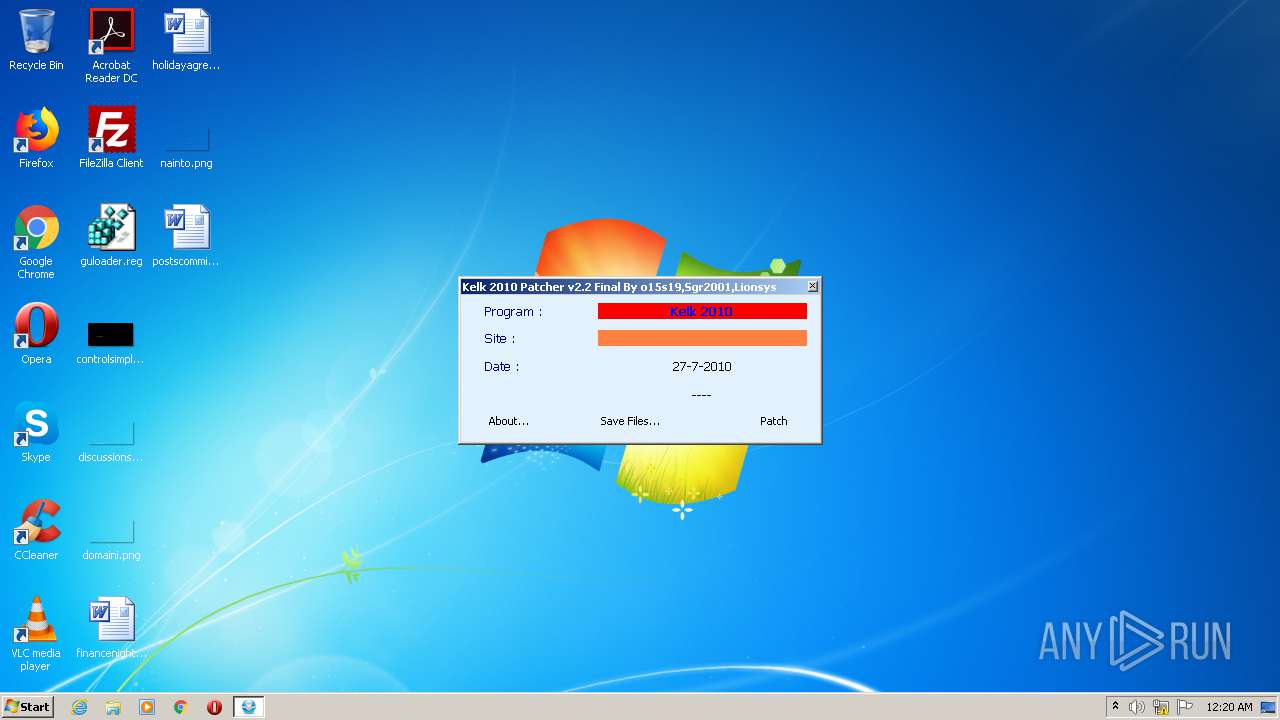
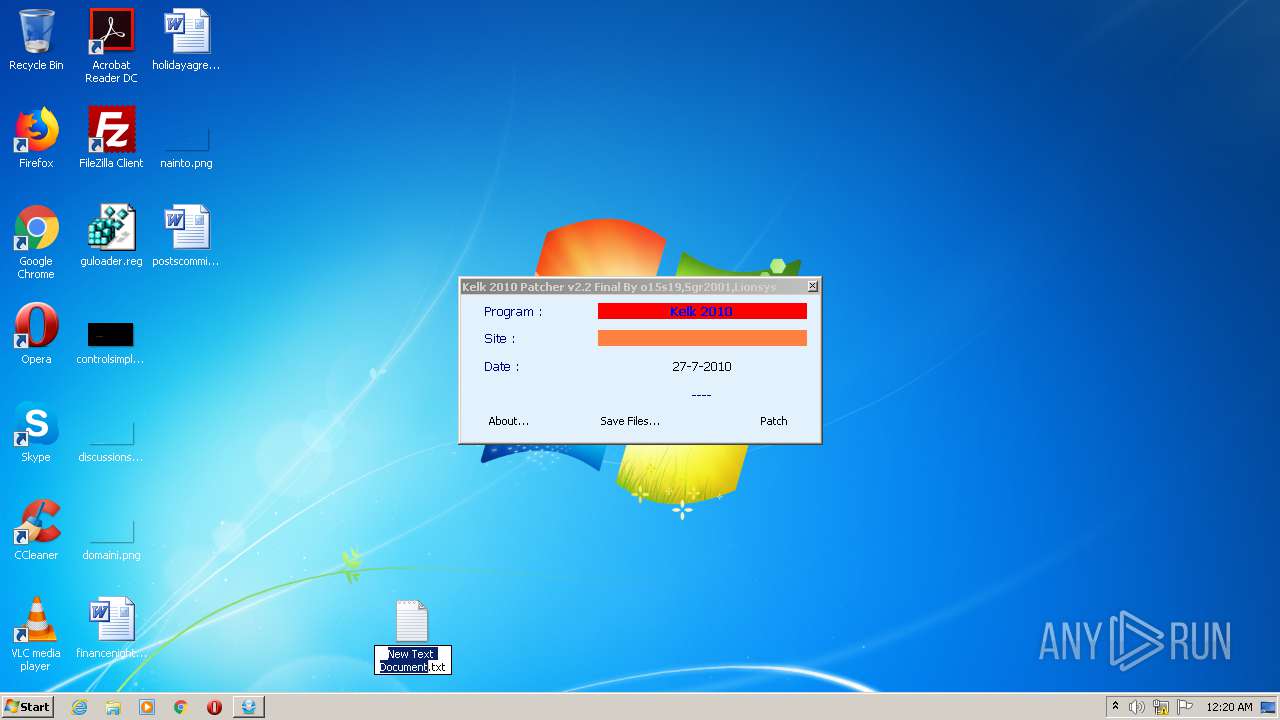
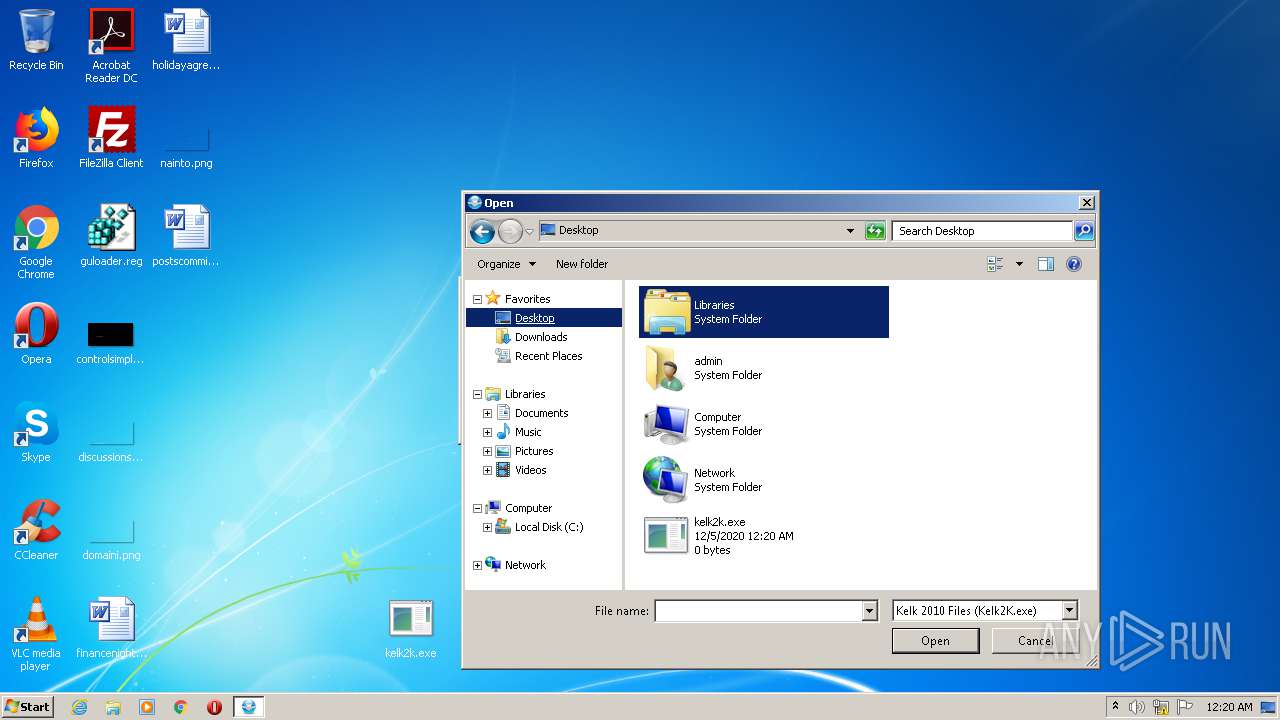
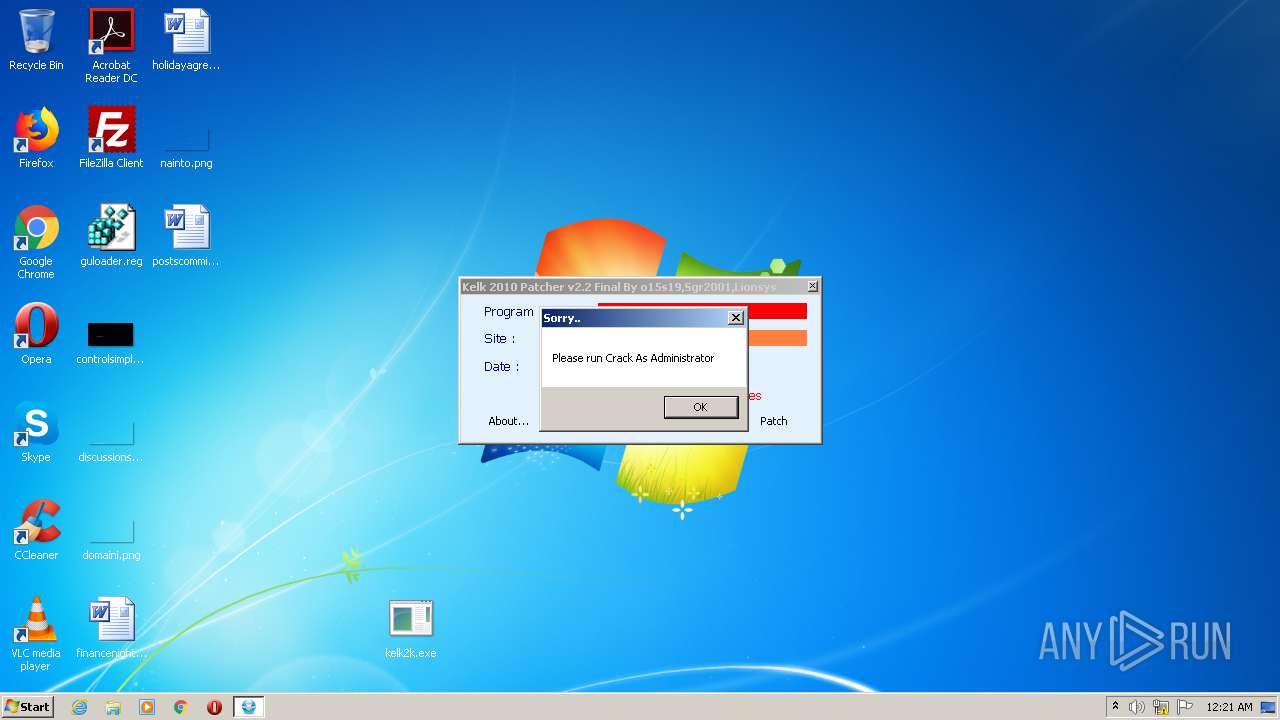
| File name: | Kelk 2010 Patcher v2.2.exe |
| Full analysis: | https://app.any.run/tasks/8b354d37-e0ff-48d0-ab42-5e31ed16cd9b |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2020, 00:20:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | AE6E474A43F6752BB9589D8B397333C9 |
| SHA1: | D653051F4E6D099E86A5845FAF0908CBBF33FD34 |
| SHA256: | F2F5C836E16CEB403F627D841152E12B8D1B2B21CB95F83471D4C7BED2D99077 |
| SSDEEP: | 49152:dGrh7jiERXmp1Ml5qOLUfwxxGUTi4zJnmHM8F/VGOt:UrhXiWyqlY/AtTV9neM8DGq |
MALICIOUS
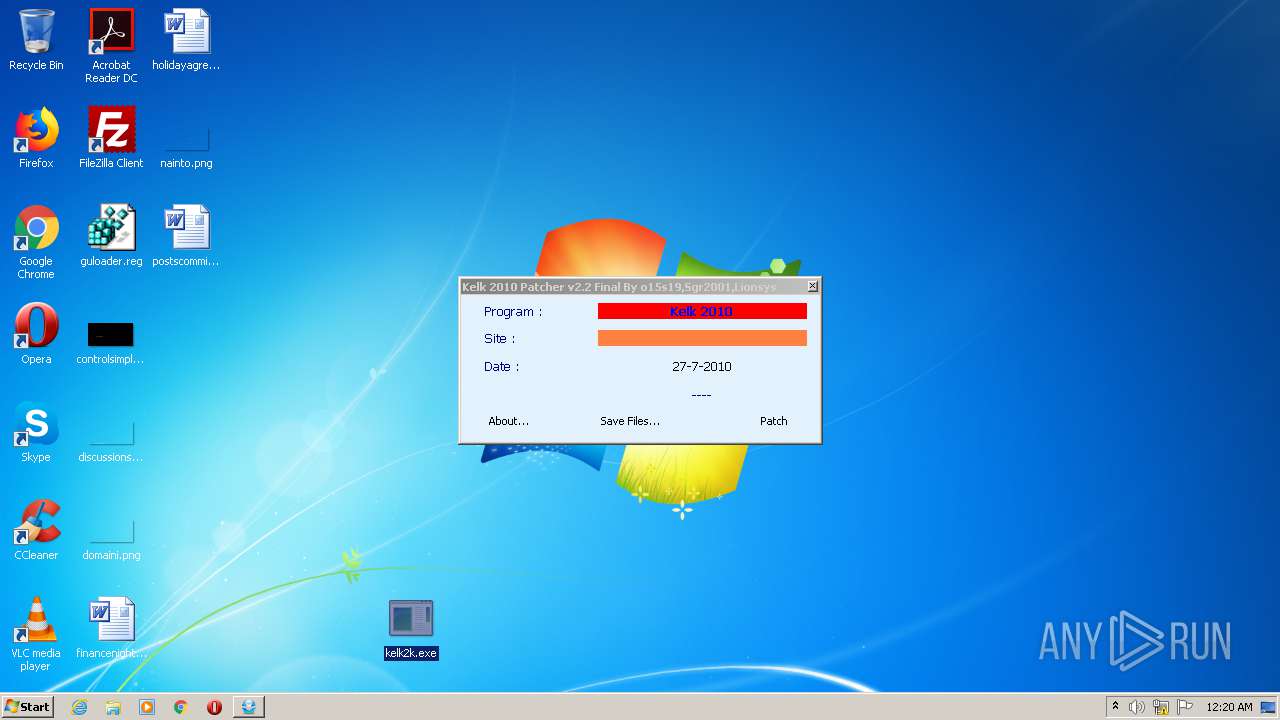
Loads dropped or rewritten executable
- Kelk2K.exe (PID: 2416)
- SearchProtocolHost.exe (PID: 3688)
