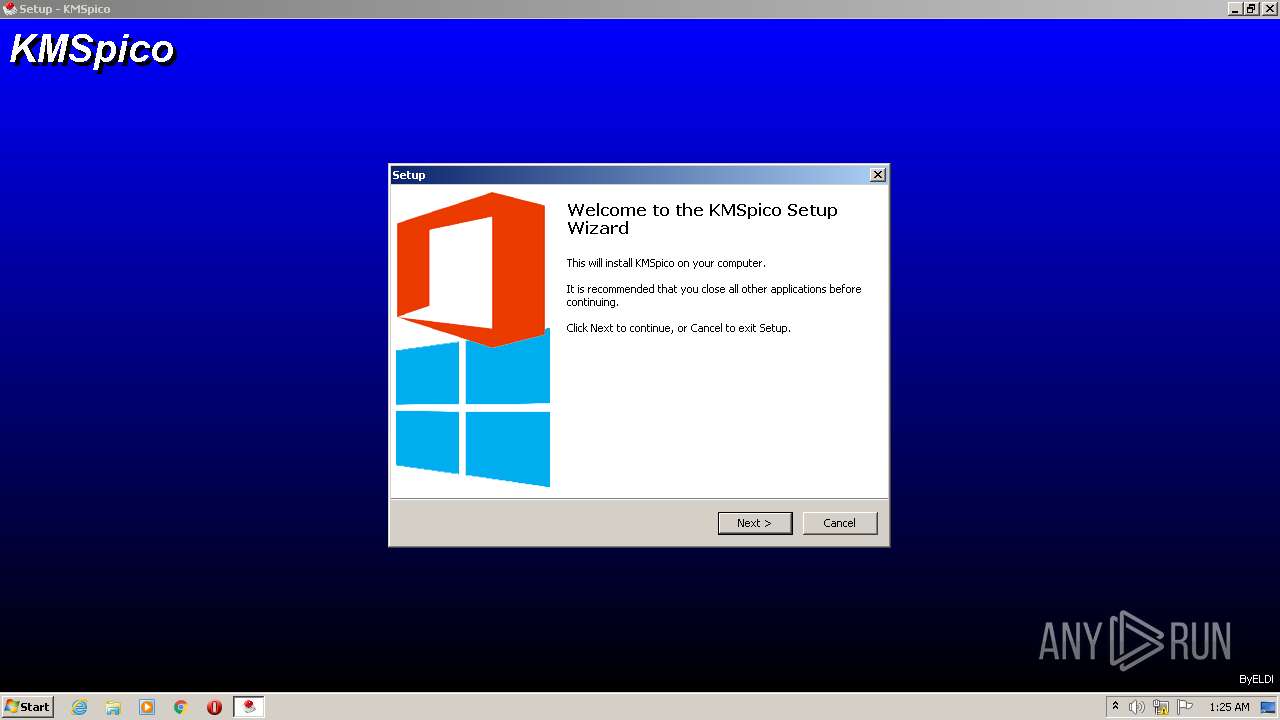
| File name: | KMSpico.exe |
| Full analysis: | https://app.any.run/tasks/db660071-26c5-40ca-b49d-8866ef86e42b |
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2022, 00:22:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E3BB2EAF87498BF9428C9DA2F923015D |
| SHA1: | 9540E54CE249B9AE4A167C571D0C0BFD7F233FC5 |
| SHA256: | F39429A2790F6BD00CFF1C8BE71C37173E5C17D2311B2AA6E147E3B0986973D2 |
| SSDEEP: | 98304:bbXxNGFPJLM4QkVj1Wz2dqN7MXyTSQBj5WTGVuYA1B7Az:bjTGFPJ44QkVj1Wz2d6IXmSyjbVuYA4z |
MALICIOUS
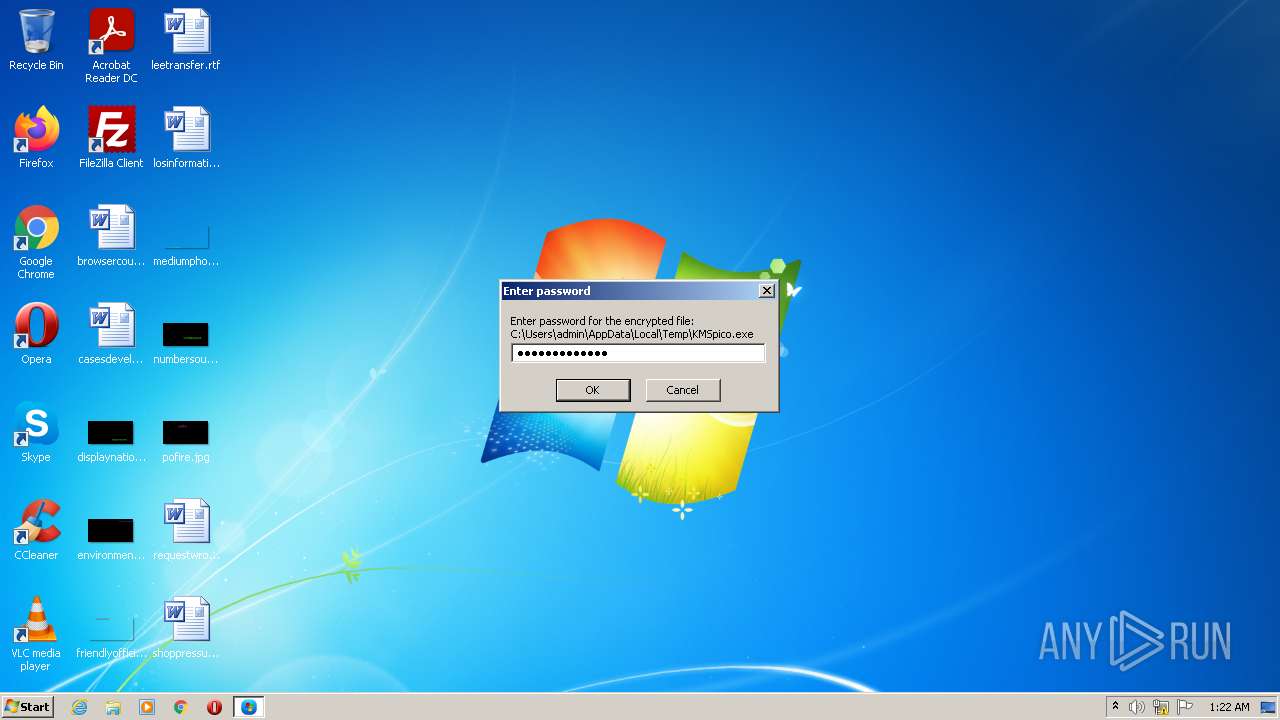
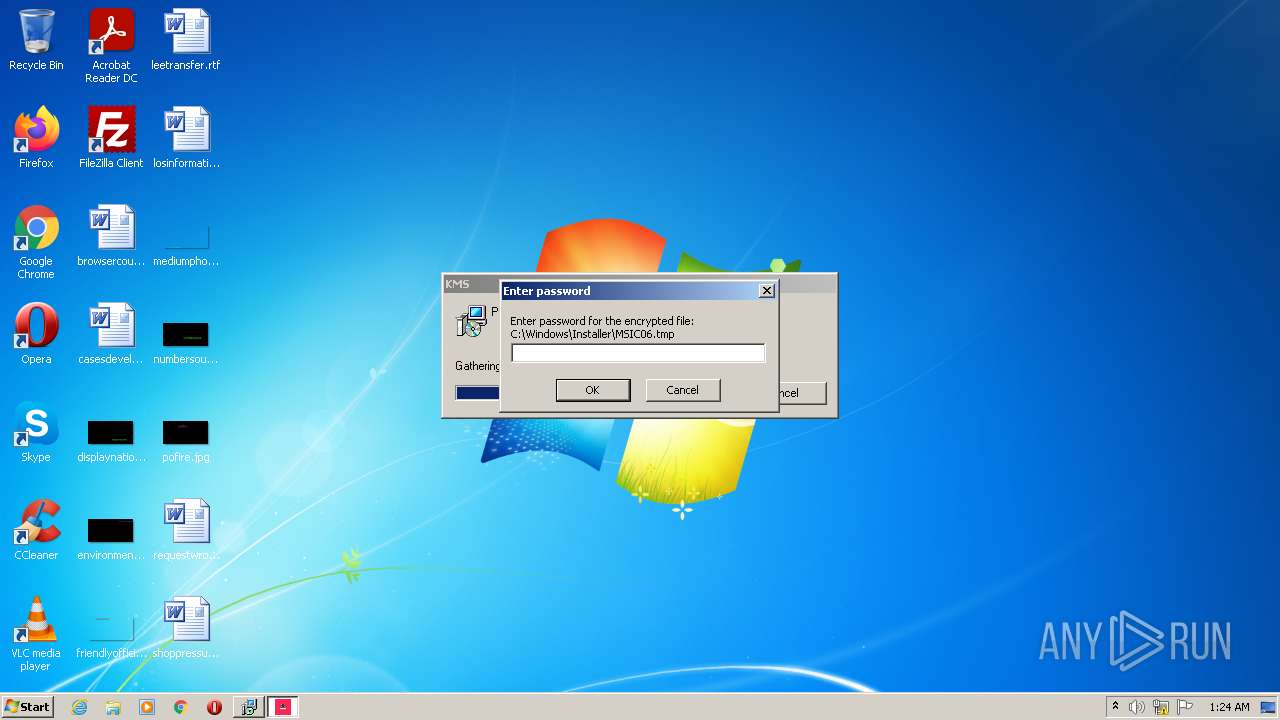
Drops the executable file immediately after the start
- KMSpico.exe (PID: 500)
- msiexec.exe (PID: 2960)
- MSIC06.tmp (PID: 4000)
- setup.exe (PID: 4032)
- setup.exe (PID: 2776)
- setup.tmp (PID: 2376)
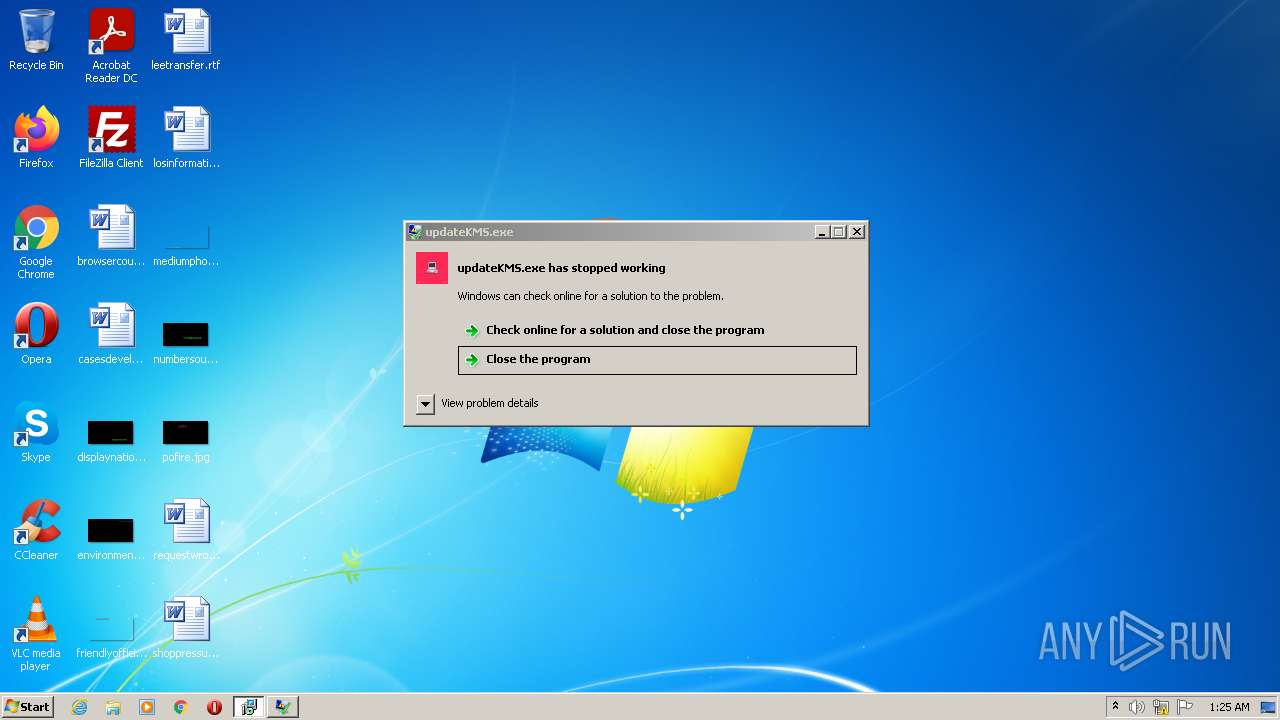
Application was dropped or rewritten from another process
- updateKMS.exe (PID: 3628)
- updateKMS.exe (PID: 360)
- setup.exe (PID: 4032)
- setup.exe (PID: 2776)
- KMSELDI.exe (PID: 3720)
- AutoPico.exe (PID: 352)
- UninsHs.exe (PID: 2240)
Steals credentials from Web Browsers
- updateKMS.exe (PID: 360)
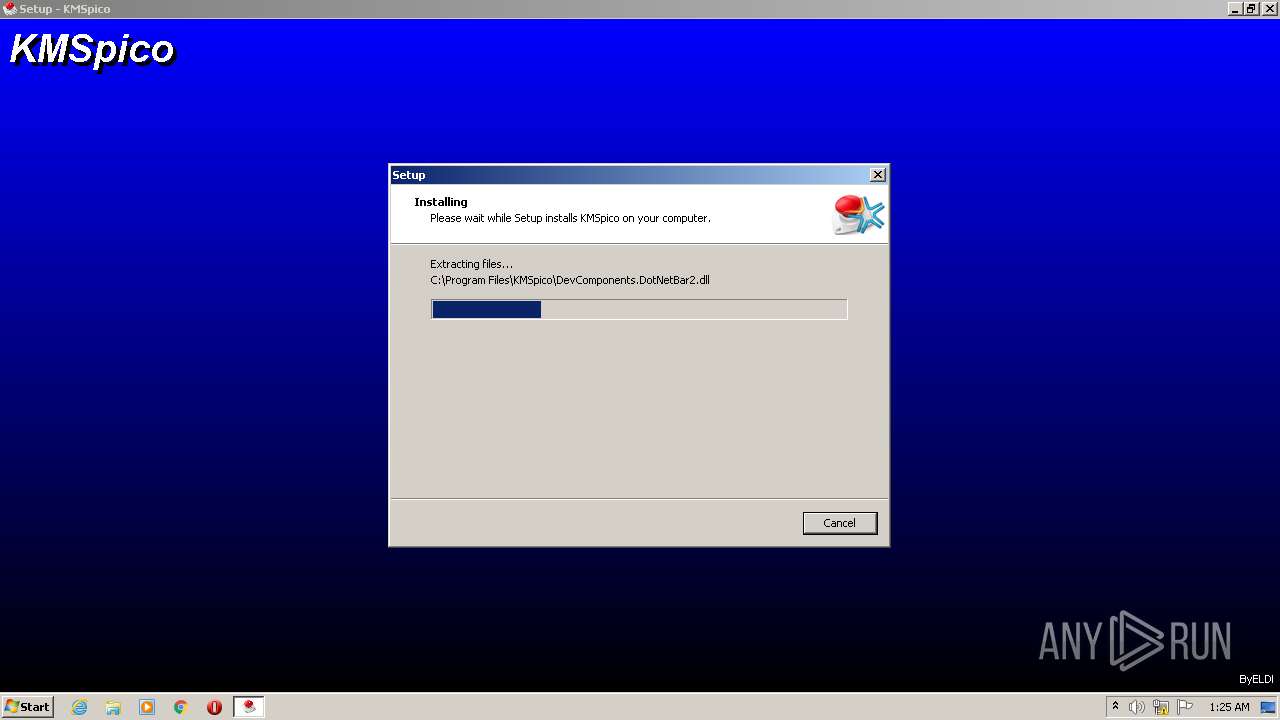
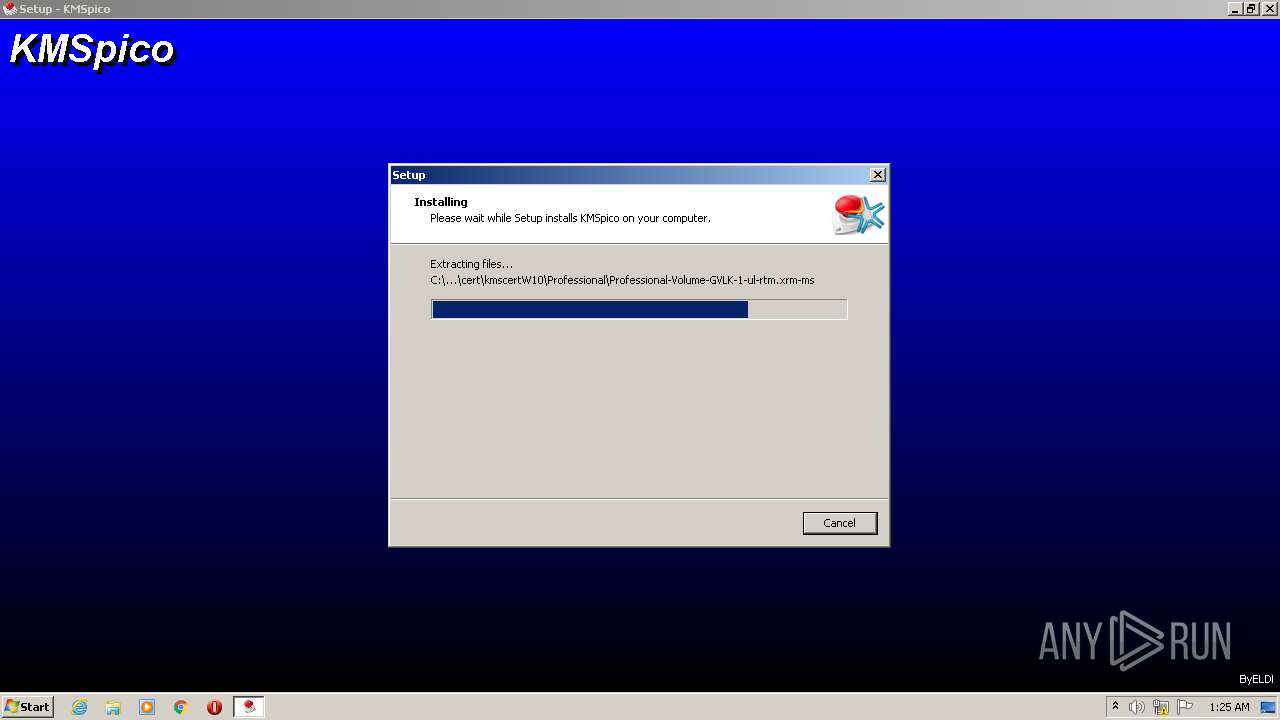
Creates a writable file the system directory
- setup.tmp (PID: 2376)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1160)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3704)
Loads dropped or rewritten executable
- KMSELDI.exe (PID: 3720)
SUSPICIOUS
