| File name: | SimulatorSetup.exe |
| Full analysis: | https://app.any.run/tasks/b0d5f6ca-66d8-4e4b-86e8-1b6a66fdf8c8 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2019, 17:59:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9941139DF3033DAED0702F681CE67D97 |
| SHA1: | 0F1D54DDFC0CBB07E3586B8078267872CFFD495F |
| SHA256: | F3010D71F4D852635BEF2F52FE65DDC7E800C382D659E6D414ADAE4AF8E8EB7E |
| SSDEEP: | 393216:amgEHuSm8mcYH4dzpOHTtsFAUdVWBuH5HgDGeuWP3I6vggm:aOmBcyUzgHTZmVgaeuyvggm |
MALICIOUS
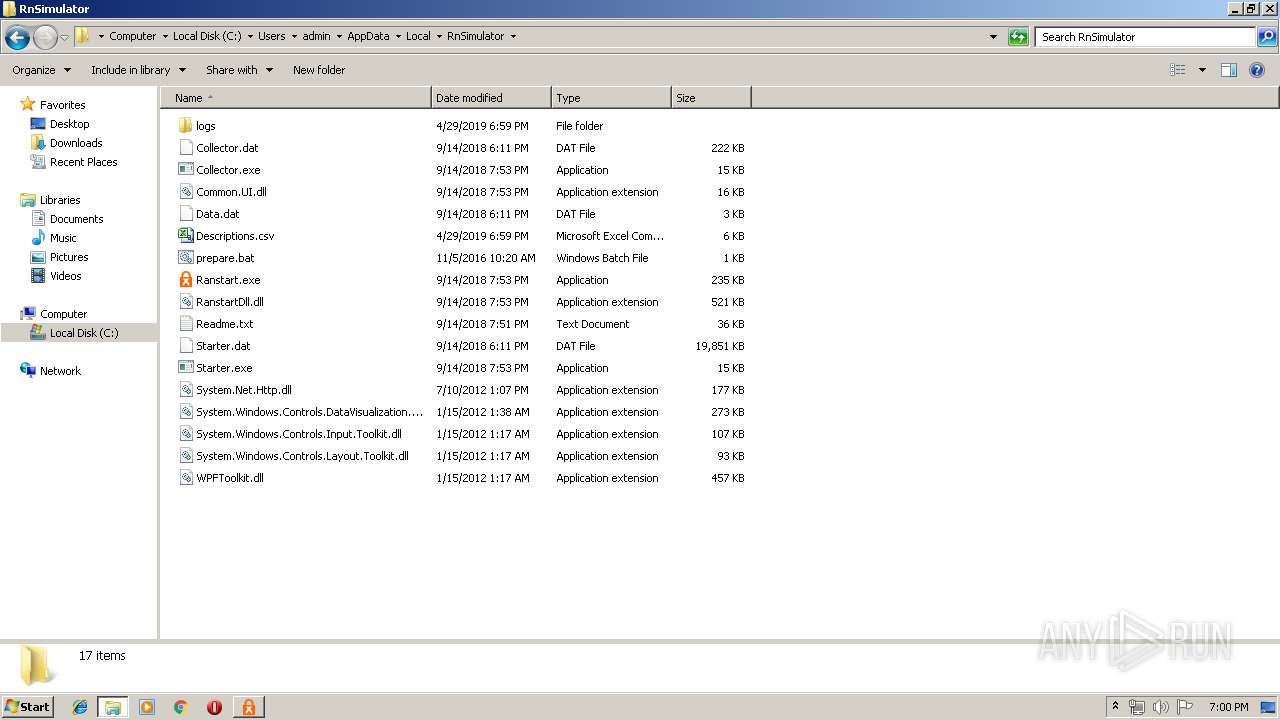
Application was dropped or rewritten from another process
- SimulatorSetup.exe (PID: 2204)
- Ranstart.exe (PID: 4028)
- Starter.exe (PID: 2536)
Loads dropped or rewritten executable
- SimulatorSetup.exe (PID: 2204)
- rundll32.exe (PID: 3540)
- rundll32.exe (PID: 2864)
- Ranstart.exe (PID: 4028)
- Starter.exe (PID: 2536)
Changes the autorun value in the registry
- SimulatorSetup.exe (PID: 2204)
SUSPICIOUS
Executable content was dropped or overwritten
- SimulatorSetup.exe (PID: 3984)
- SimulatorSetup.exe (PID: 2204)
- rundll32.exe (PID: 3540)
- msiexec.exe (PID: 2384)
- Starter.exe (PID: 2536)
- Ranstart.exe (PID: 4028)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 1108)
Searches for installed software
- rundll32.exe (PID: 3540)
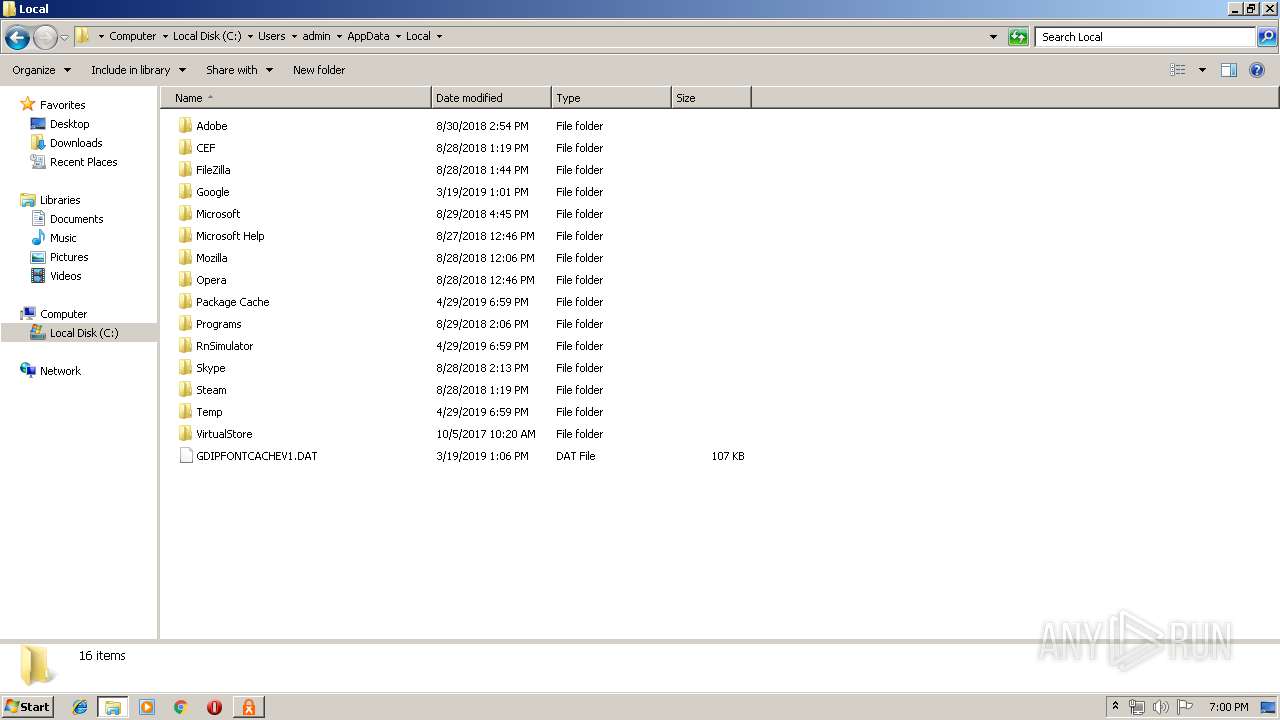
Creates files in the user directory
- msiexec.exe (PID: 2384)
