| File name: | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe |
| Full analysis: | https://app.any.run/tasks/db4b08fa-6ac7-42bd-8858-cb3ef9d39acd |
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2025, 02:53:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | D2BDC4EAD1D1D074A366603B26744596 |
| SHA1: | 047D757488AF131E45762CEBCF0B1CE6511D9C35 |
| SHA256: | F34D1BAFD285803CE4FBEBEE4ECFE62846DE0E8D7DC65F777FE94168FA7D797E |
| SSDEEP: | 49152:0Lz8TJdWybASbbU1bCJ0U3S3q89Bs1/B2FewaP9oo6jdpM6Lji0omv4:0LzgJdWybASbgAJ0U3Sa7NP9o37jI |
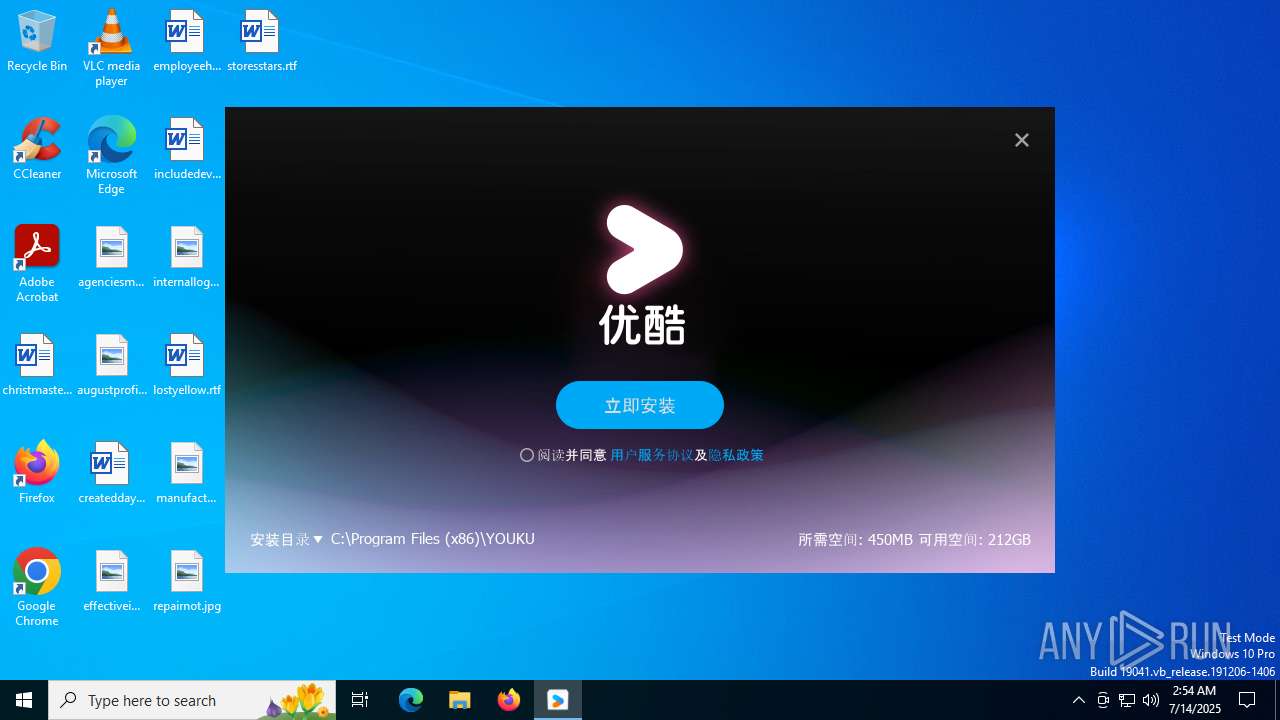
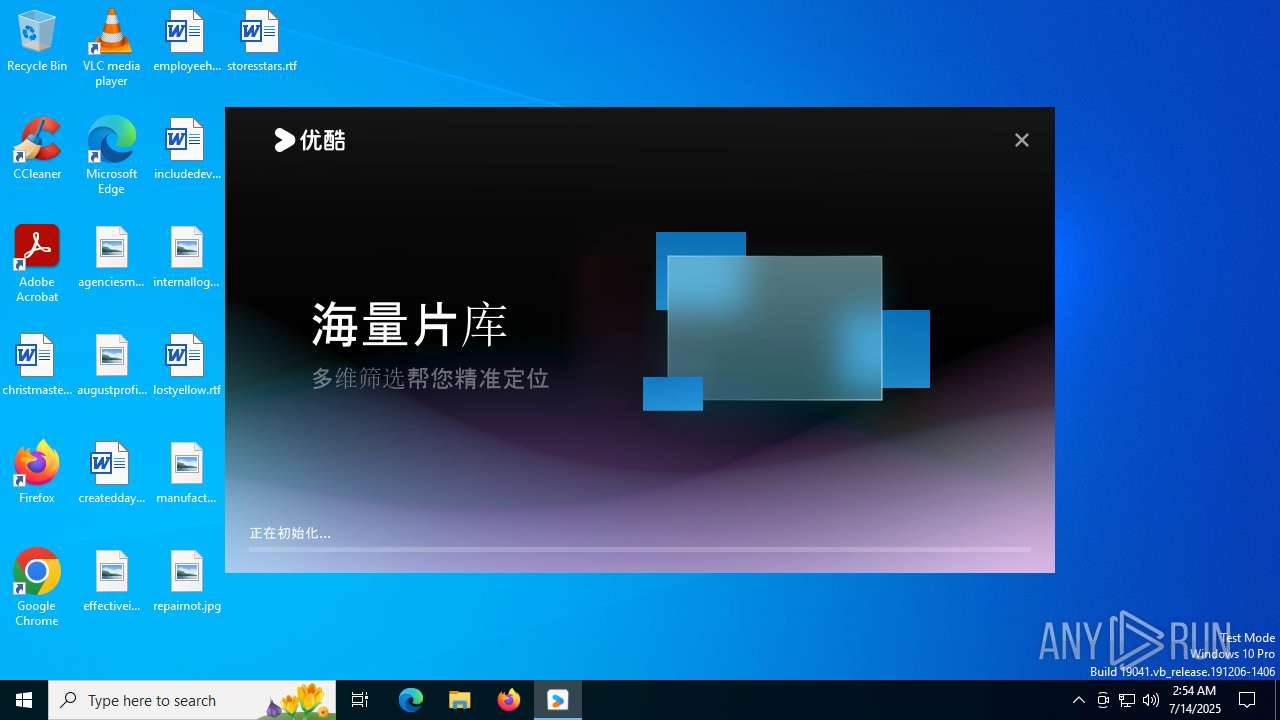
MALICIOUS
Executing a file with an untrusted certificate
- youkuclient_setup_9.2.59.1002.exe (PID: 1056)
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
SUSPICIOUS
Reads security settings of Internet Explorer
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
There is functionality for taking screenshot (YARA)
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
The process creates files with name similar to system file names
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Get information on the list of running processes
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Process drops legitimate windows executable
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Malware-specific behavior (creating "System.dll" in Temp)
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Executable content was dropped or overwritten
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
The process drops C-runtime libraries
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
INFO
The sample compiled with chinese language support
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Checks proxy server information
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
- slui.exe (PID: 6980)
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Creates files or folders in the user directory
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
Reads the computer name
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Reads the machine GUID from the registry
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Checks supported languages
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Create files in a temporary directory
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Reads the software policy settings
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
- slui.exe (PID: 6980)
Creates files in the program directory