Drops a file with too old compile date
- KMSpico.exe (PID: 500)
- msiexec.exe (PID: 2960)
- setup.exe (PID: 4032)
- setup.exe (PID: 2776)
- setup.tmp (PID: 2376)
Executable content was dropped or overwritten
- KMSpico.exe (PID: 500)
- msiexec.exe (PID: 2960)
- MSIC06.tmp (PID: 4000)
- setup.exe (PID: 4032)
- setup.exe (PID: 2776)
- setup.tmp (PID: 2376)
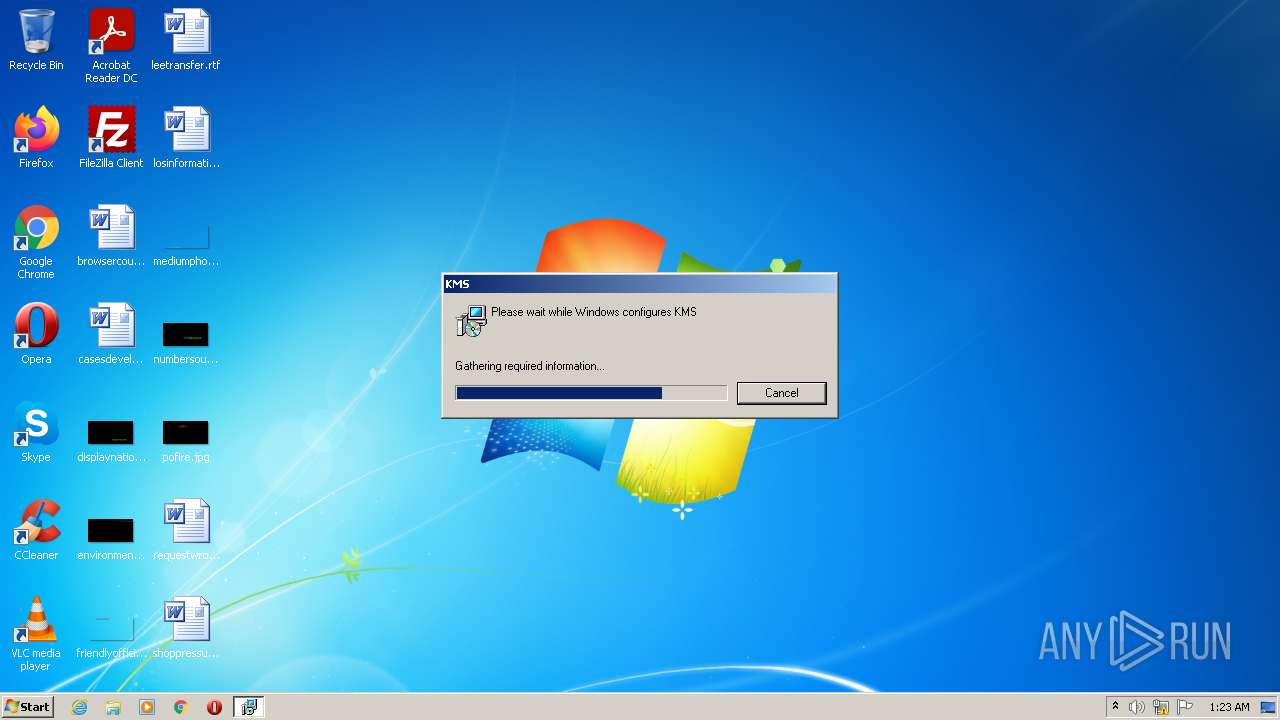
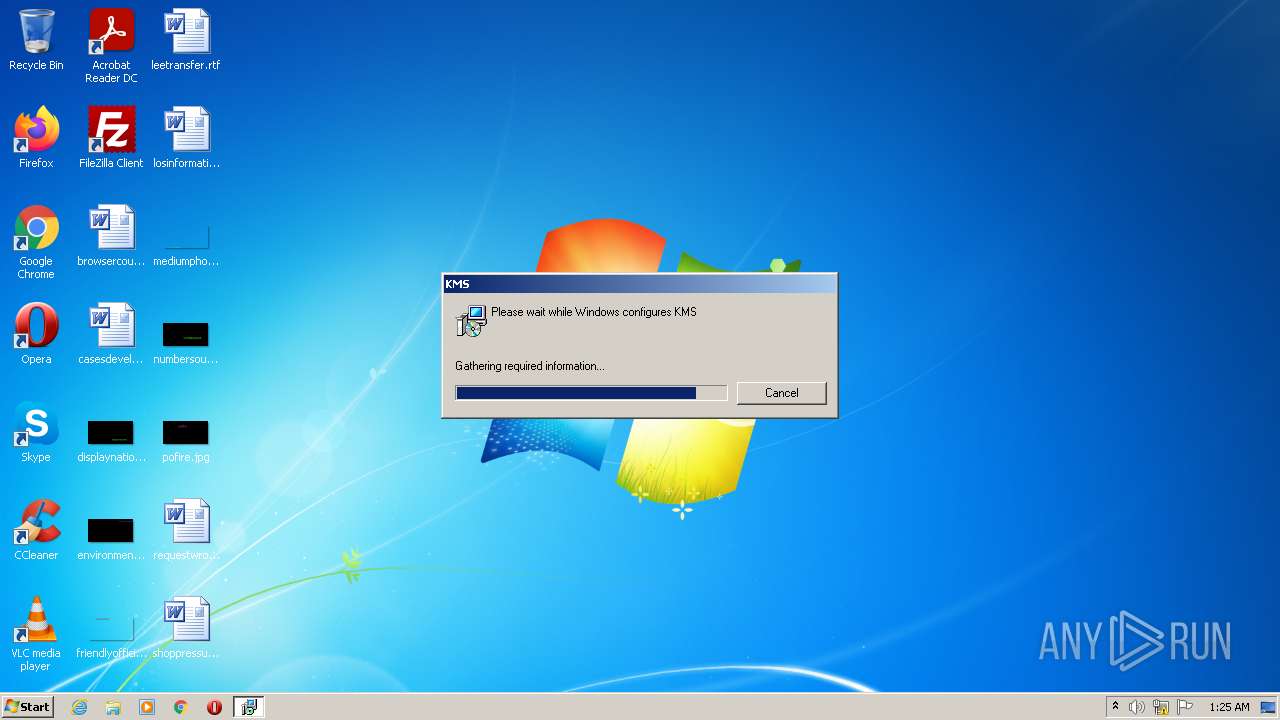
Starts Microsoft Installer
- KMSpico.exe (PID: 500)
- msiexec.exe (PID: 2960)
Reads Internet Settings
- KMSpico.exe (PID: 500)
- MSIC06.tmp (PID: 4000)
- updateKMS.exe (PID: 360)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 2960)
- setup.tmp (PID: 2376)
Reads the cookies of browsers
- updateKMS.exe (PID: 360)
Checks Windows Trust Settings
- updateKMS.exe (PID: 360)
Reads security settings of Internet Explorer
- updateKMS.exe (PID: 360)
Process checks DPAPI master keys
- updateKMS.exe (PID: 360)
Reads settings of System Certificates
- updateKMS.exe (PID: 360)
Creates files in the Windows directory
- setup.tmp (PID: 2376)
Modifies the phishing filter of IE
- setup.tmp (PID: 2376)
Starts CMD.EXE for commands execution
- setup.tmp (PID: 2376)
Starts SC.EXE for service management
- cmd.exe (PID: 3000)
Creates a directory in Program Files
- KMSELDI.exe (PID: 3720)
- setup.tmp (PID: 2376)
Creates or modifies Windows services
- KMSELDI.exe (PID: 3720)
INFO
Checks supported languages
- KMSpico.exe (PID: 500)
- msiexec.exe (PID: 2960)
- MsiExec.exe (PID: 2284)
- updateKMS.exe (PID: 360)
