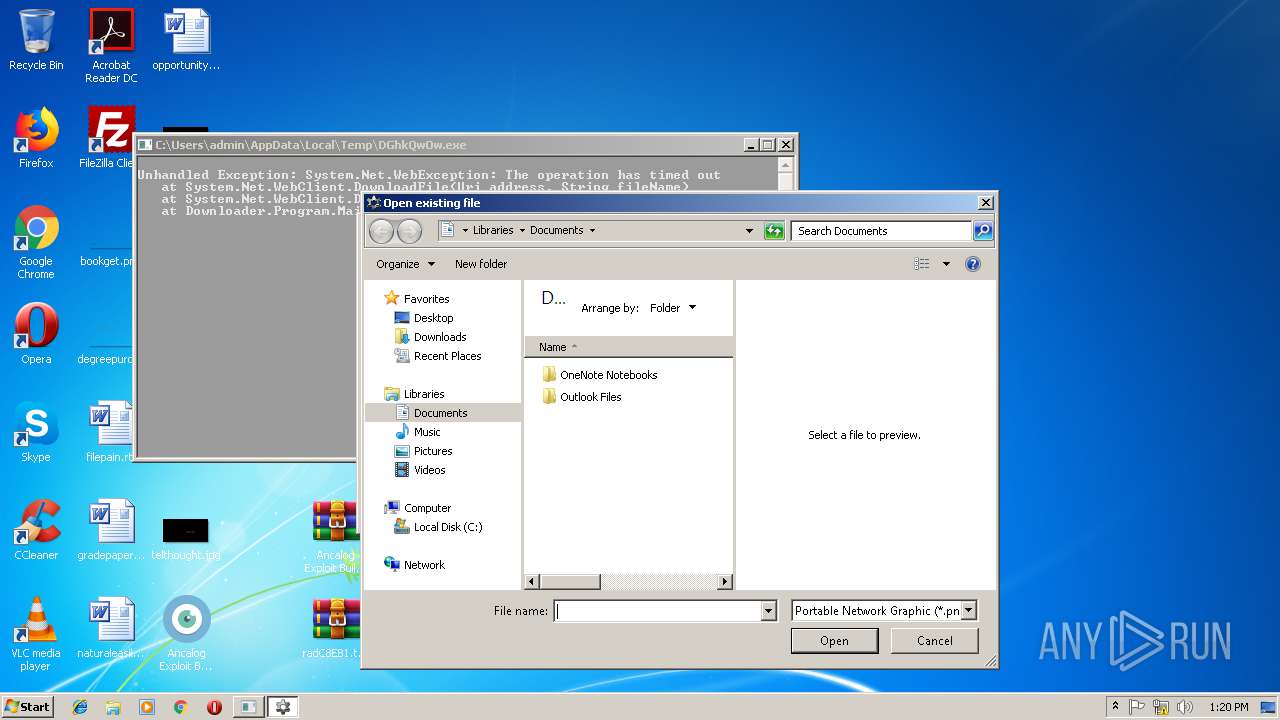
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3024.40830\Ancalog Exploit Builder.bin.zip | compressed | |
MD5:— | SHA256:— | |||
| 3428 | Ancalog Exploit Builder.exe | C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe | executable | |
MD5:— | SHA256:— | |||
| 3024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3024.40830\radC8EB1.tmp.zip | compressed | |
MD5:— | SHA256:— | |||
| 2888 | WinRAR.exe | C:\Users\admin\Desktop\Ancalog Exploit Builder.bin | executable | |
MD5:— | SHA256:— | |||
| 3632 | Ancalog Exploit Builder.exe | C:\Users\admin\AppData\Local\Temp\DGhkQwOw.exe | executable | |
MD5:— | SHA256:— | |||
| 3632 | Ancalog Exploit Builder.exe | C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe | executable | |
MD5:— | SHA256:— | |||
| 3428 | Ancalog Exploit Builder.exe | C:\Users\admin\AppData\Local\Temp\DGhkQwOw.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
3
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.22.110:80 | — | Google Inc. | US | whitelisted |
3476 | DGhkQwOw.exe | 66.55.90.17:443 | a.pomf.cat | GigeNET | US | malicious |
2316 | DGhkQwOw.exe | 66.55.90.17:443 | a.pomf.cat | GigeNET | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
a.pomf.cat |
| unknown |
ancalog.tech |
| unknown |
Threats
4 ETPRO signatures available at the full report