Application was dropped or rewritten from another process
- Kelk2K.exe (PID: 2416)
SUSPICIOUS
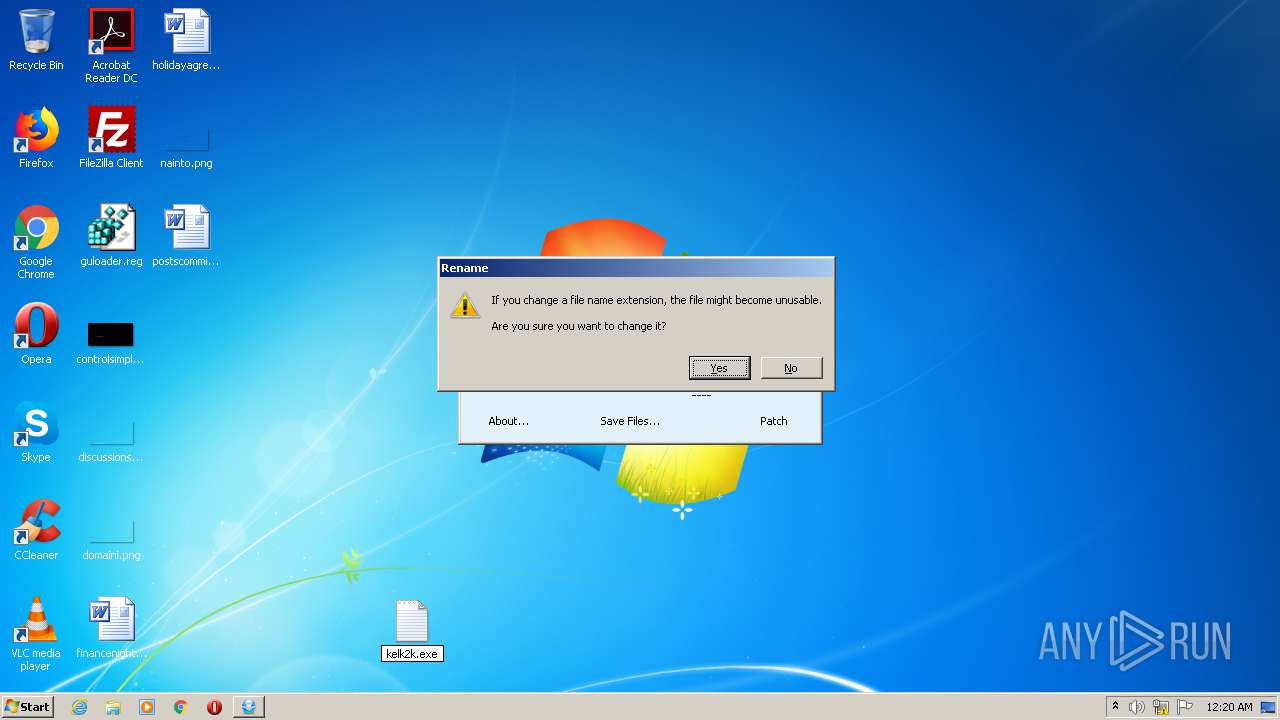
Executable content was dropped or overwritten
- Kelk 2010 Patcher v2.2.exe (PID: 2468)
Drops a file that was compiled in debug mode
- Kelk 2010 Patcher v2.2.exe (PID: 2468)
Drops a file with too old compile date
- Kelk 2010 Patcher v2.2.exe (PID: 2468)
INFO
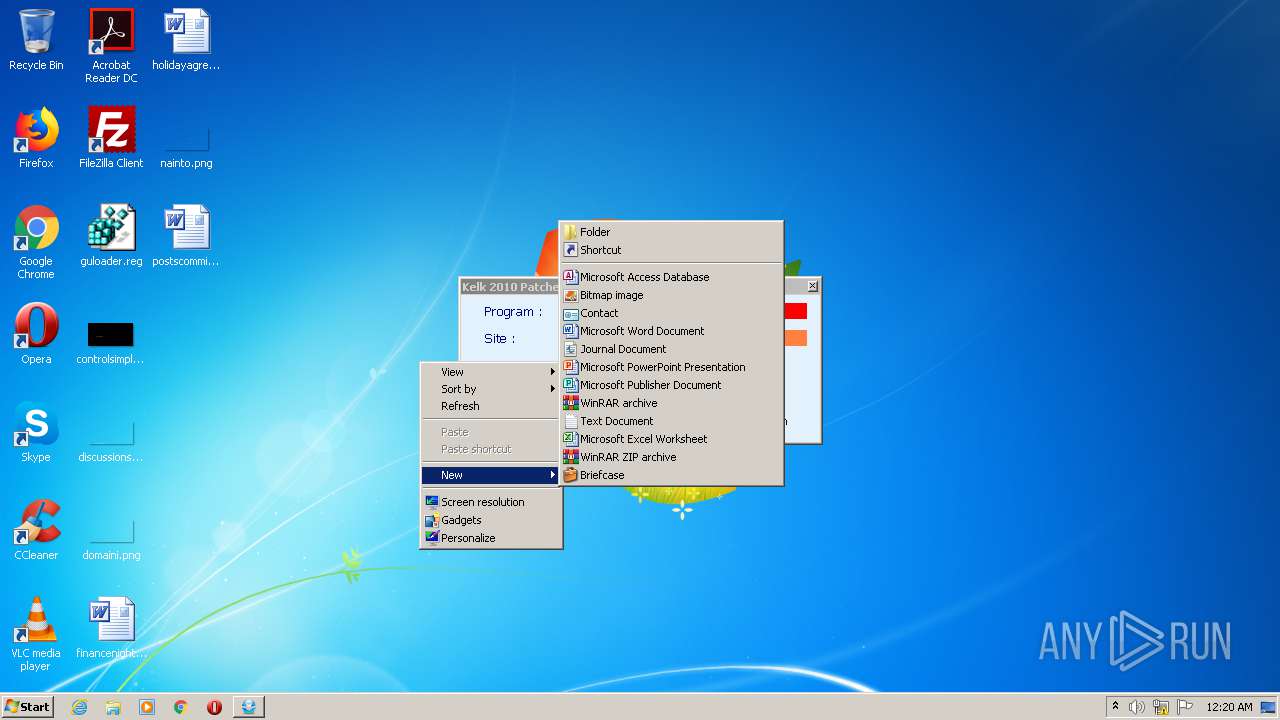
Manual execution by user
- Kelk2K.exe (PID: 2416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (42.1) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (41.3) |
| .exe | | | Win32 Executable (generic) (7) |
| .exe | | | Win16/32 Executable Delphi generic (3.2) |