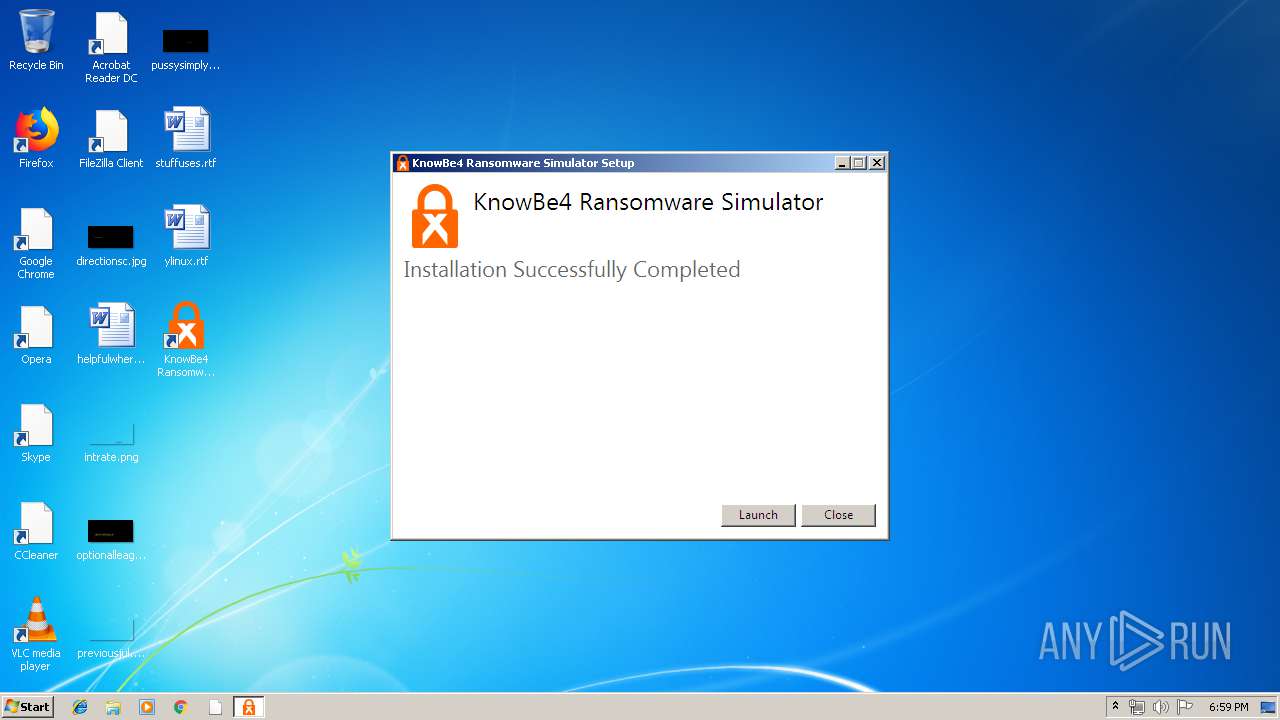
Creates a software uninstall entry
- SimulatorSetup.exe (PID: 2204)
INFO
Application launched itself
- msiexec.exe (PID: 2384)
Creates a software uninstall entry
- msiexec.exe (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:05:01 16:33:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.1 |
| CodeSize: | 302080 |
| InitializedDataSize: | 193536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e1fd |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.54 |
| ProductVersionNumber: | 2.0.0.54 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
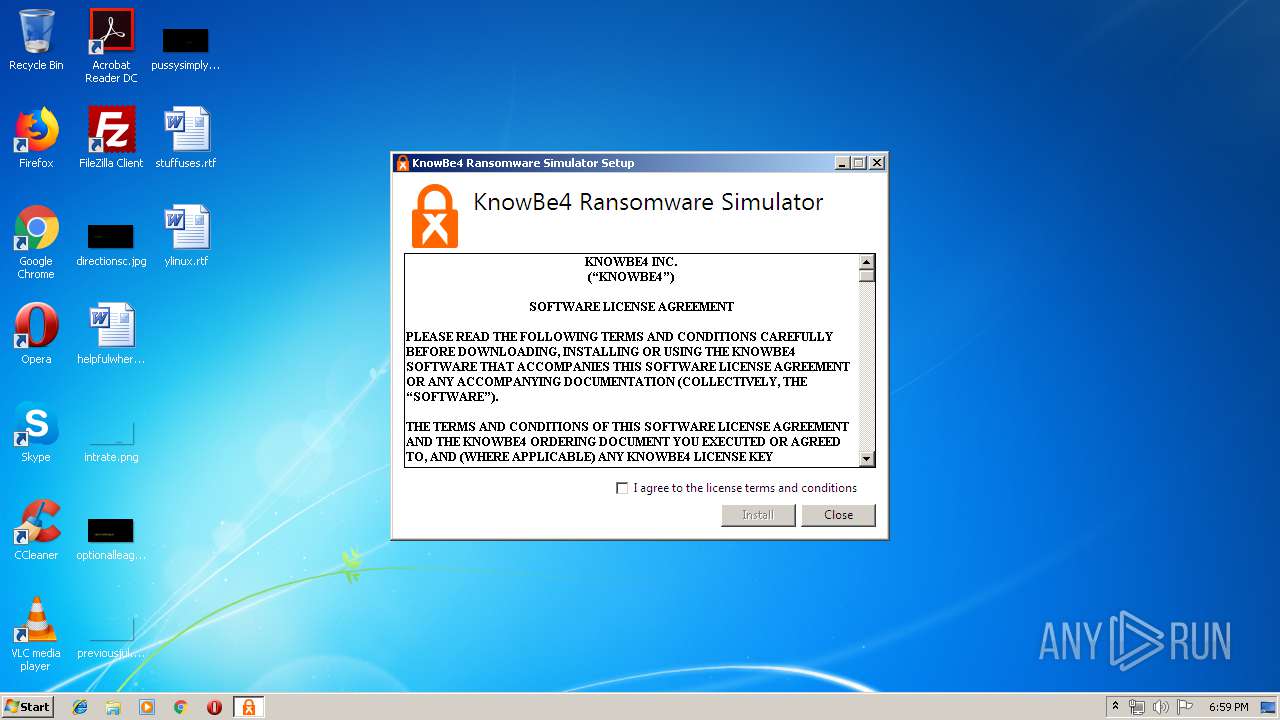
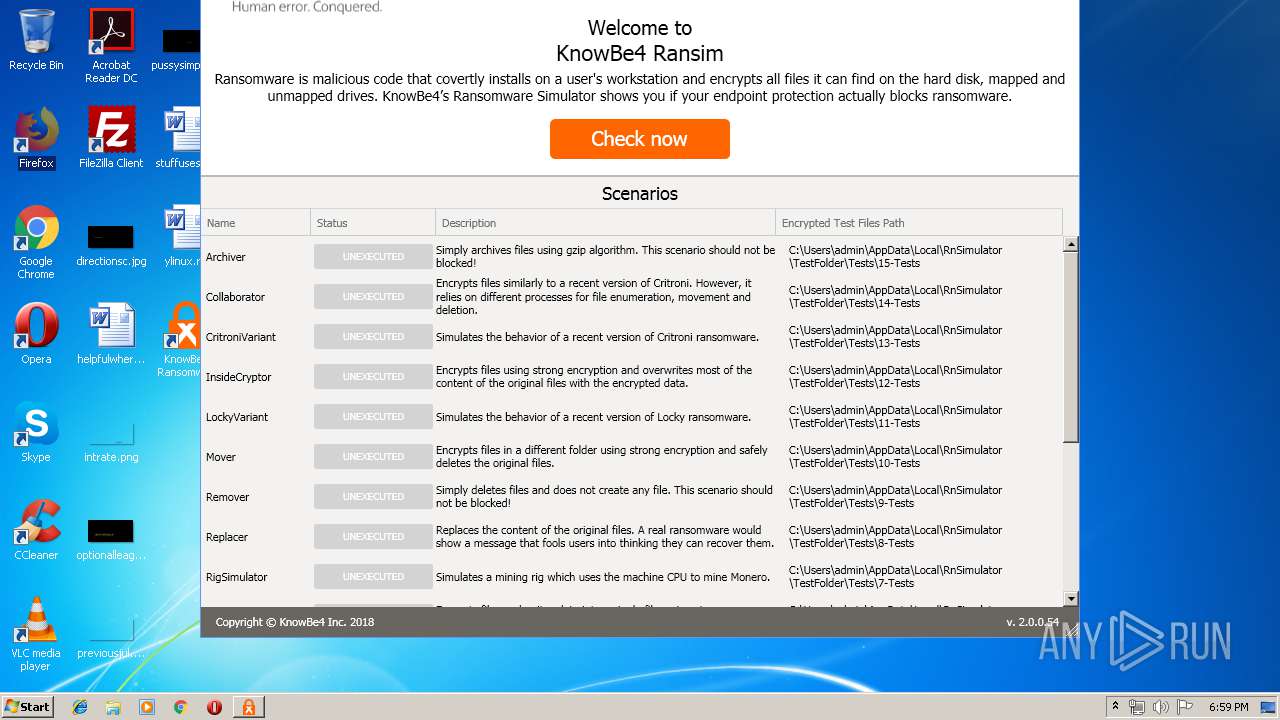
| CompanyName: | KnowBe4 Inc |
| FileDescription: | KnowBe4 Ransomware Simulator |
| FileVersion: | 2.0.0.54 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) KnowBe4 Inc. All rights reserved. |
| OriginalFileName: | SimulatorSetup.exe |
| ProductName: | KnowBe4 Ransomware Simulator |
| ProductVersion: | 2.0.0.54 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-May-2017 14:33:52 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | KnowBe4 Inc |
| FileDescription: | KnowBe4 Ransomware Simulator |
| FileVersion: | 2.0.0.54 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) KnowBe4 Inc. All rights reserved. |
| OriginalFilename: | SimulatorSetup.exe |
| ProductName: | KnowBe4 Ransomware Simulator |
