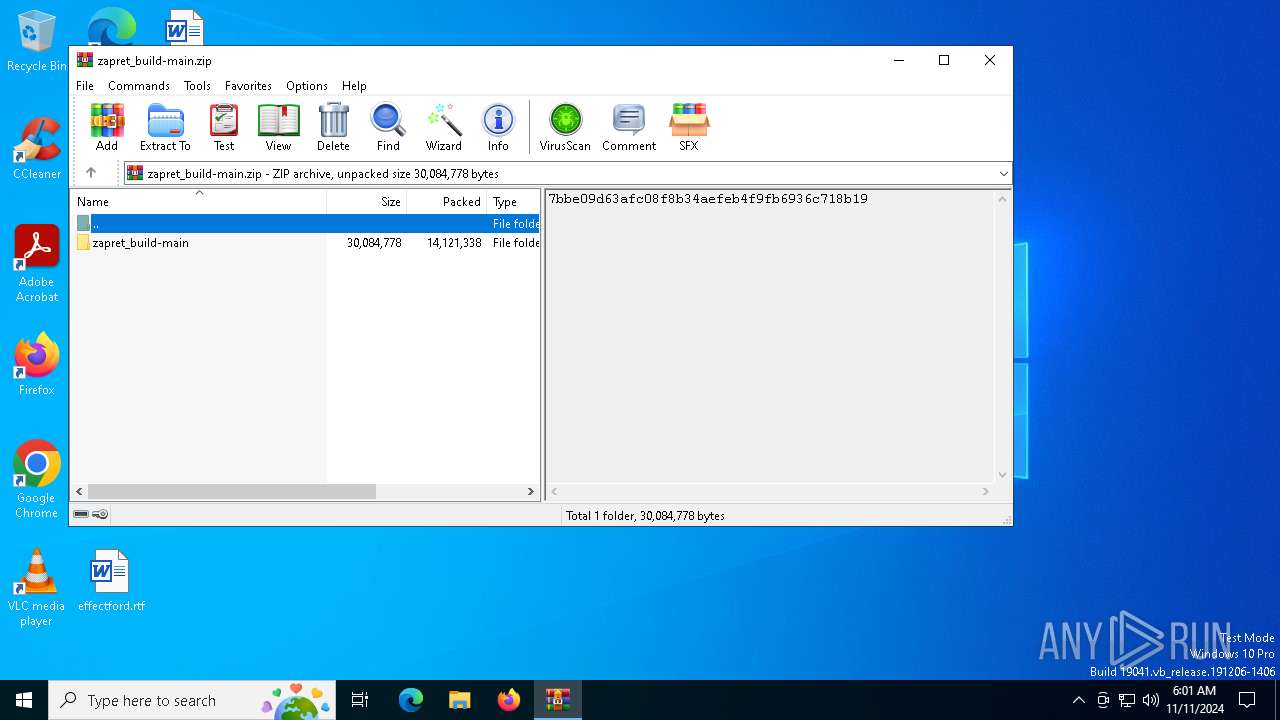
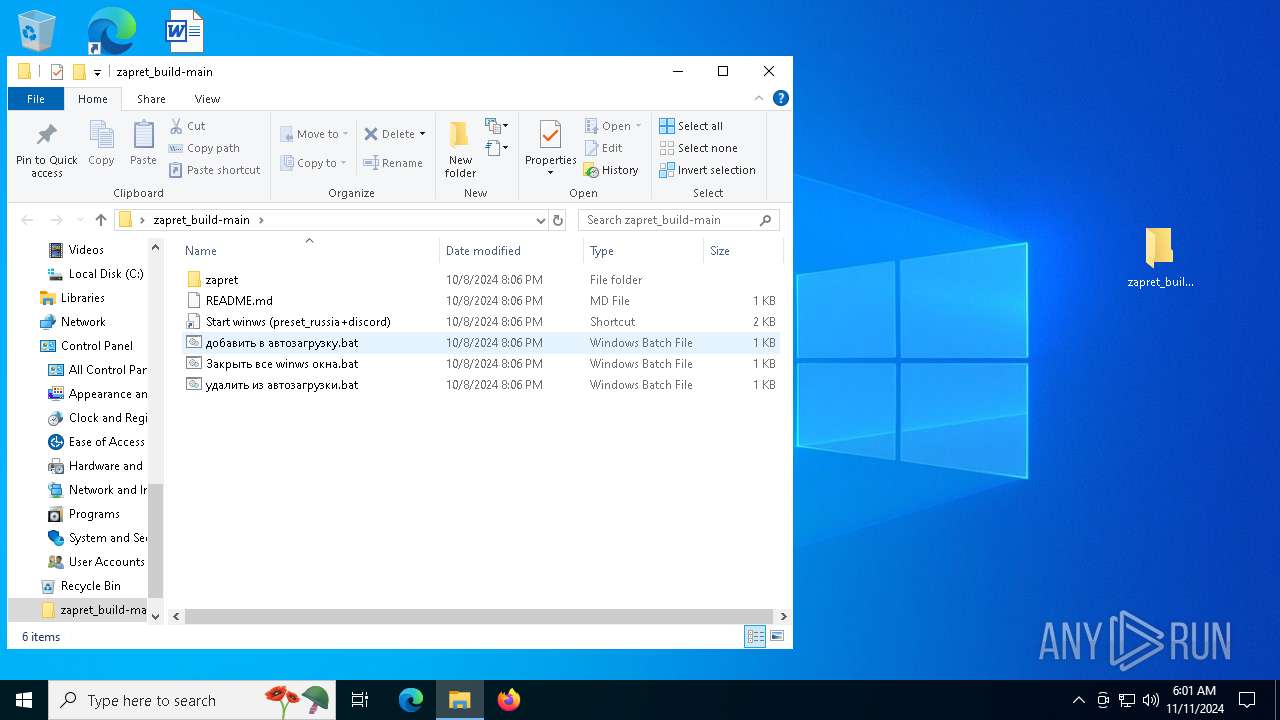
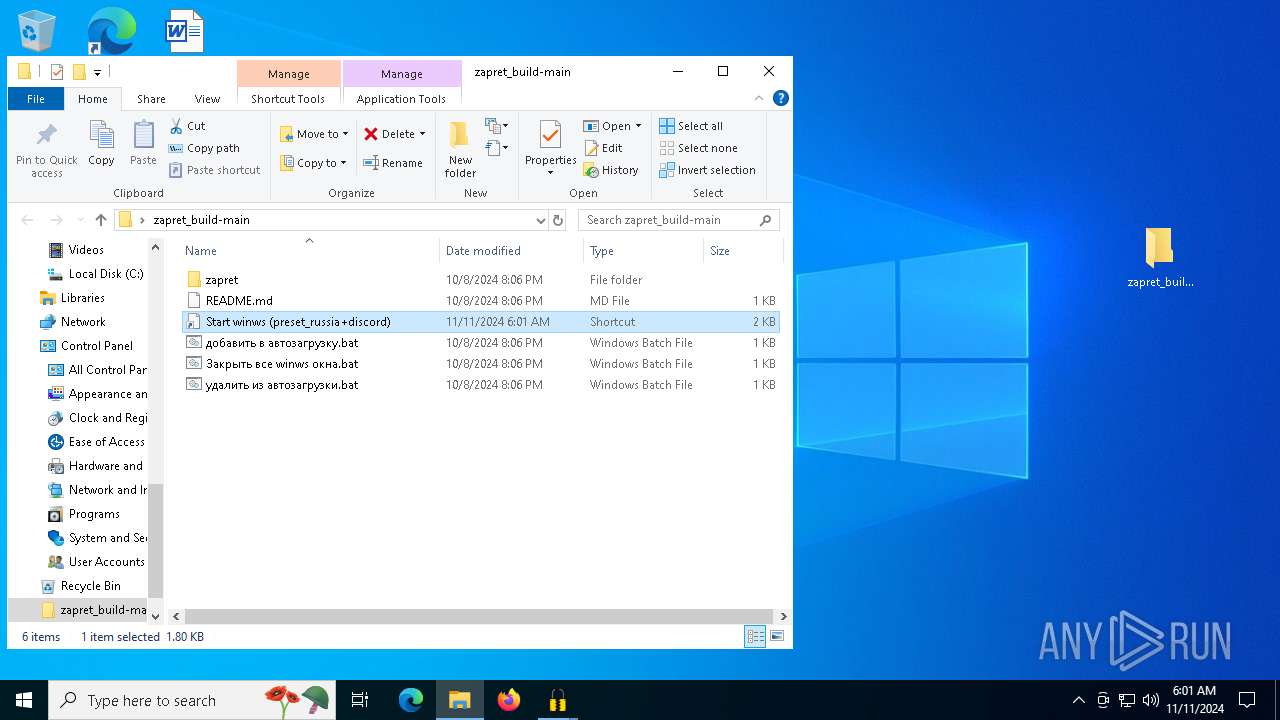
| File name: | zapret_build-main.zip |
| Full analysis: | https://app.any.run/tasks/24b648d1-9f26-42e3-a06f-b23813ef8f91 |
| Verdict: | Malicious activity |
| Analysis date: | November 11, 2024, 06:01:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | A467443E9E20853672E3B47956F499DA |
| SHA1: | 4EECE99169D716F695B84CD71A97AA6B60636DE0 |
| SHA256: | F2E007E51A2284EAEAF17D63CF20839D6B9EA7742C152B37029A8590201A6259 |
| SSDEEP: | 98304:EcZGHlS70yrjpIBHxMwlsgecngos5qdkcjYcZ4v3UcbT2MJUKsL2z8n9poYTo3Nt:VUT7Q49YO93nbpRxjY |
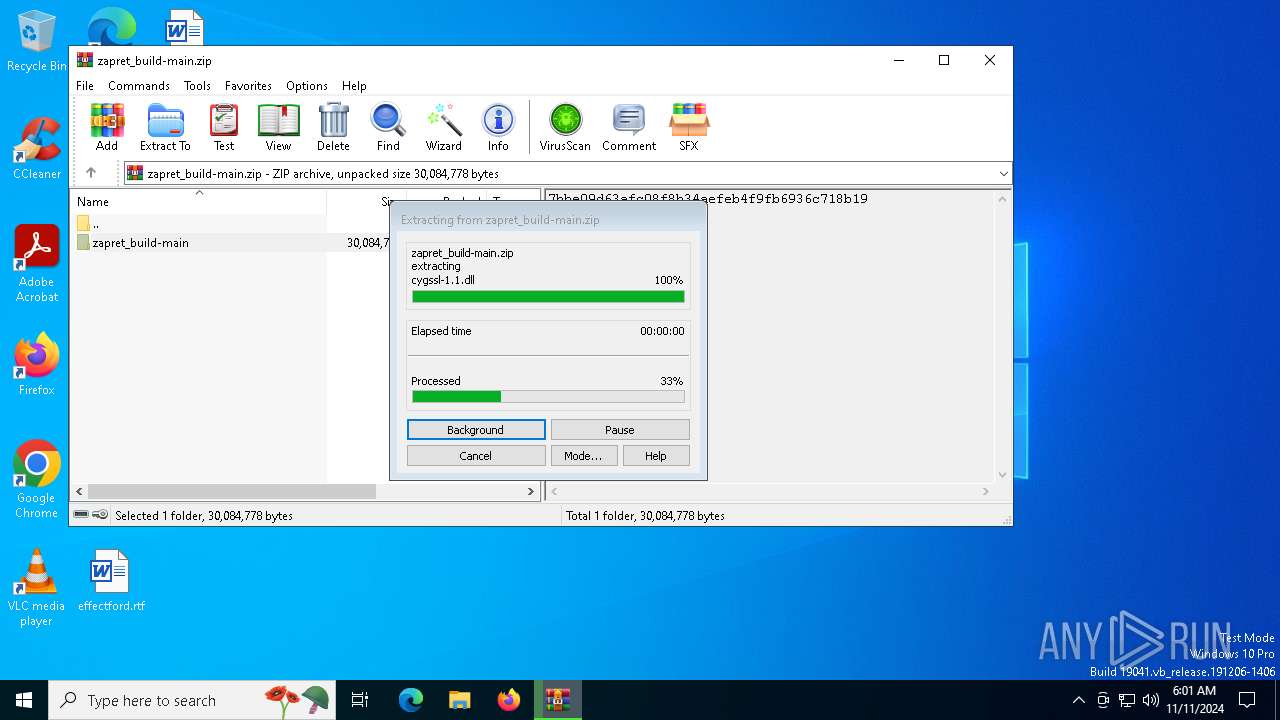
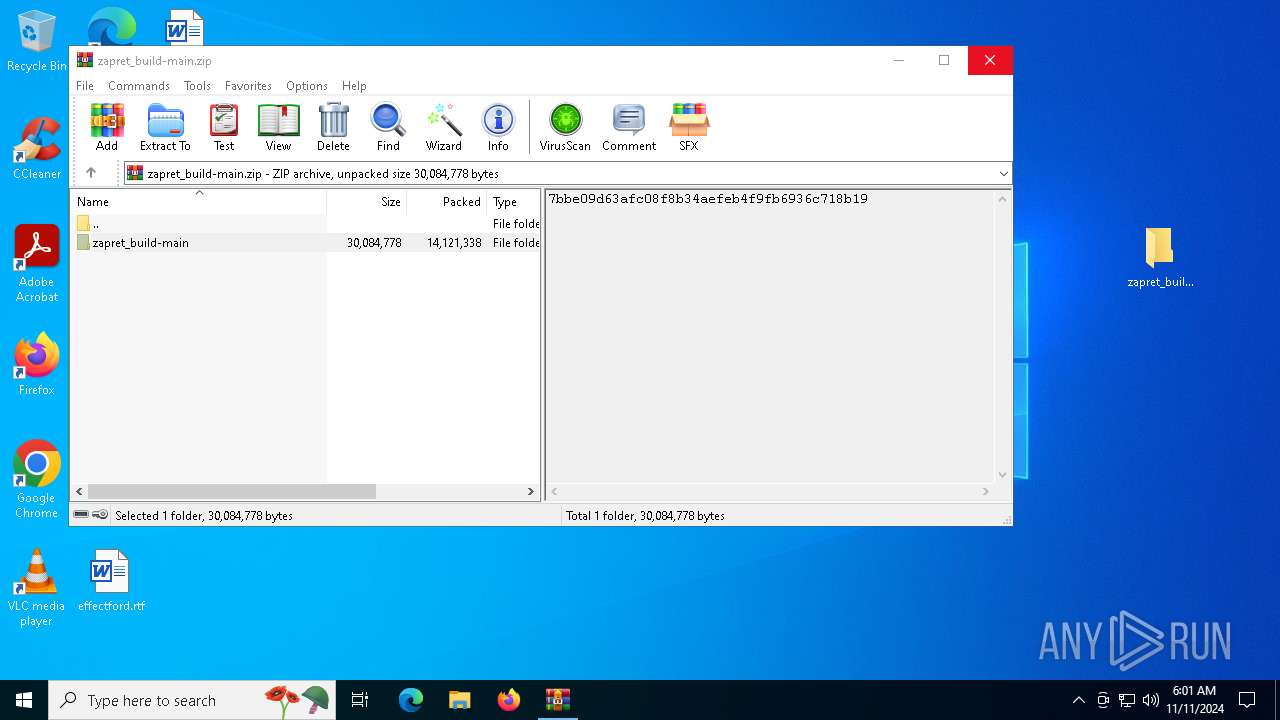
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6708)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6708)
INFO
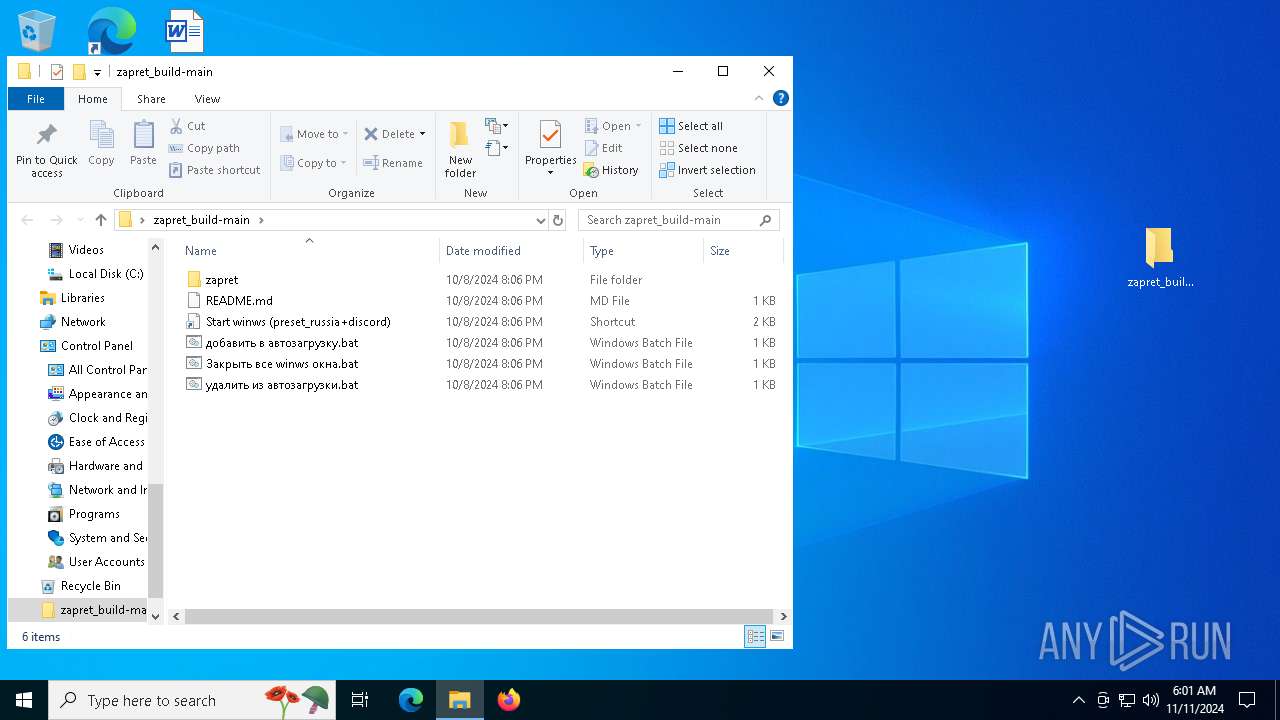
Manual execution by a user
- cmd.exe (PID: 3944)
- firefox.exe (PID: 6772)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6708)
Application launched itself
- firefox.exe (PID: 2484)
- firefox.exe (PID: 6772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:10:08 13:06:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | zapret_build-main/ |