- MSIC06.tmp (PID: 4000)
- setup.exe (PID: 4032)
- setup.tmp (PID: 1436)
- setup.exe (PID: 2776)
- UninsHs.exe (PID: 2240)
- KMSELDI.exe (PID: 3720)
- AutoPico.exe (PID: 352)
- setup.tmp (PID: 2376)
Reads the computer name
- KMSpico.exe (PID: 500)
- msiexec.exe (PID: 2960)
- MsiExec.exe (PID: 2284)
- updateKMS.exe (PID: 360)
- MSIC06.tmp (PID: 4000)
- setup.tmp (PID: 1436)
- setup.tmp (PID: 2376)
- KMSELDI.exe (PID: 3720)
- AutoPico.exe (PID: 352)
Creates a file in a temporary directory
- KMSpico.exe (PID: 500)
- msiexec.exe (PID: 2960)
- MSIC06.tmp (PID: 4000)
- setup.exe (PID: 4032)
- setup.exe (PID: 2776)
- setup.tmp (PID: 2376)
Process checks LSA protection
- msiexec.exe (PID: 2960)
- MsiExec.exe (PID: 2284)
- MSIC06.tmp (PID: 4000)
- updateKMS.exe (PID: 360)
- setup.tmp (PID: 1436)
- setup.tmp (PID: 2376)
- KMSELDI.exe (PID: 3720)
- KMSpico.exe (PID: 500)
- AutoPico.exe (PID: 352)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2960)
- MsiExec.exe (PID: 2284)
- updateKMS.exe (PID: 360)
- MSIC06.tmp (PID: 4000)
- KMSELDI.exe (PID: 3720)
- AutoPico.exe (PID: 352)
- KMSpico.exe (PID: 500)
Application launched itself
- msiexec.exe (PID: 2960)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 2960)
- MSIC06.tmp (PID: 4000)
- setup.tmp (PID: 2376)
Starts application with an unusual extension
- msiexec.exe (PID: 2960)
Application was dropped or rewritten from another process
- MSIC06.tmp (PID: 4000)
- setup.tmp (PID: 1436)
- setup.tmp (PID: 2376)
Creates files in the user directory
