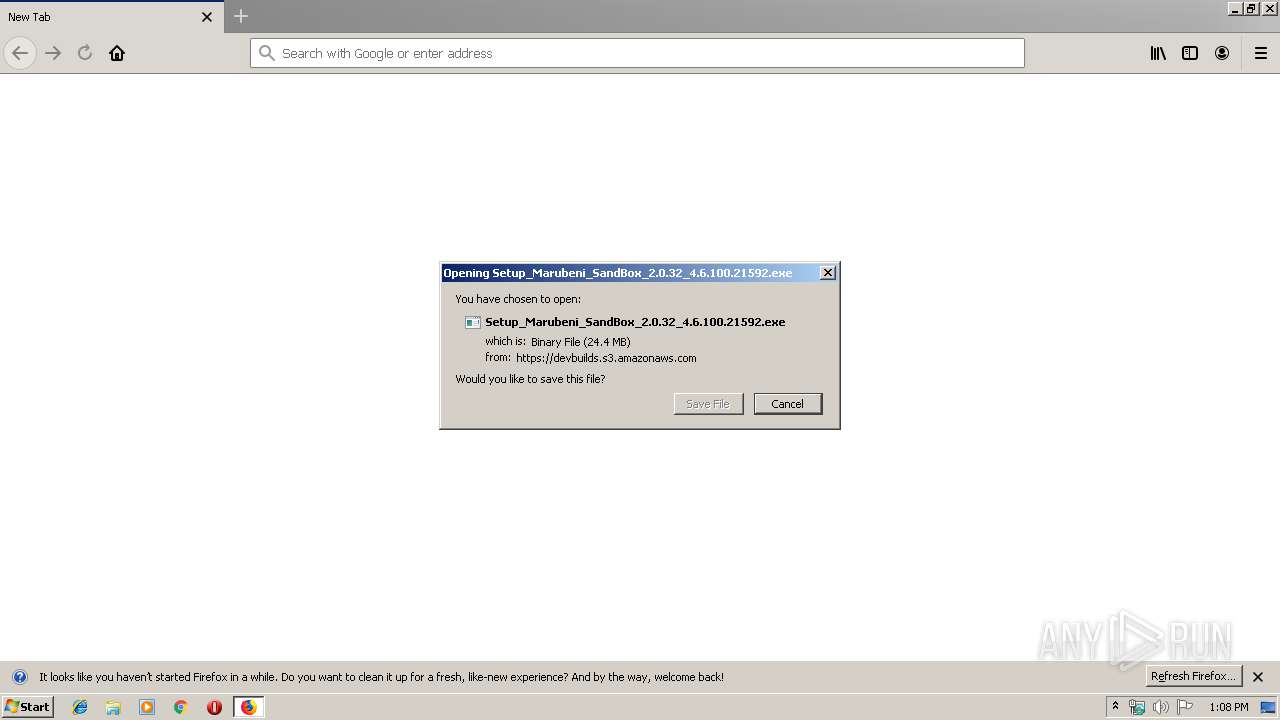
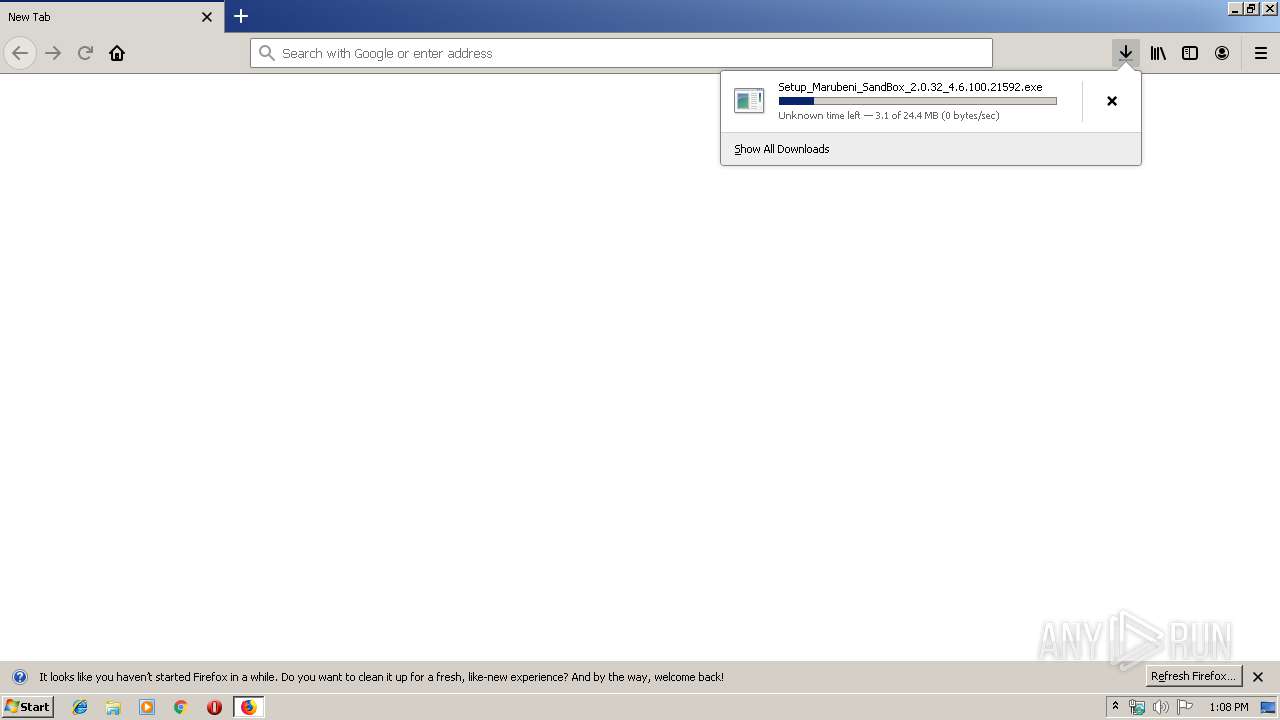
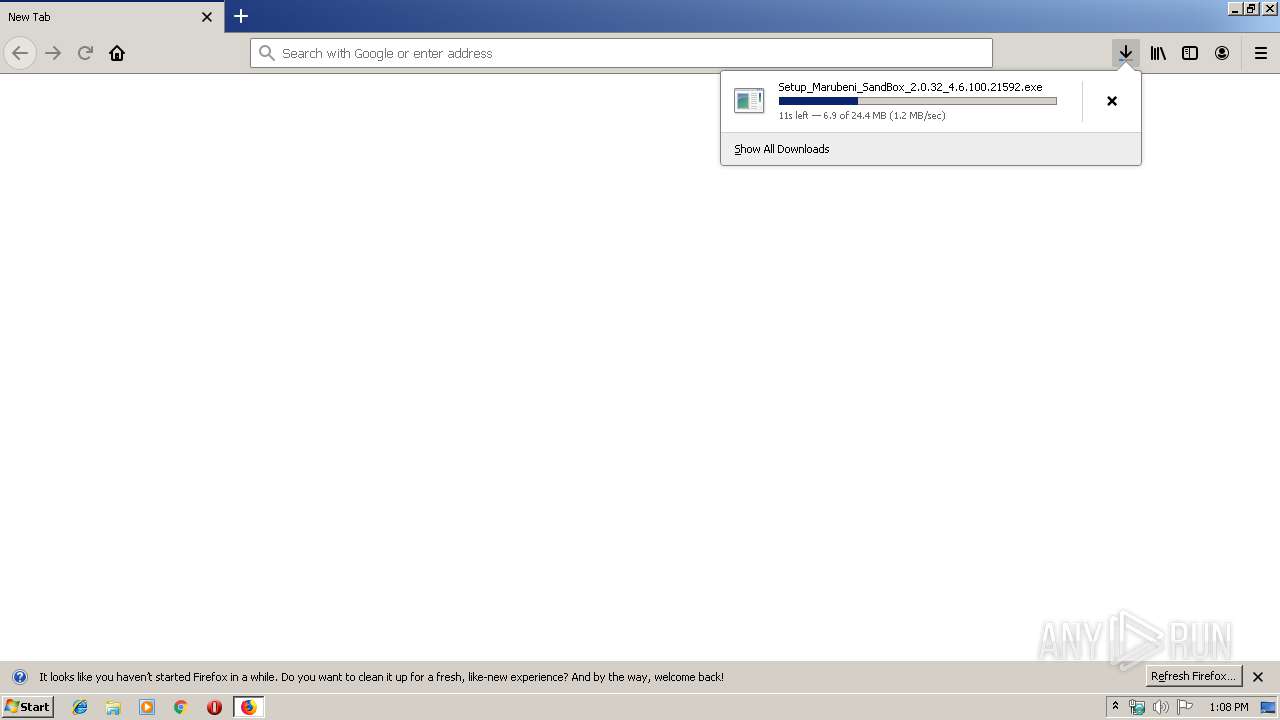
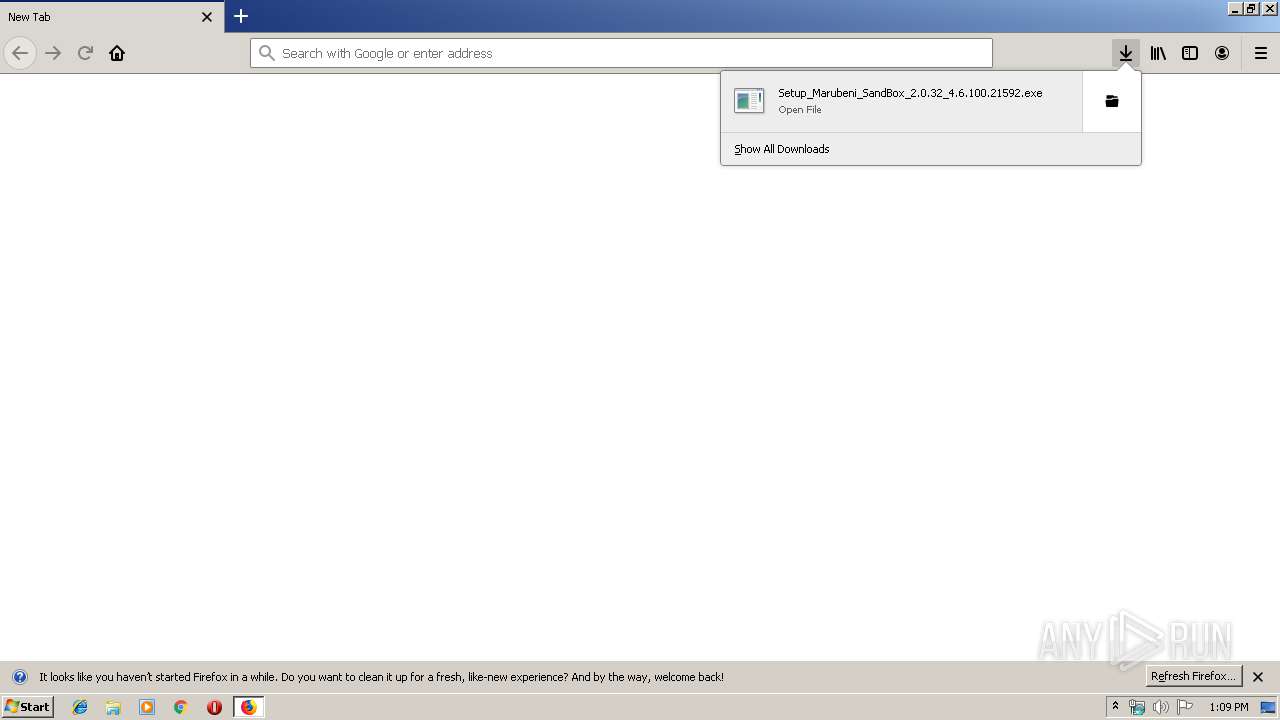
| URL: | https://devbuilds.s3.amazonaws.com/4.6/Marubeni_SandBox/Build/4.6.100/Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.exe |
| Full analysis: | https://app.any.run/tasks/3572493f-8682-4238-8c5b-6c82c47cd4f7 |
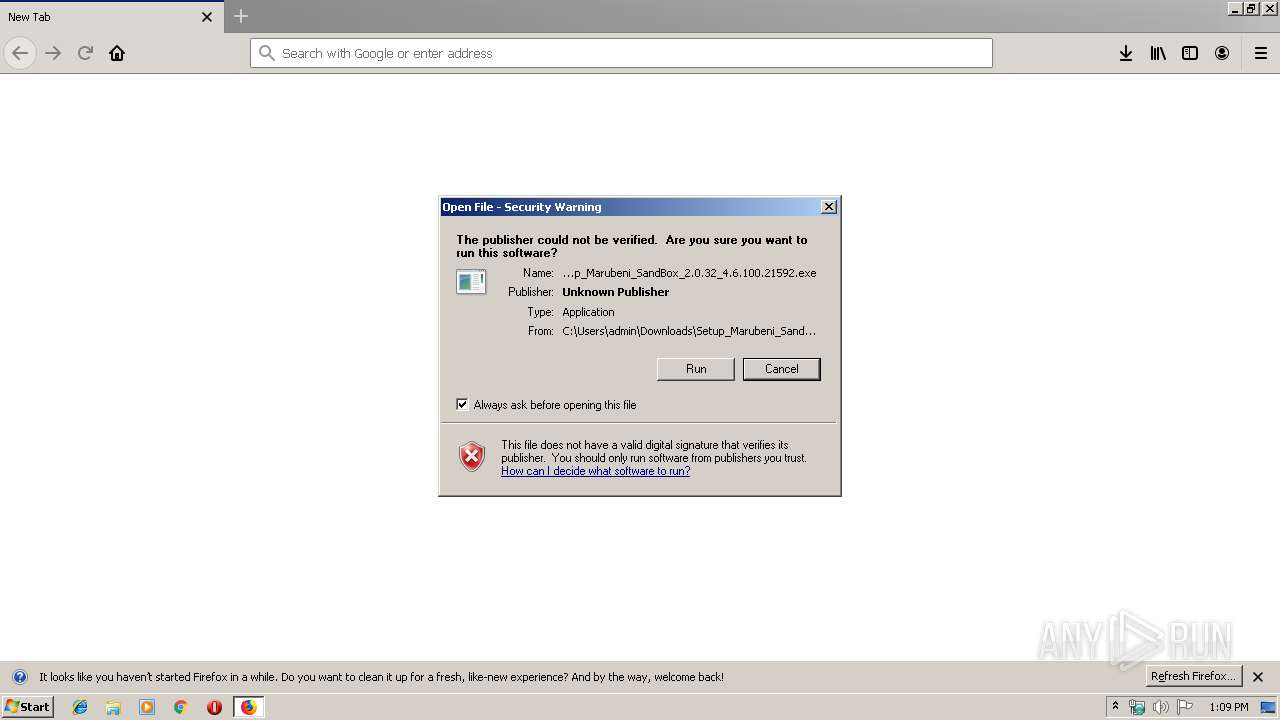
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 13:08:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C181825F84308AABE55F2FE35955CB92 |
| SHA1: | 85D2809AA327C55238DAB10C7543CA2C84A1DB70 |
| SHA256: | F33E1B2E2FB52F7A3365A9B0F15D4AA7A2269A3A79ED9F089BA471CE79FD5EB1 |
| SSDEEP: | 3:N8YkLWMSo7WthKovO7hGBMI010QV7O7hG8dWX6Rng2X0Cn:2YaSo6WYBO626WC |
MALICIOUS
Application was dropped or rewritten from another process
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.exe (PID: 3424)
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.exe (PID: 3088)
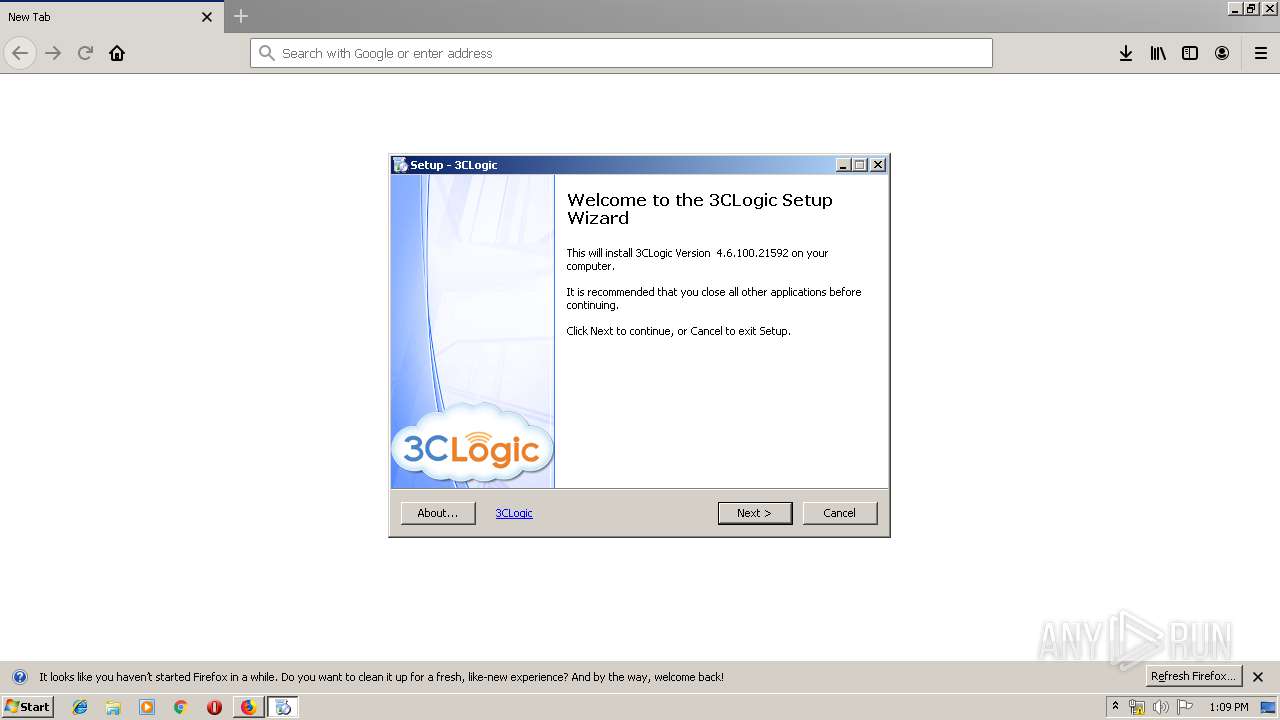
- Setup.exe (PID: 1764)
- 3CLogicService.exe (PID: 3772)
- 3CLogicService.exe (PID: 2436)
- 3CLogicStarter_2.0.32.21592.exe (PID: 3724)
- 3CLogicStarter_2.0.32.21592.exe (PID: 1516)
- 3CLogicDiagnostics.exe (PID: 1044)
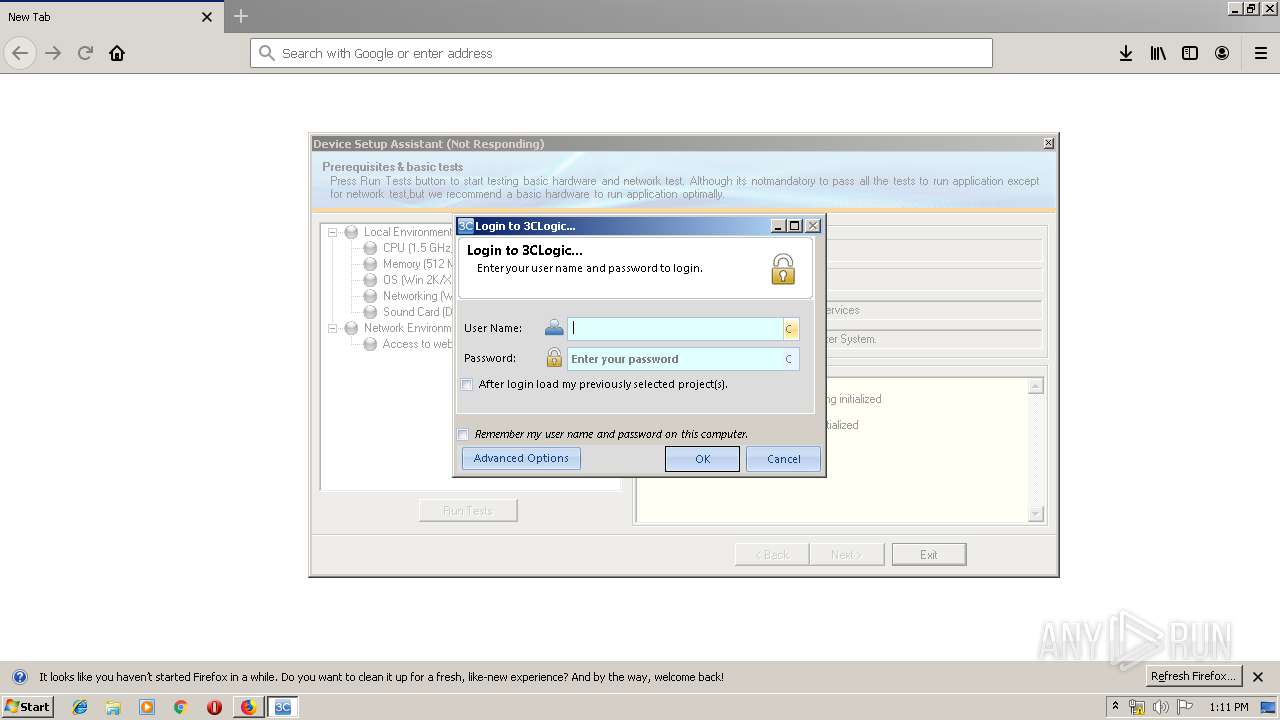
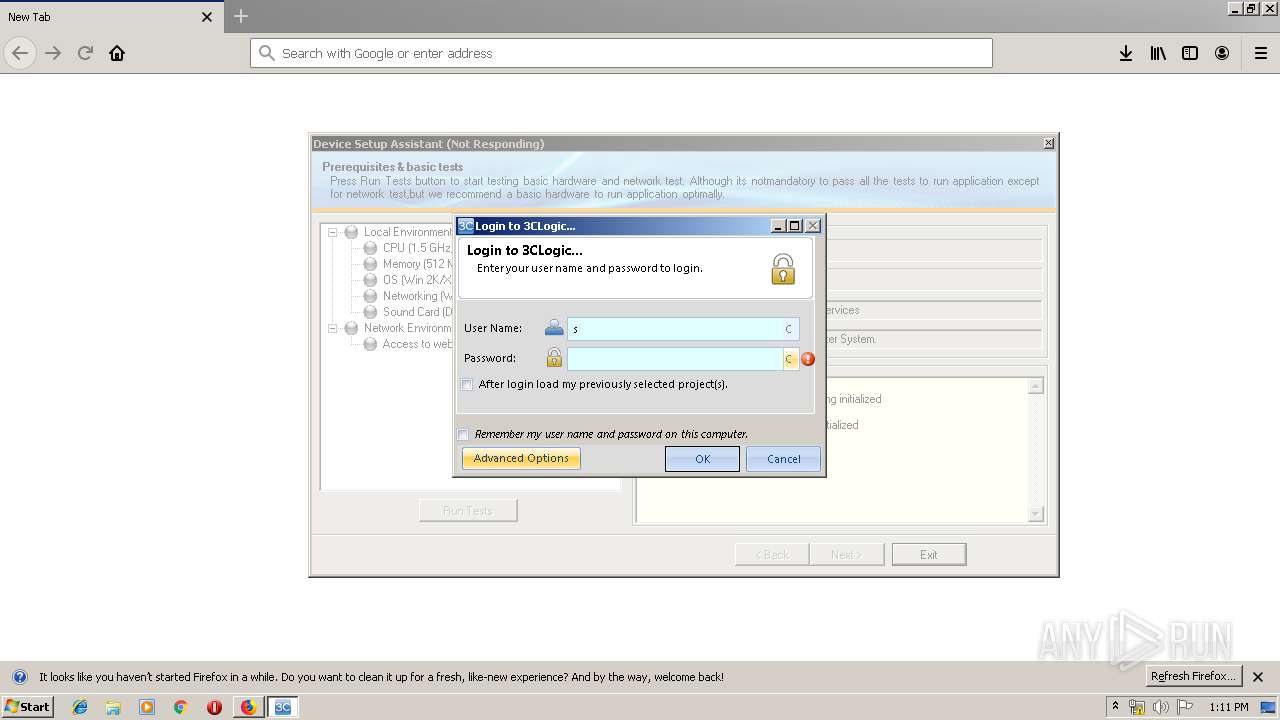
- 3CLogicLogin.exe (PID: 3672)
- 3CLogicStarter_2.0.32.21592.exe (PID: 2988)
- 3CLogicService.exe (PID: 1952)
- 3CLogicStarter_2.0.32.21592.exe (PID: 3796)
Starts NET.EXE for service management
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
Loads dropped or rewritten executable
- Setup.exe (PID: 1764)
- 3CLogicService.exe (PID: 3772)
- 3CLogicService.exe (PID: 2436)
- 3CLogicDiagnostics.exe (PID: 1044)
- 3CLogicStarter_2.0.32.21592.exe (PID: 3724)
- 3CLogicStarter_2.0.32.21592.exe (PID: 1516)
- 3CLogicService.exe (PID: 1952)
- 3CLogicStarter_2.0.32.21592.exe (PID: 2988)
- 3CLogicStarter_2.0.32.21592.exe (PID: 3796)
- 3CLogicLogin.exe (PID: 3672)
SUSPICIOUS
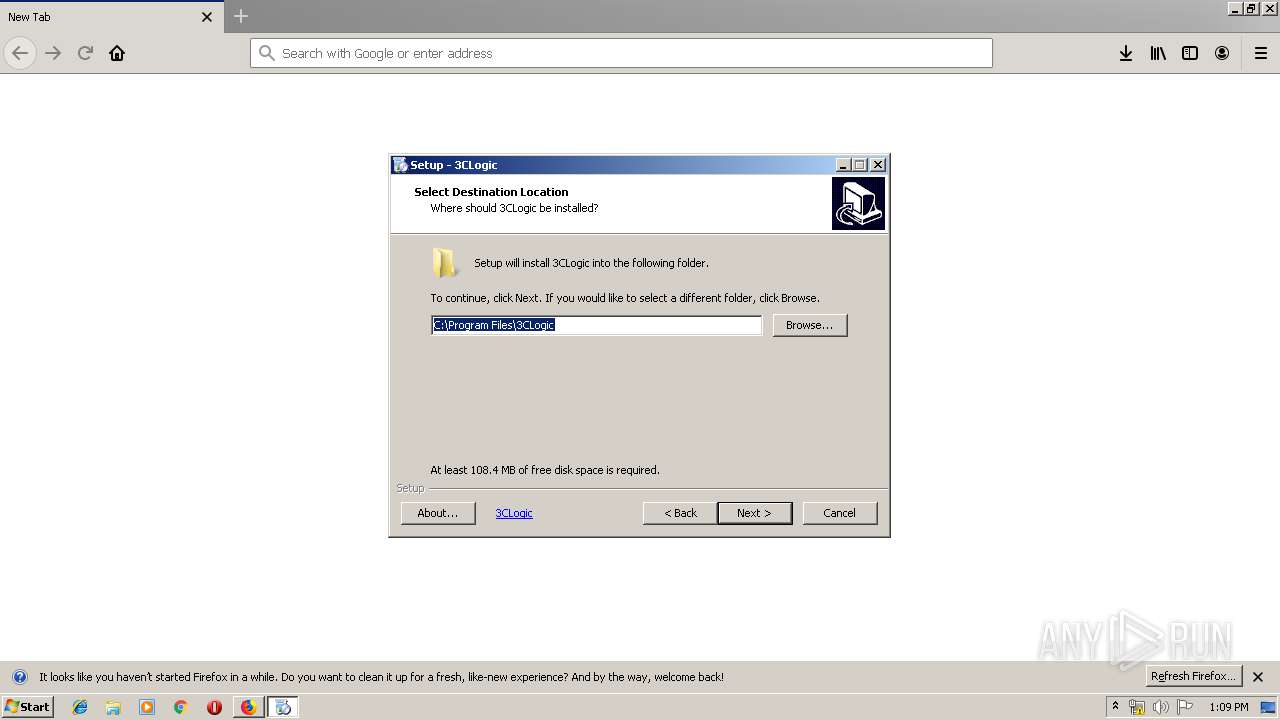
Creates files in the program directory
- firefox.exe (PID: 4004)
- 3CLogicService.exe (PID: 3772)
- 3CLogicService.exe (PID: 2436)
- 3CLogicStarter_2.0.32.21592.exe (PID: 3724)
- 3CLogicStarter_2.0.32.21592.exe (PID: 1516)
- 3CLogicDiagnostics.exe (PID: 1044)
- 3CLogicStarter_2.0.32.21592.exe (PID: 2988)
- 3CLogicStarter_2.0.32.21592.exe (PID: 3796)
Executable content was dropped or overwritten
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.exe (PID: 3424)
- firefox.exe (PID: 4004)
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.exe (PID: 3088)
- vcredist_x86.exe (PID: 2960)
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
- 3CLogicStarter_2.0.32.21592.exe (PID: 2988)
Reads Windows owner or organization settings
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
Reads the Windows organization settings
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
Removes files from Windows directory
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
Executed as Windows Service
- 3CLogicService.exe (PID: 2436)
Modifies the open verb of a shell class
- 3CLogicService.exe (PID: 3772)
Uses NETSH.EXE for network configuration
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
Creates files in the Windows directory
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
- 3CLogicStarter_2.0.32.21592.exe (PID: 3724)
- 3CLogicStarter_2.0.32.21592.exe (PID: 1516)
Reads Environment values
- 3CLogicDiagnostics.exe (PID: 1044)
- 3CLogicService.exe (PID: 2436)
INFO
Application launched itself
- firefox.exe (PID: 4004)
- firefox.exe (PID: 2368)
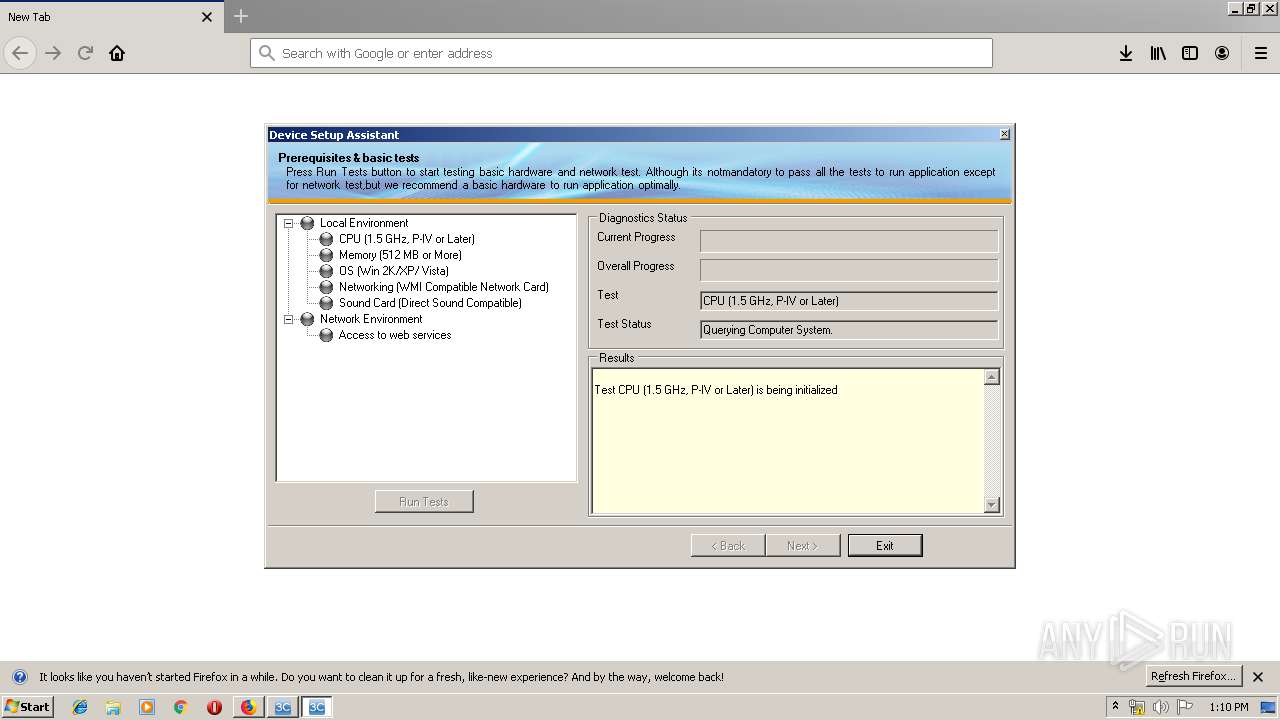
Reads CPU info
- firefox.exe (PID: 4004)
Application was dropped or rewritten from another process
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 3792)
- vcredist_x86.exe (PID: 2960)
Loads dropped or rewritten executable
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
Dropped object may contain Bitcoin addresses
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
Creates files in the user directory
- firefox.exe (PID: 4004)
Creates a software uninstall entry
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
Creates files in the program directory
- Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp (PID: 640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
110
Monitored processes
47
Malicious processes
15
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
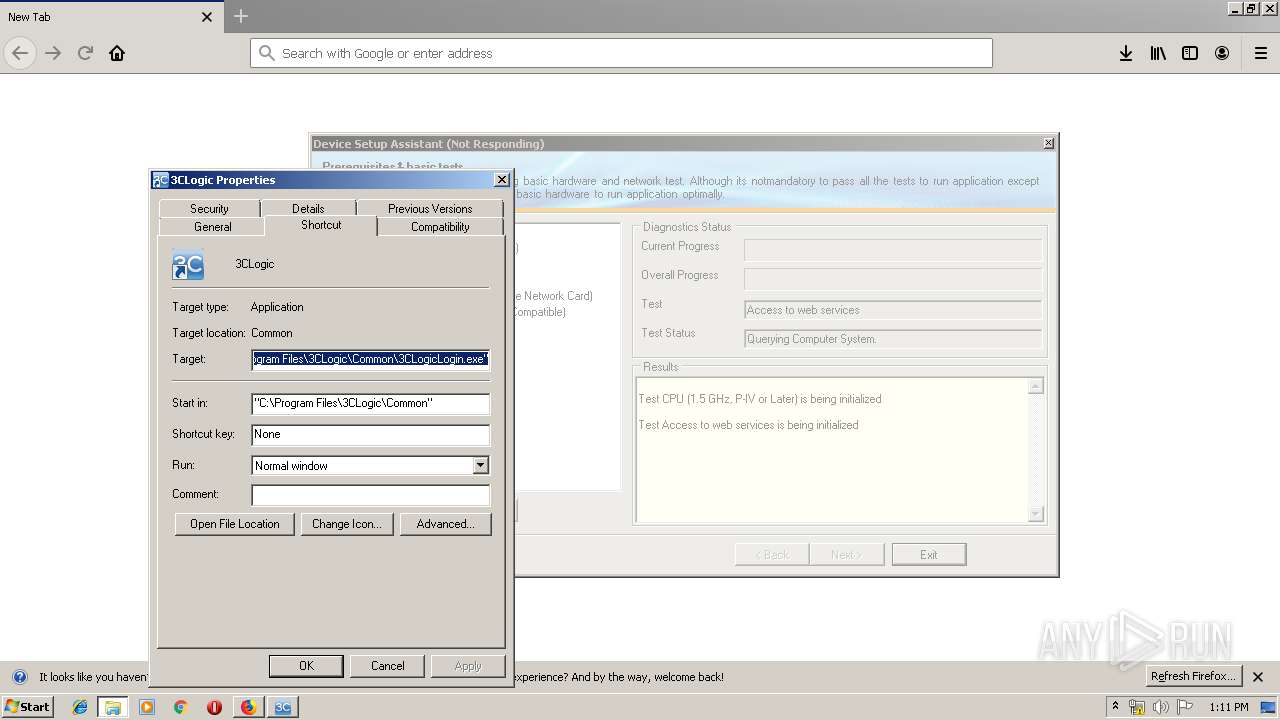
| 592 | "netsh.exe" advfirewall firewall add rule name="Allow 3CLogic Login Exe Inbound" dir=in action=allow program="C:\Program Files\3CLogic\Common\3CLogicLogin.exe" enable=yes edge=yes | C:\Windows\system32\netsh.exe | — | Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 640 | "C:\Users\admin\AppData\Local\Temp\is-A2RA8.tmp\Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp" /SL5="$4015A,25150779,124416,C:\Users\admin\Downloads\Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.exe" /SPAWNWND=$40152 /NOTIFYWND=$3018E | C:\Users\admin\AppData\Local\Temp\is-A2RA8.tmp\Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 904 | "netsh.exe" advfirewall firewall add rule name="Allow 3CLogic Phone Inbound" dir=in action=allow program="C:\Program Files\3CLogic\Versions\4.6.100\3CLogicPhone.exe" enable=yes edge=yes | C:\Windows\system32\netsh.exe | — | Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
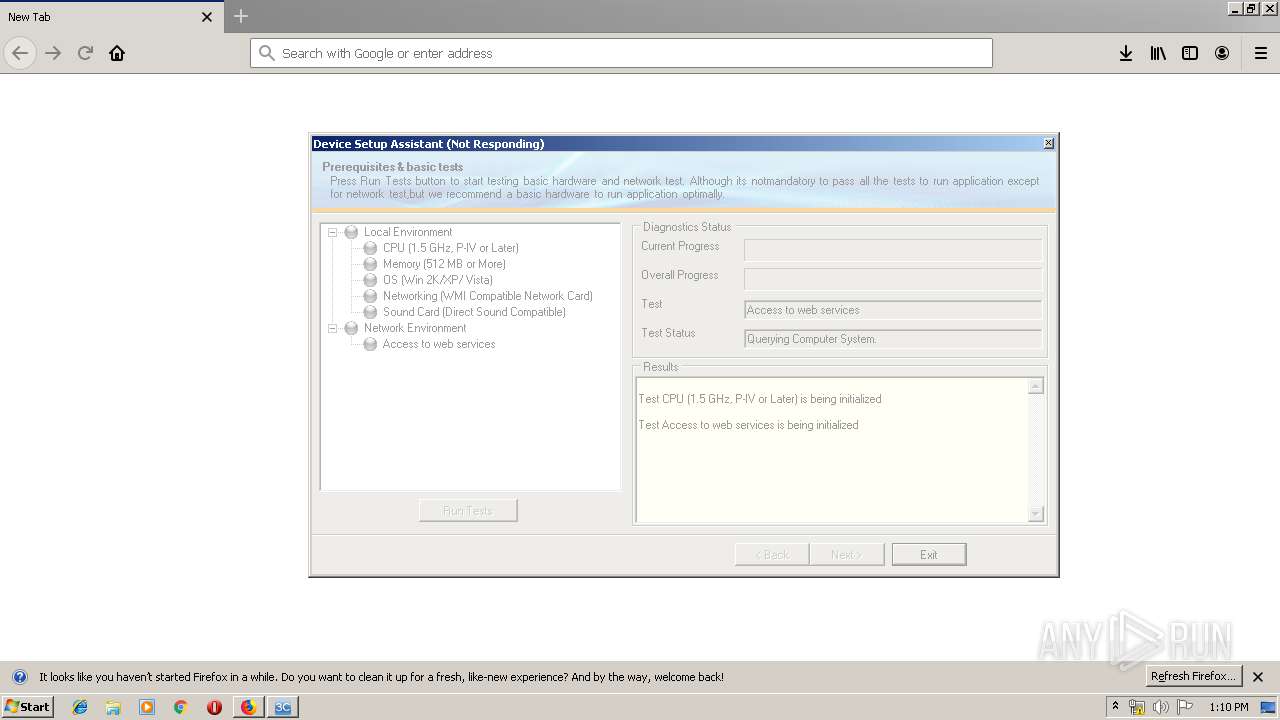
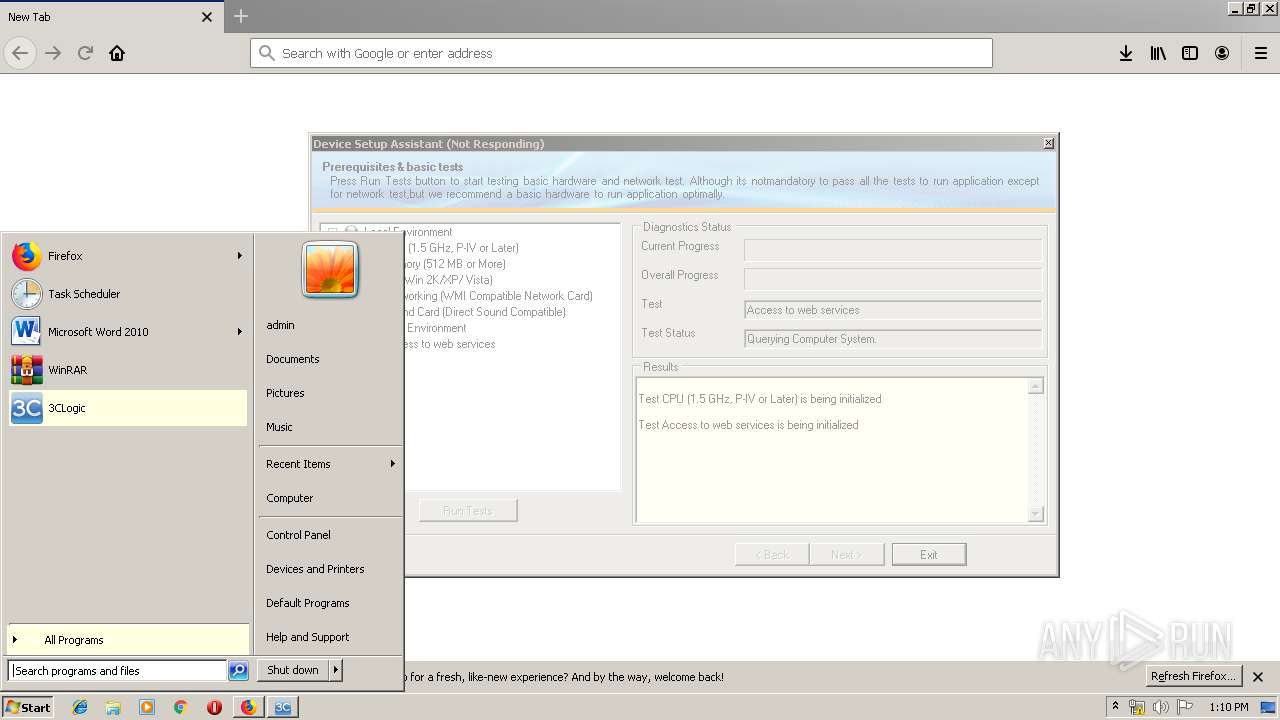
| 1044 | "C:\Program Files\3CLogic\Versions\4.6.100\3CLogicDiagnostics.exe" | C:\Program Files\3CLogic\Versions\4.6.100\3CLogicDiagnostics.exe | Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | ||||||||||||
User: admin Company: 3CLogic Integrity Level: HIGH Description: 3CLogicDiagnostics Exit code: 0 Version: 4.6.100.21592 Modules
| |||||||||||||||
| 1484 | "net" start 3clogicService | C:\Windows\system32\net.exe | — | Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | "C:\Program Files\3CLogic\Common\3CLogicStarter_2.0.32.21592.exe" "C:\Program Files\3CLogic\Versions\4.6.100\3CLogicClientSession.exe" "/v" "4.6.100.21592" | C:\Program Files\3CLogic\Common\3CLogicStarter_2.0.32.21592.exe | 3CLogicService.exe | ||||||||||||