| ProductVersion: | 2.0.0.54 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 01-May-2017 14:33:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00049A67 | 0x00049C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56282 |
.rdata | 0x0004B000 | 0x0001EC60 | 0x0001EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.10841 |
.data | 0x0006A000 | 0x00001730 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.15458 |
.wixburn8 | 0x0006C000 | 0x00000038 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.731255 |
.tls | 0x0006D000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0006E000 | 0x0000B940 | 0x0000BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.48349 |
.reloc | 0x0007A000 | 0x00003DEC | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.79026 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30829 | 1234 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 1.8863 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.25307 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.171 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.45938 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
Cabinet.dll (delay-loaded) |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
44
Monitored processes
9
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1108 | C:\Windows\system32\MsiExec.exe -Embedding B69971293120B7A55ED049811B86F5E9 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | "C:\Users\admin\AppData\Local\Temp\{02A9588B-48E0-4F28-999C-E8B82BDBBAC5}\.cr\SimulatorSetup.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\SimulatorSetup.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{02A9588B-48E0-4F28-999C-E8B82BDBBAC5}\.cr\SimulatorSetup.exe | SimulatorSetup.exe | ||||||||||||
User: admin Company: KnowBe4 Inc Integrity Level: MEDIUM Description: KnowBe4 Ransomware Simulator Exit code: 0 Version: 2.0.0.54 Modules
| |||||||||||||||
| 2384 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\AppData\Local\RnSimulator\Starter.exe" -d | C:\Users\admin\AppData\Local\RnSimulator\Starter.exe | Ranstart.exe | ||||||||||||
User: admin Company: KnowBe4, Inc. Integrity Level: MEDIUM Description: Exit code: 0 Version: 2.0.0.54 Modules
| |||||||||||||||
| 2864 | rundll32.exe "C:\Windows\Installer\MSI6035.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1138765 8 CustomActions!CustomActions.CustomActions.BeforeInstallationInitialize | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3540 | rundll32.exe "C:\Windows\Installer\MSI5E50.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1138375 1 CustomActions!CustomActions.CustomActions.CleanupPreviousInstallation | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
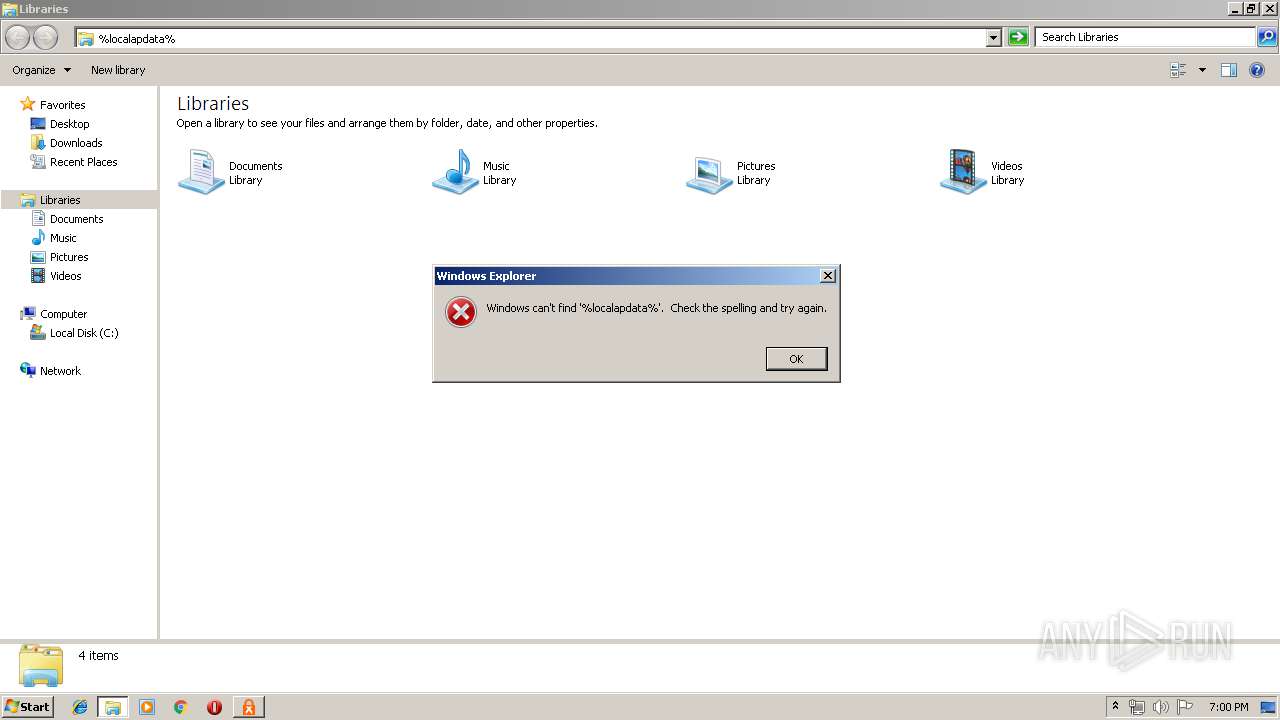