- updateKMS.exe (PID: 360)
- msiexec.exe (PID: 2960)
Process looks inside Credentials folder
- updateKMS.exe (PID: 360)
Creates a software uninstall entry
- msiexec.exe (PID: 2960)
- setup.tmp (PID: 2376)
Loads dropped or rewritten executable
- setup.tmp (PID: 2376)
Reads product name
- KMSELDI.exe (PID: 3720)
- AutoPico.exe (PID: 352)
Reads Environment values
- KMSELDI.exe (PID: 3720)
- AutoPico.exe (PID: 352)
Creates files in the program directory
- AutoPico.exe (PID: 352)
- KMSELDI.exe (PID: 3720)
- setup.tmp (PID: 2376)
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 3720)
- AutoPico.exe (PID: 352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2020-Dec-01 18:00:55 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 280 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 6 |
| TimeDateStamp: | 2020-Dec-01 18:00:55 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 200938 | 201216 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70808 |
.rdata | 208896 | 42514 | 43008 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22174 |
.data | 253952 | 145192 | 4096 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70882 |
.didat | 401408 | 392 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29825 |
.rsrc | 405504 | 233276 | 233472 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.75004 |
.reloc | 638976 | 8808 | 9216 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55486 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.98495 | 52300 | Latin 1 / Western European | Process Default Language | RT_ICON |