| .exe | | | Generic Win/DOS Executable (3.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:07:26 20:57:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1974272 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | 7778304 |
| EntryPoint: | 0x94d0e0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | By o15s19,Sgr2001,Lionsys |
| FileDescription: | Kelk 2010 Patcher |
| FileVersion: | 2.2.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Jul-2010 18:57:14 |
| Detected languages: |
|
| CompanyName: | By o15s19,Sgr2001,Lionsys |
| FileDescription: | Kelk 2010 Patcher |
| FileVersion: | 2.2.0.0 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 26-Jul-2010 18:57:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0076B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0076C000 | 0x001E2000 | 0x001E1400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93602 |
.rsrc | 0x0094E000 | 0x0002A000 | 0x00029600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.26296 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92474 | 850 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.6263 | 1128 | UNKNOWN | English - United States | RT_ICON |
3 | 5.68263 | 2440 | UNKNOWN | English - United States | RT_ICON |
4 | 5.43174 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 5.42624 | 9640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.2077 | 16936 | UNKNOWN | English - United States | RT_ICON |
7 | 5.28401 | 21640 | UNKNOWN | English - United States | RT_ICON |
8 | 5.29178 | 38056 | UNKNOWN | English - United States | RT_ICON |
9 | 5.06299 | 67624 | UNKNOWN | English - United States | RT_ICON |
4081 | 7.09171 | 308 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