User: SYSTEM Company: 3CLogic Integrity Level: SYSTEM Description: 3CLogicStarter Exit code: 0 Version: 2.0.32.21592 Modules
| |||||||||||||||
| 1764 | c:\ce0e86e3ca625909508d3e21a1e123\Setup.exe /q /norestart | c:\ce0e86e3ca625909508d3e21a1e123\Setup.exe | vcredist_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 5100 Version: 10.0.30319.1 built by: RTMRel Modules
| |||||||||||||||
| 1848 | "netsh.exe" advfirewall firewall add rule name="Allow 3CLogic Login Exe Outbound" dir=out action=allow program="C:\Program Files\3CLogic\Common\3CLogicLogin.exe" enable=yes | C:\Windows\system32\netsh.exe | — | Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1932 | "netsh.exe" advfirewall firewall add rule name="Allow 3CLogic Application Outbound" dir=out action=allow program="C:\Program Files\3CLogic\Versions\4.6.100\3CLogicDiagnostics.exe" enable=yes | C:\Windows\system32\netsh.exe | — | Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1952 | "C:\Program Files\3CLogic\Common\3CLogicService.exe" -loadversion:"C:\Program Files\3CLogic\Versions\4.6.100" | C:\Program Files\3CLogic\Common\3CLogicService.exe | Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | ||||||||||||
User: admin Company: 3CLogic Integrity Level: HIGH Description: 3CLogicService Exit code: 4294967292 Version: 2.0.32.21592 Modules
| |||||||||||||||
Total events
3 278
Read events
2 041
Write events
1 236
Delete events
1
Modification events
| (PID) Process: | (4004) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 9AA7061803000000 | |||
| (PID) Process: | (2368) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: FBA3031803000000 | |||
| (PID) Process: | (4004) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (4004) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4004) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4004) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4004) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (640) Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\3Clogic |
| Operation: | write | Name: | SetupStoppingService |
Value: true | |||
| (PID) Process: | (640) Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\3Clogic |
| Operation: | delete value | Name: | SetupStoppingService |
Value: true | |||
| (PID) Process: | (640) Setup_Marubeni_SandBox_2.0.32_4.6.100.21592.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\3CLogic\Shared\Infragistics2.Documents.v8.3.dll |
Value: 1 | |||
Executable files
222
Suspicious files
75
Text files
310
Unknown types
151
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4004 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 4004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 4004 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 4004 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 4004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 4004 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 4004 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
| 4004 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\allow-flashallow-digest256.pset | cdxl | |
MD5:076933FF9904D1110D896E2C525E39E5 | SHA256:4CBBD8CA5215B8D161AEC181A74B694F4E24B001D5B081DC0030ED797A8973E0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
34
DNS requests
79
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
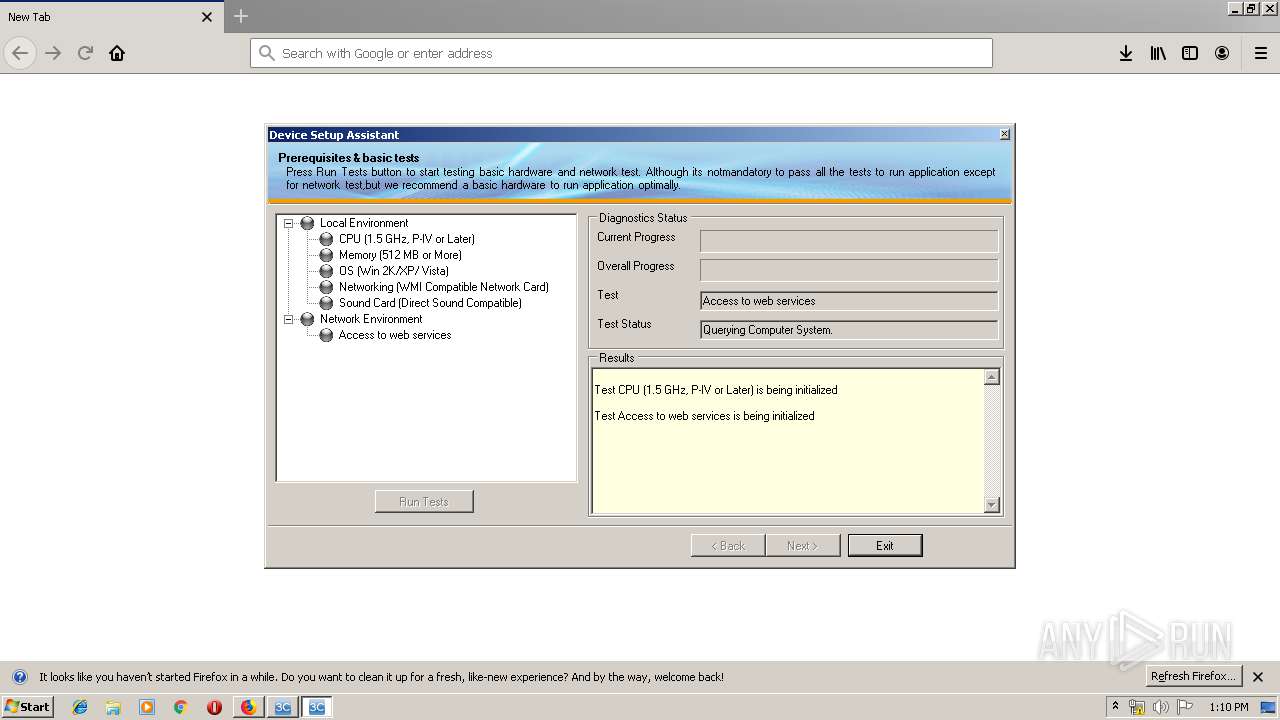
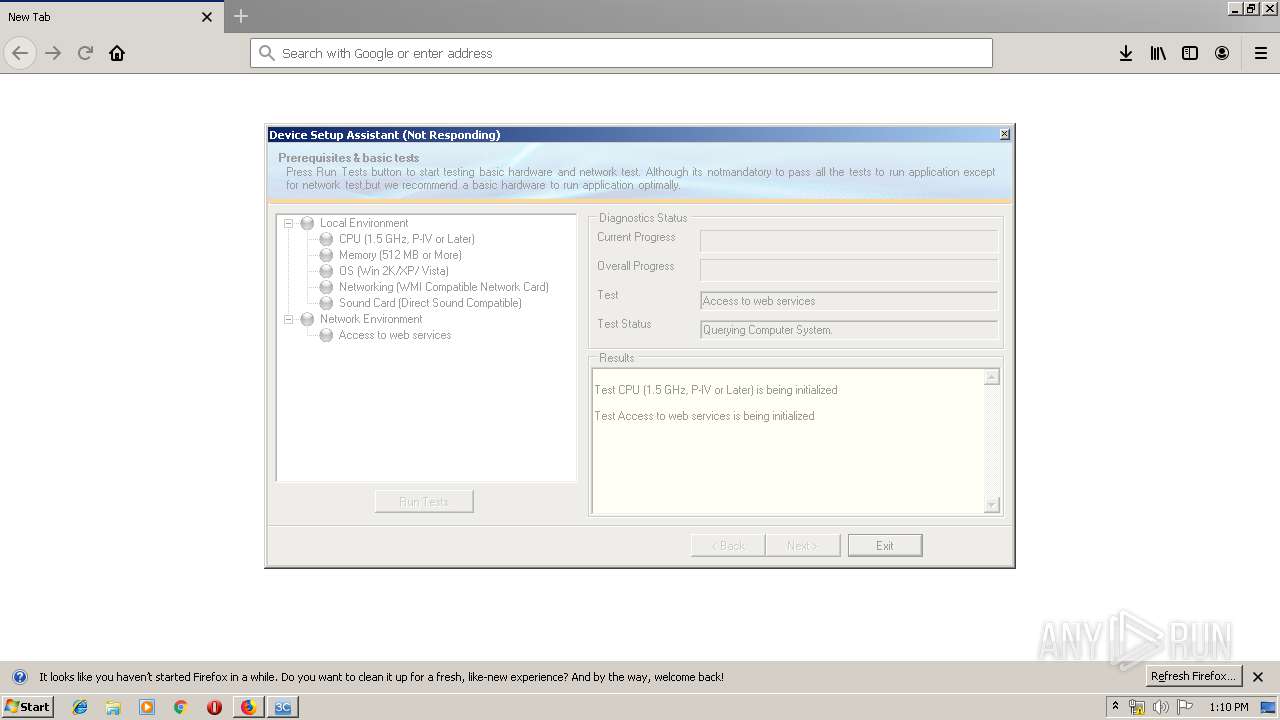
1044 | 3CLogicDiagnostics.exe | GET | — | 54.248.119.148:80 | http://msyssb.msys.3ccloud.com/ls/ws/auth?wsdl | JP | — | — | unknown |
1044 | 3CLogicDiagnostics.exe | POST | 200 | 50.112.119.37:80 | http://apis.3clogic.com/am/alerts/add? | US | text | 11 b | unknown |
2436 | 3CLogicService.exe | POST | — | 54.248.119.148:80 | http://msyssb.msys.3ccloud.com/ls/ws/auth | JP | — | — | unknown |
4004 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4004 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
4004 | firefox.exe | POST | 200 | 172.217.22.35:80 | http://ocsp.pki.goog/gts1o1 | US | der | 472 b | whitelisted |
4004 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4004 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4004 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4004 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
4004 | firefox.exe | 35.164.109.147:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
4004 | firefox.exe | 52.219.36.188:443 | devbuilds.s3.amazonaws.com | Amazon.com, Inc. | SG | unknown |
4004 | firefox.exe | 34.214.202.211:443 | push.services.mozilla.com | Amazon.com, Inc. | US | malicious |
4004 | firefox.exe | 13.35.253.31:443 | snippets.cdn.mozilla.net | — | US | malicious |
4004 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4004 | firefox.exe | 34.223.160.244:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
4004 | firefox.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4004 | firefox.exe | 13.32.158.105:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | malicious |
4004 | firefox.exe | 13.224.132.7:443 | content-signature-2.cdn.mozilla.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
devbuilds.s3.amazonaws.com |
| unknown |
s3-ap-southeast-1-w.amazonaws.com |
| shared |
snippets.cdn.mozilla.net |
| whitelisted |
d228z91au11ukj.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
Setup.exe | A StopBlock was hit or a System Requirement was not met. |
3CLogicService.exe | Extentions Installed Count:2
|
3CLogicService.exe | NEW STATE : CsmProcessFsmMap.WaitCsmProcessReady
|
3CLogicService.exe | NEW STATE : CsmProcessFsmMap.WaitCsmProcessReady
|
3CLogicStarter_2.0.32.21592.exe | Init
|
3CLogicStarter_2.0.32.21592.exe | CreateDomain: 3CLogicAppLauncher.exe - 1:09 PM WAStarter |
|
3CLogicStarter_2.0.32.21592.exe | ExecuteAssemblyBegin: C:\Program Files\3CLogic\Common\3CLogicAppLauncher.exe Args: /watmpexecute - 1:09 PM WAStarter |
|
3CLogicStarter_2.0.32.21592.exe | Init
|
3CLogicStarter_2.0.32.21592.exe | CreateDomain: 3CLogicClientSession.exe - 1:09 PM WAStarter |
|
3CLogicStarter_2.0.32.21592.exe | ExecuteAssemblyBegin: C:\Program Files\3CLogic\Versions\4.6.100\3CLogicClientSession.exe Args: /watmpexecute+/v+4.6.100.21592 - 1:09 PM WAStarter |
|