2 | 6.01474 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 6.02466 | 38056 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 6.25675 | 21640 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 6.10997 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 6.12151 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 6.18412 | 4264 | Latin 1 / Western European | Process Default Language | RT_ICON |
8 | 6.53858 | 2440 | Latin 1 / Western European | Process Default Language | RT_ICON |
9 | 6.13458 | 1128 | Latin 1 / Western European | Process Default Language | RT_ICON |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
67
Monitored processes
18
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Program Files\KMSpico\AutoPico.exe" /silent | C:\Program Files\KMSpico\AutoPico.exe | setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: AutoPico Exit code: 0 Version: 16.1.0.0 Modules
| |||||||||||||||
| 360 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\updateKMS.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\updateKMS.exe | MSIC06.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 500 | "C:\Users\admin\AppData\Local\Temp\KMSpico.exe" | C:\Users\admin\AppData\Local\Temp\KMSpico.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1160 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Task.cmd"" | C:\Windows\system32\cmd.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1436 | "C:\Users\admin\AppData\Local\Temp\is-G52JB.tmp\setup.tmp" /SL5="$2016A,2952592,69120,C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-G52JB.tmp\setup.tmp | — | setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\KMSpico\UninsHs.exe" /r0=KMSpico,default,C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe | C:\Program Files\KMSpico\UninsHs.exe | — | setup.tmp | |||||||||||
User: admin Company: Han-soft Integrity Level: HIGH Description: Uninstall for InnoSetup by Han-soft Exit code: 0 Version: 2.1.0.283 Modules
| |||||||||||||||
| 2284 | C:\Windows\system32\MsiExec.exe -Embedding B6D0A327321263F4245E539F5F29DF1C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | "C:\Users\admin\AppData\Local\Temp\is-ENC34.tmp\setup.tmp" /SL5="$3016E,2952592,69120,C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe" /SPAWNWND=$30162 /NOTIFYWND=$2016A | C:\Users\admin\AppData\Local\Temp\is-ENC34.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2656 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\RarSFX0\KMS2021.msi" | C:\Windows\System32\msiexec.exe | — | KMSpico.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe" /SPAWNWND=$30162 /NOTIFYWND=$2016A | C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe | setup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KMSpico Setup Exit code: 0 Version: 10.2.0 Modules
| |||||||||||||||
Total events
10 600
Read events
10 414
Write events
168
Delete events
18
Modification events
| (PID) Process: | (500) KMSpico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (500) KMSpico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (500) KMSpico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (500) KMSpico.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2960) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 900B0000B8CB59469AE9D801 | |||
| (PID) Process: | (2960) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 38E0E866E213141C54392BCAE8F4005FE53537AC01567A83F2CC0FA23E10B601 | |||
| (PID) Process: | (2960) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2960) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | (default) |
Value: C:\Windows\Installer\e0a10.ipi | |||
| (PID) Process: | (4000) MSIC06.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4000) MSIC06.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
44
Suspicious files
10
Text files
715
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | msiexec.exe | C:\Windows\Installer\e0a10.ipi | binary | |
MD5:— | SHA256:— | |||
| 2960 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF26521BF294BE5988.TMP | gmc | |
MD5:— | SHA256:— | |||
| 360 | updateKMS.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 360 | updateKMS.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_E83E956509DAA513B179DCD268BFCEFC | binary | |
MD5:— | SHA256:— | |||
| 360 | updateKMS.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2960 | msiexec.exe | C:\Windows\Installer\e0a0e.msi | executable | |
MD5:3E490C47CF5D9B27D6F61CB0D633CC64 | SHA256:A4EF7292A3FE3AC137735336D2C3B45BCA5A2B4B2C12A1256D7900A6CC89D129 | |||