msimg32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2416 | "C:\Users\admin\Desktop\Kelk2K.exe" | C:\Users\admin\Desktop\Kelk2K.exe | — | explorer.exe | |||||||||||
User: admin Company: SinaSoft Integrity Level: MEDIUM Exit code: 0 Version: 7.00.0097 Modules
| |||||||||||||||
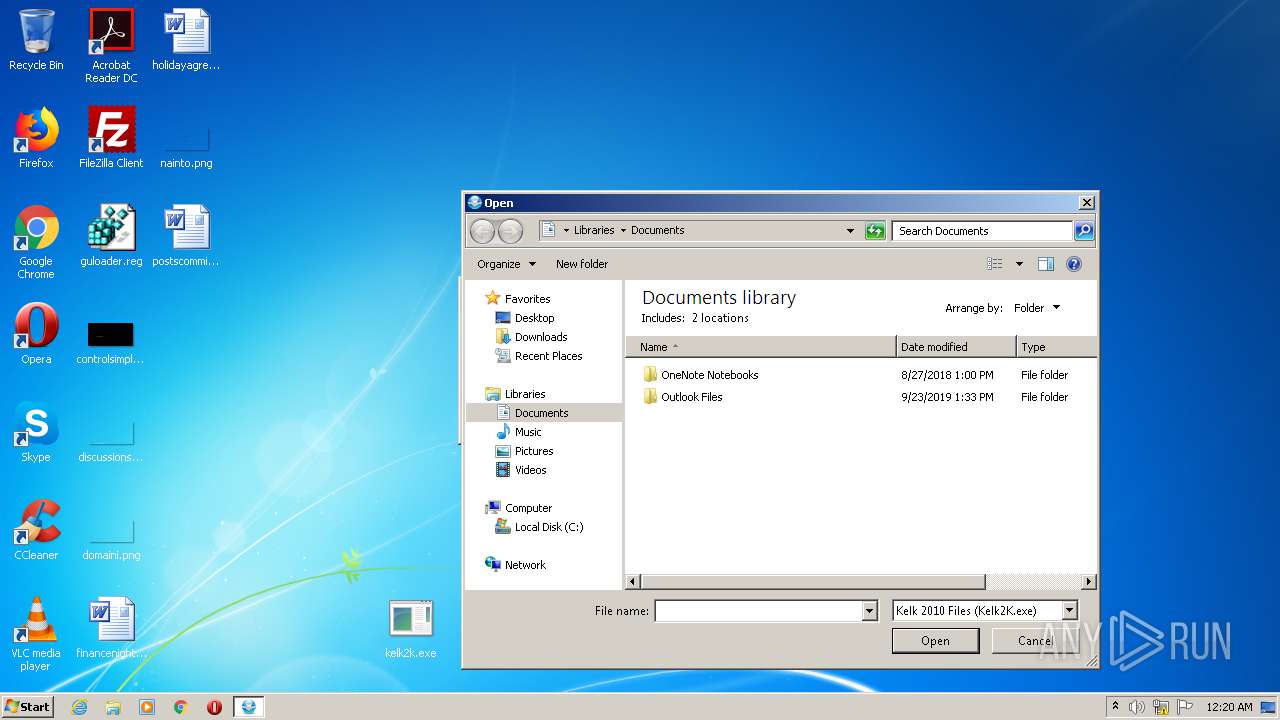
| 2468 | "C:\Users\admin\AppData\Local\Temp\Kelk 2010 Patcher v2.2.exe" | C:\Users\admin\AppData\Local\Temp\Kelk 2010 Patcher v2.2.exe | explorer.exe | ||||||||||||
User: admin Company: By o15s19,Sgr2001,Lionsys Integrity Level: MEDIUM Description: Kelk 2010 Patcher Exit code: 0 Version: 2.2.0.0 Modules
| |||||||||||||||
| 3688 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
560
Read events
497
Write events
62
Delete events
1
Modification events
| (PID) Process: | (3688) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3688) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (2468) Kelk 2010 Patcher v2.2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2468) Kelk 2010 Patcher v2.2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000001000000000000000B000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2468) Kelk 2010 Patcher v2.2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (2468) Kelk 2010 Patcher v2.2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (2468) Kelk 2010 Patcher v2.2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (2468) Kelk 2010 Patcher v2.2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2468) Kelk 2010 Patcher v2.2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (2468) Kelk 2010 Patcher v2.2.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
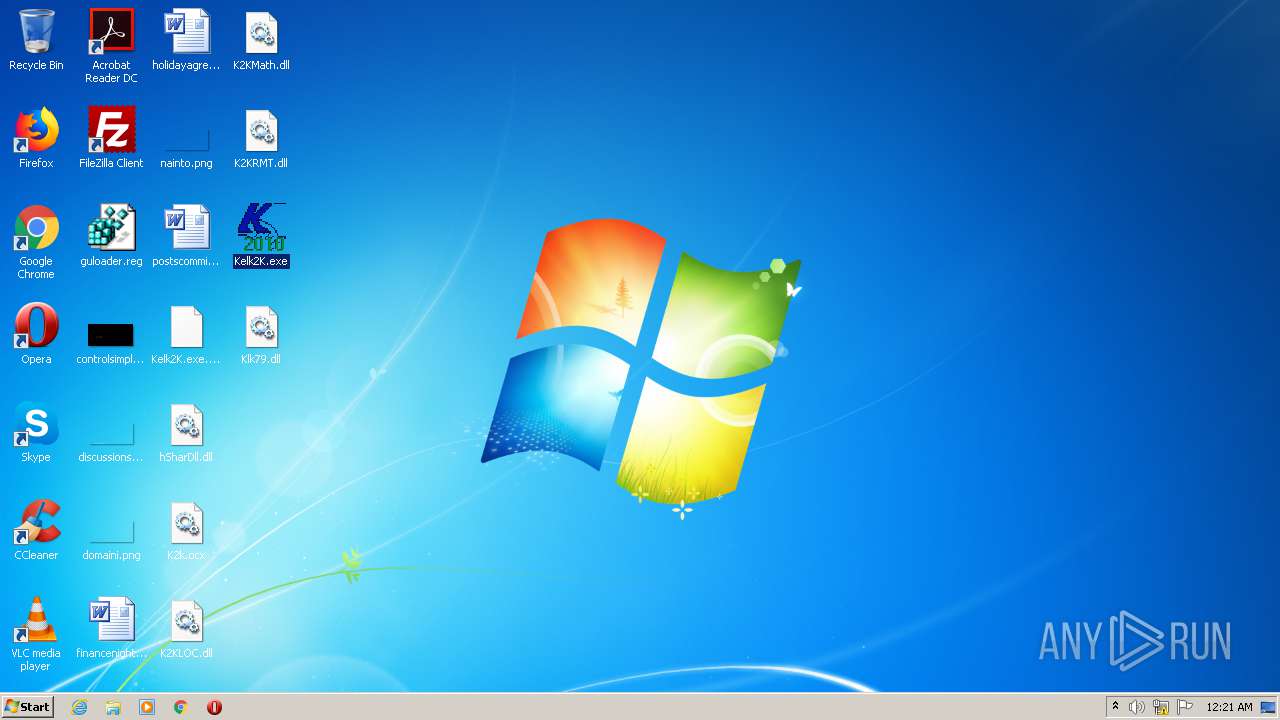
Executable files
7
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2468 | Kelk 2010 Patcher v2.2.exe | C:\Users\admin\Desktop\K2KMath.dll | executable | |
MD5:773AEA84FA0437B149BDDDF3C6B5D14F | SHA256:7439F555543C4B3B06C6F5331C150687F9F46011F58799DB950E5C8FE2D3EB85 | |||
| 2468 | Kelk 2010 Patcher v2.2.exe | C:\Users\admin\Desktop\K2KRMT.dll | executable | |
MD5:2F836450159FBCACE9BFA685C022B515 | SHA256:DB9F60E7B0B71A49AAECB801E0BFD6399B2152867098C45BB73BA059742AD8AE | |||
| 2468 | Kelk 2010 Patcher v2.2.exe | C:\Users\admin\Desktop\K2k.ocx | executable | |
MD5:0BAC96ABCC5A79AF6B06DBAA8736E1FC | SHA256:D3CF12A3D836D2A549C5464E8C302FEB5439E2EFA63A449DE9EED3612546D0C1 | |||
| 2468 | Kelk 2010 Patcher v2.2.exe | C:\Users\admin\Desktop\hSharDll.dll | executable | |
MD5:E323E70F0BE88B1EB7FCB4A584DEC1C3 | SHA256:D5EEAF9245F0E53F55EFEE3AA8A9B3E5966A2E7D873EB63982CDC0F564732C84 | |||
| 2468 | Kelk 2010 Patcher v2.2.exe | C:\Users\admin\Desktop\Kelk2K.exe | executable | |
MD5:B1887E2E87E4A1287E8C63F59CDB4A96 | SHA256:85AE0032A9AE4272CB25E24D13DBACF746DB011DA424F8AE62B2315E64DAA902 | |||
| 2468 | Kelk 2010 Patcher v2.2.exe | C:\Users\admin\Desktop\K2KLOC.dll | executable | |
MD5:8110FF69A6F7E47A12E8A2633CD39688 | SHA256:92222CDC1C70A7A68420F0CC02EB830174CBF6153D9F7D655C79DB779A0B9D53 | |||
| 2468 | Kelk 2010 Patcher v2.2.exe | C:\Users\admin\Desktop\Klk79.dll | executable | |
MD5:E984A2A975E961E8B2C949B8C18C6F98 | SHA256:2AABF1FFC1E3166541EA475DDC5C5FD3D46E09FC98E15DAE46B9CCCE96226586 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report