Total processes
152
Monitored processes
22
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3744 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2280 -parentBuildID 20240213221259 -prefsHandle 2272 -prefMapHandle 2260 -prefsLen 30705 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e7979f2d-f03e-464a-8fea-6d1fc4bdcb42} 2484 "\\.\pipe\gecko-crash-server-pipe.2484" 2c965f7f710 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3852 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3944 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\preset_russia+discord.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
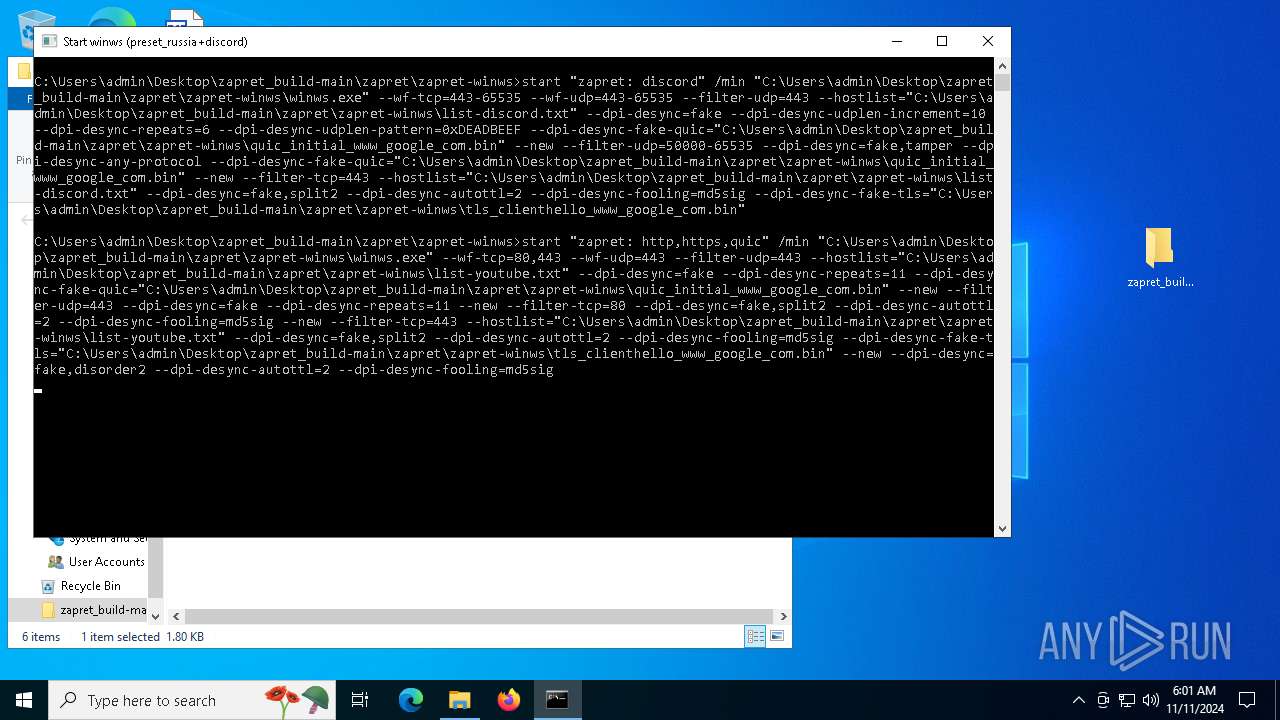
| 4448 | "C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\winws.exe" --wf-tcp=443-65535 --wf-udp=443-65535 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\list-discord.txt" --dpi-desync=fake --dpi-desync-udplen-increment=10 --dpi-desync-repeats=6 --dpi-desync-udplen-pattern=0xDEADBEEF --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-udp=50000-65535 --dpi-desync=fake,tamper --dpi-desync-any-protocol --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\list-discord.