| 500 | KMSpico.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KMS2021.msi | executable | |
MD5:3E490C47CF5D9B27D6F61CB0D633CC64 | SHA256:A4EF7292A3FE3AC137735336D2C3B45BCA5A2B4B2C12A1256D7900A6CC89D129 | |||
| 2960 | msiexec.exe | C:\Windows\Installer\MSIC06.tmp | executable | |
MD5:EF354539C0EB92E8C7B45380C9E7E021 | SHA256:BAC9495DF4C5A9703FC4424C415919F15563CA0A30C41059C83BFD78801179AF | |||
| 500 | KMSpico.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.exe | executable | |
MD5:A02164371A50C5FF9FA2870EF6E8CFA3 | SHA256:64C731ADBE1B96CB5765203B1E215093DCF268D020B299445884A4AE62ED2D3A | |||
| 2960 | msiexec.exe | C:\Windows\Installer\MSIB18.tmp | executable | |
MD5:72B1C6699DDC2BAAB105D32761285DF2 | SHA256:BF7F6F7E527AB8617766BB7A21C21B2895B5275C0E808756C2AADCD66EFF8A97 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
360 | updateKMS.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAHw%2B5n0eA8d2fn4Y8m52EU%3D | US | der | 280 b | whitelisted |
360 | updateKMS.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
360 | updateKMS.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1ae242dd8cfcd23b | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
360 | updateKMS.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
360 | updateKMS.exe | 104.21.53.121:443 | polyminers.com | CLOUDFLARENET | — | unknown |
360 | updateKMS.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
polyminers.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
2.pool.ntp.org |
| whitelisted |
3.pool.ntp.org |
| whitelisted |