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Process checks computer location settings
- sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe (PID: 6704)
The sample compiled with english language support
- youkuclient_setup_9.2.59.1002.exe (PID: 4460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (18) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (2.9) |
| .exe | | | Generic Win/DOS Executable (1.3) |
| .exe | | | DOS Executable Generic (1.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:12:26 03:40:04+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 768512 |
| InitializedDataSize: | 797696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x90e7a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.14.0 |
| ProductVersionNumber: | 1.0.14.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileDescription: | 下载器 |
| FileVersion: | 1.0.14.0 |
| LegalCopyright: | Copyright (C) 2021 |
| ProductName: | 下载器 |
| ProductVersion: | 1.0.14.0 |
Total processes
141
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Users\admin\AppData\Local\Temp\se_online_download\youkuclient_setup_9.2.59.1002.exe" | C:\Users\admin\AppData\Local\Temp\se_online_download\youkuclient_setup_9.2.59.1002.exe | — | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | |||||||||||
User: admin Company: 优酷 Integrity Level: MEDIUM Description: 优酷 Exit code: 3221226540 Version: 9.2.59.1002 Modules
| |||||||||||||||
| 4020 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | youkuclient_setup_9.2.59.1002.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4460 | "C:\Users\admin\AppData\Local\Temp\se_online_download\youkuclient_setup_9.2.59.1002.exe" | C:\Users\admin\AppData\Local\Temp\se_online_download\youkuclient_setup_9.2.59.1002.exe | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | ||||||||||||
User: admin Company: 优酷 Integrity Level: HIGH Description: 优酷 Version: 9.2.59.1002 Modules
| |||||||||||||||
| 6704 | "C:\Users\admin\Downloads\sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe" | C:\Users\admin\Downloads\sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 下载器 Version: 1.0.14.0 Modules
| |||||||||||||||
| 6980 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 239
Read events
4 235
Write events
4
Delete events
0
Modification events
| (PID) Process: | (6704) sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6704) sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6704) sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4460) youkuclient_setup_9.2.59.1002.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\YouKu\YoukuClient |
| Operation: | write | Name: | installId |
Value: {dd3fd45b-a344-48d8-9e3a-e2322f8175e1} | |||
Executable files
266
Suspicious files
448
Text files
652
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | C:\Users\admin\AppData\Local\Temp\se_online_download\youkuclient_setup_9.2.59.1002.exe | — | |
MD5:— | SHA256:— | |||
| 4460 | youkuclient_setup_9.2.59.1002.exe | C:\Users\admin\AppData\Local\Temp\nsqCF57.tmp\styles\qwindowsvistastyle.dll | executable | |
MD5:53AF56EA898BB82775FDD0F940C429D2 | SHA256:547606FC8A6B20A2616A4F390C6CF0E7AA713F6AD53BAE23C8D1B021885AAB0E | |||
| 4460 | youkuclient_setup_9.2.59.1002.exe | C:\Users\admin\AppData\Local\Temp\nsqCF57.tmp\platforms\qwindows.dll | executable | |
MD5:B2AF81698F607061986109B4A9004819 | SHA256:4D1EAF41136AC3FAEFB76F5CF2EFE8E7F8A11FD6A943A8B11F2F2A8BE5CFE19B | |||
| 4460 | youkuclient_setup_9.2.59.1002.exe | C:\Users\admin\AppData\Local\Temp\nsqCF57.tmp\Qt5Core.dll | executable | |
MD5:7D180286E9C071C7BC3A6BC2ACE792AC | SHA256:4F8DC460162407CFCCB1BE6EF9CCE45C4449DE838AEFFA3FD33378F01A3F9CC4 | |||
| 6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0DA515F703BB9B49479E8697ADB0B955_4136D3715888E22D65EBE484B233D81B | binary | |
MD5:82BFC6BB93032AB65E2DC027D2A7A94E | SHA256:635F2A918A67D41A2CC0A20564D0BFCC74BB83B86426C3121370A6A12A62C9C7 | |||
| 6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_50D7940D5D3FEDD8634D83074C7A46A3 | binary | |
MD5:B874B192E45423520D2D3D571B16C464 | SHA256:011672BC8562C211F60A24BC751D3EB7632D94E8AB0B4E032AC4903FE4FD41C0 | |||
| 6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\se_callback_mangguo_config[1].htm | binary | |
MD5:BF2151375E7A1A54A26D4C9EADB484AC | SHA256:8A338EFCEC9B33BCA496702A13FA236F198631E5CE2051C34E8DCE4597F52788 | |||
| 6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\349D186F1CB5682FA0194D4F3754EF36_6AC155AB4458D0D856D89A8608E588F4 | binary | |
MD5:C9CBD9AC98B125BE0C5079272B403D63 | SHA256:C9382A8160836D6D1F723D8938129BCF83D7856F94762B88CF0E000C0AABCC7D | |||
| 4460 | youkuclient_setup_9.2.59.1002.exe | C:\Users\admin\AppData\Local\Temp\nsqCF57.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
| 6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\349D186F1CB5682FA0194D4F3754EF36_6AC155AB4458D0D856D89A8608E588F4 | binary | |
MD5:83911A4C7617EF9C360AB6C9AE35D328 | SHA256:68880452416FDC38969340765AD0B6E9C1B4ACF76A8D5984B75B4D6C76FAAE21 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
43
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | GET | 200 | 163.171.131.197:80 | http://p0.qhimg.com/t11098f6bcdc80028f141f341ce.png | unknown | — | — | whitelisted |
6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | GET | 200 | 151.101.66.133:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | — | — | whitelisted |
6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2428 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2428 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | GET | 200 | 151.101.66.133:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDH4e5kyeFQuEifts%2Fw%3D%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6700 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | 163.171.130.132:443 | browser.360.cn | QUANTILNETWORKS | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | 163.171.131.197:80 | p0.qhimg.com | QUANTILNETWORKS | FR | whitelisted |
6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | 180.163.246.72:443 | dd.browser.360.cn | China Telecom Group | CN | whitelisted |
6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | 163.181.131.210:443 | pcclient.download.youku.com | — | US | whitelisted |
6704 | sembd_online_1.0.14.0__sem90003_sembd102389__n62791173a2__.exe | 151.101.66.133:80 | ocsp.globalsign.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
browser.360.cn |
| whitelisted |
p0.qhimg.com |
| whitelisted |
dd.browser.360.cn |
| whitelisted |
pcclient.download.youku.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
Process | Message |
|---|---|
youkuclient_setup_9.2.59.1002.exe | [NSIS-UI-Plugin] NSIS Plugin Dir: C:\Users\admin\AppData\Local\Temp\nsqCF57.tmp
|
youkuclient_setup_9.2.59.1002.exe | [NSIS-UI-Plugin] AdjustOldInstallProcess_PreInit
|
youkuclient_setup_9.2.59.1002.exe | [NSIS-UI-Plugin] ????????:
|
youkuclient_setup_9.2.59.1002.exe | [NSIS-UI-Plugin]
|
youkuclient_setup_9.2.59.1002.exe | [NSIS-UI-Plugin] oldInsDir?C:\Program Files (x86)\YOUKU
|
youkuclient_setup_9.2.59.1002.exe | [NSIS-UI-Plugin] ????oldInsDir?C:\Program Files (x86)\YOUKU
|
youkuclient_setup_9.2.59.1002.exe | [NSIS-UI-Plugin] ????????Dir?692
|
youkuclient_setup_9.2.59.1002.exe | [NSIS-UI-Plugin] ??TargetURL ?:692
|
youkuclient_setup_9.2.59.1002.exe | [NSIS-UI-Plugin] ???????C:\Program Files (x86)\YOUKU
|
youkuclient_setup_9.2.59.1002.exe | "utdid = {dd3fd45b-a344-48d8-9e3a-e2322f8175e1}"
|