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --dpi-desync-fake-tls="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\tls_clienthello_www_google_com.bin" | C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4816 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4704 -childID 2 -isForBrowser -prefsHandle 4700 -prefMapHandle 4696 -prefsLen 36339 -prefMapSize 244343 -jsInitHandle 1524 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b349500e-0399-4517-bdb0-3df0cea101da} 2484 "\\.\pipe\gecko-crash-server-pipe.2484" 2c979c36a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5508 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2956 -childID 1 -isForBrowser -prefsHandle 2948 -prefMapHandle 2944 -prefsLen 31121 -prefMapSize 244343 -jsInitHandle 1524 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3270ff80-bd7d-4690-ba55-4f4a3beaa944} 2484 "\\.\pipe\gecko-crash-server-pipe.2484" 2c978364150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6212 | "C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\winws.exe" --wf-tcp=80,443 --wf-udp=443 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\list-youtube.txt" --dpi-desync=fake --dpi-desync-repeats=11 --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-udp=443 --dpi-desync=fake --dpi-desync-repeats=11 --new --filter-tcp=80 --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\list-youtube.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --dpi-desync-fake-tls="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\tls_clienthello_www_google_com.bin" --new --dpi-desync=fake,disorder2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig | C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6336 | "C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\winws.exe" --wf-tcp=80,443 --wf-udp=443 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\list-youtube.txt" --dpi-desync=fake --dpi-desync-repeats=11 --dpi-desync-fake-quic="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\quic_initial_www_google_com.bin" --new --filter-udp=443 --dpi-desync=fake --dpi-desync-repeats=11 --new --filter-tcp=80 --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\list-youtube.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --dpi-desync-fake-tls="C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\tls_clienthello_www_google_com.bin" --new --dpi-desync=fake,disorder2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig | C:\Users\admin\Desktop\zapret_build-main\zapret\zapret-winws\winws.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