| 3844 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\AppData\Local\Temp\SimulatorSetup.exe" | C:\Users\admin\AppData\Local\Temp\SimulatorSetup.exe | explorer.exe | ||||||||||||
User: admin Company: KnowBe4 Inc Integrity Level: MEDIUM Description: KnowBe4 Ransomware Simulator Exit code: 0 Version: 2.0.0.54 Modules
| |||||||||||||||
| 4028 | "C:\Users\admin\AppData\Local\RnSimulator\Ranstart.exe" | C:\Users\admin\AppData\Local\RnSimulator\Ranstart.exe | SimulatorSetup.exe | ||||||||||||
User: admin Company: KnowBe4, Inc. Integrity Level: MEDIUM Description: Exit code: 0 Version: 2.0.0.54 Modules
| |||||||||||||||
Total events
1 450
Read events
1 275
Write events
161
Delete events
14
Modification events
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\Users\admin\AppData\Local\Package Cache\{44c676e2-79d6-4631-9659-4ce3298f6546}\SimulatorSetup.exe | |||
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {682A3E74-FFF7-499F-A2CB-E31CF3ADE4B1} | |||
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | BundleVersion |
Value: 2.0.0.54 | |||
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | VersionMajor |
Value: 2 | |||
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | VersionMinor |
Value: 0 | |||
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | BundleProviderKey |
Value: {44c676e2-79d6-4631-9659-4ce3298f6546} | |||
| (PID) Process: | (2204) SimulatorSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\{44c676e2-79d6-4631-9659-4ce3298f6546} |
| Operation: | write | Name: | BundleTag |
Value: | |||
Executable files
21
Suspicious files
8
Text files
15
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | SimulatorSetup.exe | C:\Users\admin\AppData\Local\Temp\{B2F9F3F4-7084-4043-A2C4-C878CBCE1D1E}\AppMSI | — | |
MD5:— | SHA256:— | |||
| 2204 | SimulatorSetup.exe | C:\Users\admin\AppData\Local\Package Cache\.unverified\AppMSI | — | |
MD5:— | SHA256:— | |||
| 2204 | SimulatorSetup.exe | C:\Users\admin\AppData\Local\Package Cache\{0A1BA62F-CE14-4FB3-9D98-0B43FFEA6DF3}v2.0.0.54\Installer.msi | — | |
MD5:— | SHA256:— | |||
| 2384 | msiexec.exe | C:\Windows\Installer\115b4c.msi | — | |
MD5:— | SHA256:— | |||
| 2384 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab5C17.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar5C18.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab5C29.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar5C2A.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Cab5D05.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Tar5D06.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2384 | msiexec.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
2384 | msiexec.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2384 | msiexec.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |