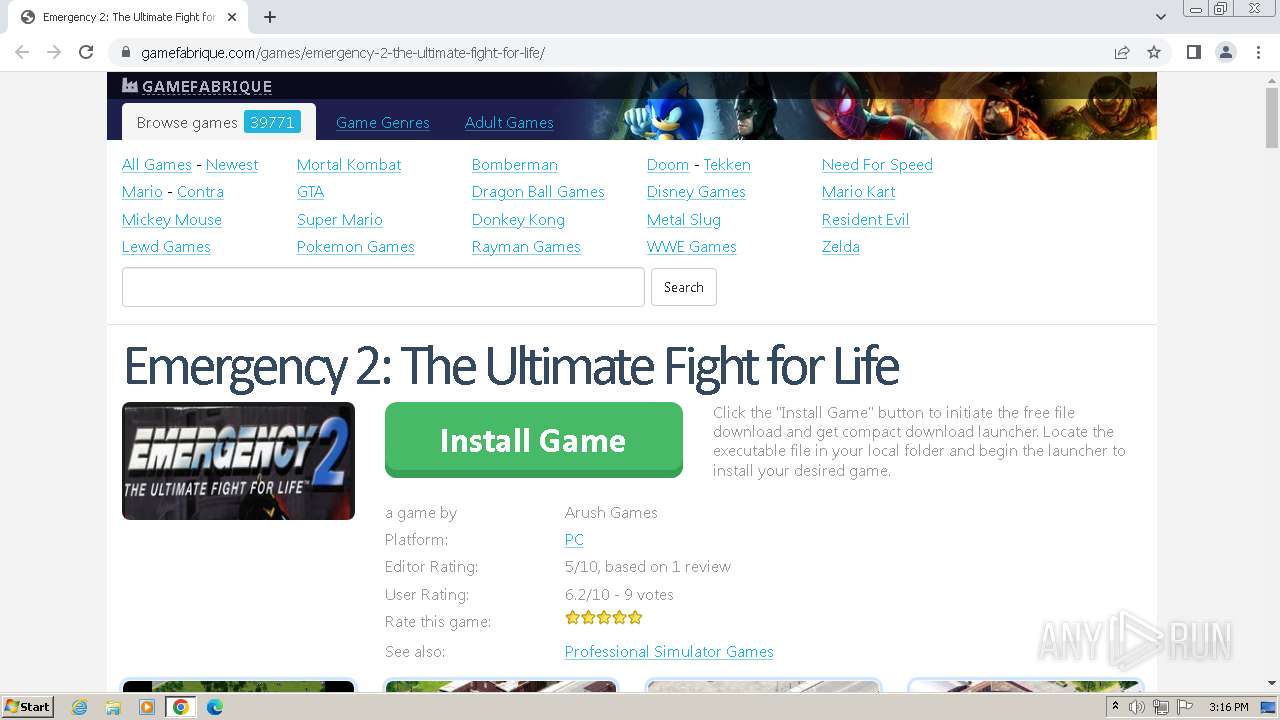
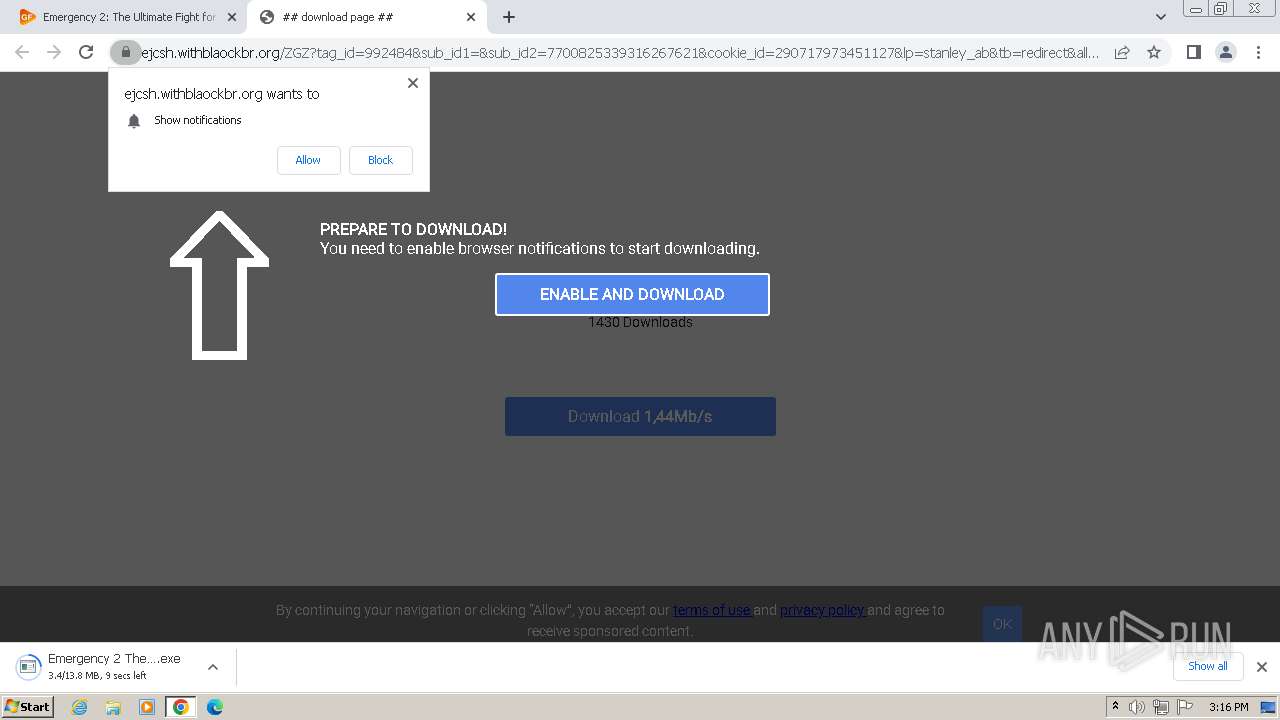
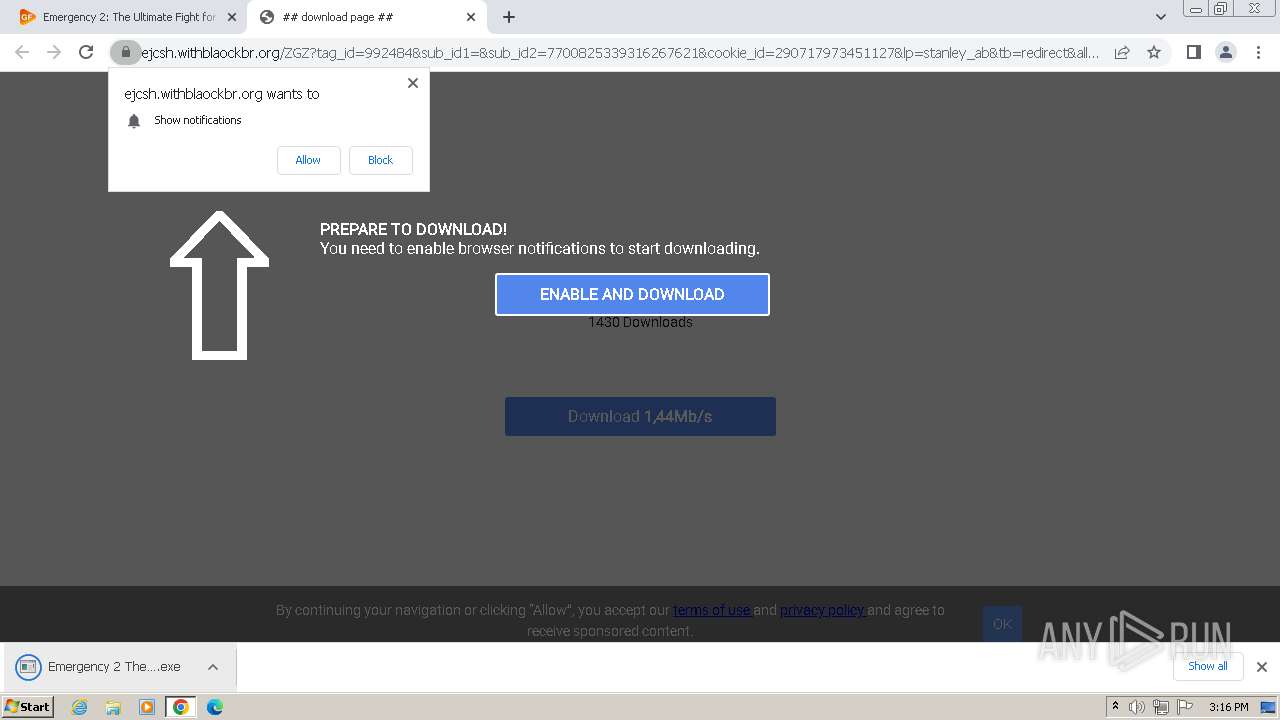
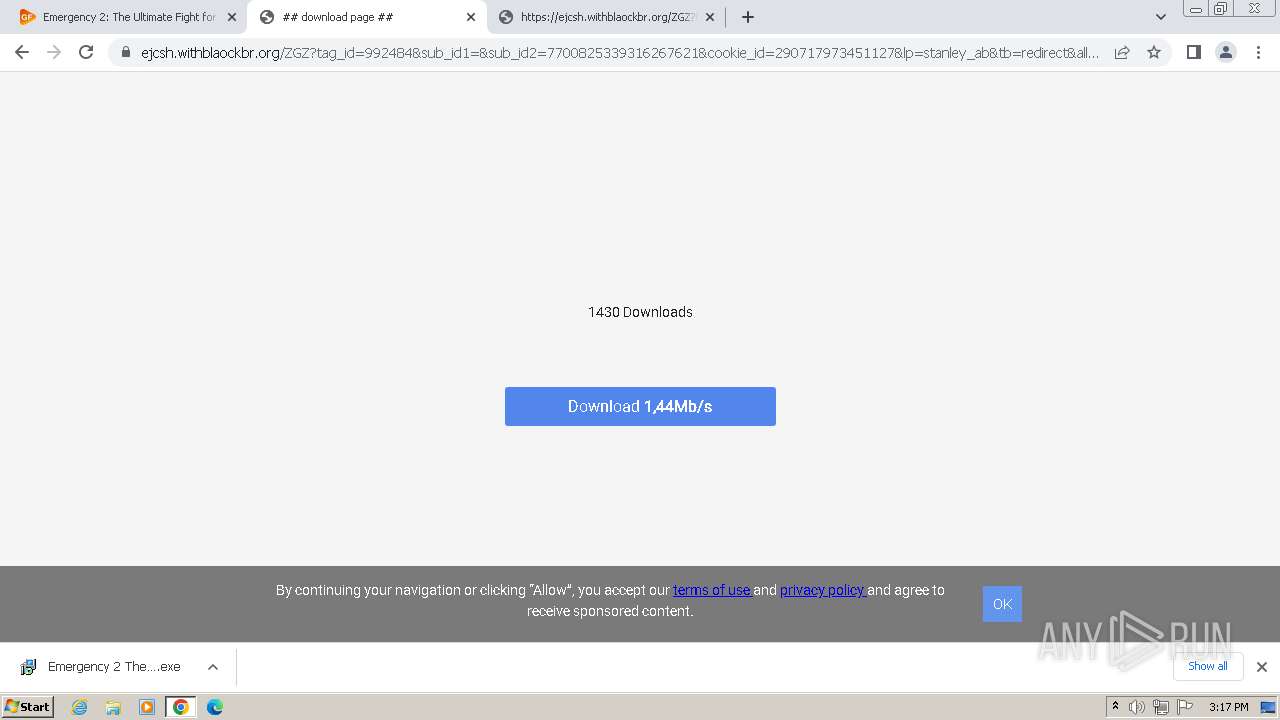
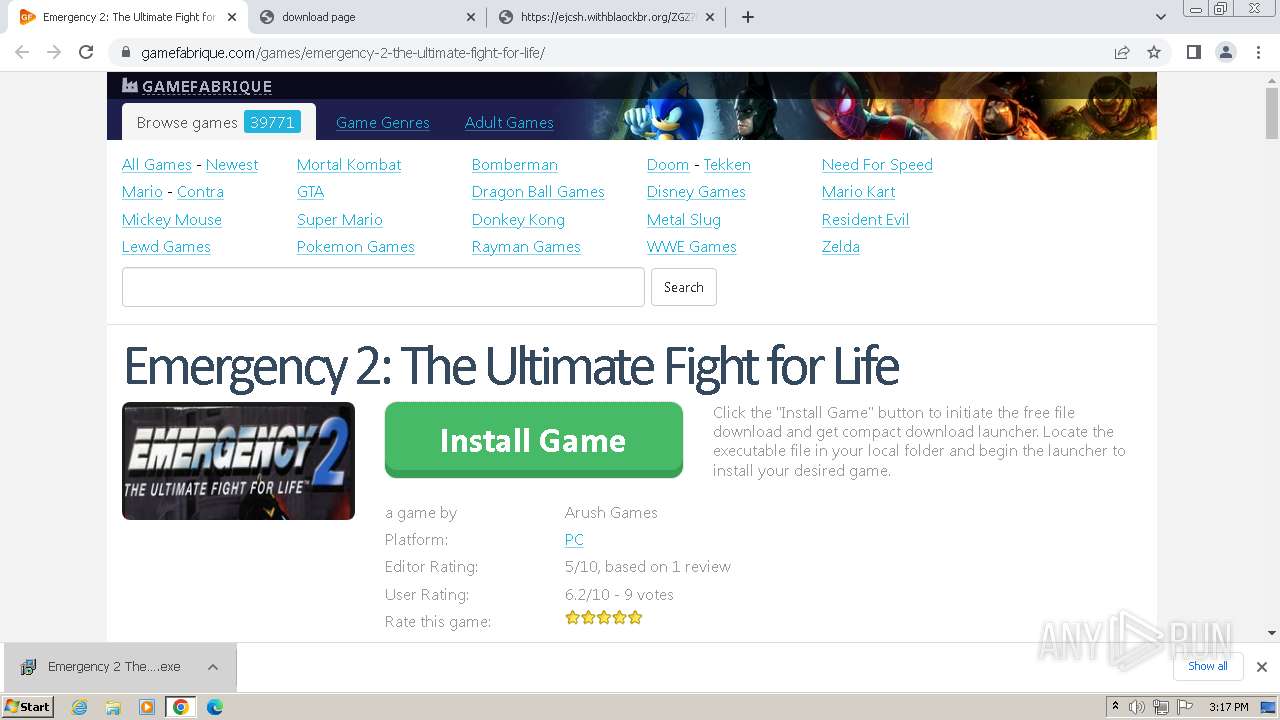
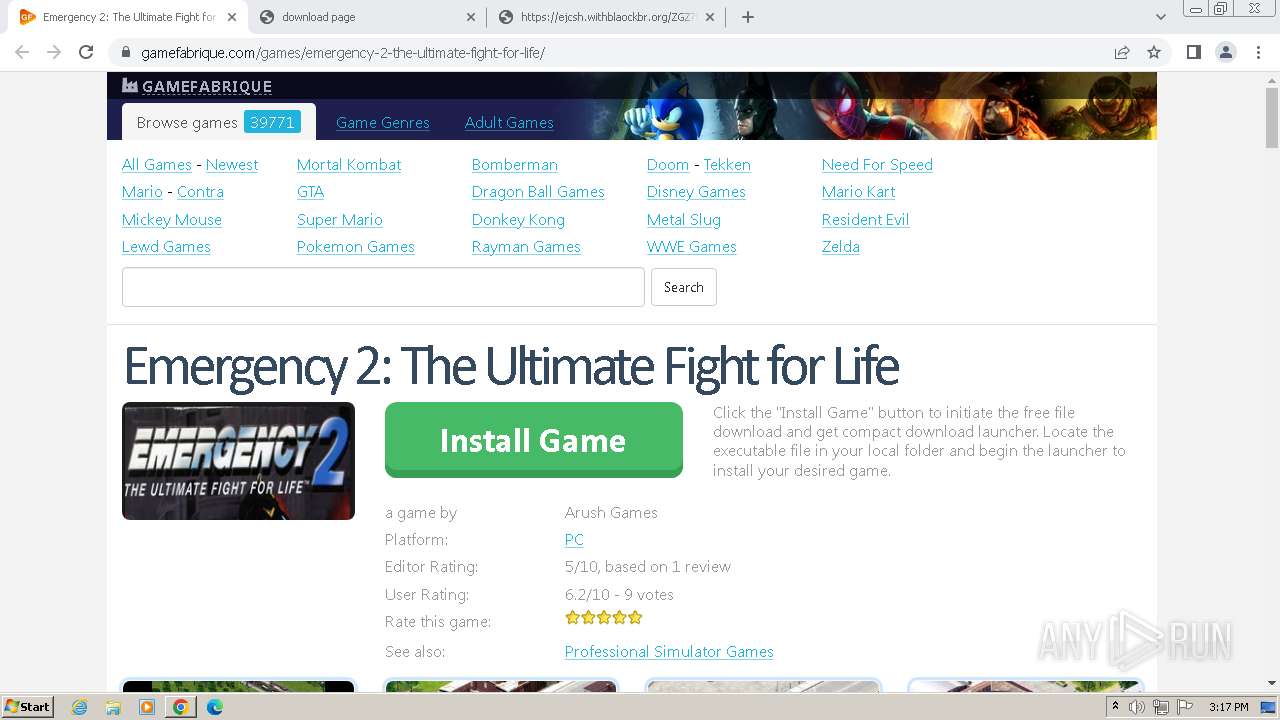
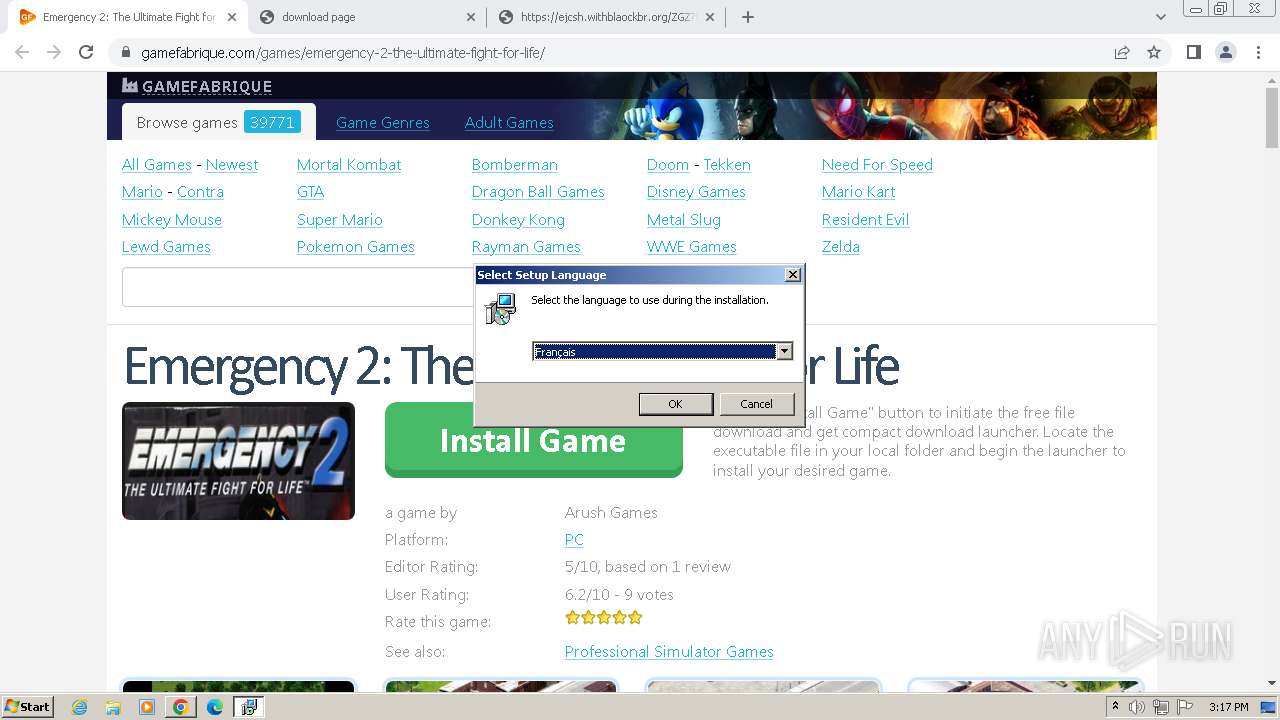
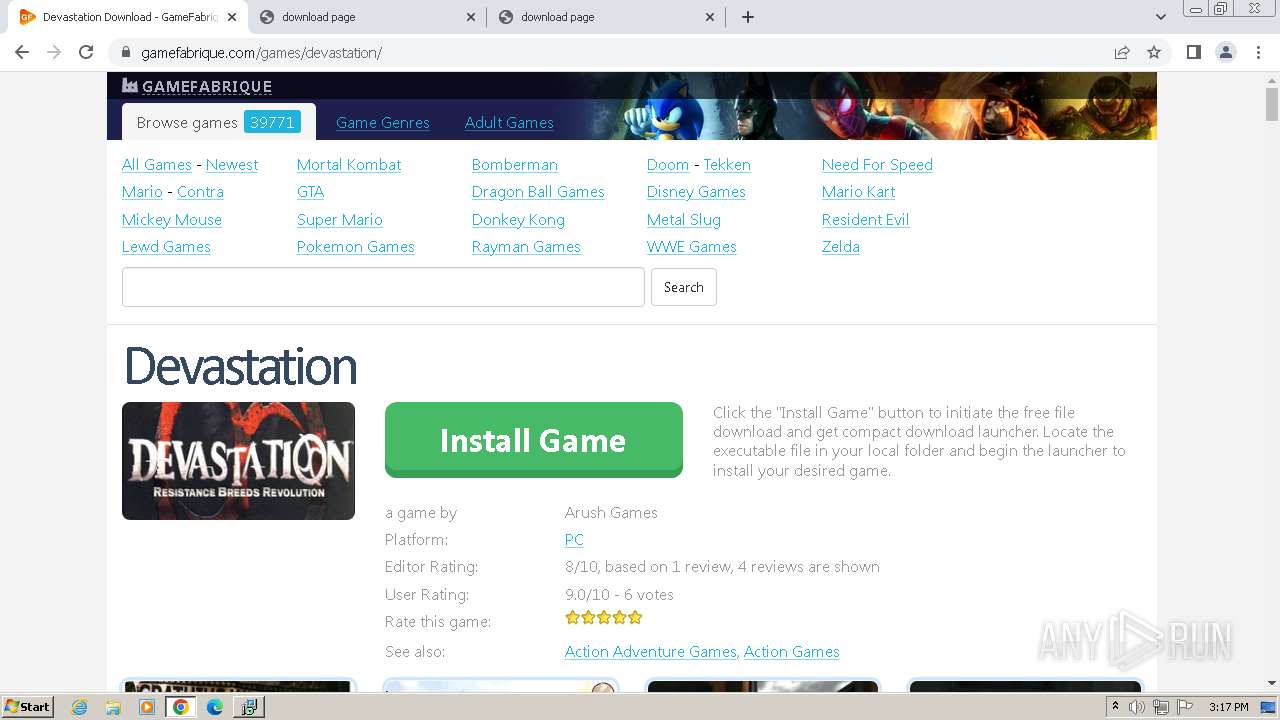
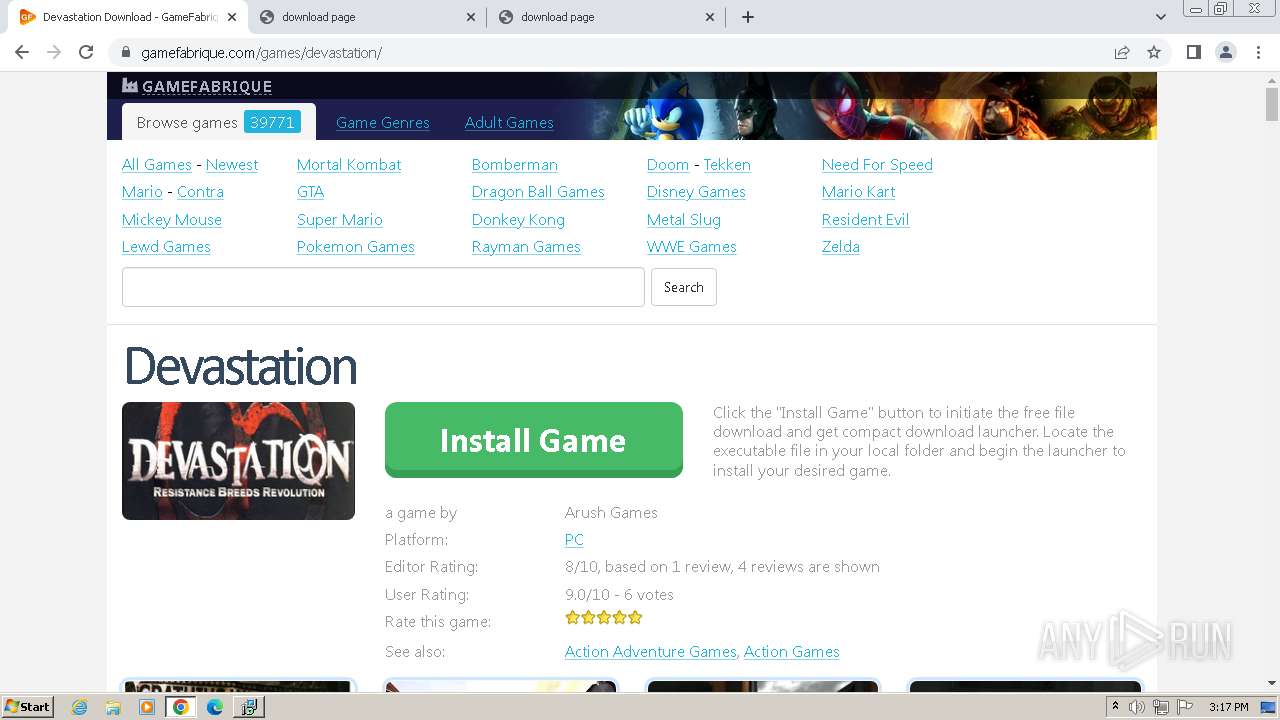
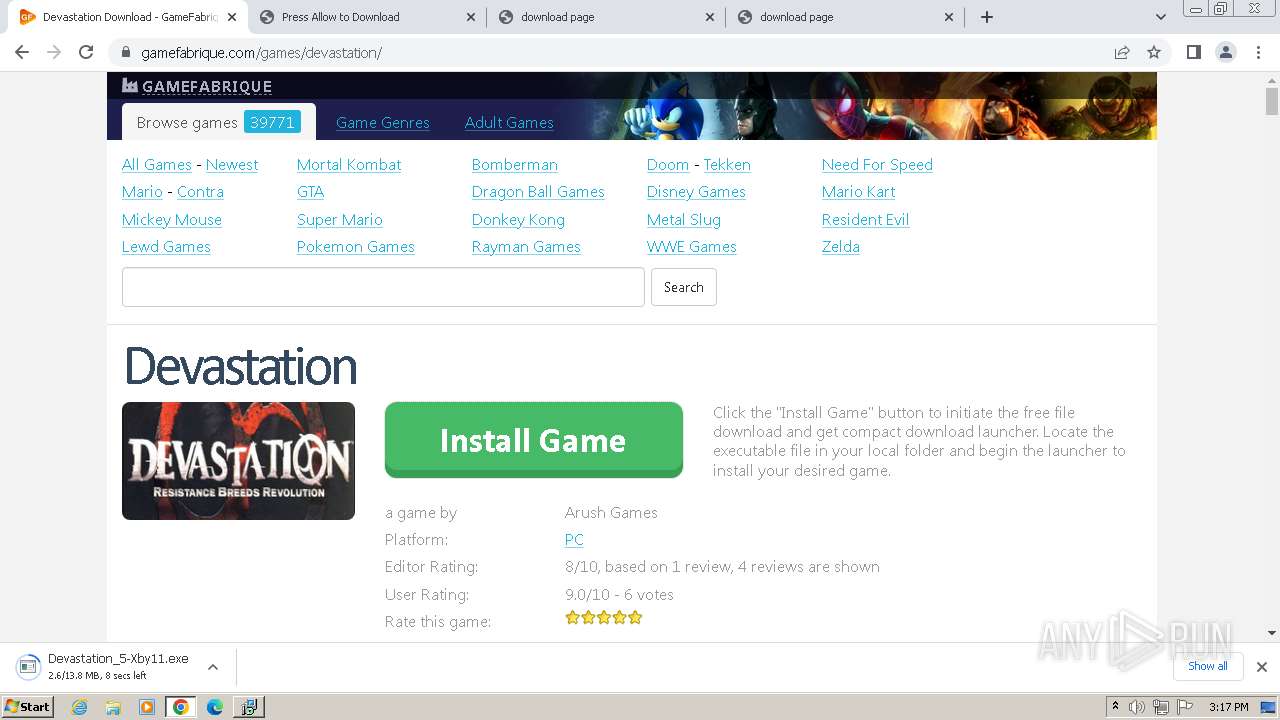
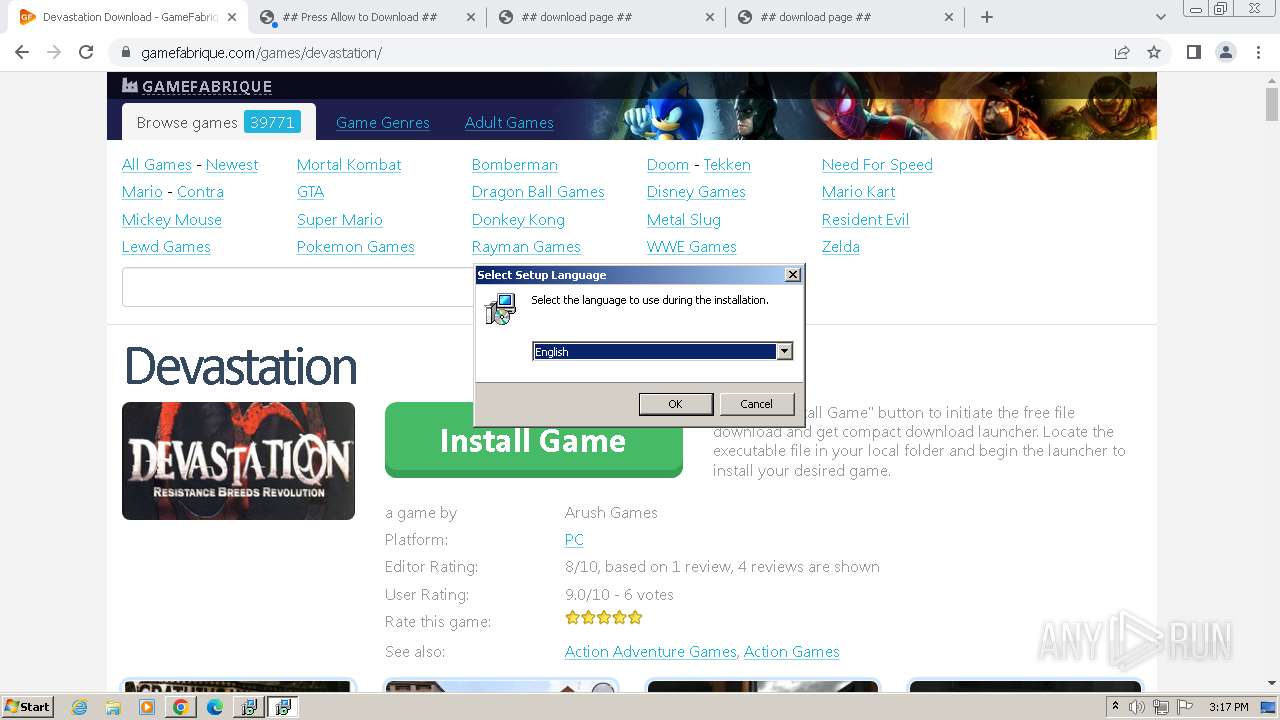
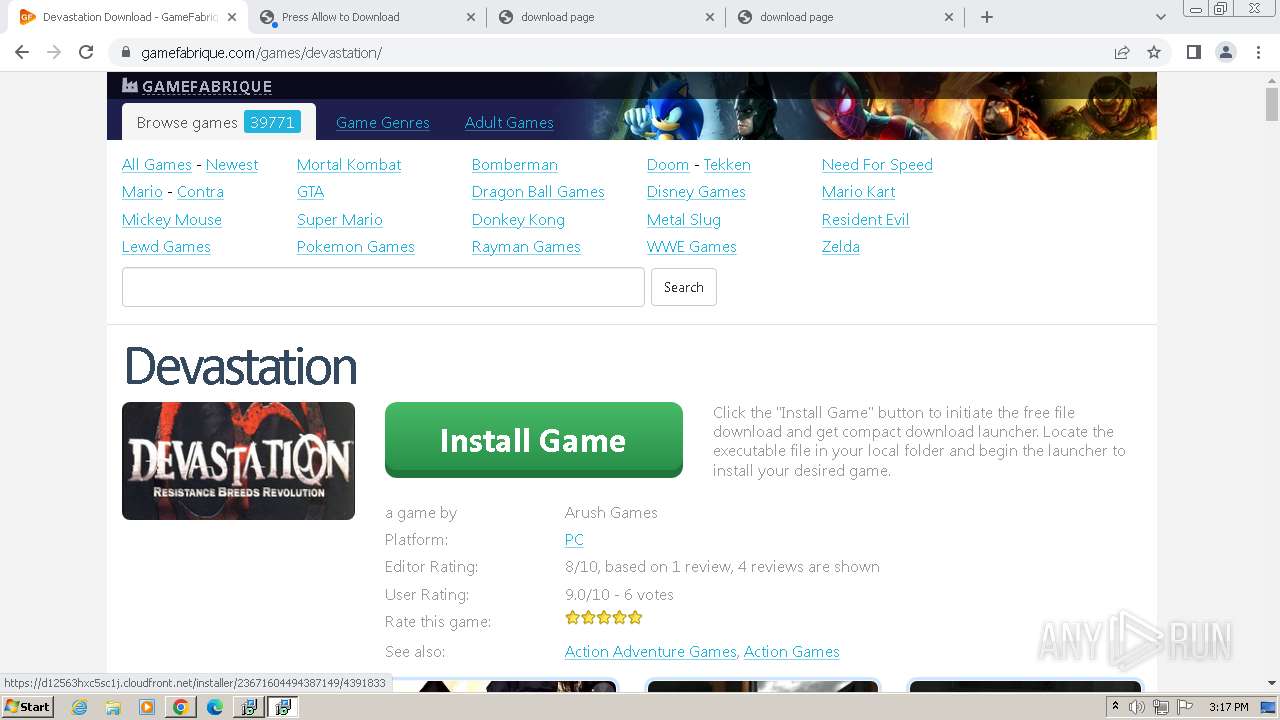
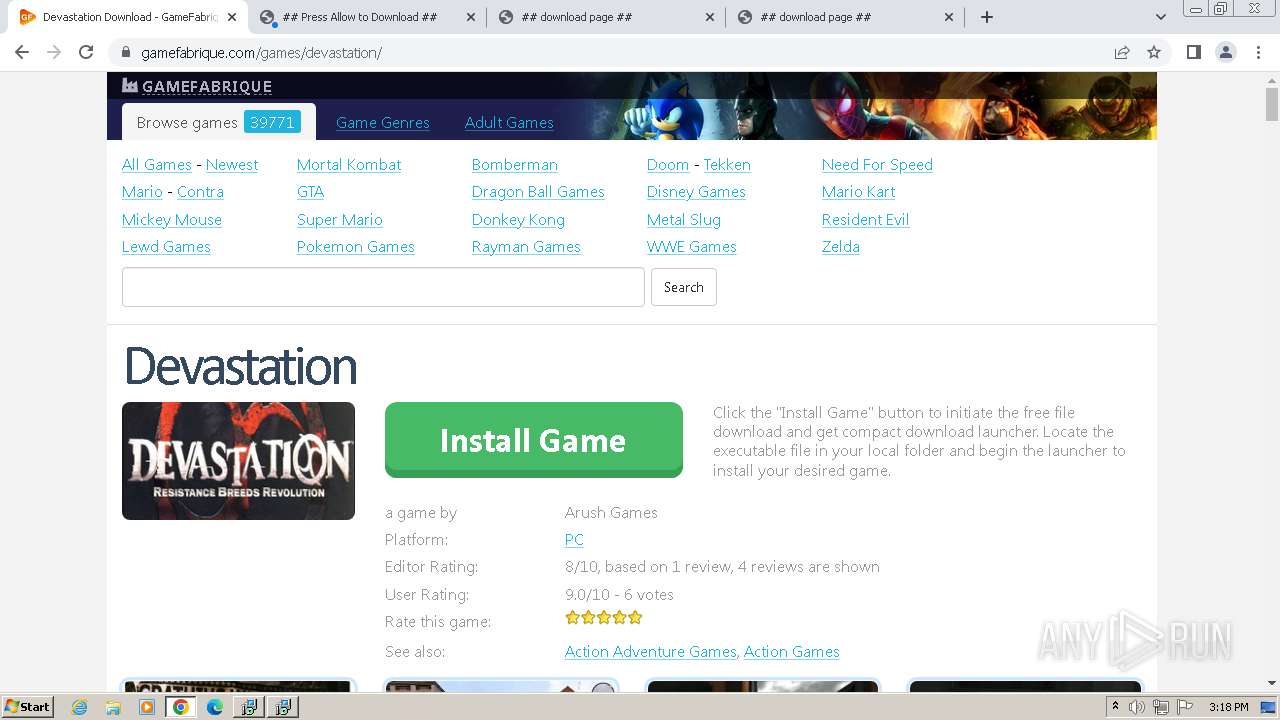
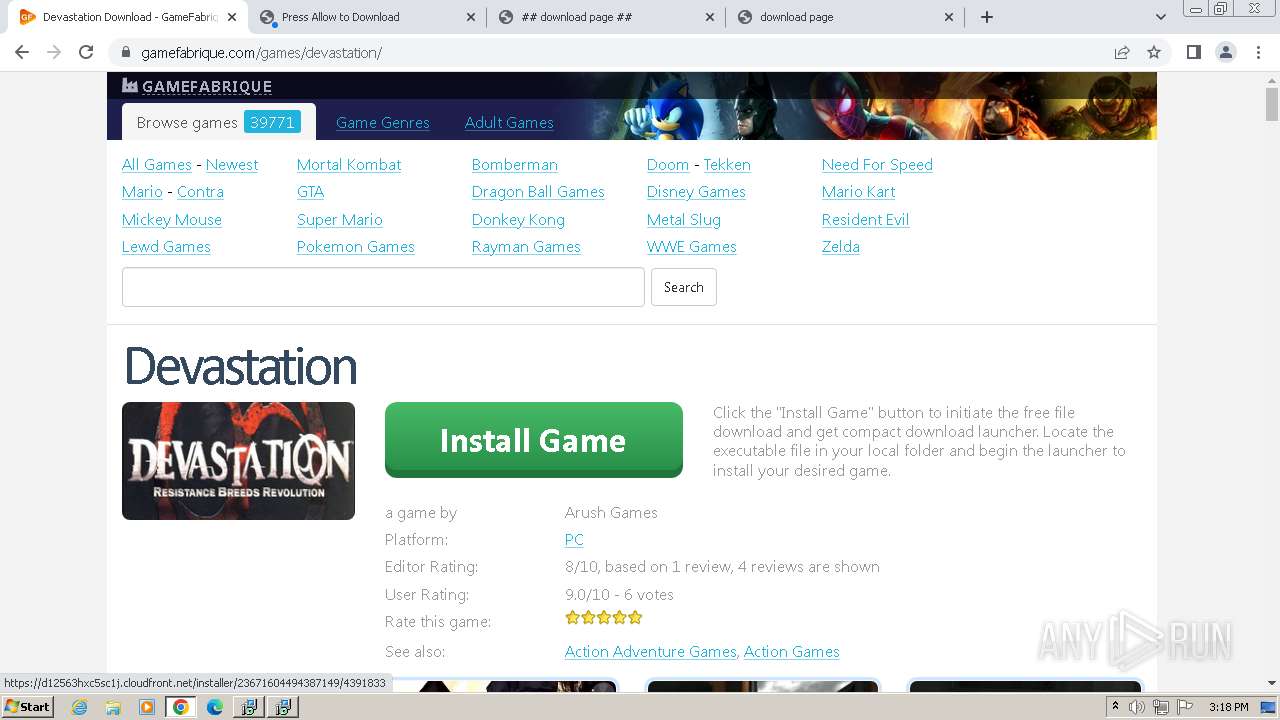
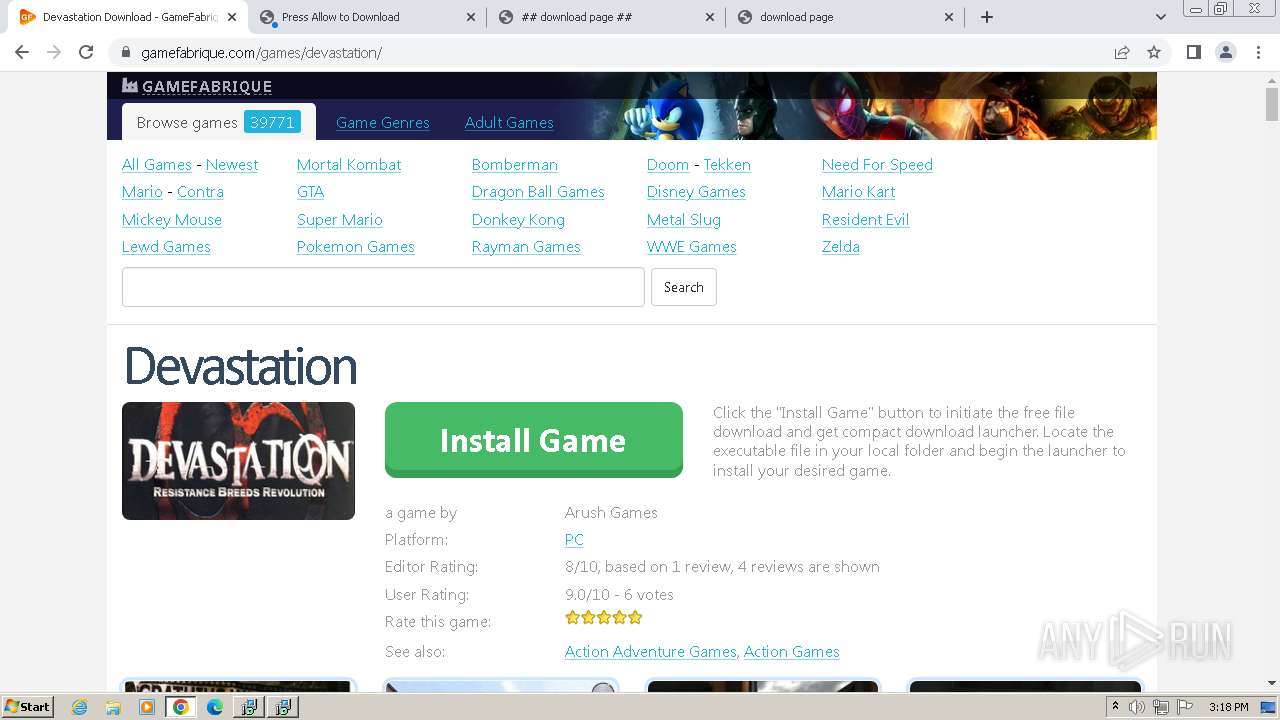
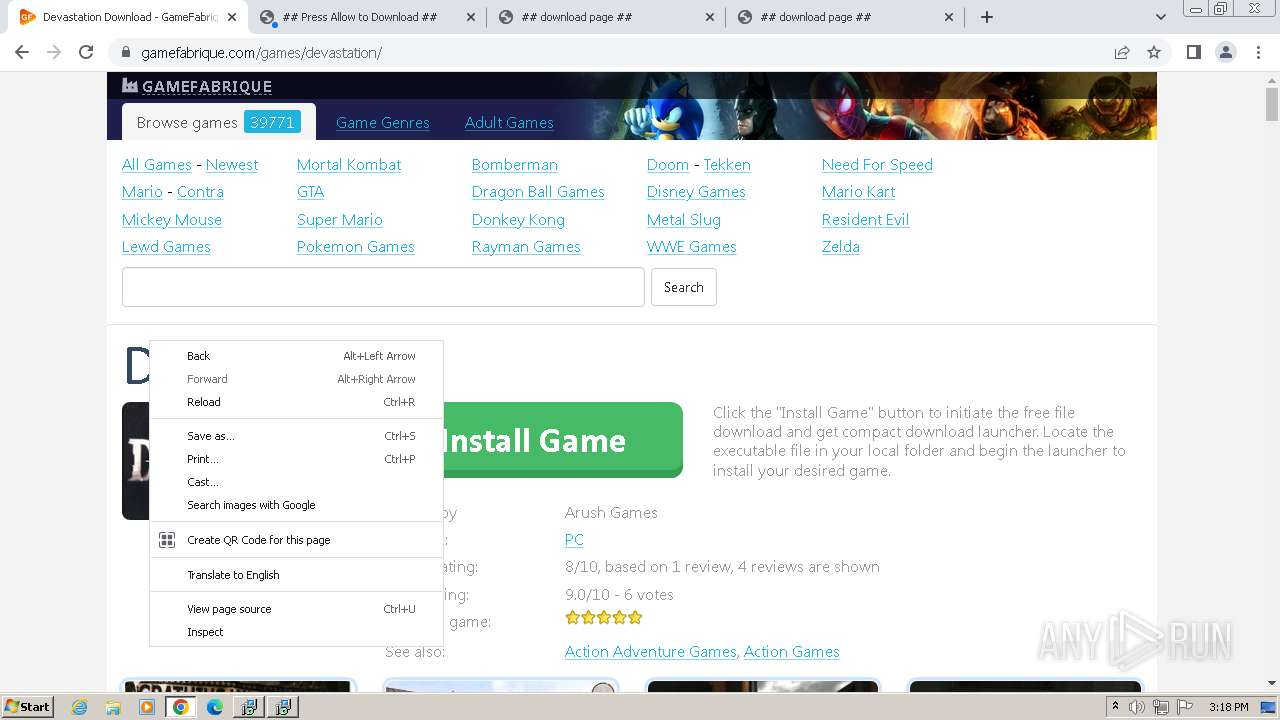
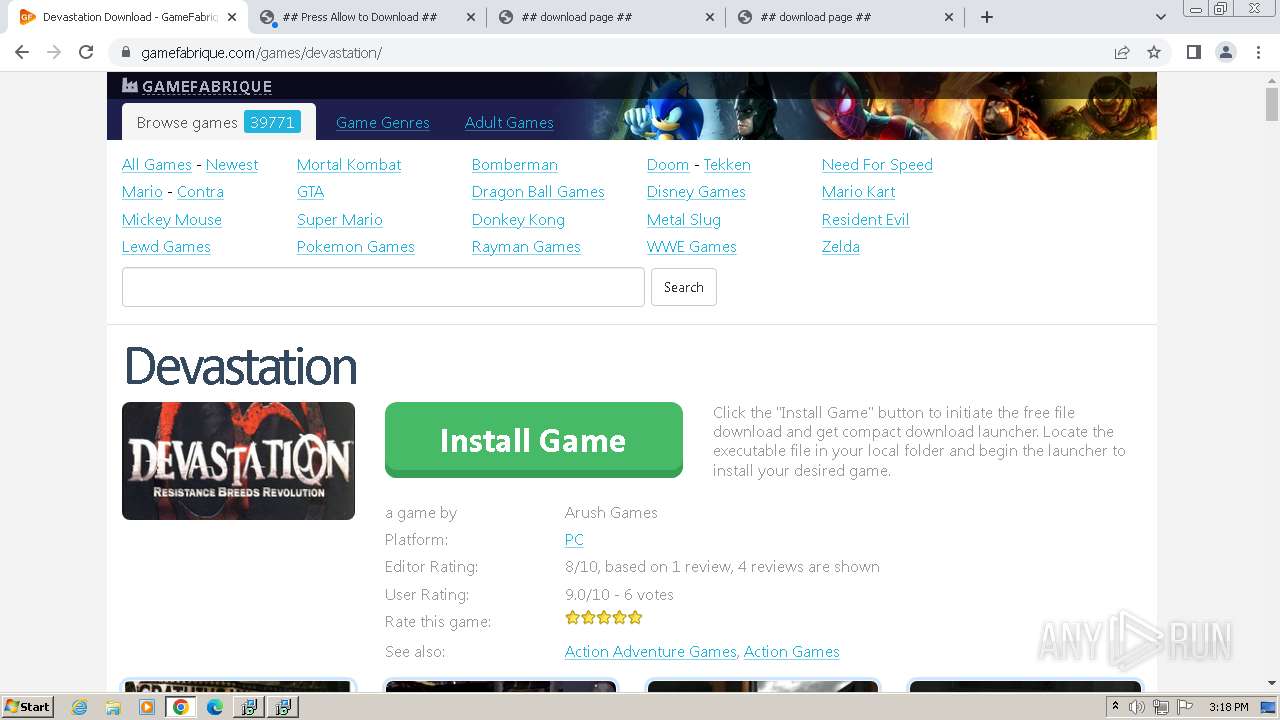
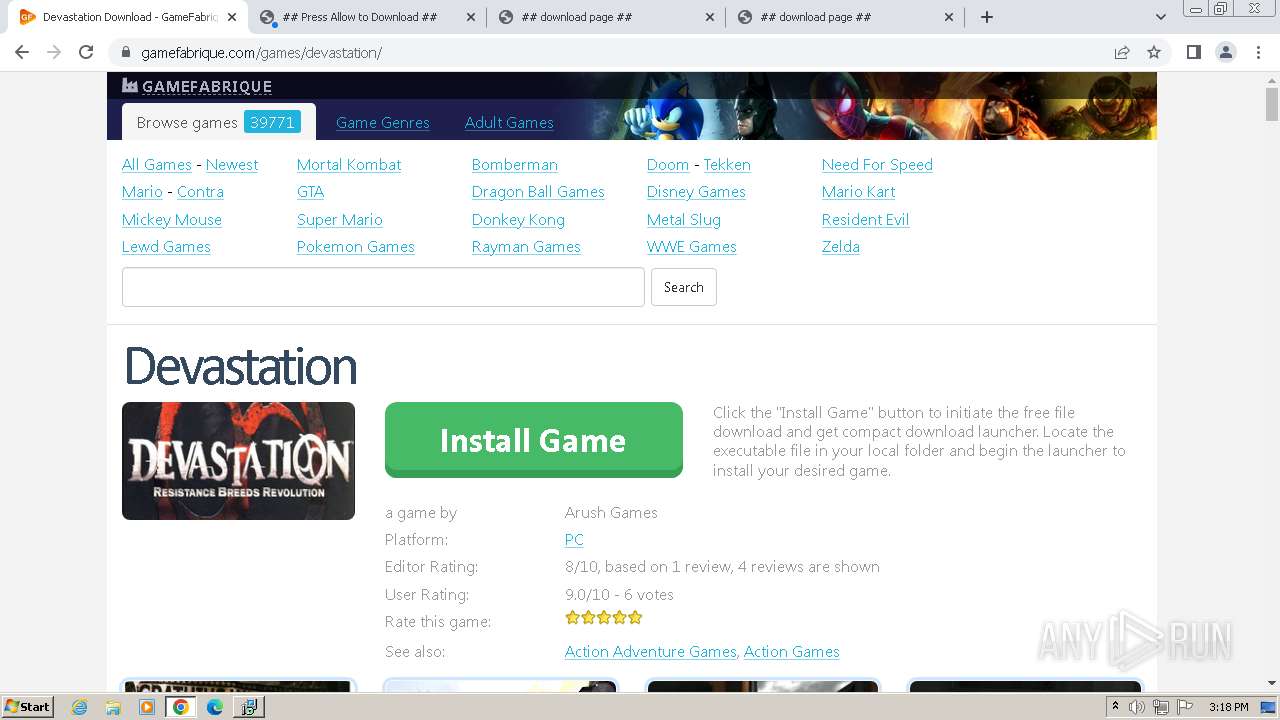
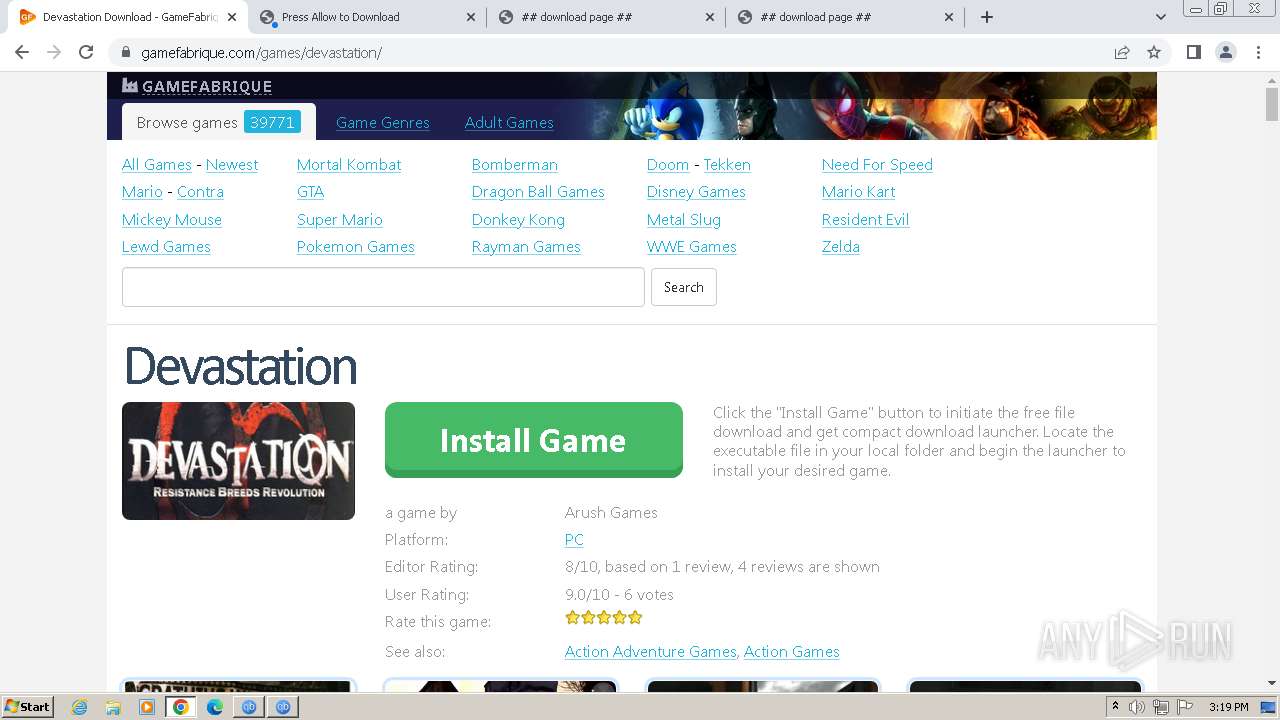
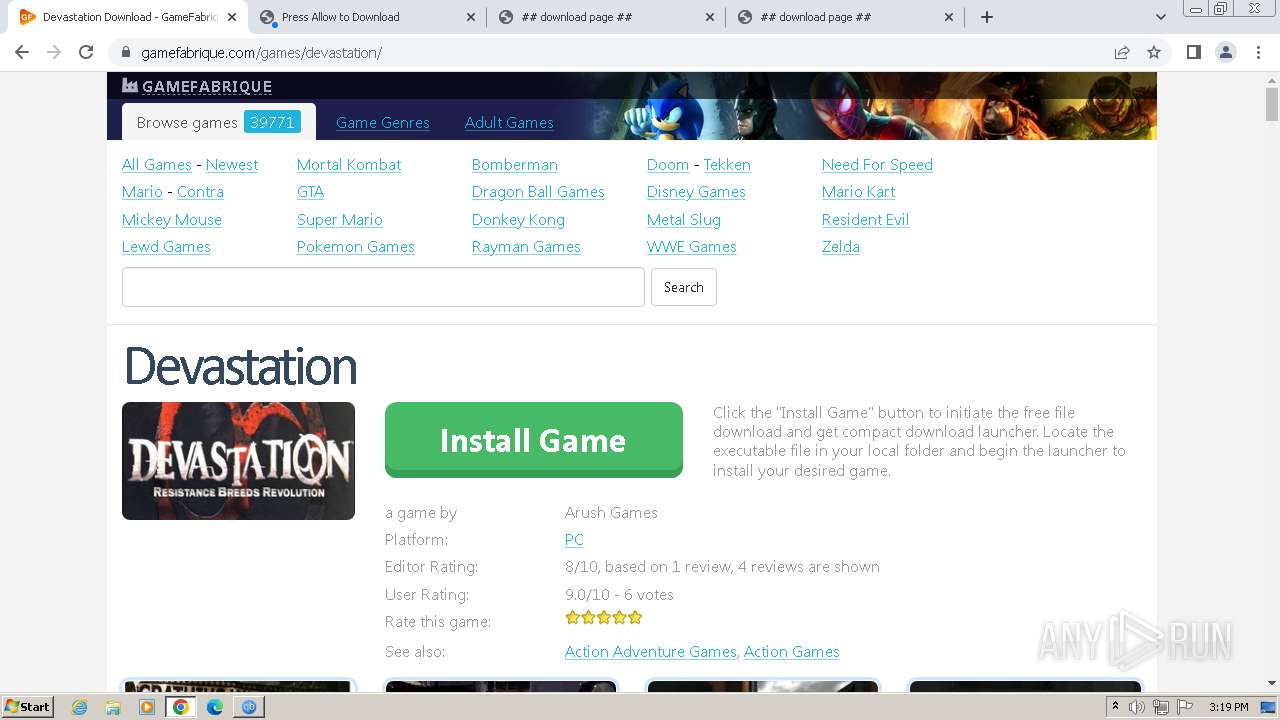
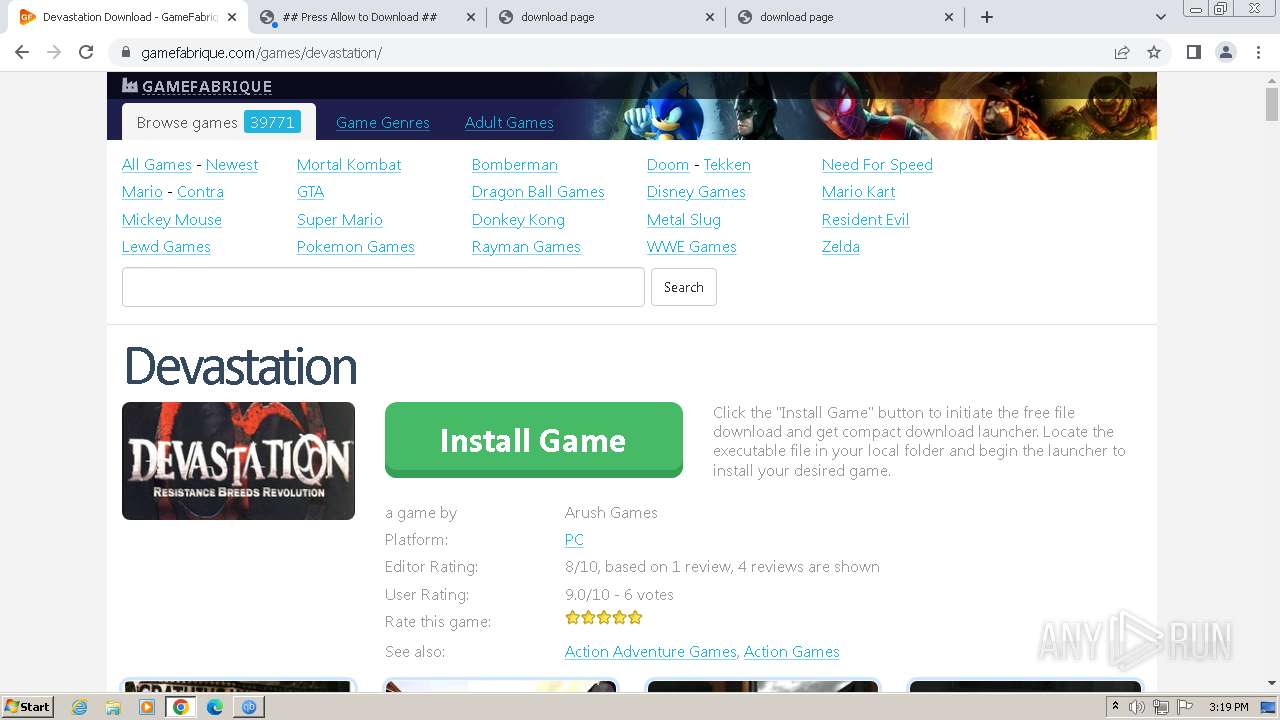
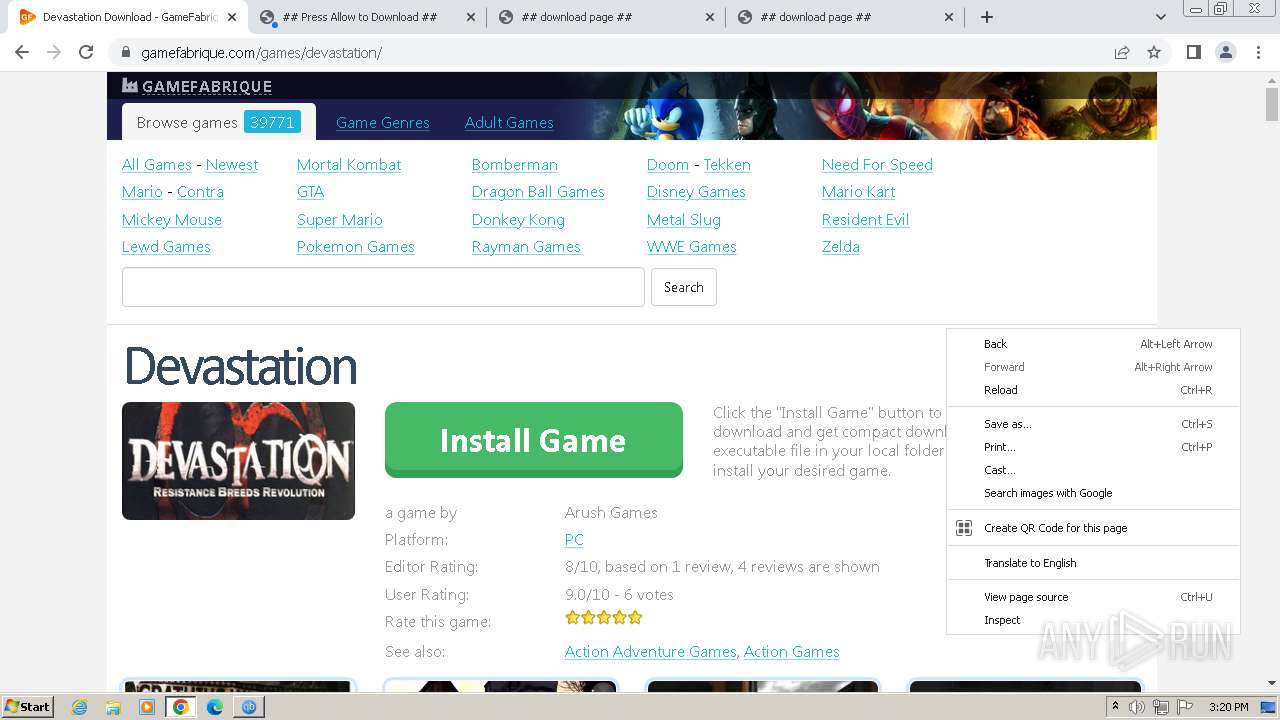
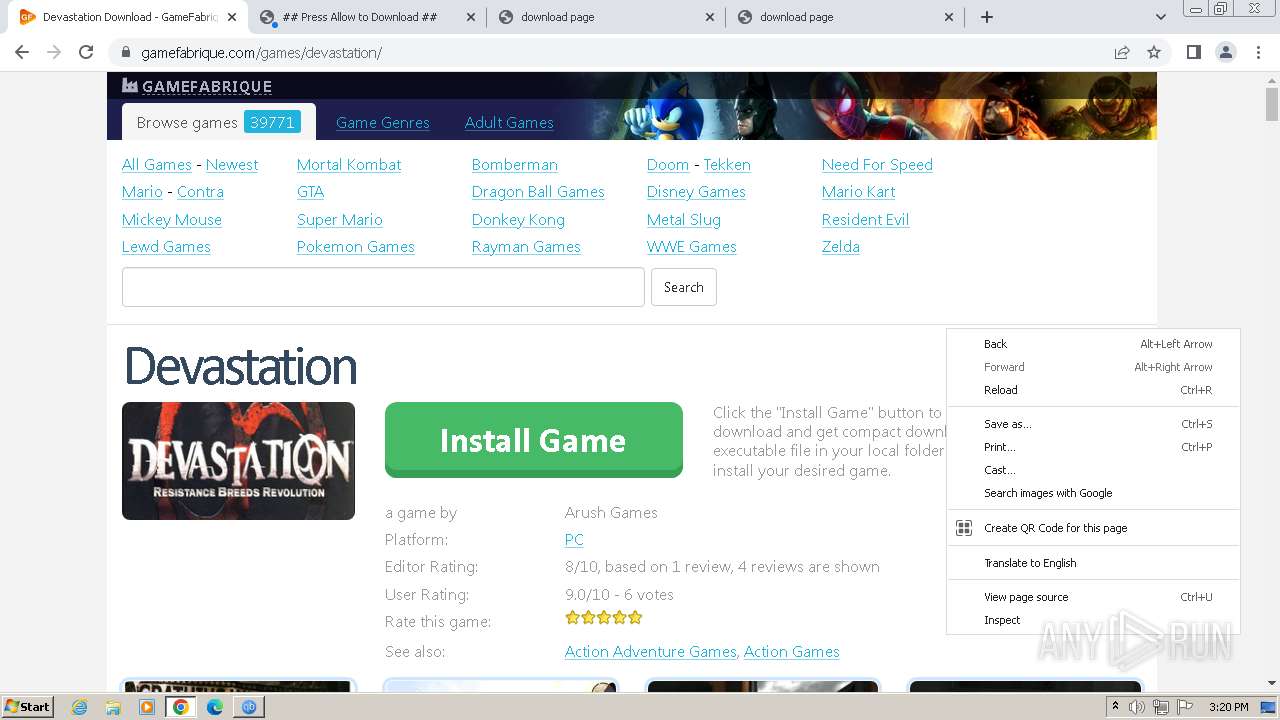
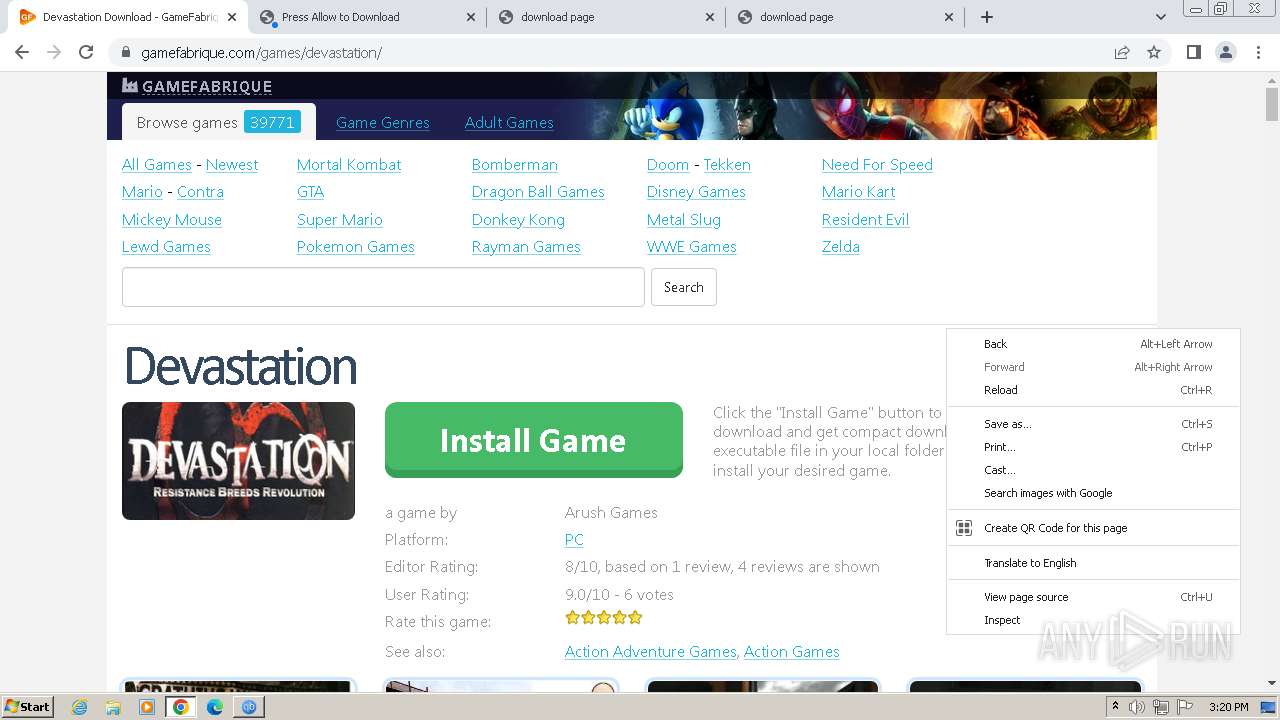
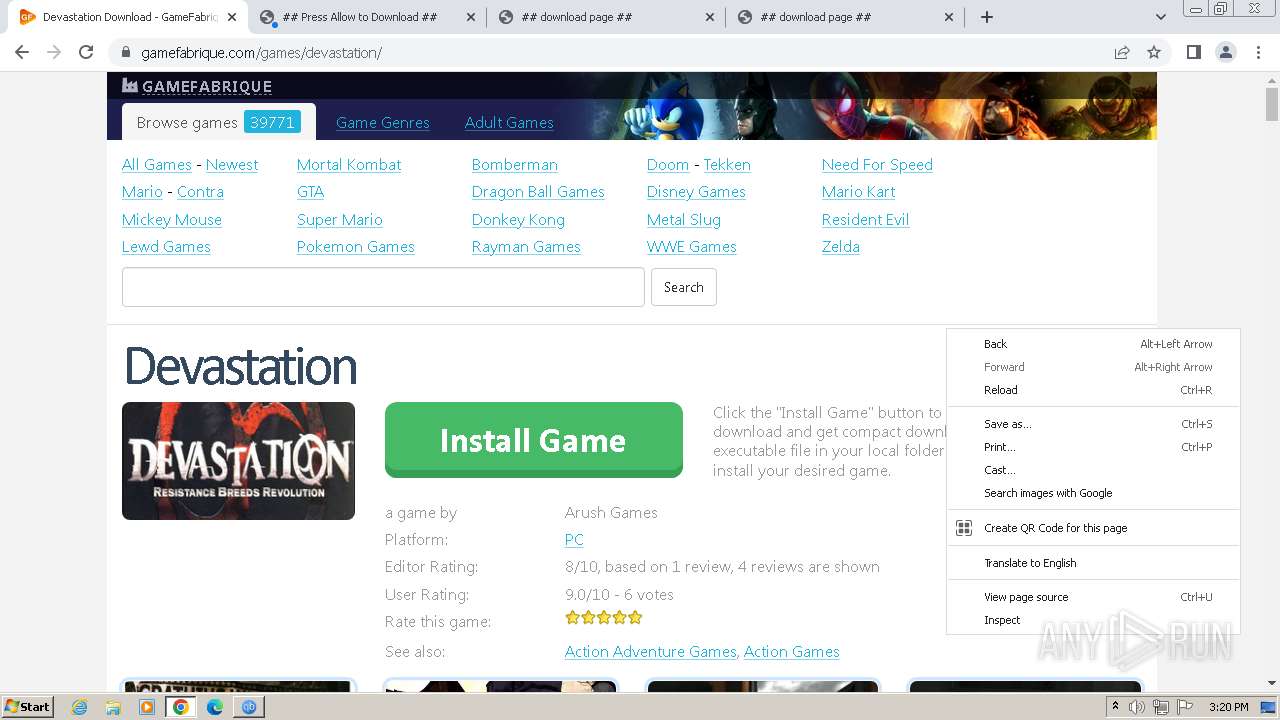
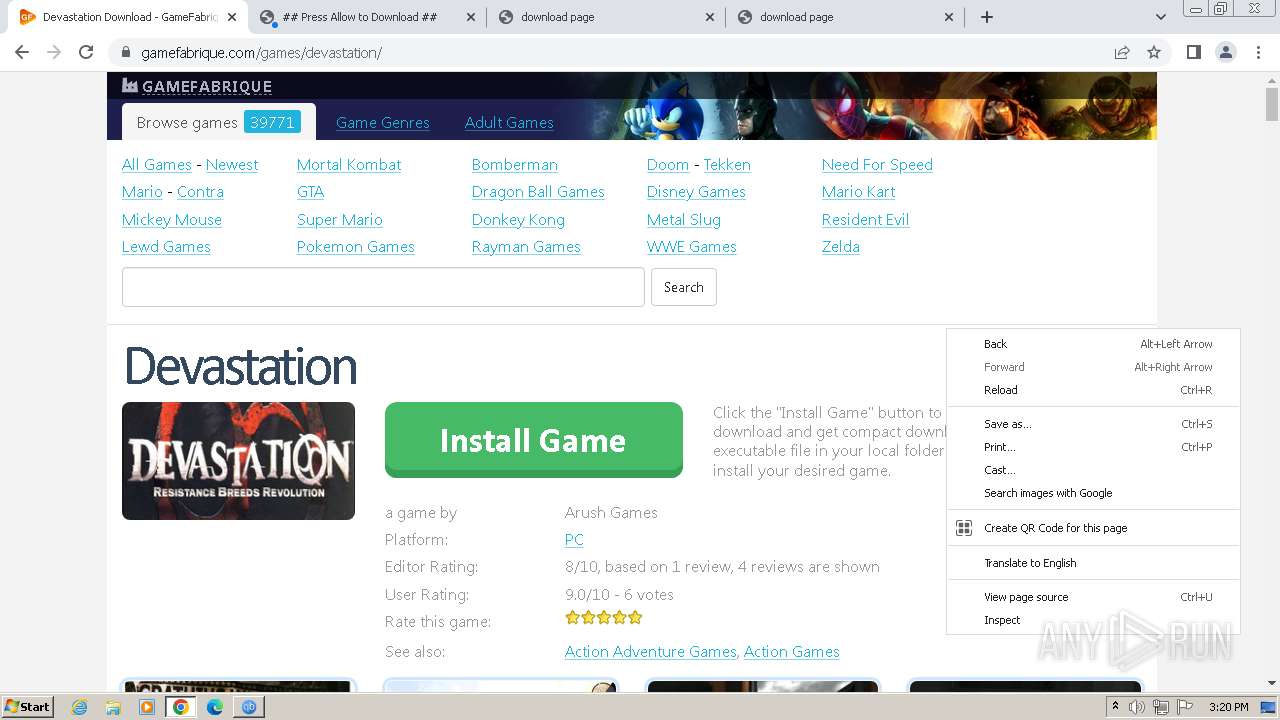
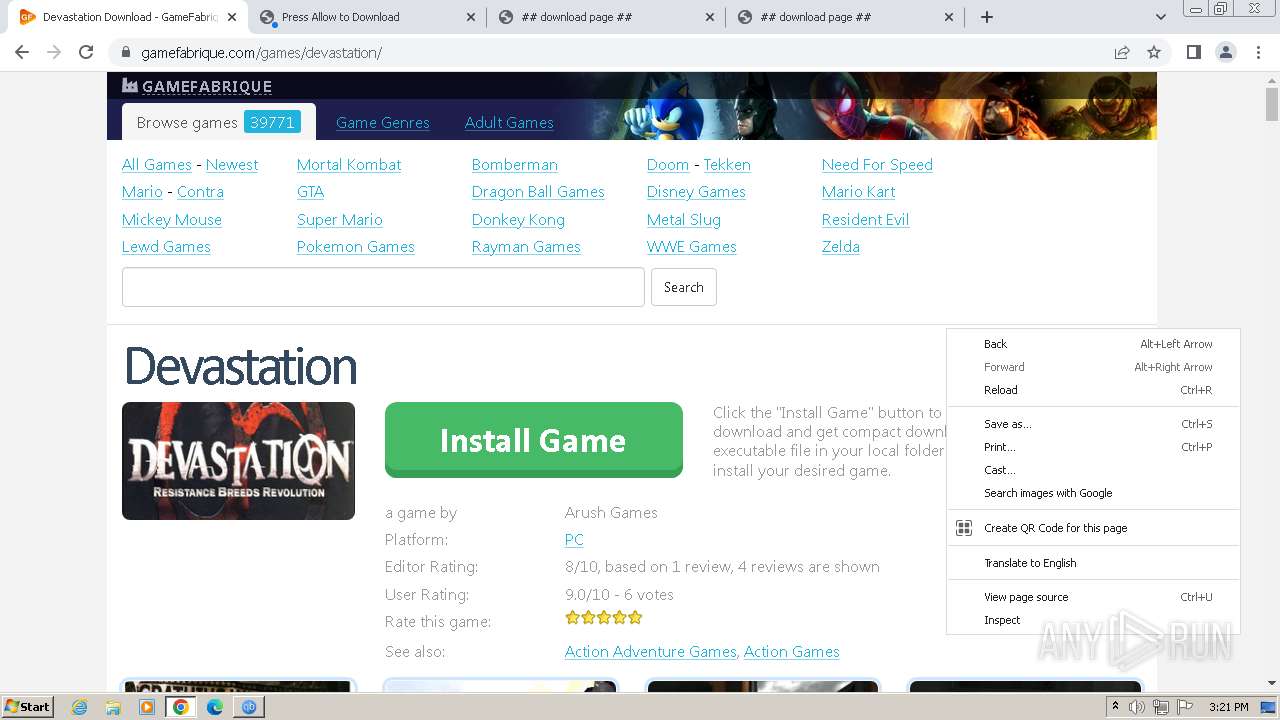
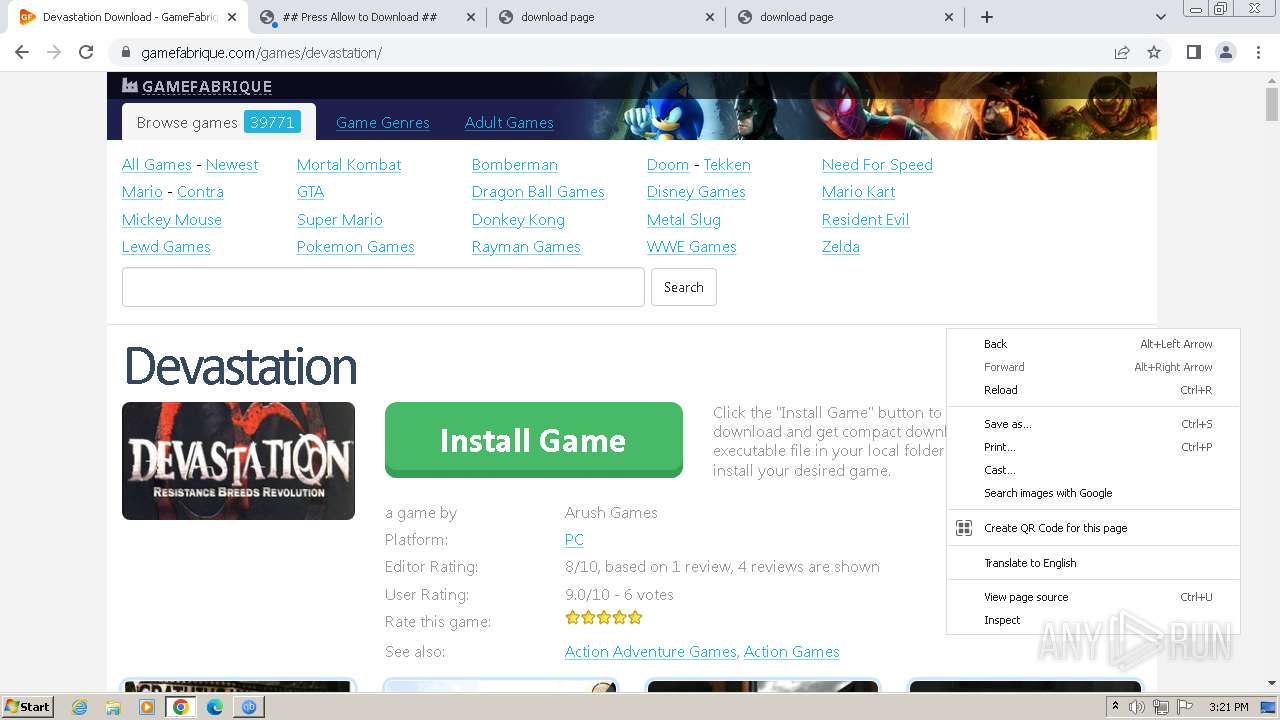
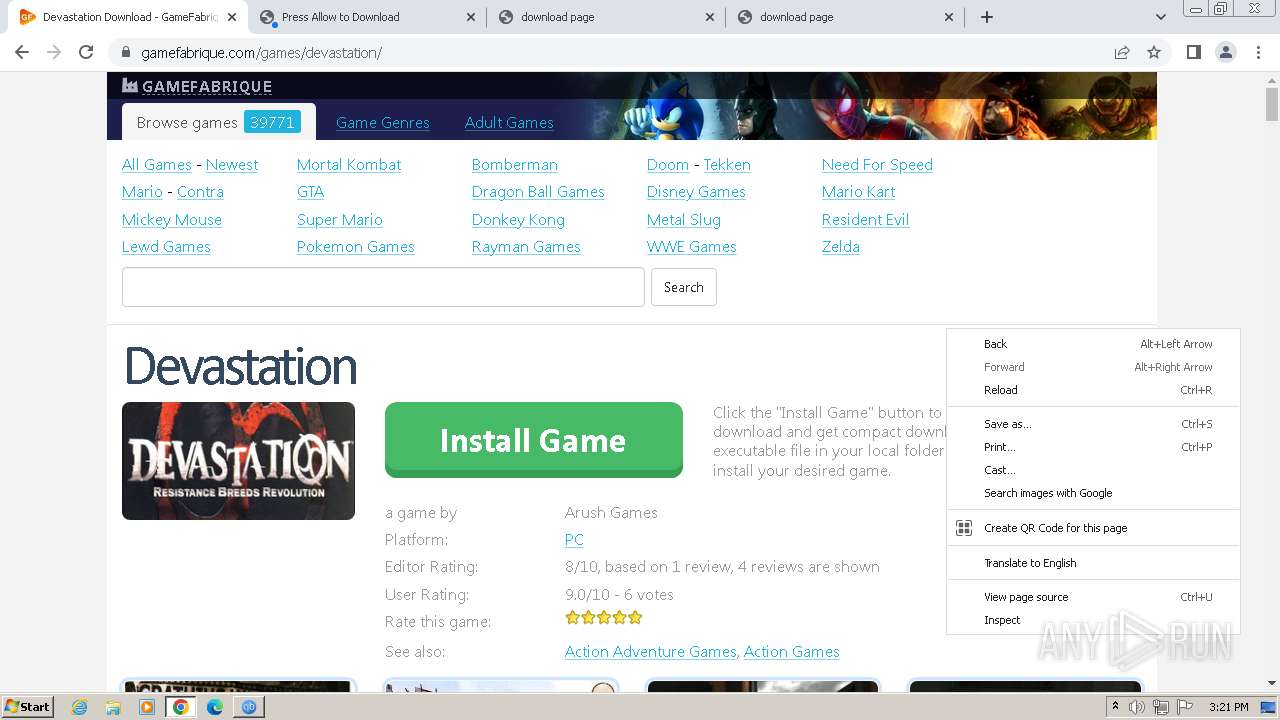
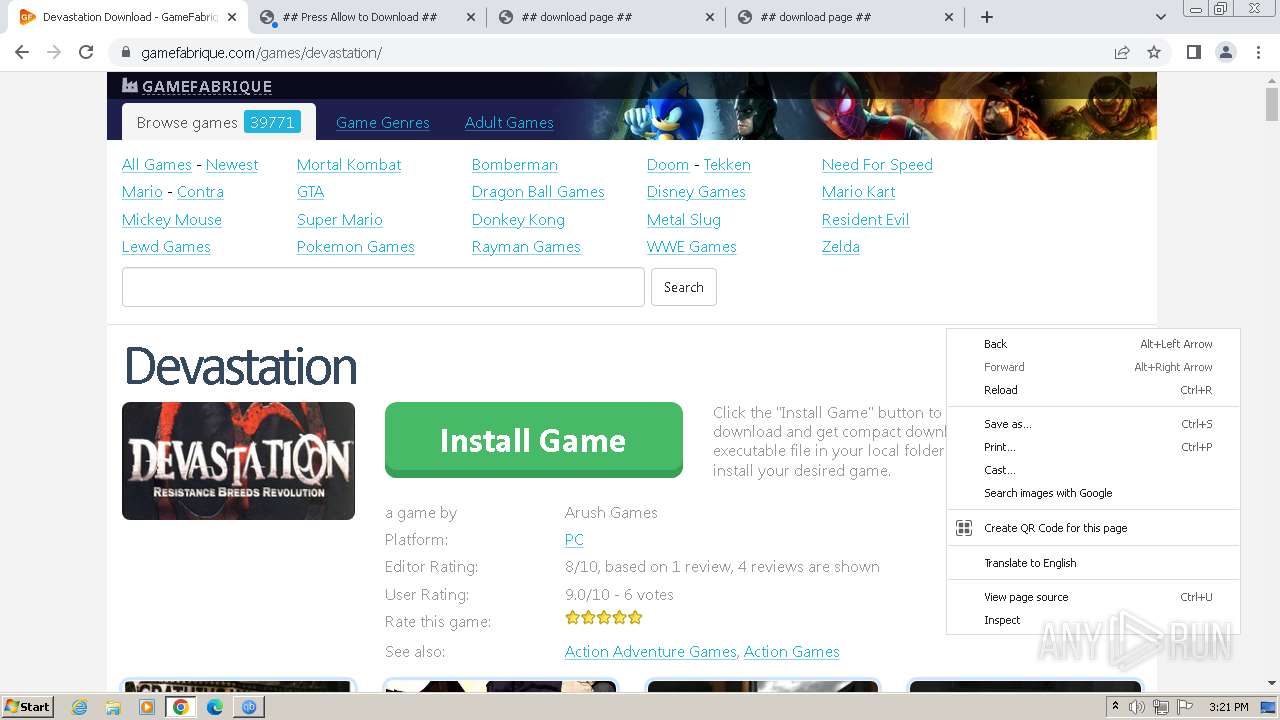
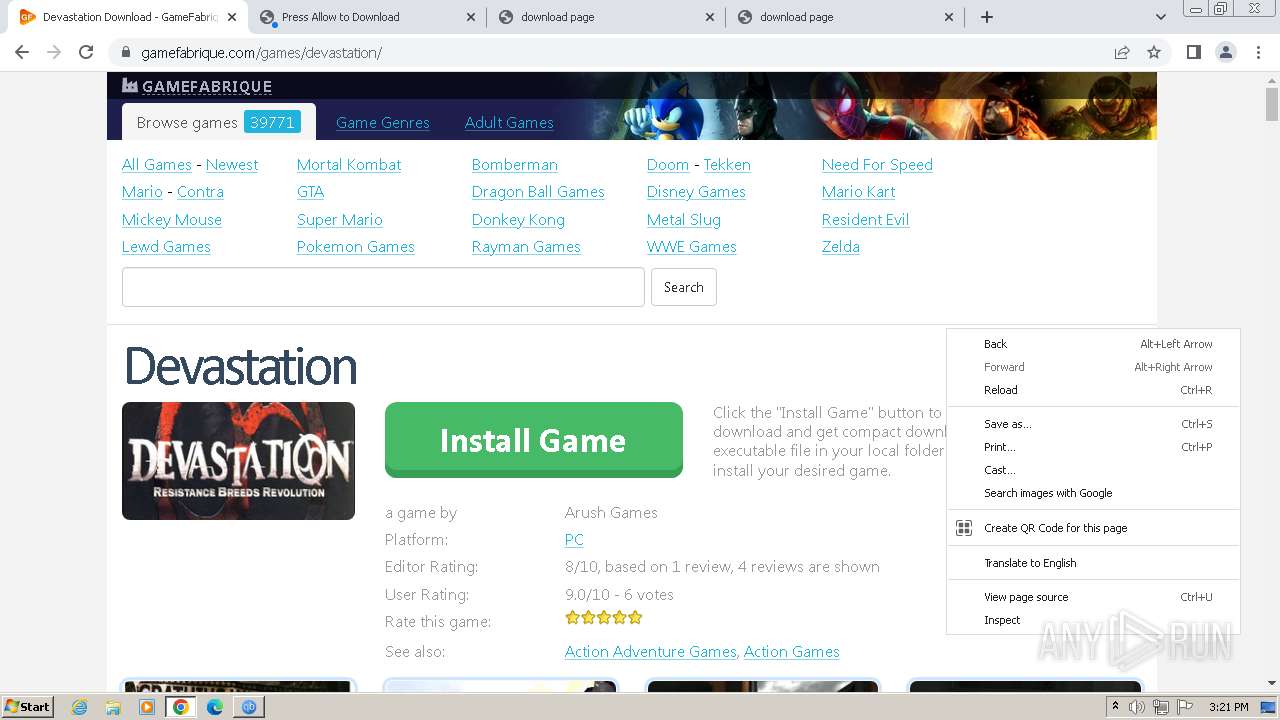
| URL: | https://gamefabrique.com/games/emergency-2-the-ultimate-fight-for-life/ |
| Full analysis: | https://app.any.run/tasks/37827661-3c35-4e26-ba43-7cd043c79375 |
| Verdict: | Malicious activity |
| Analysis date: | April 30, 2024, 14:16:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FCA900AD45ED7186E4BFD44522C42973 |
| SHA1: | BFC2B1495F162769DE069B1BDBE68C29BCB1768B |
| SHA256: | F2EE00EB34ADD190C918B52ED9BD17221802F1CA70A8D69A43E38129F55E9CEF |
| SSDEEP: | 3:N8l0XMUhGGCEIzKtAGc9NA7NMJv:22XMPVec9NAIv |
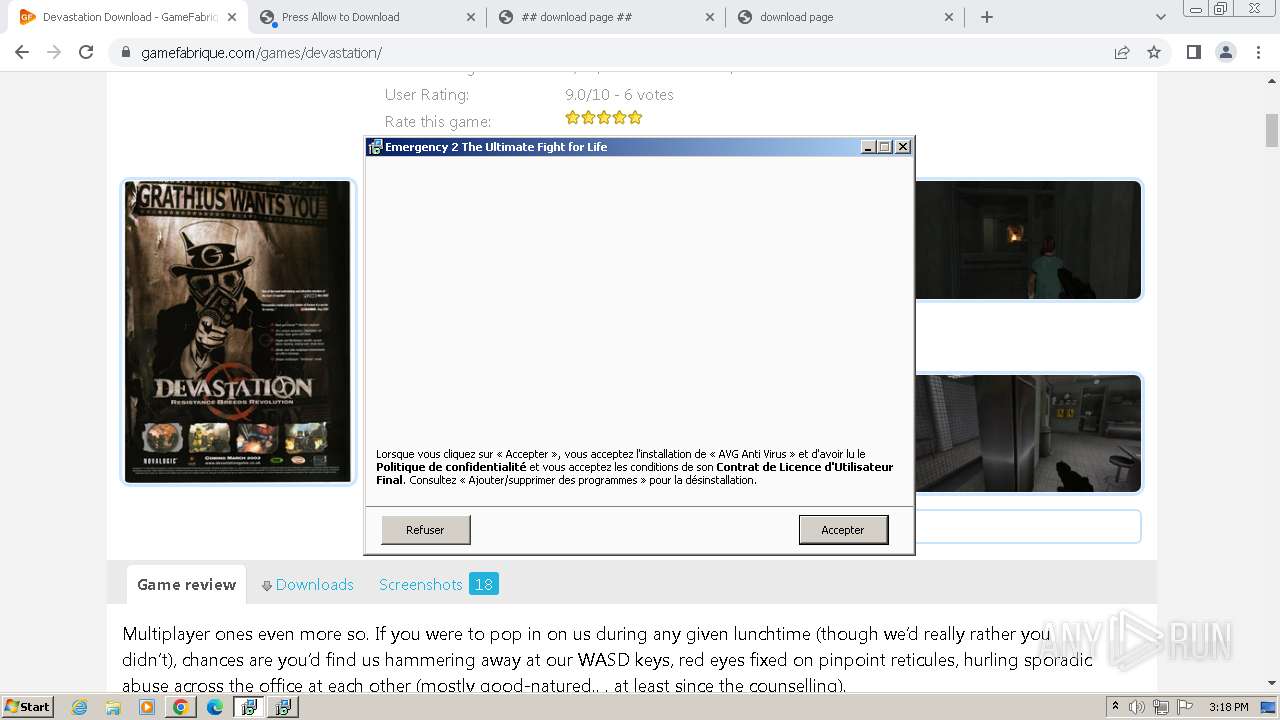
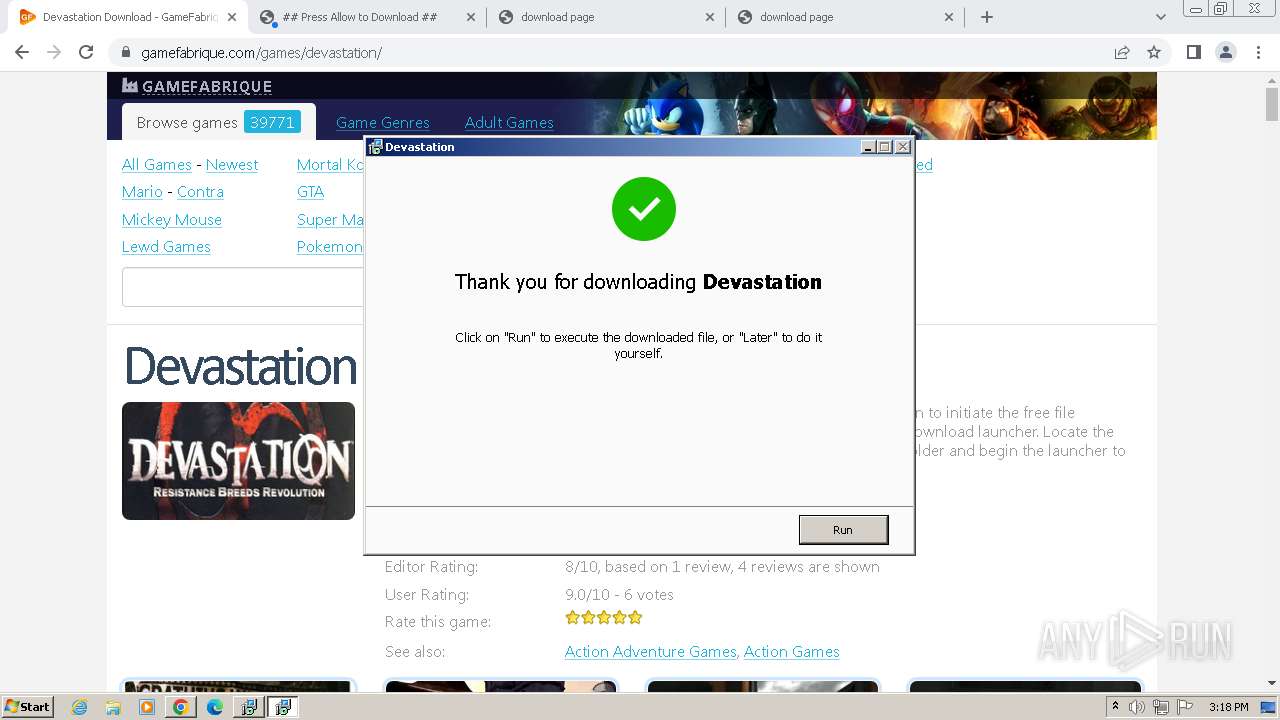
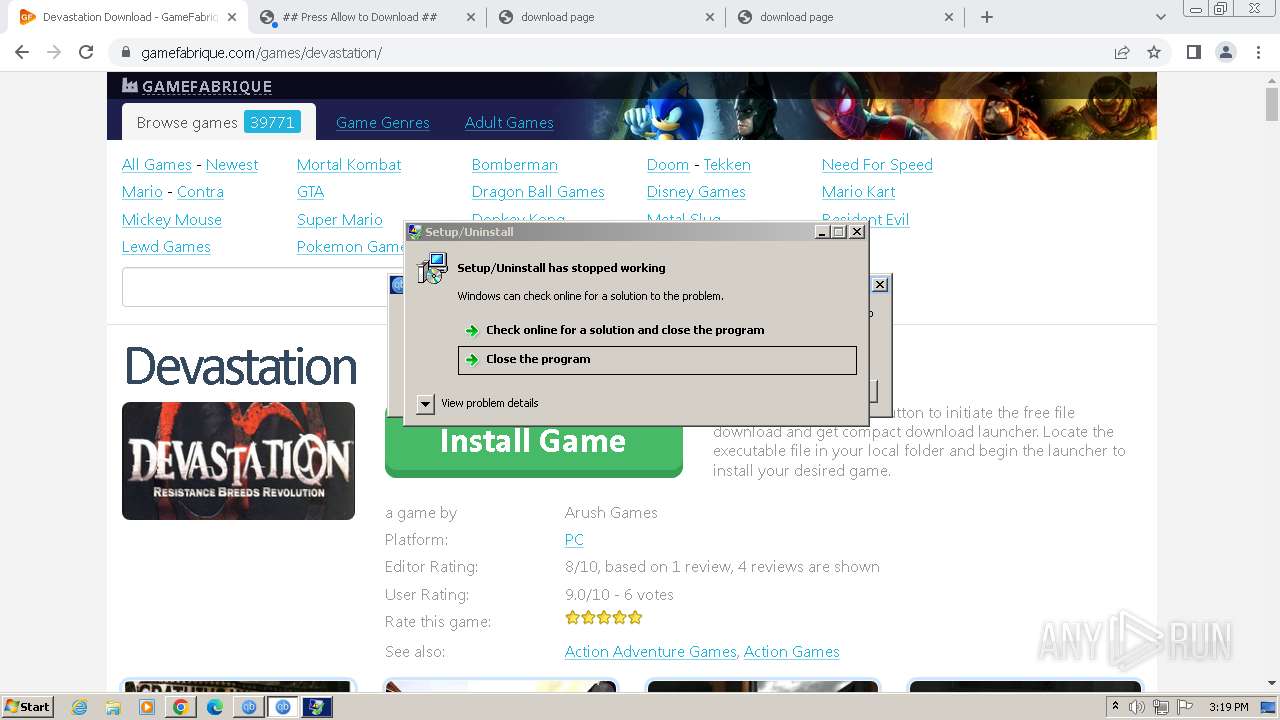
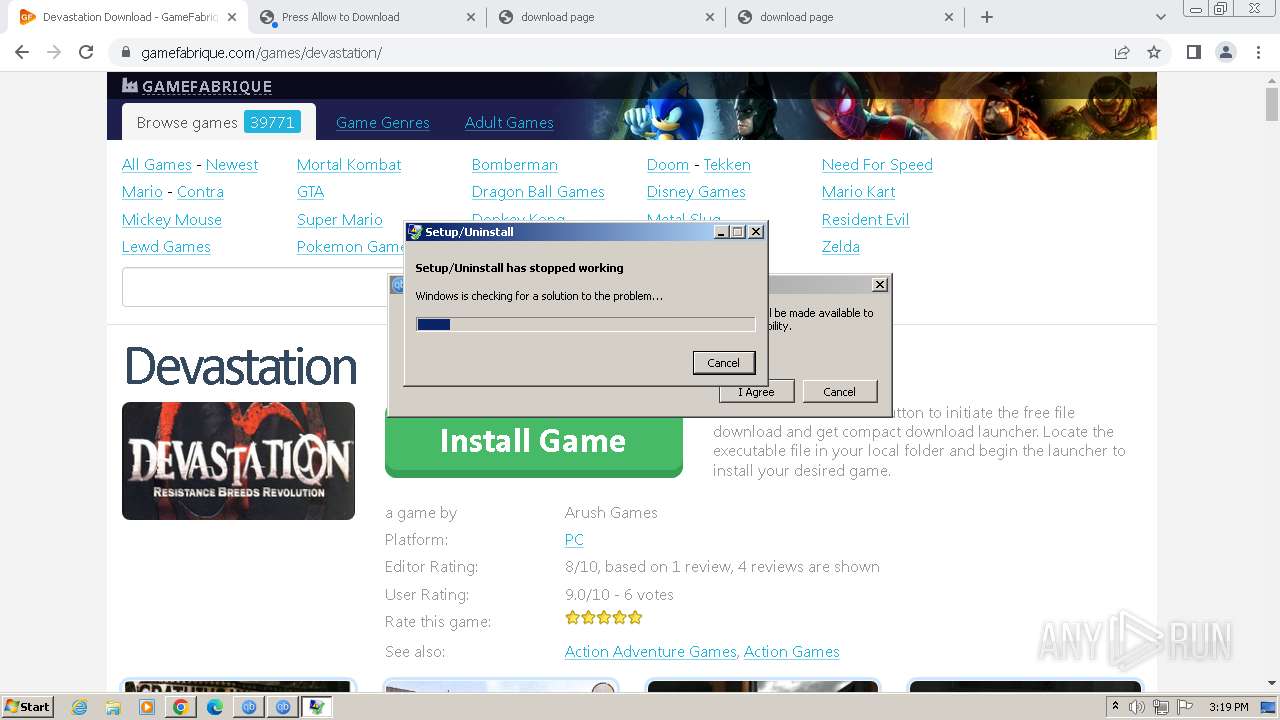
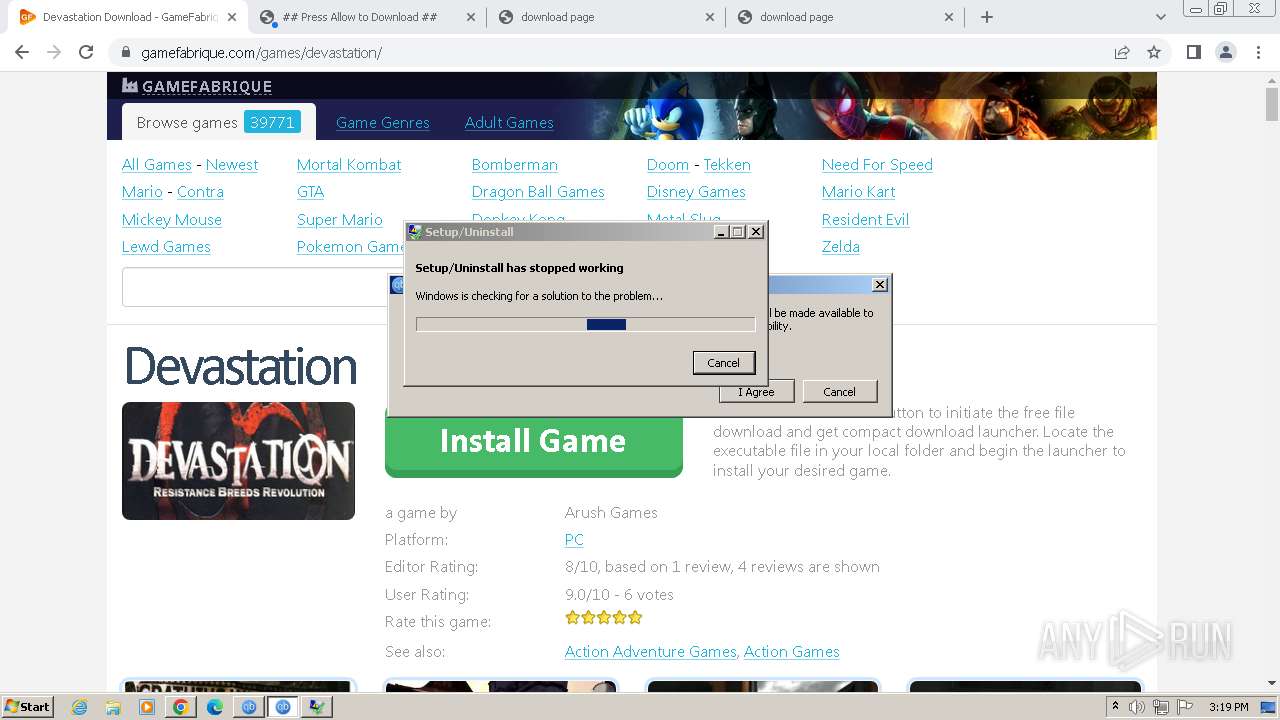
MALICIOUS
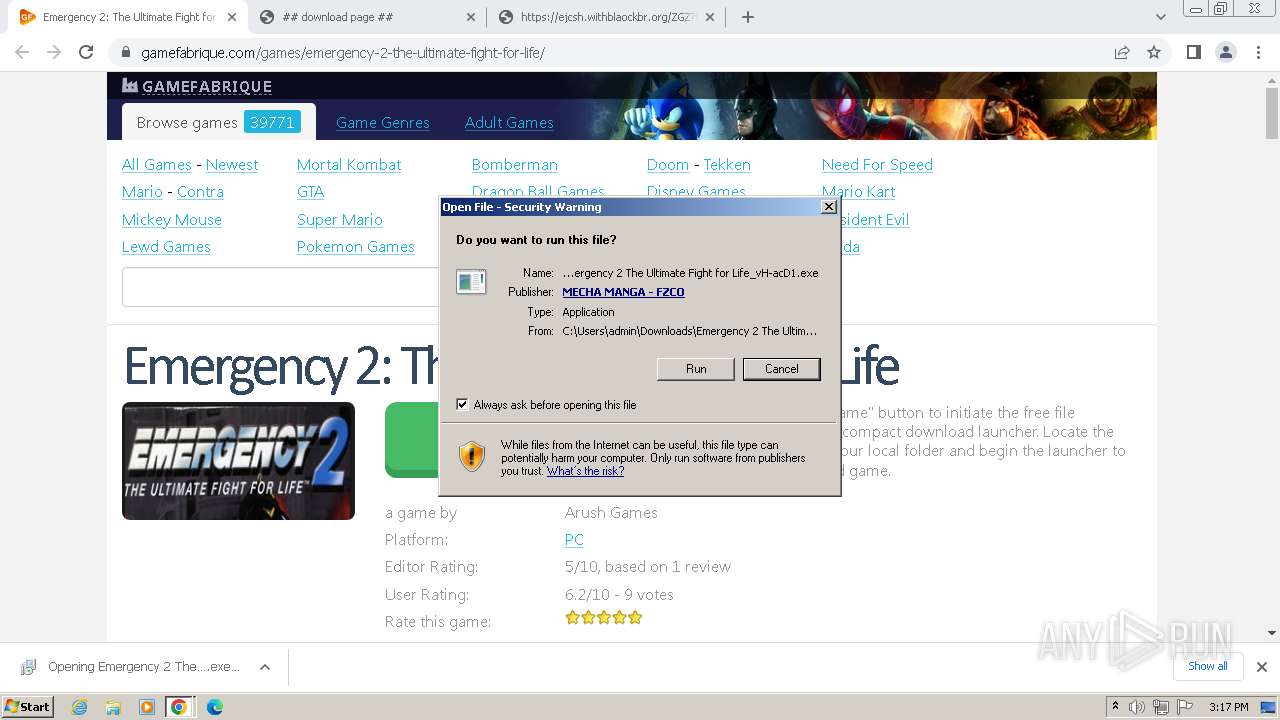
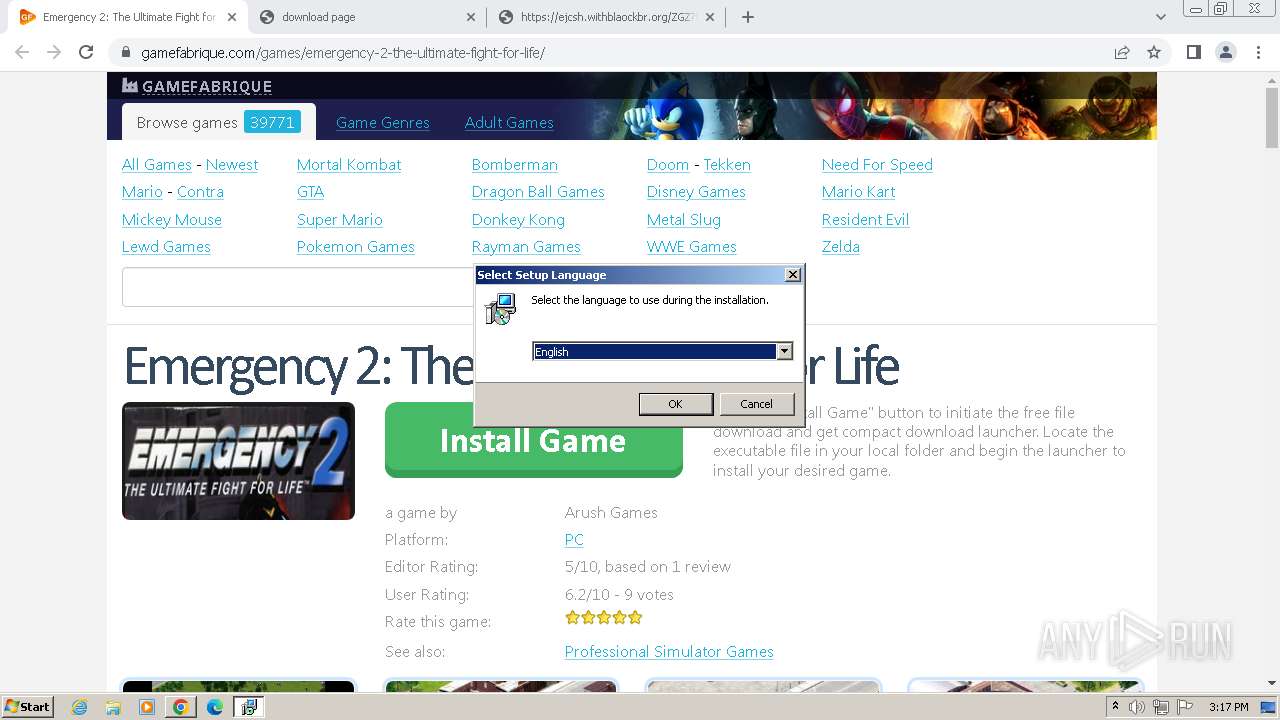
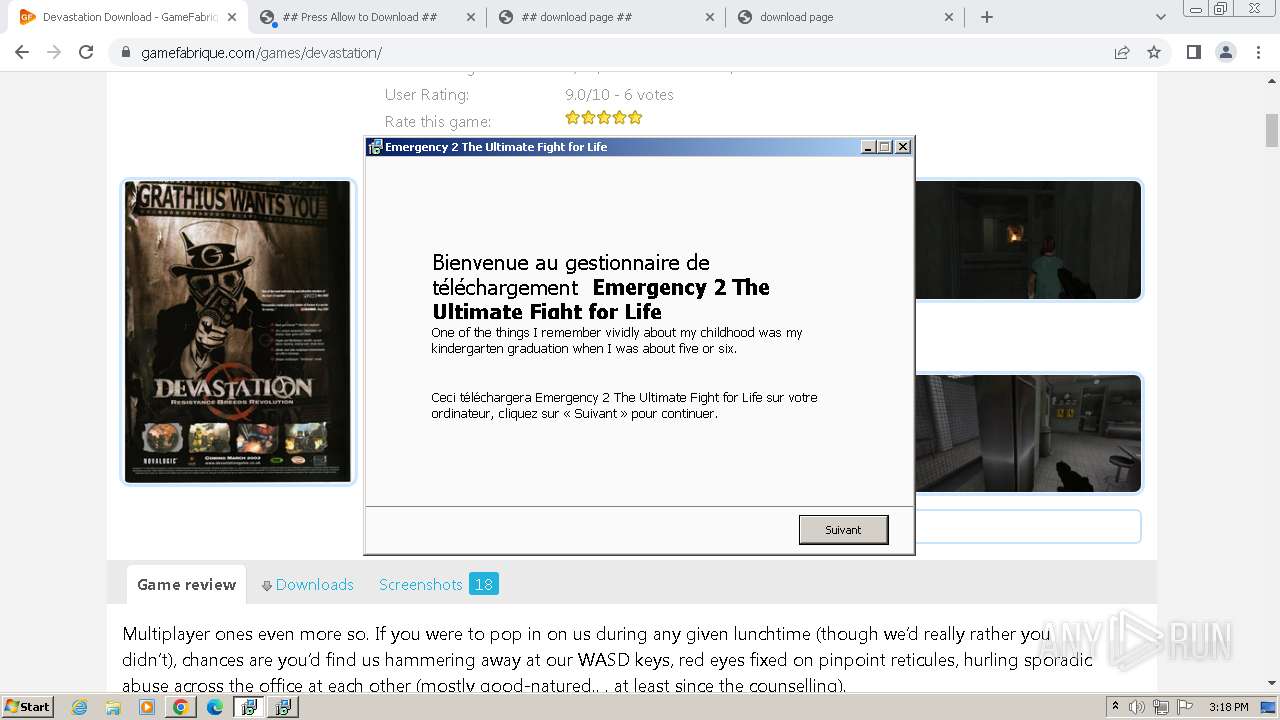
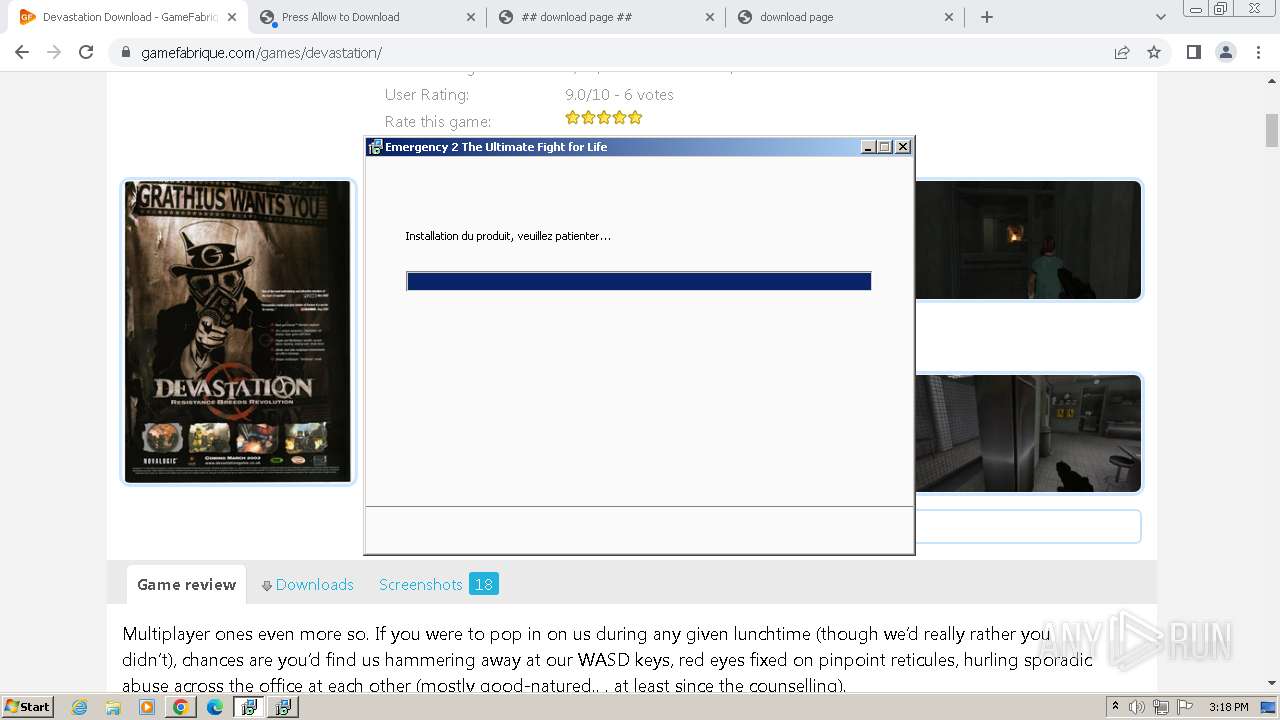
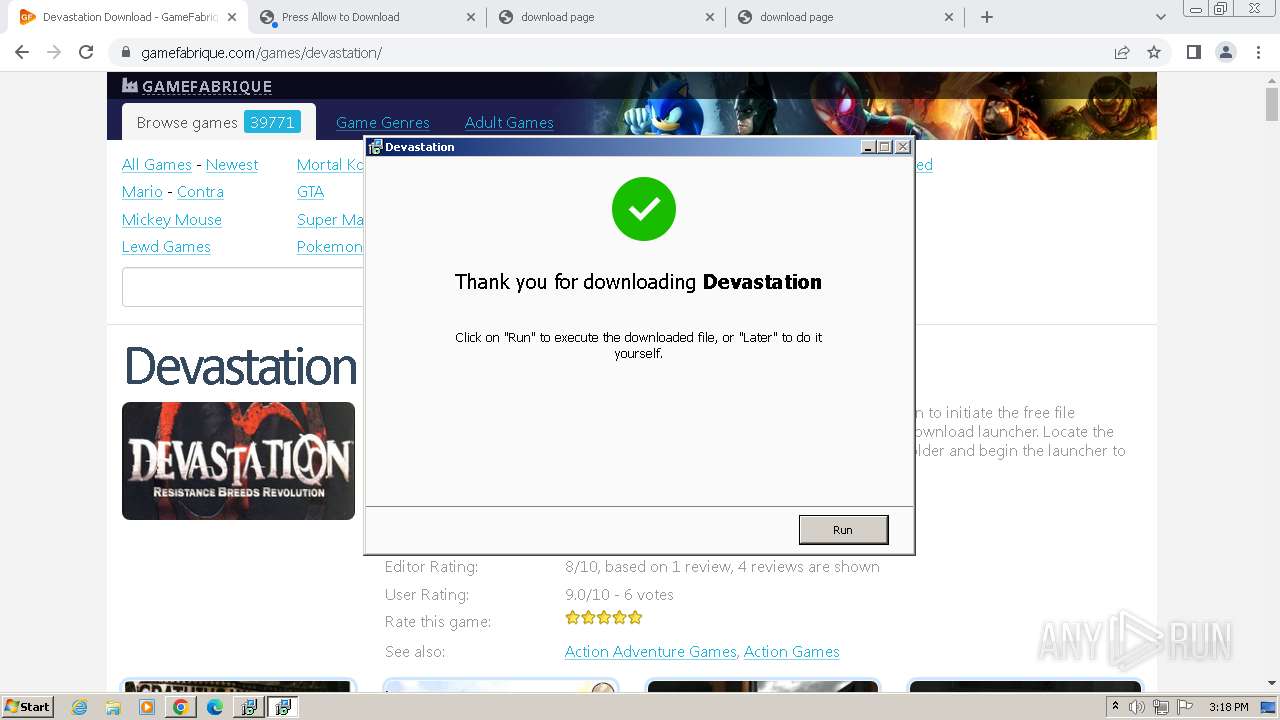
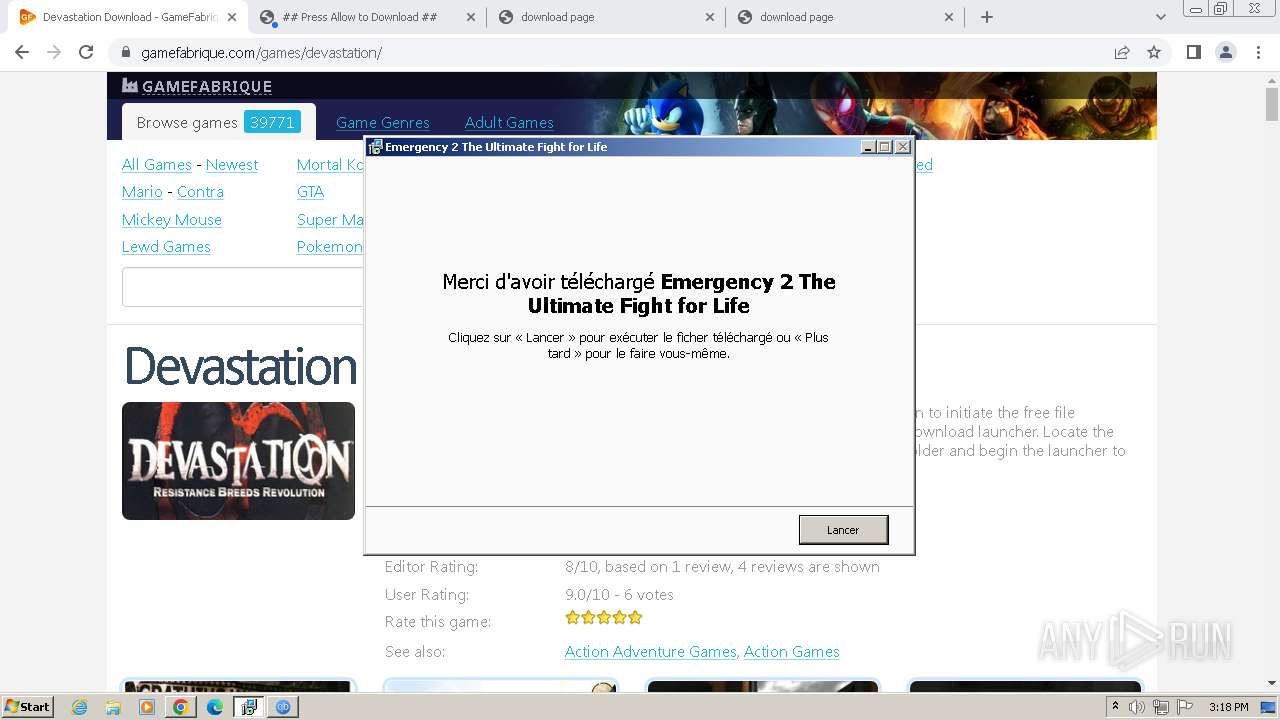
Drops the executable file immediately after the start
- Emergency 2 The Ultimate Fight for Life_vH-acD1.exe (PID: 2928)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.exe (PID: 3056)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
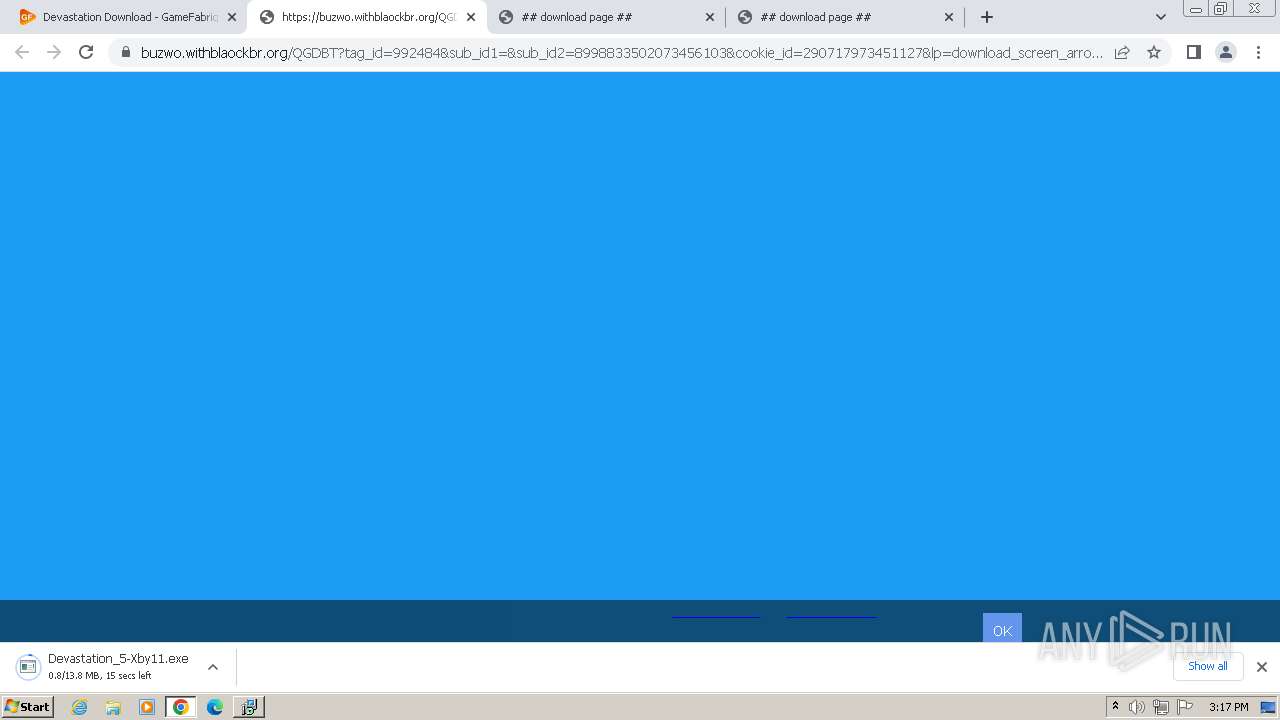
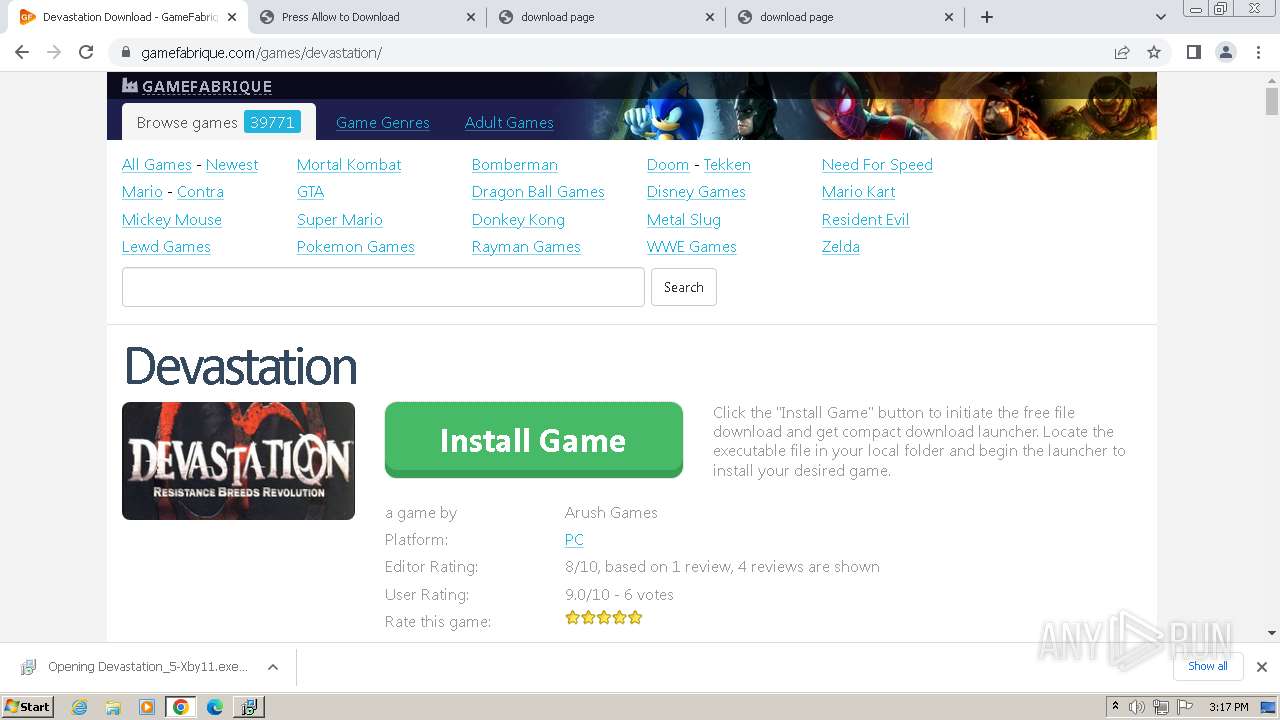
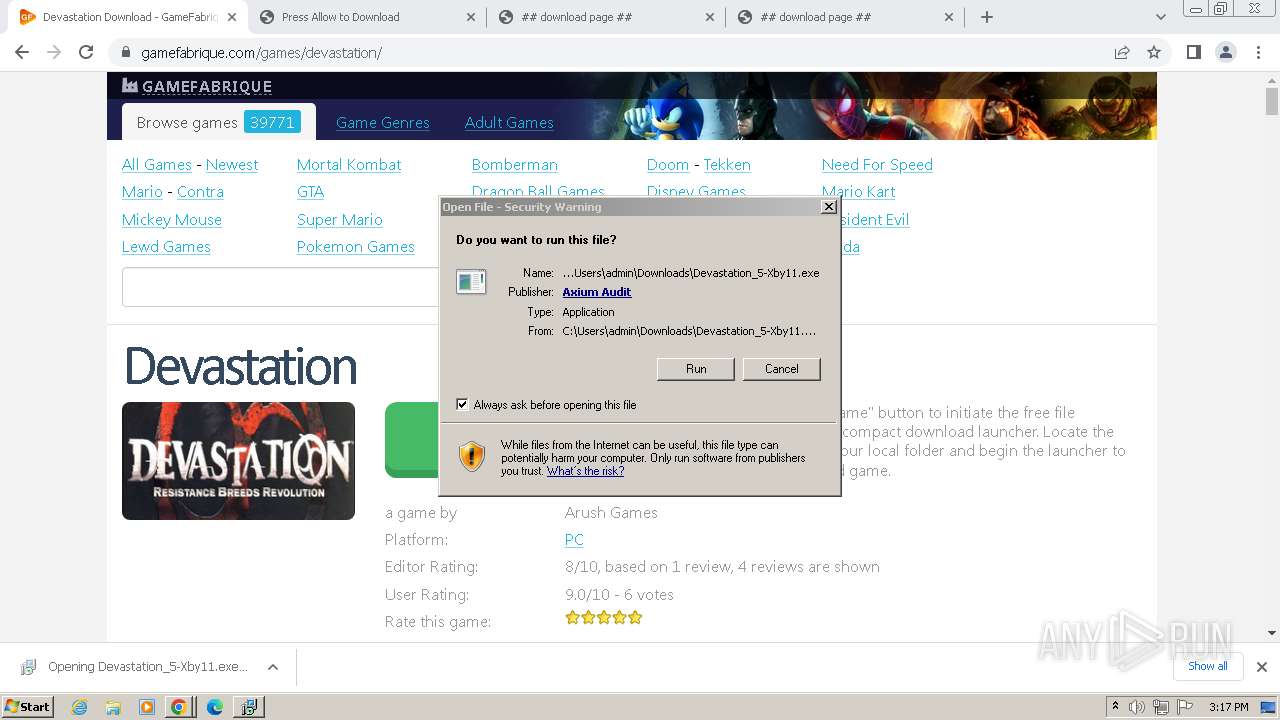
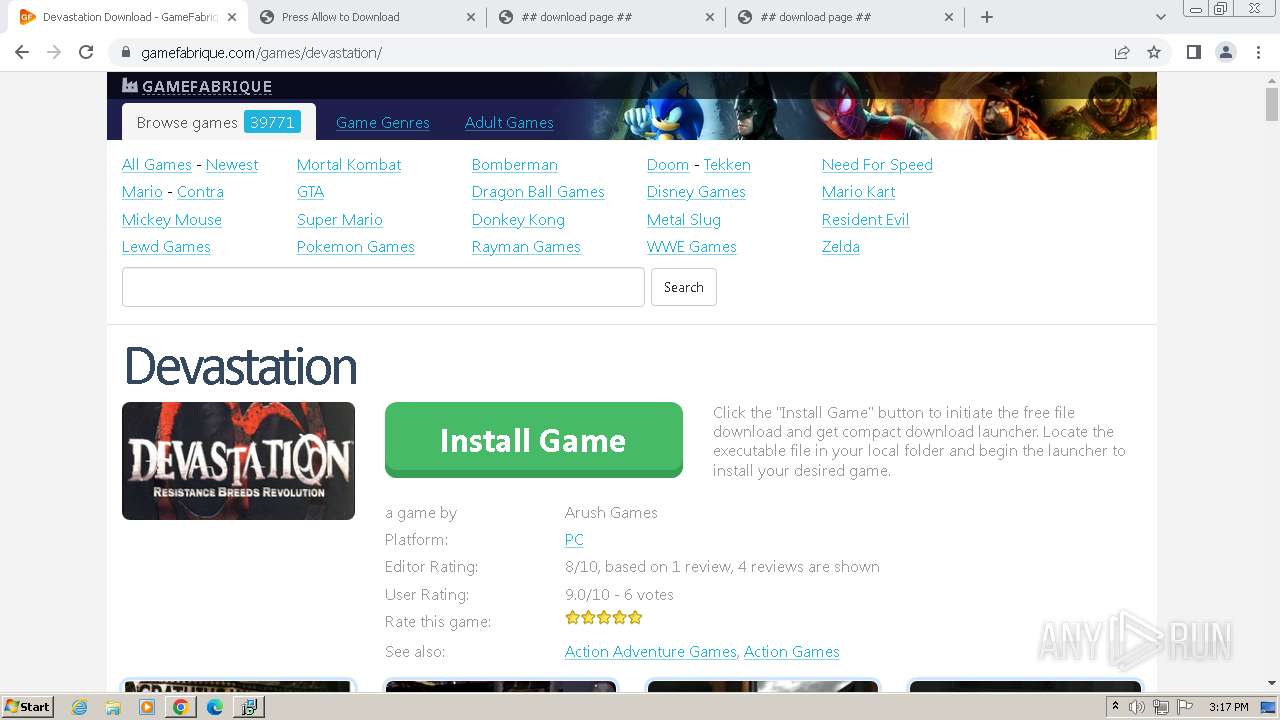
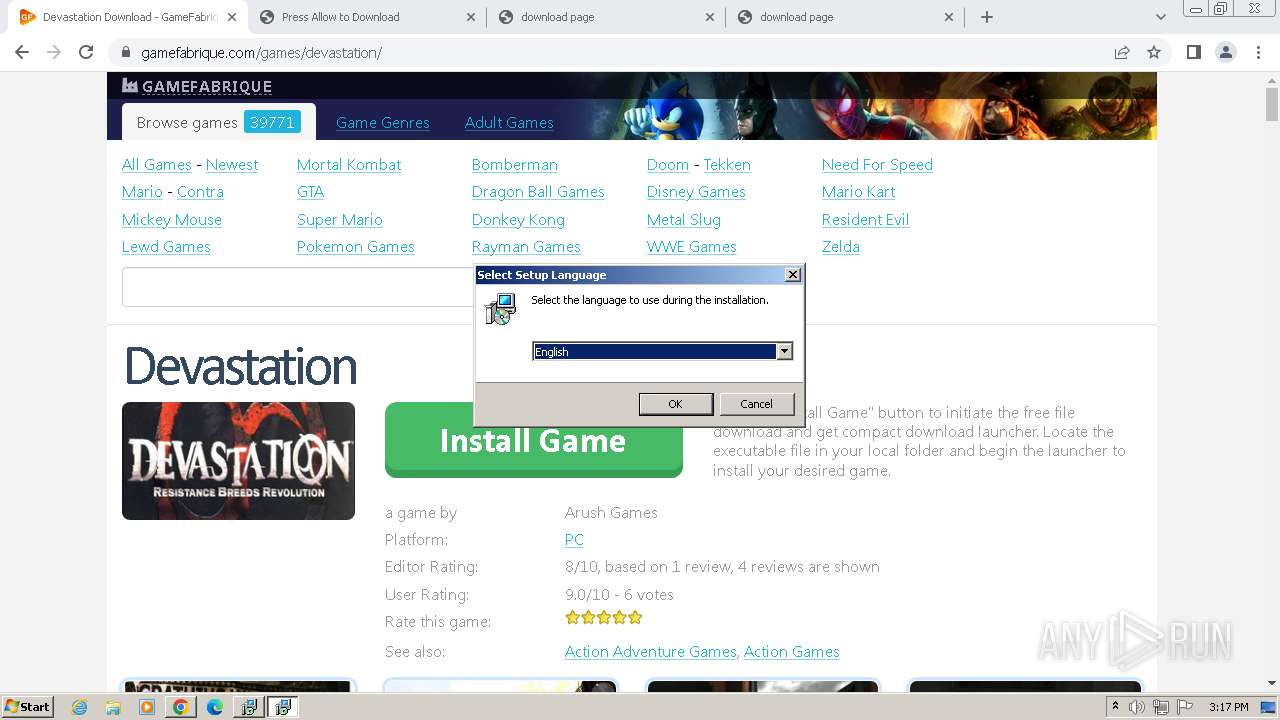
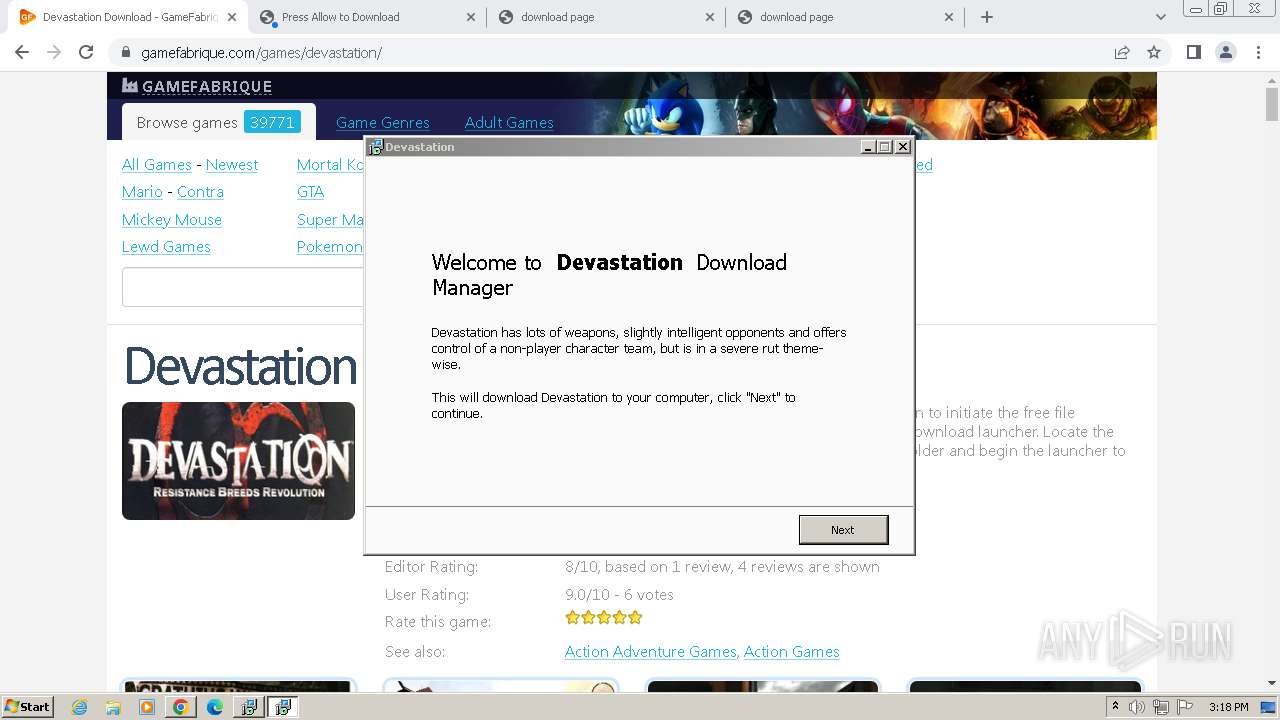
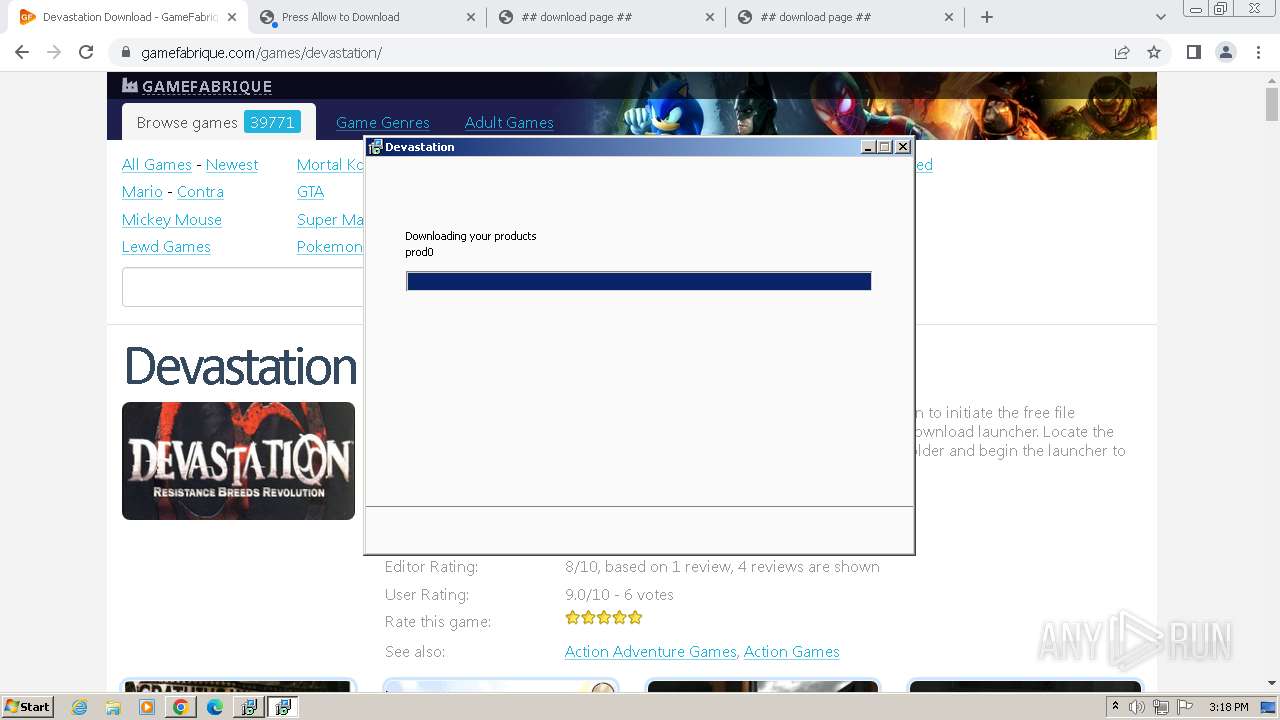
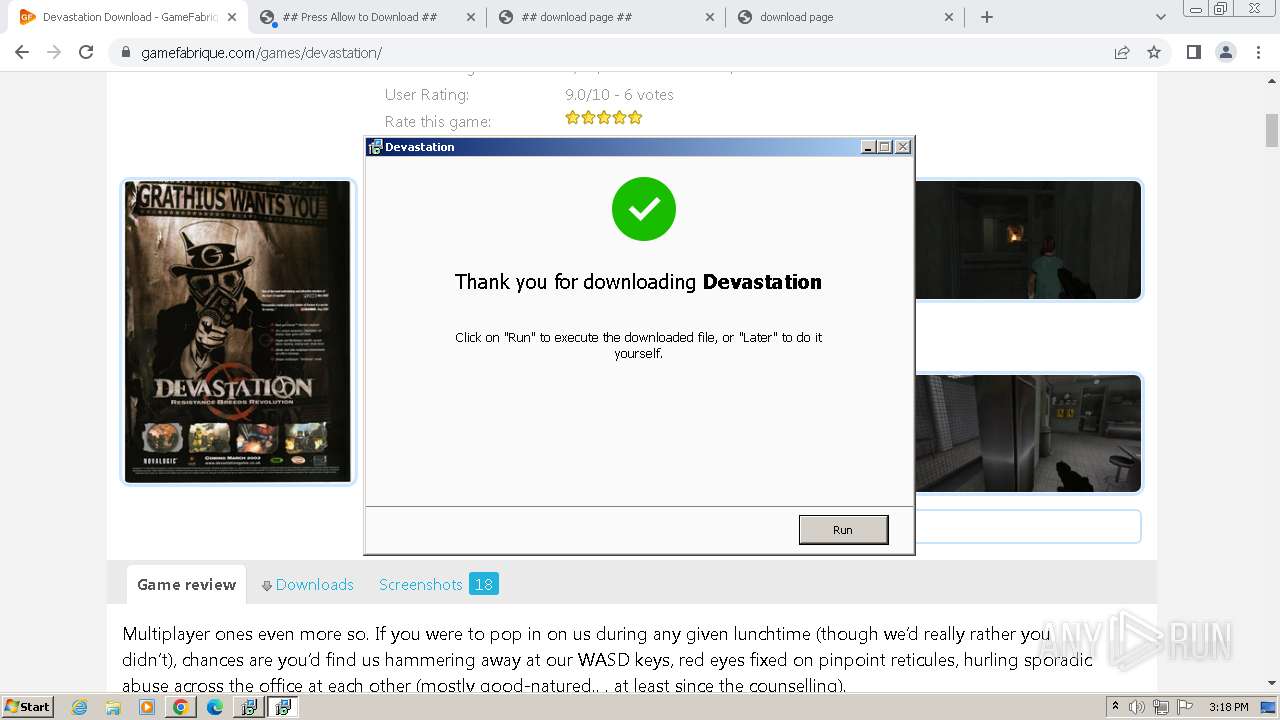
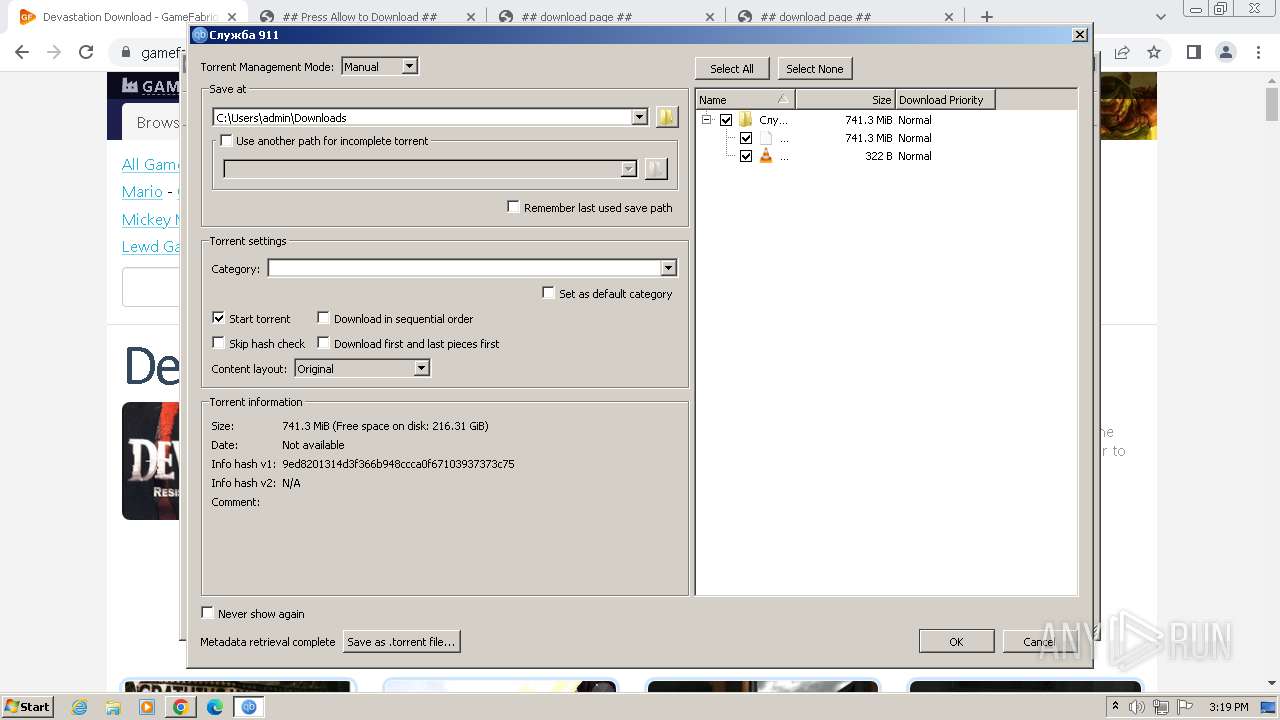
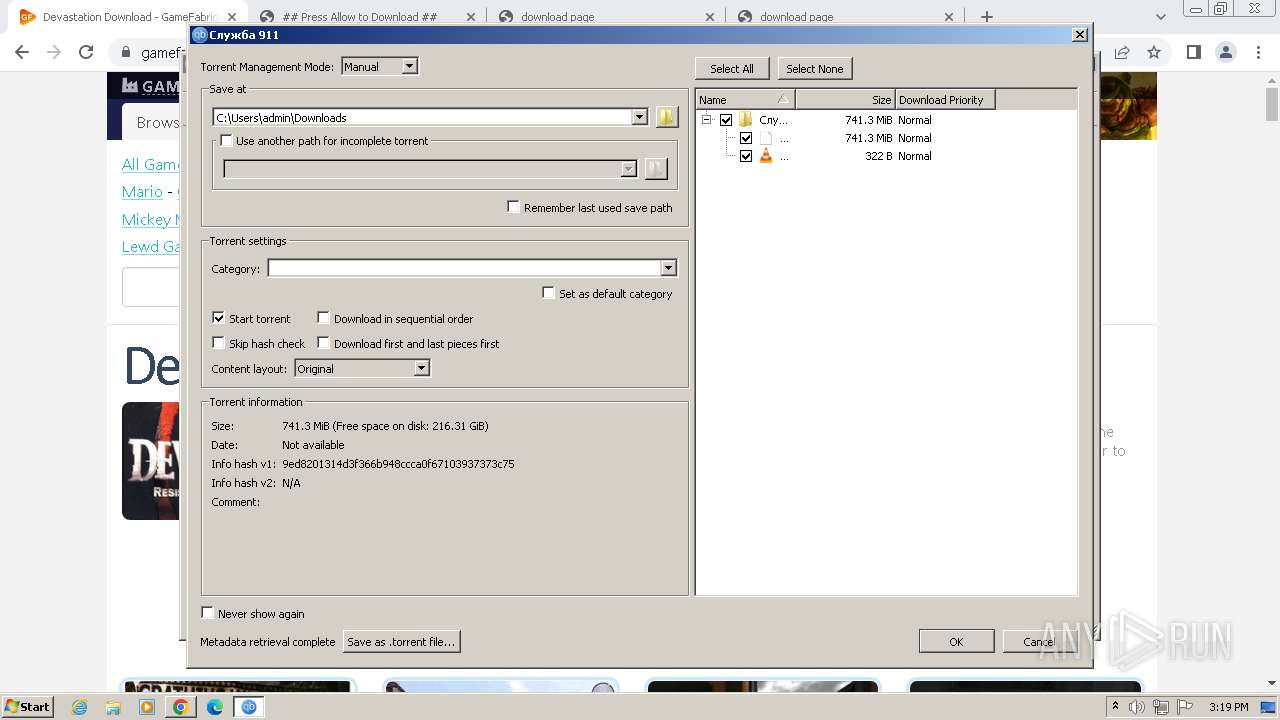
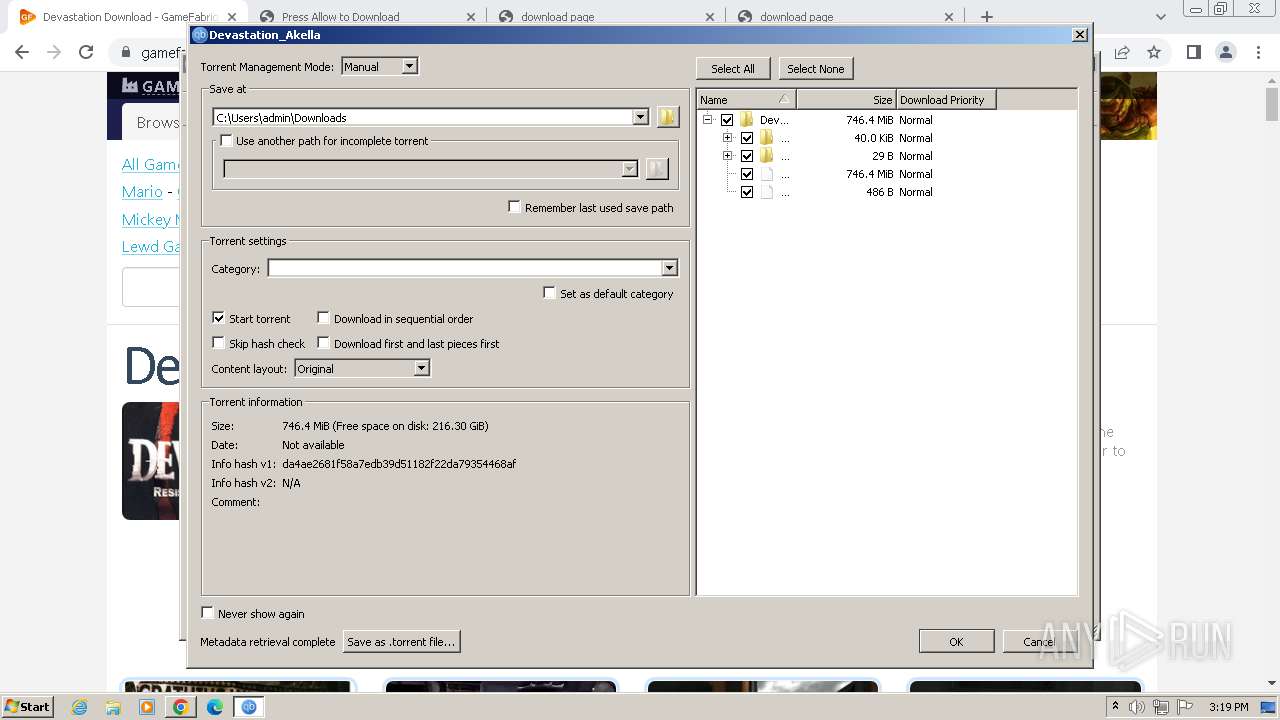
- Devastation_5-Xby11.exe (PID: 1652)
- Devastation_5-Xby11.exe (PID: 1044)
- Devastation_5-Xby11.tmp (PID: 2656)
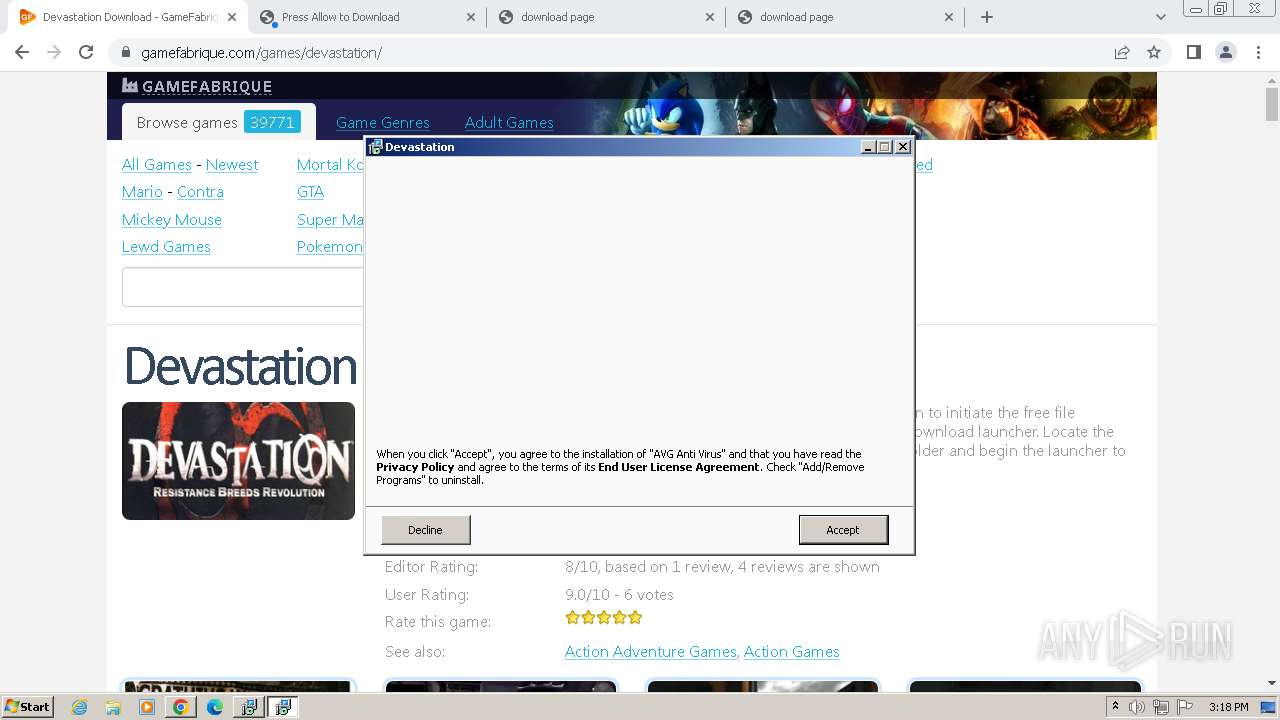
- avg_antivirus_free_setup.exe (PID: 2420)
- avg_antivirus_free_online_setup.exe (PID: 2380)
- icarus.exe (PID: 2424)
- icarus.exe (PID: 936)
- icarus.exe (PID: 1396)
Creates a writable file in the system directory
- icarus.exe (PID: 936)
SUSPICIOUS
Executable content was dropped or overwritten
- Emergency 2 The Ultimate Fight for Life_vH-acD1.exe (PID: 2928)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.exe (PID: 3056)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
- Devastation_5-Xby11.exe (PID: 1652)
- Devastation_5-Xby11.exe (PID: 1044)
- Devastation_5-Xby11.tmp (PID: 2656)
- avg_antivirus_free_setup.exe (PID: 2420)
- avg_antivirus_free_online_setup.exe (PID: 2380)
- icarus.exe (PID: 2424)
- icarus.exe (PID: 936)
- icarus.exe (PID: 1396)
Reads the Windows owner or organization settings
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
- Devastation_5-Xby11.tmp (PID: 2656)
Reads settings of System Certificates
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
- Devastation_5-Xby11.tmp (PID: 2656)
- avg_antivirus_free_setup.exe (PID: 2420)
- avg_antivirus_free_online_setup.exe (PID: 2380)
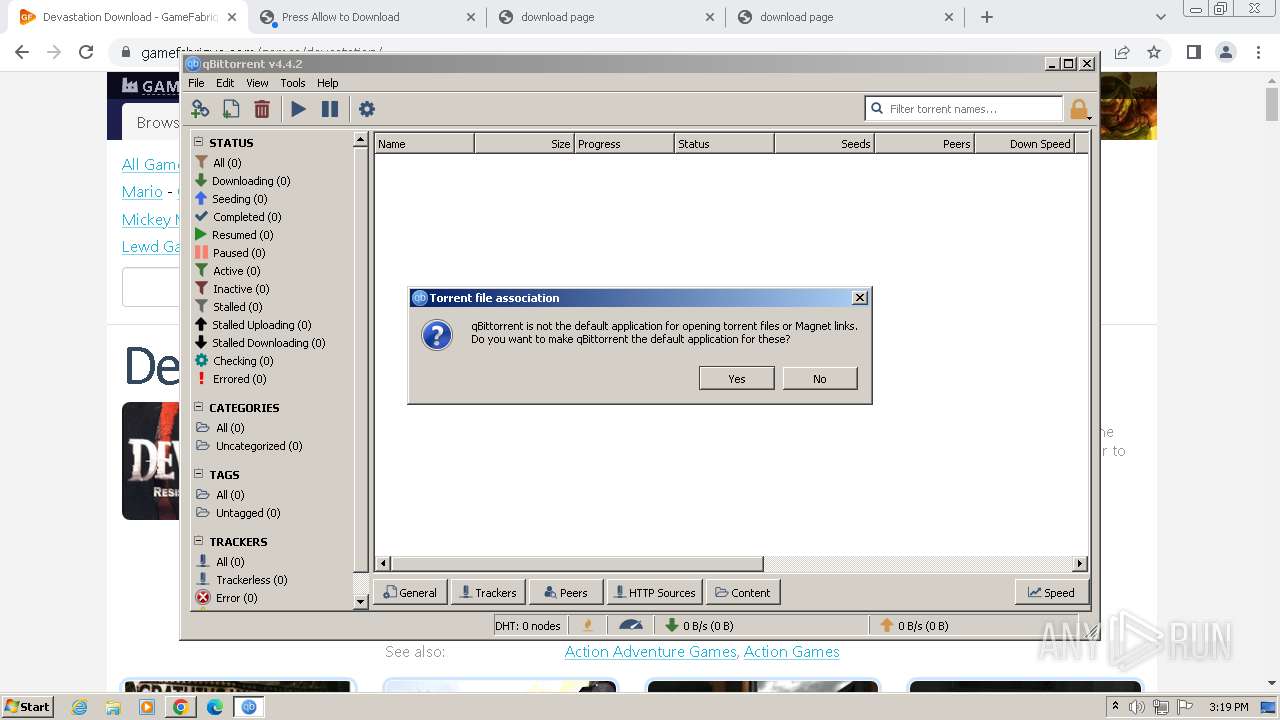
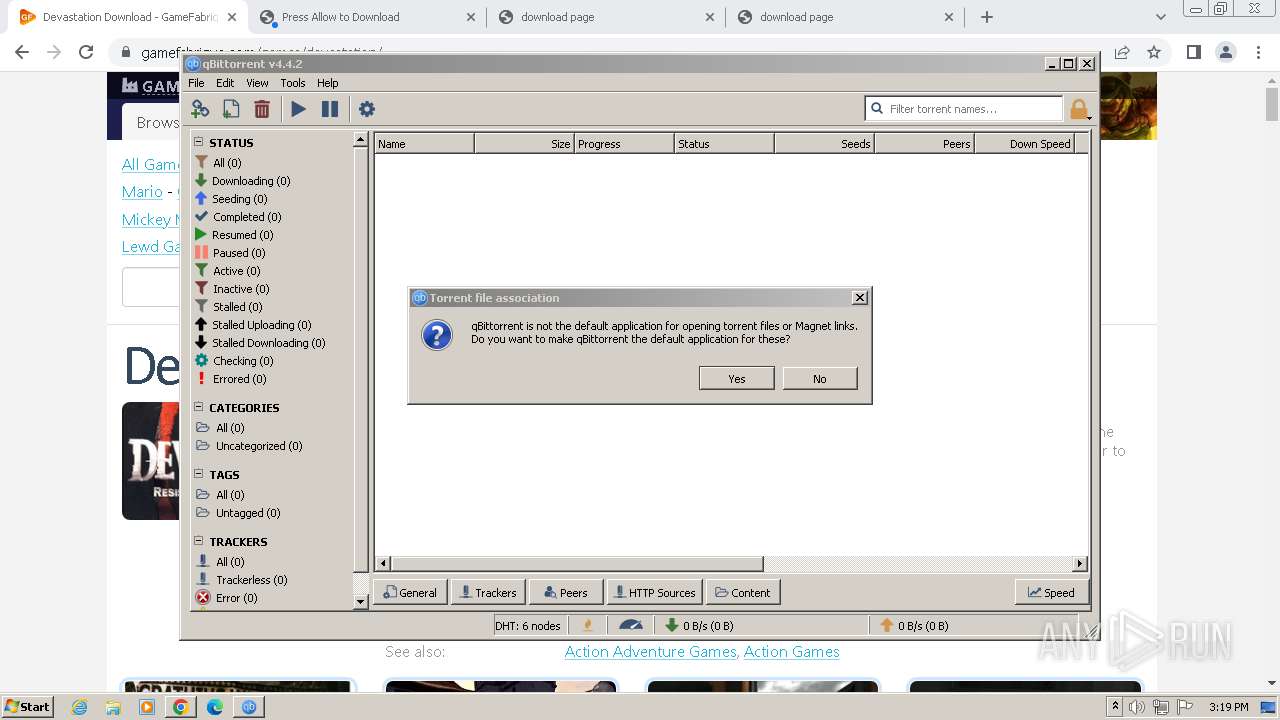
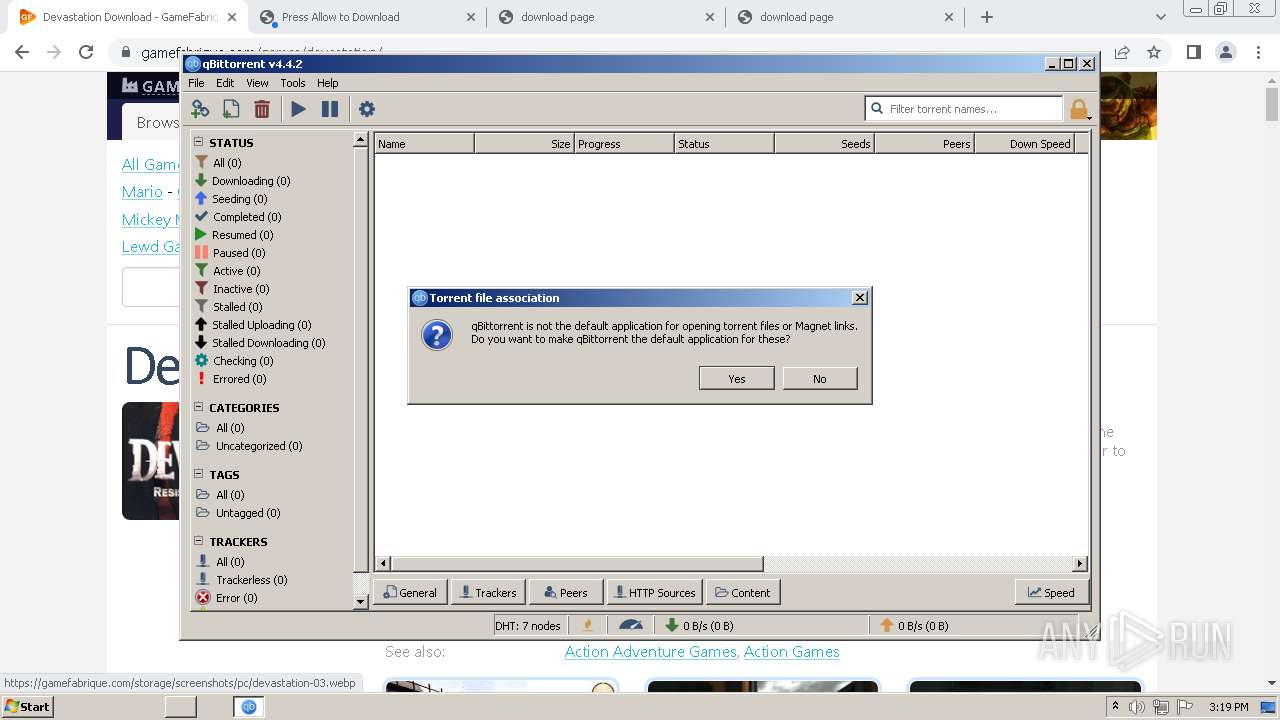
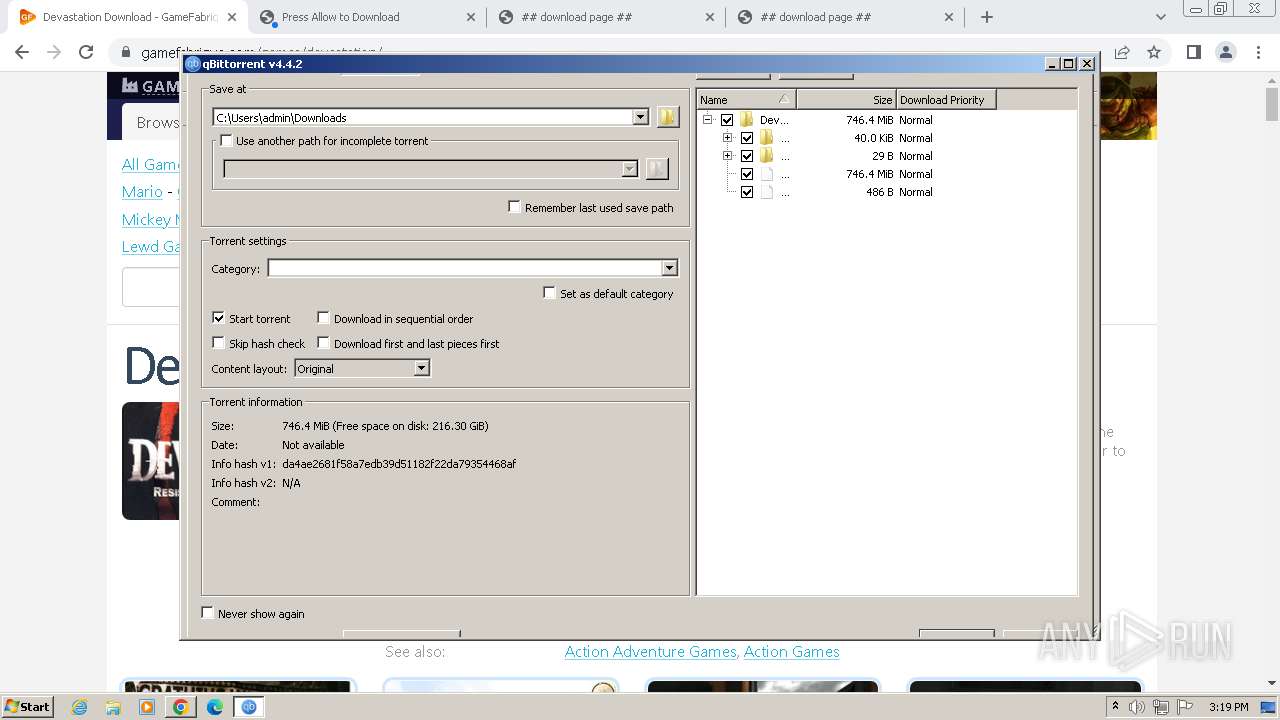
- qbittorrent.exe (PID: 3404)
Reads the Internet Settings
- Devastation_5-Xby11.tmp (PID: 2656)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
Reads security settings of Internet Explorer
- Devastation_5-Xby11.tmp (PID: 2656)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
Starts itself from another location
- icarus.exe (PID: 2424)
The process creates files with name similar to system file names
- icarus.exe (PID: 936)
Uses NETSH.EXE to add a firewall rule or allowed programs
- Devastation_5-Xby11.tmp (PID: 2656)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
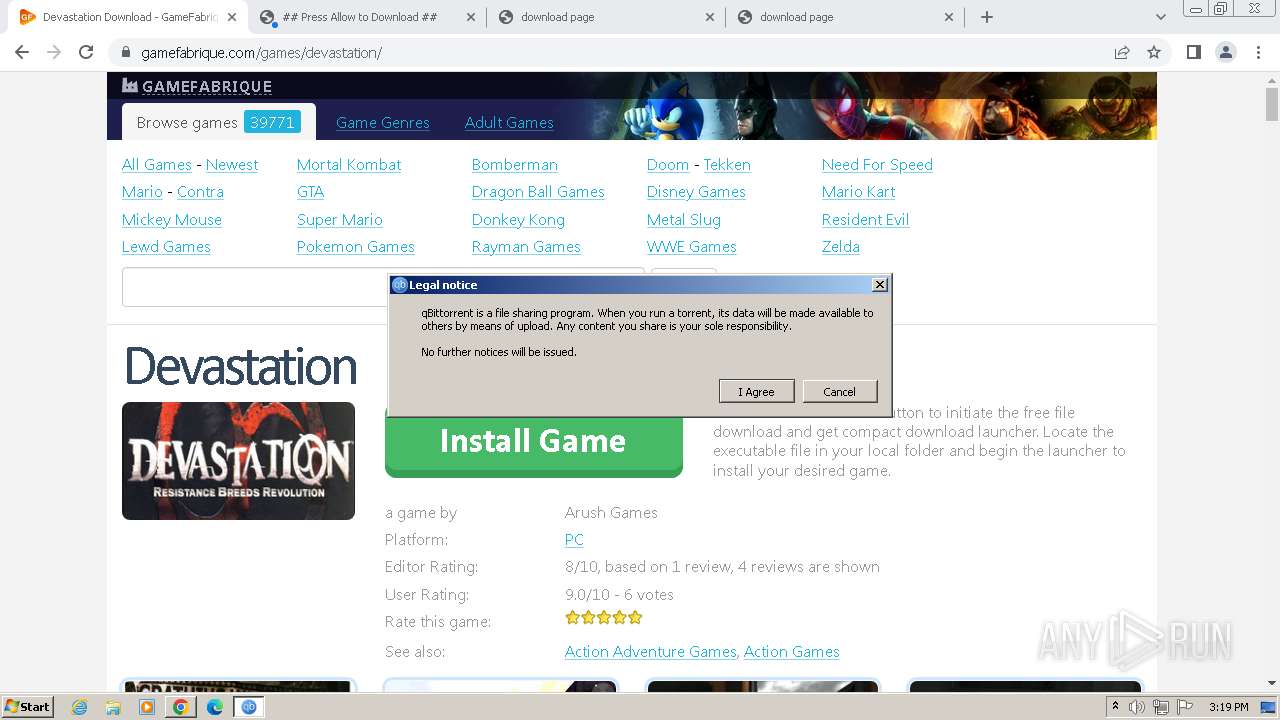
Potential Corporate Privacy Violation
- qbittorrent.exe (PID: 3404)
The process drops C-runtime libraries
- icarus.exe (PID: 936)
Connects to unusual port
- qbittorrent.exe (PID: 3404)
Process drops legitimate windows executable
- icarus.exe (PID: 936)
Drops a system driver (possible attempt to evade defenses)
- icarus.exe (PID: 936)
The process verifies whether the antivirus software is installed
- icarus.exe (PID: 1396)
- icarus.exe (PID: 936)
INFO
Manual execution by a user
- wmpnscfg.exe (PID: 2068)
Reads the computer name
- wmpnscfg.exe (PID: 2068)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2932)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
- Devastation_5-Xby11.tmp (PID: 1604)
- Devastation_5-Xby11.tmp (PID: 2656)
- avg_antivirus_free_setup.exe (PID: 2420)
- avg_antivirus_free_online_setup.exe (PID: 2380)
- icarus.exe (PID: 2424)
- icarus.exe (PID: 1396)
- icarus.exe (PID: 936)
- avg_antivirus_free_setup.exe (PID: 2368)
- qbittorrent.exe (PID: 3404)
- qbittorrent.exe (PID: 2720)
Checks supported languages
- wmpnscfg.exe (PID: 2068)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.exe (PID: 2928)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2932)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.exe (PID: 3056)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
- Devastation_5-Xby11.exe (PID: 1652)
- Devastation_5-Xby11.tmp (PID: 1604)
- Devastation_5-Xby11.exe (PID: 1044)
- Devastation_5-Xby11.tmp (PID: 2656)
- avg_antivirus_free_setup.exe (PID: 2420)
- avg_antivirus_free_online_setup.exe (PID: 2380)
- icarus.exe (PID: 2424)
- icarus.exe (PID: 1396)
- icarus.exe (PID: 936)
- avg_antivirus_free_setup.exe (PID: 2368)
- qbittorrent.exe (PID: 3404)
- qbittorrent.exe (PID: 2720)
Connects to unusual port
- chrome.exe (PID: 2108)
Create files in a temporary directory
- Emergency 2 The Ultimate Fight for Life_vH-acD1.exe (PID: 3056)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.exe (PID: 2928)
- Devastation_5-Xby11.exe (PID: 1652)
- Devastation_5-Xby11.exe (PID: 1044)
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
- Devastation_5-Xby11.tmp (PID: 2656)
- avg_antivirus_free_online_setup.exe (PID: 2380)
- icarus.exe (PID: 2424)
- icarus.exe (PID: 936)
- icarus.exe (PID: 1396)
The process uses the downloaded file
- chrome.exe (PID: 3964)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 3380)
Drops the executable file immediately after the start
- chrome.exe (PID: 3964)
- chrome.exe (PID: 920)
- chrome.exe (PID: 2124)
Executable content was dropped or overwritten
- chrome.exe (PID: 3964)
- chrome.exe (PID: 920)
- chrome.exe (PID: 2124)
Application launched itself
- chrome.exe (PID: 3964)
Reads the software policy settings
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
- Devastation_5-Xby11.tmp (PID: 2656)
- avg_antivirus_free_setup.exe (PID: 2420)
- avg_antivirus_free_online_setup.exe (PID: 2380)
Reads the machine GUID from the registry
- Emergency 2 The Ultimate Fight for Life_vH-acD1.tmp (PID: 2976)
- Devastation_5-Xby11.tmp (PID: 2656)
- avg_antivirus_free_setup.exe (PID: 2420)
- avg_antivirus_free_online_setup.exe (PID: 2380)
- icarus.exe (PID: 2424)
- icarus.exe (PID: 936)
- icarus.exe (PID: 1396)
- qbittorrent.exe (PID: 3404)
- qbittorrent.exe (PID: 2720)
Creates files in the program directory
- avg_antivirus_free_online_setup.exe (PID: 2380)
- icarus.exe (PID: 2424)
- icarus.exe (PID: 936)
- icarus.exe (PID: 1396)
Reads CPU info
- icarus.exe (PID: 2424)
- icarus.exe (PID: 1396)
- icarus.exe (PID: 936)
Dropped object may contain TOR URL's
- icarus.exe (PID: 2424)
- icarus.exe (PID: 936)
- icarus.exe (PID: 1396)
Reads Environment values
- icarus.exe (PID: 936)
Creates files or folders in the user directory
- qbittorrent.exe (PID: 3404)
- qbittorrent.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
98
Monitored processes
52
Malicious processes
12
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3100 --field-trial-handle=1156,i,9399700953726788011,4656143776798769722,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3564 --field-trial-handle=1156,i,9399700953726788011,4656143776798769722,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3996 --field-trial-handle=1156,i,9399700953726788011,4656143776798769722,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2016 --field-trial-handle=1156,i,9399700953726788011,4656143776798769722,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3464 --field-trial-handle=1156,i,9399700953726788011,4656143776798769722,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3012 --field-trial-handle=1156,i,9399700953726788011,4656143776798769722,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1104 --field-trial-handle=1156,i,9399700953726788011,4656143776798769722,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 936 | C:\Windows\Temp\asw-fc707be9-8f4e-4697-991d-5516b85317bc\avg-av\icarus.exe /silent /ws /psh:92pTu5fa59EutsMXso2zfiTUDyR3CCa0R1yhhas8gK4moxm69DsTcnpvCiDeElO3Ko7ImzSjz74CcS /cookie:mmm_irs_ppi_902_451_o /edat_dir:C:\Windows\Temp\asw.b3bbd05e8851634c /track-guid:c1225a32-edd7-4d7d-ad00-bf8a5278c570 /er_master:master_ep_8149e4ea-cf45-46cc-ae2e-59cb8f488db2 /er_ui:ui_ep_b75c8269-cf36-4ac5-aa57-3051b3abf994 /er_slave:avg-av_slave_ep_240f2a31-2e2e-445a-b090-87270050eca6 /slave:avg-av | C:\Windows\Temp\asw-fc707be9-8f4e-4697-991d-5516b85317bc\avg-av\icarus.exe | icarus.exe | ||||||||||||
User: admin Company: AVG Technologies Integrity Level: HIGH Description: AVG Installer Version: 24.4.7245.0 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3600 --field-trial-handle=1156,i,9399700953726788011,4656143776798769722,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --mojo-platform-channel-handle=4648 --field-trial-handle=1156,i,9399700953726788011,4656143776798769722,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
46 811
Read events
46 219
Write events
566
Delete events
26
Modification events
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
459
Suspicious files
689
Text files
309
Unknown types
97
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF105f96.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF1063ec.TMP | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:FF6BABA737D50E515029C3F3A1305BBC | SHA256:670EED15EAA8E3F1A4F8612B229654EB0C64107AEAF0B1017E4BD45E3F7EED83 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF106c0a.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF107baa.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
410
DNS requests
128
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2108 | chrome.exe | 142.251.168.84:443 | accounts.google.com | GOOGLE | US | unknown |
3964 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2108 | chrome.exe | 104.21.37.165:443 | gamefabrique.com | CLOUDFLARENET | — | unknown |
2108 | chrome.exe | 172.217.18.104:443 | www.googletagmanager.com | GOOGLE | US | unknown |
2108 | chrome.exe | 142.250.185.74:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
2108 | chrome.exe | 104.18.10.207:443 | stackpath.bootstrapcdn.com | CLOUDFLARENET | — | unknown |
2108 | chrome.exe | 18.66.137.137:443 | d1pdf4c3hchi80.cloudfront.net | AMAZON-02 | US | unknown |
2108 | chrome.exe | 216.239.36.178:443 | www.google-analytics.com | GOOGLE | US | unknown |
2108 | chrome.exe | 188.114.97.3:443 | pogothere.xyz | CLOUDFLARENET | NL | unknown |
2108 | chrome.exe | 104.21.83.210:443 | ightsapph.info | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
gamefabrique.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
d1pdf4c3hchi80.cloudfront.net |
| unknown |
www.google-analytics.com |
| whitelisted |
pogothere.xyz |
| unknown |
getrunkhomuto.info |
| unknown |
ightsapph.info |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3404 | qbittorrent.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT announce_peers request |
Process | Message |
|---|---|
qbittorrent.exe | QObject::startTimer: Timers cannot have negative intervals
|