12 521
Read events
12 499
Write events
22
Delete events
0
Modification events
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\zapret_build-main.zip | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6708) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
Executable files
147
Suspicious files
313
Text files
97
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\zapret\.gitattributes | text | |
MD5:847ED55B058F99CA654DAA2F0363711A | SHA256:9CB902885C6862F5C4D719B24D0A795EE0B67F6A4EF5E6B75286DE914F33A81E | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\zapret\arm64\WinDivert64.sys | executable | |
MD5:DEB29A3F3A032B99A8B95D70087C1840 | SHA256:55CD5C827A28FC91448F2AD1AE629E3FC951F07726819AEB035969DFBF3712C9 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\zapret\arm64\mdig.exe | executable | |
MD5:4EEC6963869BADA03FA8183FEFCAD5CF | SHA256:BA54B262675A3E1DF6D784DC9383658B598D254F53F5402FF7075D45CB8E4F92 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\zapret\binaries\win64\zapret-winws\WinDivert64.sys | executable | |
MD5:89ED5BE7EA83C01D0DE33D3519944AA5 | SHA256:8DA085332782708D8767BCACE5327A6EC7283C17CFB85E40B03CD2323A90DDC2 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\zapret\arm64\install_arm64.cmd | text | |
MD5:19C59B3508D934F93799667BF50D5714 | SHA256:8F72C1F1F1B98C56B13CB26B1E414807D50E0D6A0C982ED9D698581F952A4D96 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\zapret\arm64\ip2net.exe | executable | |
MD5:014F0D3929E0A167600BCD41816301B4 | SHA256:7FF9847DC3D693D02BA2CE8DF6D4295BDDB15F9552E868308A91391AB3A23E94 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\README.md | text | |
MD5:ED875A3DD021A279A4EB2C53D07CC956 | SHA256:977D500FE396F14F970D2482A6A5EC4EE4910F078F6E0804F93673855B89BF6C | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\zapret\blockcheck\blockcheck.cmd | text | |
MD5:C8F6CE2373AE8CFCBE070E8347FEC6B7 | SHA256:C62021151E53F72DE851086CE377B13FF7BCE291D4D58BCC527CC2BE5DE6D697 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\Start winws (preset_russia+discord).lnk | lnk | |
MD5:38F6F44A7296303298D5AA4AD1C301C8 | SHA256:D0342D2035F4656153925D982802B69FE45C4268DA7854E7C232FBF44A9E0CB4 | |||
| 6708 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6708.19460\zapret_build-main\zapret\blockcheck\zapret\blog.sh | text | |
MD5:A5F7B48E604B1CD5B929879FDCA4D856 | SHA256:A848F249447E65346ED4BB44FDAC5DE4C515522896C251CBCB937E2A701EAB08 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
72
DNS requests
88
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4 | System | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4 | System | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6384 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3644 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://www.iana.org/ | unknown | — | — | whitelisted |
4 | System | GET | 200 | 95.101.149.131:80 | http://www.iana.org/ | unknown | — | — | whitelisted |
4 | System | GET | 200 | 34.107.221.82:80 | http://www.iana.org/ | unknown | — | — | whitelisted |
4 | System | GET | 200 | 34.107.221.82:80 | http://www.iana.org/ | unknown | — | — | whitelisted |
2484 | firefox.exe | GET | 200 | 2.16.206.143:80 | http://www.iana.org/ | unknown | — | — | whitelisted |
2484 | firefox.exe | GET | 200 | 142.250.185.163:80 | http://www.iana.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1248 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
816 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.100.136:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3644 | backgroundTaskHost.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
3644 | backgroundTaskHost.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |